Blockchain-Based Secure Storage Management with Edge Computing for IoT
Abstract
:1. Introduction
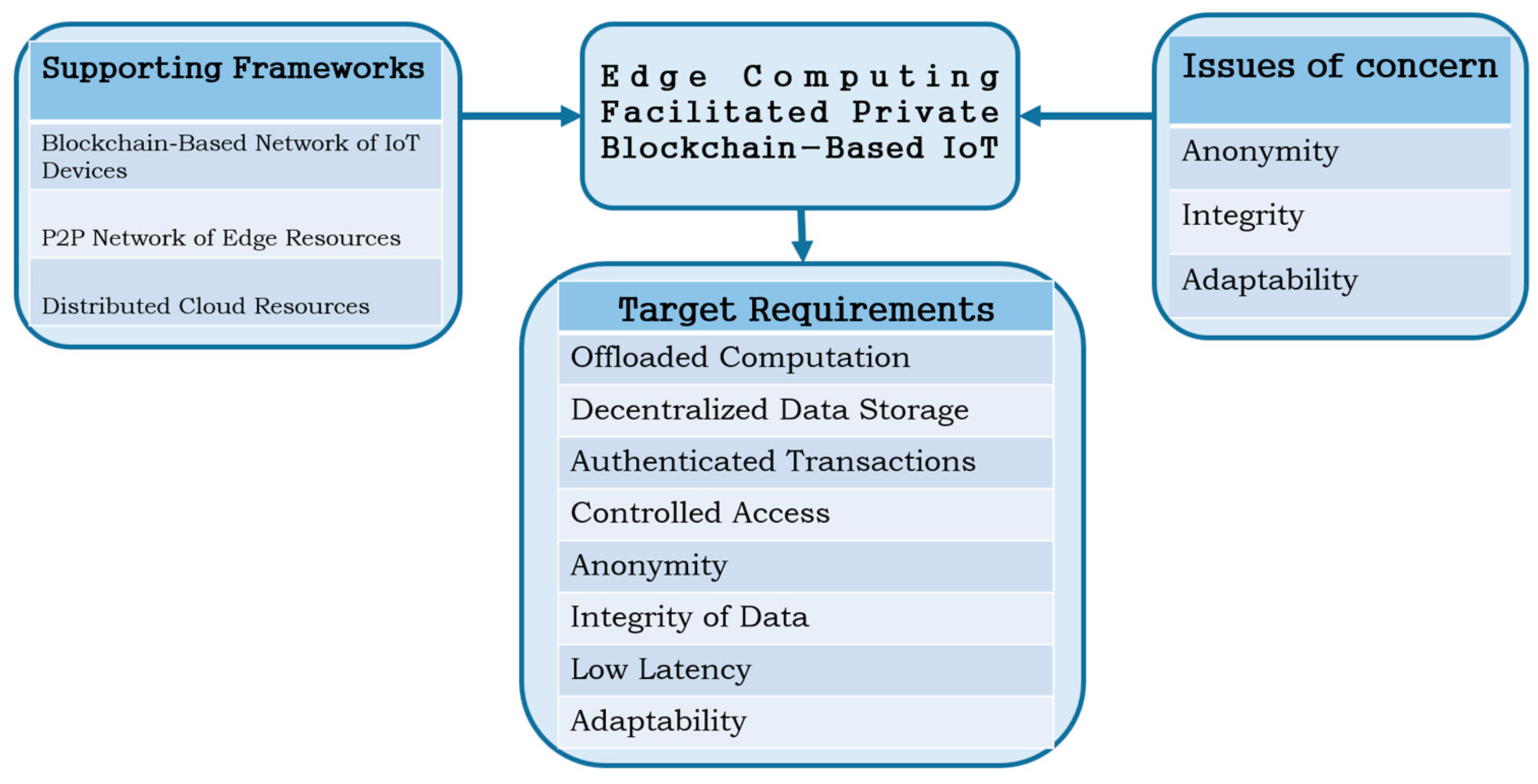
- Based on the edge computing layered architecture and blockchain’s P2P distributed ledger, we provide a thorough account of the typical stumbling blocks to be overcome to enable deployment of blockchain in IoT systems.
- We propose a novel framework to solve the identified issues of anonymity, integrity and adaptability in order to achieve successful integration of blockchain and edge computing for IoT systems. We further provide description of how these solutions can be implemented in the different layers of edge computing architecture.
- We present a practical approach towards the implementation of a decentralized application on the blockchain and give conceptual analysis of the protocols and operating environments for a prototype to achieve implementation of scalable and secure blockchain data storage in edge computing platforms for IoT applications.
