Towards Development of a High Abstract Model for Drone Forensic Domain
Abstract
:1. Introduction
- Discussing the existing challenges and issues related to the DRF domain
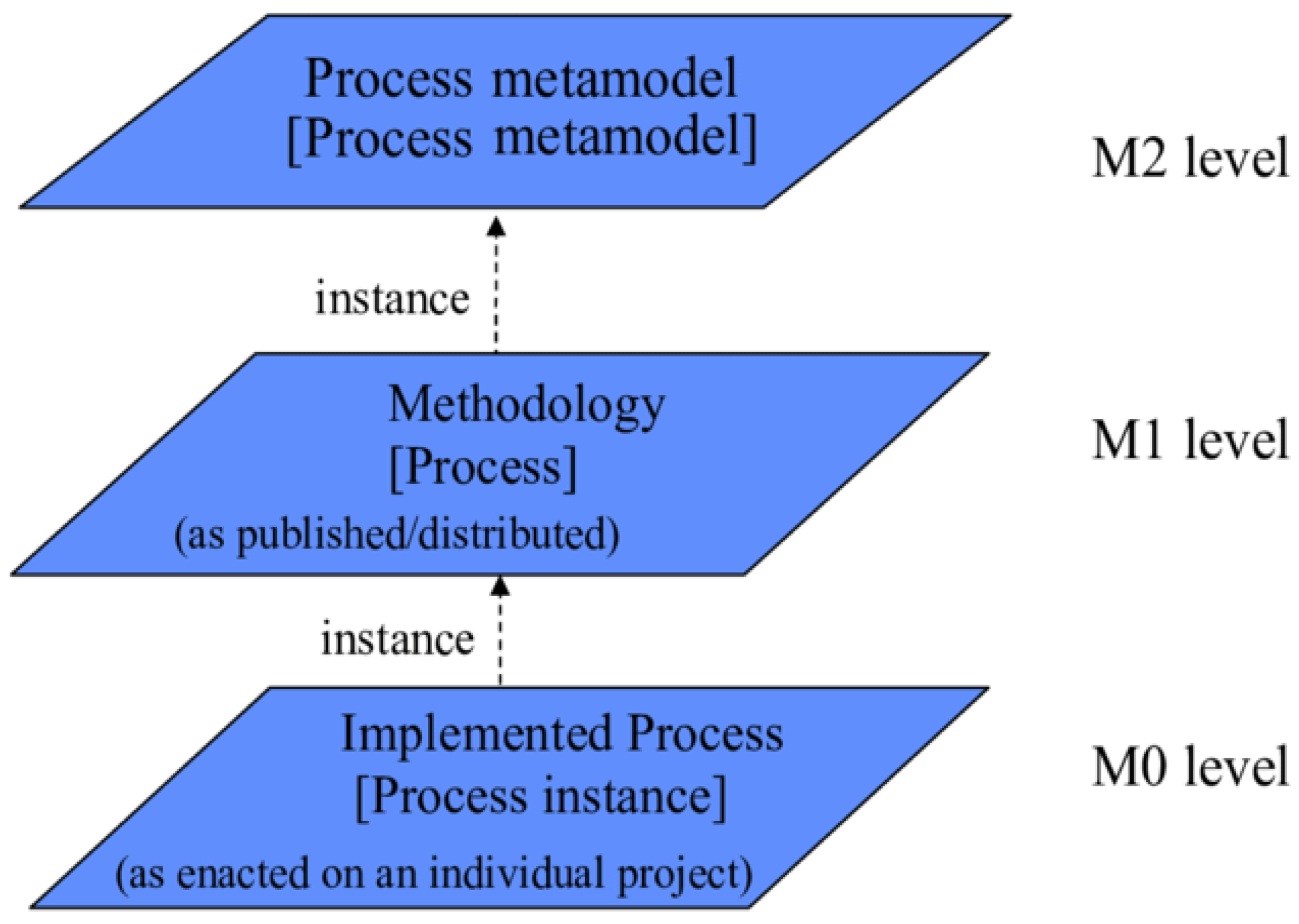
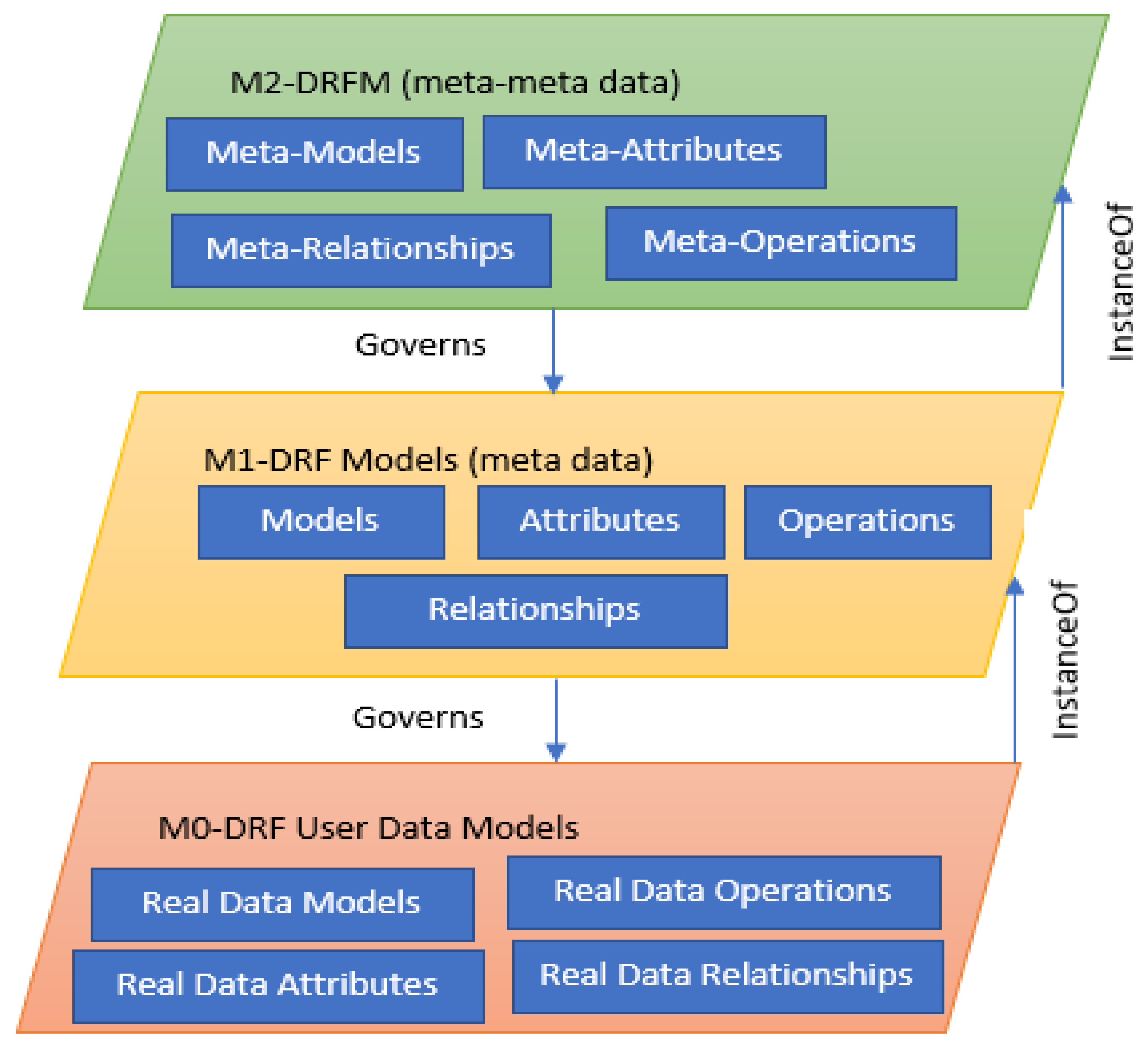
- Developing a high abstract model (DRFM) using a metamodeling approach
- Validating the developed DRFM
2. Related Works
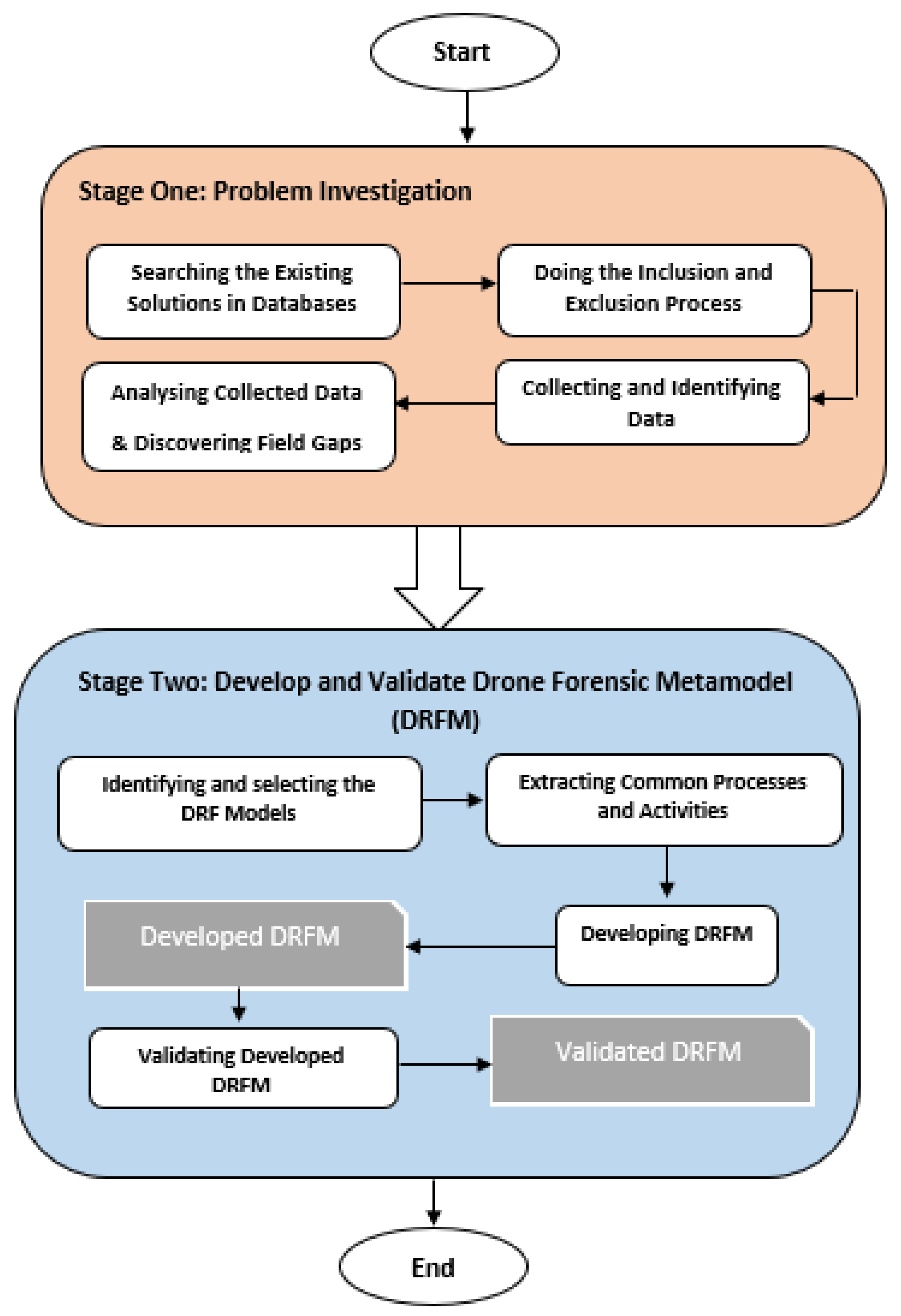
3. Research Methodology
3.1. Stage 1: Problem Investigation
- (1)
- Searching the Existing Solutions in Databases: At this step, the existing solutions are searched in five well-known databases: IEEE Explorer, Web of Science, Springer, Scopus, and Google Scholar. The search is based on keywords like drone forensics and UAV;
- (2)
- Doing the Inclusion and Exclusion Process: This step excludes the searched solutions. The searched protocols are identified based on the research questions presented below:
- What are the existing models of the DRF?
- What are the current limitations, challenges, advantages, and disadvantages of the DRF domain?
