1. Introduction
The Internet of things (IoT) era—in which various objects are connected through information and communication technology to collect, share, and process information—has emerged. IoT provides a more convenient environment by enabling various devices to communicate and share information with each other without human intervention [
1]. IoT technology is developing rapidly every year and many companies and countries are making huge efforts toward vitalizing IoT. The International Data Corporation estimates that the global IoT market will achieve 15% year-on-year growth reaching
$745 billion in 2019 and exceeding
$1 trillion by 2022 [
2,
3]. However, hacking and cyber attacks targeting IoT devices are increasing every year and, as most of them are lightweight, low-power, and low-performance devices, it is difficult to apply security methods adopted for traditional PCs to IoT devices, thus making them vulnerable to cyber attacks [
4,
5]. As IoT devices collect and process various types of information including personal and sensitive information in everyday life, if IoT devices with vulnerabilities are exposed to such security threats, it can infringe on personal information, cause financial loss, and even threaten human life. If IoT security issues are not properly addressed, a hyper-connected society in which 5G technology is commercially available and everything is connected along with smart cities, smart factories, and smart cars becomes remote. As a solution to these issues, the convergence of blockchain technology and IoT has drawn attention [
6]. In this study, we investigate the blockchain using technology that can securely and automatically extend IoT devices by considering security when authenticating them. In addition, we design a mechanism that evaluates the security of devices by using the whitelist, which first defines the list of safety-proven software and then restricts things beyond the list [
7,
8]. Accordingly, the proposed model enables IoT devices to verify security automatically by using blockchain and smart contract technology; thus, they can be securely and automatically extended. Further, we ensure that secure extension is available by proposing a method that imposes a penalty on connection extension for low-security devices based on the security of the devices recorded in the blockchain.
The remainder of the paper is organized as follows.
Section 2 describes the background and related works on the IoT connectivity tehchnologies and authentication methods.
Section 3 analyzes limitations of IoT authentication for secure scalability.
Section 4 present the proposed scheme for scalable and secure IoT connectivity.
Section 5 describes the performance evaluation results. Finally,
Section 6 draws conclusions.
3. Limitations of IoT Authentication for Secure Scalability
The authentication methods of traditional IoT devices mainly confirm and verify their legitimacy and integrity. However, they require user or server intervention and do not consider the security level of devices at the time of determining their extension. Attackers can easily bypass ID/PW-based and MAC address-based authentication methods, and the encryption algorithm-based, challenge response-based, and OTP-based authentication methods are not suitable for low-performance IoT devices [
34]. Security verification for maintaining the security of IoT devices is time consuming and expensive, and the need for intervention by specialists or accredited agencies rather than by general users reduces its efficiency [
35]. Moreover, there are no security authentication and evaluation systems that satisfy the characteristics of IoT devices legally and institutionally but are only authentication and evaluation systems for each product in most cases. If IoT device’s security validation is performed through a smart contract, verification can be relied on without third party intervention. It is also convenient to check the integrity of the white list or the security information of the device and can provide compensation for security maintenance in cryptocurrency. Therefore, there is an urgent need for technology to verify security for known malicious code and security vulnerabilities, and to evaluate the security of IoT devices continuously and securely extend them. For an IoT environment development, a technical solution that can interoperate IoT devices securely and promptly by automatically analyzing security vulnerabilities and verifying security should be provided. Therefore, in this study, we automatically verify and evaluate the security of IoT devices and then record it in the blockchain and propose a method to extend them securely by automating authentication and connection between devices accordingly.
By setting the security level required for IoT devices at the time of authenticating and connecting them, only the devices that satisfy a certain security level are allowed to be connected automatically while connection to devices with low security is restricted, thus inducing manufacturers to maintain security through patches and updates. By determining whether there are some security vulnerabilities of target devices, devices are automatically connected, and the connection is completed after verifying whether the security of the connected devices is suitable, thus ensuring secure interoperability between IoT devices.
4. Scalable and Secure Internet of Things Connectivity
IoT usage can be divided into two types. One is to offer user-centered entertainment and various services by installing applications according to users’ convenience and preferences, such as smartphones and smart TVs. The other is to network the social infrastructure and environment such as smart grid, smart city, and smart home. IoT devices can be hacked owing to various vulnerabilities, but malicious programs installed by the user’s carelessness or by hackers’ attacks account for the most frequent infiltration routes [
36]. IoT devices infected with malicious programs such as Trojan viruses, ransomware, and rootkits as well as IoT devices on the connected networks are at high risk of being exposed to attacks. In the upcoming IoT era, a single object will be dynamically connected with surrounding objects in a distributed ad-hoc network. A secure and scalable IoT connection method is required in this environment.
