Artificial Intelligence Techniques for Cognitive Sensing in Future IoT: State-of-the-Art, Potentials, and Challenges
Abstract
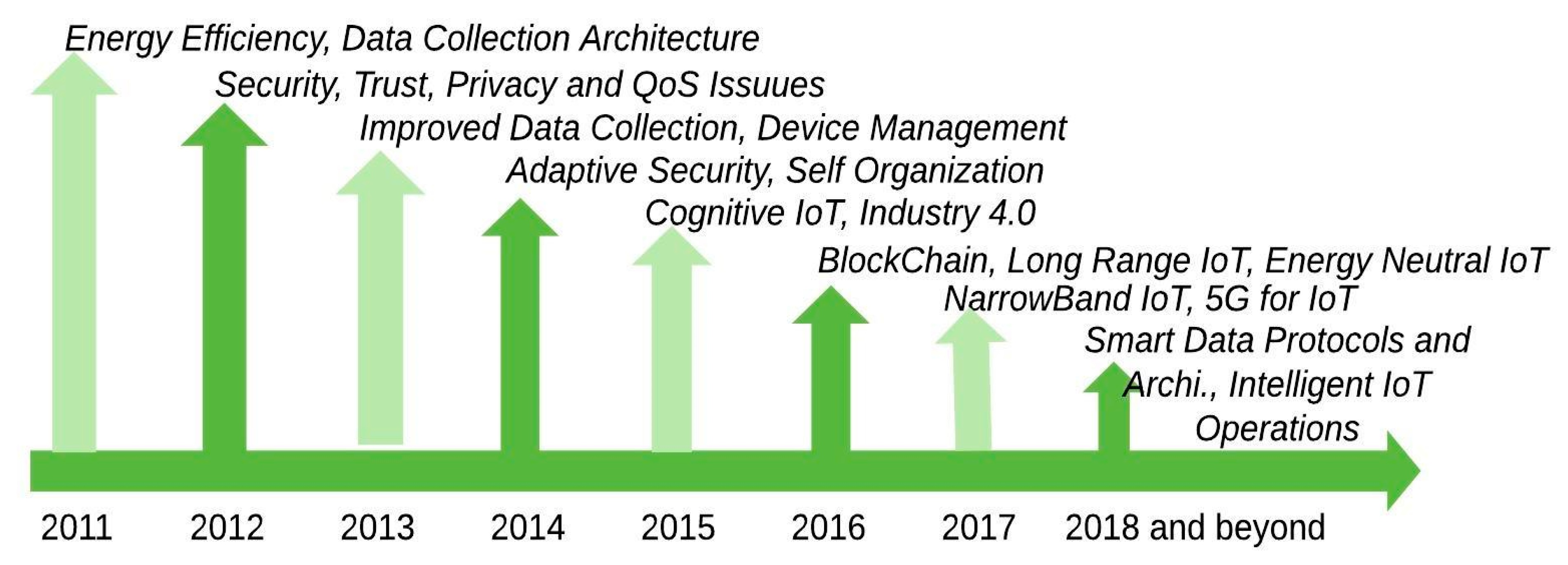
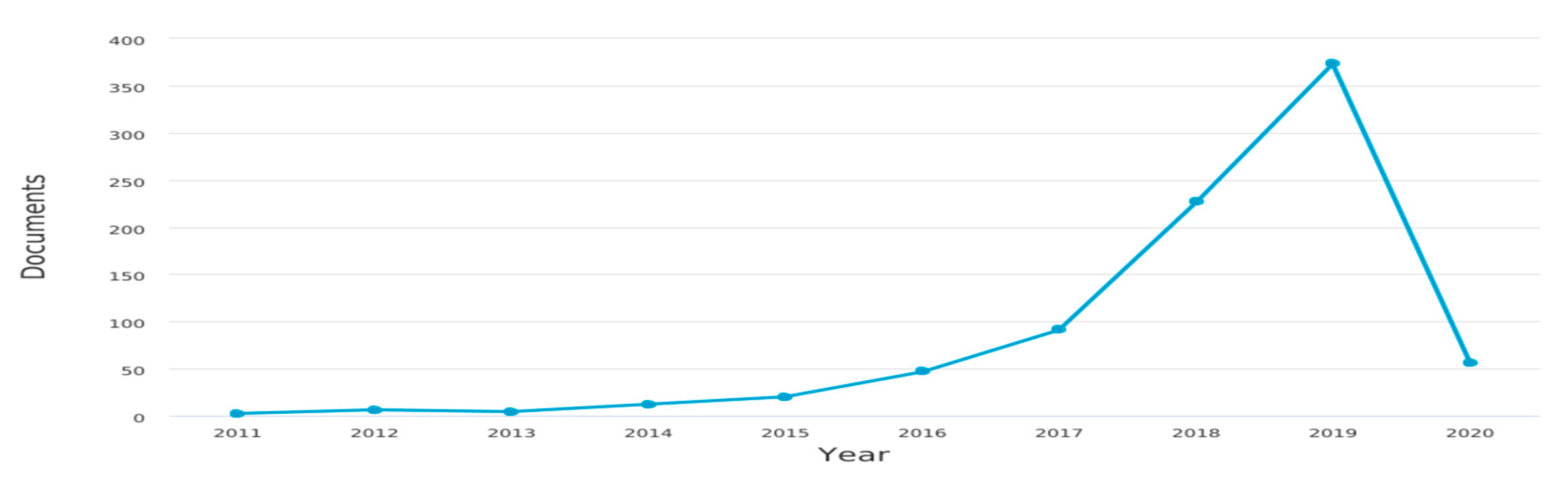
1. Introduction
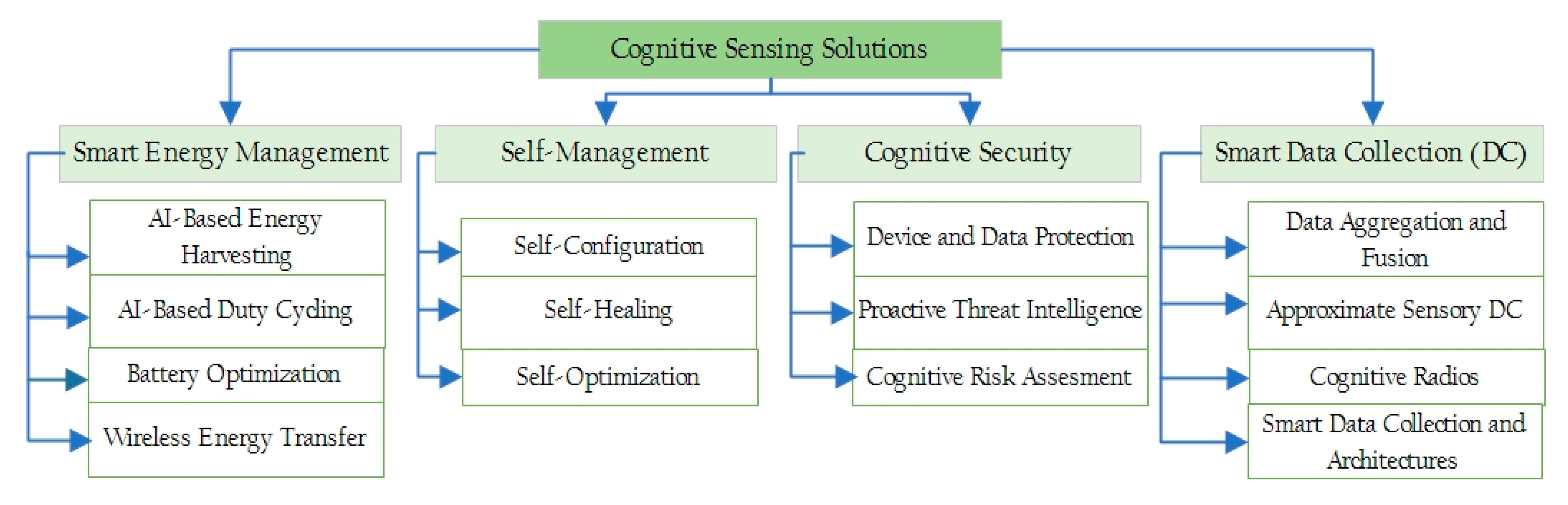
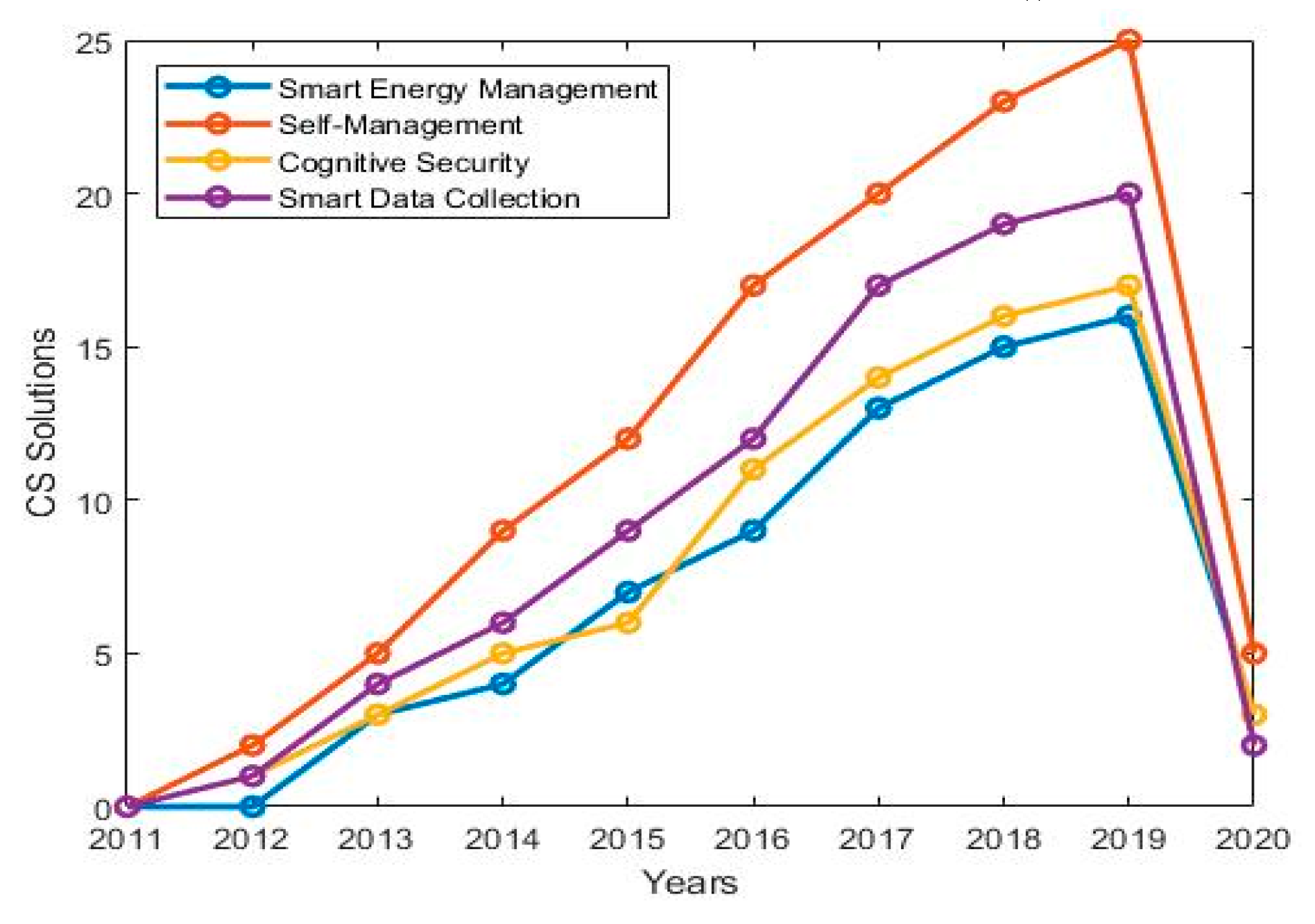
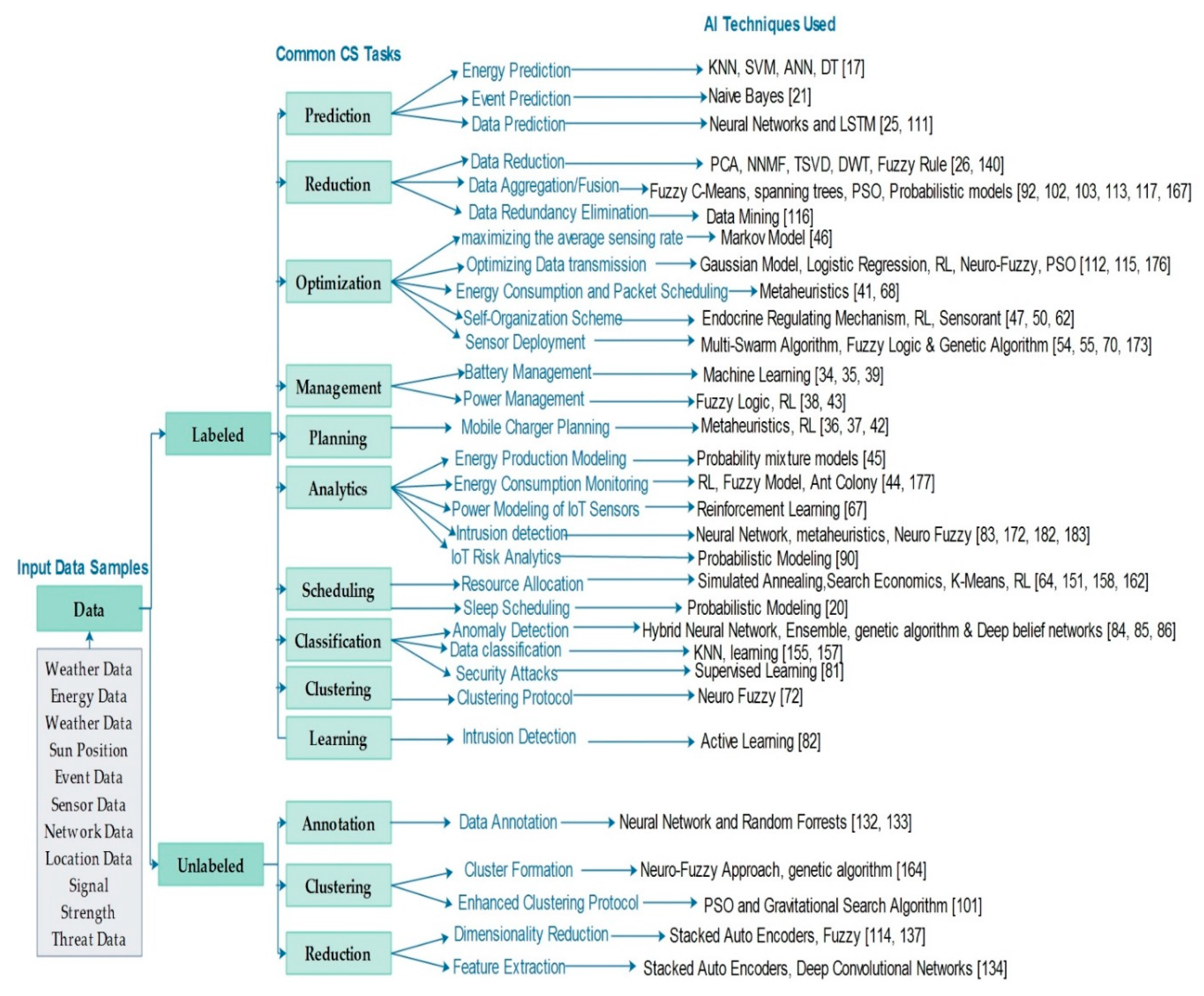
2. Classification of the Cognitive Sensing Solutions and Surveyed AI Techniques
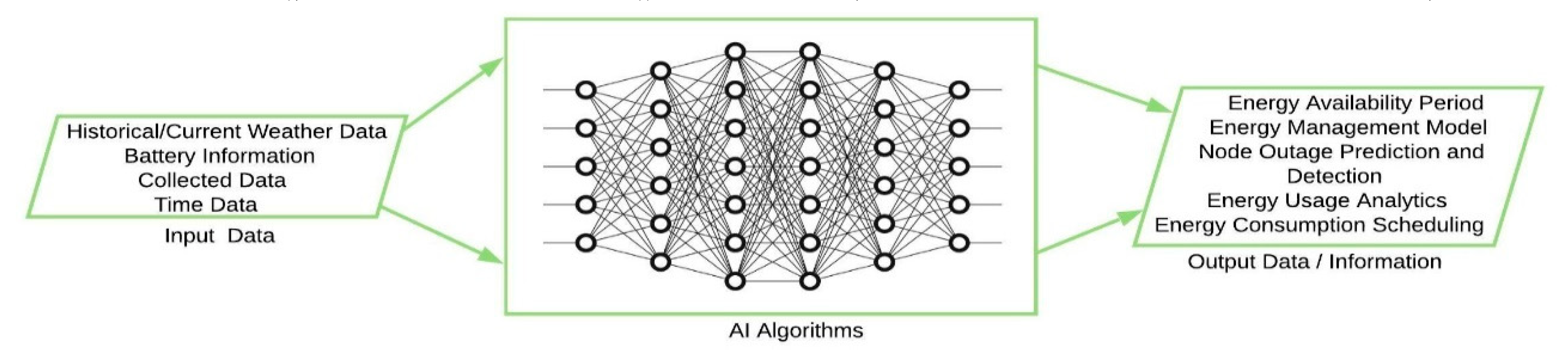
3. Smart Energy Management in the Future IoT
3.1. AI-Enabled Energy Harvesting in IoT Devices
3.2. AI-Enabled Duty Cycling in IoT Devices
3.3. AI-Enabled Battery Optimization in IoT Devices
3.4. AI-Enabled Wireless Energy Transfer in IoT Devices
4. Self-Management in the Future IoT
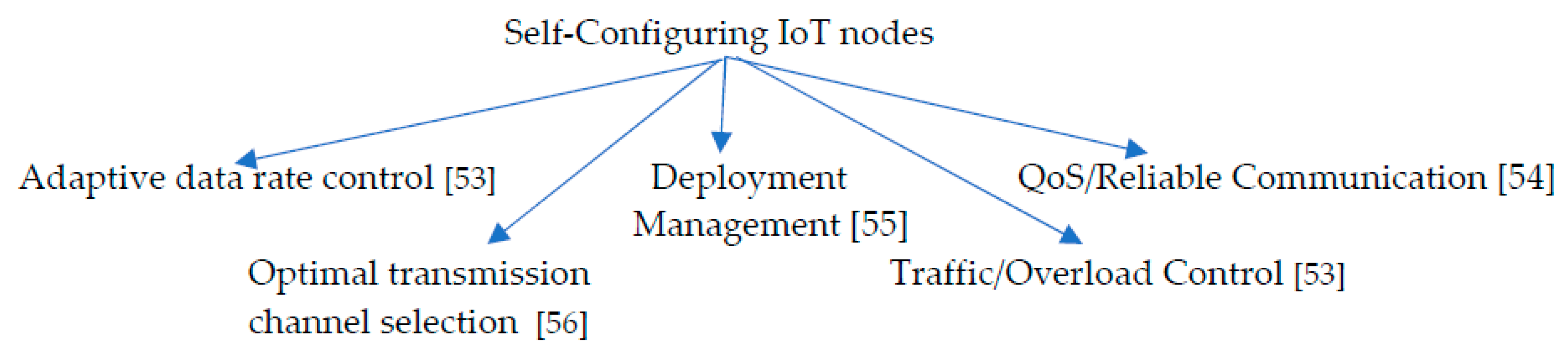
4.1. Self-Configuring IoT Nodes
4.2. Self-Healing IoT Nodes
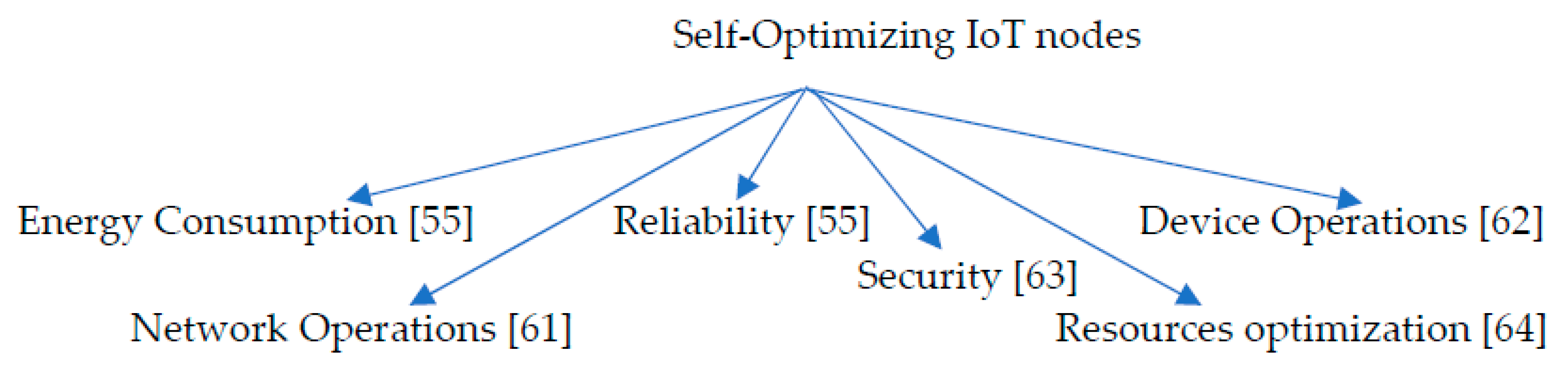
4.3. Self-Optimizing IoT Nodes
5. Cognitive Security in the Future IoT
6. Smart Data Collection in the Future IoT
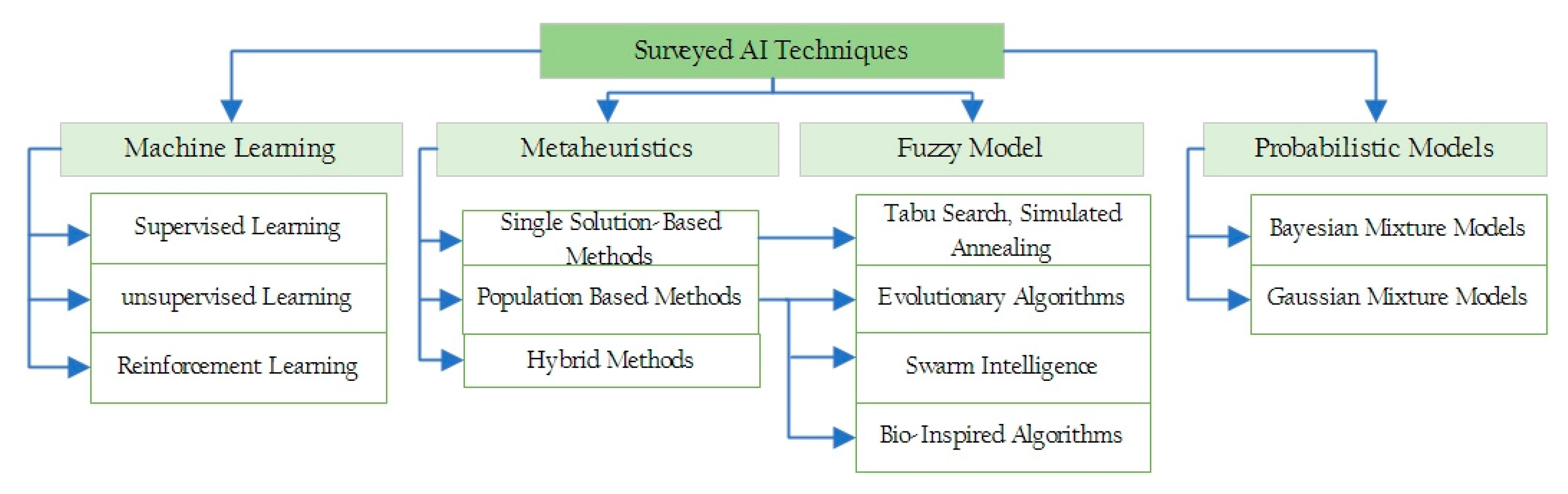
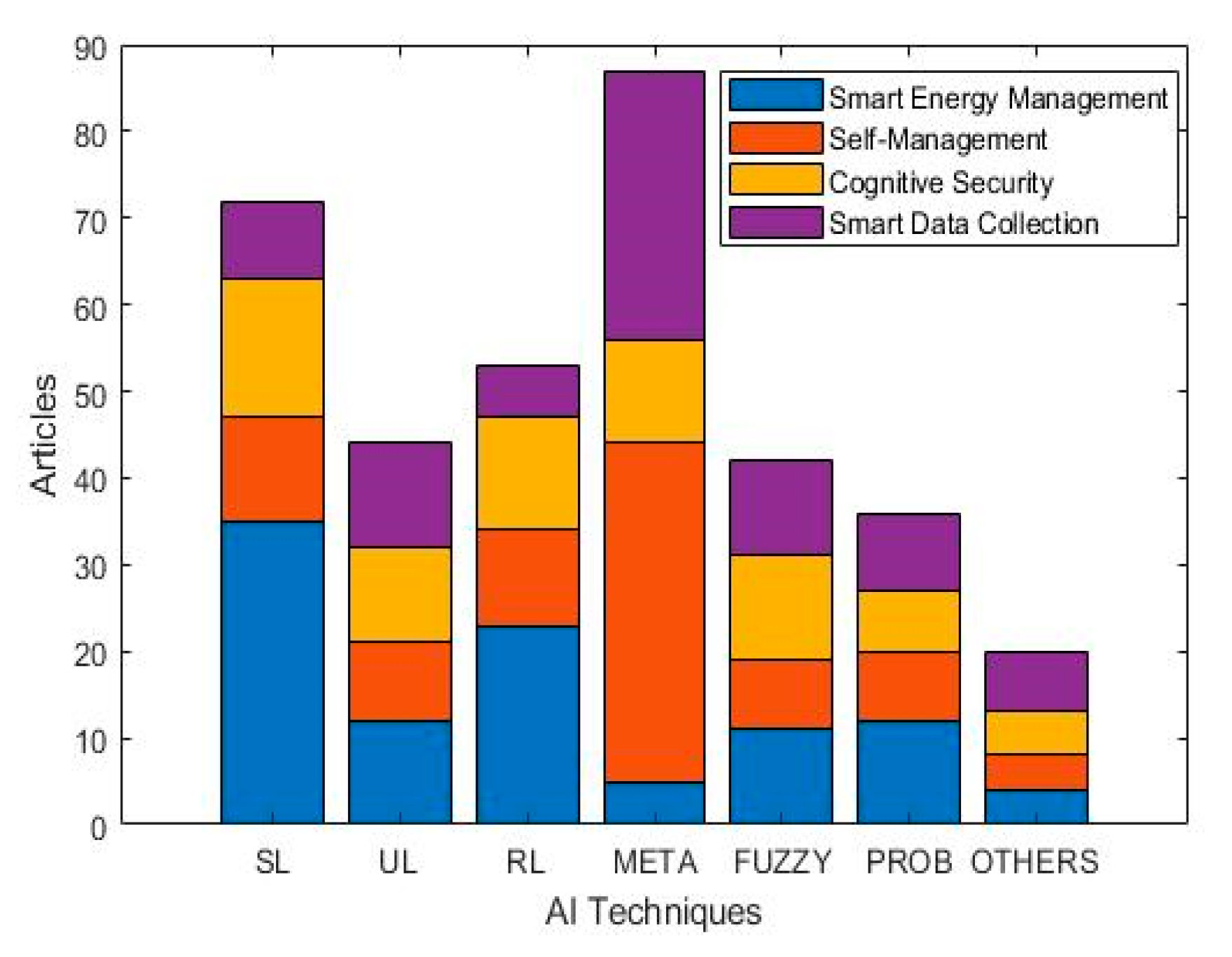
7. Classification of the Surveyed AI Techniques
7.1. Machine Learning Techniques
7.1.1. Supervised Learning Techniques
7.1.2. Unsupervised Learning
7.1.3. Reinforcement Learning
7.2. Metaheuristics
7.2.1. Single Solution Based Metaheuristics
7.2.2. Population-Based Metaheuristics
Evolutionary Algorithms
Swarm Intelligence Algorithms
Bio-Inspired Algorithms
7.2.3. Hybrid Metaheuristics
7.3. Fuzzy Models
7.4. Probabilistic Models
8. Challenges of AI in Cognitive Sensing and the Way Forward
8.1. Challenges of AI for Cognitive Sensing Solutions
- (i)
- Modeling Difficulties: IoT systems have the requirements of usability in real-time, low latency and high availability. Hence, in such systems, developing parameterized models for application or research purposes is difficult.
- (ii)
- Lack of Needed/Quality Data: Poor quality of data or its lack thereof reduces the efficiency of predictive models or knowledge base used by cognitive systems. Such models are used for tasks like forecasting, analysis, decision making, etc. Thus, it becomes a problem when such tasks are carried out using faulty models.
