FQ-AGO: Fuzzy Logic Q-Learning Based Asymmetric Link Aware and Geographic Opportunistic Routing Scheme for MANETs
Abstract
1. Introduction
- We propose FQ-AGO fuzzy Q-learning opportunistic routing scheme that learns and makes the route decisions on-the-fly by considering one-hop performance.
- The proposed scheme takes into account the available throughput, distance progress, asymmetric link, and link quality in the candidate selection process.
- The proposed protocol is flexible because we can easily tune the protocol to work for different MANETs networks by modifying the fuzzy membership functions and fuzzy rules.
- We implemented and tested the proposed routing scheme in the ns-3 simulator.
2. Background and Related Works
3. Fuzzy Logic Q-Learning Routing Scheme with Asymmetric Link Aware
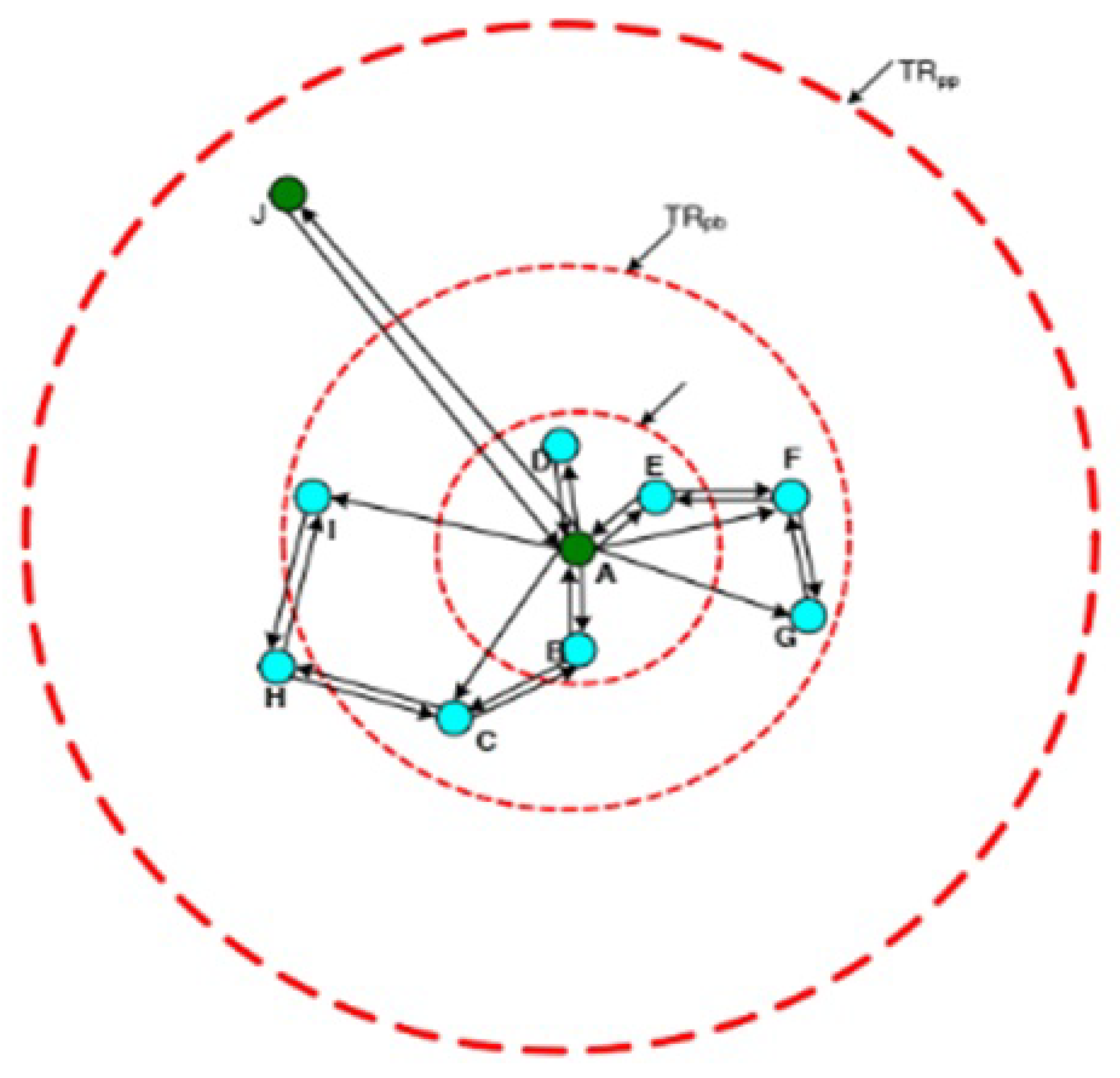
3.1. System Model and Assumption
3.2. Proposed Scheme
3.3. Neighbors Evaluation Criteria
3.3.1. Link Quality Estimation Using ETX
3.3.2. Available Throughput Estimation
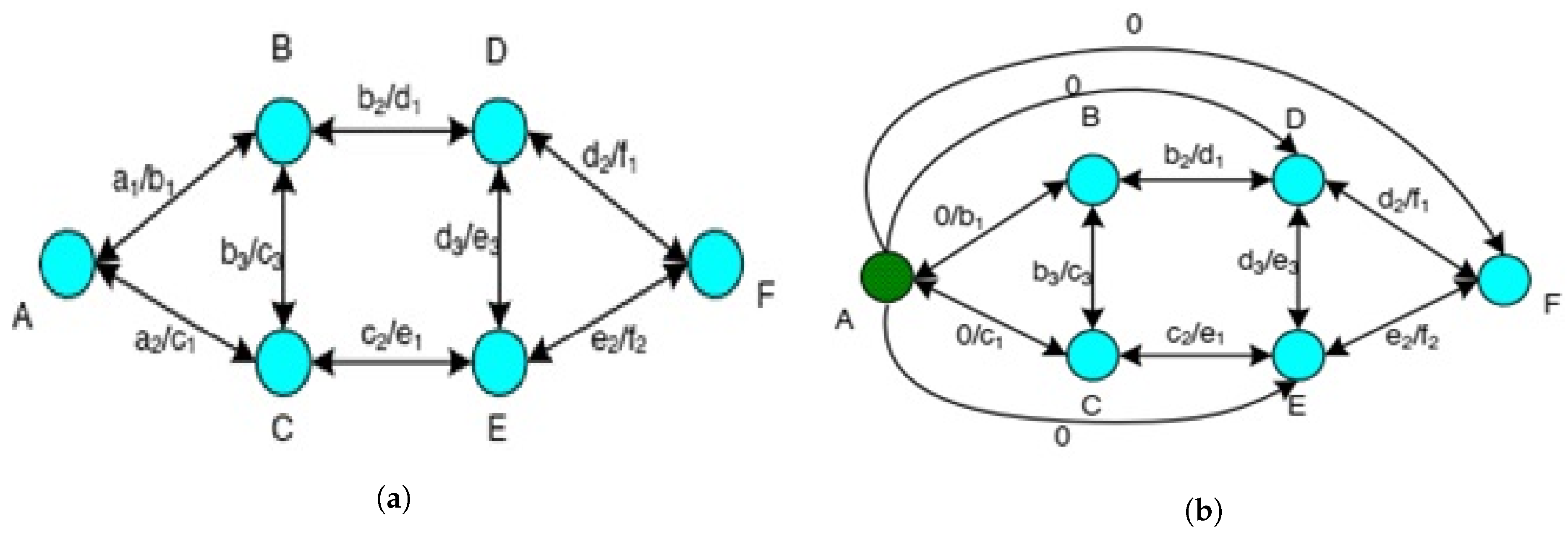
3.3.3. Asymmetric Link
