A High Capacity Watermarking Technique for the Printed Document
Abstract
1. Introduction
2. Related Theory
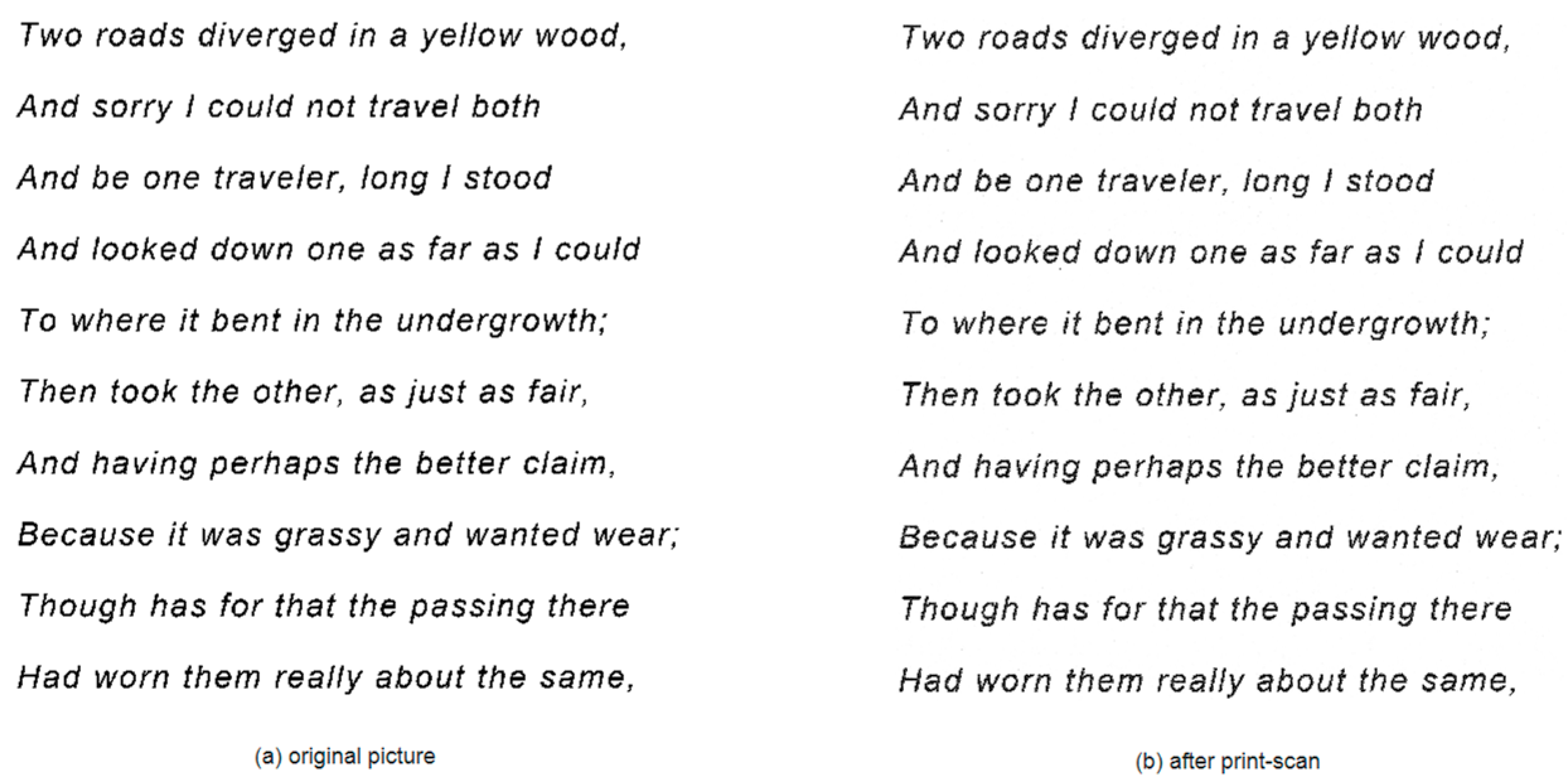
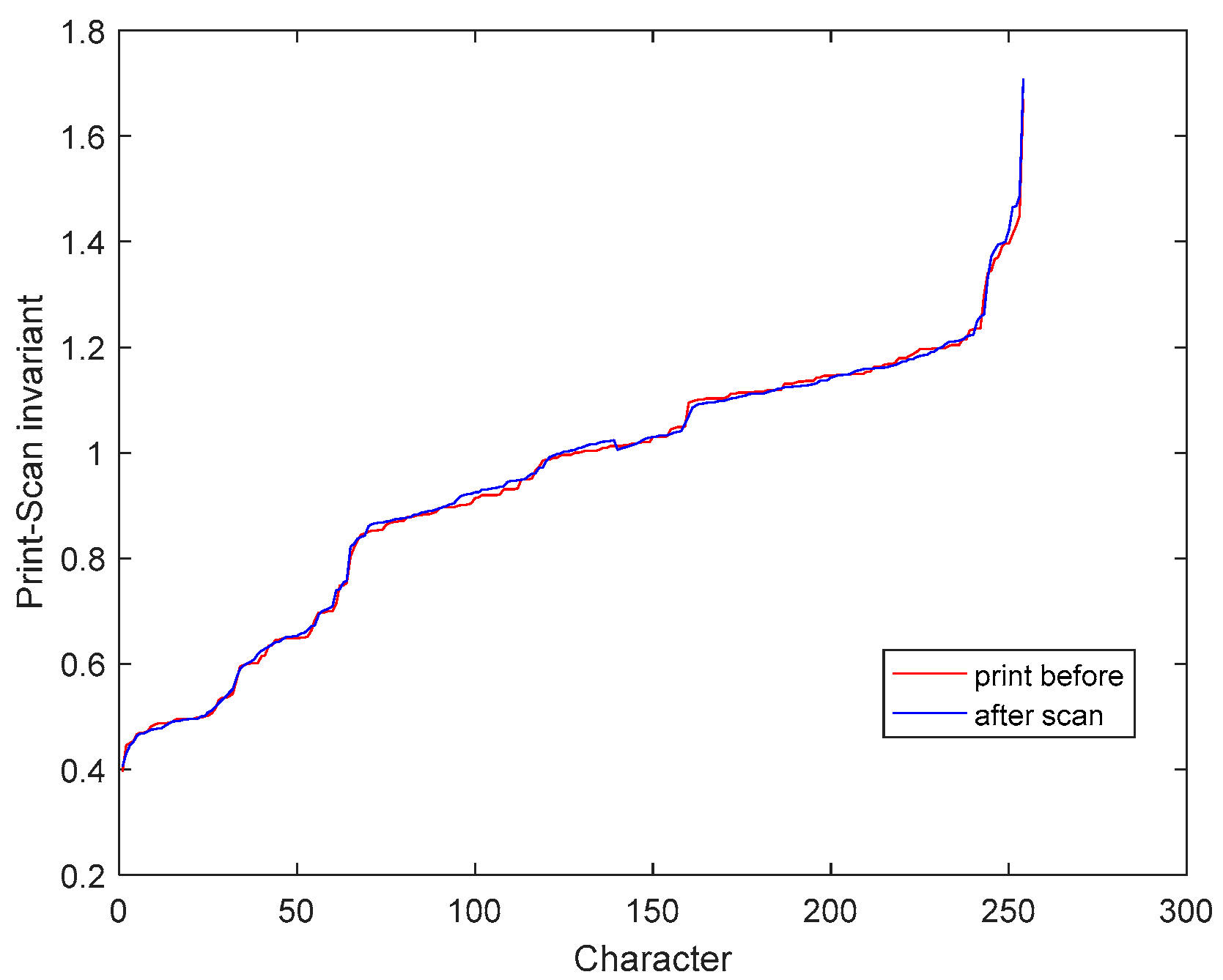
2.1. Print-Scan Invariant
2.2. Fourier Boundary Descriptors
2.3. Quadratic Quantization Function
2.4. QR Code
3. Proposed Model
3.1. Watermark Embedding Process
- The watermark information is obtained and arranged into a sequence , where is the watermark length.
- Converting the text image into a binary image, denoising, removing characters whose pixels are less than a certain threshold , for example, punctuation, etc. This paper takes greater than half of the average pixels of all characters.
- The processed binary image is divided into character row units, and then the effective characters of each row are segmented to obtain a character set , where is the row index and is the column index. The corresponding black pixels set is .
- Calculating the average value of black pixels of all characters in the first row, then calculating the ratio set of the remaining character black pixels to . And they are shown in Equations (9) and (10), respectively.
- Solving the quantization function Equation (6) according to the watermark information. If , then solving ; else if , then solving ; else if , then solving ; else if , then solving ; finding the appropriate solution . Then we can get the print-scan invariant set of all characters after embedding the watermark information and the set is .
- Calculating the pixel flipping ratio set for watermarked characters.
- According to the pixel flipping ratio set , the pixel points of the corresponding characters are flipped with the pixel flipping strategy in Section 3.3.