- (iii)
- Irregular data usage pattern: Cognitive systems use various planning and optimization models built based on their usage patterns to optimize resource consumption. Hence, developing such models become difficult when nodes receive irregular requests or commands from users/applications
- (iv)
- Resource Limitation: The energy and computational requirement of some AI algorithms can sometimes be high for the resource-deprived nodes. Algorithms such as SVM, KNN, ANN are known to be computationally complex and using them on a resource-starved node becomes a difficult task.
- (v)
- Improved Algorithms: Currently, some algorithms are sensitive to data outliers while others lack accuracy and are prone to overfitting. Thus, using these algorithms without addressing the aforementioned issues might yield undesired results. Recent trends adopt the use of ensemble models to mitigate some of these issues.
- (vi)
- Data Privacy: In IoT systems, data privacy emphasizes the proper handling of data in terms of consent, notice, and regulatory obligations. As a result, some of the data needed by AI algorithms might become unavailable due to privacy violation concerns or their outright sensitive nature. Apart from this, some of the data privacy-related technologies such as protection and encryption further complicate the data availability challenge for AI algorithms. Hence, a serious effort is needed from the research community on how to make these data available without compromising privacy and its associated concerns.
8.2. The Way Forward
- (i)
- Data Warehousing: This concept describes the use of a central database to integrate data from multiple heterogeneous sources to support FIoT operations. Historical weather data, threat/attack data, user data, and other applicable IoT data are required by AI algorithms but sometimes these are not available due to new installations having insufficient data or outright data loss. As a result, keeping these datasets in locations where they can be accessed on demand by FIoT nodes when needed for their operation becomes a valuable approach.
- (ii)
