Resilience Evaluation of Demand Response as Spinning Reserve under Cyber-Physical Threats
Abstract
:1. Introduction
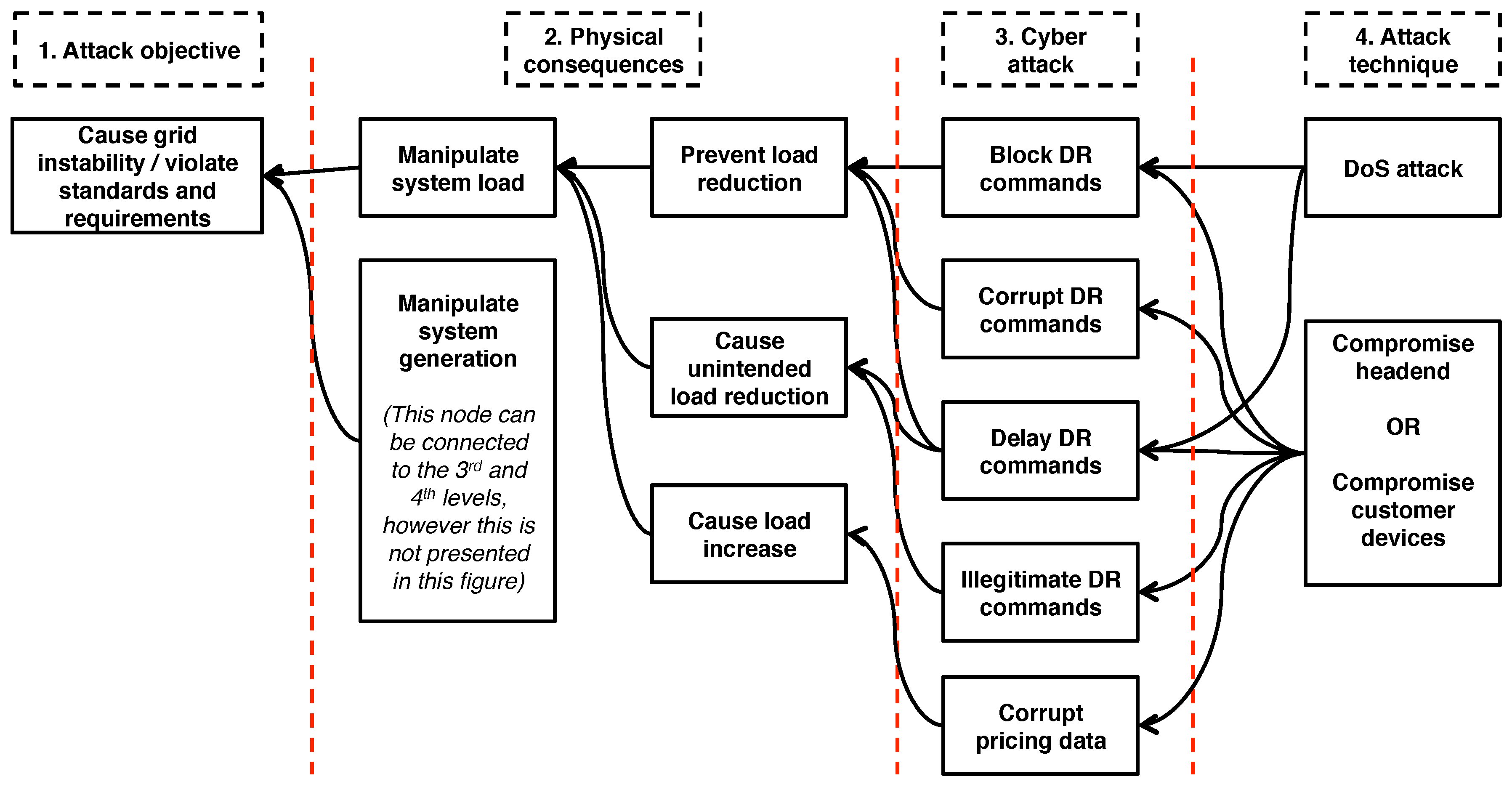
- Identify dependencies and failure conditions of the function under evaluation (DRASR in this case).