2. Related Works
2.1. Core Technologies
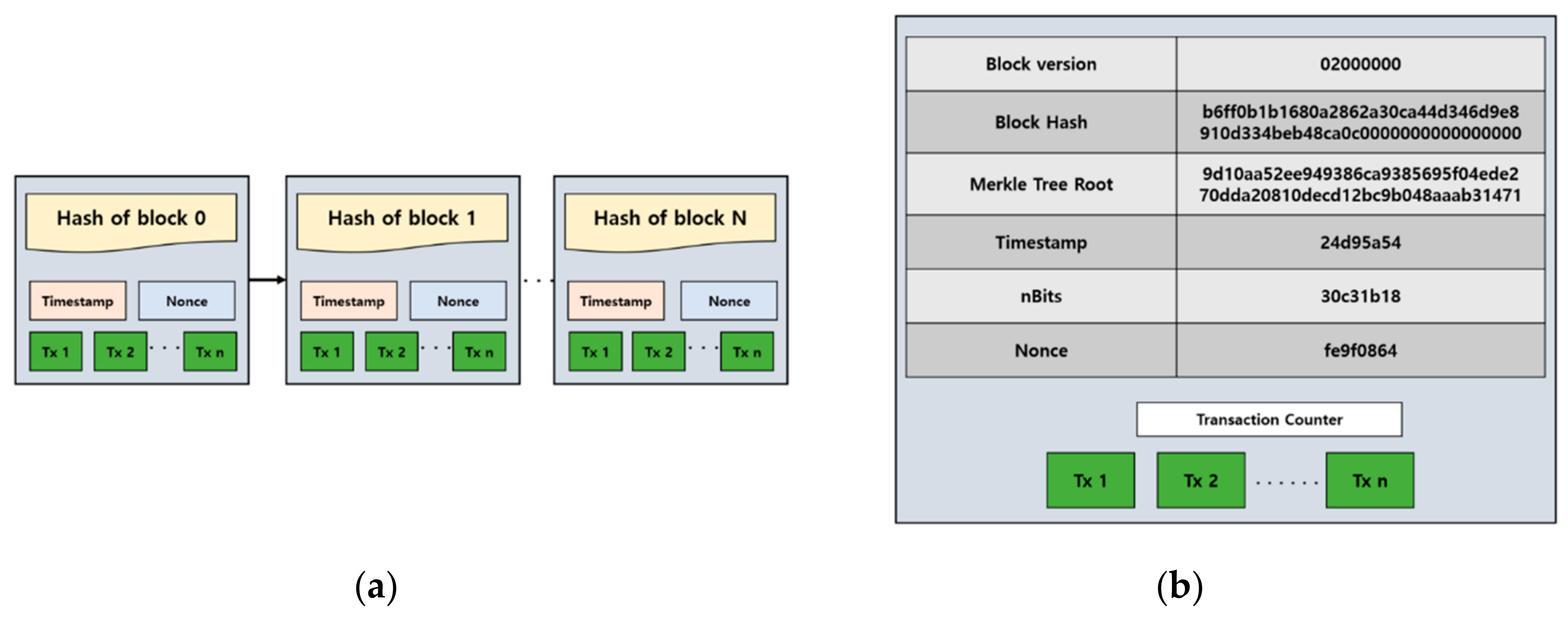
2.1.1. Blockchain Technology
2.1.2. Internet of Things
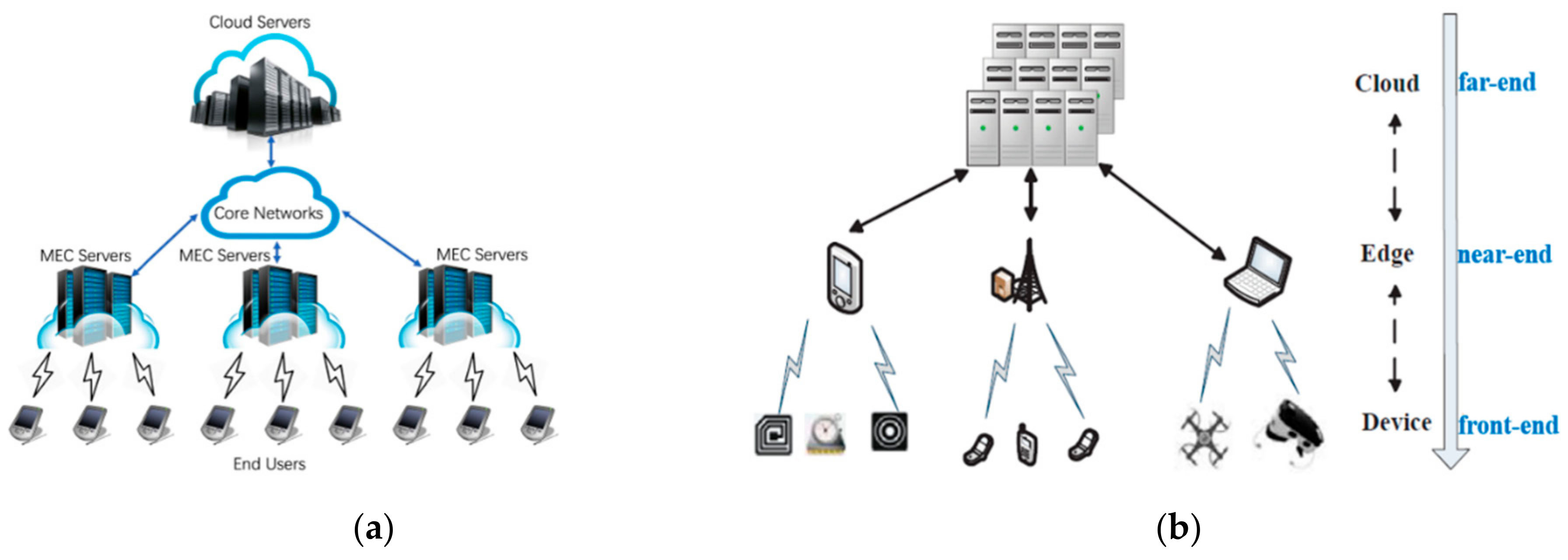
2.1.3. Edge Computing
2.2. Existing Research Works
3. Requirements and Considerations for the Proposed Framework
3.1. The Need for Integration
3.2. Issues Affecting Blockchain Adoption for IoT
3.3. Problem Statement
3.4. Design Requirements
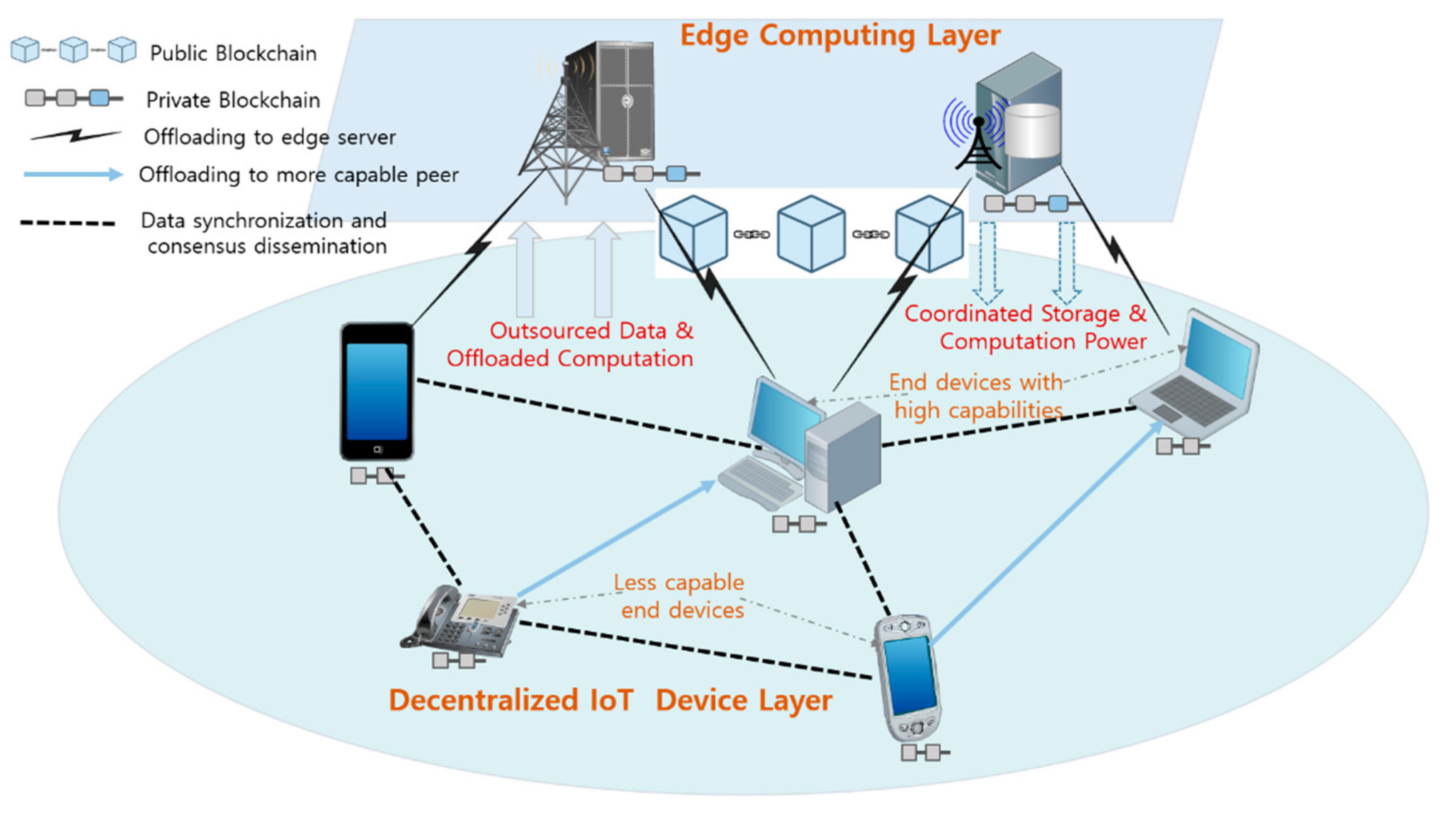
- Decentralized data storage, the integrated architecture of edge computing and blockchain should complement each other to extend storage capacities of IoT devices by combining the storage capacities of participating entities in a P2P basis in storing and sharing the transactions.
- Offloaded computation, the processing tasks outsourced to the edge servers by end devices should be verifiable and guaranteed to produce accurate results.
- Data integrity, the integrated system requires built-in reliable mechanisms to verify actions of both the data owners and consumers to ensure consistent and accurate modification of the outsourced data in the decentralized environment.
- Authenticity of transactions, to establish secure communication channels in the mobile, decentralized and heterogeneous environments of edge computing; validity of the involved entities and their respective transactions must be adequately authenticated.
- Anonymity, to ensure user data privacy in the blockchain network and allow participants in the network to conveniently perform their desired transactions without worry about being tracked or their identity being traced on the network. Their identity should not be mandatory for authentication, instead, only the transaction address shall suffice [13,14].
- Adaptability, the architecture must be flexible enough to support fluctuating environments and meet future growth in the number of devices and increasing amounts of transactions continuously generated and stored. It should adapt to these growing needs and increased complexities in future applications while maintaining acceptable levels of system throughput, delays and security.