- Computational offloading: This is a technique that can help alleviate the resource constrain problem in IoT nodes by transferring complex computations to more resourceful devices and receiving the results back from these devices [184]. It has been used in mobile device clouds and mobile edge for task execution but yet to be fully exploited for IoT operations.
- (iii)
- Energy Neutral Operation: This is a mode of operation of an IoT device where the energy consumed during operation is always less or equal to the energy harvested from the environment. In this mode, devices can theoretically operate infinitely without energy constraint. Hence, this concept is worth further exploration of its usage in the FIoT.
- (iv)
- Lightweight AI Algorithms: Due to the computationally intense nature of some algorithms which make them difficult for use in IoT devices, resource-efficient AI algorithms that can run seamlessly on FIoT nodes are needed from the research community.
- (v)
- Effective Data Management Policies: Data privacy describes the interwoven relationship between data collection, transmission, usage, user’s privacy, and the legal issues surrounding them. Hence, if not managed well, data privacy poses a threat to data availability for AI algorithms. Furthermore, data abuse or leaks could result in unwanted scandals that negatively affect individuals, businesses and organizational processes [185]. Some of the existing data management solutions or policies like the general data protection regulation [186], the databox project [187], and the IBM data privacy protection framework [188], could be leveraged or extended to provide customized solutions for the IoT domain.
- (vi)
- AI-assisted Data Collection: Over the years, AI/ML systems have proven to be far more accurate than other systems at a variety of tasks such as automation, diagnostics, analytics, etc. hence, using AI to assist the data collection process is a potential research direction for the future. This, however, is likely to raise the issue of its effect on human rights and ethics. For example, how can such a system understand the human right to data consent, access, protection, privacy or fair processing? Will it understand the thin line between private and public data?
9. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Akpakwu, G.A.; Silva, B.J.; Hancke, G.P.; Abu-Mahfouz, A.M. A survey on 5g networks for the internet of things: Communication technologies and challenges. IEEE Access 2018, 6, 3619–3647. [Google Scholar] [CrossRef]
- Ogbodo, E.U.; Dorrell, D.; Abu-Mahfouz, A.M. Cognitive radio based sensor network in smart grid: Architectures, applications and communication technologies. IEEE Access 2017, 5, 19084–19098. [Google Scholar] [CrossRef]
- Desai, M.; Phadke, A. Internet of Things based vehicle monitoring system. In Proceedings of the 2017 Fourteenth International Conference on Wireless and Optical Communications Networks (WOCN), Mumbai, India, 24–26 February 2017; pp. 1–3. [Google Scholar]
- Parpala, R.C.; Iacob, R. Application of IoT concept on predictive maintenance of industrial equipment. Proc. MATEC Web Conf. 2017. [Google Scholar] [CrossRef]
- Wu, Q.; Ding, G.; Xu, Y.; Feng, S.; Du, Z.; Wang, J.; Long, K. Cognitive Internet of Things: A New Paradigm Beyond Connection. IEEE Int. Things J. 2014, 1, 129–143. [Google Scholar] [CrossRef]
- Pramanik, P.K.D.; Pal, S.; Choudhury, P. Beyond Automation: The Cognitive IoT. Artificial Intelligence Brings Sense to the Internet of Things. In Cognitive Computing for Big Data Systems Over IoT: Frameworks, Tools and Applications; Sangaiah, A.K., Thangavelu, A., Meenakshi Sundaram, V., Eds.; Springer International Publishing: Cham, Switzerland, 2018; pp. 1–37. [Google Scholar]
- Osuwa, A.A.; Ekhoragbon, E.B.; Fat, L.T. Application of artificial intelligence in Internet of Things. In Proceedings of the 2017 9th International Conference on Computational Intelligence and Communication Networks (CICN), Girne, Cyprus, 16–17 September 2017; pp. 169–173. [Google Scholar]
- He, A.; Bae, K.K.; Newman, T.R.; Gaeddert, J.; Kim, K.; Menon, R.; Tranter, W.H. A survey of artificial intelligence for cognitive radios. IEEE Trans. Veh. Technol. 2010, 59, 1578–1592. [Google Scholar] [CrossRef]
- Mahdavinejad, M.S.; Rezvan, M.; Barekatain, M.; Adibi, P.; Barnaghi, P.; Sheth, A.P. Machine learning for Internet of Things data analysis: A survey. Digital Commun. Netw. 2017, 4, 161–175. [Google Scholar] [CrossRef]
- Zaheer, K.; Othman, M.; Rehmani, M.H.; Perumal, T. A Survey of Decision-Theoretic Models for Cognitive Internet of Things (CIoT). IEEE Access 2018, 6, 22489–22512. [Google Scholar] [CrossRef]
- Al-Garadi, M.A.; Mohamed, A.; Al-Ali, A.; Du, X.; Guizani, M. A Survey of Machine and Deep Learning Methods for Internet of Things (IoT) Security. arXiv 2018, arXiv:1807.11023. [Google Scholar] [CrossRef]
- Mohammadi, M.; Al-Fuqaha, A.; Sorour, S.; Guizani, M. Deep Learning for IoT Big Data and Streaming Analytics: A Survey. IEEE Commun. Surv. Tutor. 2018, 20, 2923–2960. [Google Scholar] [CrossRef]
- Sanislav, T.; Zeadally, S.; Mois, G.D.; Folea, S.C. Wireless energy harvesting: Empirical results and practical considerations for Internet of Things. J. Netw. Comput. Appl. 2018, 121, 149–158. [Google Scholar] [CrossRef]
- Tuna, G.; Gungor, V.C.; Gulez, K.; Hancke, G.; Gungor, V. Energy harvesting techniques for industrial wireless sensor networks. In Industrial Wireless Sensor Networks: Applications, Protocols, Standards, and Products; Taylor & Francis: Milton Park, Didcot, UK; Abingdon, UK, 2013; pp. 119–136. [Google Scholar]
- Akan, O.B.; Cetinkaya, O.; Koca, C.; Ozger, M. Internet of hybrid energy harvesting things. IEEE Internet Things J. 2017, 5, 736–746. [Google Scholar] [CrossRef]
- Sharma, H.; Haque, A.; Jaffery, Z.A. Modeling and optimisation of a solar energy harvesting system for wireless sensor network nodes. J. Sens. Actuator Netw. 2018, 7, 40. [Google Scholar] [CrossRef]
- Kraemer, F.A.; Ammar, D.; Braten, A.E.; Tamkittikhun, N.; Palma, D. Solar energy prediction for constrained IoT nodes based on public weather forecasts. In Proceedings of the Seventh International Conference on the Internet of Things, Linz, Austria, 22–25October 2017; pp. 1–8. [Google Scholar]
- Patil, S.; Vijayalashmi, M.; Tapaskar, R. Solar energy monitoring system using IOT. Indian J. Sci. Res. 2017, 149–156. Available online: https://go.gale.com/ps/anonymous?id=GALE%7CA521163122&sid=googleScholar&v=2.1&it=r&linkaccess=abs&issn=09762876&p=AONE&sw=w (accessed on 15 April 2020).
- Arifuzzaman, M.; Matsumoto, M. An efficient medium access control protocol with parallel transmission for wireless sensor networks. J. Sens. Actuator Netw. 2012, 1, 111–122. [Google Scholar] [CrossRef]
- Mukherjee, M.; Shu, L.; Prasad, R.V.; Wang, D.; Hancke, G.P. Sleep scheduling for unbalanced energy harvesting in industrial wireless sensor networks. IEEE Commun. Mag. 2019, 57, 108–115. [Google Scholar] [CrossRef]
- Karakostas, B. Event Prediction in an IoT Environment Using Naïve Bayesian Models. Procedia Comput. Sci. 2016, 83, 11–17. [Google Scholar] [CrossRef]
- Rani, S.; Talwar, R.; Malhotra, J.; Ahmed, S.; Sarkar, M.; Song, H. A novel scheme for an energy efficient Internet of Things based on wireless sensor networks. Sensors 2015, 15, 28603–28626. [Google Scholar] [CrossRef]
- Wu, F.; Rüdiger, C.; Yuce, M.R. Real-time performance of a self-powered environmental IoT sensor network system. Sensors 2017, 17, 282. [Google Scholar] [CrossRef]
- Hesse, H.C.; Schimpe, M.; Kucevic, D.; Jossen, A. Lithium-ion battery storage for the grid—A review of stationary battery storage system design tailored for applications in modern power grids. Energies 2017, 10, 2107. [Google Scholar] [CrossRef]
- Dias, G.M.; Bellalta, B.; Oechsner, S. Using data prediction techniques to reduce data transmissions in the IoT. In Proceedings of the 2016 IEEE 3rd World Forum on Internet of Things (WF-IoT), Reston, VA, USA, 12–14 December 2016; pp. 331–335. [Google Scholar]
- Jarwan, A.; Sabbah, A.; Ibnkahla, M. Data transmission reduction schemes in WSNs for efficient IoT systems. IEEE J. Sel. Areas Commun. 2019, 37, 1307–1324. [Google Scholar] [CrossRef]
- Chen, M.; Miao, Y.; Jian, X.; Wang, X.; Humar, I. Cognitive-LPWAN: Towards intelligent wireless services in hybrid low power wide area networks. IEEE Trans. Green Commun. Netw. 2018, 3, 409–417. [Google Scholar] [CrossRef]
- Onumanyi, A.J.; Abu-Mahfouz, A.M.; Hancke, G.P. Cognitive Radio in Low Power Wide Area Network for IoT Applications: Recent Approaches, Benefits and Challenges. IEEE Trans. Ind. Inform. 2019. [Google Scholar] [CrossRef]
- Nikoletseas, S.; Raptis, T.P.; Souroulagkas, A.; Tsolovos, D. Wireless power transfer protocols in sensor networks: Experiments and simulations. J. Sens. Actuator Netw. 2017, 6, 4. [Google Scholar] [CrossRef]
- He, S.; Chen, J.; Jiang, F.; Yau, D.K.; Xing, G.; Sun, Y. Energy provisioning in wireless rechargeable sensor networks. IEEE Trans. Mob. Comput. 2012, 12, 1931–1942. [Google Scholar] [CrossRef]
- Shi, Y.; Xie, L.; Hou, Y.T.; Sherali, H.D. On renewable sensor networks with wireless energy transfer. In Proceedings of the 2011 Proceedings IEEE INFOCOM, Shanghai, China, 10–15 April 2011; pp. 1350–1358. [Google Scholar]
- Lai, W.-Y.; Hsiang, T.-R. Wireless Charging Deployment in Sensor Networks. Sensors 2019, 19, 201. [Google Scholar] [CrossRef] [PubMed]
- Perez, S.; Fuertes, J.A.C.; Coupechoux, M. ODMAC++: An IoT communication manager based on energy harvesting prediction. In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2017; pp. 1–7. [Google Scholar]
- Ashraf, N.; Faizan, M.; Asif, W.; Qureshi, H.K.; Iqbal, A.; Lestas, M. Energy management in harvesting enabled sensing nodes: Prediction and control. J. Netw. Comput. Appl. 2019, 132, 104–117. [Google Scholar] [CrossRef]
- Rodrigues, L.M.; Montez, C.; Budke, G.; Vasques, F.; Portugal, P. Estimating the lifetime of wireless sensor network nodes through the use of embedded analytical battery models. J. Sens. Actuator Netw. 2017, 6, 8. [Google Scholar] [CrossRef]
- Chen, M.; Wang, J.; Lin, K.; Wu, D.; Wan, J.; Peng, L.; Youn, C.-H. M-plan: Multipath planning based transmissions for IoT multimedia sensing. In Proceedings of the 2016 International Wireless Communications and Mobile Computing Conference (IWCMC), Paphos, Cyprus, 5–9 September 2016; pp. 339–344. [Google Scholar]
- Wei, Z.; Liu, F.; Lyu, Z.; Ding, X.; Shi, L.; Xia, C. Reinforcement learning for a novel mobile charging strategy in wireless rechargeable sensor networks. In International Conference on Wireless Algorithms, Systems, and Applications; Springer: Berlin, Germany, 2018; pp. 485–496. [Google Scholar]
- Shresthamali, S.; Kondo, M.; Nakamura, H. Adaptive power management in solar energy harvesting sensor node using reinforcement learning. Acm Trans. Embed. Comput. Syst. (Tecs) 2017, 16, 1–21. [Google Scholar] [CrossRef]
- Conti, S.; Faraci, G.; Nicolosi, R.; Rizzo, S.A.; Schembra, G. Battery management in a green fog-computing node: A reinforcement-learning approach. IEEE Access 2017, 5, 21126–21138. [Google Scholar] [CrossRef]
- Murad, A.; Kraemer, F.A.; Bach, K.; Taylor, G. Autonomous Management of Energy-Harvesting IoT Nodes Using Deep Reinforcement Learning. In Proceedings of the 2019 IEEE 13th International Conference on Self-Adaptive and Self-Organizing Systems (SASO), Umea, Sweden, 16–20 June 2019; pp. 43–51. [Google Scholar]
- Yang, Y.; Ma, Y.; Xiang, W.; Gu, X.; Zhao, H. Joint optimization of energy consumption and packet scheduling for mobile edge computing in cyber-physical networks. IEEE Access 2018, 6, 15576–15586. [Google Scholar] [CrossRef]
- Chien, W.-C.; Cho, H.-H.; Chen, C.-Y.; Chao, H.-C.; Shih, T.K. An efficient charger planning mechanism of WRSN using simulated annealing algorithm. In Proceedings of the 2015 IEEE International Conference on Systems, Man, and Cybernetics, Kowloon, China, 9–12 October 2015; pp. 2585–2590. [Google Scholar]
- Nabil, M.S.; Elkhatib, M.M.; Tammam, A. Fuzzy Power Management for Internet of Things (IOT) Wireless Sensor Nodes. In Proceedings of the 2019 36th National Radio Science Conference (NRSC), Port Said, Egypt, 16–18 April 2019; pp. 173–182. [Google Scholar]
- Hua, D.; Wang, L.; Xu, Y.; Li, H.; Gombay, N. Fuzzy system for monitoring energy consumption of wireless sensor network nodes. J. Intell. Fuzzy Syst. 2018, 35, 4319–4328. [Google Scholar] [CrossRef]
- Smart, G.; Atkinson, J.; Mitchell, J.; Rodrigues, M.; Andreopoulos, Y. Energy harvesting for the Internet-of-Things: Measurements and probability models. In Proceedings of the 2016 23rd International Conference on Telecommunications (ICT), Thessaloniki, Greece, 16–18 May 2016; pp. 1–6. [Google Scholar]
- Tunc, C.; Akar, N. Markov fluid queue model of an energy harvesting IoT device with adaptive sensing. Perform. Eval. 2017, 111, 1–16. [Google Scholar] [CrossRef]
- De Castro, M.F.; Ribeiro, L.B.; Oliveira, C.H.S. An autonomic bio-inspired algorithm for wireless sensor network self-organization and efficient routing. J. Netw. Comput. Appl. 2012, 35, 2003–2015. [Google Scholar] [CrossRef]
- Computing, A. An architectural blueprint for autonomic computing. Ibm White Pap. 2006, 31, 1–6. [Google Scholar]
- Ndiaye, M.; Hancke, G.P.; Abu-Mahfouz, A.M. Software defined networking for improved wireless sensor network management: A survey. Sensors 2017, 17, 1031. [Google Scholar] [CrossRef]
- Ding, Y.; Jin, Y.; Ren, L.; Hao, K. An Intelligent Self-Organization Scheme for the Internet of Things. IEEE Comput. Intell. Mag. 2013, 8, 41–53. [Google Scholar] [CrossRef]
- Bassoli, M.; Bianchi, V.; Munari, I.D. A plug and play IoT Wi-Fi smart home system for human monitoring. Electronics 2018, 7, 200. [Google Scholar] [CrossRef]
- Solano, A.; Dormido, R.; Duro, N.; Sánchez, J.M. A self-provisioning mechanism in OpenStack for IoT devices. Sensors 2016, 16, 1306. [Google Scholar] [CrossRef]
- Kim, D.-Y.; Kim, S.; Hassan, H.; Park, J.H. Adaptive data rate control in low power wide area networks for long range IoT services. J. Comput. Sci. 2017, 22, 171–178. [Google Scholar] [CrossRef]
- Hasan, M.Z.; Al-Rizzo, H. Optimization of Sensor Deployment for Industrial Internet of Things Using a Multiswarm Algorithm. IEEE Internet Things J. 2019, 6, 10344–10362. [Google Scholar] [CrossRef]
- Lanza-Gutiérrez, J.M.; Caballé, N.; Gómez-Pulido, J.A.; Crawford, B.; Soto, R. Toward a Robust Multi-Objective Metaheuristic for Solving the Relay Node Placement Problem in Wireless Sensor Networks. Sensors 2019, 19, 677. [Google Scholar] [CrossRef] [PubMed]
- Oyewobi, S.S.; Hancke, G.P.; Abu-Mahfouz, A.M.; Onumanyi, A.J. An Effective Spectrum Handoff Based on Reinforcement Learning for Target Channel Selection in the Industrial Internet of Things. Sensors (Basel) 2019, 19, 1395. [Google Scholar] [CrossRef] [PubMed]
- Kühn, F.; Hellbrück, H.; Fischer, S.A. Model-based Approach for Self-healing IoT Systems. 2018. Available online: https://dl.acm.org/doi/abs/10.1145/582128.582134 (accessed on 4 April 2020).