4. Evaluation of One-Hop Neighbor Wireless Link Status Based on Fuzzy Logic Model
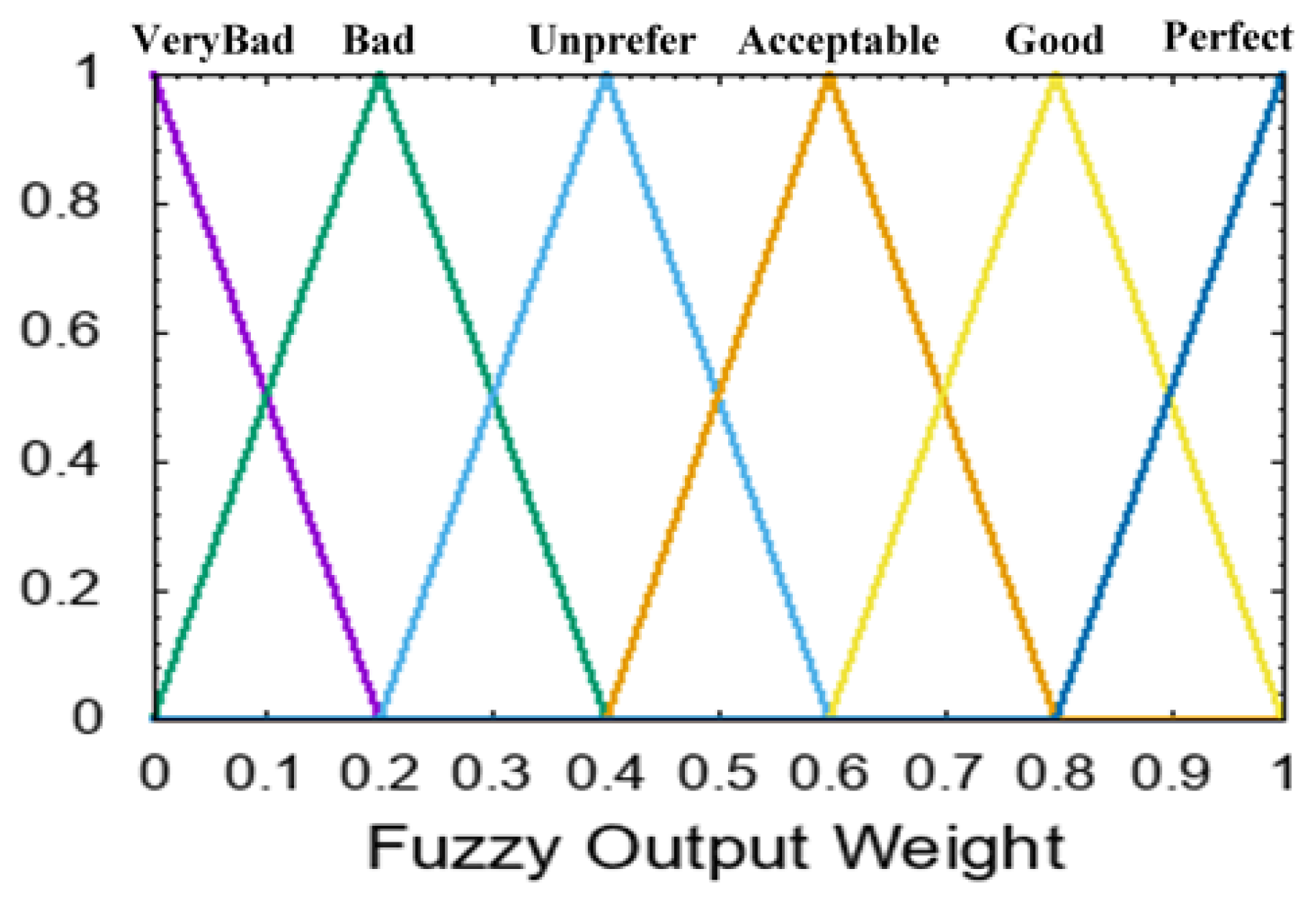
4.1. Fuzzification
4.2. Rule-Based and Inference Procedure
4.3. Defuzzification
4.4. Q-Learning Routing Decisions
4.4.1. Q-Learning Model
4.4.2. Updates of the Q-Values
5. Simulation and Evaluation
5.1. Simulation Setup
5.2. Evaluation Metrics
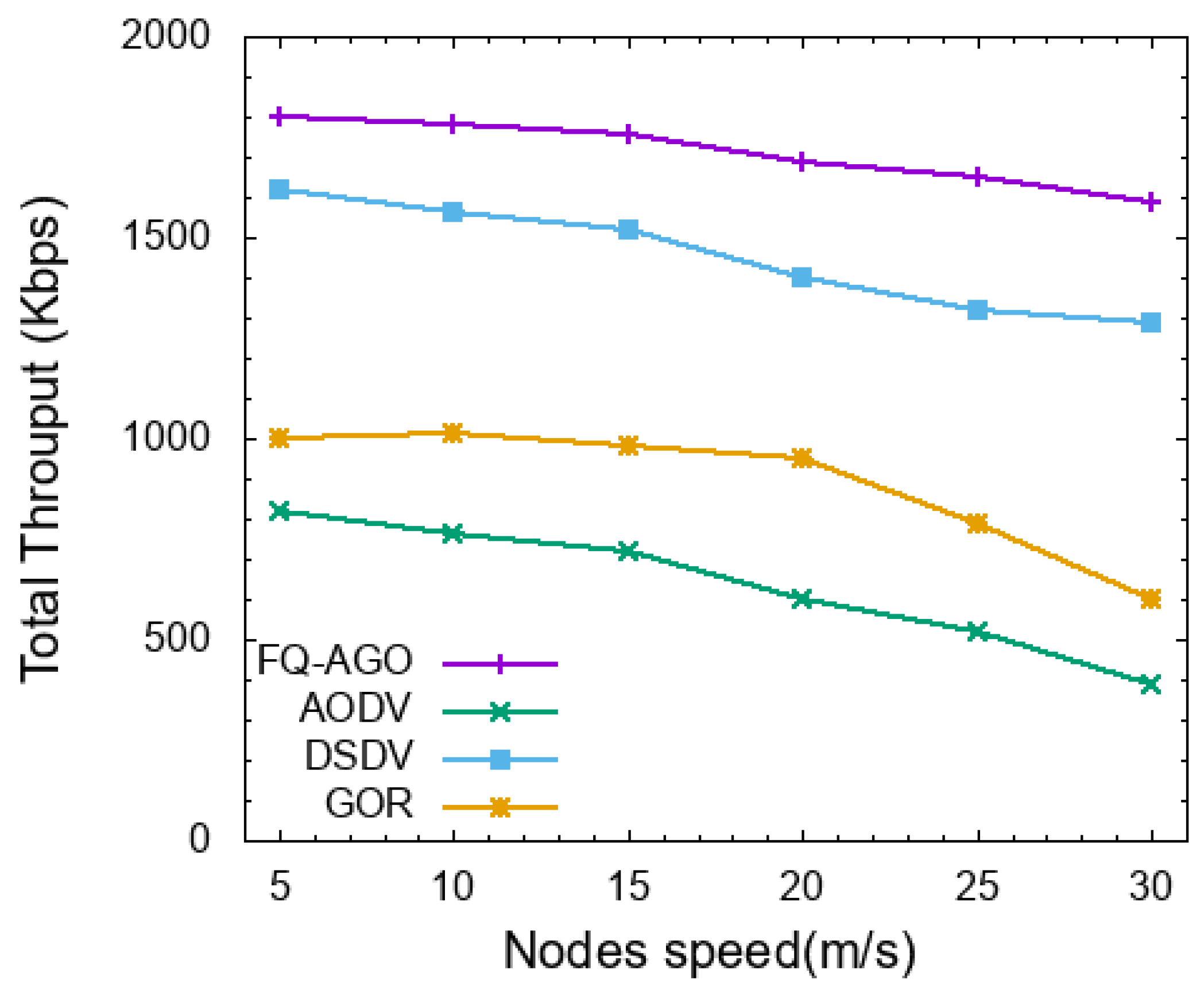
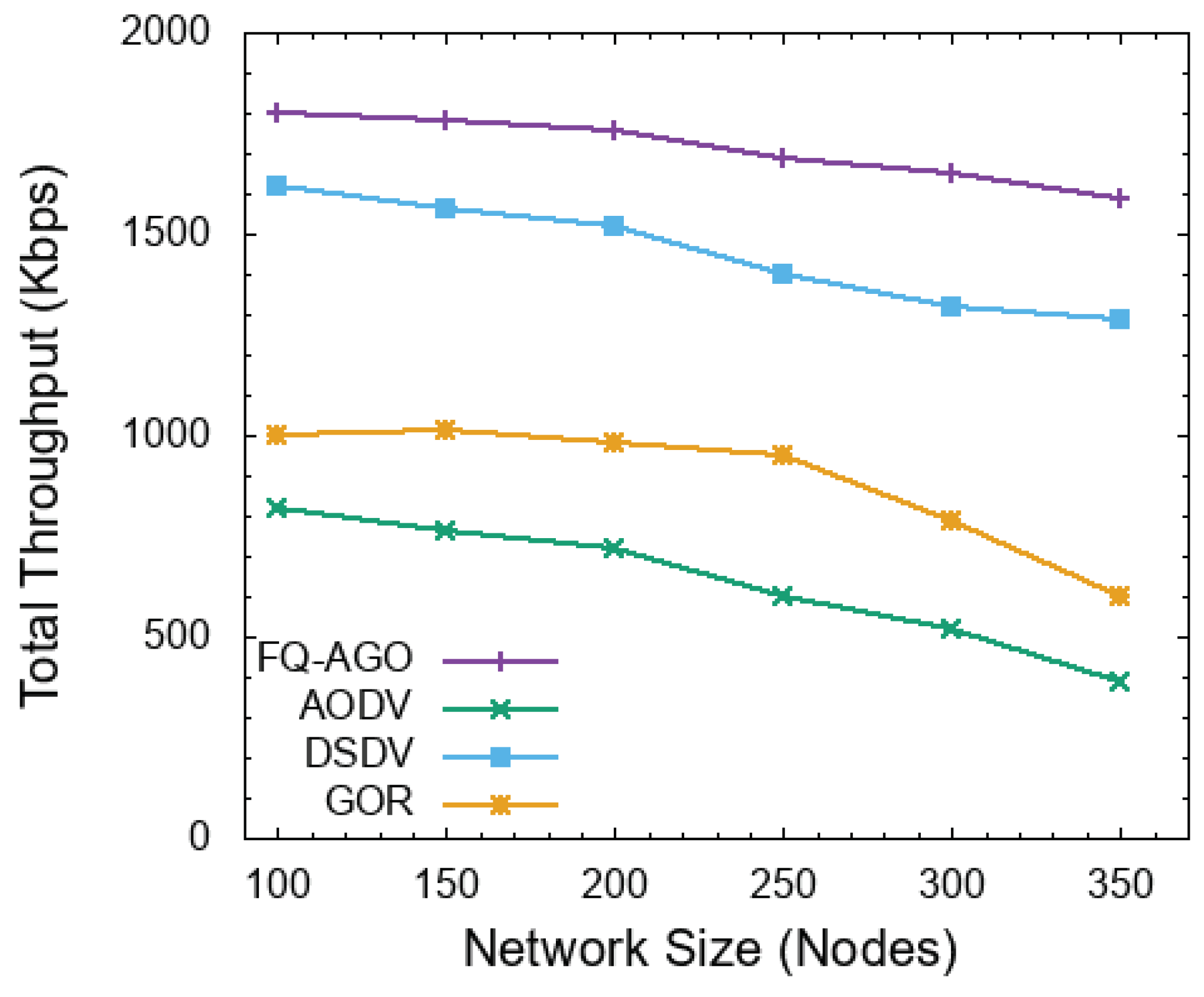
- Throughput defines as the rate of successfully delivered data packets per second over the communication channel from source to destination.