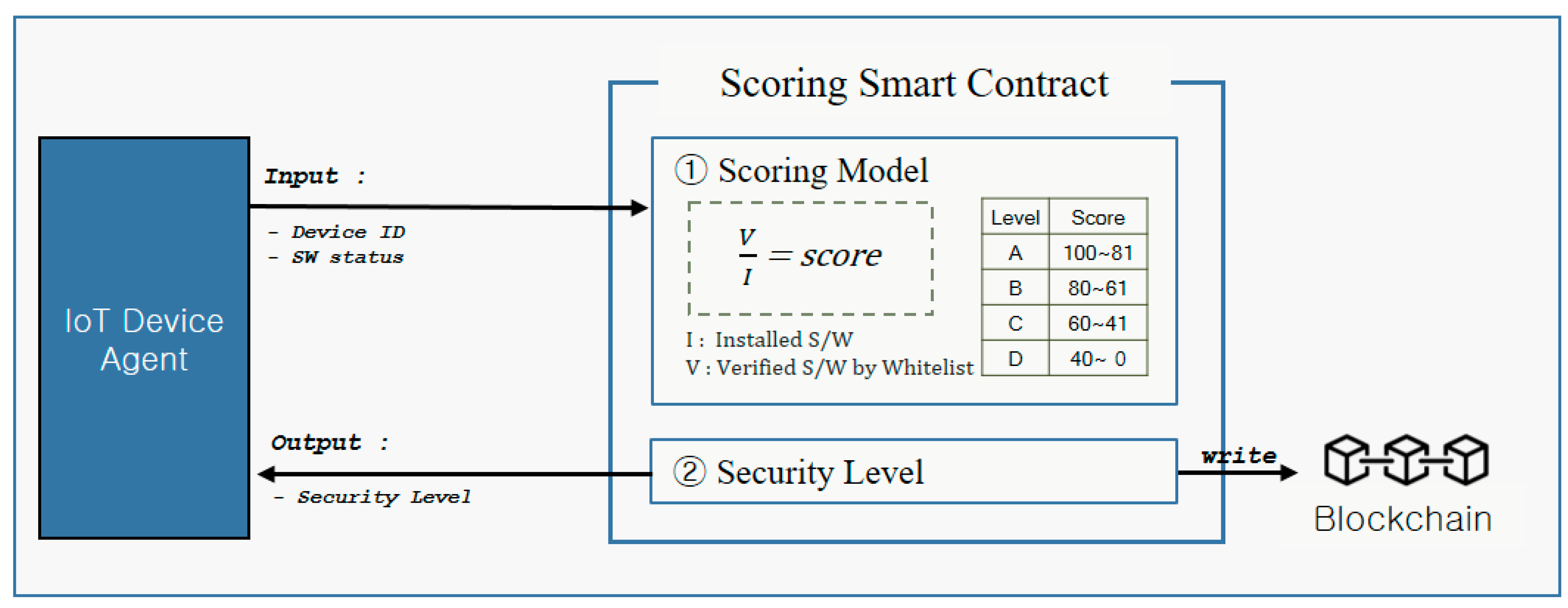
For automated authentication and extension of IoT devices, there must be a trust on the security level and the security evaluation system of IoT devices. The method proposed in this paper evaluates the security level based on the verification of software installed in IoT devices using the whitelist and records it in the blockchain through the smart contract. Assuming that IoT devices adopt an Agent stored in a secure area that is resilient against physical tampering, reverse engineering or compromising by malicious softwares,
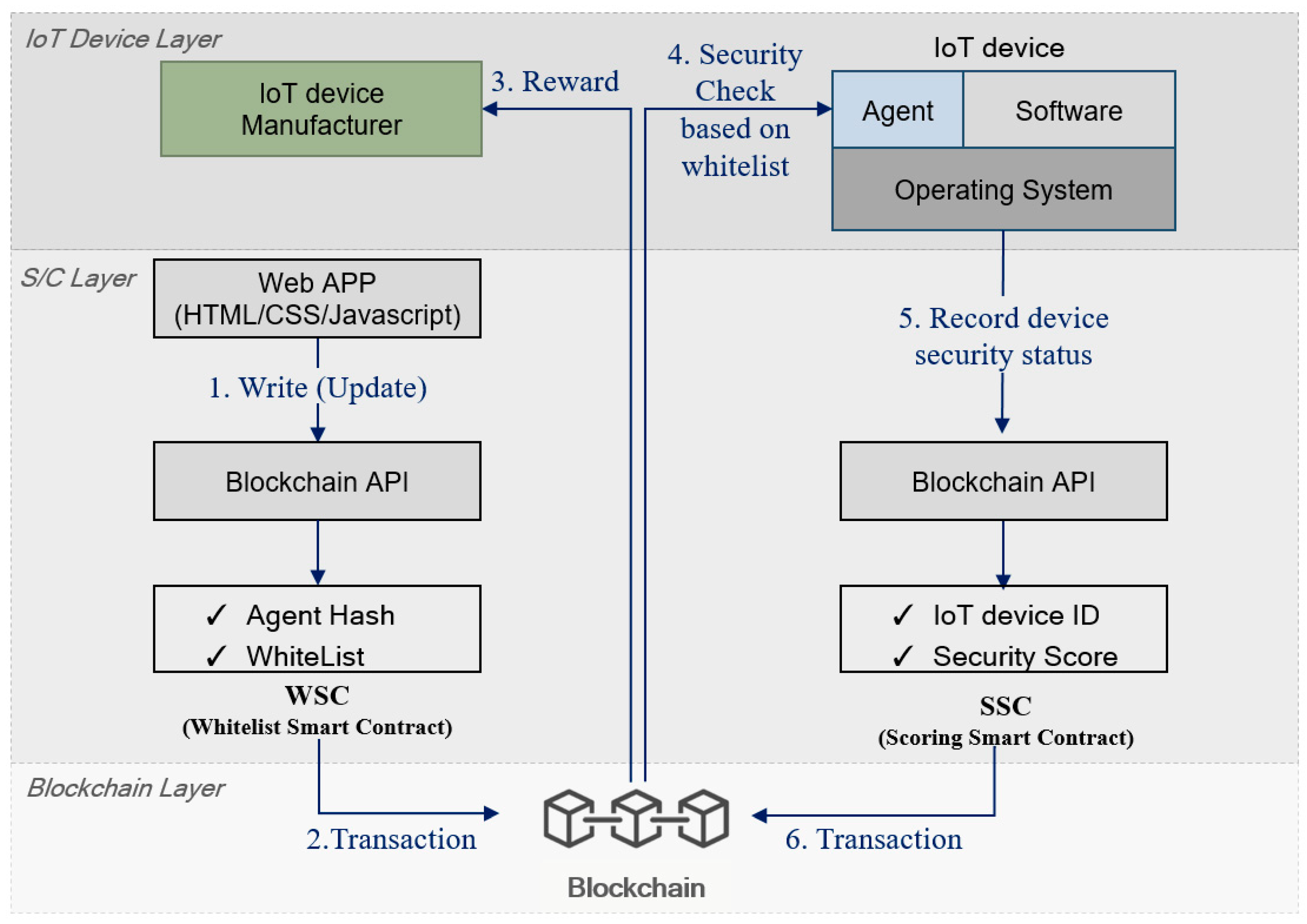
Figure 1 shows the system configuration for evaluating the security of IoT devices, which is described in the following steps.