- Create an attack tree by exploiting the dependencies identified in the first step.
- Perform sensitivity analysis based on the first two steps to identify the boundaries between acceptable and failed function operation.
- Analyze a bottom-up attack scenario to verify that at least one cyber-physical attack is possible.
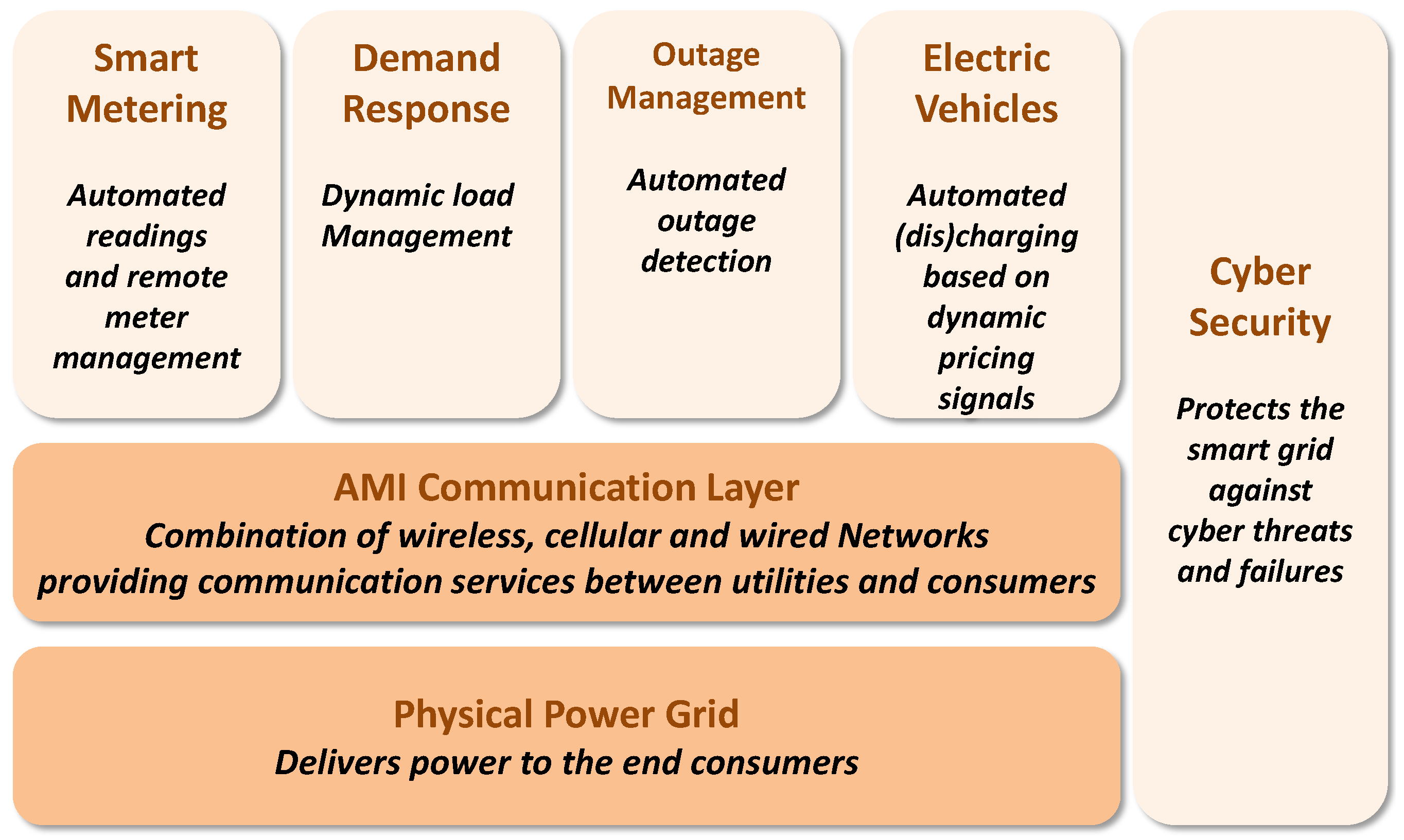
2. Background and Related Work
2.1. Smart Grid Resilience
- Measures of dependability in the presence of disturbances.
