We carry out the informal/formal security analysis, such as “AVISPA implementation and ROR oracle model”. We demonstrate that PUF-PSS can prevent various cyber/physical security threats, including “impersonation, session key disclosure, and MITM attacks” and ensure “anonymity, perfect forward secrecy, and mutual authentications”.
5.1. Informal Security Analysis
We perform the “informal security analysis to prove the security of PUF-PSS”. We prove that PUF-PSS is able to prevent potential security threats and provide “secure anonymity, perfect forward secrecy, and mutual authentication”.
5.1.1. Impersonation Attack
We suppose that tries to impersonate by intercepting the exchanged messages of each participant over an open channel. However, cannot correctly generate the authentication request message , and response message , because does not receive the “random nonces and secret credentials ”. Thus, PUF-PSS is resilient to this attack since cannot calculate the valid authentication messages of each entity.
5.1.2. Physical Capture Attack
We assume that can physically capture any , and then extract all the secret credentials in the memory of a physically captured , compromising of the data from the ’s memory. However, there are independent and distinct factors for all deployed since and are randomly generated. Thus, the compromised data does not help in computing a session key between and an other non-compromised . Consequently, PUF-PSS is secure to this attack since the output of PUF challenge and response pair depends upon the intrinsic physical variations in the IC chip.
5.1.3. Replay Attack
If eavesdrops the transmitted messages over an open channel, tries to authenticate with other participants by retransmitting the intercepted messages from the previous session. However, in PUF-PSS, all of the entities check the freshness of the random nonces and . Moreover, the transmitted messages are protected with secret credentials and . Hence, PUF-PSS is resilient against replay attacks.
5.1.4. Session Key Disclosure Attack
should obtain the “PUF response and random nonces (short-term secrets)
and the long-term secrets credentials
to generate the correct
”. However,
cannot calculate because
is protected with the “shared secret key
, random number
, and PUF challenge
” using the hash function. Moreover,
cannot obtain
since
does not know the “real identity
of
and
, the secret credentials
, and PUF secret parameter
”. Thus, PUF-PSS is resilient to this attack under the CK model [
38] as the presented threat model in
Section 3.2.
5.1.5. Offline Password Guessing Attack
We suppose that attempts to guess the ’s password , and also extract all secret credentials in ’s memory using the differential power analysis. If can guess ’s , can calculate “several equations and the correct credentials with the guessed ”. However, should know a “unique biometric and a random number of ” to calculate the correct credentials and equations. Hence, is difficult to correctly guess ’s because cannot obtain the biometric and random number .
5.1.6. MITM Attack
We suppose that if can eavesdrop the transmitted messages through an open channel, then this attack may be possible. However, is unable to successfully calculate the authentication request and confirmation messages since cannot obtain the “random nonces , PUF secret parameter , biometric , real identity ”. Consequently, PUF-PSS can prevent this attack since cannot get the secret credentials of the legal entities.
5.1.7. Stolen Verifier Attack
We assume that steals the secret credential stored in S’s database and then tries to impersonate the legitimate participant. Even if obtains the secret credentials for and for stored in database of , cannot obtain sensitive information and impersonate as legitimate entities. Even if the secret credential for is revealed, does not obtain the sensitive information without the fresh random nonce , the correct shared secret key for and S. Moreover, the secret credential for is protected with the secret private key of S and the shared secret key by performing XOR and hash functions. PUF challenge/response pairs for are computationally difficult to compromise the PUF secret value because the output of PUF relies on the unique physical characteristics. Hence, PUF-PSS is resilient to this attack since cannot impersonate the legitimate participant because does not receive the sensitive data for and .
5.1.8. Ephemeral Secret Leakage (ESL) Attack
According to
Section 3.2, we assume that
can compromise the session states and secret credentials under the CK adversary model. If the short-term secrets
are revealed, an
is protected since
cannot obtain the sensitive information, such as the random nonces
and the real identities
. On the other hand, if the long-term secrets
are compromised, an
is still protected since
does not obtain the shared secret keys
, the biometric secret value
, and the PUF secret value
. Thus, PUF-PSS resists an ESL attack based on the CK model [
38].