- Low latency, the model should strike a balance and achieve optimal levels in the amounts of delays incurred during the computation and transmission of transactions from one entity to another. Identification of what computation tasks are involved and decision on where they should be performed between the end devices and servers on the cloud are important in ensuring minimal latencies in the system.
- Controlled access, it is imperative that access policies are enforced in the framework to regulate which data of a user can be shared and be viewed by whom.
4. Proposed Framework
4.1. Design Overview
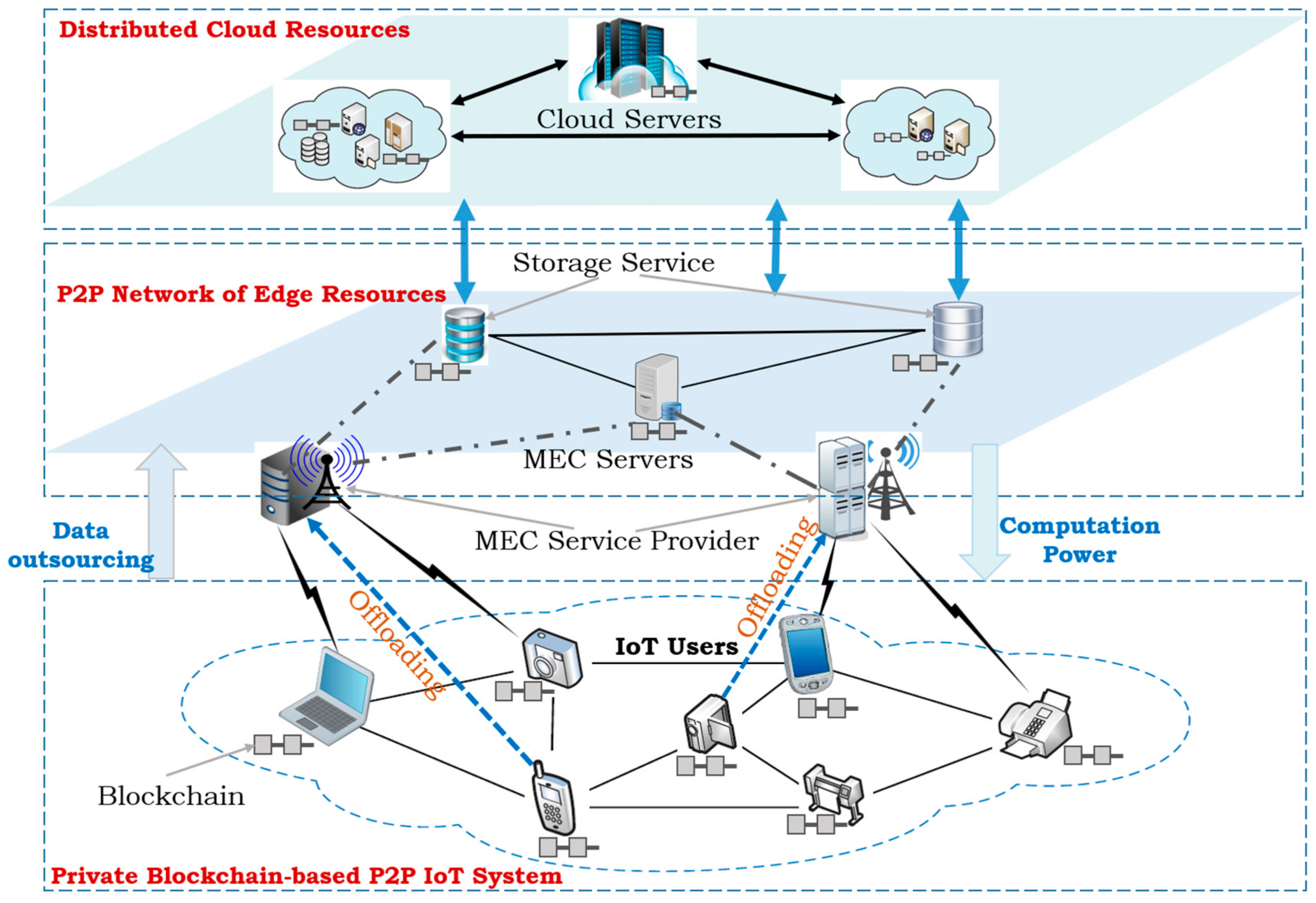
4.2. The Layered Architecture of the Proposed Framework
4.2.1. Decentralized IoT Device Layer
4.2.2. P2P Network of Edge Servers
4.2.3. Distributed Cloud Resources
4.3. Deployment of Services and Fulfillment of Design Requirements for IoT Applications
4.3.1. Deployment of Services for IoT Requirements
4.3.2. Fulfillment of Design Requirements in the Framework
5. Experimental Evaluation
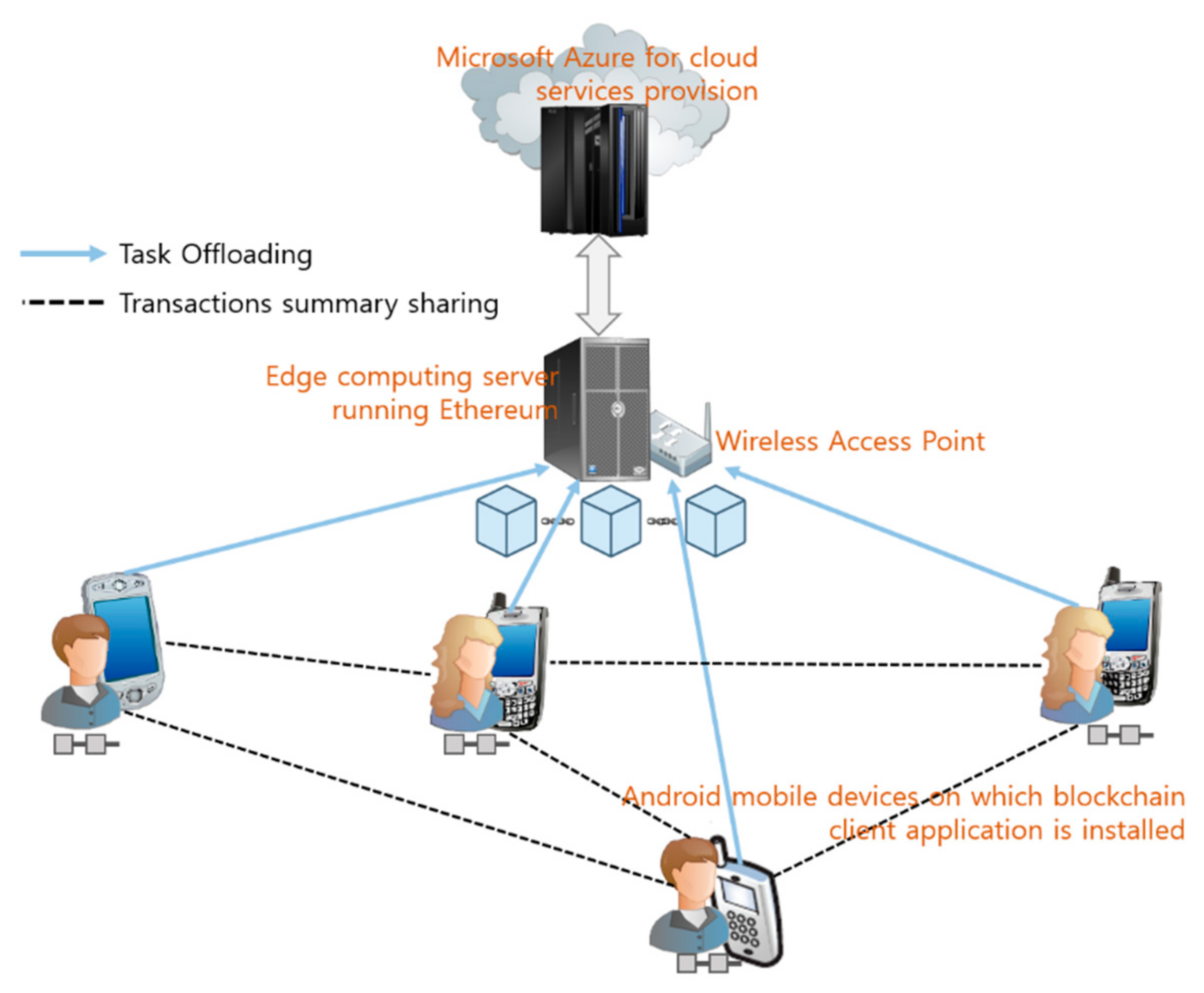
5.1. Prototype Design of the Proposed Framework
5.2. Conceptual Evaluation and Discussion
6. Conclusions and Future Directions
Author Contributions
Funding
Conflicts of Interest
References
- Kubendiran, M.; Singh, S.; Sangaiah, A.K. Enhanced Security Framework for E-Health Systems using Blockchain. J. Inf. Process. Syst. 2019, 15, 239–250. [Google Scholar]
- Xiong, Z.; Zhang, Y.; Niyato, D.; Wang, P.; Han, Z. When Mobile Blockchain Meets Edge Computing. IEEE Commun. Mag. 2018, 56, 33–39. [Google Scholar] [CrossRef] [Green Version]
- Feng, Q.; He, D.; Zeadally, S.; Khan, M.K.; Kumar, N. A survey on privacy protection in blockchain system. J. Netw. Comput. Appl. 2018, 13, 45–58. [Google Scholar] [CrossRef]
- Kim, H.W.; Jeong, Y.S. Secure Authentication-Management human-centric Scheme for trusting personal resource information on mobile cloud computing with blockchain. Hum. Centric Comput. Inf. Sci. 2018, 8, 11. [Google Scholar] [CrossRef] [Green Version]
- Vukolić, M. The quest for scalable blockchain fabric: Proof-of-work vs. BFT replication. In International Workshop on Open Problems in Network Security; Springer: Berlin, Germany, 2015. [Google Scholar]
