A Multiple End-Devices Authentication Scheme for LoRaWAN
Abstract
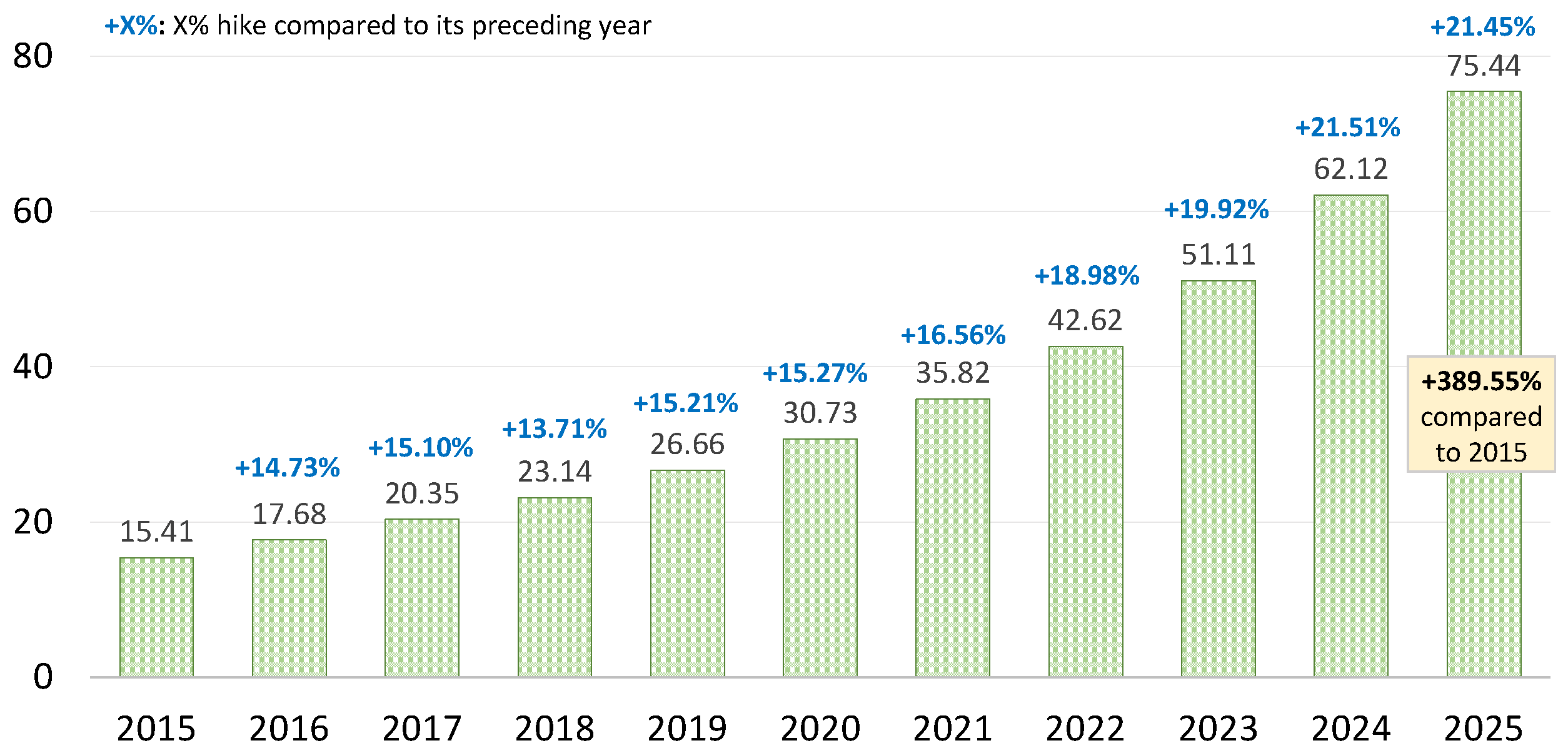
:1. Introduction
- Smart city management: Connecting all the assets of the city and providing better services by collecting data and analyzing data, including waste management, parking, street lighting, and public safety data.
- Asset tracking: Obtaining location information for people and private assets, including equipment, vehicles, pets, and cattle.
- Gas and water metering: Enabling utility customers to remotely read and control gas and water meters to reduce technical costs.