Step 1: IoT device manufacturers verify software to be installed on IoT devices in advance and prepare the whitelist. IoT devices of the same type can have the same whitelist and have the whitelist that satisfies the required conditions for each IoT environment. A smart contract is created by including the whitelist prepared by manufacturers and the initial agent hash value (IAHV) of the agent embedded in an IoT device. IoT device manufacturers can access smart contract through Decentralized Applications (dApps), such as web pages. Internally, they can easily access the blockchain through an Application Programming Interface (API). IoT device manufacturers constantly update White List via smart contract.
Step 2: Manufacturers record the whitelist and the IAHV of the agent embedded in an IoT device in the blockchain through the whitelist smart contract (WSC). The IoT device can verify that the IAHV of the agent matches the device agent hash value (DAHV) of the installed agent by inquiring the information recorded in the blockchain through the WSC. It verifies that the agent has not been forged or falsified by comparing it with the agent hash value stored in the blockchain; thus, the security evaluation process of IoT devices through the agent can be reliable.
Step 3: Manufacturers are rewarded with tokens whenever they create and update the WSC.
Step 4: Based on the agent information of the device and the whitelist recorded in the blockchain through the WSC, the agent of the IoT device checks whether unverified programs are installed. At this time, the smart contract approaches the most up-to-date state, so IoT device will see the most recent White List.
Step 5: The security status of the IoT device evaluated by the agent is transmitted to the scoring smart contract (SSC) along with the unique identification information of the device and the security level of the device is set through the internal function. When the SSC is used, the agent hash value of the device is checked to verify the integrity.
Step 6: The unique identification information and security level of the device are recorded into the blockchain through the SSC and the security level of the device recorded in the blockchain can be inquired when it is connected to other devices.
The light and secure authentication is an essential and important for IoTs, especially when IoTs are dealing with an immense number of devices. One of the state-of-the-art solutions for IoTs is a Physical Unclonable Function (PUF)-based authentication [
37,
38]. PUFs are digital fingerprints of IoTs which utilize the physical disorder of random nanoscale phenomena. A PUF is unique to each IoT which cannot be reverse engineered. Therefore, PUF can provide unique identifiers and keys to help secure the massive number of devices found in IoT networks. Thus, the PUF can effectively support IoT authentication. In this research, we assume that an initial state of IoT devices is a ‘pure’ state which is not contaminated from malicious software because they operate on the verified softwares made by manufacturers. The ‘pure’ IoT devices can securely connect to others by an authentication technology. However, if a malicious software contaminates an IoT device, the ‘contaminated’ IoT device may affect to neighbor IoTs in the network because the conventional authentication cannot detect the contaminated state and prevent from propagating it to others.
