A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security
Abstract
:1. Introduction
2. Problem Definition
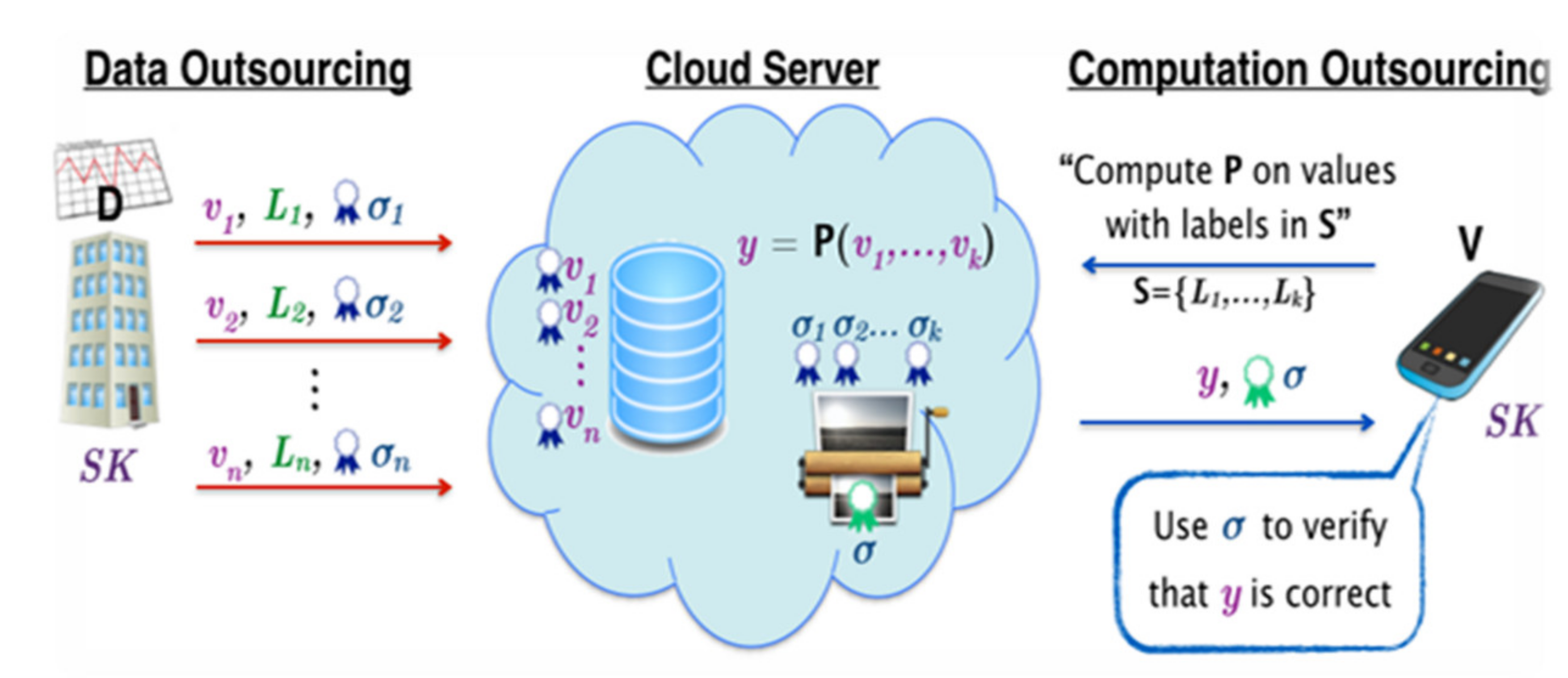
2.1. The Three Main Phases of a Verifiable Computation Scheme
- Pretreatment: the client performs this step in order to calculate some auxiliary information associated with f. Some of this information is public and shared with the server while the rest is private and kept at the client’s side.
- Preparation of inputs: At this stage, the client calculates auxiliary information on the input of the function f. Some of this information is public while the rest is private and kept at the client’s side. The public information is sent to the server to calculate f on the inputs.
- Output computation and verification: In this step, the server uses the public information associated with f and the inputs of f, which were computed in the two preceding phases, to calculate an output of the function f applied to the inputs provided. This result is then returned to the client to verify its accuracy by calculating the actual value of the output by decoding the result returned by the server using the private information calculated in the previous phases.