- Aktas, M.S.; Astekin, M. Provenance aware run-time verification of things for self-healing Internet of Things applications. Concurr. Comput. Pract. Exp. 2019, 31, e4263. [Google Scholar] [CrossRef]
- Zamanifar, A.; Nazemi, E.; Vahidi-Asl, M. DSHMP-IOT: A distributed self healing movement prediction scheme for internet of things applications. Appl. Intell. 2017, 46, 569–589. [Google Scholar] [CrossRef]
- De Almeida, F.M.; Ribeiro, A.D.R.L.; Moreno, E.D. An Architecture for Self-healing in Internet of Things. UBICOMM 2015, 2015, 89. [Google Scholar]
- Srinidhi, N.N.; Kumar, S.M.D.; Venugopal, K.R. Network optimizations in the Internet of Things: A review. Eng. Sci. Technol. Int. J. 2019, 22, 1–21. [Google Scholar] [CrossRef]
- Shamsan Saleh, A.M.; Ali, B.M.; Rasid, A.; Fadlee, M.; Ismail, A. A self-optimizing scheme for energy balanced routing in wireless sensor networks using sensorant. Sensors 2012, 12, 11307–11333. [Google Scholar] [CrossRef]
- Xiao, L.; Wan, X.; Lu, X.; Zhang, Y.; Wu, D. IoT security techniques based on machine learning: How do IoT devices use AI to enhance security? IEEE Signal Process. Mag. 2018, 35, 41–49. [Google Scholar] [CrossRef]
- Tsai, C.-W. SEIRA: An effective algorithm for IoT resource allocation problem. Comput. Commun. 2018, 119, 156–166. [Google Scholar] [CrossRef]
- Kishore Ramakrishnan, A.; Preuveneers, D.; Berbers, Y. Enabling self-learning in dynamic and open IoT environments. Procedia Comput. Sci. 2014, 32, 207–214. [Google Scholar] [CrossRef]
- Cao, N.; Nasir, S.B.; Sen, S.; Raychowdhury, A. Self-optimizing IoT wireless video sensor node with in-situ data analytics and context-driven energy-aware real-time adaptation. IEEE Trans. Circuits Syst. I Regul. Pap. 2017, 64, 2470–2480. [Google Scholar] [CrossRef]
- Kumar, T.P.; Krishna, P.V. Power modelling of sensors for IoT using reinforcement learning. Int. J. Adv. Intell. Paradig. 2018, 10, 3–22. [Google Scholar] [CrossRef]
- Iwendi, C.; Maddikunta, P.K.R.; Gadekallu, T.R.; Lakshmanna, K.; Bashir, A.K.; Piran, M.J. A metaheuristic optimization approach for energy efficiency in the IoT networks. Softw. Pract. Exp. 2020. [Google Scholar] [CrossRef]
- Amri, S.; Khelifi, F.; Bradai, A.; Rachedi, A.; Kaddachi, M.L.; Atri, M. A new fuzzy logic based node localization mechanism for Wireless Sensor Networks. Future Gener. Comput. Syst. 2017, 93, 799–813. [Google Scholar] [CrossRef]
- Cuka, M.; Elmazi, D.; Obukata, R.; Ozera, K.; Oda, T.; Barolli, L. An integrated intelligent system for IoT device selection and placement in opportunistic networks using fuzzy logic and genetic algorithm. In Proceedings of the 2017 31st International Conference on Advanced Information Networking and Applications Workshops (WAINA), Taipei, Taiwan, 27–29 March 2017; pp. 201–207. [Google Scholar]
- Nazari Cheraghlou, M.; Khadem-Zadeh, A.; Haghparast, M. A New Hybrid Fault Tolerance Approach for Internet of Things. Electronics 2019, 8, 518. [Google Scholar] [CrossRef]
- Julie, E.G.; Selvi, S.T. Development of Energy Efficient Clustering Protocol in Wireless Sensor Network Using Neuro-Fuzzy Approach. Scientific World J. 2016, 2016, 5063261. [Google Scholar] [CrossRef]
- Luo, J.; Wu, D.; Pan, C.; Zha, J. Optimal energy strategy for node selection and data relay in WSN-based IoT. Mob. Netw. Appl. 2015, 20, 169–180. [Google Scholar] [CrossRef]
- Siegel, J.; Sarma, S. A Cognitive Protection System for the Internet of Things. IEEE Secur. Priv. 2019, 17, 40–48. [Google Scholar] [CrossRef]
- Abdul-Ghani, H.A.; Konstantas, D. A comprehensive study of security and privacy guidelines, threats, and countermeasures: An IoT perspective. J. Sens. Actuator Netw. 2019, 8, 22. [Google Scholar] [CrossRef]
- Abu-Mahfouz, A.M.; Hancke, G.P. Evaluating ALWadHA for providing secure localisation for wireless sensor networks. In Proceedings of the 2013 Africon, Pointe-Aux-Piments, Mauritius, 9–12 September 2013. [Google Scholar]
- Ntuli, N.; Abu-Mahfouz, A. A Simple Security Architecture for Smart Water Management System. Procedia Comput. Sci. 2016, 83, 1164–1169. [Google Scholar] [CrossRef]
- O’connor, C. Security in the Era of Cognitive IT-the Risks and Mitigations to Be Aware of. Available online: https://www.ibm.com/blogs/internet-of-things/security-cognitive-iot/ (accessed on 5 April 2020).
- Andrade, R.O.; Yoo, S.G. Cognitive security: A comprehensive study of cognitive science in cybersecurity. J. Inf. Secur. Appl. 2019, 48, 102352. [Google Scholar] [CrossRef]
- Andrade, R.; Torres, J.; Cadena, S. Cognitive security for incident management process. In International Conference on Information Technology & Systems; Springer: Cham, Switzerland, 2019; pp. 612–621. [Google Scholar]
- Ioannou, C.; Vassiliou, V. Classifying Security Attacks in IoT Networks Using Supervised Learning. In Proceedings of the 2019 15th International Conference on Distributed Computing in Sensor Systems (DCOSS), Santorini Island, Greece, 29–31 May 2019; pp. 652–658. [Google Scholar]
- Yang, K.; Ren, J.; Zhu, Y.; Zhang, W. Active learning for wireless IoT intrusion detection. IEEE Wirel. Commun. 2018, 25, 19–25. [Google Scholar] [CrossRef]
- Hodo, E.; Bellekens, X.; Hamilton, A.; Dubouilh, P.-L.; Iorkyase, E.; Tachtatzis, C.; Atkinson, R. Threat analysis of IoT networks using artificial neural network intrusion detection system. In Proceedings of the 2016 International Symposium on Networks, Computers and Communications (ISNCC), Yasmine Hammamet, Tunisia, 11–13 May 2016; pp. 1–6. [Google Scholar]
- Khraisat, A.; Gondal, I.; Vamplew, P.; Kamruzzaman, J.; Alazab, A. A Novel Ensemble of Hybrid Intrusion Detection System for Detecting Internet of Things Attacks. Electronics 2019, 8, 1210. [Google Scholar] [CrossRef]
- Khorram, T.; Baykan, N.A. Feature selection in network intrusion detection using metaheuristic algorithms. Int. J. Adv. Res. Ideas Innov. Technol. 2018, 4, 704–710. [Google Scholar]
- Zhang, Y.; Li, P.; Wang, X. Intrusion detection for IoT based on improved genetic algorithm and deep belief network. IEEE Access 2019, 7, 31711–31722. [Google Scholar] [CrossRef]
- Mahalle, P.N.; Thakre, P.A.; Prasad, N.R.; Prasad, R. A fuzzy approach to trust based access control in internet of things. In Proceedings of the Wireless VITAE 2013, Atlantic City, NJ, USA, 24–27 June 2013; pp. 1–5. [Google Scholar]
- Dovom, E.M.; Azmoodeh, A.; Dehghantanha, A.; Newton, D.E.; Parizi, R.M.; Karimipour, H. Fuzzy pattern tree for edge malware detection and categorization in IoT. J. Syst. Archit. 2019, 97, 1–7. [Google Scholar] [CrossRef]
- Wang, J.; Kuang, Q.; Duan, S. A new online anomaly learning and detection for large-scale service of internet of thing. Pers. Ubiquitous Comput. 2015, 19, 1021–1031. [Google Scholar] [CrossRef]
- Mohsin, M.; Sardar, M.U.; Hasan, O.; Anwar, Z. IoTRiskAnalyzer: A probabilistic model checking based framework for formal risk analytics of the Internet of Things. IEEE Access 2017, 5, 5494–5505. [Google Scholar] [CrossRef]
- Cheng, S.; Cai, Z.; Li, J. Approximate sensory data collection: A survey. Sensors 2017, 17, 564. [Google Scholar] [CrossRef]
- Din, S.; Ahmad, A.; Paul, A.; Rathore, M.M.U.; Jeon, G. A Cluster-Based Data Fusion Technique to Analyze Big Data in Wireless Multi-Sensor System. IEEE Access 2017, 5, 5069–5083. [Google Scholar] [CrossRef]
- Khan, A.A.; Rehmani, M.H.; Rachedi, A. Cognitive-radio-based internet of things: Applications, architectures, spectrum related functionalities, and future research directions. IEEE Wirel. Commun. 2017, 24, 17–25. [Google Scholar] [CrossRef]
- Khedr, A.M. Effective data acquisition protocol for multi-hop heterogeneous wireless sensor networks using compressive sensing. Algorithms 2015, 8, 910–928. [Google Scholar] [CrossRef]
- Jaloudi, S. Communication protocols of an industrial internet of things environment: A comparative study. Future Internet 2019, 11, 66. [Google Scholar] [CrossRef]
- Dos Santos, Y.L.; Canedo, E.D. On the design and implementation of an IoT based architecture for reading ultra high frequency tags. Information 2019, 10, 41. [Google Scholar] [CrossRef]
- Kotsev, A.; Pantisano, F.; Schade, S.; Jirka, S. Architecture of a service-enabled sensing platform for the environment. Sensors 2015, 15, 4470–4495. [Google Scholar] [CrossRef]
- Abu-Mahfouz, A.M.; Hancke, G.P. Localised information fusion techniques for location discovery in wireless sensor networks. Int. J. Sens. Netw. 2018, 26, 12–25. [Google Scholar] [CrossRef]
- Abdelgawad, A.M. Resourse-Aware Data Fusion Algorithms for Wireless Sensor Networks. Ph.D. Thesis, University of Louisiana at Lafayette, Lafayette, LA, USA, 2011; p. 149. [Google Scholar]
- Dobslaw, F.; Gidlund, M.; Zhang, T. Challenges for the use of data aggregation in industrial Wireless Sensor Networks. In Proceedings of the 2015 IEEE International Conference on Automation Science and Engineering (CASE), Gothenburg, Sweden, 24–28 August 2015; pp. 138–144. [Google Scholar]
- Rejinaparvin, J.; Vasanthanayaki, C. Particle Swarm Optimization-Based Clustering by Preventing Residual Nodes in Wireless Sensor Networks. IEEE Sens. J. 2015, 15, 4264–4274. [Google Scholar] [CrossRef]
- Wan, R.; Xiong, N.; Hu, Q.; Wang, H.; Shang, J. Similarity-aware data aggregation using fuzzy c-means approach for wireless sensor networks. Eurasip J. Wirel. Commun. Netw. 2019, 2019, 59. [Google Scholar] [CrossRef]