Based on this technical background, blockchain can serve as a data store for the hashes of public key certificates of IoT devices. The private keys are stored on the devices themselves assuming that the private keys are PUFs or the keys are stored in the secure zone that are resilient against physical tampering because IoT devices are often used in public locations. In this paper, based on the aforementioned authentication, the proposed scheme provides additional criteria for secure connection and scalability. That is the whitelist/scoring smart contract for device integrity check.
The proposed security evaluation system checks the security of an IoT device twice by first verifying the integrity of the agent installed in the device and then verifying the integrity of the software one more time through the verified agent. The security status verified by the agent is graded as security levels through the smart contract, which is recorded in the blockchain. Based on the recording in the blockchain, the IoT device can be extended safely and quickly when connected to other devices. If device users do not prepare the whitelist or do not update periodically, they will not be rewarded, and the scalability of devices will be reduced. Through this concept of penalty, the security of devices can be steadily maintained, and manufacturers and users can continue to maintain the security of devices to ensure a secure IoT ecosystem.
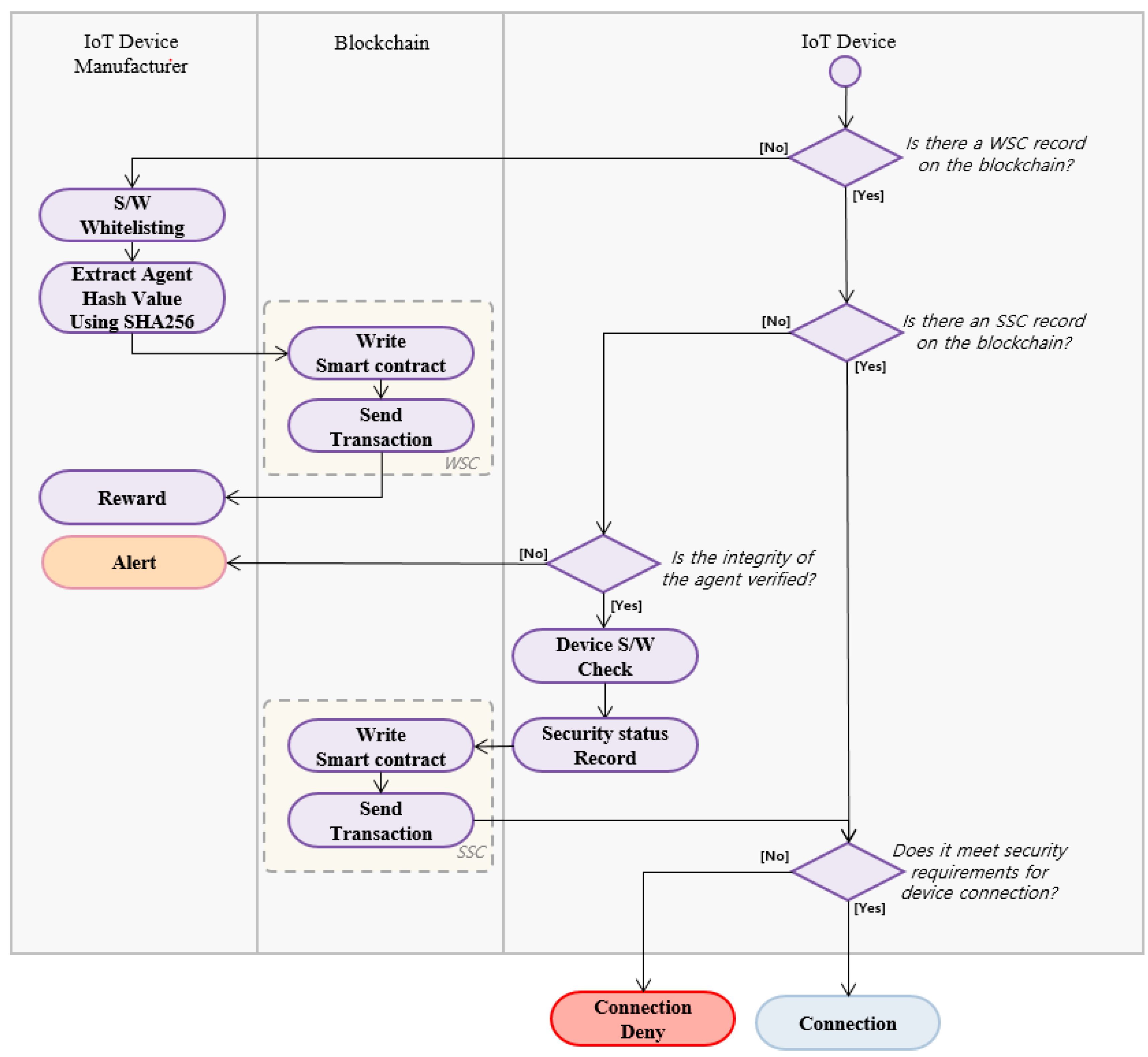
Figure 2 shows the overall flow of the proposed model. First, an IoT device checks whether whitelisting information on the hash value of software for which security is verified through the WSC and the hash value of the agent were recorded. If there is no record, the IoT device records them in the blockchain by requesting them from the manufacturer. The manufacturer records the hash value of the initial IoT device software as a sha256 function. If they are recorded in the blockchain through the WSC, the manufacturer is rewarded. If the record of the WSC exists, it checks whether there is a record scoring the security of the IoT device through the SSC. If the information recorded in the blockchain through the SSC exists, it attempts to connect to other devices based on this information. A connection is not made if the security level required by the device is not satisfied. If there is no information recorded through the SSC, an integrity verification process is performed in advance to record the security level of the IoT device. If the agent is detected to be forged or falsified, it is alerted to the manufacturer with a request for an update. If the integrity of the agent is verified, the security of the device is evaluated and recorded in the blockchain through the SSC.
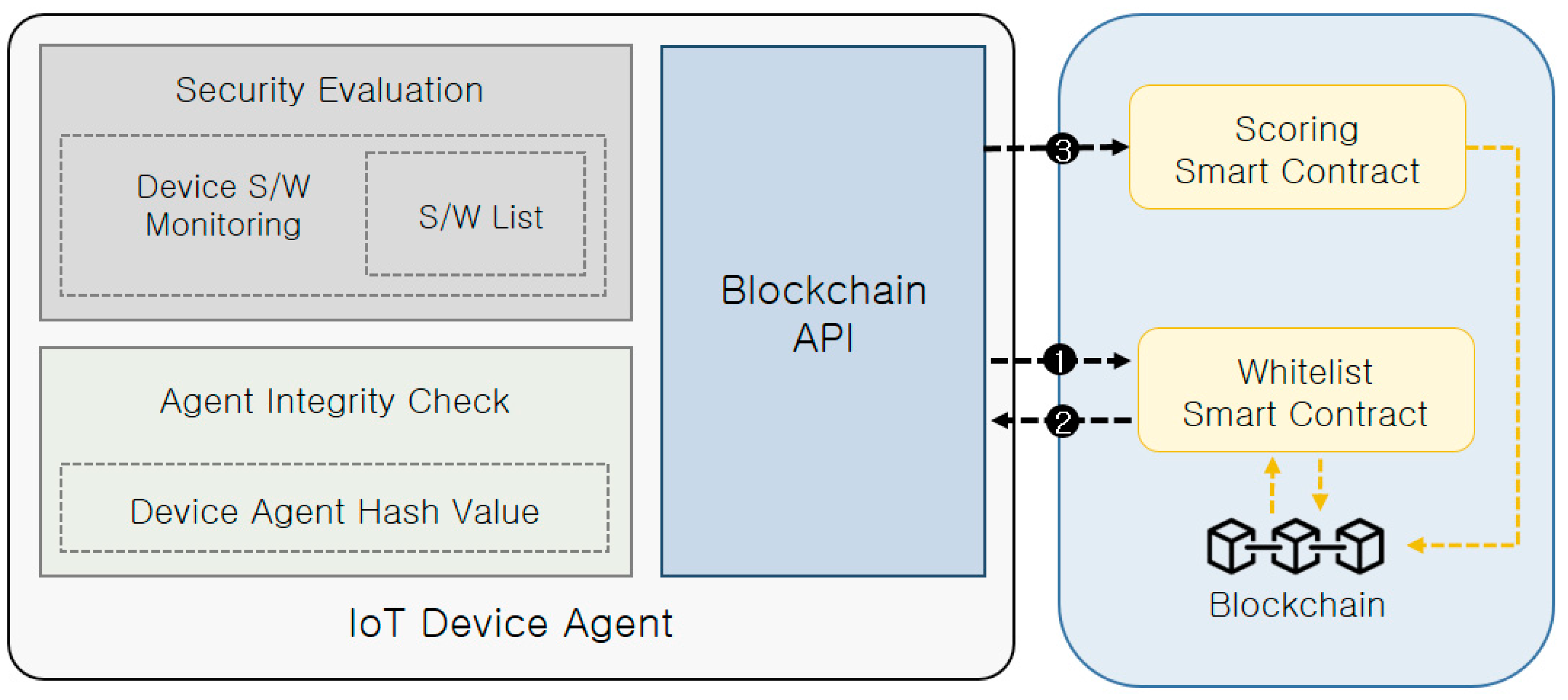
Figure 3 shows the structure of the agent. The agent embedded in the IoT device serves to evaluate the security of the device. Therefore, the integrity verification for the agent should be performed in advance for the evaluation of device security. Agent Integrity Check manages the DAHV and compares it with the hash value recorded in the blockchain. This ensures the integrity of the agent. The blockchain API of the agent serves to record information in the blockchain or retrieve the recorded information using the smart contract. If the security of the IoT device is evaluated and then recorded in the blockchain, everyone can directly have access to it. However, the initial IAHV of the device and the whitelist recorded in the block are only accessible through the smart contract. Security Evaluation is responsible for comparing the software installed on the device through Device S/W Monitoring with the verified software recorded in the whitelist, and it calculates the security level by transmitting the verified and unverified software information to the SSC. The process of accessing the blockchain through the smart contract using the blockchain API inside the agent is as follows.