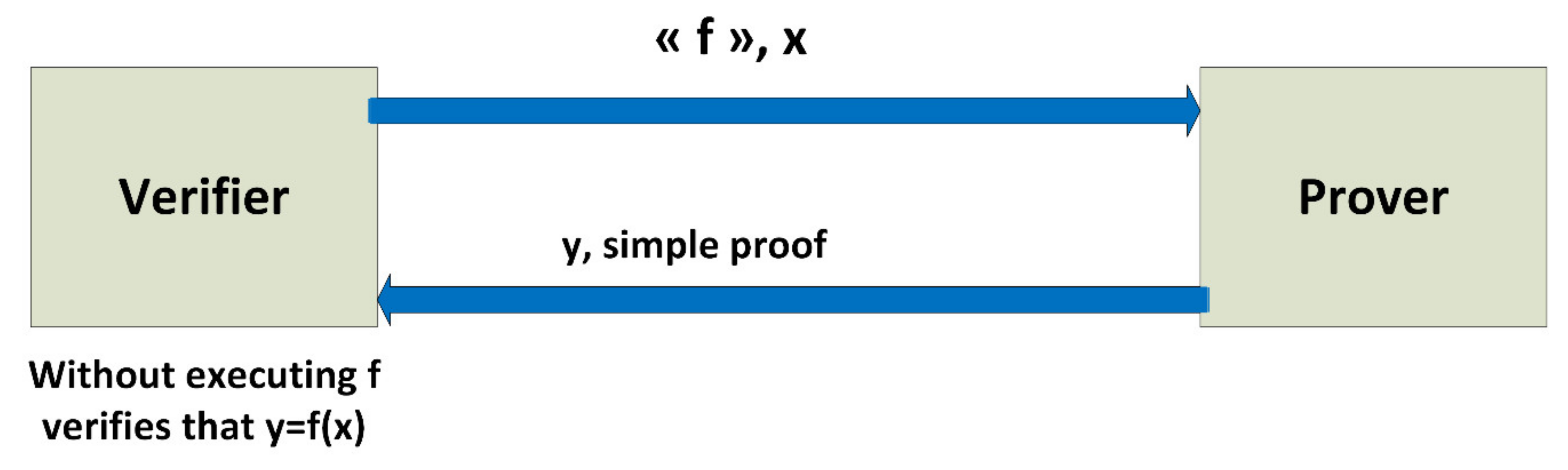
2.2. Definition of a Verifiable Computation Scheme
- : Based on security parameter λ, the key generation algorithm randomly generates a public key PK (which encodes the target function f) which is used by the server to compute f. It also calculates a corresponding secret key SK, which is kept private by the customer.
- : The problem generation algorithm uses the secret key SK to code the input x as a public value which is given to the server to calculate, and a secret value which is kept private by the client.
- : Using the client’s public key and coded entry, the server calculates an encoded version of the output of the function y = f (x).
- : Using the secret key SK and the secret , the verification algorithm converts the output of the server into an acc bit and a y string. If acc = 1 we say that the client accepts y = f (x), if acc = 0 we say that the client rejects.
2.3. Properties of a Verifiable Computation Scheme
- The security level: A verifiable computation scheme is secure if a malicious server will not be able to convince a verifier of the accuracy of a calculation even though the result is not correct. The level of security provided describes an adversary’s ability to attack the system.
- Level of confidentiality: The level of confidentiality includes different aspects. It depends on the point of view where he is related, whether to servers or to verifiers. In both cases, confidentiality means that both parties do not learn anything about inputs, output, or even the input and output of a calculation. Such a feature is desirable when processing sensitive data, e.g. medical data, government data, commercial data and military data. For example, a cloud can store medical records and perform statistics on them. In this scenario, the cloud (the server) and the auditors should not learn the health status of individual patients during the processing and verification of calculations.
- Efficiency: Efficiency considers the work required by the client (the client is the one with the verifier) and the verifier. Usually, the client must perform a preprocessing which is an additional input to the calculations made by the server. If both preprocessing and verification are more efficient than performing the calculation locally, a verifiable computation scheme is considered effective. However, efficiency is often considered in a depreciated sense, that is, the customer has installation costs that are executed once and then several operations can be performed and verified. Thus, schemes for which at least the verification process is more efficient than performing the calculations are expected to provide depreciated efficiency.