3.2. Watermark Extraction Process
- Converting the watermarked image into a binary image, removing noise, and removing characters whose pixel points are less than a certain threshold , such as punctuation. It should be stressed that this paper takes greater than half of the average pixels of all characters.
- The processed binary image is divided into character line units, and then the effective characters of each line are segmented to obtain a valid character set , where is the row index and is the column index. The corresponding black pixels set is .
- Calculating the average value of black pixels of all characters in the first row. Then calculating the ratio set of the remaining character black pixels to , as shown in Equations (11) and (12), respectively.
- Finding the watermark information carried by the character according to and the quantization function Equation (6). If , then getting ; else if ; then getting ; else if ; then getting ; else if ; then getting ;
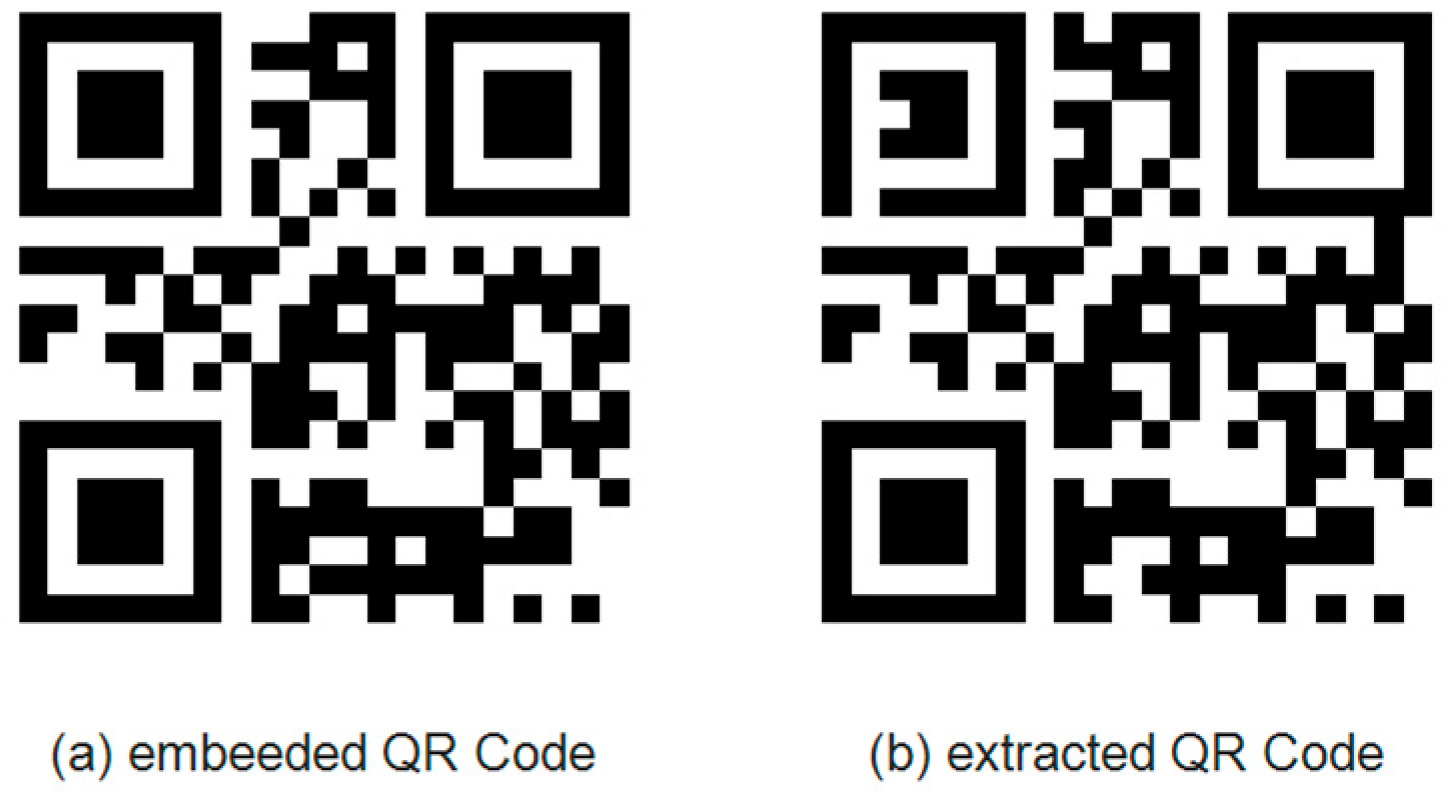
- Generating a corresponding QR code based on the watermark information.