The WSC checks the information of the corresponding device and the DAHV verified through the agent integrity check.
The WSC checks whether the DAHV matches the IAHV of the device recorded in the blockchain and transmits the whitelist to the agent.
The lists of the verified and unverified software through Security Evaluation are transmitted to the SSC along with the device identification value.
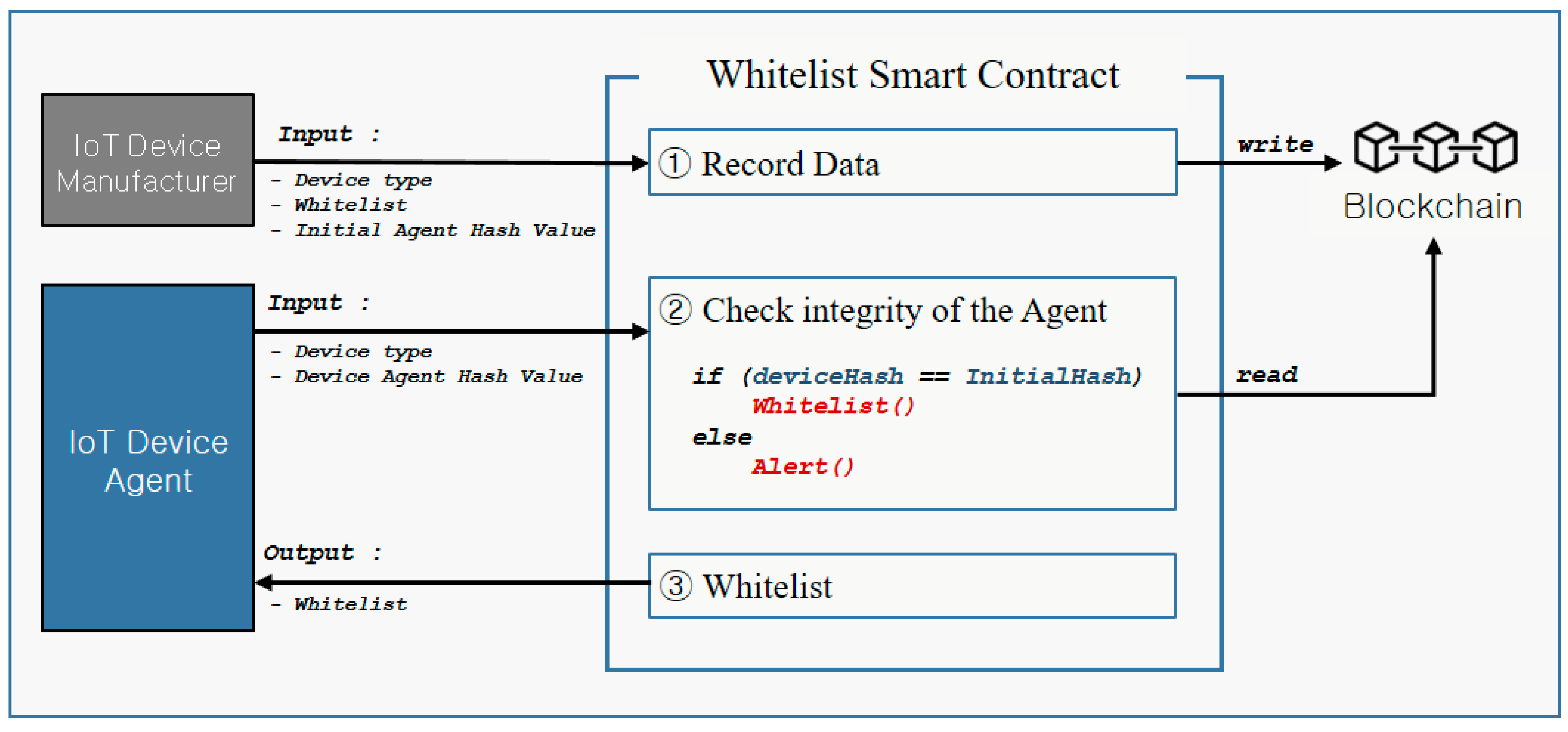
Figure 4 shows the WSC. The WSC receives the whitelist including the information of each device and the IAHV from the manufacturer and records them in the blockchain. If data recorded in the block through the WSC from the manufacturer exist, the WSC can be used through the agent of the IoT device. First, the WSC verifies the integrity by comparing the IAHV of the IoT device with the current hash value of the device. If the IAHV does not match the hash value recorded in the block, it sends an alert message to the device and the manufacturer. If the integrity of the agent is verified, the list for software whitelist of the IoT device recorded in the blockchain is transmitted to the IoT device. The agent makes a list of verified and unverified software through Security Evaluation using the transmitted information and transmits it to the SSC.
Figure 5 illustrates the SSC. The SSC sets the security score of a device based on the software installed on the device and the list of verified software through the agent and sets the security level based on the security score. The security level set through the SSC is recorded in the blockchain along with the device information. The security level is recorded in the IoT device, which can be used to connect to other devices. The integrity can be verified by comparing it with the security level recorded in the blockchain. The security level can be set to a device, which can be used for IoT environments and applications at the time of authenticating and extending the device. The lower the security level of a device is, the more it is restricted to extension. It can be designed to extend proportionally with the security level. For medical IoT device for which security is critical, connections to devices other than Level A can be restricted. If the security score is lowered and the security level of the device changes, a connection is restricted, and the user is notified through the smart contract.