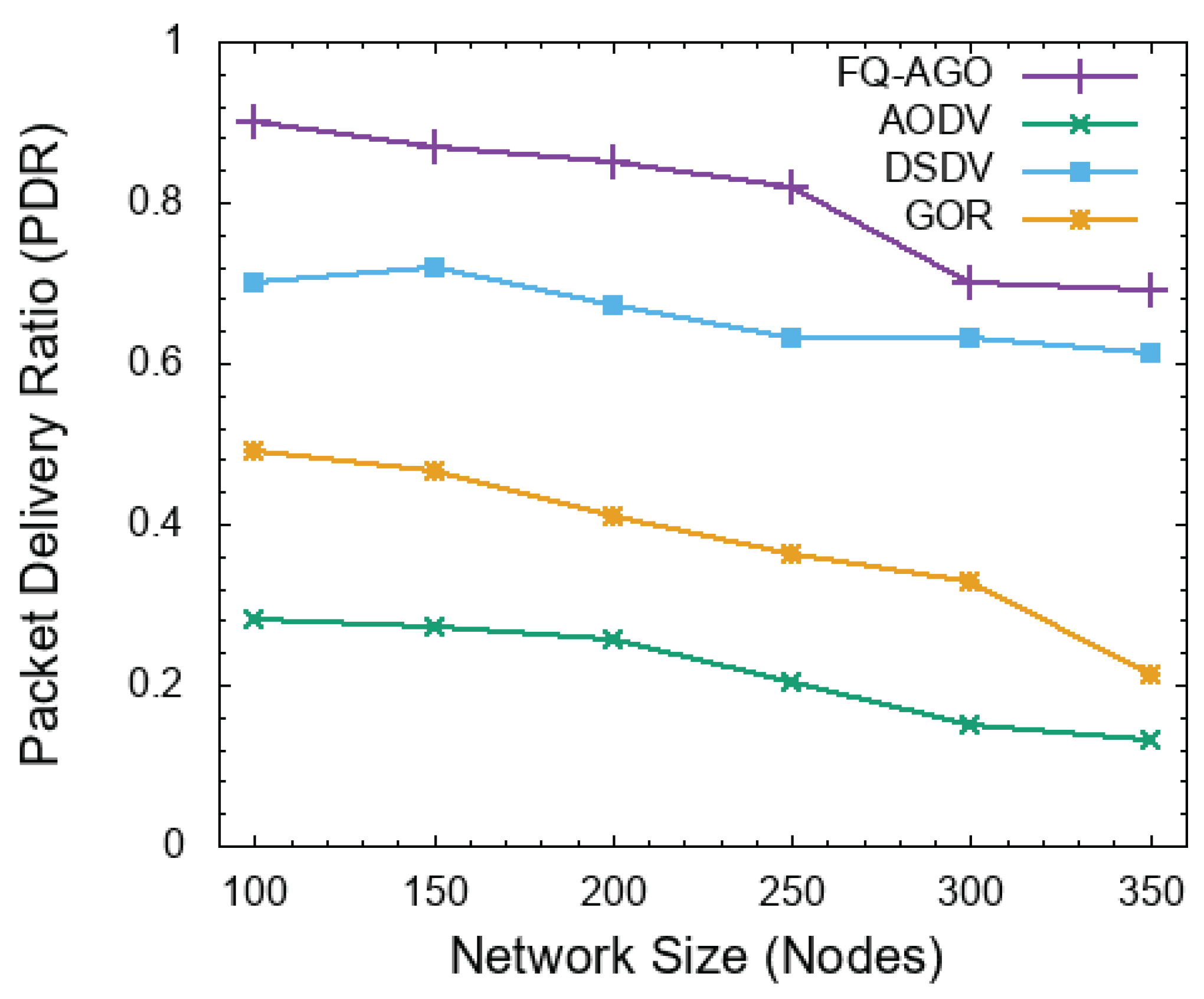
- Packet delivery ratio defines as the ratio of packets successfully delivered to the corresponding destination compared to the total number of data packets transmitted by the sender. This can be easily calculated by dividing the number of received data packets at the destination by the number of data packets that were transmitted by the sender.