3.3. Pixel Flipping Strategy
- According to the result of Section 3.1, inputting character and its corresponding pixel flipping rate .
- If , it is considered that the character does not need to be flipped, and it can be left as it is; otherwise, it will enter step 3.
- Extracting the boundary of the character and calculating the Fourier descriptor of the character according to Equation (4), where and is the number of boundary points of the character . Let , , .
- Reconstructing the boundary with Equation (5), then filling the boundary to get the character .
- If , then let ; otherwise . Then calculating the print scan invariant of the character and getting the difference between and the target . Let .
- If , then let , .
- If or , Then the flipping process ends, replacing the original character with ; Otherwise, let , jump to step 4 and continue the flipping process.
4. Experimental Results and Discussion
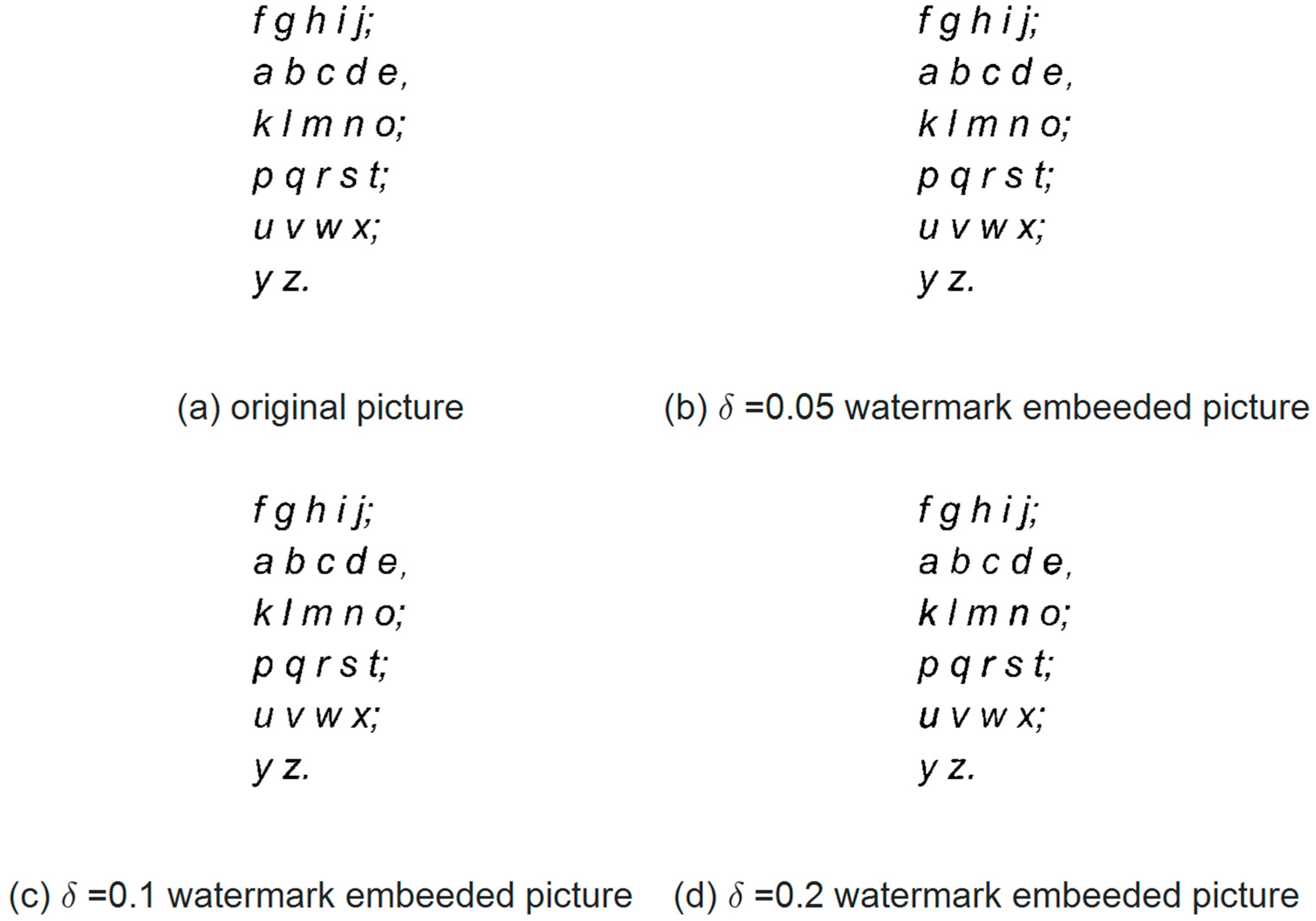
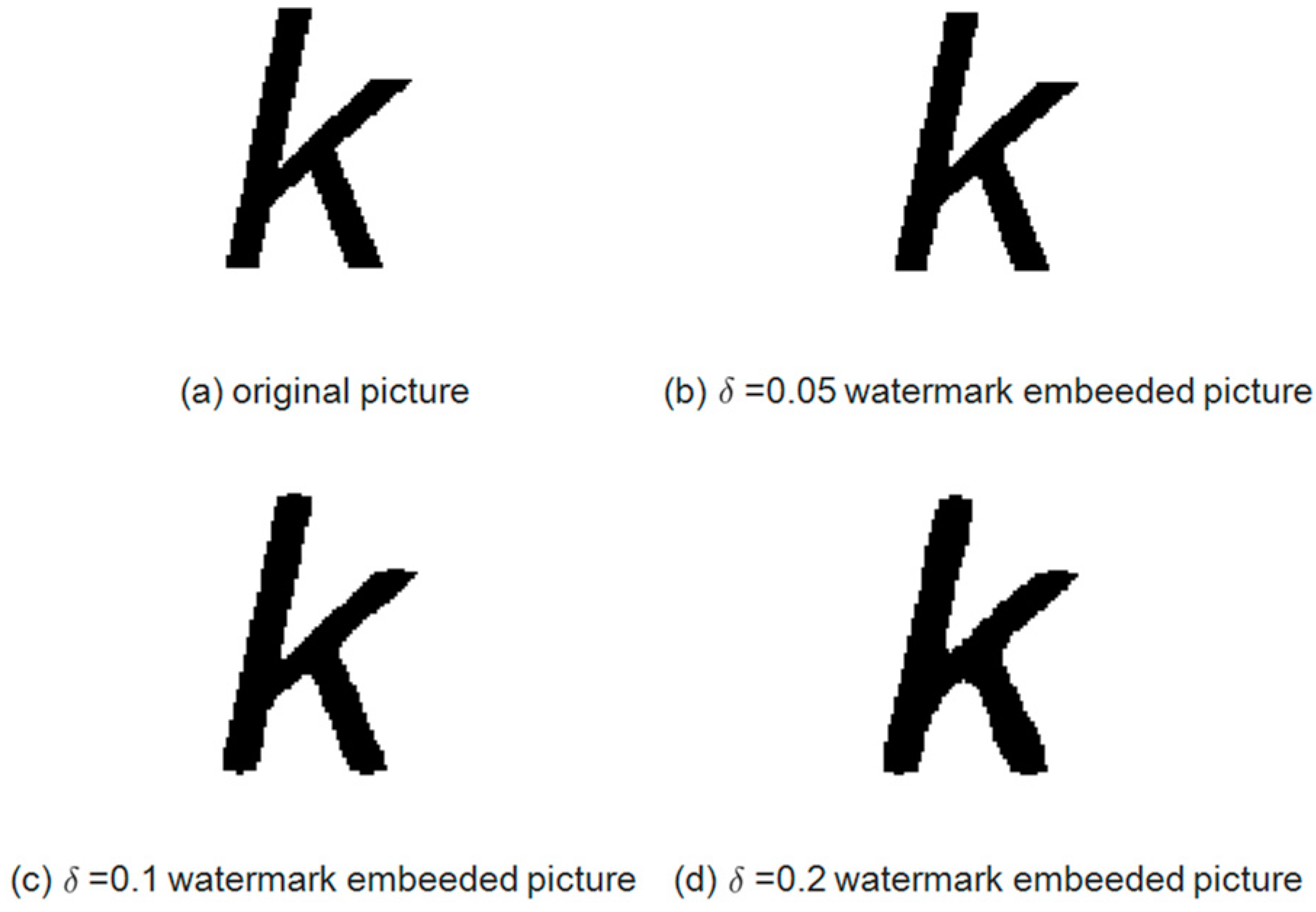
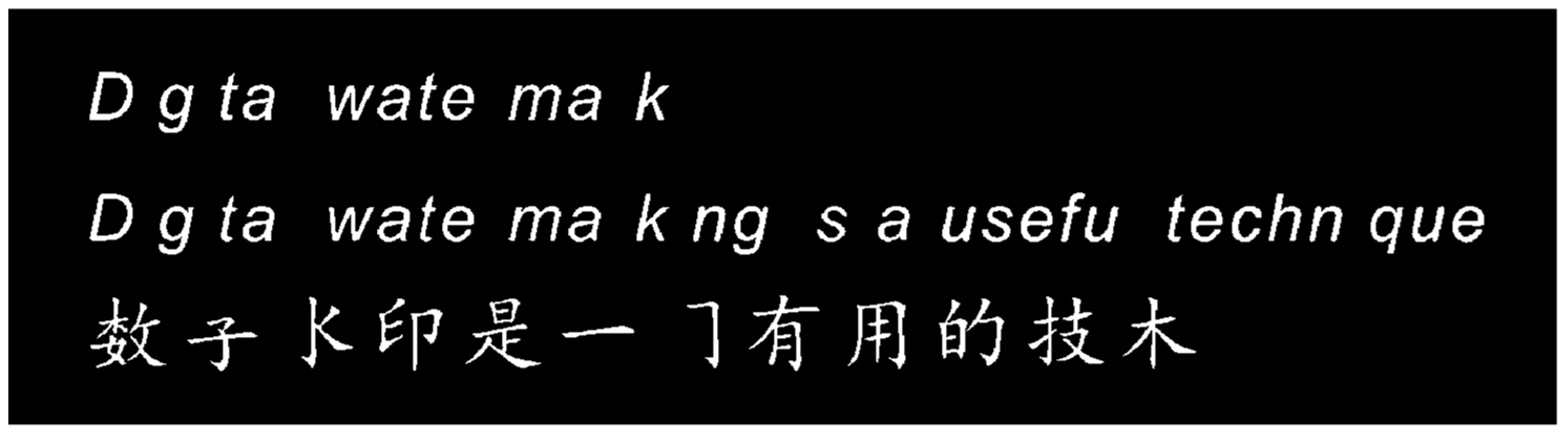
4.1. Visual Effect
4.2. Capacity and Robustness
4.3. Comparison with the State-of-the-Arts
5. Conclusions
- Larger watermark capacity. This paper analyzes the accuracy of the print-scan equipment to design a suitable quantization function, and makes a reasonable balance between the visual effect and the watermark capacity, so that the watermark capacity is greatly improved. In addition, by using the quantization function, a single character can carry bits watermark information, making it possible to embed QR code or other patterns in the document. The QR code itself has a larger information capacity, so this paper implements a large-capacity text watermarking algorithm.
- Better visual effect. Compared with the existing methods, this algorithm has a better visual effect and the visual effect can be adjusted according to the actual situation. This visual effect has strong generality, both English and Chinese fonts have good results.