- The type of verifiability: There are two types of verifiability. If the verification can be done by a third party, then we are talking about public verifiability. If the verification requires secret information from the client then we are talking about private verifiability.
- The class of provided functions: The class of provided functions determines the expressivity of the calculations that can be performed by the verifiable computation scheme. While some systems cover only arithmetic circuits of fixed degree, others can handle arbitrary arithmetic circuits.
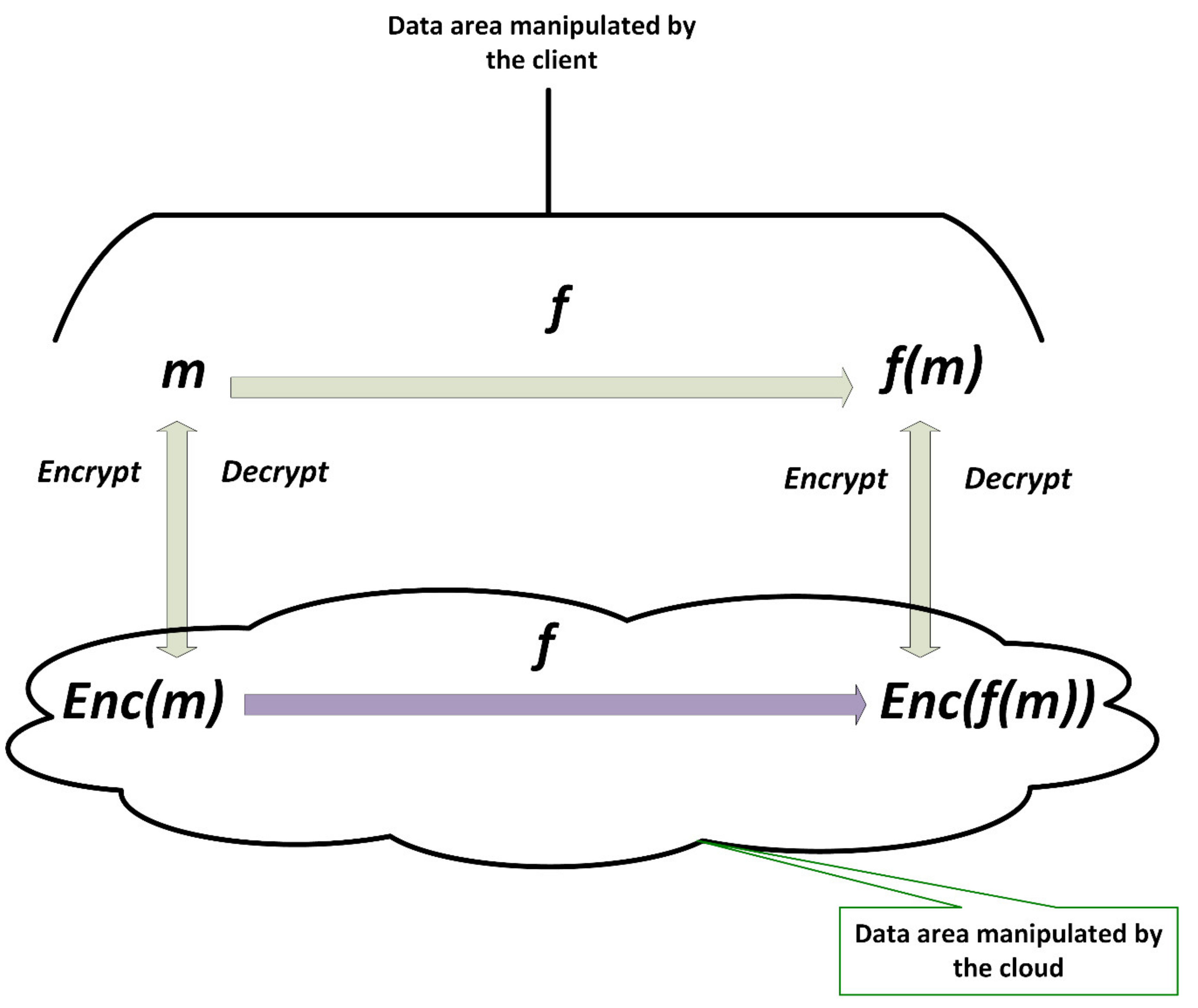
3. Definition of Fully Homomorphic Encryption
- Is an algorithm of key generation, takes as input a security parameter and outputs public and secret keys
- Is an encryption algorithm, takes as input a plaintext and a public key and outputs a ciphertext .