- Conoscenti, M.; Vetro, A.; De Martin, J.C. Blockchain for the Internet of Things: A systematic literature review. In Proceedings of the 2016 IEEE/ACS 13th International Conference of Computer Systems and Applications (AICCSA), Agadir, Morocco, 29 November–2 December 2016. [Google Scholar]
- Satyanarayanan, M. The emergence of edge computing. Computer 2017, 50, 30–39. [Google Scholar] [CrossRef]
- Yang, R.; Yu, F.R.; Si, P.; Yang, Z.; Zhang, Y. Integrated Blockchain and Edge Computing Systems: A Survey, Some Research Issues and Challenges. IEEE Commun. Surv. Tutor. 2019, 21, 1508–1532. [Google Scholar] [CrossRef]
- Meng, W.; Tischhauser, E.W.; Wang, Q.; Wang, Y.; Han, J. When Intrusion Detection Meets Blockchain Technology: A Review. IEEE Access 2018, 6, 10179–10188. [Google Scholar] [CrossRef]
- Samaniego, M.; Deters, R. Blockchain as a Service for IoT. In Proceedings of the 2016 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Chengdu, China, 15–18 December 2016. [Google Scholar]
- Lin, I.C.; Liao, T.C. A Survey of Blockchain Security Issues and Challenges. IJ Netw. Secur. 2017, 19, 653–659. [Google Scholar]
- Wüst, K.; Gervais, A. Do you need a Blockchain? In Proceedings of the 2018 Crypto Valley Conference on Blockchain Technology (CVCBT), Zug, Switzerland, 20–22 June 2018. [Google Scholar]
- Brickell, E.; Li, J. Enhanced privacy ID: A direct anonymous attestation scheme with enhanced revocation capabilities. In Proceedings of the 2007 ACM Workshop on Privacy in Electronic Society, Alexandria, VA, USA, 29 October 2007. [Google Scholar]
- Jiao, Y.; Wang, P.; Niyato, D.; Xiong, Z. Social welfare maximization auction in edge computing resource allocation for mobile blockchain. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Beijing, China, 16–18 August 2018. [Google Scholar]
- Yu, W.; Liang, F.; He, X.; Hatcher, W.G.; Lu, C.; Lin, J.; Yang, X. A Survey on the Edge Computing for the Internet of Things. IEEE Access 2018, 6, 6900–6919. [Google Scholar] [CrossRef]