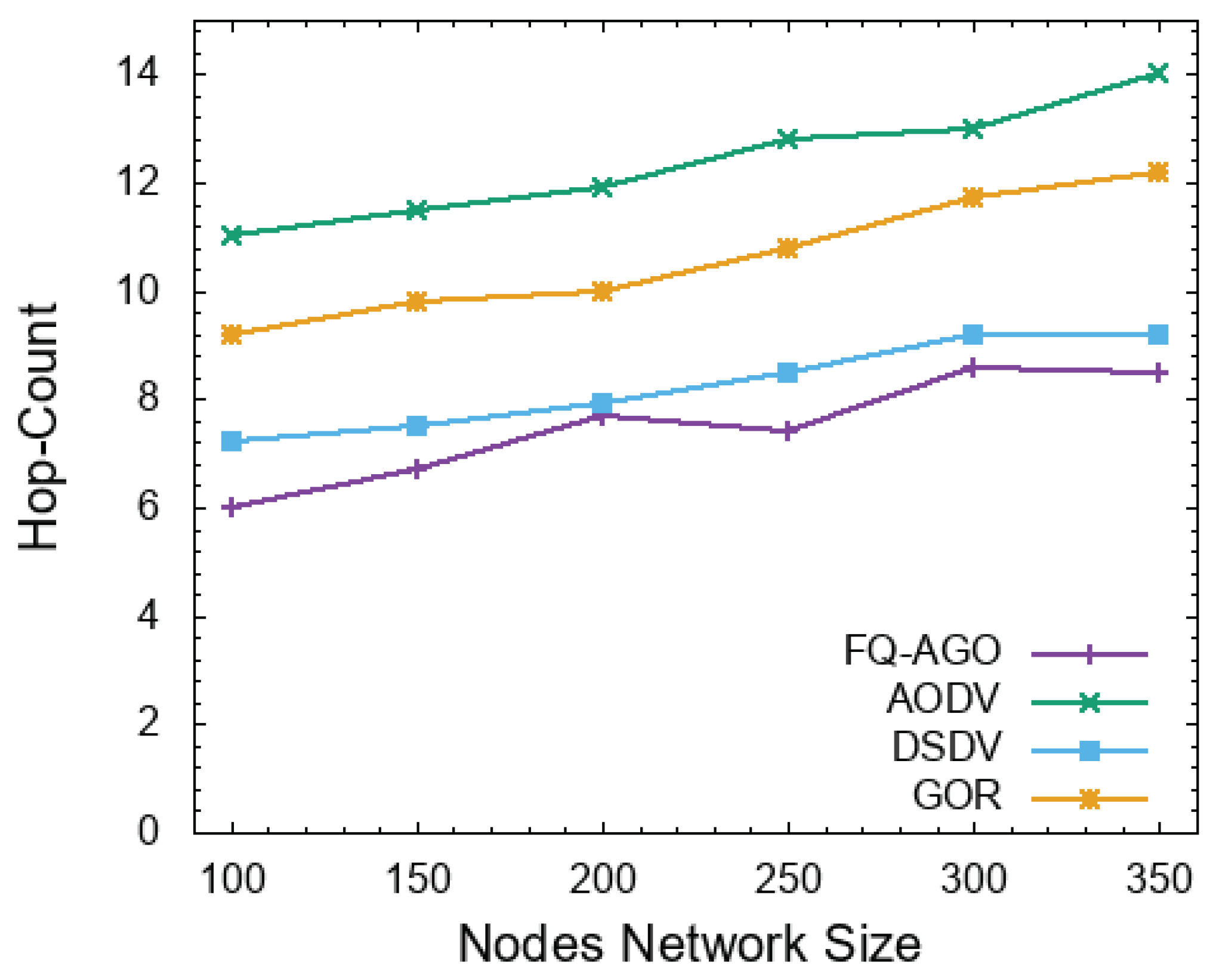
- Average hop-count refers to the number of intermediate nodes that participate in the transmission process to deliver data packets from the source node to a given destination.
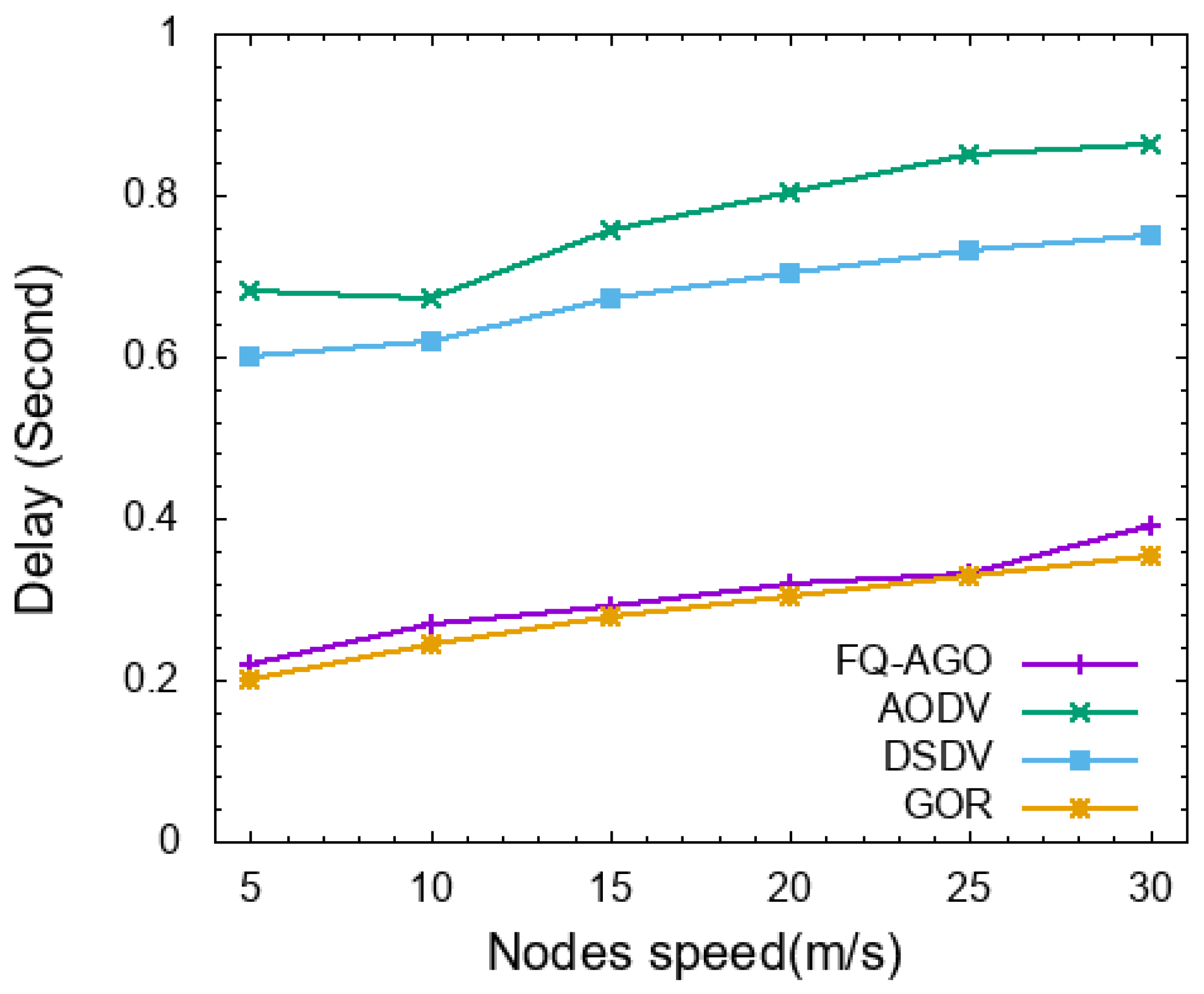
- Average packet delay defines as the average delay that elapses between sending a data packet from a source and its arrival at a given destination, which may include delays due to route discovery, queuing, and re-transmissions.