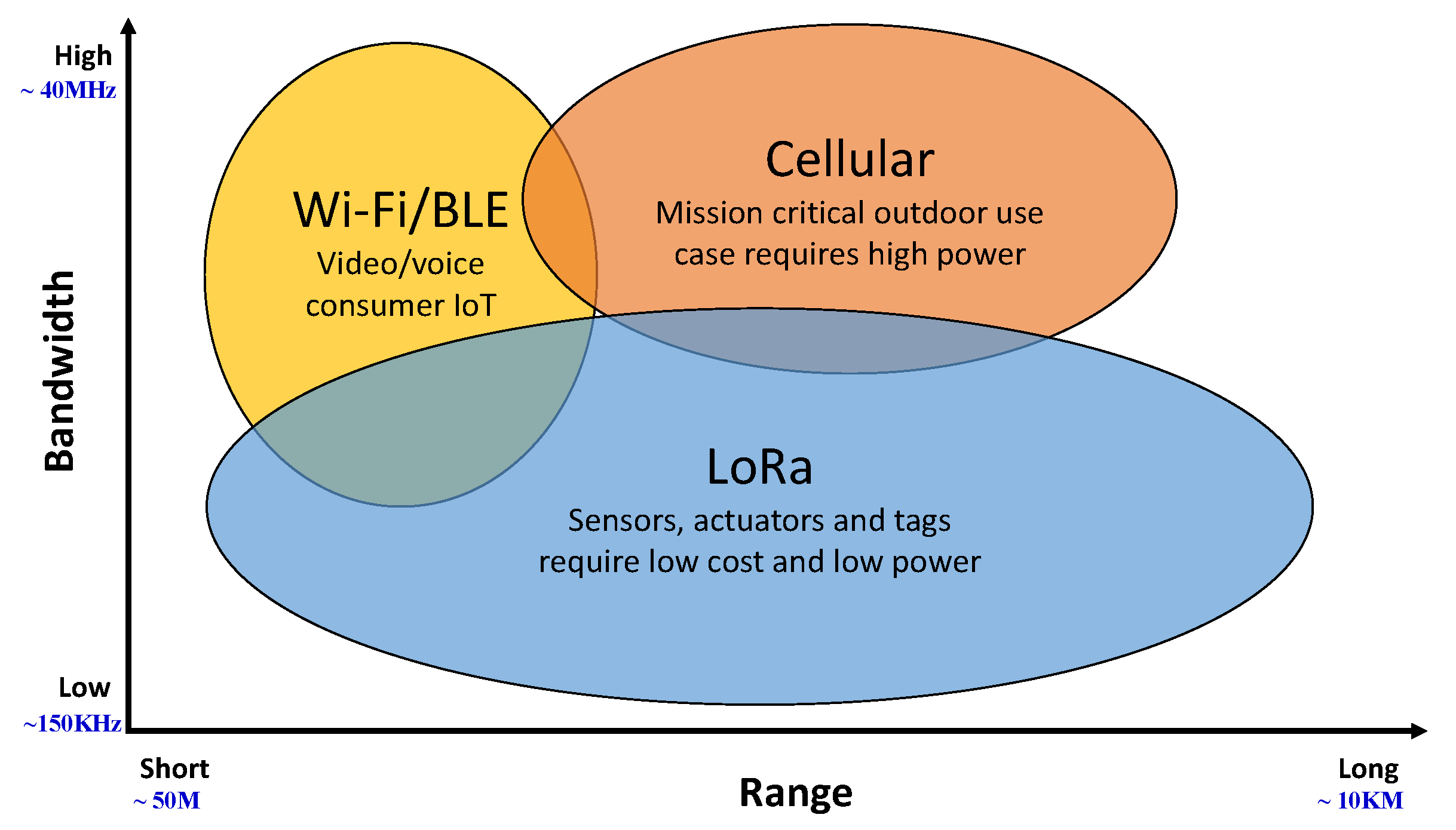
- Long range: Not only can LoRaWAN serve indoor applications in unlicensed bands such as Wi-Fi, but it can also support outdoor applications with the same security as a cellular network [14]. As a result, it can connect to a broader range of networks than Wi-Fi and cellular networks.
- Max lifetime: Asynchronous communication is the most extensively utilized mode for end-devices in the LoRaWAN network. End-devices only communicate over the network when sending event-driven or planned data. As a result, they can conserve the wake-up monitoring power. End-devices in other synchronous networks must wake up frequently in order to synchronize with the network and verify messages, which consumes more power.
- Multi-usage: Depending on the environment, the LoRaWAN network may handle public networks with a significant capacity of hundreds or even tens of thousands of nodes. As a result, it can meet the needs of large online communities or markets [15].
- Low cost: Low power consumption in LoRa end devices enhances battery life and lowers battery replacement expenses. Semtech has also made the hardware and software designs for the gateway and end-devices public. This can help to save money on infrastructure and terminal device development.
- Device classes: End-devices are used for a variety of purposes and have varying needs. LoRaWAN has created three end-device categories, dubbed class A, B, and C, to optimize diverse end-application profiles to balance network downlink communication delays and battery life.
1.1. Contributions
- We offer a comprehensive authentication strategy based on the linked end-device(s) features that use exclusive-OR operations to achieve batch authentication.
- The suggested technique allows several end-devices of the same gateway to generate group keys. Supporting group key creation may be helpful for future applications because end-devices from the same gateway may have specific correlations. Furthermore, each end-device requires one additional hash operation.
- Under the formal model, the new technique is protected against major threats such as phoney end-devices, network servers, and the leakage of session keys.
- Considering multi-end-device authentication, the suggested technique saves overall execution time by around 33% compared to the LoRA Specification.