- Khan, M.A.; Salah, K. IoT security: Review, blockchain solutions, and open challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- Shafagh, H.; Hithnawi, A.; Burkhalter, L.; Fischli, P.; Duquennoy, S. Secure sharing of partially homomorphic encrypted iot data. In Proceedings of the 15th ACM Conference on Embedded Network Sensor Systems, Delft, The Netherlands, 6–8 November 2017. [Google Scholar]
- Hummen, R.; Shafagh, H.; Raza, S.; Voig, T.; Wehrle, K. Delegation-based Authentication and Authorization for the IP-based Internet of Things. In Proceedings of the 2014 Eleventh Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), Singapore, 30 June–3 July 2014. [Google Scholar]
- Hu, Y.C.; Patel, M.; Sabella, D.; Sprecher, N.; Young, V. Mobile edge computing—A key technology towards 5G. ETSI White Pap. 2015, 11, 1–16. [Google Scholar]
- Jararweh, Y.; Doulat, A.; AlQudah, O.; Ahmed, E.; Al-Ayyoub, M.; Benkhelifa, E. The future of mobile cloud computing: Integrating cloudlets and mobile edge computing. In Proceedings of the 2016 23rd International Conference on Telecommunications (ICT), Thessaloniki, Greece, 16–18 May 2016. [Google Scholar]
- Abbas, N.; Zhang, Y.; Taherkordi, A.; Skeie, T. Mobile edge computing: A survey. IEEE Int. Things J. 2018, 5, 450–465. [Google Scholar] [CrossRef]
- Aijaz, A.; Dohler, M.; Aghvami, A.H.; Friderikos, V.; Frodigh, M. Realizing the Tactile Internet: Haptic Communications over Next Generation 5G Cellular Networks. IEEE Wirel. Commun. 2017, 24, 2–9. [Google Scholar] [CrossRef]
- Liu, M.; Yu, F.R.; Teng, Y.; Leung, V.C.M.; Song, M. Distributed Resource Allocation in Blockchain-Based Video Streaming Systems With Mobile Edge Computing. IEEE Trans. Wirel. Commun. 2019, 18, 695–708. [Google Scholar] [CrossRef]
- Eyal, I.; Gencer, A.E.; Sirer, E.G.; Van Renesse, R. Bitcoin-ng: A scalable blockchain protocol. In Proceedings of the 13th {USENIX} Symposium on Networked Systems Design and Implementation ({NSDI} 16), Santa Clara, CA, USA, 16–18 March 2016. [Google Scholar]
- Kasireddy, P. Blockchains don’t Scale. Not Today, at Least. But there’s Hope. 2017. Available online: https://hackernoon.com/blockchains-dont-scale-not-today-at-least-but-there-s-hope-2cb43946551a (accessed on 19 May 2019).