5. Performance Evaluation
Most authentication methods of traditional IoT devices check whether devices are legitimate by testing the existence of a key. However, this authentication method does not consider security when extending the network and requires user intervention. Therefore, we designed a reliable security evaluation system by automatically verifying security using the whitelist and the smart contract and then recording it in the blockchain.
As IoT devices are used in various fields, security and scalability required by each field are also varied. Therefore, the proposed model ensures maximum scalability when security is high, and restricts scalability when security is low. In this study, we compare the proposed method with the conventional authentication method [
39,
40] using a network simulation model.
5.1. Evaluation Method
We implemented an abstraction model to evaluate the performance of the proposed model. For network simulation, 200 IoT device nodes were randomly arranged and placed on a 30 × 30 two-dimensional planes. After setting the location information of each IoT device, the devices were allowed to perform connection with only devices capable of physically communicating. The security score is assumed to be recorded in the blockchain through the agent and the smart contract. The security score was set to all 200 nodes and the security level was properly assigned to them as the level A, B, C, and D. Four malicious nodes infected with viruses were also set (two Cs and two Ds). In addition, in order to evaluate security, for the level A node in which the installed software is thoroughly verified, the integrity of all software is verified so that it is set not to be infected by viruses even though it is connected to malicious devices. If it is installed with unverified software, it is set to be infected with viruses even for a simple connection. In addition, when IoT devices were in use, an unproven malicious software would have a significant impact on security. Therefore, based on the assumption that unverified software, i.e., new software that does not exist in the whitelist, is installed after a certain period of time when IoT devices are in use, the security score is set to randomly drop from 10 to 19 points with a probability of 1/50 when 200 nodes make a single connection within the range. The proposed model sets the security score and level according to the number of unverified software. The lower the level is, the more it is restricted to extension.
Table 2 shows security scores and levels according to the number of unverified software. The proposed model offers different connection ranges depending on the level and it is possible to connect only to devices of the same level among all the devices within the connection range. In contrast, the comparative model (i.e., conventional model) is set to extend IoT devices to all the devices within the connection range regardless of the security of devices.
The proposed model checks whether new software has been installed or unverified software is present through the WSC agent, and the security level is given through the SSC. It is extended depending on the security level. If other IoT devices are within the connection range but connection to them fails owing to low security, it requests for the whitelist update.
If the failure of connection to devices within the connection range is continuously accumulated, the whitelist is updated to verify software and the security score is set to increase from 10 to 19 points randomly. In addition, when viruses are removed by the whitelist update, it is set to improve scalability by increasing the security score. However, there is a case where software has not been verified despite the whitelist update and there are other vulnerabilities although a single vulnerability is improved. To consider these realistic factors, we set different score increase criteria by each security level. The basic update period of the whitelist is determined depending on the cumulative number of connection failures and the update period for the level A device is the same as the basic update cycle.
Table 3 shows the criteria for score increase by each level according to the whitelist update cycle. As the level decreases, it has 2, 3, or 4 times of the basic update period as the score increase criteria.
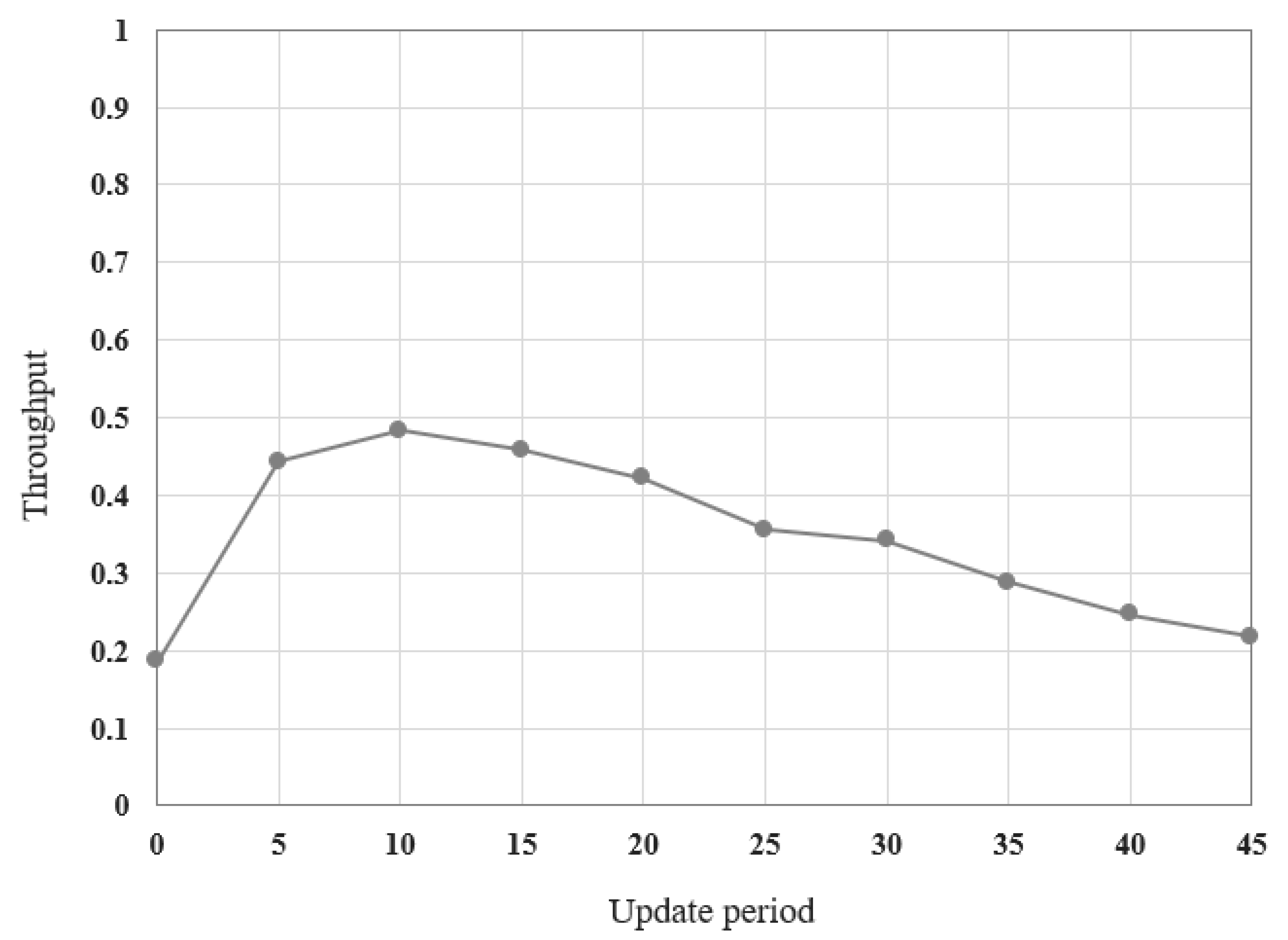
As scalability and security results can vary for the proposed model according to the whitelist update period, a value with the highest network throughput was set as the basic value of the update period to have an appropriate value.