- Measures of the amount of disturbances that a system can tolerate.
- Measures of the probability of correct service given that a disturbance occurred.
2.2. DR as Spinning Reserve
3. Resilience Evaluation of DRASR
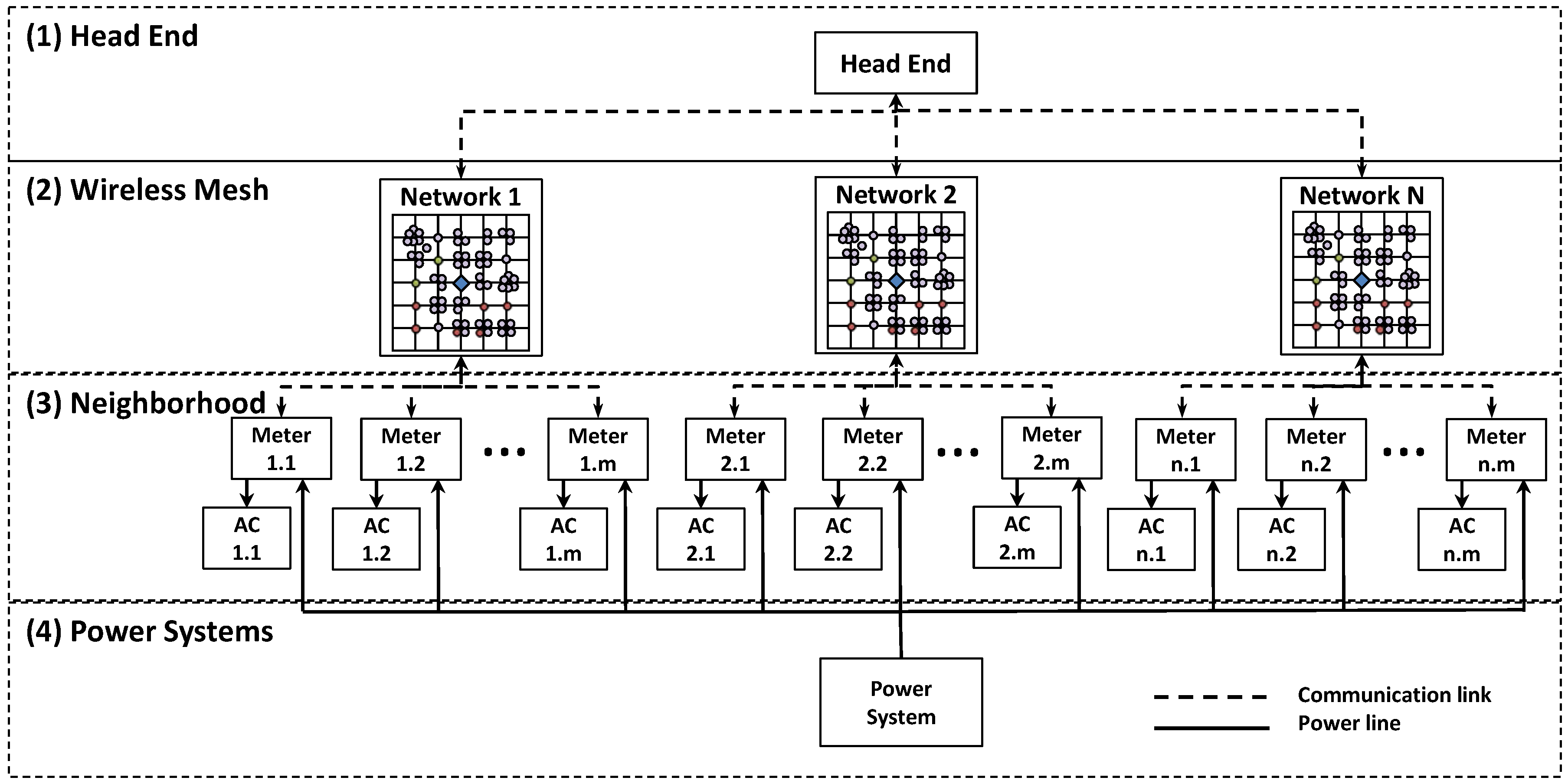
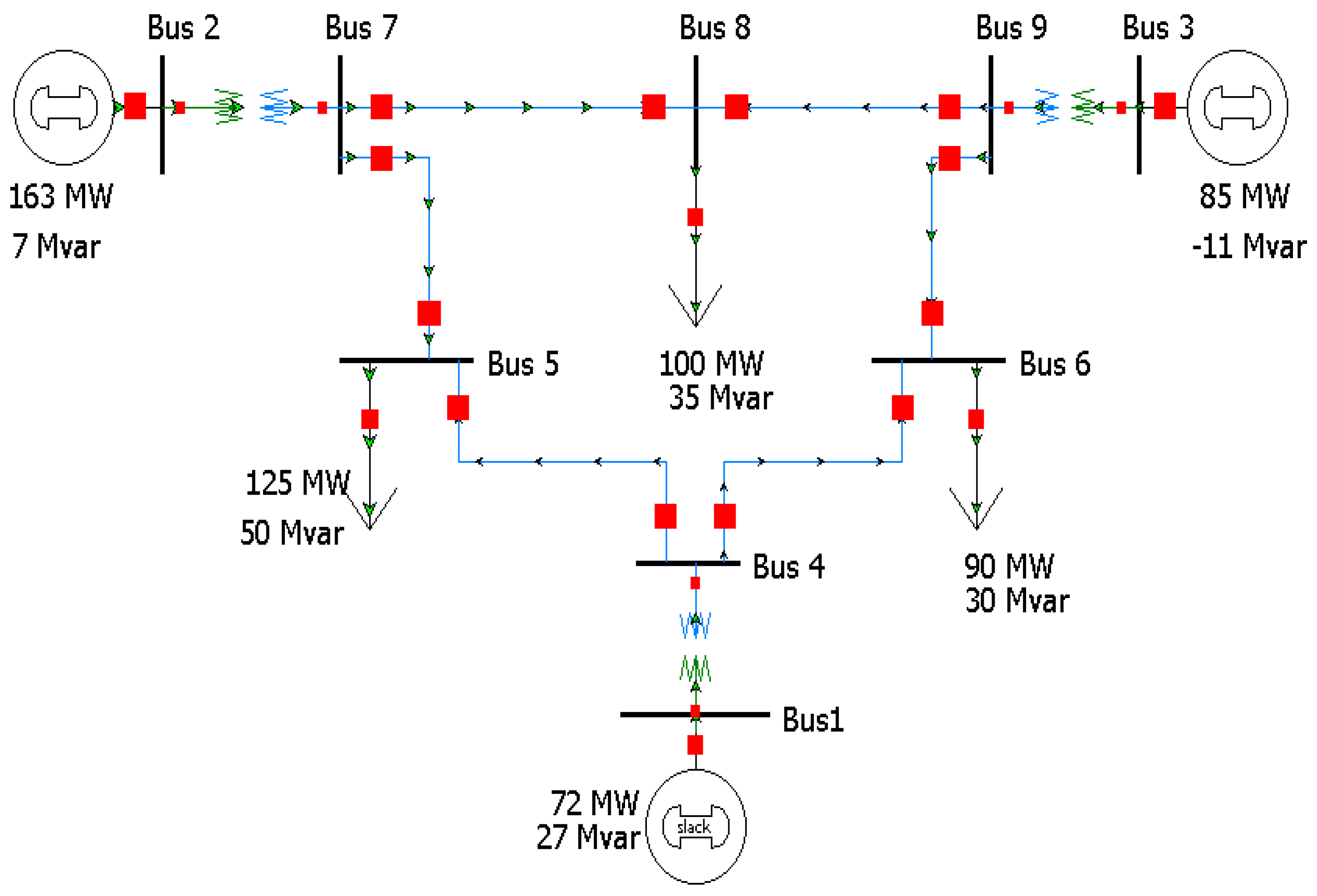
3.1. Modeling and Simulation Setup
3.2. Evaluation Process
3.2.1. Identify Dependencies and Failure Conditions
3.2.2. Create Attack Tree
3.2.3. Perform Sensitivity Analysis Based on the First Two Steps
3.2.4. Analyze a Bottom-Up Attack Scenario
4. Results
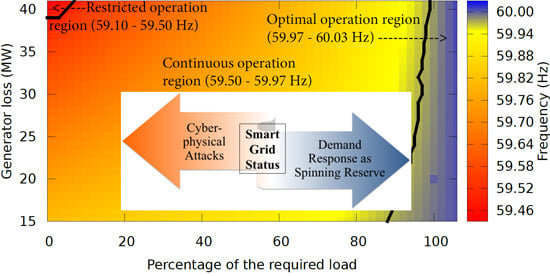
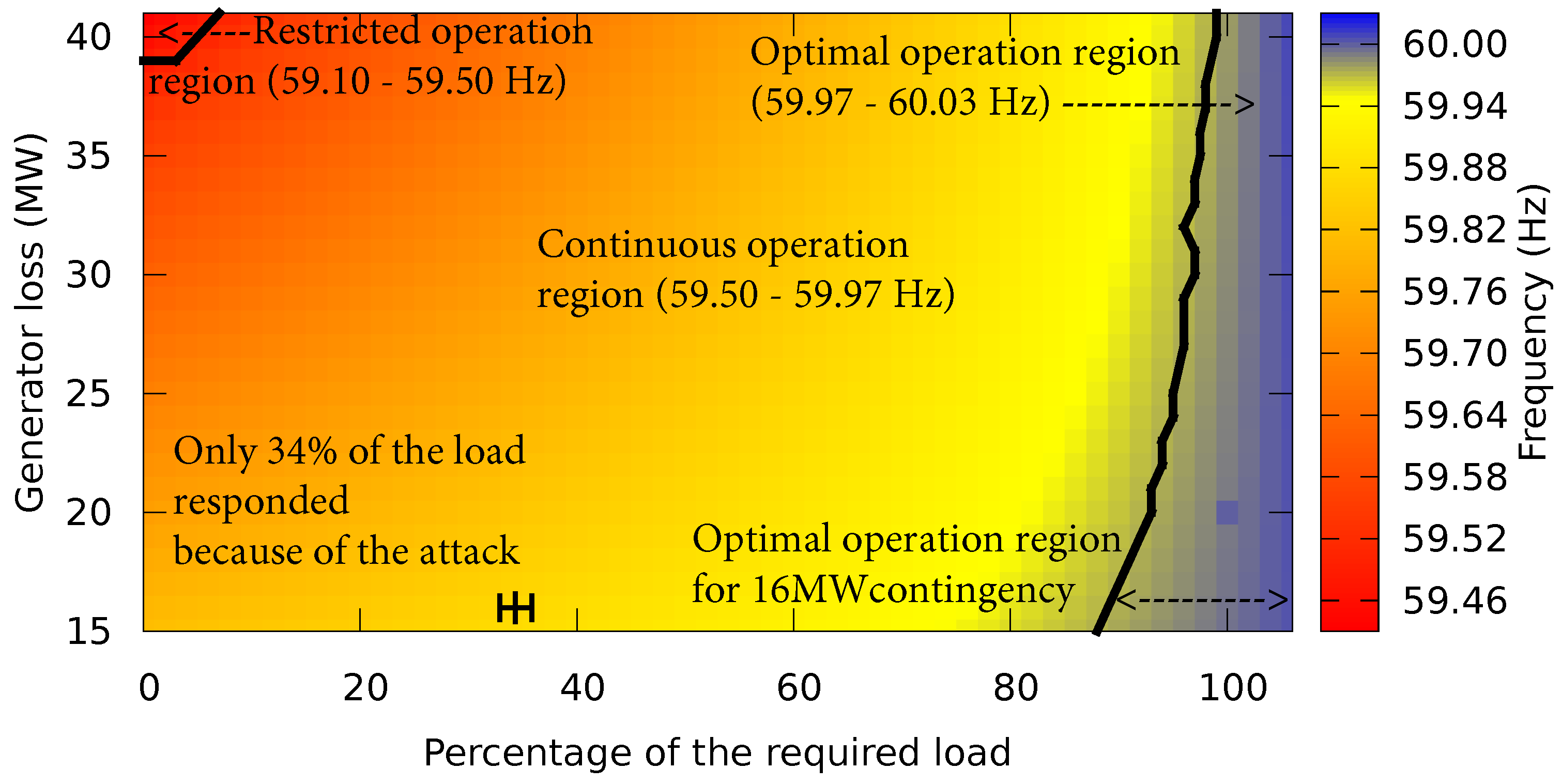
4.1. Optimal Operation Region (59.97–60.03 Hz)
4.2. Continuous Operation Region (59.50–59.97 Hz)
4.3. Restricted Operation Region (59.10–59.50 Hz)