- Is a decryption algorithm, takes as input a ciphertext and a secret key and outputs a plaintext .
- Is an evaluation algorithm, takes as input a circuit and ciphertexts and verifies . Anyone can evaluate , since it does not require the secret key .
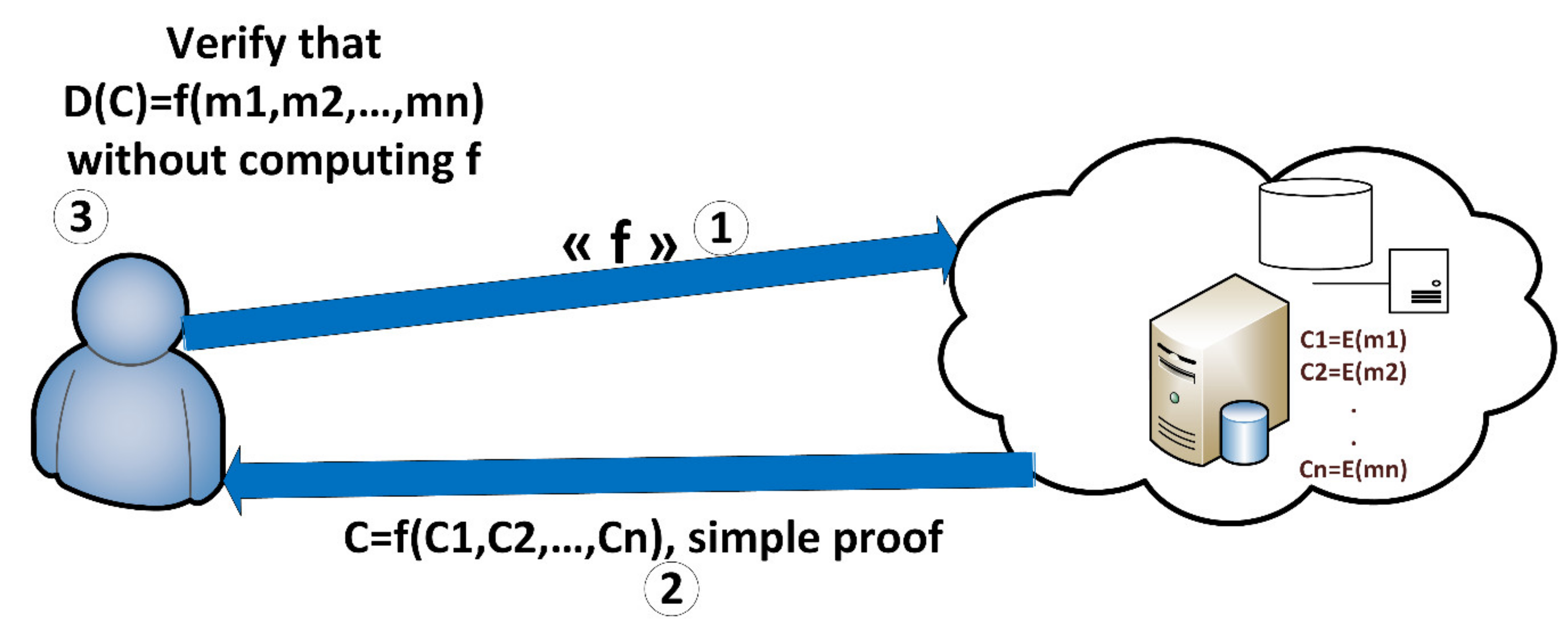
4. Definition of Verifiable Fully Homomorphic Encryption
- :
- Execute to generate the FHE keys.
- Execute to generate the VC keys. Knowing that is a function that takes as input and gives as output . This function is efficiently calculable from the algorithm .
- Take and
- :
- Calculate
- Execute to obtain .
- :
- Execute to compute . Note that is an encoding of .
- :
- Execute to obtain .
- If reject. Si , decrypt .
5. Our Techniques and Results
5.1. Mathematical Background
5.1.1. Quaternionique Field ℍ
5.1.2. Reduced Form of Quaternion
- and
- where is the cross product of .
- and .
5.1.3. Ring of Lipschitz Integers
5.1.4. Quaternionique Matrices
5.1.5. Schur Complement and Inversibility of Quaternionique Matrices
- Choose randomly three quaternions for which is invertible.