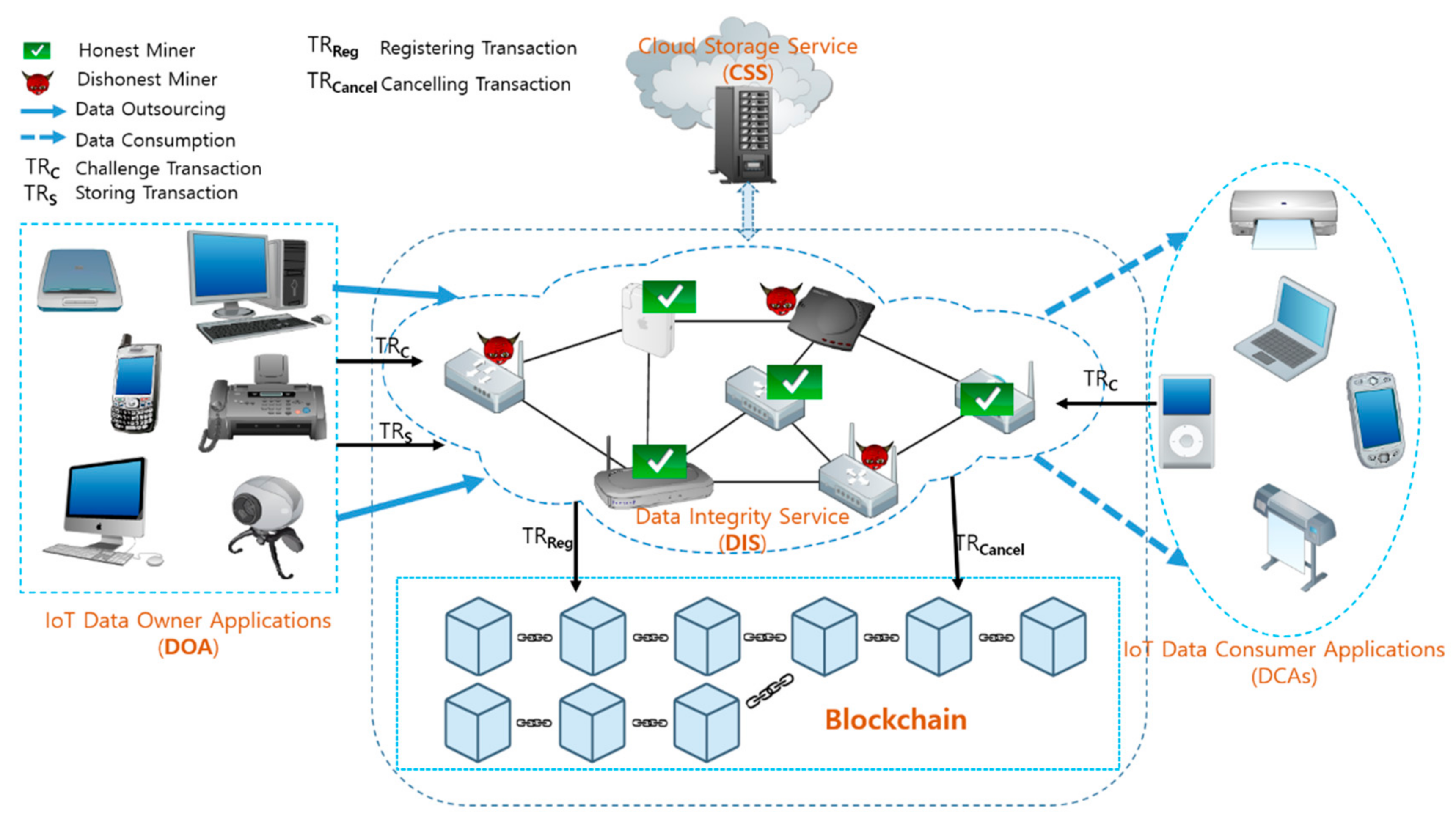
- Liu, B.; Yu, X.L.; Chen, S.; Xu, X.; Zhu, L. Blockchain based data integrity service framework for IoT data. In Proceedings of the 2017 IEEE International Conference on Web Services (ICWS), Honolulu, HI, USA, 25–30 June 2017. [Google Scholar]
- Miers, I.; Garman, C.; Green, M.; Rubin, A.D. Zerocoin: Anonymous distributed e-cash from bitcoin. In Proceedings of the 2013 IEEE Symposium on Security and Privacy, Berkeley, CA, USA, 19–22 May 2013. [Google Scholar]
- Sasson, E.B.; Chiesa, A.; Garman, C.; Green, M.; Miers, I.; Tromer, E.; Virza, M. Zerocash: Decentralized anonymous payments from bitcoin. In Proceedings of the 2014 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 18–21 May 2014. [Google Scholar]
- Yeow, K.; Gani, A.; Ahmad, R.W.; Rodrigues, J.J.; Ko, K. Decentralized consensus for edge-centric internet of things: A review, taxonomy, and research issues. IEEE Access 2017, 6, 1513–1524. [Google Scholar] [CrossRef]
- Yu, Y.; Li, Y.; Tian, J.; Liu, J. Blockchain-Based Solutions to Security and Privacy Issues in the Internet of Things. IEEE Wirel. Commun. 2018, 25, 12–18. [Google Scholar] [CrossRef]
- Möser, M.; Böhme, R.; Breuker, D. An inquiry into money laundering tools in the Bitcoin ecosystem. In Proceedings of the 2013 APWG eCrime Researchers Summit, San Francisco, CA, USA, 17–18 September 2013. [Google Scholar]
- Koshy, P.; Koshy, D.; McDaniel, P. An analysis of anonymity in bitcoin using p2p network traffic. In International Conference on Financial Cryptography and Data Security; Springer: Berlin, Germany, 2014. [Google Scholar]
- Valenta, L.; Rowan, B. Blindcoin: Blinded, accountable mixes for bitcoin. In International Conference on Financial Cryptography and Data Security; Springer: Berlin, Germany, 2015. [Google Scholar]
- Wörner, D.; Von Bomhard, T. When your sensor earns money: Exchanging data for cash with Bitcoin. In Proceedings of the 2014 ACM International Joint Conference on Pervasive and Ubiquitous Computing: Adjunct Publication, Seattle, WA, USA, 13–17 September 2014. [Google Scholar]
- Zyskind, G.; Nathan, O.; Pentland, A. Enigma: Decentralized Computation Platform with Guaranteed Privacy. arXiv 2015, arXiv:1506.03471. [Google Scholar]
- Poon, J.; Dryja, T. The Bitcoin Lightning Network: Scalable Off-Chain Instant Payments, Draft Version 0.5; 2015. Available online: http://www.bitcoinlightning.com (accessed on 19 May 2019).