1.2. Organization
2. Preliminaries
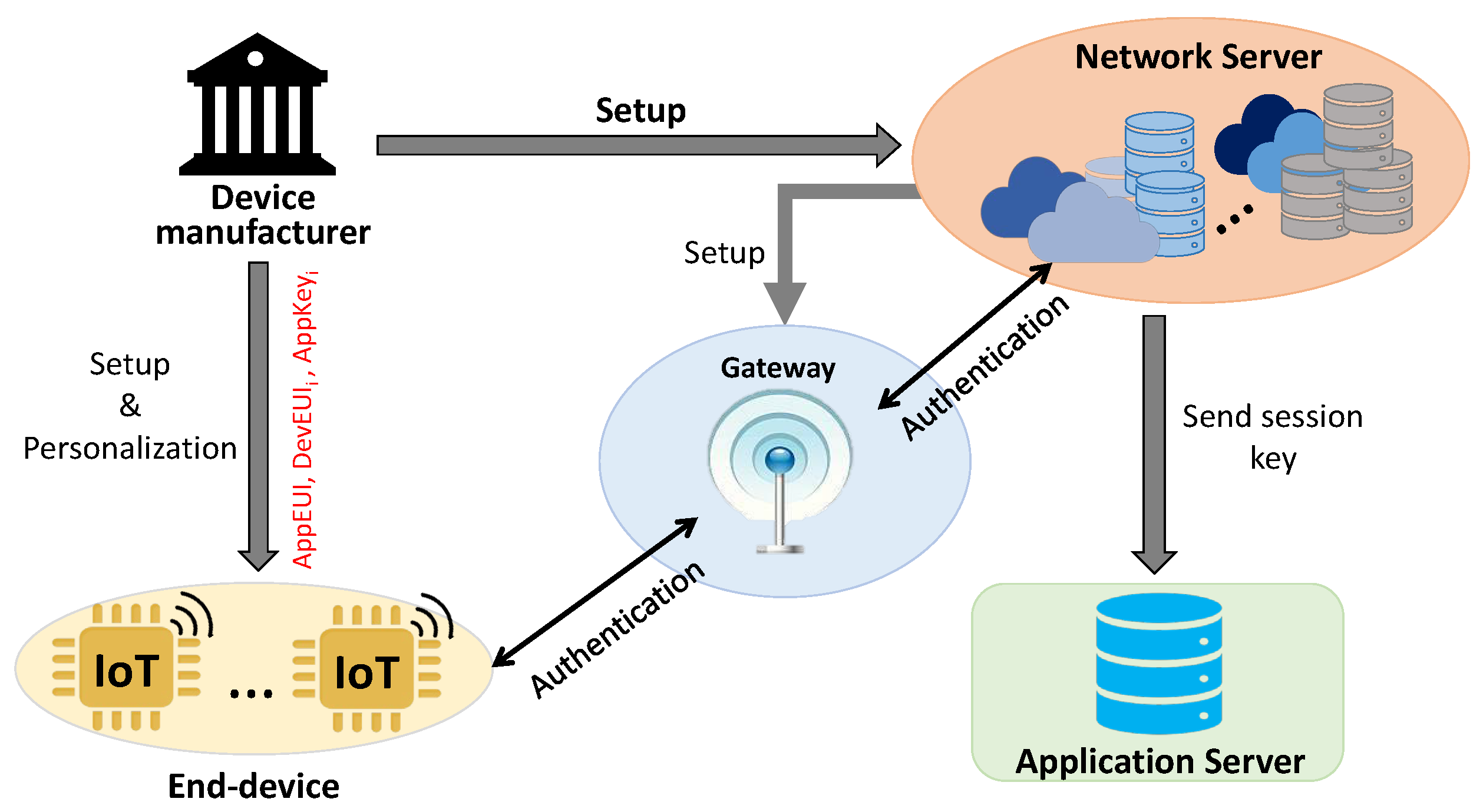
2.1. The LoRaWAN Architecture
- End-Devices: These could be anything from water meters to smoke alarms to trash cans and pet trackers. LoRaWAN divides end-devices into classes A, B, and C. Each type of device fulfills various long-distance communication requirements.
- -
- Class A: This is the most basic communication mode, with minor power consumption. It transmits data in bursts. As a result, network servers and applications cannot predict the communication time. Class A refers to end-devices that only require upload link communications.
- -
- Class B: Class B end-devices will open additional receive windows at predetermined times in addition to the random receive windows of class A devices. The gateway will send a time synchronization signal to the end-devices in order for them to open the receive windows on a predetermined schedule. As a result, the network server knows when the end-devices are listening.
- -
- Class C: The receive windows on class C end-devices are almost always open and only close when transmitting. This end-device consumes the most power, while having the shortest delay because these receive windows remain open.
- Gateways: A device in the LoRaWAN network is not assigned to a specific gateway. Instead, data sent by a node are typically received by multiple gateways. Each gateway will route data packets from the end node to the cloud-based network server via backhaul cellular or Ethernet networks.