- Menaria, V.K.; Jain, S.; Nagaraju, A. A fault tolerance based route optimisation and data aggregation using artificial intelligence to enhance performance in wireless sensor networks. Int. J. Wirel. Mob. Comput. 2018, 14, 123–137. [Google Scholar] [CrossRef]
- Cheng, S.; Li, J.; Cai, Z. O(ε)-Approximation to physical world by sensor networks. In Proceedings of the 2013 Proceedings IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 3084–3092. [Google Scholar]
- Djelouat, H.; Amira, A.; Bensaali, F. Compressive sensing-based IoT applications: A review. J. Sens. Actuator Netw. 2018, 7, 45. [Google Scholar] [CrossRef]
- Ejaz, W.; Naeem, M.; Shahid, A.; Anpalagan, A.; Jo, M. Efficient energy management for the internet of things in smart cities. IEEE Commun. Mag. 2017, 55, 84–91. [Google Scholar] [CrossRef]
- Ishaq, I.; Carels, D.; Teklemariam, G.K.; Hoebeke, J.; Abeele, F.V.D.; Poorter, E.D.; Demeester, P. IETF standardization in the field of the internet of things (IoT): A survey. J. Sens. Actuator Netw. 2013, 2, 235–287. [Google Scholar] [CrossRef]
- Xu, C.; Yang, H.H.; Wang, X.; Quek, T.Q. On peak age of information in data preprocessing enabled IoT networks. In Proceedings of the 2019 IEEE Wireless Communications and Networking Conference (WCNC), Marrakesh, Morocco, 15–18 April 2019; pp. 1–6. [Google Scholar]
- Rathore, M.M.; Ahmad, A.; Paul, A.; Rho, S. Urban planning and building smart cities based on the Internet of Things using Big Data analytics. Comput. Netw. 2016, 101, 63–80. [Google Scholar] [CrossRef]
- Azar, J.; Makhoul, A.; Barhamgi, M.; Couturier, R. An energy efficient IoT data compression approach for edge machine learning. Future Gener. Comput. Syst. 2019, 96, 168–175. [Google Scholar] [CrossRef]
- Karjee, J.; Rath, H.K.; Pal, A. Efficient Data Prediction, Reconstruction and Estimation in Indoor IoT Networks. In Proceedings of the 2018 IEEE 6th International Conference on Future Internet of Things and Cloud (FiCloud), Barcelona, Spain, 6–8 August 2018; pp. 236–243. [Google Scholar]
- Chang, H.; Feng, J.; Duan, C. Reinforcement learning-based data forwarding in underwater wireless sensor networks with passive mobility. Sensors 2019, 19, 256. [Google Scholar] [CrossRef] [PubMed]
- Izadi, D.; Abawajy, J.H.; Ghanavati, S.; Herawan, T. A Data Fusion Method in Wireless Sensor Networks. Sensors 2015, 15, 2964–2979. [Google Scholar] [CrossRef] [PubMed]
- Kumar, G.R.; Mangathayaru, N.; Narsimha, G. Design of novel fuzzy distribution function for dimensionality reduction and intrusion detection. In Proceedings of the 2016 International Conference on Engineering & MIS (ICEMIS), Agadir, Morocco, 22–24 September 2016; pp. 1–6. [Google Scholar]
- Thangaramya, K.; Kulothungan, K.; Logambigai, R.; Selvi, M.; Ganapathy, S.; Kannan, A. Energy aware cluster and neuro-fuzzy based routing algorithm for wireless sensor networks in IoT. Comput. Netw. 2019, 151, 211–223. [Google Scholar] [CrossRef]
- Kumar, S.; Chaurasiya, V.K. A strategy for elimination of data redundancy in internet of things (IoT) based wireless sensor network (wsn). IEEE Syst. J. 2018, 13, 1650–1657. [Google Scholar] [CrossRef]
- Akbar, A.; Kousiouris, G.; Pervaiz, H.; Sancho, J.; Ta-Shma, P.; Carrez, F.; Moessner, K. Real-time probabilistic data fusion for large-scale IoT applications. IEEE Access 2018, 6, 10015–10027. [Google Scholar] [CrossRef]
- Alsharif, M.H.; Kelechi, A.H.; Yahya, K.; Chaudhry, S.A. Machine Learning Algorithms for Smart Data Analysis in Internet of Things Environment: Taxonomies and Research Trends. Symmetry 2020, 12, 88. [Google Scholar] [CrossRef]
- Akmandor, A.O.; Hongxu, Y.I.N.; Jha, N.K. Smart, Secure, Yet Energy-Efficient, Internet-of-Things Sensors. IEEE Trans. Multi-Scale Comput. Syst. 2018, 4, 914–930. [Google Scholar] [CrossRef]
- Ferrando, R.; Stacey, P. Classification of device behaviour in internet of things infrastructures: Towards distinguishing the abnormal from security threats. In Proceedings of the 1st International Conference on Internet of Things and Machine Learning, Liverpool, UK, 17–18 October 2017; pp. 1–7. [Google Scholar]
- Kaliya, N.; Hussain, M. Framework for privacy preservation in iot through classification and access control mechanisms. In Proceedings of the 2017 2nd International Conference for Convergence in Technology (I2CT), Mumbai, India, 7–9 April 2017; pp. 430–434. [Google Scholar]
- Akbar, A.; Carrez, F.; Moessner, K.; Zoha, A. Predicting complex events for pro-active IoT applications. In Proceedings of the 2015 IEEE 2nd World Forum on Internet of Things (WF-IoT), Milan, Italy, 14–16 December 2015; pp. 327–332. [Google Scholar]
- Da Rosa Righi, R.; Correa, E.; Gomes, M.M.; da Costa, C.A. Enhancing performance of IoT applications with load prediction and cloud elasticity. Future Gener. Comput. Syst. 2018, in press. [Google Scholar] [CrossRef]
- Zhang, H.; Yi, Y.; Wang, J.; Cao, N.; Duan, Q. Network attack prediction method based on threat intelligence for IoT. Multimed. Tools Appl. 2019, 78, 30257–30270. [Google Scholar] [CrossRef]
- Khelifi, H.; Luo, S.; Nour, B.; Sellami, A.; Moungla, H.; Ahmed, S.H.; Guizani, M. Bringing Deep Learning at the Edge of Information-Centric Internet of Things. IEEE Commun. Lett. 2019, 23, 52–55. [Google Scholar] [CrossRef]
- Lawrence, T.; Zhang, L. IoTNet: An Efficient and Accurate Convolutional Neural Network for IoT Devices. Sensors 2019, 19, 5541. [Google Scholar] [CrossRef]
- Du, L.; Du, Y.; Li, Y.; Su, J.; Kuan, Y.-C.; Liu, C.-C.; Chang, M.-C.F. A reconfigurable streaming deep convolutional neural network accelerator for Internet of Things. IEEE Trans. Circuits Syst. I Regul. Pap. 2017, 65, 198–208. [Google Scholar] [CrossRef]
- Lopez-Martin, M.; Carro, B.; Sanchez-Esguevillas, A.; Lloret, J. Network traffic classifier with convolutional and recurrent neural networks for Internet of Things. IEEE Access 2017, 5, 18042–18050. [Google Scholar] [CrossRef]
- Shen, Y.; Han, T.; Yang, Q.; Yang, X.; Wang, Y.; Li, F.; Wen, H. CS-CNN: Enabling robust and efficient convolutional neural networks inference for Internet-of-Things applications. IEEE Access 2018, 6, 13439–13448. [Google Scholar] [CrossRef]
- Njima, W.; Ahriz, I.; Zayani, R.; Terre, M.; Bouallegue, R. Deep CNN for Indoor Localization in IoT-Sensor Systems. Sensors 2019, 19, 3127. [Google Scholar] [CrossRef]
- Disabato, S.; Roveri, M.; Alippi, C. Distributed Deep Convolutional Neural Networks for the Internet-of-Things. arXiv 2019, arXiv:1908.01656. [Google Scholar]
- Pius Owoh, N.; Singh, M.M.; Zaaba, Z.F. Automatic Annotation of Unlabeled Data from Smartphone-Based Motion and Location Sensors. Sensors 2018, 18, 2134. [Google Scholar] [CrossRef] [PubMed]
- Cruciani, F.; Cleland, I.; Nugent, C.; Mccullagh, P.; Synnes, K.; Hallberg, J. Automatic annotation for human activity recognition in free living using a smartphone. Sensors 2018, 18, 2203. [Google Scholar] [CrossRef] [PubMed]
- Zabalza, J.; Ren, J.; Zheng, J.; Zhao, H.; Qing, C.; Yang, Z.; Marshall, S. Novel segmented stacked autoencoder for effective dimensionality reduction and feature extraction in hyperspectral imaging. Neurocomputing 2016, 185, 1–10. [Google Scholar] [CrossRef]
- Su, S.; Sun, Y.; Gao, X.; Qiu, J.; Tian, Z. A correlation-change based feature selection method for IoT equipment anomaly detection. Applied Sciences 2019, 9, 437. [Google Scholar] [CrossRef]
- Nõmm, S.; Bahşi, H. Unsupervised anomaly based botnet detection in IoT networks. In Proceedings of the 2018 17th IEEE International Conference on Machine Learning and Applications (ICMLA), Orlando, FL, USA, 17–20 December 2018; pp. 1048–1053. [Google Scholar]
- Ejaz, W.; Anpalagan, A. Dimension Reduction for Big Data Analytics in Internet of Things. In Internet of Things for Smart Cities; Springer: Berlin, Germany, 2019; pp. 31–37. [Google Scholar]
- Fekade, B.; Maksymyuk, T.; Kyryk, M.; Jo, M. Probabilistic recovery of incomplete sensed data in IoT. IEEE Internet Things J. 2017, 5, 2282–2292. [Google Scholar] [CrossRef]
- Zhang, R.; Pan, J.; Xie, D.; Wang, F. NDCMC: A Hybrid Data Collection Approach for Large-Scale WSNs Using Mobile Element and Hierarchical Clustering. IEEE Internet Things J. 2016, 3, 533–543. [Google Scholar] [CrossRef]
- Yu, T.; Wang, X.; Shami, A. Recursive principal component analysis-based data outlier detection and sensor data aggregation in IoT systems. IEEE Internet Things J. 2017, 4, 2207–2216. [Google Scholar] [CrossRef]
- Mnih, V.; Kavukcuoglu, K.; Silver, D.; Rusu, A.A.; Veness, J.; Bellemare, M.G.; Ostrovski, G. Human-level control through deep reinforcement learning. Nature 2015, 518, 529–533. [Google Scholar] [CrossRef]
- Fachantidis, A.; Taylor, M.E.; Vlahavas, I. Learning to teach reinforcement learning agents. Mach. Learn. Knowl. Extr. 2019, 1, 21–42. [Google Scholar] [CrossRef]
- Willig, A.; Matusovsky, Y.; Kind, A. Relayer-Enabled Retransmission Scheduling in 802.15. 4e LLDN—Exploring a Reinforcement Learning Approach. J. Sens. Actuator Netw. 2017, 6, 6. [Google Scholar] [CrossRef]
- Derhab, A.; Guerroumi, M.; Gumaei, A.; Maglaras, L.; Ferrag, M.A.; Mukherjee, M.; Khan, F.A. Blockchain and random subspace learning-based IDS for SDN-enabled industrial IoT security. Sensors 2019, 19, 3119. [Google Scholar] [CrossRef] [PubMed]