- Sharma, P.K.; Chen, M.Y.; Park, H.J. A software defined fog node based distributed blockchain cloud architecture for IoT. IEEE Access 2018, 6, 115–124. [Google Scholar] [CrossRef]
- Salahuddin, M.A.; Al-Fuqaha, A.; Guizani, M.; Shuaib, K.; Sallabi, F. Softwarization of Internet of Things Infrastructure for Secure and Smart Healthcare. arXiv 2018, arXiv:1805.11011. [Google Scholar] [CrossRef]
- Samaniego, M.; Deters, R. Virtual resources & blockchain for configuration management in IoT. J. Ubiquitous Syst. Pervasive Netw. 2017, 9, 1–13. [Google Scholar]
- Liu, K.J.; Wei, K.V.; Wong, S.D. Linkable spontaneous anonymous group signature for ad hoc groups. In Australasian Conference on Information Security and Privacy; Springer: Berlin, Germany, 2004. [Google Scholar]
- Wang, L.; Zhang, G.; Ma, C. A survey of ring signature. Front. Electr. Electron. Eng. China 2008, 3, 10–19. [Google Scholar] [CrossRef]
- Rivest, R.L.; Shamir, A.; Tauman, Y. How to leak a secret. In International Conference on the Theory and Application of Cryptology and Information Security; Springer: Berlin, Germany, 2001. [Google Scholar]
| Target Requirement | Fulfillment in the Framework |
|---|---|
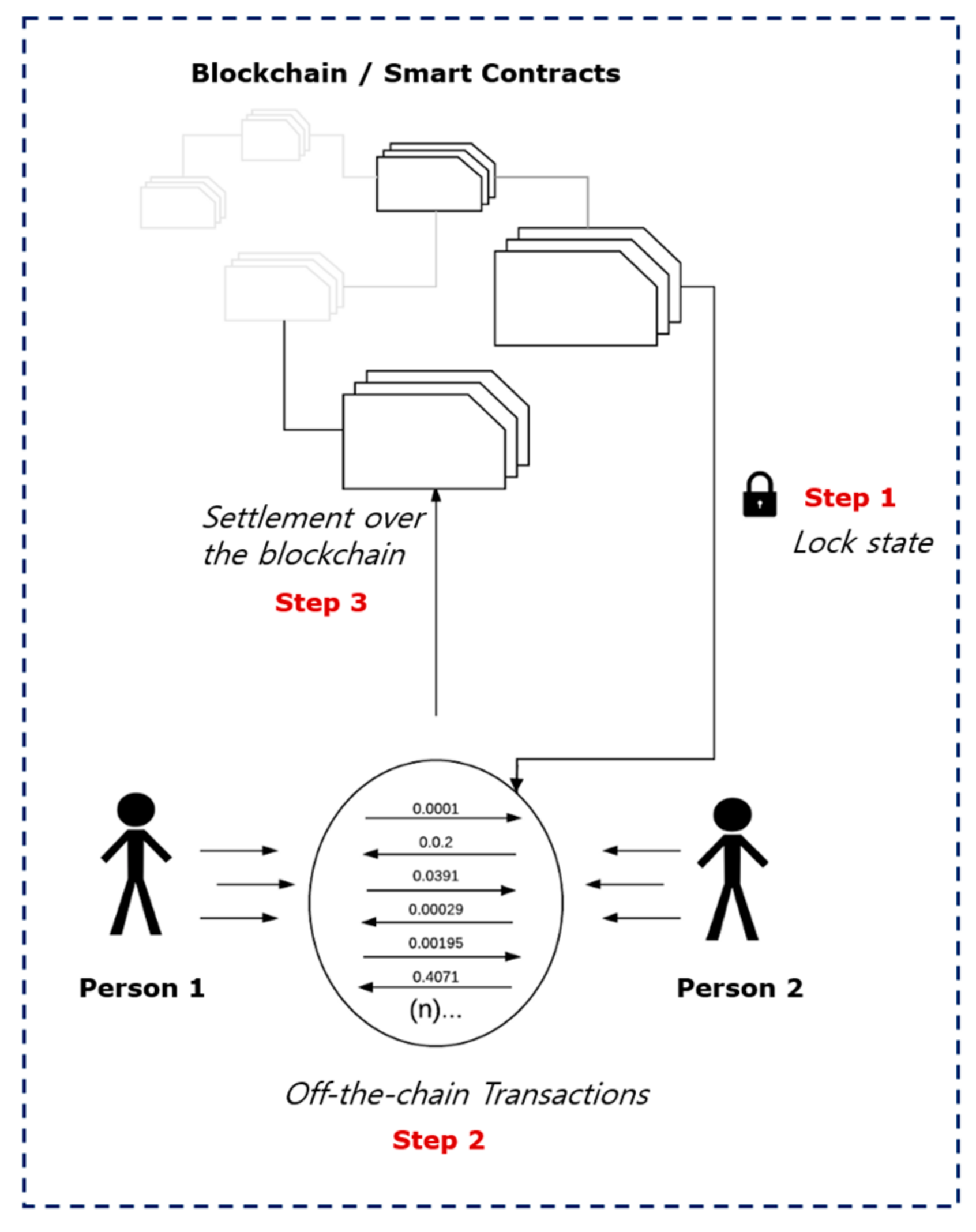
| Offloaded Computation | Through the use of off-chain state channels implemented by raiden networks, complex and heavy computational loads are relieved from IoT devices onto powerful servers at the edge. |
| Decentralized Data Storage | By utilization of the data integrity service (DIS) and the off-chain state channels, secure and large storage capacities are obtained through blockchain and edge computing and data is managed in P2P basis without entrusting to any centralized authority. |
| Authenticated Transactions | To ensure validity of transactions in the system, nodes are required to solve a predefined challenge as set in the smart contracts of the DIS when storing the transactions. A transaction is valid only when the computed proof for the issued challenge is verified by users. |
| Controlled Access | Through the use of private and public key pairs generated for data owners and consumers when being registered in the DIS, nodes’ accounts are identified by the public keys whose access is governed by the corresponding private keys. This ensures controlled access to the stored data in the system. |
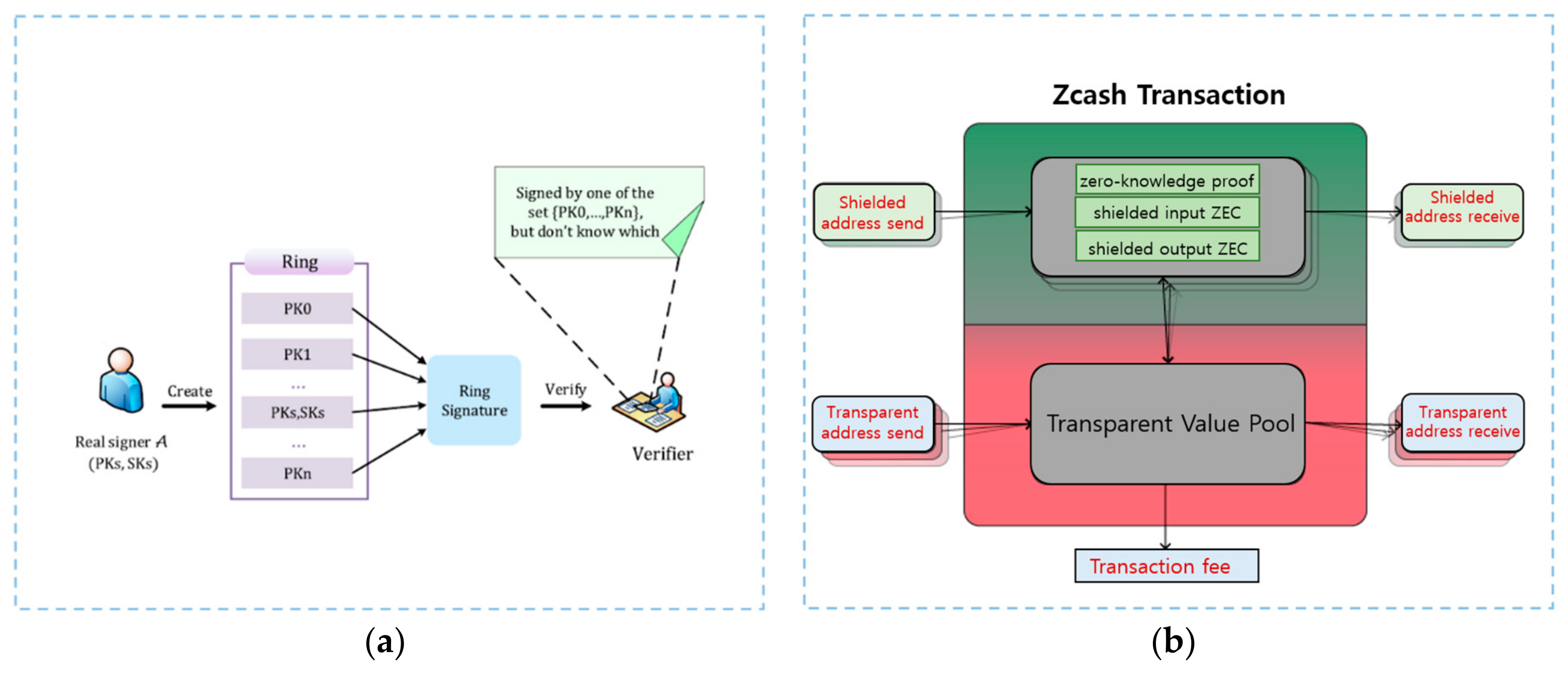
| Anonymity | A hybrid of cryptographic mechanisms in such tools as linkable ring signatures, zerocoin and zerocash are utilized in achieving stronger anonymity of transactions beyond the pseudonyms in blockchain in ensuring privacy of users and their respective data. |
