1. Introduction
Vector data are widely used in the geographic information industry. Because of the small amount of data stored in vectors, as well as their fast updates and ease of copying and distribution, such data is vulnerable to illegal infringement and embezzlement. Effective copyright protection has always been the main focus in the field of data security. Digital watermark technology provides good technical support for protecting the copyrights of vector data [
1]. The existing digital watermark algorithms for vector data are mainly divided into spatial domain [
2,
3,
4] and frequency domain [
5,
6] algorithms. These two types of methods embed watermark information by modifying coordinate values directly or indirectly. This kind of embedding model will inevitably cause a loss of accuracy with respect to vector map data. Especially for vector data with high data accuracy requirements, the destruction of accuracy will directly reduce the data quality [
7]. Under this circumstance, lossless watermark technology can provide copyright protection without losing the original data’s accuracy, so it has more advantages than the traditional watermark. Therefore, lossless copyright protection technology for vector data has become a research focus in data security.
Currently, there are three leading technologies for the lossless copyright protection of vector data. The first is the reversible watermark, which completely restores the original carrier data after extracting the watermark [
8,
9,
10]. The data lose protection after being restored, although a reversible watermark avoids the loss of data accuracy. Therefore, the reversible watermark cannot provide permanent copyright protection for data, one of the existing issues faced by a reversible watermark.
The second lossless watermark technology embeds the watermark by modifying the attribute domain. This kind of method embeds the watermark information into vector data attributes and adjusts the storage order to achieve copyright protection [
11,
12,
13]. For example, Sun et al. [
11] hid watermark information in data attributes according to the TAB file structure, a file format for vector maps. The watermark is effectively concealed after embedding, since each vector object reserves redundant space when defining attributes. However, because their approach chooses a redundant space for the attribute data, which is most likely to be lost when processing the data to embed the watermark, the proposed method has poor practicality. Zhou et al. [
12] proposed a lossless watermark algorithm based on stored features that determines the watermark position according to the chosen line’s length and angle. The storage order of the arc points in the line element is then changed according to the value of the watermark (zero or one). This algorithm realizes the copyright protection of vector map line elements by adjusting the arc points’ storage order. However, the algorithm is only applicable to vector line elements, not to vector points or area elements. Based on the work of Zhou, Ren et al. [
13] gave the rules for constructing arc segments with vector points and area elements, and this improved the previously developed algorithm by allowing it to realize the copyright protection of all vector data elements; the new approach reflected strong robustness and imperceptibility. However, Ren and Zhou’s methods destroy the storage order when embedding a watermark, and this is not suitable for the situation where features or vertices reorder. Therefore, the functional objects of their algorithms are relatively limited. In other words, this kind of lossless watermark algorithm provides copyright protection without any loss of precision by embedding it into the attribute domain. Nevertheless, the embedded watermark is likely to be destroyed by pirates, and the lossless data obtained after destroying the watermark still have usefulness.
The third lossless watermark technique is zero watermarking. Zero watermarking algorithms are structural watermark algorithms whose key is to extract stable feature information from given data to construct watermarks [
14]. The current research on zero watermarking for vector data can be divided into two types: spatial domain and frequency domain research. The spatial domain includes constructing the average coordinates of, for example, feature points [
7], distance sequences [
15], and angle sequences [
16] through specific methods. This kind of algorithm has certain robustness to geometric attacks, cropping, compression, and other watermark attacks. The frequency domain includes constructing zero watermarks through frequency domain transformation methods such as the discrete Fourier transform (DFT) [
17] and wavelet transform [
18]. These kinds of methods have stronger robustness and higher computational complexity than spatial domain algorithms. Zero watermarking algorithms register their constructed watermarks with the intellectual property rights (IPR) to resist interpretation attacks [
19,
20,
21] instead of embedding the watermark information into the data. The interpretation attack is a scheme for attacking watermarks proposed by International Business Machines Corporation (IBM). The attack scheme neither erases nor invalidates the target watermark. It generates copyright confusion by forging the original image or watermarking the image [
22]. Unfortunately, the actual application of zero watermarking is often restricted by a series of factors, such as the required registration period, cost, and the credibility of the IPR.
In other words, the reversible watermark can restore data after extraction, but the restored data lose copyright protection at the same time. In addition, although modifying the attribute domain to embed a watermark can protect the data and ensure accuracy, the accuracy of the data is destroyed, which may lead to data theft. Zero watermarking can provide permanent copyright protection for data without damage. Moreover, the constructed watermark information is closely related to the coordinate accuracy, which makes up for the deficiencies of the two methods above. However, zero watermarking technology has tremendous practical application limitations due to its heavy reliance on centralized third-party copyright agencies. If the demand for third-party copyright agency certifications is solved, zero watermarking can become an ideal solution in the domain of lossless copyright protection technology.
Therefore, based on the above research, this paper thoroughly analyzes vector data’s spatial relationships and proposes a robust zero watermarking algorithm based on angular features. Besides that, we introduce blockchain technology to solve the issue such that zero watermarking fundamentally relies on the IPR. This will be a new exploration that will provide a new opportunity to further study and develop zero watermarking for vector data.