5.3. Impact of Nodes Mobility
5.4. Impact of Network Size
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Ding, Y.Z.; Li, Y.C.; Xu, Y.C.; Zhou, Y.Z.; Zhang, Y.l. An Opportunistic Routing Protocol for Mobile Ad Hoc Networks Based on Stable Ideology. Wirel. Pers. Commun. 2017, 97, 309–331. [Google Scholar] [CrossRef]
- Liu, H.; Zhang, B.; Mouftah, H.T.; Shen, X.; Ma, J. Opportunistic routing for wireless ad hoc and sensor networks: Present and future directions. IEEE Commun. Mag. 2009, 47, 103–109. [Google Scholar] [CrossRef]
- Gupta, P.; Kumar, P.R. The capacity of wireless networks. IEEE Trans. Inf. Theory 2000, 46, 388–404. [Google Scholar] [CrossRef]
- Huang, H.; Jaradat, Y.; Misra, S.; Tourani, R. Towards Achieving Linear Capacity Scaling in Wireless Networks through Directed Energy Links. IEEE Trans. Wirel. Commun. 2014, 13, 1806–1814. [Google Scholar] [CrossRef]
- Biswas, S.; Morris, R. ExOR: Opportunistic multi-hop routing for wireless networks. In Proceedings of the 2005 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communications; ACM SIGCOMM Computer Communication Review; ACM: New York, NY, USA, 2005; pp. 133–144. [Google Scholar]
- Lebedeva, O. Fuzzy set theory: Foundations and applications. In Proceedings of the 7th Latvian Mathematical Conference, Rezekne, Latvia, 18–19 April 2008; p. 29. [Google Scholar]
- Watkins, C.J.C.H. Learning from Delayed Rewards; King’s College: Cambridge, UK, 1989. [Google Scholar]
- Perkins, C.E.; Bhagwat, P. Highly Dynamic Destination-Sequenced Distance-Vector Routing (DSDV) for Mobile Computers. In Proceedings of the Conference on Communications Architectures, Protocols and Applications; SIGCOMM ’94; ACM: New York, NY, USA, 1994; pp. 234–244. [Google Scholar] [CrossRef]
- Perkins, C.E.; Royer, E.M. Ad-hoc on-demand distance vector routing. In Proceedings of the Second IEEE Workshop on Mobile Computing Systems and Applications—WMCSA’99, New Orleans, LA, USA, 25–26 February 1999; pp. 90–100. [Google Scholar] [CrossRef]
- Leontiadis, I.; Mascolo, C. GeOpps: Geographical opportunistic routing for vehicular networks. In Proceedings of the 2007 IEEE International Symposium on a World of Wireless, Mobile and Multimedia Networks, Espoo, Finland, 18–21 June 2007; pp. 1–6. [Google Scholar]
- Sanchez-Iborra, R.; Cano, M. JOKER: A Novel Opportunistic Routing Protocol. IEEE J. Sel. Areas Commun. 2016, 34, 1690–1703. [Google Scholar] [CrossRef]
- Venkatraman, S.; Sarvepalli, S.K. Load balance technique with adaptive position updates (LAPU) for geographic routing in MANETs. In EURASIP Journal of Wireless Communication Network; Springer: Berlin, Germany, 2018; Volume 2018, p. 73. [Google Scholar]
- Lee, G.Y.; Haas, Z.J. Simple, Practical, and Effective Opportunistic Routing for Short-Haul Multi-Hop Wireless Networks. IEEE Trans. Wirel. Commun. 2011, 10, 3583–3588. [Google Scholar] [CrossRef]
- Yuan, Y.; Yang, H.; Wong, S.H.; Lu, S.; Arbaugh, W. ROMER: Resilient opportunistic mesh routing for wireless mesh networks. IEEE Workshop Wirel. Mesh Netw. (WiMesh) 2005, 12. Available online: http://citeseerx.ist.psu.edu/viewdoc/summary?doi=10.1.1.80.7105 (accessed on 26 March 2020).