- Network Server: This is in charge of managing the entire network through specific functions. It deletes redundant packets and runs security checks when it receives them from gateways. Finally, it sends back an accept message via the best gateway.
- Application Servers: This is in charge of interpreting data from end-devices and solving problems with advanced technologies such as deep learning or artificial intelligence.
2.2. The LoRaWAN Specifications
- Device EUI (DevEUI): The DevEUI is a global unique end-device identification number that is assigned by the device manufacturer.
- Application EUI (AppEUI): The AppEUI is a global unique application identification number, which is stored in the device in advance by the device manufacturer.
- Application key (AppKey): The AppKey is an AES-128 secret key stored in the end-device and used to derive two keys, NwkSKey and AppSKey.
- Device address (DevAddr): The DevAddr is a 32-bit hexadecimal number, which can be divided into two parts: the network identifier and network address.
- -
- Network identifier (NwkID): The NwkID is a 7-bit network identifier used to distinguish between the addresses of overlapping networks operated by different network operators.
- -
- Network address (NwkAddr): The NwkAddr is a 25-bit network address assigned by the network manager.
- Network session key (NwkSKey): The NwkSKey is a network session key which is used for MAC layer message encryption and authentication.
- Application session key (AppSKey) The AppSKey is an application session key which is used for application-layer message encryption and authentication.
2.2.1. End-Device Activation
2.2.2. Join Procedure
3. The Proposed Scheme
3.1. Setup
3.2. Personalization
- : an application global unique identifier
- : a global unique identifier of the end-device
- : a secret key shared between the end-device and the network server
3.3. Authentication
- Step 1: An end-device sends a join-request message to the network server to join the LoRaWAN network. The end-device
- -
- chooses at random and computes a message integrity code
- -
- sends Join-Request, which contains , and , to the network server.
- Step 2: To confirm the join-request, the network server sends a join-confirm message to the end-device. The network server waits until the authentication slot expires. It
- -
- checks the correctness of for each join-request received during the slot.
- If is invalid, then it aborts.
- Otherwise, it selects a random and a common random c.
- -
- It computes and sends it to end-device.
- Step 3: The end-device decrypts the join-confirm message and sends a response message to the gateway. The end-device
- -
- uses to get , and c by decrypting and
- -
- verifies whether is correct.If is incorrect, it aborts; otherwise, it stores c and sends to the gateway.
- Step 4: The gateway collects all the response messages at the time slot and sends a group-response message to the network server for the verification.