- The stability level of the system measured by system frequency (Hz) when there is an attack on DR measured by the percentage of load that responds at the time of a contingency.
- The attack level on DR measured by the percentage of load that responds that the system can tolerate at the time of a contingency, in order to stay in the optimal operation region.
5. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
Abbreviations
| DR | Demand Response |
| DRASR | Demand Response as Spinning Reserve |
| AC | Air Conditioning |
| AGC | Automatic Generation Control |
| AMI | Advanced Metering Infrastructure |
| HAM | Home Area Network |
| DoS | Denial of Service |
| UFLS | Under Frequency Load Shedding |
| UFGP | Under Frequency Generator Protection |
References
- Neuman, C.; Tan, K. Mediating cyber and physical threat propagation in secure smart grid architectures. In Proceedings of the IEEE International Conference on Smart Grid Communications (SmartGridComm), Brussels, Belgium, 17–20 October 2011; pp. 238–243.
- Almajali, A.; Rice, E.; Viswanathan, A.; Tan, K.; Neuman, C. A systems approach to analysing cyber-physical threats in the Smart Grid. In Proceedings of the IEEE International Conference on Smart Grid Communications (SmartGridComm), Vancouver, BC, Canada, 21–24 October 2013; pp. 456–461.
- Eto, J.; Nelson-Hoffman, J.; Parker, E.; Bernier, C.; Young, P.; Sheehan, D.; Kueck, J.; Kirby, B. The Demand Response Spinning Reserve Demonstration–Measuring the Speed and Magnitude of Aggregated Demand Response. In Proceedings of the 45th Hawaii International Conference on System Science (HICSS), Maui, HI, USA, 4–7 January 2012; pp. 2012–2019.
- North American Electric Reliability Corporation (NERC). WECC Standard BAL-002-WECC-2—Contingency Reserve. Available online: http://www.nerc.com/files/BAL-002-WECC-2.pdf (accessed on 18 December 2016).
- U.S. Department of Energy. Smart Grid System Report; Technical Report; U.S. Department of Energy: Washington, DC, USA, 2009.
- U.S. Department of Energy. A Vision For The Modern Grid; Technical Report; U.S. Department of Energy: Washington, DC, USA, 2007.
- USC/ISI. Network Simulator—2 (ns-2). Available online: http://www.isi.edu/nsnam/ns/ (accessed on 18 December 2016).
- Power World Corporation. PowerWorld. Available online: http://www.powerworld.com/ (accessed on 18 December 2016).