- Is there a generic model for the DRF domain?
- (3)
- Collecting and Identifying Data: in this step, the authors collected data based on steps 1 and 2. The collected Data is refined based on year of publication, relevancy, and quality. Furthermore, only the papers that develop a framework, a model, or a procedure for conducting a forensic investigation on UAVs are selected. A further manual filtration approach is used where the title and name of the authors are considered to avoid duplications from multiple sources. Finally, based on the criteria mentioned above, 32 out of 102 first-selected articles were identified to be used in this study;
- (4)
- Analyzing Collected Data and Discovering Field Gaps: After a detailed review, it is clear that the DRF domain suffers from several challenges and issues, as discussed below:
- Challenges to the Investigation Process: DRF mainly has six investigation processes, and the challenge is to select the best one to have complete harmony with the drone actions. In general, vast volumes of data are produced by a drone device, which may consist of significant evidence; this affects the whole investigation process. It is not an easy task to identify the exact device involved in the crime. It also takes more time to identify the devices engaged in crimes;
- Lack of Log Standardization: Several investigation resources have the potential to aid the investigators in clearly understanding the complete action in the device; these resources include process logs, network logs, and application logs from various resources. However, the literature has not yet offered a clear standard for logging resources through different systems;
- The Volatility of Evidence The issues related to evidence volatility in drones are much more challenging than the conventional computing platforms. This is mainly because of the low memory of sensor devices.
- Proving Ownership: Sometimes, even if digital investigators seize a crime-involved drone, they cannot physically tie it to its owner. As the owner can deny the ownership, the investigators have to prove it forensically. This poses another challenge to the investigation process, which needs to be well addressed. The following question should be answered clearly: What digital forensic approach could an investigator take to identify a drone’s owner? To this end, first, the way the drone is manufactured (whether it records the information of the ground control station device or not) needs to be identified. In some cases, though, the ground control station records the drone’s information. Some manufacturers have no access to this feature since no mobile application could be utilized to control the drone, and everything is limited to the drone’s remote controller. Due to the high significance of the capability of proving the drones’ ownership, one of the hearings in the House of Lords in the UK is dedicated to discussing this subject [36];
- The Difficulty of Supporting the Newer Drone Devices: The currently used digital forensic techniques/tools fail to support the newer drone devices fully. This has led to many problems for digital investigators when there is a need to obtain data from such devices;
- The Absence of Strict Security Procedures: This domain still suffers from the deficiency of high-security procedures and policies, which has led to several drawbacks resulting, in turn, in cyber-incidents through the devices.
- Data Acquisition: A critical step in the digital forensics’ domain is to obtain the data in a completely safe mode and then determine the acceptability of the received data in a court of law. Based on the guidelines released by the National Institute of Standards and Technology (NIST), capturing data needs to be completely repeatable and authentic and preserve the integrity of the data. On the other hand, sometimes, the way a device has been built is a barrier to this objective. Drones are of several types; each device is different in how it can be connected. Some drones may need just a USB cable, while some others might connect through specific protocols such as FTP or Telnet. In addition, different brands of drones are different in the permissions granted when accessing the drone; in most cases, access is limited to only the media folder or the system files. In other words, any consistent means do not exist currently to conduct the acquisition process on drones; for this reason, each drone might need to be moved differently. To address such challenges and obtain more knowledge of drone forensics, we need to use innovative technologies together with the knowledge obtained from these studies as starting points toward deeper insights into drone infrastructures.
- The diversity of Devices, Operation Systems, and Infrastructures: Drones are devices that run with Operation Systems (OSs) and infrastructures, making drone forensic investigation more complex. Attackers also use such characteristics in their destructive activities.
- Flight Data: Drones are devices that run with Operation Systems (OSs) and infrastructures, making drone forensic investigation more complex. Attackers also use such characteristics in their destructive activities; Flight Data: The flight data need to be recovered to identify a seized drone’s flight path or determine whether the drone has entered a restricted area. The reconstruction of the drone’s flight path could help this objective, but the problem is that different drones are using other methods to record the flight data, and some may not record such data at all. In some cases, the investigators may even encounter a drone with encrypted flight data. In these cases, not a single person but the technical team members who have the encrypting keys can access the flight data. Criminals usually use anti-forensic techniques such as encryption to prevent digital investigators from gaining access to their data. It should be noted that the more critical challenge here is not finding a way to access the encrypted data. Instead, it is finding the best way to deal with those drones that cannot record flight data. According to the authors in [37], changing the scope of information processing at independent locations makes it more difficult to uphold integrity, confidentiality, and accessibility, whereas carrying out an investigation could be applied to drones.
- Media Taken by the Drone: To approve or reject the violation of the law by a drone, it is important to consider its flight path and the photos and videos taken by the drone to check whether or not it has violated others’ privacy. Such violation of privacy has been properly documented across the world. For instance, in Kentucky, the United States, a man shot a drone with a shotgun since the drone was flying above his house, and he decided to shoot it to protect his privacy [38]. The claim was accepted in the court of law, and the man was dismissed from all charges [37]. In [39], the authors discussed an incident in Sydney, Australia, where a drone was flying around the beach and taking photos of people, and the drone operator was unknown [39]. In addition, as a predictor of a privacy violation, the media content recorded by the drone can provide a clue as to the drone’s owner since the photos consist of some EXIF data storing the image location. The EXIF data can help forensic investigators to reconstruct the flight path from the flight data through the reconstruction of the metadata stored in the photos.
3.2. Stage 2: Develop and Validate Drone Forensic Metamodel (DRFM)
- Identifying and selecting the DRF Models: The models identified and selected at this step are based on coverage, as discussed in [40,41]. The vast convergence of concepts and terminologies is broadly applicable to fulfilling the requirements of the investigation process in DRF. The coverage metrics indicated the sourced model applicability. If the model wants to cover all DRF perspectives (i.e., technology perspective and investigation process perspective), the model should have high coverage. The model has a reduced amount of coverage value if the model only describes a specific DRF perspective, such as the technology perspective. Therefore, models (tools, methods, and algorithms) cover at least two DRF processes, i.e., investigation and technologies. These factors were identified to develop DRFM. However, the existing systems only cover the specific DRF with only one or two perspectives and are set for validation purposes;
- Extracting Common Processes and Activities: The DRF investigation processes and activities were derived from the models selected in Step 1. Certain criteria [35,41] were followed for the investigation processes during the extraction. The criteria used to determine the DRF investigation processes and activities are as follows:
- Extracting the investigation process from the main model design and its phases;
- The investigation process should be based on actions to extract the main objectives, purpose, and process;
- Avoiding any irrelevant material which is not related to DRF investigation processes;
- Select the clear and implicit investigation processes used in existing models.