- -
- The gateway, on receiving from end-devices at the time slot, sends the group-response message to the network server.
- -
- The network server computes and verifies whether . If it does not hold, the gateway will send to the network server and the network server will verify of each end-device.
- Step 5: The network server sends a join-accept message to the end-devices and sends the session keys to the application server
- -
- The network server computesandand sends - to the end-device.
- -
- The end-device decrypts - with the corresponding . Then, the end-device verifies whether is valid. After that, both the network server and end-device compute a shared session key as
- -
- Finally, the network server sends the corresponding and to the application server for each end-device.
4. Security Assurance
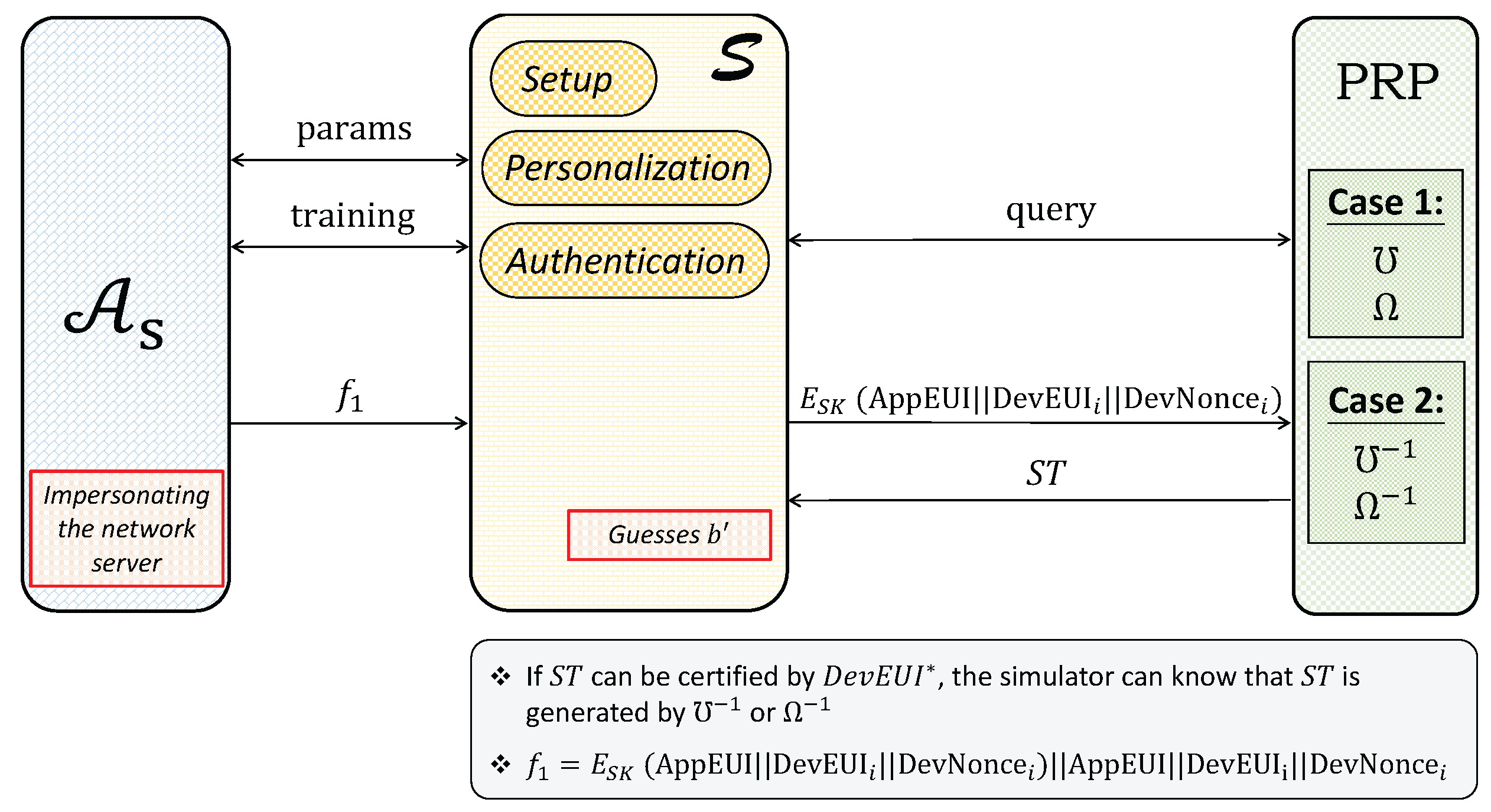
4.1. Security Model
- 1.
- Secure Authentication: outputs a target before the game starts.
- Setup: sends system public parameters and the symmetric functions , and sets the key and other public parameters as in the original scheme.
- Training: queries the two oracles as follows:
- -
- Personalization: inputs . If , then sends data transmitted in the personalization phase to . Otherwise, aborts.
- -
- Authentication: inputs and . sends the packages transmitted in the authentication phase to .
- Challenge: picks one of the following two cases and sends to .
- impersonates a network server in the authentication phase to pass the verification. The advantage of winning the game for is .
- impersonates an end-device in the authentication phase to pass the verification. The advantage of winning the game for is .
- 2.
- Secure session key exchange: As like earlier, first outputs a target .
- Setup: sends system public parameters and the symmetric functions , and sets the key and other public parameters as in the original scheme.
- Training 1: queries the two oracles as follows.
- -
- Personalization: inputs . If , then sends data transmitted in the personalization phase to . Otherwise, aborts.
- -
- Authentication: inputs and and sends packages transmitted in the authentication phase to .
- Challenge: sends and two random numbers and . Then, randomly chooses . sends to , where c is a random number chosen by .
- Training 2: queries the same queries in Training 1.
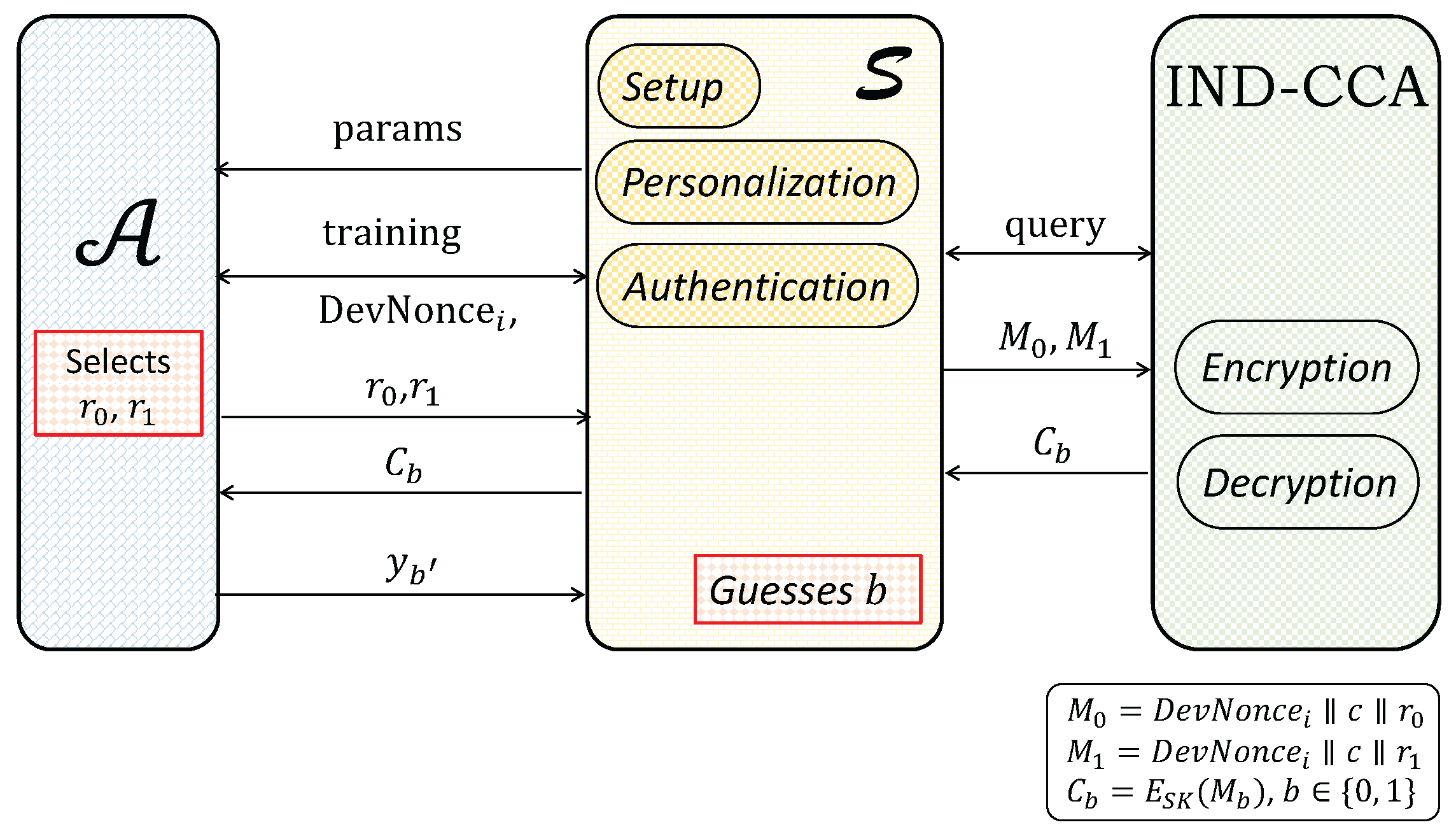
- Guess: guesses whether or 1. The advantage of winning the game for is defined as .
4.2. Security Proof
- Setup: sets the public parameters and the symmetric functions according to the pseudorandom permutation. After that, it sends the public parameters and the symmetric functions to .
- Training: simulates the following oracles for
- -
- Personalization: sends an end-device identity . If , then returns as in the actual scheme. Otherwise, aborts.
- -