Figure 6 shows the throughput simulation results according to the update period. Throughput is the result of the successfully transmitted data size divided by the data transmission time as described in Equation (1).
As the overhead required for sending data increases, throughput is reduced owing to the increased transmission time. In contrast, throughput increases as overhead decreases. IoT devices with excellent scalability can send data to destinations promptly and efficiently, resulting in improved throughput. The restricted connection will reduce throughput. Simulation results demonstrate that the packet overhead for updating is reduced as the update period becomes longer; thus, the network throughput is improved. However, throughput is improved only when the update period increases to a certain level. Network scalability is restricted when the update period is set to be excessively long, resulting in the decrease in throughput. Therefore, based on the simulation results, the basic update period was set to 10 times as the highest throughput was achieved when 10 connection failures were accumulated and then the whitelist was updated. In this study, as the provided updating period is different depending on the applications and requirements of IoT devices, we also evaluated 0.5 and 1.5 times of the basic period along with the comparative model.
Table 3 shows the criteria for score increase by each level according to the whitelist update period. The value of the update period evaluated in the proposed model is divided into 5, 10, and 15, which is the basic period and 0.5 and 1.5 times of the basic period, respectively.
5.2. Evaluation Results and Analysis
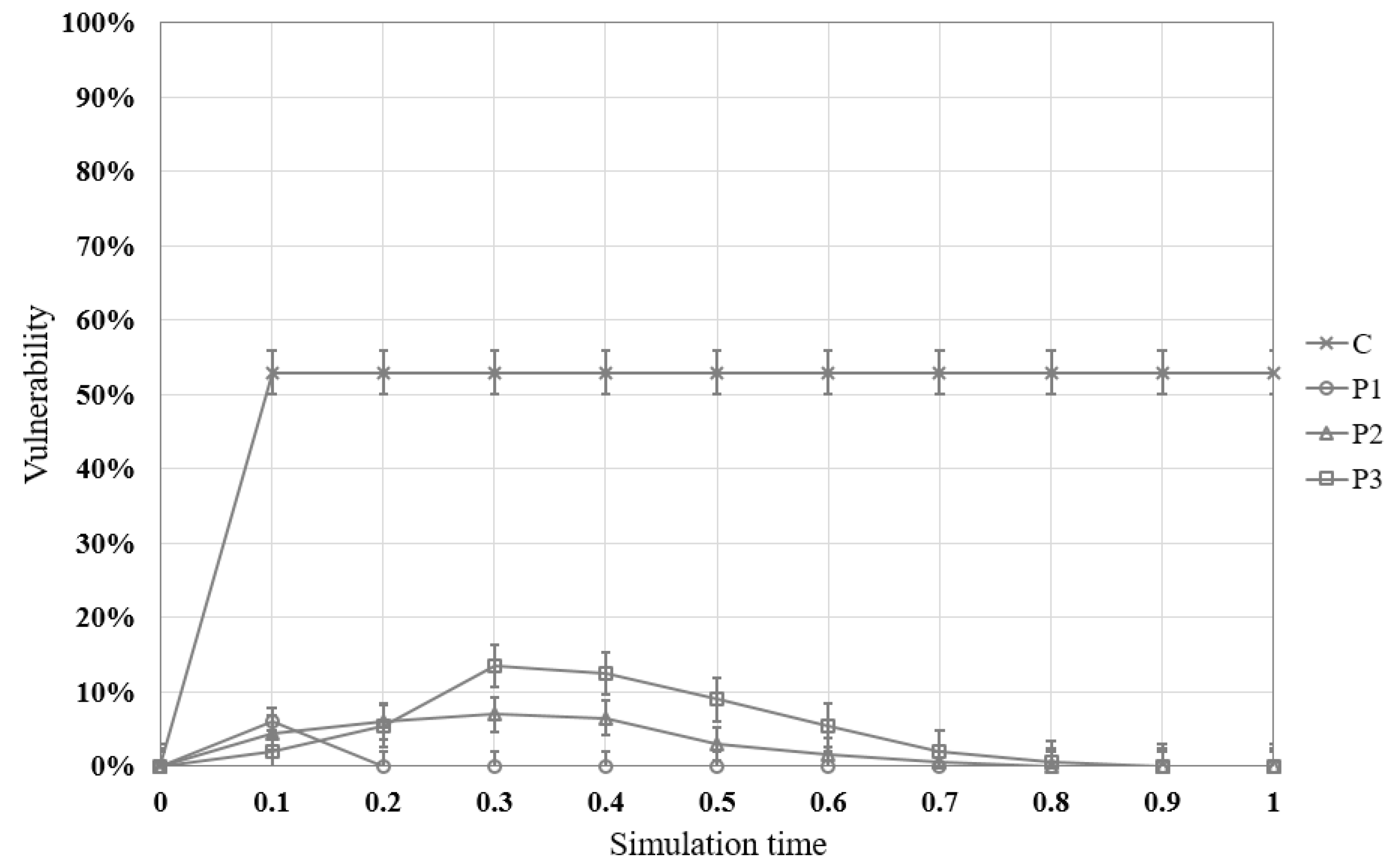
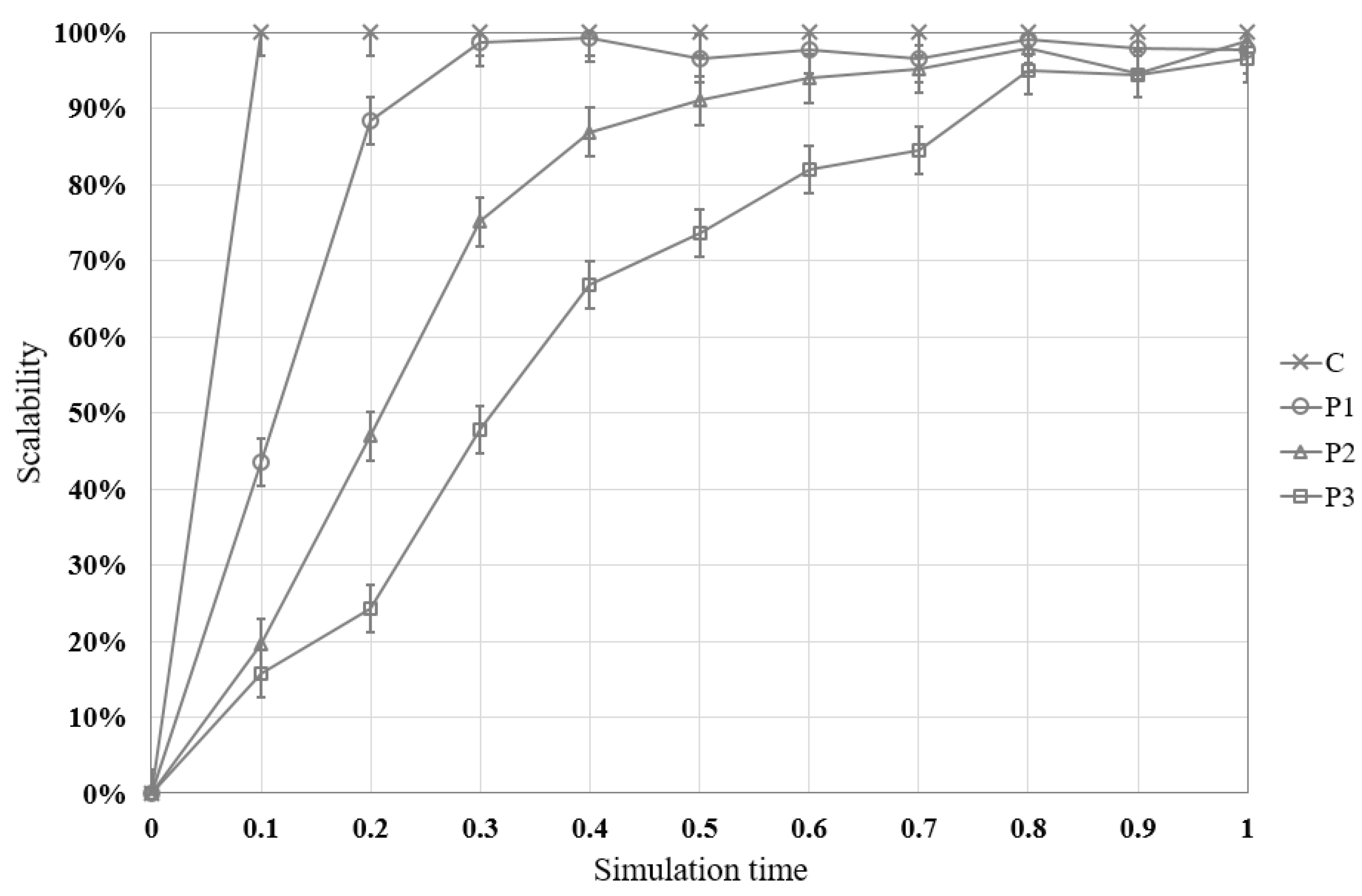
In this study, each node is allowed to connect to devices automatically within the connection range in order to evaluate the scalability of the proposed model and the comparative model. The comparative model allows all devices to be connected to each other within the connection range whereas the proposed model allows them to be connected to only the devices of the same level within the connection range according to the security level defined by the proposed method. The conventional (i.e., comparative) model is denoted by C, and the proposed model with 5, 10, and 15 of the update period denoted by P1, P2, and P3, respectively.