- Mao, X.; Tang, S.; Xu, X.; Li, X.; Ma, H. Energy-Efficient Opportunistic Routing in Wireless Sensor Networks. IEEE Trans. Parallel Distrib. Syst. 2011, 22, 1934–1942. [Google Scholar] [CrossRef]
- Huang, P.; Chen, H.; Xing, G.; Tan, Y. SGF: A state-free gradient-based forwarding protocol for wireless sensor networks. In ACM Transactions on Sensor Networks (TOSN); ACM: New York, NY, USA, 2009; Volume 5, pp. 1–25. [Google Scholar]
- Xiao, M.; Wu, J.; Liu, C.; Huang, L. Tour: Time-sensitive opportunistic utility-based routing in delay tolerant networks. In Proceedings of the 2013 IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 2085–2091. [Google Scholar]
- Yoon, S.G.; Jang, S.; Kim, Y.H.; Bahk, S. Opportunistic routing for smart grid with power line communication access networks. IEEE Trans. Smart Grid 2013, 5, 303–311. [Google Scholar] [CrossRef]
- Boukerche, A.; Darehshoorzadeh, A. Opportunistic Routing in Wireless Networks: Models, Algorithms, and Classifications. ACM Comput. Surv. 2014, 47, 22:1–22:36. [Google Scholar] [CrossRef]
- Zeng, K.; Lou, W.; Yang, J.; Brown, D.R., III. On throughput efficiency of geographic opportunistic routing in multihop wireless networks. Mob. Netw. Appl. 2007, 12, 347–357. [Google Scholar] [CrossRef]
- Sharma, D.; Sohi, G.; Dhankhar, H.; Yadav, M. Direct Perceptive Routing Protocol for Opportunistic Networks. In Proceedings of the 2018 Eleventh International Conference on Contemporary Computing (IC3), Noida, India, 2–4 August 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Sharma, D.K.; Dhurandher, S.K.; Woungang, I.; Srivastava, R.K.; Mohananey, A.; Rodrigues, J.J.P.C. A Machine Learning-Based Protocol for Efficient Routing in Opportunistic Networks. IEEE Syst. J. 2018, 12, 2207–2213. [Google Scholar] [CrossRef]
- Hendriks, T.; Camelo, M.; Latré, S. Q 2-routing: A Qos-aware Q-routing algorithm for wireless ad hoc networks. In Proceedings of the 2018 IEEE 14th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Limassol, Cyprus, 15–17 October 2018; pp. 108–115. [Google Scholar]
- Jung, W.; Yim, J.; Ko, Y. QGeo: Q-learning-Based Geographic Ad Hoc Routing Protocol for Unmanned Robotic Networks. IEEE Commun. Lett. 2017, 21, 2258–2261. [Google Scholar] [CrossRef]
- Alzamzami, O.; Mahgoub, I. Fuzzy logic-based geographic routing for urban vehicular networks using link quality and achievable throughput estimations. IEEE Trans. Intell. Transp. Syst. 2018, 20, 2289–2300. [Google Scholar] [CrossRef]
- Wu, C.; Yoshinaga, T.; Ji, Y.; Zhang, Y. Computational intelligence inspired data delivery for vehicle-to-roadside communications. IEEE Trans. Veh. Technol. 2018, 67, 12038–12048. [Google Scholar] [CrossRef]
- Boussoufa-Lahlah, S.; Semchedine, F.; Bouallouche-Medjkoune, L. Geographic routing protocols for Vehicular Ad hoc NETworks (VANETs): A survey. In Vehicular Communications; Elsevier: Amsterdam, The Netherlands, 2018; Volume 11, pp. 20–31. [Google Scholar]
- Hu, C.L.; Sosorburam, C. Enhanced Geographic Routing with Two-Hop Neighborhood Information in Sparse MANETs. In Wireless Personal Communications; Springer: Berlin, Germany, 2019; Volume 107, pp. 417–436. [Google Scholar]
- Cheng, L.; Cao, J.; Chen, C.; Chen, H.; Ma, J. Towards intelligent contention-based geographic forwarding in wireless sensor networks. In IET Communications; IET: Stevenage, UK, 2011; Volume 5, pp. 1711–1719. [Google Scholar]
- Saleet, H.; Basir, O.; Langar, R.; Boutaba, R. Region-based location-service-management protocol for VANETs. IEEE Trans. Veh. Technol. 2009, 59, 917–931. [Google Scholar] [CrossRef]
- Woo, H.; Lee, M. Mobile group based location service management for vehicular ad-hoc networks. In Proceedings of the 2011 IEEE International Conference on Communications (ICC), Kyoto, Japan, 5–9 June 2011; pp. 1–6. [Google Scholar]
- Alshehri, A.; Huang, H.; Parvin, S. Cooperative Hybrid and Scalable Opportunistic Routing Scheme for Mobile Large-scale Wireless Network. J. Comput. Eng. Inf. Technol. 2020, 9, 1–10. [Google Scholar] [CrossRef]
- De Couto, D.S.; Aguayo, D.; Bicket, J.; Morris, R. A high-throughput path metric for multi-hop wireless routing. In Proceedings of the 9th Annual International Conference on Mobile Computing and Networking; ACM: New York, NY, USA, 2003; pp. 134–146. [Google Scholar]
- Zhang, X.; Qian, Z.; Li, T.; Qian, L.; Fu, C.; Li, Y. An efficient routing protocol for heterogeneous wireless ad hoc networks. In Proceedings of the 2011 IEEE International Conference on Multimedia Technology, Hangzhou, China, 26–28 July 2011; pp. 172–175. [Google Scholar]
- Le, T.; Sinha, P.; Xuan, D. Turning heterogeneity into an advantage in wireless ad-hoc network routing. Ad Hoc Netw. 2010, 8, 108–118. [Google Scholar] [CrossRef]
- Shah, V.; Krishnamurthy, S. Handling asymmetry in power heterogeneous ad hoc networks: A cross layer approach. In Proceedings of the 25th IEEE International Conference on Distributed Computing Systems (ICDCS’05), Columbus, OH, USA, 6–10 June 2005; pp. 749–759. [Google Scholar]
- Nesargi, S.; Prakash, R. A tunneling approach to routing with unidirectional links in mobile ad-hoc networks. In Proceedings of the IEEE 9th International Conference on Computer Communications and Networks (Cat. No. 00EX440), Las Vegas, NV, USA, 16–18 October 2000; pp. 522–527. [Google Scholar]