- The above-discussed criteria and the processes were adopted to design the proposed DRFM.
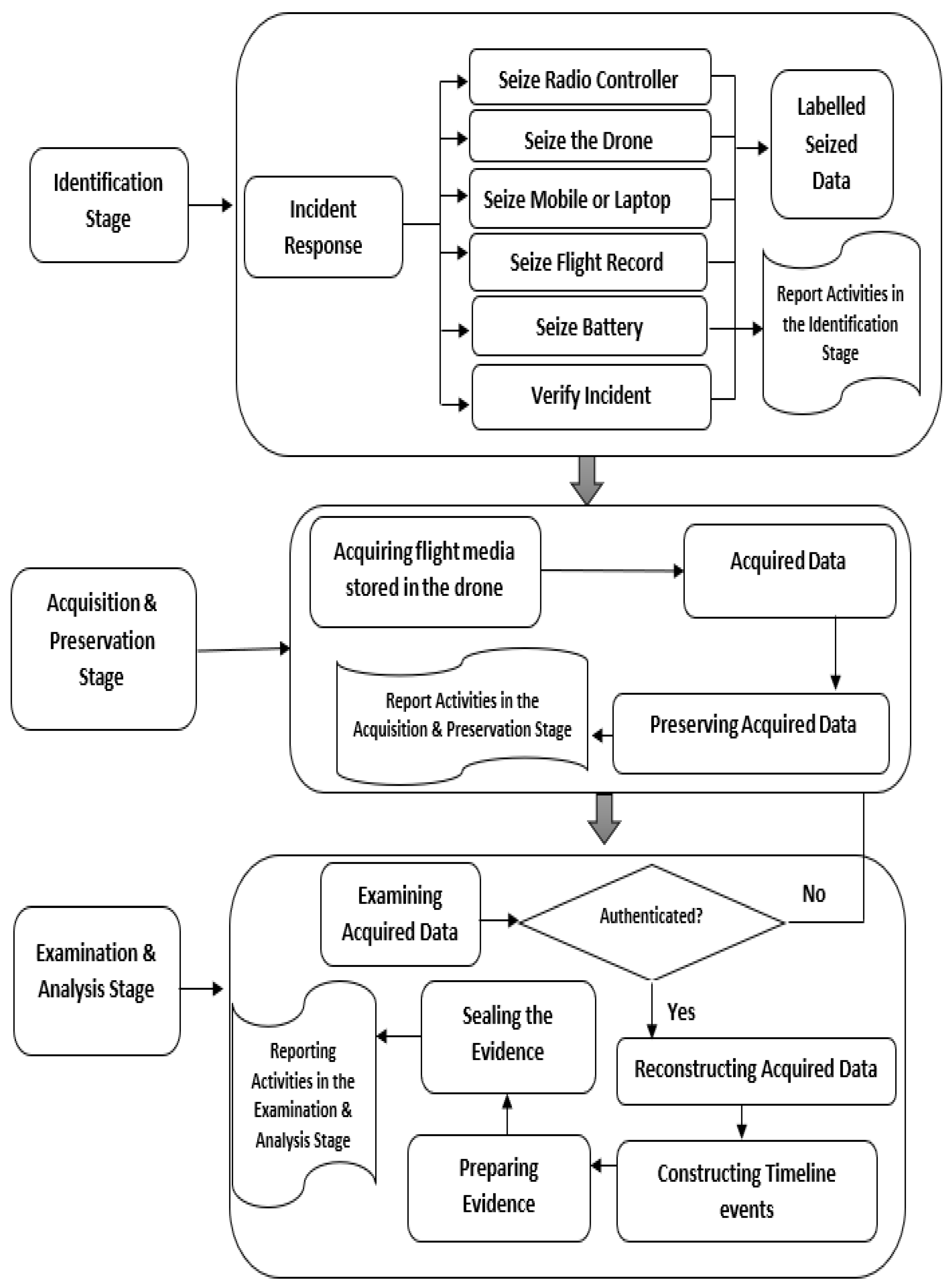
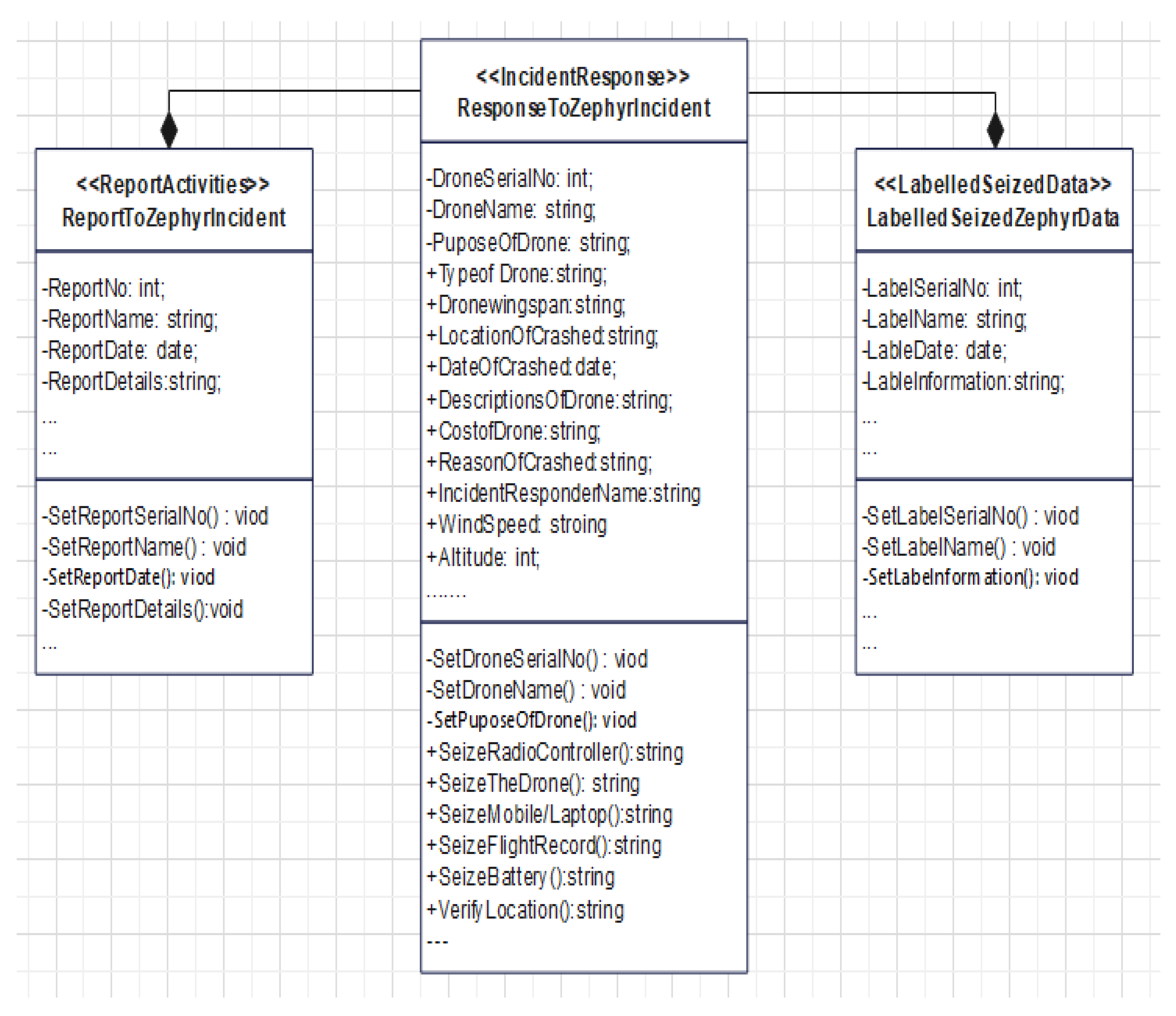
- Developing Drone Forensic Metamodel
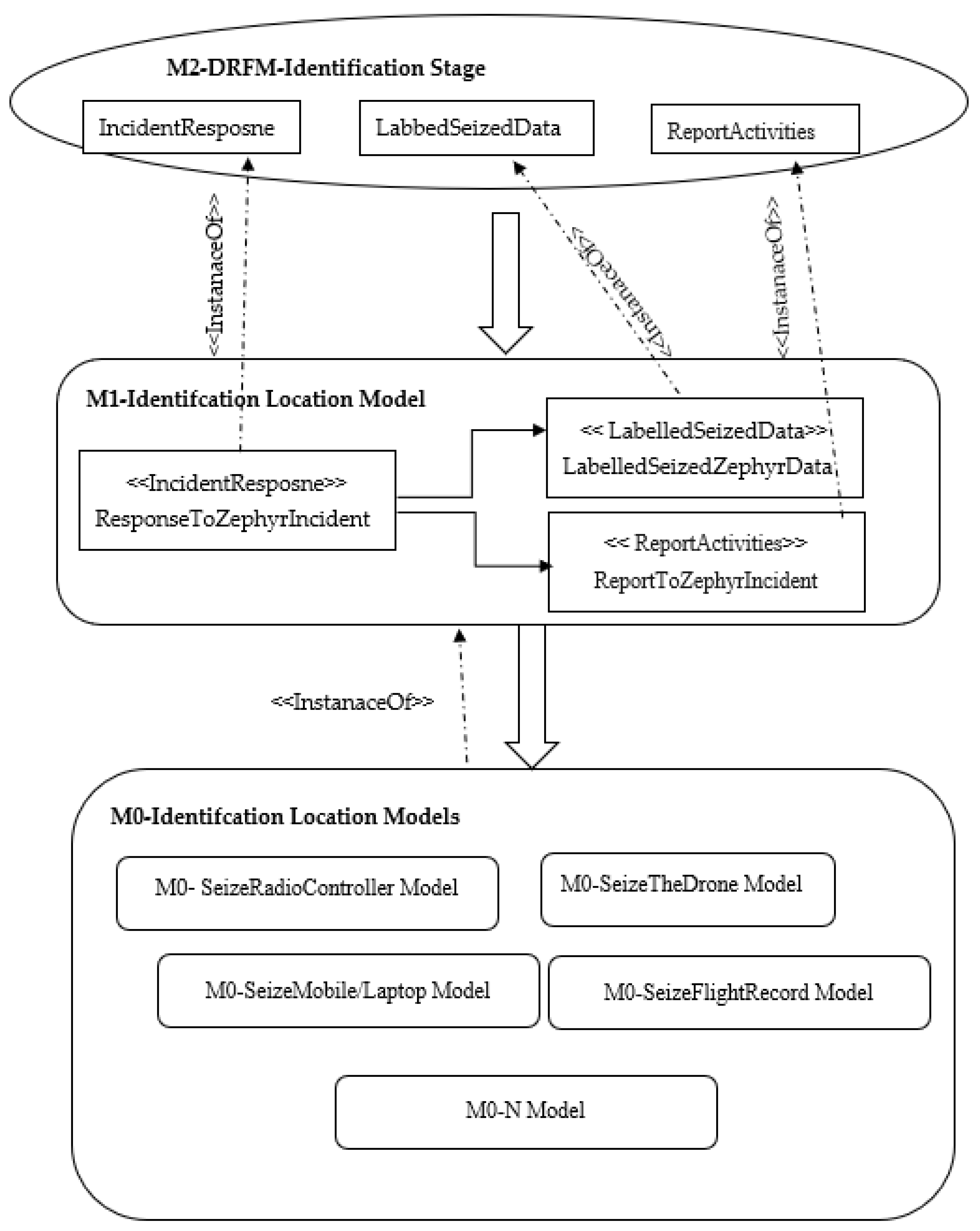
- Stage 1: Identification Stage
- Seize the Drone: In this activity, the first responder needs to search and seize the drone device, take a photo, and document it;
- Seize Radio Controller: The radio controller should be seized for examination during the DRF investigation. Although, this component is less important because it has the configuration settings that are stored and can contribute to understanding the scenario of the drone and its operation;
- Seize Mobile or Laptop: The mobile or laptop is used to manage and handle the drone device, which should be seized and moved to the lab.