2. Basic Idea and Preliminaries
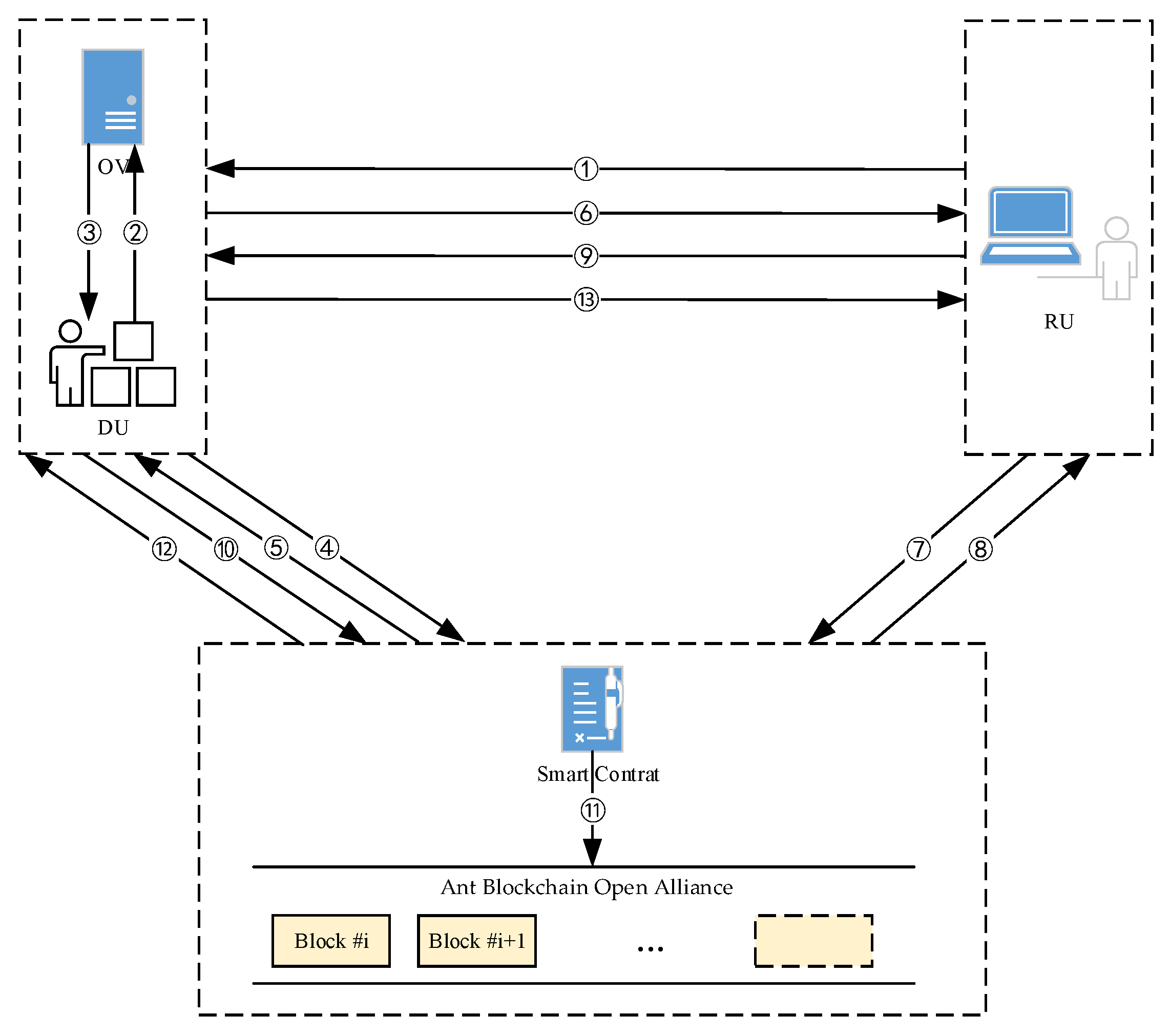
This paper introduces blockchain technology into the process of copyright protection for zero watermarking for the first time. It proposes a zero watermarking storage framework for vector data based on blockchain. Under this framework, the distribution of the given data is synchronized and chained with zero watermarking. When distributing the data to the user, the data’s zero watermark information is linked to the blockchain with both sides’ information to generate and save the certificate of copyright. This framework introduces blockchain into zero watermarking, providing an effective, safe, and traceable copyright protection scheme.