- Narayanaswamy, S.; Kawadia, V.; Sreenivas, R.S.; Kumar, P. Power control in ad-hoc networks: Theory, architecture, algorithm and implementation of the COMPOW protocol. In Proceedings of the European Wireless Conference, Florence, Italy, 25–28 February 2002; Volume 2002, p. 156162. [Google Scholar]
- Kawadia, V.; Kumar, P.R. Power control and clustering in ad hoc networks. In Proceedings of the IEEE INFOCOM 2003 22nd Annual Joint Conference of the IEEE Computer and Communications Societies (IEEE Cat. No. 03CH37428), San Francisco, CA, USA, 30 March–3 April 2003; Volume 1, pp. 459–469. [Google Scholar]
- Liu, W.; Zhang, C.; Yao, G.; Fang, Y. DELAR: A device-energy-load aware relaying framework for heterogeneous mobile ad hoc networks. IEEE J. Sel. Areas Commun. 2011, 29, 1572–1584. [Google Scholar] [CrossRef]
- Dalman, H.; Güzel, N.; Sivri, M. A fuzzy set-based approach to multi-objective multi-item solid transportation problem under uncertainty. Int. J. Fuzzy Syst. 2016, 18, 716–729. [Google Scholar] [CrossRef]
- Wu, C.; Ohzahata, S.; Kato, T. Flexible, portable, and practicable solution for routing in VANETs: A fuzzy constraint Q-learning approach. IEEE Trans. Veh. Technol. 2013, 62, 4251–4263. [Google Scholar] [CrossRef]
- Sutton, R.S.; Barto, A.G. Reinforcement Learning: An Introduction; MIT Press: Cambridge, MA, USA, 2018. [Google Scholar]
- Bettstetter, C.; Resta, G.; Santi, P. The node distribution of the random waypoint mobility model for wireless ad hoc networks. IEEE Trans. Mob. Comput. 2003, 2, 257–269. [Google Scholar] [CrossRef]
- Parvin, S.; Mtibaa, A.; Huang, H.; Misra, S.; Mahbub, S.M.Y.; Alshehri, A.; Zahedi, R. STAR: STAble routing for hidden interfering primary user problems in mobile cognitive radio networks. In Proceedings of the MILCOM 2017—2017 IEEE Military Communications Conference (MILCOM), Baltimore, MD, USA, 23–25 October 2017; pp. 569–574. [Google Scholar] [CrossRef]
- Darehshoorzadeh, A.; Cerdà-Alabern, L. Distance Progress Based Opportunistic Routing for wireless mesh networks. In Proceedings of the 2012 8th International Wireless Communications and Mobile Computing Conference (IWCMC), Limassol, Cyprus, 27–31 August 2012; pp. 179–184. [Google Scholar] [CrossRef]





| Parameter | Value |
|---|---|
| Packet Sequence Number | 2 bytes |
| Originator ID | 4 bytes |
| Originator Position | 16 bytes |
| Transmission Range | 1 byte |
| Rules | ATE | LQ | DP | TP | Fuzzy Weight |
|---|---|---|---|---|---|
| Rule1 | High | High | VeryClose | Long | Perfect |
| Rule2 | High | High | Close | Short | Good |
| Rule3 | High | High | Far | Long | Good |
| Rule4 | High | Medium | VeryClose | Short | Acceptable |
| Rule5 | High | Medium | Close | Long | Good |
| Rule6 | High | Medium | Far | Short | Not Preferred |
| Rule7 | High | Low | VeryClose | Long | Good |
| Rule8 | High | Low | Close | Long | Good |
| Rule9 | High | Low | Far | Short | Not Preferred |
| Rule10 | Medium | High | VeryClose | Long | Good |
| Rule11 | Medium | High | Close | Short | Acceptable |
| Rule12 | Medium | High | Far | Short | Acceptable |
| Rule13 | Medium | Medium | VeryClose | Long | Acceptable |
| Rule14 | Medium | Medium | Close | Short | Not Preferred |
| Rule15 | Medium | Medium | Far | Long | Acceptable |
| Rule16 | Medium | Low | VeryClose | Short | Bad |
| Rule17 | Medium | Low | Close | Long | Not Preferred |
| Rule18 | Medium | Low | Far | Short | Bad |
| Rule19 | Low | High | VeryClose | Long | Bad |
| Rule20 | Low | High | Close | Short | Not Preferred |
| Rule21 | Low | High | Far | Long | Bad |
| Rule22 | Low | Medium | VeryClose | Short | Very Bad |
| Rule23 | Low | Medium | Close | Long | Not Preferred |
| Rule24 | Low | Medium | Far | Short | Bad |
| Rule25 | Low | Low | VeryClose | Long | Very Bad |
| Rule26 | Low | Low | Close | Short | Bad |
| Rule27 | Low | Low | Far | Long | Very Bad |
| Parameter | Acronym | Value |
|---|---|---|
| Number of nodes | 100 | |
| Long transmission nodes ratio | - | 20% |
| Simulation Area | - | 1500 m × 1500 m |
| Long Transmission Range | 200–400 m | |
| Short Transmission Range | 200 m | |
| Maximum speed | 5–30 m/s | |
| Packet size | 512 B | |
| Data rate | 10 pps | |
| Buffer size | 0 packets |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alshehri, A.; Badawy, A.-H.A.; Huang, H. FQ-AGO: Fuzzy Logic Q-Learning Based Asymmetric Link Aware and Geographic Opportunistic Routing Scheme for MANETs. Electronics 2020, 9, 576. https://doi.org/10.3390/electronics9040576
Alshehri A, Badawy A-HA, Huang H. FQ-AGO: Fuzzy Logic Q-Learning Based Asymmetric Link Aware and Geographic Opportunistic Routing Scheme for MANETs. Electronics. 2020; 9(4):576. https://doi.org/10.3390/electronics9040576
Chicago/Turabian StyleAlshehri, Ali, Abdel-Hameed A. Badawy, and Hong Huang. 2020. "FQ-AGO: Fuzzy Logic Q-Learning Based Asymmetric Link Aware and Geographic Opportunistic Routing Scheme for MANETs" Electronics 9, no. 4: 576. https://doi.org/10.3390/electronics9040576
APA StyleAlshehri, A., Badawy, A.-H. A., & Huang, H. (2020). FQ-AGO: Fuzzy Logic Q-Learning Based Asymmetric Link Aware and Geographic Opportunistic Routing Scheme for MANETs. Electronics, 9(4), 576. https://doi.org/10.3390/electronics9040576