5.1.9. Perfect Forward Secrecy
We assume that can obtain TMIS server S’s secret key . After that, attempts to compute a session key between and . However, cannot compute an because does not obtain the random nonces and the PUF value . Therefore, PUF-PSS scheme ensures perfect forward secrecy.
5.1.10. Mutual Authentication
During the authentication and key agreement process, all of the participants successfully perform mutual authentication. After getting the messages from the , S checks whether . If it is correct, S authenticates . After obtaining the messages from , S verifies whether . If the condition is correct, S authenticates . After getting the messages from S, checks whether . If it is valid, authenticates S. After obtaining the message from and S, verifies whether and . If it is correct, authenticates and S and establishes an . Consequently, all of the participants are “mutually authenticated because cannot calculate the authentication request and confirmation messages successfully”.
5.1.11. Anonymity
According to
Section 3.2,
can extract secret parameters stored in
and intercept the transmitted messages in each session. However,
cannot retrieve the “real identity
of
and
because the transmitted messages are masked with random nonce
, secret credentials
, biometric
and shared secret key
” using the PUF function, hash function, and XOR operation. Therefore, PUF-PSS guarantees the anonymity of
and
.
5.2. Formal Security Analysis Using BAN Logic
We demonstrate that PUF-PSS guarantees secure mutual authentication among
, and
S by performing BAN logic [
10]. We introduce the symbols in
Table 2 and also define rules, idealized forms, security goals, and assumptions for BAN logic.
- 1.
Message meaning rule (MMR):
- 2.
Nonce verification rule (NVR):
- 3.
- 4.
- 5.
5.2.1. Security Goals
We present the security goals of PUF-PSS to prove the BAN logic.
- Goal 1:
- Goal 2:
- Goal 3:
- Goal 4:
5.2.2. Idealized Forms
The idealized forms of the messages in PUF-PSS are as follows.
- :
- :
- :
- :
5.2.3. Assumptions
We present the assumptions of PUF-PSS as follows.
- :
- :
- :
- :
- :
- :
- :
- :
- :
- :
5.2.4. BAN Logic Proof
We then present the BAN logic proof as follows.
- Step 1:
Based on
, we obtain
- Step 2:
Using
and
with the MMR, we obtain
- Step 3:
Based on the
and
with the FR, we obtain
- Step 4:
Using
and
with the NVR, we obtain
- Step 5:
Based on the
with the BR, we obtain
- Step 6:
According to
, we obtain
- Step 7:
Using
and
with the MMR, we obtain
- Step 8:
Based on the
and
with the FR, we obtain
- Step 9:
Using
and
with the NVR, we obtain
- Step 10:
According to
, we obtain
- Step 11:
Using
and
with the MMR, we obtain
- Step 12:
Based on the
and
with the FR, we obtain
- Step 13:
Using
and
with the NVR, we obtain
- Step 14:
According to
, we obtain
- Step 15:
Using
and
with the MMR, we obtain
- Step 16:
Based on the
and
with the FR, we obtain
- Step 17:
Using
and
with the NVR, we obtain
- Step 18:
Based on the
with the BR, we obtain
- Step 19:
Using
and
with the JR, we obtain
- Step 20:
Because of
from
,
,
and
, we obtain
- Step 21:
Based on the
and
with the JR, we obtain
Consequently, we prove that , , and S are mutually authenticated because they achieve security goals 1–4.
5.3. Formal Security Analysis Using ROR Oracle Model
We evaluate a session key (SK) security of PUF-PSS from
under the ROR oracle model [
7]. We define the necessary queries for the ROR model [
7] as follows.
In PUF-PSS, there are three entities: the users
, the sensing devices
, and the TMIS server
, where
,
, and
are instances
of
,
of
, and
of
S, respectively.