- Seize Flight Record: The mobile or laptop is used to manage and handle the drone device, which should be seized and moved to the lab;
- Seize Battery and the Wi-Fi: The battery and Wi-Fi components and range are valuable in the DRF investigation. The battery is used to run the drone, whereas the Wi-Fi range extender provides a communication range to the drone. The battery stores the digital artifacts; thus, it is useful to extract the battery information [43];
- Label the Seized Data: The seized data should be marked and sent to the lab;
- Report Activities in the Identification Stage: Documenting and reporting are fundamental steps in the identification stage.
- Stage 2: Acquisition and Preservation Stage
- Acquiring Flight Media Stored in the Drone: In this process, the investigator uses some trusted mobile tools to acquire the flight media stored in the drone, for example, by using the DJI GO app [44], where the mobile device is attached with the drone and connected with remote control for flight data storage. The micro-SD card is used to store the data, which is installed under the hood of the drone. The DJI GO application is used to connect the drone with a computer for data removal and storage processes;
- Acquired Data: It is the data acquired from the drone. It includes photos, videos, and GPS paths.
- Preserving the Acquired Data: The acquired data must be preserved to protect its data integrity. The investigator should use a strong hash algorithm to protect the authenticity of the gathered data;
- Reporting the Acquisition and Preservation Stage: All the acquisition and preservation stages’ steps, activities, and processes should be documented and reported.
- Stage 3: Examination and Analysis Stage
- Examining the Acquired Data: The data acquired and preserved in the previous stage should be examined to check and verify the authenticity of the data [42]. Examiner should rehash the hashed value of the received data and check the consistency of the data. If the data is changed or modified, the examiner should return to the previous stage and collect another original copy. However, if the information is correct and has no tamper, the examiner should proceed to the next step to reconstruct the acquired data;
- Reconstructing the Acquired Data: The data examined is reconstructed to extract the evidence explaining the causes of the crime committed;
- Constructing the Timeline Events: This task can be carried out after a valid data integrity verification. This task is used to rebuild the timeline of the UAV events and reveal the evidence of the crime. Particular emphasis is expected to be taken on this step as the accuracy of the entire investigation process hinges on the accuracy of the event timeline reconstruction. Furthermore, the logic of timeline reconstruction posits that event sequencing and correlation during an investigation are built on the integrity of the reconstructed time-of-event occurrence;
- Preparing the Evidence: In this process, the investigators must identify the evidence and provide a detailed explanation. This step answers the question of who, what, when, where, and potentially, why based on the data. Who is the criminal? What time did the crime happen? And how did the crime happen?
- Sealing the Evidence: This process is used to protect the integrity of the evidence while sending it to the court.
- Reporting the Activities in the Examination and Analysis Stage: Documenting and reporting whole activities in the examination and analysis stage.
- Validating Developed Drone Forensic Metamodel
4. Finding and Discussion
- The model provides communication among drones through a common layer that employs all tasks, concepts, activities, and processes for DRF;
- It provides a conceptual roadmap to design an effective model to manage, reuse, and share DRF knowledge and information;
- It is easily applicable, especially for DRF practitioners, to design and create new solutions by using all the attributes and operations based on the model requirements;
- It provides quick access to DRF knowledge and helps to design new solutions.
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Kovar, D.; Dominguez, G.; Murphy, C. UAV (aka drone) Forensics. In Proceedings of the SANS DFIR Summit, Online, 9 October 2016; pp. 23–24. [Google Scholar]
- Al-Dhaqm, A.; Ikuesan, R.A.; Kebande, V.R.; Razak, S.; Ghabban, F.M. Research Challenges and Opportunities in Drone Forensics Models. Electronics 2021, 10, 1519. [Google Scholar] [CrossRef]
- Abdullah, A.; Othman, S.H.; Razali, M.N. Structuring knowledge on house Price Volatility through a metamodel. ARPN J. Eng. Appl. Sci. 2015, 10, 17785–17795. [Google Scholar]
- Colette, R. Modeling the Requirements Engineering Process. In Proceedings of the 3rd European-Japanese Seminar on Information Modelling and Knowledge Bases, Budapest, Hungary, 31 May–3 June 1993. [Google Scholar]
- Mhatre, V.; Chavan, S.; Samuel, A.; Patil, A.; Chittimilla, A.; Kumar, N. Embedded video processing and data acquisition for unmanned aerial vehicle. In Proceedings of the 2015 International Conference on Computers, Communications, and Systems (ICCCS), Kanyakumari, India, 2–3 November 2015; pp. 141–145. [Google Scholar]
- Roder, A.; Choo, K.-K.R.; Le-Khac, N.-A. Unmanned aerial vehicle forensic investigation process: Dji phantom 3 drone as a case study. arXiv 2018, arXiv:1804.08649. [Google Scholar] [CrossRef]
- Horsman, G. Unmanned aerial vehicles: A preliminary analysis of forensic challenges. Digit. Investig. 2016, 16, 1–11. [Google Scholar] [CrossRef]
- Ikuesan, R.A.; Ganiyu, S.O.; Majigi, M.U.; Opaluwa, Y.D.; Venter, H.S. Practical Approach to Urban Crime Prevention in Developing Nations. In Proceedings of the 3rd International Conference on Networking, Information Systems & Security, Marrakech, Morocco, 31 March–2 April 2020; pp. 1–8. [Google Scholar]
- Maarse, M.; Sangers, L.; van Ginkel, J.; Pouw, M. Digital Forensics on a DJI Phantom 2 Vision+ UAV; University of Amsterdam: Amsterdam, The Netherlands, 2016; Volume 1, p. 22. [Google Scholar]
- Procházka, T. Capturing, Visualizing, and Analyzing Data from Drones. Bachelor’s Thesis, Charles University, Prague, Czech Republic, 2016. [Google Scholar]
- Mohan, M. Cybersecurity in Drones. Ph.D. Thesis, Utica College, Utica, NY, USA, 2016. [Google Scholar]