- Authentication: sends and . If , executes the authentication phase of the proposed scheme. Otherwise, selects , c, and , and then queries the encryption oracle of PRP to receive ciphertext and asThen, selects and queries the encryption oracle of PRP to encrypt , , , , and as ciphertext and , whereFinally, receives , , , and from the the simulator .
- Challenge: For , sends to , whereThen, sends to the PRP and chooses case 2 for the challenge. After that, the PRP randomly chooses . If , is a random string acquired by performing the function. If , is a pseudorandom string acquired by performing the decryption function on . As a result, the PRP game returns to .
- Guess: On receiving , checks if is equal to . If the condition is true, knows that is calculated by the decryption function , and thus sets ; otherwise, sets . Finally, sends guess to the PRP.
- Setup: sets the the public parameters and the symmetric functions according to the IND-CCA symmetric encryption process. Then, sends the public parameters and the symmetric functions to .
- Training: simulates the following oracles for as follows.
- -
- Personalization: inputs an end-device identity to . If , then returns and according to the proposed scheme. Otherwise, aborts.
- -
- Authentication: sends an end-device’s identity and . If , executes the authentication phase of the proposed scheme. Otherwise, selects , c, and , and then queries the encryption oracle of the IND-CCA symmetric encryption to encrypt , , , c and into ciphertext and asThen, selects and queries the encryption oracle of the IND-CCA symmetric encryption to encrypt system parameters: , , , , and to ciphertext and asFinally, receives , , , and from .
- Challenge: sends identity to , where . Then, chooses and to compute and . After that, sends to the IND-CCA oracles to start the challenge phase of the IND-CCA game. Finally, receives given from the encryption oracle and sends it to , where b, chosen by the encryption oracle, is unknown to .
- Guess: outputs a bit to . If , sets ; otherwise, sets . Finally, sends the guess to the IND-CCA game.
- Setup: sets the the public parameters and the symmetric functions according to the IND-CCA symmetric encryption. Then, sends the public parameters and the symmetric functions to .
- Training 1: simulates the following oracles for as follows.
- -
- Personalization: sends an end-device identity . If , then returns and , according to the proposed scheme. Otherwise, aborts.
- -
- Authentication: sends identity and to S. If , executes the authentication phase of the proposed scheme. Otherwise, selects , c and and then queries the encryption oracle of the IND-CCA symmetric encryption to encrypt , and to ciphertext and encrypts c and to ciphertext . Once, receives , it selects and queries encryption oracle of the IND-CCA symmetric encryption for , and gets ciphertext asFinally, receives , , , and from .