- Better robustness. This algorithm can resist the attack of print-scan process, the attack of image scaling, the attack of noise and many more, and this algorithm can realize the blind extraction. Moreover, in order to further reduce the influence of the extraction error rate, this paper proposes to use the QR code as the watermark information. Since the QR code itself has an error correction function, the information carried by the QR code can still be scanned within a certain error range, thereby making the robustness better.
Author Contributions
Funding
Conflicts of Interest
References
- Vaidya, S.P.; Mouli, P.C.; Santosh, K.C. Imperceptible watermark for a game-theoretic watermarking system. Int. J. Mach. Learn. Cybern. 2018, 10, 1323–1339. [Google Scholar] [CrossRef]
- Lee, Y.; Seo, Y.; Kim, D. Digital blind watermarking based on depth variation prediction map and DWT for DIBR free-viewpoint image. Signal Process. Image Commun. 2019, 70, 104–113. [Google Scholar] [CrossRef]
- Leopardi, A.; Soresina, D.; Marcantonio, D.; Malacarne, A.; Conci, N.; Boato, G. Blind image watermarking in Wavelet-domain robust to printing and smart-phone acquisition. Electron. Imaging 2018, 13, 1–9. [Google Scholar] [CrossRef]
- Nguyen, T.H.; Duong, D.A. Robust and high capacity watermarking for image based on DWT-SVD. In Proceedings of the 11th IEEE-RIVF International Conference on Computing and Communication Technologies, Can Tho, Vietnam, 25–28 January 2015. [Google Scholar]
- Sang, J.; Fang, Q.; Xu, C. Exploiting Social-Mobile Information for Location Visualization. ACM Trans. Intell. Syst. Technol. 2017, 8, 1–19. [Google Scholar] [CrossRef]
- Zeeshan, M.; Ullah, S.; Anayat, S.; Hussain, R.G.; Nasir, N. A Review Study on Unique Way of Information Hiding: Steganography. Int. J. Data Sci. Technol. 2017, 3, 45–51. [Google Scholar] [CrossRef][Green Version]
- Xie, G.; Liu, Y.; Xin, G.; Yang, P. Review on Text Watermarking Resistant to Print-Scan, Screen-Shooting; Springer Science and Business Media LLC: Cham, Switzerland, 2019; pp. 140–149. [Google Scholar]