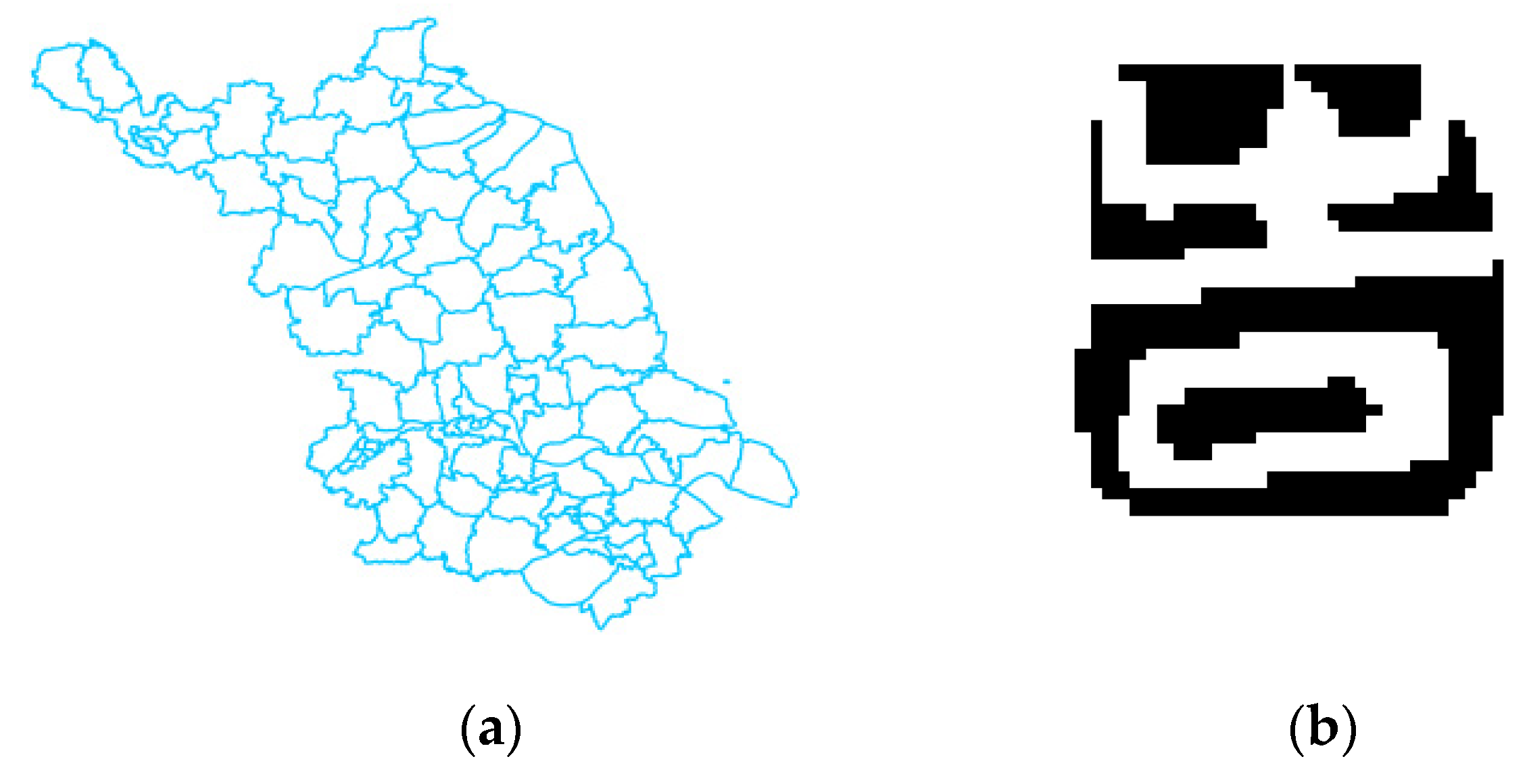
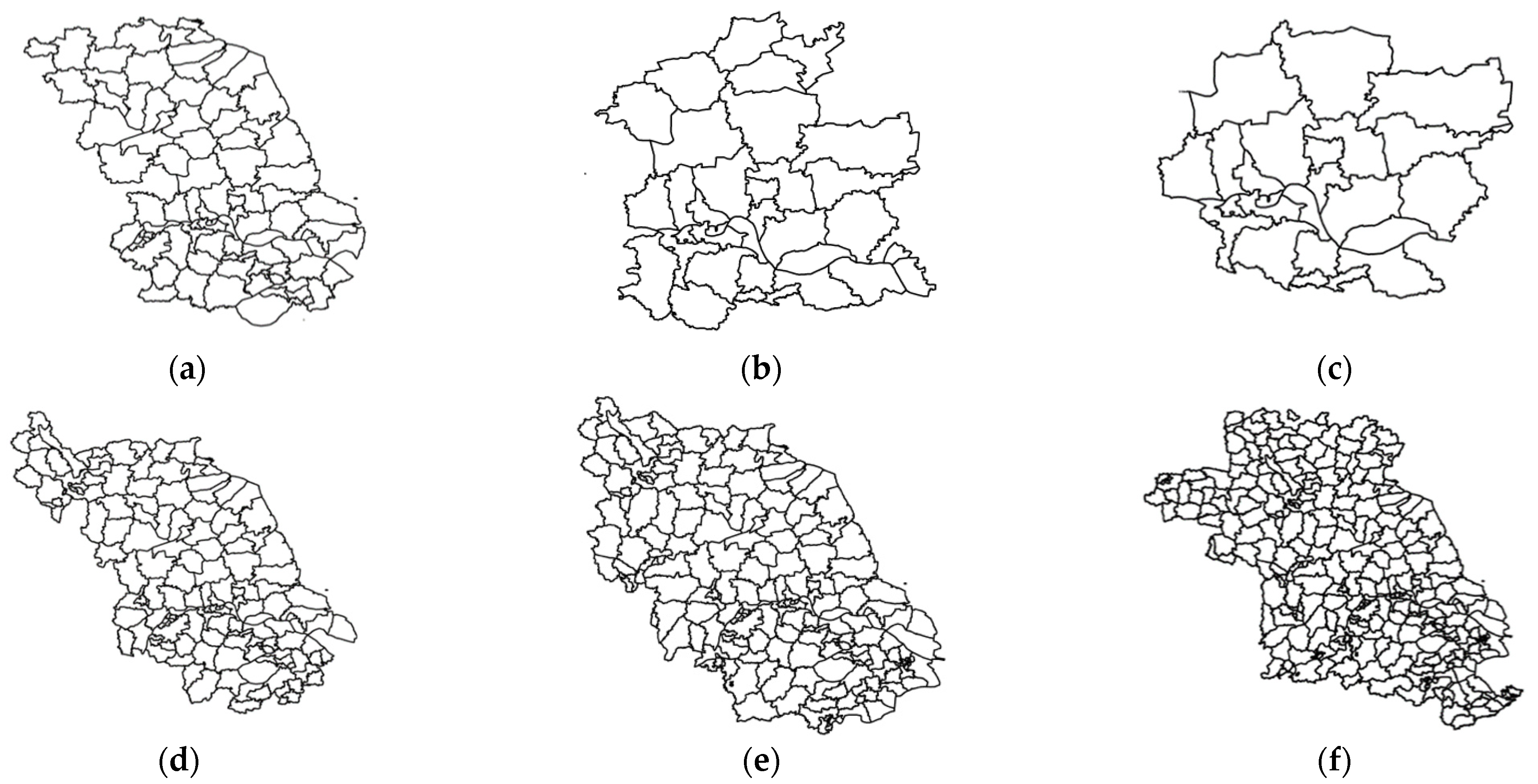
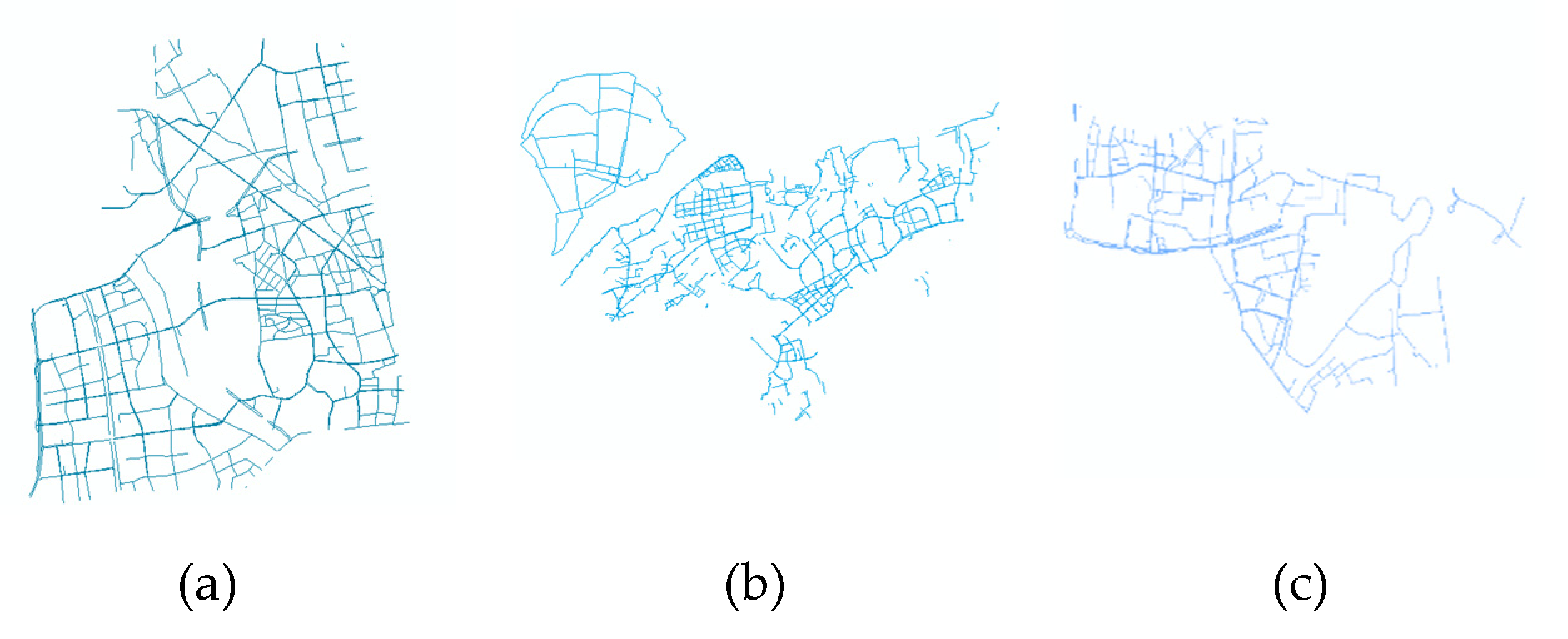
Moreover, the basic idea of a zero watermarking algorithm based on the angular feature proposed in this paper is as follows: First, the vector map line and surface are compressed to extract the feature points. Then, the angle sequence of the feature points is extracted by constructing concentric circles. Finally, an XOR operation is performed between the copyright image and angle sequence to obtain multiple zero watermarks. Experiments show that the proposed algorithm completely resists translation, rotation, and scaling attacks and has good robustness to compression, cropping, and adding attacks.