- Challenge: sends and of equal-length and , where . Then, computes and and sends to the IND-CCA oracles to start the challenge phase of the underlying IND-CCA game. After that, receives given from the encryption oracle and sends it to , where is unknown to .
- Training 2: can query the same queries as those in Training 1.
- Guess: The adversary outputs a bit to . If , sets ; otherwise, sets . Finally, sends the guess to the IND-CCA game.
5. Comparison
5.1. Security Properties
5.2. Computation Cost
5.3. Performance
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Basford, P.J.; Bulot, F.M.; Apetroaie-Cristea, M.; Cox, S.J.; Ossont, S.J. LoRaWAN for smart city IoT deployments: A long term evaluation. Sensors 2020, 20, 648. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Lima, E.; Moraes, J.; Oliveira, H.; Cerqueira, E.; Zeadally, S.; Rosário, D. Adaptive priority-aware LoRaWAN resource allocation for Internet of Things applications. Ad Hoc Netw. 2021, 122, 102598. [Google Scholar] [CrossRef]
- Ericsson, S. Internet of Things to Overtake Mobile Phones by 2018. Available online: http://www.satellitemarkets.com/market-trends/internet-things-overtake-mobile-phones-2018 (accessed on 2 March 2022).
- Statista, I. Internet of Things (IoT) Connected Devices Installed Base Worldwide from 2015 to 2025 (In Billions). Available online: https://statinvestor.com/data/33967/iot-number-of-connected-devices-worldwide/ (accessed on 2 March 2022).
- Alliance, L. LPWA Technologies Unlock New IoT Market Potential; White Paper; LoRa Alliance: Fremont, CA, USA, 2015; Available online: https://lora-alliance.org/resource_hub/lorawan-security-whitepaper/ (accessed on 2 March 2022).
- Sinha, R.S.; Wei, Y.; Hwang, S.H. A survey on LPWA technology: LoRa and NB-IoT. ICT Express 2017, 3, 14–21. [Google Scholar] [CrossRef]
- Navarro-Ortiz, J.; Sendra, S.; Ameigeiras, P.; Lopez-Soler, J.M. Integration of LoRaWAN and 4G/5G for the Industrial Internet of Things. IEEE Commun. Mag. 2018, 56, 60–67. [Google Scholar] [CrossRef]
- Noura, H.; Hatoum, T.; Salman, O.; Yaacoub, J.P.; Chehab, A. LoRaWAN security survey: Issues, threats and possible mitigation techniques. Internet Things 2020, 12, 100303. [Google Scholar] [CrossRef]
- Adelantado, F.; Vilajosana, X.; Tuset-Peiro, P.; Martinez, B.; Melia-Segui, J.; Watteyne, T. Understanding the limits of LoRaWAN. IEEE Commun. Mag. 2017, 55, 34–40. [Google Scholar] [CrossRef] [Green Version]
- Semtech. Why Lora®? Available online: https://www.semtech.com/lora/why-lora (accessed on 2 March 2022).
- Bocker, S.; Arendt, C.; Jorke, P.; Wietfeld, C. LPWAN in the Context of 5G: Capability of LoRaWAN to Contribute to mMTC. In Proceedings of the 2019 IEEE 5th World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 15–18 April 2019; pp. 737–742. [Google Scholar]
- Cisco. Cisco Solution for LoRaWAN. Available online: https://www.cisco.com/c/en/us/solutions/internet-of-things/lorawan-solution.html (accessed on 2 March 2022).
- LoRa Alliance. A Technical Overview of LoRa and LoRaWAN; LoRa Alliance: Fremont, CA, USA, 2015; Available online: https://www.everythingrf.com/whitepapers/details/2682-a-technical-overview-of-lora-and-lorawan (accessed on 2 March 2022).