- Khadam, U.; Iqbal, M.M.; Azam, M.A.; Khalid, S.; Rho, S.; Chilamkurti, N. Digital Watermarking Technique for Text Document Protection Using Data Mining Analysis. IEEE Access 2019, 7, 64955–64965. [Google Scholar] [CrossRef]
- Brassil, J.T.; Low, S.; Maxemchuk, N.F. Copyright protection for the electronic distribution of text documents. Proc. IEEE 1999, 87, 1181–1196. [Google Scholar] [CrossRef]
- Brassil, J.T.; Low, S.; Maxemchuk, N.F. Electronic marking and identification techniques to discourage document copying. IEEE J. Sel. Areas Commun. 1995, 13, 1495–1504. [Google Scholar] [CrossRef]
- Alattar, A.M.; Alattar, O.M. Watermarking Electronic Text Documents Containing Justified Paragraphs and Irregular Line Spacing. In Proceedings of the SPIE—The International Society for Optical Engineering, San Jose, CA, USA, 22 June 2004; pp. 685–695. [Google Scholar]
- Liu, Y.; Zhu, Y.; Xin, G. A zero-watermarking algorithm based on merging features of sentences for Chinese text. J. Chin. Inst. Eng. 2015, 38, 391–398. [Google Scholar] [CrossRef]
- Liu, Y.; Sun, X.; Gan, C.; Wang, H. An Efficient Linguistic Steganography for Chinese Text. In Proceedings of the IEEE International Conference on Multimedia & Expo, Beijing, China, 2–5 July 2007. [Google Scholar]
- Taleby Ahvanooey, M.; Li, Q.; Shim, H.J.; Huang, Y. A Comparative Analysis of Information Hiding Techniques for Copyright Protection of Text Documents. Secur. Commun. Netw. 2018, 2018, 5325040. [Google Scholar] [CrossRef]
- Tan, L.; Sun, X.; Sun, G. Print-Scan Resilient Text Image Watermarking Based on Stroke Direction Modulation for Chinese Document Authentication. Radioengineering 2012, 21, 170–181. [Google Scholar]
- Borges, P.V.K.; Mayer, J. Text luminance modulation for hardcopy watermarking. Signal Process. 2007, 87, 1754–1771. [Google Scholar] [CrossRef]
- Villán, R.; Voloshynovskiy, S.; Koval, O.; Vila, J.; Topak, E.; Deguillaume, F. Text data-hiding for digital and printed documents: Theoretical and practical considerations. In Proceedings of the Security, Steganography, and Watermarking of Multimedia Contents VIII, San Jose, CA, USA, 17 February 2006. [Google Scholar]