| Integrity of Data | By the use of incentive and punishment schemes enforced through smart contracts to data owners and consumers in the DIS, integrity is guaranteed for IoT devices to outsource their data to be decentrally kept in a P2P storage. |
| Low Latency | Fast responses (hence low delays) to IoT applications through deployment of edge servers at the edge of the network closer to end devices. |
| Adaptability | Enhanced ability to scale in the scheme through the off-chain state channels availed by the use of Lightning or Raiden networks to allow future growth of more devices and massive transactions. |
| Serial # | Item Name | Item Description |
|---|---|---|
| 1 | Android Mobile Devices | End nodes on which IoT applications run. |
| 2 | Edge Computing Server | A powerful server to host offloaded tasks. |
| 3 | Wireless Access Point | A network hub to provide connectivity between devices. |
| 4 | Microsoft Azure Cloud | Provision of cloud services. |
| 5 | TestRPC | Simulation of Ethereum blockchain. |
| 6 | Truffle | Framework for development of smart contracts. |
| 7 | MetaMask | Ethereum client for web browser. |
| 8 | web3 API | Ethereum JavaScript API. |
| 9 | npm | JavaScript’s Node Package Manager. |
| 10 | Node.js | JavaScript’s run-time environment. |
| 11 | Data integrity service | Smart contracts-based framework for data integrity. |
| 12 | Raiden network | Ethereum extension to provide off-chain scaling. |
| 13 | Linkable ring signatures | A digital signature scheme to verify anonymous message signer. |
| 14 | Zerocash | A cryptocurrency to enable selective transparency of transactions. |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nyamtiga, B.W.; Sicato, J.C.S.; Rathore, S.; Sung, Y.; Park, J.H. Blockchain-Based Secure Storage Management with Edge Computing for IoT. Electronics 2019, 8, 828. https://doi.org/10.3390/electronics8080828
Nyamtiga BW, Sicato JCS, Rathore S, Sung Y, Park JH. Blockchain-Based Secure Storage Management with Edge Computing for IoT. Electronics. 2019; 8(8):828. https://doi.org/10.3390/electronics8080828
Chicago/Turabian StyleNyamtiga, Baraka William, Jose Costa Sapalo Sicato, Shailendra Rathore, Yunsick Sung, and Jong Hyuk Park. 2019. "Blockchain-Based Secure Storage Management with Edge Computing for IoT" Electronics 8, no. 8: 828. https://doi.org/10.3390/electronics8080828
APA StyleNyamtiga, B. W., Sicato, J. C. S., Rathore, S., Sung, Y., & Park, J. H. (2019). Blockchain-Based Secure Storage Management with Edge Computing for IoT. Electronics, 8(8), 828. https://doi.org/10.3390/electronics8080828





_Park.png)