2.1. Zero Watermarking
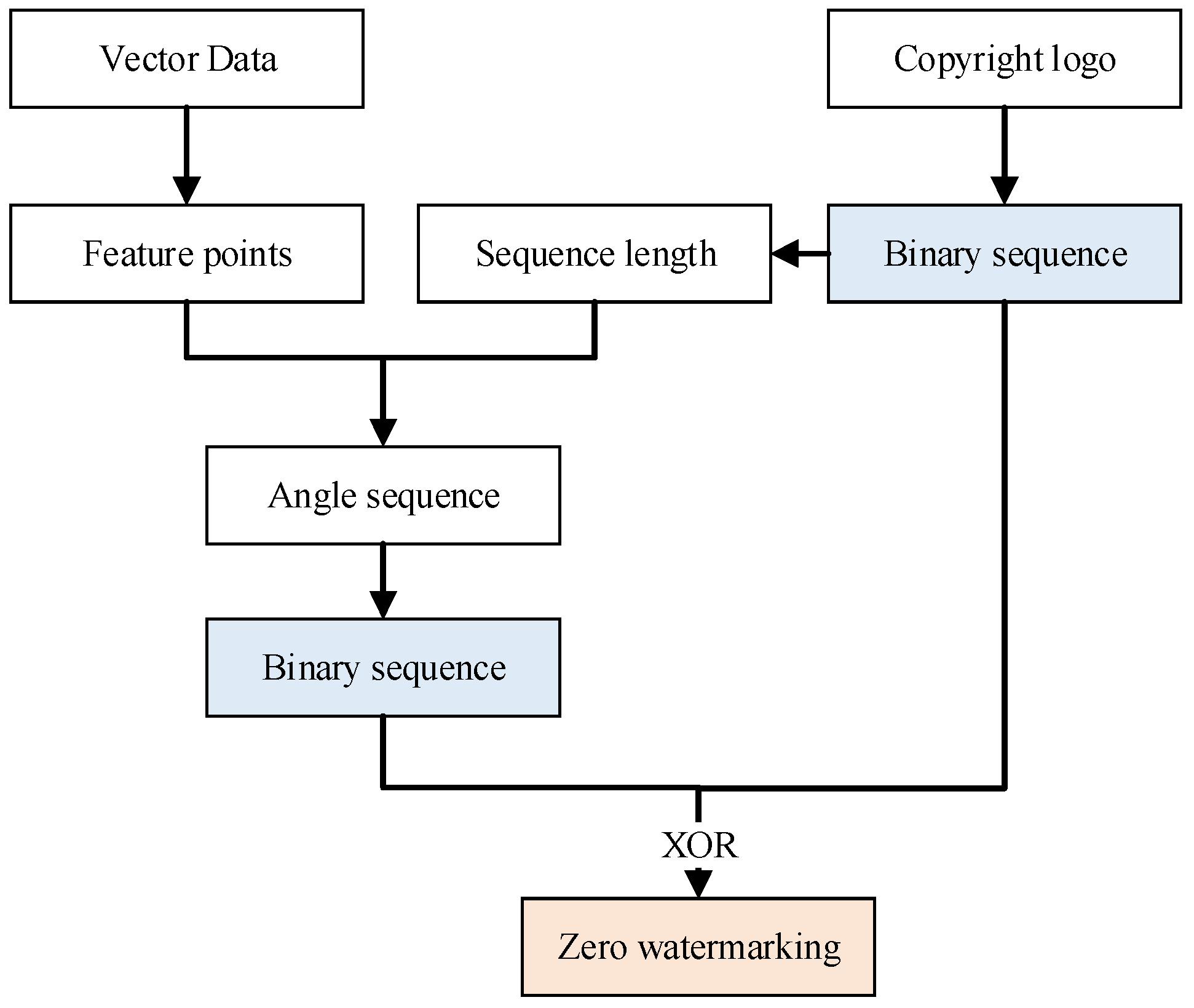
Because several nodes connect the line segments of the vector line elements and surface elements, we regard the two types of elements as a set of nodes. The points that can reflect the full features of the vector data are regarded as feature points. To resist simplification attacks, we use the Douglas–Peucker algorithm to compress the vector data for selecting feature points and calculating the mean value of these feature points. We draw several concentric circles with the mean value as the center and a sequence of numbers determined by the length of the binary sequence of the copyright image as the radii. Then, we calculate the value of each point’s angles in each circle and binarize the sequence consisting of these values. After that, we can perform an XOR operation between the binary sequence of angles and the copyright image sequence to extract the zero watermarking. The algorithm ensures the even distribution of watermark features in space and improves the watermark’s ability to resist various attacks. The construction process of zero watermarking is shown in
Figure 1.