Table 3 shows the necessary queries, including “
,
,
,
and
to perform security analysis”. Furthermore, we use a “hash function
, and a PUF function
as a random oracle”. We utilize Zipf’s law [
43] to prove the SK security of PUF-PSS.
Theorem 1. presents the “advantages of in violating SK security for PUF-PSS”. Hence, we derive the following: , , , and are “the range space of PUF , the range space of hash function , query, and the number of query”, respectively. In addition, , s, , and C are the Zipf’s credentials [43]. Proof. We introduce the five games (). We present that is the “probability of winning the ”. □
Game: “
is considered as an actual attack executed by
in PUF-PSS. The bit
c is randomly selected prior to the beginning of
”. Based on
, the result is as follows:
Game: “
presents that
executes an eavesdropping attack using
query.
perform
and
queries to reveal
. The output of the
and
queries decide if
gets the secret credentials and
. To reveal
,
needs the PUF value
and random nonces
. Thus,
’s probability of winning
by eavesdropping on the exchanged messages does not increase”. Based on
, the result is as presented below:
Game:
is considered as the “passive/active attacks by using
and
queries”.
can intercept the messages
,
,
, and
during the AKA process. All of the messages are not compromised by
since it is protected by using
with the random nonces
and
. Based on the birthday paradox [
44], the
’s result is as follows:
Game:
is an “extended game to
which the simulation of PUF query is included in this game”. By utilizing an analogous argument presented in
, this game’s results is presented below:
Game:
is modeled on the simulation of the
and
qeries.
is able to extract the secret parameters
in
memory by performing the differential power analysis. Note that
,
,
,
, and
. In addition,
can obtain the secret credentials
in
memory by performing physical capture attacks. Note that the PUF random challenge set
,
,
, and
. However, this game is computationally infeasible for
to compromise
over the
query without the
,
, and
. Moreover,
cannot distinguish the biometric and PUF value since the “probability of guessing the biometric credential of
bits and the PUF secret value of
by
is
and
”. Consequently,
and
are “indistinguishable if the off-line biometric or password guessing attacks are not implemented”. The
’s result is as follows:
After
are successfully executed,
tries to guess the “bit
c to win the games by performing
query”. Hence, we obtain the following:
Combining Formulas (1), (2) and (6), we obtain the following:
Based on the “triangular inequality with the Formulas (3)–(5) and (7)”, we obtain the following:
Finally, by multiplying both sides of Equation (
8) by a factor of 2, we obtain the following:
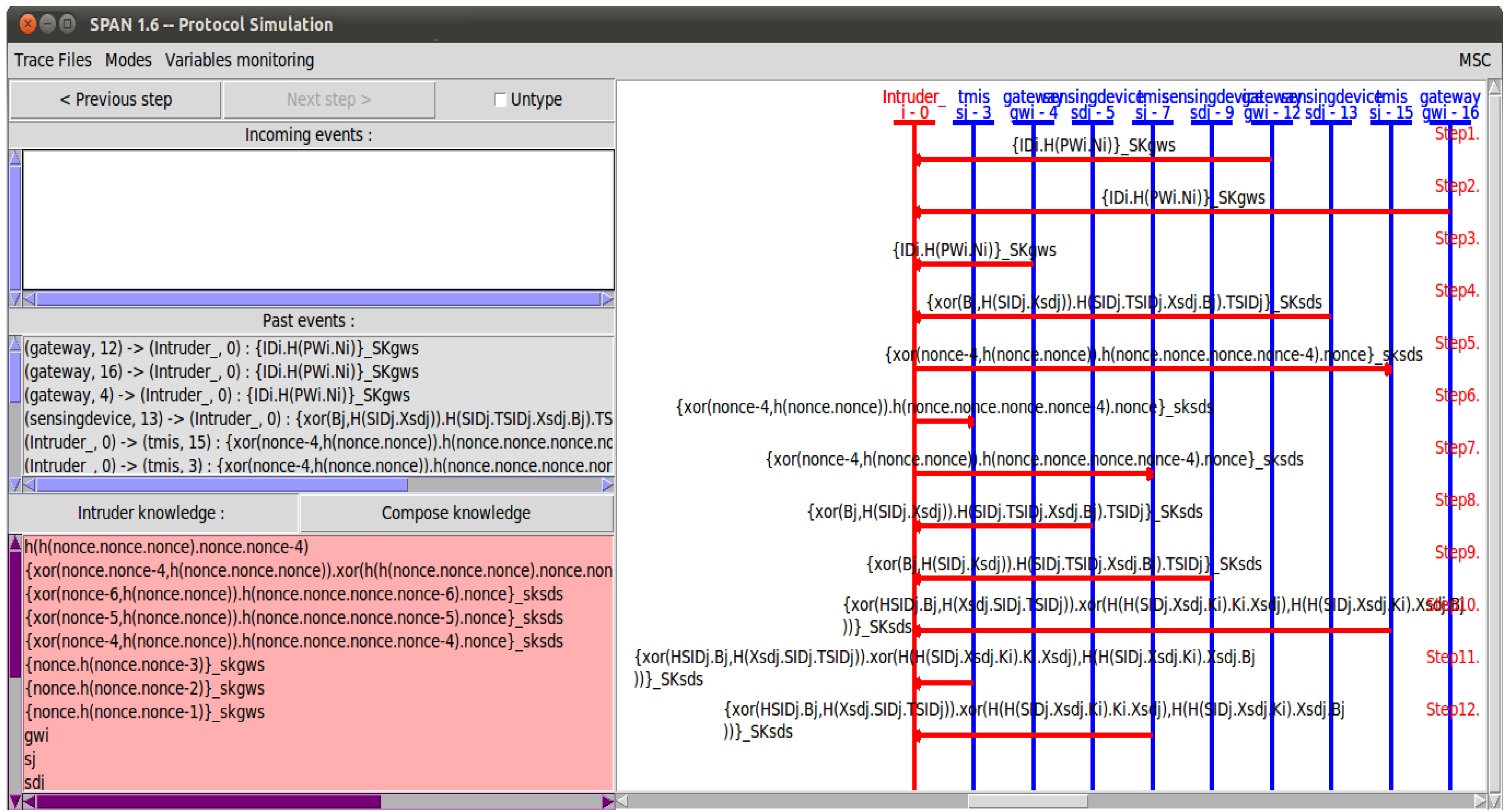