- Thongkor, K.; Amornraksa, T. Digital image watermarking for printed and scanned documents. In Proceedings of the Ninth International Conference on Digital Image Processing (ICDIP 2017), Hong Kong, China, 21 July 2017. [Google Scholar]
- Solachidis, V.; Pitas, I. Watermarking Polygonal Lines Using Fourier Descriptors. IEEE Comput. Graph. Appl. 2004, 24, 44. [Google Scholar] [CrossRef]
- Wu, M.; Liu, B. Data hiding in binary image for authentication and annotation. IEEE Trans. Multimed. 2004, 6, 538. [Google Scholar] [CrossRef]
- Qi, W.F.; Li, X.L.; Yang, B.; Cheng, D. Document watermarking scheme for information tracking. J. Commun. 2008, 29, 183–190. [Google Scholar]
- Tan, L.; Hu, K.; Zhou, X.; Chen, R.; Jiang, W. Print-scan invariant text image watermarking for hardcopy document authentication. Multimed. Tools Appl. 2019, 78, 13189–13211. [Google Scholar] [CrossRef]
- Kim, H.Y.; Mayer, J. Data Hiding for Printed Binary Documents Robust to Print-Scan, Photocopy and Geometric Attacks. J. Commun. Inf. Syst. 2008, 23. [Google Scholar] [CrossRef]
- Cardamone, N.; d’Amore, F. DWT and QR Code Based Watermarking for Document DRM. In International Workshop on Digital Watermarking; Springer: Cham, Switzerland, 2018. [Google Scholar]
- Smith, E.B.; Qiu, X. Statistical image differences, degradation features, and character distance metrics. Int. J. Doc. Anal. Recognit. 2003, 6, 146–153. [Google Scholar] [CrossRef]
- Dong, L.; Wang, J.; Li, Y.; Tang, Y.Y. Sector Projection Fourier Descriptor for Chinese character recognition. In Proceedings of the IEEE International Conference on Cybernetics (CYBCO), Lausanne, Switzerland, 13–15 June 2013. [Google Scholar]
- Zhang, L.; Zheng, H. A high capacity multiple watermarking scheme based on Fourier descriptor and Sudoku. In Proceedings of the Eighth International Conference on Machine Vision (ICMV 2015), Barcelona, Spain, 8 December 2015. [Google Scholar]
- Labeljoy. Available online: https://www.labeljoy.com/qr-code/qr-code-specification/ (accessed on 10 October 2019).