2.2. Blockchain
Traditional zero watermarking algorithms send watermark information to the IPR for registration to ensure that the obtained watermark has a credible copyright attribute. When facing a copyright dispute, we can restore the copyright through a public algorithm designed for copyright protection. However, this method is unrealistic to apply to the protection of massive geographic data due to its long review cycle, high cost, and inability to trace infringement. The emergence of blockchain provides the right solution for the above issues.
2.2.1. Blockchain Technology
Blockchain technology was first proposed by a scholar named Satoshi Nakamoto in his paper “Bitcoin: A peer-to-peer e-cash system” published in 2008 [
23].
2.2.2. Ant Blockchain Open Alliance
Nowadays, there are many mature blockchain applications, such as Bitcoin [
24], Ethereum blockchain [
25], and Antchain [
26]. Among them, Antchain is the latest and most popular blockchain application in China. It is widely used in many fields, such as finance, digital copyright protection, and government affairs. The Ant Blockchain Open Alliance is a blockchain network for enterprises and developers in Antchain, which does not need to be built and can be linked quickly. We briefly introduce the Ant Blockchain Open Alliance from the following aspects:
This is a computer protocol designed to disseminate, verify, or execute contracts in an information-based manner. A smart contract is a set of promises defined in digital form, including the agreements on which the contract participants can execute these promises. Smart contract allows trusted transactions without a third party, which is traceable and irreversible.