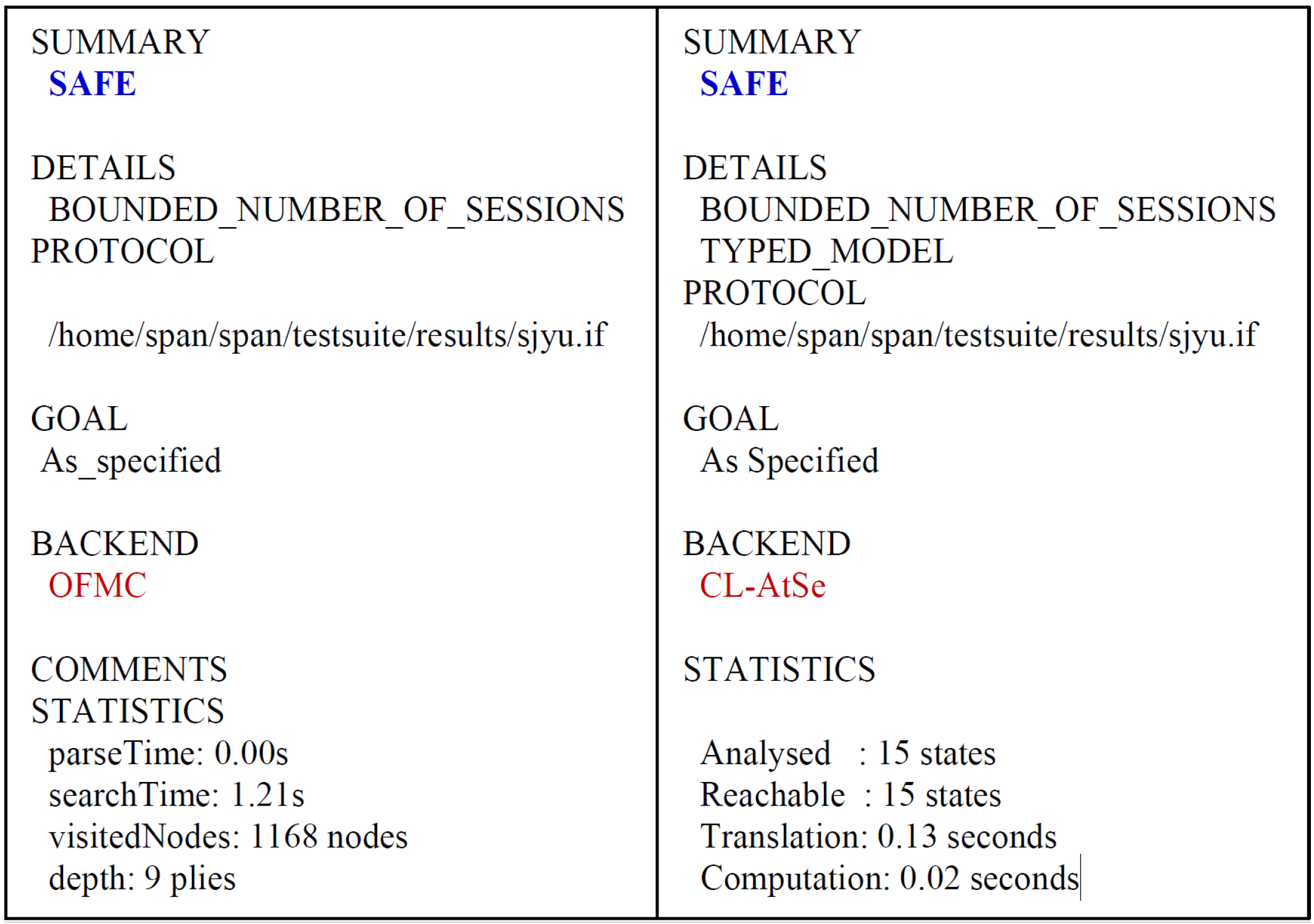
5.4. Formal Security Analysis Using AVISPA Simulation
AVISPA is a “formal security verification simulation that demonstrates whether the cryptographic protocol is resilient against various security threats such as MITM and replay attacks. AVISPA simulation is implemented by utilizing High-Level Protocol Specification Language (HLPSL) [
45] to generate input format (IF) of the backends such as On-the-Fly Model Checker (OFMC), Constraint Logic-based Attack Searcher (CL-AtSE), Tree Automata based on Automatic Approximations for Analysis of Security Protocol (TA4SP), and SAT-based Model Checker (SATMC)”.
To evaluate the security of PUF-PSS, we first “express utilizing a rule-oriented HLPSL. The various specification roles for the , , and S, and for the mandatory roles for the sessions, environments and security goals are implemented in HLPSL for PUF-PSS. Since XOR operation is not provided for the SATMC and TA4SP backends, AVISPA implementation results for these backends are not included”.
Under the HLPSL, we simulated “PUF-PSS using the Security Protocol ANimator (SPAN) [
46] for AVISPA. The simulation result for
utilizing SPAN is shown in
Figure 2. Furthermore, the implementation results by performing CL-AtSe and OFMC back-ends are as shown in
Figure 3”. Consequently, we demonstrate that PUF-PSS is resistant to the cyber security attacks.