- Select randomly the fourth quaternion such that the Schur complement of in is invertible.
5.2. A Verifiable FHE Scheme
5.2.1. Key Generation
- Bob generates randomly two big prime numbers p and q.
- Then, he calculates .
- Bob generates randomly an invertible matrixsuch that is an invertible matrix.
- Bob calculates the inverse of and , Which will be denoted and .
- The secrete key is .
5.2.2. Encryption
- Bob transforms into a quaternion:
- Bob generates a matrix: such that and are randomly generated.
- Bob calculates .
- Bob transforms into a quaternion:
- Bob generates a matrix such that
- The ciphertext of is:such that is randomly generated.
5.2.3. Decryption and Verification
- He calculates .
- He computes .
- Then he takes the first inputs of the resulting matrices and
- Finally, he recovers his clear message by verifying if . If the verification is true, then the clear message returned is σ otherwise the ciphertext has been modified.
5.2.4. Addition and Multiplication
- (1)
- = .
- (2)
- = .
6. Security of the Proposed Scheme
6.1. Semantic Security
6.1.1. The Adversary:
- Is a probabilistic polynomial time Turing machine.
- Has all the algorithms.
- Has full access to communication media.
6.1.2. Chosen Ciphertext Attack
Startup
- The challenger generates a secret key based on some security parameter (e.g., a key size in bits) and retains it.
- The adversary may ask the encryption oracle for any number of encryptions, calls to the decryption oracle based on arbitrary ciphertexts, or other operations.
- Eventually, the adversary submits two distinct chosen plaintexts , to the challenger.
The Challenge
- The challenger selects a bit uniformly at random, and sends the “challenge” ciphertext back to the adversary. The adversary is free to perform any number of additional computations or encryptions.
- In the non-adaptive case (IND-CCA), the adversary may not make further calls to the decryption oracle before guessing.
- In the adaptive case (IND-CCA2), the adversary may make further calls to the decryption oracle, but may not submit the challenge ciphertext C.
- In the end it will guess the value of .
The Result
- Again, the adversary wins the game if it guesses the bit .
- A cryptosystem is indistinguishable under chosen ciphertext attack if no adversary can win the above game with probability greater than where is a negligible function in the security parameter .
- If then the difference is the advantage of the given adversary in distinguishing the ciphertext.
In Our Situation
- The adversary should distinguish an encryption of zero from an encryption of one after asking the encryption oracle of a number of encryptions and the decryption oracle to decrypt arbitrary ciphertexts.
- The adversary can do operations on the two given ciphertexts to distinguish zero from one.
- As he can do operations on the entire ciphertext matrices or just to use some entrees (the diagonal of ciphertexts matrices, computations on the trace and the diagonal).
- In our case, even if the diagonal of completely determines the invertibility of , an encryption of a bit is always non invertible because of the choice of the random () which gives always det(C) = 0.
6.2. Breakability
- (1)
- (2)
- (3)
- (4)
- (5)
- (6)
- (7)
- (8)
- (9)
- (10)
- (11)
- (12)
- (13)
- (14)
- (15)
- (16)
- (17)
7. Comparison with Other Schemes
8. Implementation and Tests
9. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Rivest, R.L.; Adleman, L.; Dertouzos, M.L. On data banks and privacy homomorphisms. Found. Secur. Comput. 1978, 4, 169–180. [Google Scholar]
- Gentry, C. A Fully Homomorphic Encryption Scheme. Ph. D Thesis, Stanford University, Stanford, CA, USA, 2009. Available online: http://crypto.stanford.edu/craig-thesis (accessed on 20 December 2018).
- Smart, N.; Vercauteren, F. Fully Homomorphic Encryption with Relatively Small Key and Ciphertext Sizes. In International Workshop on Public Key Cryptography; Cryptology ePrint Archive, Report 2009/571; Springer: Berlin, Germany, 2009; Available online: http://eprint.iacr.org/571.pdf (accessed on 20 December 2018).
- Van Dijk, M.; Gentry, C.; Halevi, S.; Vaikuntanathan, V. Fully homomorphic encryption over the integers. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques Cryptology, Cologne, Germany, 26–30 April 2009; Available online: http://eprint.iacr.org/ (accessed on 20 December 2018).
- Chunsheng, G. Fully Homomorphic Encryption Based on Approximate Matrix GCD. Available online: http://eprint.iacr.org/2011/645.pdf (accessed on 20 December 2018).