Figure 7 shows the results of comparing the security of the proposed model with that of the comparative model when 200 IoT devices in ad-hoc mode attempted to connect to devices within the connection range. Vulnerability is the result of dividing the number of infected devices by the number of all devices as described in Equation (2).
The X-axis represents the number of executions and the Y-axis represents the number of devices infected owing to their connection to malicious devices when 200 devices are connected to the peripheral devices. The error bar represents the standard deviation. In the comparative model, malicious devices were directly connected to all connectable devices and 53% of the devices were infected owing to their connection to malicious devices. However, in the proposed model, the number of devices connected to malicious devices was reduced by 14% for P3, 8.5% for P2, and 4.5% for P1. The number of devices connected to malicious devices decreased by up to 48.5% for P1. Further, as the proposed model is restricted to connection depending on the security level and continuously verifies software through the agent and the whitelist, the number of malicious devices continues to decrease owing to the whitelist update.
Figure 8 shows the results of comparing the scalability of the proposed model with that of the conventional model when 200 devices attempted to connect to devices within the connection range. Scalability is the result of dividing the number of connected IoTs by the number of physically available connections as described in Equation (3).
The X-axis represents the number of executions, and the Y-axis represents scalability based on the number of connected devices within the connectable range. The error bar represents the standard deviation. If they are connected with all devices within the connection range, they have a value of 100%. In the early connection stage, the proposed model shows very low scalability compared with the comparative model because the devices can be connected with only the devices of the same level and the connection range is also restricted by the level. However, whenever the devices attempt to connect to other devices, devices with low security level are restricted to connection, resulting in the continuous whitelist update. After a certain period of time, most devices will have level A security level, showing similar scalability to the comparative model. As the period to update the whitelist becomes longer, it takes longer to extend the devices by over 90%. As shown in
Figure 8, it took 0.23 for P1, 0.5 for P2, and 0.8 for P3 before achieving a scalability of 90% or more.