- Chincoli, M.; Liotta, A. Self-learning power control in wireless sensor networks. Sensors 2018, 18, 375. [Google Scholar] [CrossRef] [PubMed]
- Escolar, S.; Caruso, A.; Chessa, S.; del Toro, X.; Villanueva, F.J.; López, J.C. Statistical energy neutrality in IoT hybrid energy-harvesting networks. In Proceedings of the 2018 IEEE Symposium on Computers and Communications (ISCC), Natal, Brazil, 25–28 June 2018; pp. 444–449. [Google Scholar]
- Caruso, A.; Chessa, S.; Escolar, S.; del Toro, X.; López, J.C. A dynamic programming algorithm for high-level task scheduling in energy harvesting IoT. IEEE Internet Things J. 2018, 5, 2234–2248. [Google Scholar] [CrossRef]
- Fraternali, F.; Balaji, B.; Gupta, R. Scaling configuration of energy harvesting sensors with reinforcement learning. In Proceedings of the 6th International Workshop on Energy Harvesting & Energy-Neutral Sensing Systems, Shenzhen, China, 4–7 November 2018; pp. 7–13. [Google Scholar]
- Dulac-Arnold, G.; Mankowitz, D.; Hester, T. Challenges of Real-World Reinforcement Learning. arXiv 2019, arXiv:1904.12901. [Google Scholar]
- Chu, M.; Li, H.; Liao, X.; Cui, S. Reinforcement learning-based multiaccess control and battery prediction with energy harvesting in IoT systems. IEEE Internet Things J. 2018, 6, 2009–2020. [Google Scholar] [CrossRef]
- Nassar, A.; Yilmaz, Y. Reinforcement Learning for Adaptive Resource Allocation in Fog RAN for IoT With Heterogeneous Latency Requirements. IEEE Access 2019, 7, 128014–128025. [Google Scholar] [CrossRef]
- Guo, C.; Zhuang, R.; Su, C.; Liu, C.Z.; Choo, K.-K.R. Secure and Efficient K Nearest Neighbor Query Over Encrypted Uncertain Data in Cloud-IoT Ecosystem. IEEE Internet Things J. 2019, 6, 9868–9879. [Google Scholar] [CrossRef]
- Quek, Y.T.; Woo, W.L.; Thillainathan, L. IoT Load Classification and Anomaly Warning in ELV DC Picogrids Using Hierarchical Extended k—Nearest Neighbors. IEEE Internet Things J. 2020, 7, 863–873. [Google Scholar] [CrossRef]
- Chen, Y.; Lu, L.; Yu, X.; Li, X. Adaptive Method for Packet Loss Types in IoT: An Naive Bayes Distinguisher. Electronics 2019, 8, 134. [Google Scholar] [CrossRef]
- Khan, M.A.; Khan, A.; Khan, M.N.; Anwar, S. A novel learning method to classify data streams in the internet of things. In Proceedings of the 2014 National Software Engineering Conference, Rawalpindi, Pakistan, 11–12 November 2014; pp. 61–66. [Google Scholar]
- Coello Coello, C.A.; Brambila, S.G.; Gamboa, J.F.; Tapia, M.G.C.; Gómez, R.H. Evolutionary multiobjective optimization: Open research areas and some challenges lying ahead. Complex Intell. Syst. 2019. [Google Scholar] [CrossRef]
- Khosravanian, R.; Mansouri, V.; Wood, D.A.; Alipour, M.R. A comparative study of several metaheuristic algorithms for optimizing complex 3-D well-path designs. J. Pet. Explor. Prod. Technol. 2018, 8, 1487–1503. [Google Scholar] [CrossRef]
- Liu, X.; Qin, Z.; Gao, Y. Resource allocation for edge computing in iot networks via reinforcement learning. In Proceedings of the ICC 2019-2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar]
- Talbi, E.-G. Single-solution based metaheuristics. Metaheuristics Des. Implement. 2009, 74, 87–189. [Google Scholar] [CrossRef]
- Leivadeas, A.; Kesidis, G.; Ibnkahla, M.; Lambadaris, I. VNF placement optimization at the edge and cloud. Future Internet 2019, 11, 69. [Google Scholar] [CrossRef]
- Téllez, N.; Jimeno, M.; Salazar, A.; Nino-Ruiz, E. A tabu search method for load balancing in fog computing. Int. J. Artif. Intell 2018, 16, 78–105. [Google Scholar]
- Moschakis, I.A.; Karatza, H.D. Towards scheduling for Internet-of-Things applications on clouds: A simulated annealing approach. Concurr. Comput. Pract. Exp. 2015, 27, 1886–1899. [Google Scholar] [CrossRef]
- Sreenivasamurthy, S.; Obraczka, K. Clustering for load balancing and energy efficiency in IoT applications. In Proceedings of the 2018 IEEE 26th International Symposium on Modeling, Analysis, and Simulation of Computer and Telecommunication Systems (MASCOTS), Milwaukee, WI, USA, 25–28 September 2018; pp. 319–332. [Google Scholar]
- Rani, S.; Ahmed, S.H.; Rastogi, R. Dynamic clustering approach based on wireless sensor networks genetic algorithm for IoT applications. Wirel. Netw. 2020, 26, 2307–2316. [Google Scholar] [CrossRef]
- Hussain, A.; Manikanthan, S.; Padmapriya, T.; Nagalingam, M. Genetic algorithm based adaptive offloading for improving IoT device communication efficiency. Wirel. Netw. 2020, 26, 2329–2338. [Google Scholar] [CrossRef]
- Habib, M.; Aljarah, I.; Faris, H.; Mirjalili, S. Multi-objective Particle Swarm Optimization for Botnet Detection in Internet of Things. In Evolutionary Machine Learning Techniques; Springer: Berlin, Germany, 2020; pp. 203–229. [Google Scholar]
- Yin, X.; Li, S.; Lin, Y. A Novel Hierarchical Data Aggregation with Particle Swarm Optimization for Internet of Things. Mob. Netw. Appl. 2019, 24, 1994–2001. [Google Scholar] [CrossRef]
- Scott, S. How Swarm Intelligence Is Making Simple Tech Much Smarter. 2018. Available online: https://singularityhub.com/2018/02/08/how-swarm-intelligence-is-making-simple-tech-much-smarter/#sm.0000exyrw0h6feo6ygy1c415091lk (accessed on 5 April 2020).
- Long, T.; Ozger, M.; Cetinkaya, O.; Akan, O.B. Energy Neutral Internet of Drones. IEEE Commun. Mag. 2018, 56, 22–28. [Google Scholar] [CrossRef]
- Suryani, V.; Sulistyo, S.; Widyawan, W. Trust-Based Privacy for Internet of Things. Int. J. Electr. Comput. Eng. (Ijece) 2016, 6, 2396–2402. [Google Scholar] [CrossRef]
- Najjar-Ghabel, S.; Yousefi, S.; Farzinvash, L. Reliable data gathering in the Internet of Things using artificial bee colony. Turk. J. Electr. Eng. Comput. Sci. 2018, 26, 1710–1723. [Google Scholar] [CrossRef]
- Chen, Z.-H.; Tsai, C.-W. An Effective Metaheuristic Algorithm for Intrusion Detection System. In Proceedings of the 2018 IEEE International Conference on Smart Internet of Things (SmartIoT), Xi’an, China, 17–19 August 2018; pp. 154–159. [Google Scholar]
- Dos Santos, W.G.; Costa, W.S.; Faber, M.J.; Silva, J.A.; Rocha, H.R.; Segatto, M.E. Sensor Allocation in a Hybrid Star-Mesh IoT Network using Genetic Algorithm and K-Medoids. In Proceedings of the 2019 IEEE Latin-American Conference on Communications (LATINCOM), Salvador, Brazil, 11–13 November 2019; pp. 1–6. [Google Scholar]
- Cuka, M.; Elmazi, D.; Ikeda, M.; Matsuo, K.; Barolli, L. IoT Node Selection and Placement: A New Approach Based on Fuzzy Logic and Genetic Algorithm. In Conference on Complex, Intelligent, and Software Intensive Systems; Springer: Cham, Switzerland, 2019; pp. 22–35. [Google Scholar]
- Choochotkaew, S.; Yamaguchi, H.; Higashino, T.; Shibuya, M.; Hasegawa, T. EdgeCEP: Fully-distributed complex event processing on IoT edges. In Proceedings of the 2017 13th International Conference on Distributed Computing in Sensor Systems (DCOSS), Ottawa, ON, Canada, 5–7 June 2017; pp. 121–129. [Google Scholar]
- Da Silva Fré, G.L.; Silva, J.d.; Reis, F.A.; Mendes, L.D.P. Particle swarm optimization implementation for minimal transmission power providing a fully-connected cluster for the Internet of Things. In Proceedings of the 2015 International Workshop on Telecommunications (IWT), Santa Rita do Sapucai, Brazil, 14–17 June 2015; pp. 1–7. [Google Scholar]
- Zhao, H.-Y.; Wang, J.-C.; Guan, X.; Wang, Z.; He, Y.-H.; Xie, H.-L. Ant Colony Based Energy Consumption Optimization for Mobile IoT Networks. In Proceedings of the 2019 International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Atlanta, GA, USA, 14–17 July 2019; pp. 118–122. [Google Scholar]
- Muhammad, Z.; Saxena, N.; Qureshi, I.M.; Ahn, C.W. Hybrid arificial bee colony algorithm for an energy efficient internet of things based on wireless sensor network. IETE Tech. Rev. 2017, 34 (Suppl. 1), 39–51. [Google Scholar] [CrossRef]
- Zhang, X.; Zhang, X.; Han, L. An energy efficient Internet of Things network using restart artificial bee colony and wireless power transfer. IEEE Access 2019, 7, 12686–12695. [Google Scholar] [CrossRef]
- Ding, C.; Peng, W.; Wang, W. Hybrid Metaheuristics and their Implementations. Int. J. Online Eng. 2015, 11, 25–28. [Google Scholar] [CrossRef]
- Pau, G.; Collotta, M.; Maniscalco, V. Bluetooth 5 energy management through a fuzzy-pso solution for mobile devices of internet of things. Energies 2017, 10, 992. [Google Scholar]
- Rahman, S.; Al Mamun, S.; Ahmed, M.U.; Kaiser, M.S. PHY/MAC layer attack detection system using neuro-fuzzy algorithm for IoT network. In Proceedings of the 2016 International Conference on Electrical, Electronics, and Optimization Techniques (ICEEOT), Chennai, India, 3–5 March 2016; pp. 2531–2536. [Google Scholar]
- Liu, L.; Xu, B.; Zhang, X.; Wu, X. An intrusion detection method for internet of things based on suppressed fuzzy clustering. Eurasip J. Wirel. Commun. Netw. 2018, 2018, 113. [Google Scholar] [CrossRef]
- Shukla, R.M.; Munir, A. A computation offloading scheme leveraging parameter tuning for real-time IoT devices. In Proceedings of the 2016 IEEE International Symposium on Nanoelectronic and Information Systems (iNIS), Gwalior, India, 19–21 December 2016; pp. 208–209. [Google Scholar]
- Lapowsky, I. How Cambridge Analytica Sparked the Great Privacy Awakening. 2020. Available online: https://www.wired.com/story/cambridge-analytica-facebook-privacy-awakening/ (accessed on 5 April 2020).