- Jain, U.; Rogers, M.; Matson, E.T. Drone forensic framework: Sensor and data identification and verification. In Proceedings of the SAS 2017—2017 IEEE Sensors Applications Symposium, Glassboro, NJ, USA, 13–15 March 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Clark, D.R.; Meffert, C.; Baggili, I.; Breitinger, F. DROP (DRone open source parser) your drone: Forensic analysis of the DJI phantom III. Digit. Investig. 2017, 22, S3–S14. [Google Scholar] [CrossRef]
- Prastya, S.E.; Riadi, I.; Luthfi, A. Forensic Analysis of Unmanned Aerial Vehicle to Obtain GPS Log Data as Digital Evidence. Int. J. Comput. Sci. Inf. Secur. 2017, 15, 280–285. [Google Scholar]
- Bucknell, A.; Bassindale, T. An investigation into the effect of surveillance drones on textile evidence at crime scenes. Sci. Justice 2017, 57, 373–375. [Google Scholar] [CrossRef]
- Llewellyn, M. DJI Phantom 3-Drone Forensic Data Exploration; Edith Cowan University: Perth, Australia, 2017. [Google Scholar]
- Barton, T.E.A.; Azhar, M.A.H. Bin Forensic analysis of popular UAV systems. In Proceedings of the 2017 7th International Conference on Emerging Security Technologies (EST), Canterbury, UK, 6–8 September 2017; pp. 91–96. [Google Scholar] [CrossRef] [Green Version]
- Kebande, V.R.; Venter, H.S. Adding event reconstruction to a Cloud Forensic Readiness model. In Proceedings of the 2015 Information Security for South Africa (ISSA), Johannesburg, South Africa, 12–13 August 2015; pp. 1–9. [Google Scholar]
- Bouafif, H.; Kamoun, F.; Iqbal, F.; Marrington, A. Drone Forensics: Challenges and New Insights. In Proceedings of the 2018 9th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Paris, France, 26–28 February 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Esteves, J.L.; Cottais, E.; Kasmi, C. Unlocking the Access to the Effects Induced by IEMI on a Civilian UAV. In Proceedings of the 2018 International Symposium on Electromagnetic Compatibility (EMC EUROPE), Amsterdam, The Netherlands, 7–30 August 2018; pp. 48–52. [Google Scholar]
- Gülataş, İ.; Baktır, S. Unmanned aerial vehicle digital forensic investigation framework. J. Nav. Sci. Eng. 2018, 14, 32–53. [Google Scholar]
- Dawam, E.S.; Feng, X.; Li, D. Autonomous arial vehicles in smart cities: Potential cyber-physical threats. In Proceedings of the 2018 IEEE 20th International Conference on High Performance Computing and Communications; IEEE 16th International Conference on Smart City; IEEE 4th International Conference on Data Science and Systems (HPCC/SmartCity/DSS), Exeter, UK, 28–30 June 2018; pp. 1497–1505. [Google Scholar]
- Renduchintala, A.; Jahan, F.; Khanna, R.; Javaid, A.Y. A comprehensive micro unmanned aerial vehicle (UAV/Drone) forensic framework. Digit. Investig. 2019, 30, 52–72. [Google Scholar] [CrossRef]
- Renduchintala, A.L.P.S.; Albehadili, A.; Javaid, A.Y. Drone Forensics: Digital Flight Log Examination Framework for Micro Drones. In Proceedings of the International Conference Computational Science Computational Intelligence CSCI 2017, Las Vegas, NV, USA, 14–16 December 2017; pp. 91–96. [Google Scholar]
- Fitwi, A.; Chen, Y.; Zhou, N. An agent-administrator-based security mechanism for distributed sensors and drones for smart grid monitoring. In Proceedings of the Signal Processing, Sensor/Information Fusion, and Target Recognition XXVIII, Baltimore, MD, USA, 14–18 April 2019; p. 19. [Google Scholar] [CrossRef]
- Jones, Z.V.; Gwinnett, C.; Jackson, A.R.W. The effect of tape type, taping method and tape storage temperature on the retrieval rate of fibres from various surfaces: An example of data generation and analysis to facilitate trace evidence recovery validation and optimisation. Sci. Justice 2019, 59, 268–291. [Google Scholar] [CrossRef]
- Salamh, F.E.; Rogers, M. Drone Disrupted Denial of Service Attack (3DOS): Towards an Incident Response and Forensic Analysis of Remotely Piloted Aerial Systems (RPASs). In Proceedings of the 2019 15th International Wireless Communications & Mobile Computing Conference (IWCMC), Tangier, Morocco, 24–28 June 2019; pp. 704–710. [Google Scholar]
- Esteves, J.L. Electromagnetic Watermarking: Exploiting IEMI effects for forensic tracking of UAVs. In Proceedings of the EMC EUROPE—2019 International Symposium on Electromagnetic Compatibility, Barcelona, Spain, 2–6 September 2019; pp. 1144–1149. [Google Scholar] [CrossRef]
- Mei, N. Unmanned Aircraft Systems Forensics Framework an Approach to Unmanned Aircraft Systems Forensics Framework. Ph.D. Thesis, Capitol Technology University, Laurel, MD, USA, 2019. [Google Scholar]
- Le Roy, F.; Roland, C.; Le Jeune, D.; Diguet, J.P. Risk assessment of SDR-based attacks with UAVs. In Proceedings of the 2019 16th International Symposium on Wireless Communication Systems (ISWCS), Oulu, Finland, 27–30 August 2019; pp. 222–226. [Google Scholar] [CrossRef] [Green Version]
- Sciancalepore, S.; Ibrahim, O.A.; Oligeri, G.; Di Pietro, R. Detecting drones status via encrypted traffic analysis. In Proceedings of the WiseML 2019—ACM Workshop on Wireless Security and Machine Learning, Miami, FL, USA, 15–17 May 2019; pp. 67–72. [Google Scholar] [CrossRef]
- Lakew Yihunie, F.; Singh, A.K.; Bhatia, S. Assessing and Exploiting Security Vulnerabilities of Unmanned Aerial Vehicles. Smart Innov. Syst. Technol. 2020, 141, 701–710. [Google Scholar]
- March, S.T.; Smith, G.F. Design and natural science research on information technology. Decis. Support Syst. 1995, 15, 251–266. [Google Scholar] [CrossRef]
- Al-Dhaqm, A.; Razak, S.; Othman, S.H.; Ngadi, A.; Ahmed, M.N.; Mohammed, A.A. Development and validation of a database forensic metamodel (DBFM). PLoS ONE 2017, 12, e0170793. [Google Scholar] [CrossRef] [PubMed]
- Al-Dhaqm, A.; Razak, S.; Othman, S.H.; Choo, K.-K.R.; Glisson, W.B.; Ali, A.; Abrar, M. CDBFIP: Common database forensic investigation processes for Internet of Things. IEEE Access 2017, 5, 24401–24416. [Google Scholar] [CrossRef]
- Kerner, M.; Berry, M.; Zammit, B.; Chongolnee, B. Drones vs. Privacy in The Modern Era; Benya Chongolnee: San Diego, CA, USA, 2017. [Google Scholar]
- Matyszczyk, C. Judge Rules Man Had Right to Shoot Down Drone over His House; CNET: San Francisco, CA, USA, 2015; Volume 28. [Google Scholar]
- Frank, M. Drone Privacy: Is Anyone in Charge; Consumer Reports; Available online: https://www.consumerreports.org/electronics/drone-privacy-is-anyone-in-charge-a1127325389/ (accessed on 11 February 2016).