- Panyavaraporn, J.; Horkaew, P.; Wongtrairat, W. QR code watermarking algorithm based on wavelet transform. In Proceedings of the Communications and Information Technologies (ISCIT), Surat Thani, Thailand, 4–6 September 2013. [Google Scholar]
- Nishane, S.; Umale, V.M. Digital image watermarking based on DWT using QR code. Int. J. Curr. Eng. Technol. 2015, 5, 1530–1532. [Google Scholar]
- OSCHINA.NET. Available online: http://tool.oschina.net/qr (accessed on 10 October 2019).
- Arena, P.; Baglio, S.; Fortuna, L.; Manganaro, G. Self-organization in a two-layer CNN. IEEE Trans. Circuits Syst. 1998, 45, 157–162. [Google Scholar] [CrossRef]

| Num | Author-year | Features | Capacity | Visual | Robustness | Drawbacks |
|---|---|---|---|---|---|---|
| 1 | [15]-2012 | Stroke | High | Medium | Medium | Only for characters with strokes |
| 2 | [16]-2007 | Grayscale | High | Low | High | Affecting visual effects |
| 3 | [17]-2006 | Grayscale | High | Low | High | Affecting visual effects |
| 4 | [18]-2017 | Grayscale | High | Low | High | Affecting visual effects |
| 5 | [19]-2004 | Boundary | Medium | High | Low | Watermark is not blind, not resistant to print scanning |
| 6 | [20]-2004 | Pixel | Medium | Medium | Medium | Pixel flipping strategy is complex, affecting visual effects |
| 7 | [21]-2008 | Pixel | Medium | Medium | Medium | Pixel flipping strategy is complex, affecting visual effects |
| 8 | [22]-2019 | Pixel | High | Medium | Medium | Affecting visual effects |
| 9 | [23]-2008 | Shading | Medium | Low | Low | poor robustness, affecting visual effects |
| 10 | [24]-2018 | Shading | High | Low | Low | Not blind, affecting visual effects, poor robustness |
| PSNR | 31.17 | 27.73 | 25.05 |
| SIM | 97.24% | 95.89% | 94.41% |
| Num | Author-Year | Feature | Capacity |
|---|---|---|---|
| 1 | [21]-2008 | pixel | <75% |
| 2 | [22]-2019 | pixel | <100% |
| 3 | Proposed method | pixel | >200% |
| Num | Author-Year | Arial 14pt | TNR 14pt | LiSu 14pt | KaiTi 14pt | Century 14pt |
|---|---|---|---|---|---|---|
| 1 | [21]-2008 | 25.2 | 24.4 | 24.0 | 25.6 | 26.9 |
| 2 | [22]-2019 | 27.9 | 26.3 | 25.8 | 28.4 | 26.7 |
| 3 | Proposed method | 31.3 | 30.9 | 28.2 | 33.1 | 31.8 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Huang, K.; Tian, X.; Yu, H.; Yu, M.; Yin, A. A High Capacity Watermarking Technique for the Printed Document. Electronics 2019, 8, 1403. https://doi.org/10.3390/electronics8121403
Huang K, Tian X, Yu H, Yu M, Yin A. A High Capacity Watermarking Technique for the Printed Document. Electronics. 2019; 8(12):1403. https://doi.org/10.3390/electronics8121403
Chicago/Turabian StyleHuang, Kai, Xiaobo Tian, Hongzhou Yu, Min Yu, and Aiguo Yin. 2019. "A High Capacity Watermarking Technique for the Printed Document" Electronics 8, no. 12: 1403. https://doi.org/10.3390/electronics8121403
APA StyleHuang, K., Tian, X., Yu, H., Yu, M., & Yin, A. (2019). A High Capacity Watermarking Technique for the Printed Document. Electronics, 8(12), 1403. https://doi.org/10.3390/electronics8121403