- Laprie, J.C. From dependability to resilience. In Proceedings of the 38th IEEE/IFIP International Conference On Dependable Systems and Networks, Anchorage, AK, USA, 24–27 June 2008; pp. G8–G9.
- Avizienis, A.; Laprie, J.C.; Randell, B.; Landwehr, C. Basic concepts and taxonomy of dependable and secure computing. IEEE Trans. Dependable Secur. Comput 2004, 1, 11–33. [Google Scholar] [CrossRef]
- Cárdenas, A.A.; Amin, S.; Lin, Z.S.; Huang, Y.L.; Huang, C.Y.; Sastry, S. Attacks against process control systems: Risk assessment, detection, and response. In Proceedings of the 6th ACM Symposium on Information, Computer and Communications Security, Hong Kong, China, 22–24 March 2011; pp. 355–366.
- Huang, Y.L.; Cárdenas, A.A.; Amin, S.; Lin, Z.S.; Tsai, H.Y.; Sastry, S. Understanding the physical and economic consequences of attacks on control systems. Int. J. Crit. Infrastruct. Prot. 2009, 2, 73–83. [Google Scholar] [CrossRef]
- Chiaradonna, S.; Di Giandomenico, F.; Lollini, P. Case study on critical infrastructures: Assessment of electric power systems. In Resilience Assessment and Evaluation of Computing Systems; Springer: Berlin/Heidelberg, Germany, 2012; pp. 365–390. [Google Scholar]
- Sridhar, S.; Hahn, A.; Govindarasu, M. Cyber–physical system security for the electric power grid. Proc. IEEE 2012, 100, 210–224. [Google Scholar] [CrossRef]
- Bodeau, D.J.; Graubart, R.D.; Laderman, E.R. Cyber Resiliency Engineering Overview of the Architectural Assessment Process. Procedia Comput. Sci. 2014, 28, 838–847. [Google Scholar] [CrossRef]
- Reed, D.; Kapur, K.; Christie, R. Methodology for Assessing the Resilience of Networked Infrastructure. IEEE Syst. J. 2009, 3, 174–180. [Google Scholar] [CrossRef]
- Ouyang, M.; Dueñas-Osorio, L. Resilience modeling and simulation of smart grids. In Proceedings of the Structures Congress, Las Vegas, NV, USA, 14–16 April 2011; pp. 1996–2009.
- Dondossola, G.; Lamquet, O.; Torkilseng, A. Key issues and related methodologies in the security risk analysis and evaluation of electric power control systems. In Proceedings of the 2006 CIGRE Session, Paris, France, 27 August–1 September 2006.
- Stamp, J.; McIntyre, A.; Ricardson, B. Reliability impacts from cyber attack on electric power systems. In Proceedings of the IEEE Power Systems Conference and Exposition, Seattle, WA, USA, 15–18 March 2009; pp. 1–8.
- Sridhar, S.; Manimaran, G. Data integrity attacks and their impacts on SCADA control system. In Proceedings of the IEEE Power and Energy Society General Meeting, Minneapolis, MN, USA, 25–29 July 2010; pp. 1–6.
- Strigini, L. Fault tolerance and resilience: Meanings, measures and assessment. In Resilience Assessment and Evaluation of Computing Systems; Springer: Berlin/Heidelberg, Germany, 2012; pp. 3–24. [Google Scholar]
- Vieira, M.; Madeira, H.; Sachs, K.; Kounev, S. Resilience benchmarking. In Resilience Assessment and Evaluation of Computing Systems; Springer: Berlin/Heidelberg, Germany, 2012; pp. 283–301. [Google Scholar]
- Electric Power Research Institute (EPRI). EPRI Power System Dynamics Tutorial; Technical Report 1016042; EPRI: Palo Alto, CA, USA, 2009. [Google Scholar]
- Kirby, B.J. Demand Response For Power System Reliability; Oak Ridge National Laboratory: Oak Ridge, TN, USA, 2006. [Google Scholar]
- Eto, J.H.; Nelson-Hoffman, J.; Torres, C.; Hirth, S.; Yinger, B.; Kueck, J.; Kirby, B.; Bernier, C.; Wright, R.; Barat, A.; et al. Demand Response Spinning Reserve Demonstration; Lawrence Berkeley National Laboratory: Berkeley, CA, USA, 2007. [Google Scholar]
- Eto, J.H. Demand Response Spinning Reserve Demonstration—Phase 2 Findings from the Summer of 2008; Lawrence Berkeley National Laboratory: Berkeley, CA, USA, 2010. [Google Scholar]
- Lichtensteiger, B.; Bjelajac, B.; Müller, C.; Wietfeld, C. RF Mesh Systems for Smart Metering: System Architecture and Performance. In Proceedings of the 2010 First IEEE International Conference on Smart Grid Communications (SmartGridComm), Gaithersburg, MD, USA, 4–6 October 2010; pp. 379–384.