- Gair, K. Privacy Concerns Mount as Drones Take to the Skies; CNET: San Francisco, CA, USA, 2015; Volume 12. [Google Scholar]
- Caro, M.F.; Josyula, D.P.; Cox, M.T.; Jiménez, J.A. Design and validation of a metamodel for metacognition support in artificial intelligent systems. Biol. Inspired Cogn. Archit. 2014, 9, 82–104. [Google Scholar] [CrossRef]
- Ali, A.; Abd Razak, S.; Othman, S.H.; Mohammed, A.; Saeed, F. A metamodel for mobile forensics investigation domain. PLoS ONE 2017, 12, e0176223. [Google Scholar] [CrossRef]
- Alotaibi, F.M.; Al-Dhaqm, A.; Al-Otaibi, Y.D. A Novel Forensic Readiness Framework Applicable to the Drone Forensics Field. Comput. Intell. Neurosci. 2022, 2022, 8002963. [Google Scholar] [CrossRef]
- Al-Room, K.; Iqbal, F.; Baker, T.; Shah, B.; Yankson, B.; MacDermott, A.; Hung, P.C.K. Drone Forensics: A Case Study of Digital Forensic Investigations Conducted on Common Drone Models. Int. J. Digit. Crime Forensics 2021, 13, 1–25. [Google Scholar] [CrossRef]
- Cabassi, J.; Lazzaroni, M.; Giannini, L.; Mariottini, D.; Nisi, B.; Rappuoli, D.; Vaselli, O. Continuous and near real-time measurements of gaseous elemental mercury (GEM) from an Unmanned Aerial Vehicle: A new approach to investigate the 3D distribution of GEM in the lower atmosphere. Chemosphere 2022, 288, 132547. [Google Scholar] [CrossRef]
- Mens, T.; Van Gorp, P. A taxonomy of model transformation. Electron. Notes Theor. Comput. Sci. 2006, 152, 125–142. [Google Scholar] [CrossRef] [Green Version]
- Štuikys, V.; Damaševičius, R. A model-driven view to meta-program development process. In Meta-Programming and Model-Driven Meta-Program Development; Springer: Berlin/Heidelberg, Germany, 2013; pp. 127–142. [Google Scholar]
- Gardner, T.; Griffin, C.; Koehler, J.; Hauser, R. A review of OMG MOF 2.0 Query/Views/Transformations Submissions and Recommendations towards the final Standard. In MetaModelling for MDA Workshop; Citeseer: Princeton, NJ, USA, 2003; Volume 13, p. 41. [Google Scholar]
- France, R.; Bieman, J.M. Multi-view software evolution: A UML-based framework for evolving object-oriented software. In Proceedings of the IEEE International Conference on Software Maintenance, ICSM 2001, Florence, Italy, 7–9 November 2001; pp. 386–395. [Google Scholar]
- Sargent, R.G. Model verification and validation. In Modeling and Simulation in the Systems Engineering Life Cycle; Springer: Berlin/Heidelberg, Germany, 2015; pp. 57–65. [Google Scholar]
- Rose, L.M.; Kolovos, D.S.; Paige, R.F.; Polack, F.A.C. Model migration with epsilon flock. In Proceedings of the International Conference on Theory and Practice of Model Transformations, Málaga, Spain, 28 June–2 July 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 184–198. [Google Scholar]
- Henderson-Sellers, B. Bridging metamodels and ontologies in software engineering. J. Syst. Softw. 2011, 84, 301–313. [Google Scholar] [CrossRef]
- Corfield, G. Second MoD Airbus Zephyr Spy Drone Crashes on Aussie Test Flight. 2019. Available online: https://www.theregister.com (accessed on 11 October 2019).
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alhussan, A.A.; Al-Dhaqm, A.; Yafooz, W.M.S.; Razak, S.B.A.; Emara, A.-H.M.; Khafaga, D.S. Towards Development of a High Abstract Model for Drone Forensic Domain. Electronics 2022, 11, 1168. https://doi.org/10.3390/electronics11081168
Alhussan AA, Al-Dhaqm A, Yafooz WMS, Razak SBA, Emara A-HM, Khafaga DS. Towards Development of a High Abstract Model for Drone Forensic Domain. Electronics. 2022; 11(8):1168. https://doi.org/10.3390/electronics11081168
Chicago/Turabian StyleAlhussan, Amel Ali, Arafat Al-Dhaqm, Wael M. S. Yafooz, Shukor Bin Abd Razak, Abdel-Hamid M. Emara, and Doaa Sami Khafaga. 2022. "Towards Development of a High Abstract Model for Drone Forensic Domain" Electronics 11, no. 8: 1168. https://doi.org/10.3390/electronics11081168
APA StyleAlhussan, A. A., Al-Dhaqm, A., Yafooz, W. M. S., Razak, S. B. A., Emara, A.-H. M., & Khafaga, D. S. (2022). Towards Development of a High Abstract Model for Drone Forensic Domain. Electronics, 11(8), 1168. https://doi.org/10.3390/electronics11081168