- Gdpr. General Data Protection Regulation (GDPR)–Official Legal Text. 2020. Available online: https://gdpr-info.eu/ (accessed on 5 April 2020).
- Epsrc. Databox Project. 2019. Available online: https://www.databoxproject.uk/ (accessed on 4 April 2020).
- Ibm. Data Privacy Protection Solutions. Available online: https://www.ibm.com/security/privacy (accessed on 5 April 2020).

| References | Review |
|---|---|
| He, Bae [8] | AI techniques as applied to the cognitive radio |
| Mahdavinejad, Rezvan [9] | Machine learning (ML) methods for IoT data analytics |
| Zaheer, Othman [10] | Decision-theoretic models in Cognitive IoT |
| Al-Garadi, Mohamed [11] | ML and Deep Learning (DL) methods solutions for IoT security |
| Mohammadi, Al-Fuqaha [12] | DL in data analytics and learning in the IoT domain |
| AI Technique | Usage for Smart Energy Management |
|---|---|
| Supervised and Unsupervised Learning | (i) Predicting the availability of energy sources [17] (ii) EH-based communication management [33,34] (iii) Real-time insights into energy usage pattern [35] |
| Reinforcement Learning | (i) Energy consumption planning [36] (ii) learning an optimal charging path for mobile chargers [37] (iii) Adaptive Power Management [38] (iv) IoT battery management techniques [39] (v) Autonomous Management of Energy-Harvesting IoT Nodes [40] |
| Metaheuristics | (i) Energy consumption scheduling [41] (ii) Optimizing operations of Mobile chargers [42] |
| Fuzzy Model | (i) Power management using a fuzzy controller [43] (ii) Energy consumption monitoring and control [44] |
| Probabilistic Model | (i) Data based probability models of energy production in EH-IoT nodes [45] (ii) Sleep scheduling [20] (iii) Event Prediction [21] (iv) Maximizing the average sensing rate [46] |
| AI Technique | Usage for Self-Management |
|---|---|
| Supervised Learning | (i) Self-Learning nodes [65] (ii) self-optimization [66] |
| Reinforcement Learning | (i) Modeling of IoT sensors [67] |
| Metaheuristics | (i) Optimizing the deployment and coverage of nodes [54,55,62] (ii) developing self-organization schemes [50] (v) Adaptive data transmission (vi) resource management [64] (vii) cluster head selection [68] |
| Fuzzy Model | (i) Node localization technique [69] (ii) device selection/placement [70] (iii) modeling and evaluating fault-tolerant architectures [71] (iv) Development of an Efficient Clustering Protocol [72] |
| Probabilistic Model | (i) Evaluating optimum node selection strategy [73] |
| AI Technique | Usage for IoT Cognitive Security |
|---|---|
| Supervised and Unsupervised Learning | (i) Classifying Security Attacks [81] (ii) Active learning for intrusion detection [82] (iii) Security analytics [83] (iv) learning-based malware detection system [63] (v) learning-based authentication system [63] (vi) Hybrid Intrusion Detection System [84] |
| Metaheuristics | (i) Feature selection approach for intrusion detection [85] (ii) Attack recovery (iii) Intrusion detection [86] |
| Fuzzy Model | (i) Privacy and identity management [87] (ii) Malware and attack detection [88] |
| Probabilistic Model | (i) Anomaly learning and detection [89] (ii) Security analytics [90] |
| AI Technique | Potential Usage for Smart Data Collection |
|---|---|
| Supervised and Unsupervised Learning | (i) Data compression [110] (ii) Data Encoding (iii) Data Prediction and Reconstruction [111] (iv) Improving Data transmission [53] |
| Reinforcement Learning | (i) Learning an optimal data forwarding policy [112] |
| Metaheuristics | (i) Optimizing data transmission paths (ii) Data Fusion |
| Fuzzy Model | (i) Data fusion and Aggregation [113] (ii) Dimensionality Reduction [114] (iii) Data routing algorithm [115] |
| Probabilistic Model | (i) Redundancy Elimination [116] (ii) Data Fusion [117] |
| ML Type | CS Tasks | Algorithm | Usage and Ref | Strength | Weakness |
|---|---|---|---|---|---|
| Supervised learning | • Classification | KNN | • Secure and Efficient Query Over Encrypted Uncertain Data [152] • IoT Load Classification and Anomaly Warning [153] | • No training time is required which makes it fast, simple and easy to implement | • Performs poorly for large datasets because it stores and scans the entire dataset for each operation |
| Naive Bayes | • Congestion control [154] | • High accuracy of the method | • Tends towards complexity on a large dataset | ||
| Ensemble (DT & SVM) | • Intrusion detection system [84] | • Cascaded SL algorithms • High Detection Accuracy | • Used algorithms are unstable and sensitive to data outliers | ||
| Logistic Regression | • predicts congestion status by learning and determines whether a node drops data rate or not [53] | • The ability to learn from network parameters | • Extensive computing resources are required for learning | ||
| • Prediction | Linear Regression | • Solar energy prediction [17] | • Uses preprocessed data from multiple sources | • Unreliable predictions • No energy data is collected once the battery is full | |
| SVM | • Data Streams Classification [155] | • Used a real dataset and achieved 80% accuracy | • Computationally intensive because the method iterates twice over the data. | ||
| Unsupervised learning | • Clustering | K-Means | • Probabilistic Recovery of Incomplete Sensed Data in IoT [138] | • Higher accuracy than the SVM and the DNN approach | • Reduced accuracy when used with large datasets. |
| Hierarchical | • Hybrid Data Collection Approach Using Mobile Element and Hierarchical Clustering [139] | • More uniformed power consumption among nodes. | • The difficulty in scheduling the traveling paths of the data collectors | ||
| • Dimensionality Reduction | PCA | • Outlier Detection and Sensor Data Aggregation [140] | • High data recovery accuracy | • Energy consumption at the cluster head | |
| Reinforcement Learning | Optimization | Monte Carlo | • Adaptive Resource Allocation (RA) in Fog RAN [151] | • Ability to adapt to the IoT environment | • The technique may not be suitable for RA with multi fog nodes |
| Dyna Q | • Spectrum handoff for Target Channel Selection [56] | • Reduced latency | • The algorithm is computationally complex | ||
| Q Learning | • Resource Allocation for Edge Computing [156] | • Good trade-off performance between energy consumption and task execution delay | • Uses only numerical simulation to demonstrate the viability of the technique |
| Category | Algorithm | Usage for IoT Cognitive Sensing Activities | Strengths | Weaknesses |
|---|---|---|---|---|
| Single Solution Search | Tabu Search | • VNF placement optimization at the IoT edge and cloud [160] • Optimal load balancing between fog and cloud nodes [161] • Complex event processing [175] | • The possibility of a direct search through the solution space without gradient information • Flexible memory for a thorough search | • Not practical in problem with a large solution space • Not easy to use for multi-objective tasks • Increased computational cost • Mono objectivity |
| Simulated Annealing | • Scheduling for IoT applications on clouds [162] | • Uses a probability function to select a solution which prevents working through the entire space | ||
| Evolutionary Algorithms | GA | • Elect the most preferred nodes in the cluster [164] • Adaptive offloading for IoT traffic [165] | • Fast convergence • Efficient at complex uncertain and nonlinear problems • Suitable for multi-objective tasks | • Easy to fall into local optimum in high-dimensional space • A low convergence rate |
| PSO | • Botnet detection [166] • Transmission power allocation [176] • Hierarchical data aggregation for IoT nodes [167] | |||
| Swarm Intelligence Algorithms | ACO | • Energy consumption optimization [177] | • Supports parallel search techniques • Guaranteed convergence | • Complex and slow • Guaranteed but uncertain convergence time |
| ABC | • Task scheduling for energy-efficiency [178] • Optimal data transfer in a wireless power transfer network [179] • Reliable data gathering on the Internet of Things [171] | |||
| Hybrid Methods | GA+DBN | • Intrusion detection [86] | • Combines the strength and diversity of multiple heuristics to provide for a faster and more efficient operations | • Identifying the right heuristics for the hybridization process is not a straightforward process. • The setting of the newly introduced hybrid parameters is a complex process [180] |
| GA+K-Medoids | • Sensor Allocation in a Hybrid Star-Mesh IoT Network [173] | |||
| GA + Fuzzy Logic | • IoT node selection and placement [70,174] | |||
| PSO + Fuzzy Logic | • selection of an optimal Bluetooth communication mode that allows the best energy efficiency [181] |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Osifeko, M.O.; Hancke, G.P.; Abu-Mahfouz, A.M. Artificial Intelligence Techniques for Cognitive Sensing in Future IoT: State-of-the-Art, Potentials, and Challenges. J. Sens. Actuator Netw. 2020, 9, 21. https://doi.org/10.3390/jsan9020021
Osifeko MO, Hancke GP, Abu-Mahfouz AM. Artificial Intelligence Techniques for Cognitive Sensing in Future IoT: State-of-the-Art, Potentials, and Challenges. Journal of Sensor and Actuator Networks. 2020; 9(2):21. https://doi.org/10.3390/jsan9020021
Chicago/Turabian StyleOsifeko, Martins O., Gerhard P. Hancke, and Adnan M. Abu-Mahfouz. 2020. "Artificial Intelligence Techniques for Cognitive Sensing in Future IoT: State-of-the-Art, Potentials, and Challenges" Journal of Sensor and Actuator Networks 9, no. 2: 21. https://doi.org/10.3390/jsan9020021
APA StyleOsifeko, M. O., Hancke, G. P., & Abu-Mahfouz, A. M. (2020). Artificial Intelligence Techniques for Cognitive Sensing in Future IoT: State-of-the-Art, Potentials, and Challenges. Journal of Sensor and Actuator Networks, 9(2), 21. https://doi.org/10.3390/jsan9020021