- Butun, I.; Pereira, N.; Gidlund, M. Security risk analysis of LoRaWAN and future directions. Future Internet 2019, 11, 3. [Google Scholar] [CrossRef] [Green Version]
- Lombardo, A.; Parrino, S.; Peruzzi, G.; Pozzebon, A. LoRaWAN vs NB-IoT: Transmission Performance Analysis within Critical Environments. IEEE Internet Things J. 2021, 9, 1068–1081. [Google Scholar] [CrossRef]
- Chen, X.; Wang, J.; Wang, L. A fast session key generation scheme for LoRaWAN. In Proceedings of the 2019 Australian & New Zealand Control Conference (ANZCC), Auckland, New Zealand, 27–29 November 2019; pp. 63–66. [Google Scholar]
- Danish, S.M.; Lestas, M.; Asif, W.; Qureshi, H.K.; Rajarajan, M. A lightweight blockchain based two factor authentication mechanism for LoRaWAN join procedure. In Proceedings of the 2019 IEEE International Conference on Communications Workshops (ICC Workshops), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar]
- Tsai, K.L.; Leu, F.Y.; Hung, L.L.; Ko, C.Y. Secure session key generation method for LoRaWAN servers. IEEE Access 2020, 8, 54631–54640. [Google Scholar] [CrossRef]
- Jabbari, A.; Mohasefi, J.B. A Secure and LoRaWAN Compatible User Authentication Protocol for Critical Applications in the IoT Environment. IEEE Trans. Ind. Inform. 2021, 18, 56–65. [Google Scholar] [CrossRef]
- Kaven, S.; Bornholdt, L.; Skwarek, V. Authentication by rssi-position based localization in a lora lpwan. In Proceedings of the 2020 6th IEEE Congress on Information Science and Technology (CiSt), Agadir, Morocco, 5–12 June 2021; pp. 448–454. [Google Scholar]
- Gu, C.; Jiang, L.; Tan, R.; Li, M.; Huang, J. Attack-aware synchronization-free data timestamping in lorawan. ACM Trans. Sens. Netw. (TOSN) 2021, 18, 1–31. [Google Scholar] [CrossRef]
- Ertürk, M.A.; Aydın, M.A.; Büyükakkaşlar, M.T.; Evirgen, H. A survey on LoRaWAN architecture, protocol and technologies. Future Internet 2019, 11, 216. [Google Scholar] [CrossRef] [Green Version]
- Sornin, N.; Luis, M.; Eirich, T.; Kramp, T.; Hersent, O. Lorawan Specification; LoRa Alliance: Fremont, CA, USA, 2015; Available online: https://lora-alliance.org/resource_hub/lorawan-specification-v1-1/ (accessed on 2 March 2022).
- Eldefrawy, M.; Butun, I.; Pereira, N.; Gidlund, M. Formal security analysis of LoRaWAN. Comput. Netw. 2019, 148, 328–339. [Google Scholar] [CrossRef] [Green Version]
- Draft, F. Advanced Encryption Standard (AES); National Institute of Standards and Technology: Gaithersburg, MD, USA, 2001. [Google Scholar]
- Lavric, A.; Popa, V. Performance evaluation of LoRaWAN communication scalability in large-scale wireless sensor networks. Wirel. Commun. Mob. Comput. 2018, 2018, 1–10. [Google Scholar] [CrossRef] [Green Version]




| Notation | Meaning |
|---|---|
| Application global unique identifier | |
| Global unique identifier of the end-device i | |
| Secret key for the end-device i | |
| Nonce generated by the end-device i | |
| Message integrity code | |
| MAC function based on the AES-128 for secret key K and message M | |
| MAC header | |
| Random number for the end-device i | |
| c | Common random number |
| Network identifier | |
| Reserved field for the future use | |
| The delay field of the end-device i | |
| Optional list of channel frequencies | |
| Zero octets for padding such that data length is a multiple of 16 | |
| H | Hash function |
| Application session key for the end-device i | |
| Network session key for the end-device i | |
| Common session key |
| Security Properties | LoRaWAN Spec. | The Proposed Scheme |
|---|---|---|
| Mutual Authentication | Yes | Yes |
| Data Integrity Protection | Yes | Yes |
| Authentication of Multiple End-Devices | No | Yes |
| (a) The hardware information. | |
| Specification | Windows 10 64-bit |
| CPU | Intel(R) Core(TM) i5-8250U CPU @ 1.60GHz 1.80 GHz |
| RAM | 8.00 GB |
| Motherboard | KBL Strongbow KL |
| (b) Benchmark time. | |
| Operation | Time(s) |
| AES [25] encryption /decryption | 0.0209808 |
| XOR operation | 0.0009536 |
| Entity | LoRaWAN Specification | The Proposed Scheme |
|---|---|---|
| Each End-device | ||
| Gateway | — | |
| Network Server |
| Number of Devices | Overhead | Efficacy | |
|---|---|---|---|
| LoRaWAN Spec. | The Proposed Scheme | ||
| 50 | 31% | ||
| 100 | 32% | ||
| 1000 | 33% | ||
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fan, C.-I.; Zhuang, E.-S.; Karati, A.; Su, C.-H. A Multiple End-Devices Authentication Scheme for LoRaWAN. Electronics 2022, 11, 797. https://doi.org/10.3390/electronics11050797
Fan C-I, Zhuang E-S, Karati A, Su C-H. A Multiple End-Devices Authentication Scheme for LoRaWAN. Electronics. 2022; 11(5):797. https://doi.org/10.3390/electronics11050797
Chicago/Turabian StyleFan, Chun-I, Er-Shuo Zhuang, Arijit Karati, and Chun-Hui Su. 2022. "A Multiple End-Devices Authentication Scheme for LoRaWAN" Electronics 11, no. 5: 797. https://doi.org/10.3390/electronics11050797
APA StyleFan, C.-I., Zhuang, E.-S., Karati, A., & Su, C.-H. (2022). A Multiple End-Devices Authentication Scheme for LoRaWAN. Electronics, 11(5), 797. https://doi.org/10.3390/electronics11050797