- Vikuntanathan, V.; Brakerski, Z. Efficient Fully Homomorphic Encryption from (Standard) LWE. Available online: http://eprint.iacr.org/2011/344.pdf (accessed on 20 December 2018).
- El-Yahyaoui, A.; Elkettani, M.D. Fully homomorphic encryption: State of art and comparison. Int. J. Comput. Sci. Inf. Secur. 2016, 14, 159–167. [Google Scholar]
- Coron, J.; Mandal, A.; Naccache, D.; Tibouchi, M. Fully Homomorphic Encryption over the Integers with Shorter Public Keys. Available online: http://eprint.iacr.org/2011/441.pdf (accessed on 20 December 2018).
- Lepoint, J.C.T.; Tibouchi, M. Batch Fully Homomorphic Encryption over the Integers. 2012. Available online: http://eprint.iacr.org/2013/036.pdf (accessed on 20 December 2018).
- Genaro, R.; Gentry, C.; Parno, B. Non-Interactive Verifiable Computing: Outsourcing Computation to Untrusted Workers; Cryptology eprint IACR, Report 547/2009; Springer: Berlin, Germany, 2009. [Google Scholar]
- Demirel, D.; Schabhüser, L.; Buchmann, J. Privately and Publicly Verifiable Computing Techniques a Survey; Briefs in Computer Science; Springer: Darmstadt, Germany, 2016. [Google Scholar]
- Fiore, D.; Gennaro, R.; Pastro, V. Efficiently Verifiable Computation on Encrypted Data. In Proceedings of the 2014 ACM SIGSAC Conference on Computer and Communications Security Cryptology, Scottsdale, AZ, USA, 3–7 November 2014. [Google Scholar]
- Li, J.; Wang, L. Noise-Free Symmetric Fully Homomorphic Encryption Based on Noncommutative Rings; Cryptology ePrint Archive, Report 2015/641. Available online: http://eprint.iacr.org/2015/641.pdf (accessed on 20 December 2018).
- Gjøsteen, K.; Strand, M. Can There Be Efficient and Natural FHE Schemes? Available online: https://eprint.iacr.org/2016/105.pdf (accessed on 20 December 2018).
| Algorithm | Cleartext | Secrete Key | Public Key | Ciphertext |
|---|---|---|---|---|
| Gentry [2] | {0,1} | |||
| Smart-Verc [3] | {0,1} | |||
| DGHV [4] | {0,1} | |||
| CMNT [8] | {0,1} | |||
| BatchDGHV [9] | ||||
| LI-WANG [13] | ||||
| Our scheme |
| Security Param (bits) | Key Gen (ms) | Enc (ms) | Dec (ms) | Verification (ms) | Add (ms) | Mult (ms) | Secrete Key (kbits) | Cleartext (kbits) | Ciphertext (kbits) |
|---|---|---|---|---|---|---|---|---|---|
| 256 | 67 | 10 | 1 | <<1 | <<1 | <<1 | 40 | 0.5 | 16 |
| 512 | 166 | 26 | 3 | 1 | <<1 | <<1 | 80 | 1 | 32 |
| 1024 | 718 | 111 | 9 | 2 | <<1 | 2 | 160 | 2 | 64 |
| 2048 | 5209 | 849 | 28 | 8 | <<1 | 8 | 320 | 4 | 128 |
| 4096 | 63,516 | 10,075 | 84 | 18 | <<1 | 23 | 640 | 8 | 256 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
EL-YAHYAOUI, A.; ECH-CHERIF EL KETTANI, M.D. A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security. Technologies 2019, 7, 21. https://doi.org/10.3390/technologies7010021
EL-YAHYAOUI A, ECH-CHERIF EL KETTANI MD. A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security. Technologies. 2019; 7(1):21. https://doi.org/10.3390/technologies7010021
Chicago/Turabian StyleEL-YAHYAOUI, Ahmed, and Mohamed Dafir ECH-CHERIF EL KETTANI. 2019. "A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security" Technologies 7, no. 1: 21. https://doi.org/10.3390/technologies7010021
APA StyleEL-YAHYAOUI, A., & ECH-CHERIF EL KETTANI, M. D. (2019). A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security. Technologies, 7(1), 21. https://doi.org/10.3390/technologies7010021