Here, a smart contract is used to measure the consumption of computing and storage in a virtual machine, which can prevent malicious attacks and the waste of computing and storage.
A virtual machine is a high-level abstraction that simulates a physical machine based on a native operating system. It allows the same platform to run on many different hardware architectures and operating systems. Virtual machines in blockchain are mainly used to run intelligent contracts on the chain.
The storage status of blockchain accounts includes the basic storage status of all accounts and the internal storage status of contract accounts. The contract platform can be understood as a kind of "state machine" of transaction. The world state describes the current basic storage state. After executing the smart contract, the world state may change into another new world state.
This is the algorithm for data consistency assurance in the distributed system, which ensures the data consistency of multiple participants through certain protocol interactions. Standard algorithms include PDFT, RAFT, POW, POS, and so on.
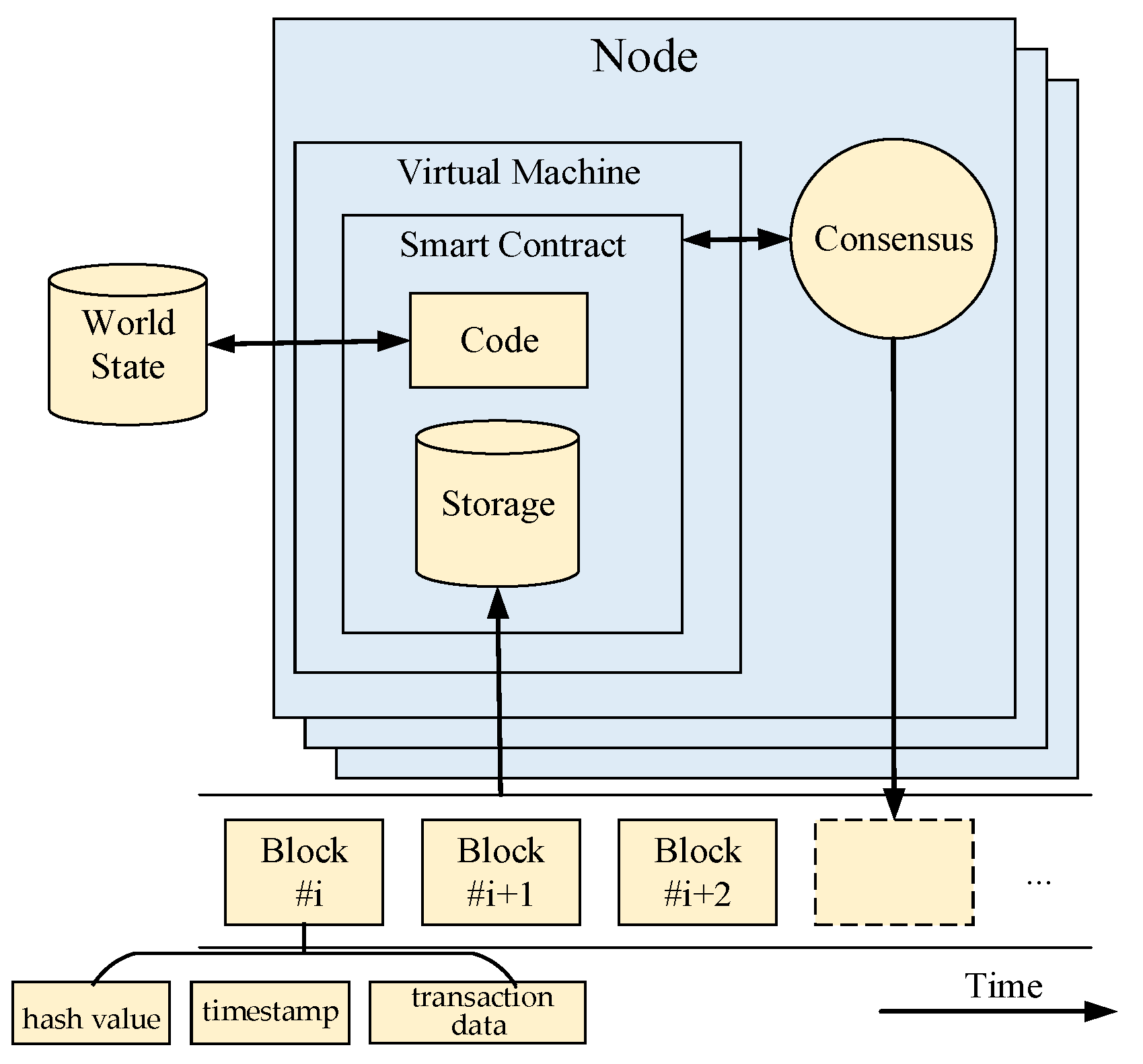
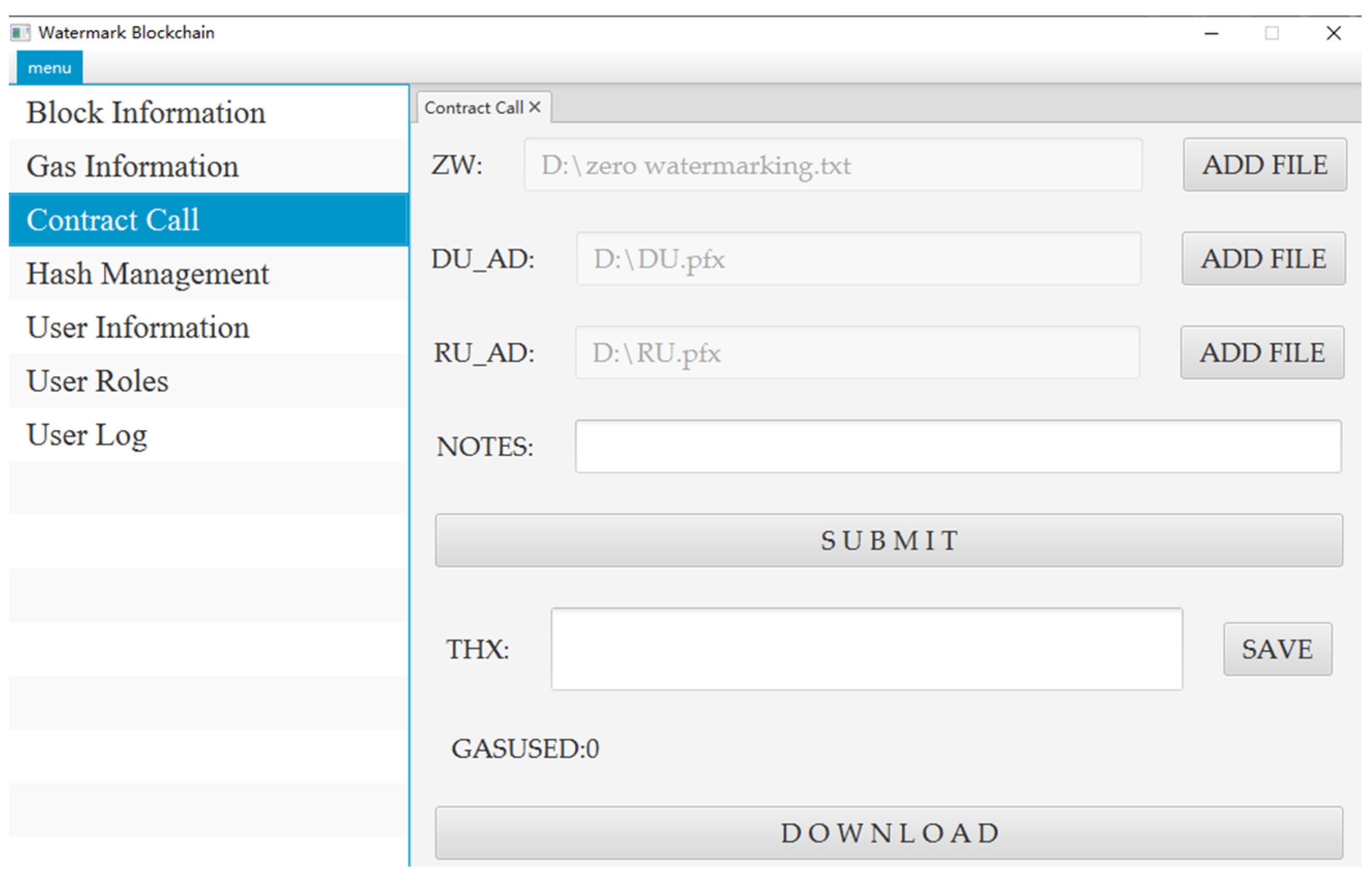
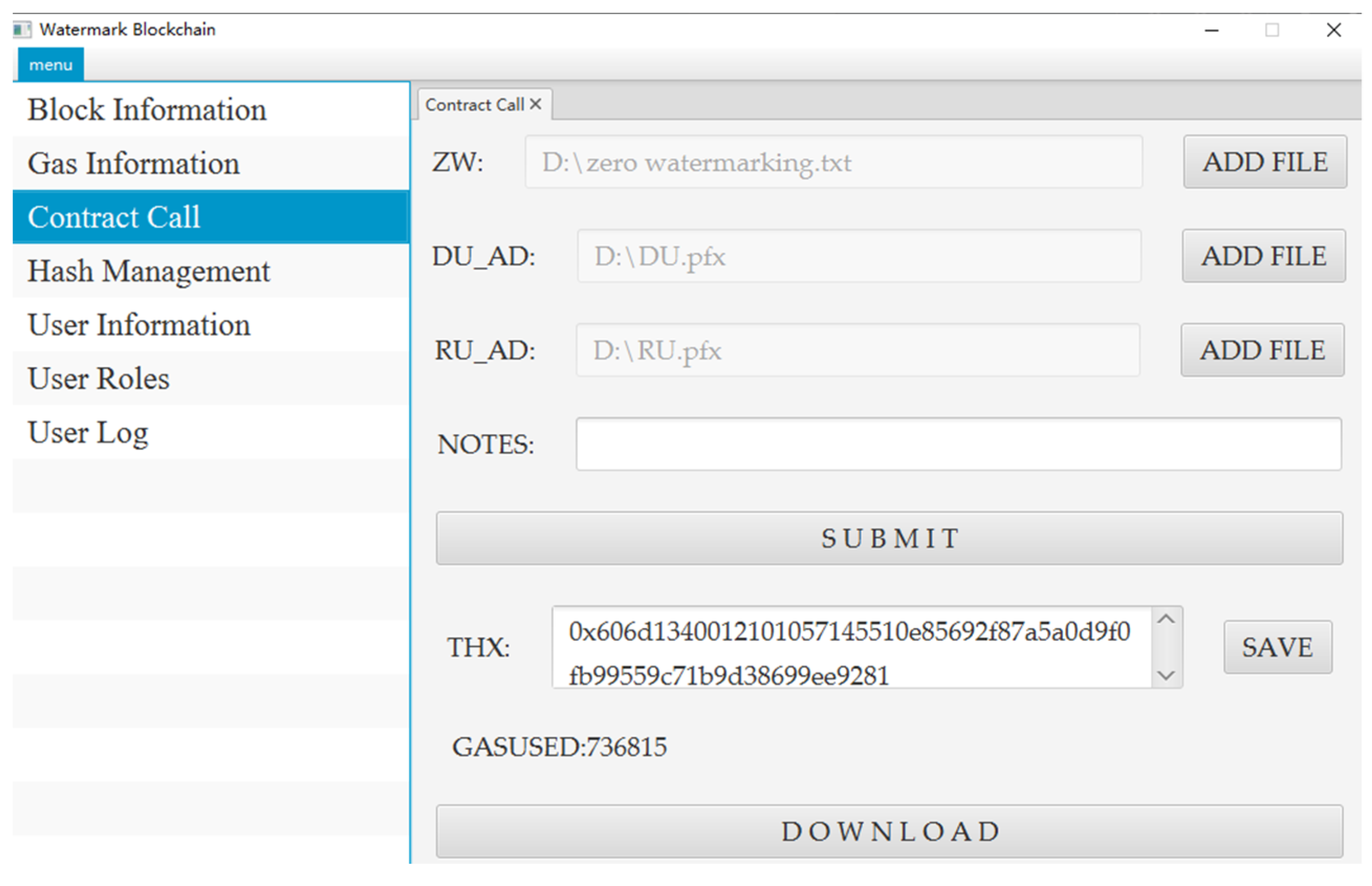
As shown in
Figure 2, a blockchain is a growing list of records, called blocks, linked through cryptography. Each block contains the encrypted hash value, timestamp, and transaction data of the previous block [
24]. When applied to zero watermarking-based copyright protection, once the extracted watermark information is uploaded to the blockchain, each node in the blockchain will execute the smart contract code in the virtual machine. Then, the consensus can be reached on the execution result of the smart contract. Finally, the world state will be updated, and new blocks will be generated. Once the block is on the chain, each node in the blockchain will contain a block’s backup, eliminating the risk of data centralization [
27]. Compared with traditional IPR, the application of blockchain makes the protection of vector data more credible.
6. Conclusions
The existing zero watermarking algorithm has the disadvantages of a long audit cycle, easy copyright loss, and difficult copyright ownership confirmation due to the requirement of copyright authentication by the IPR. We proposed a framework based on blockchain to solve these issues, making the resulting data distribution more traceable, more efficient, and cheaper than that yielded by registration with the traditional IPR. In addition, we proposed a zero watermarking algorithm based on the angular features of concentric circles with strong robustness. This algorithm constructs concentric circles with angular information from many inflection points in the line and area vector elements and generates multiple sequences of zero watermarking. The experiments show that the proposed algorithm reflects strong robustness under common watermark attacks, such as rotation, cropping, and compression, with different intensities and satisfies the requirement of uniqueness. This article fully combines zero watermarking and blockchain technology to achieve a lossless data protection scheme. When a copyright dispute occurs, the copyright information can be extracted with a public algorithm and compared with the same information stored on the blockchain to achieve copyright protection for the lossless vector map. This provides a new way of thinking about zero watermarking copyright authentication.