- U.S. Energy Information Administration. Electric Sales, Revenue, and Average Price. Available online: http://www.eia.gov/electricity/sales_revenue_price/ (accessed on 18 December 2016).
- WECC. WECC Approved Dynamic Model Library. 2011. Available online: https://www.wecc.biz/Administrative/Approved_Dynamic_Models_June_2015.pdf (accessed on 18 December 2016).
- Meserve, J. Staged Cyber Attack Reveals Vulnerability in Power Grid. 2007. Available online: http://www.cnn.com/2007/US/09/26/power.at.risk/index.html?_s=PM:US (accessed on 18 December 2016).
| Customer Type | Percent of Customers (%) | Num. of ACs | Avg. AC (kW) |
|---|---|---|---|
| Industrial | 0.50 | 2 | - |
| Commercial | 12.20 | 49 | 3.50 |
| Residential *, 1 unit | 5 | 17 | 3.50 |
| Residential, 2 units | 2 | 6 | 3.50 |
| Residential, 3–5 units | 5 | 20 | 1.44 |
| Residential, 5–9 units | 6 | 21 | 1.44 |
| Residential, 10–19 units | 12 | 45 | 1.44 |
| Residential, 20+ units | 70 | 240 | 0.70 |
| Totals | 100 | 400 | - |
| Customer Type | Total Num. of ACs | Avg. AC Load (kW) per Customer | Avg. Load Curtailed (kW) |
|---|---|---|---|
| Commercial | 457 | 3.50 | 1599.5 |
| Residential *, 1 unit | 457 | 3.50 | 1599.5 |
| Residential, 2 units | 457 | 3.50 | 1599.5 |
| Residential, 3–5 units | 914 | 1.44 | 1316.16 |
| Residential, 5–9 units | 457 | 1.44 | 658.08 |
| Residential, 10–19 units | 2285 | 1.44 | 3290.4 |
| Residential, 20+ units | 8683 | 0.70 | 6078.1 |
| Totals | 13,710 | - | 16,141.24 |
© 2016 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license ( http://creativecommons.org/licenses/by/4.0/).
Share and Cite
AlMajali, A.; Viswanathan, A.; Neuman, C. Resilience Evaluation of Demand Response as Spinning Reserve under Cyber-Physical Threats. Electronics 2017, 6, 2. https://doi.org/10.3390/electronics6010002
AlMajali A, Viswanathan A, Neuman C. Resilience Evaluation of Demand Response as Spinning Reserve under Cyber-Physical Threats. Electronics. 2017; 6(1):2. https://doi.org/10.3390/electronics6010002
Chicago/Turabian StyleAlMajali, Anas, Arun Viswanathan, and Clifford Neuman. 2017. "Resilience Evaluation of Demand Response as Spinning Reserve under Cyber-Physical Threats" Electronics 6, no. 1: 2. https://doi.org/10.3390/electronics6010002
APA StyleAlMajali, A., Viswanathan, A., & Neuman, C. (2017). Resilience Evaluation of Demand Response as Spinning Reserve under Cyber-Physical Threats. Electronics, 6(1), 2. https://doi.org/10.3390/electronics6010002