When Data Fly: An Open Data Trading System in Vehicular Ad Hoc Networks
Abstract
1. Introduction
2. Background
2.1. Vehicular Ad Hoc Networks
2.2. Distributed Ledger Technology
2.3. Open Data Trading with Distributed Ledger Technology
3. Design and Implementation of the Open Data Trading System
3.1. System Model
3.1.1. System Components
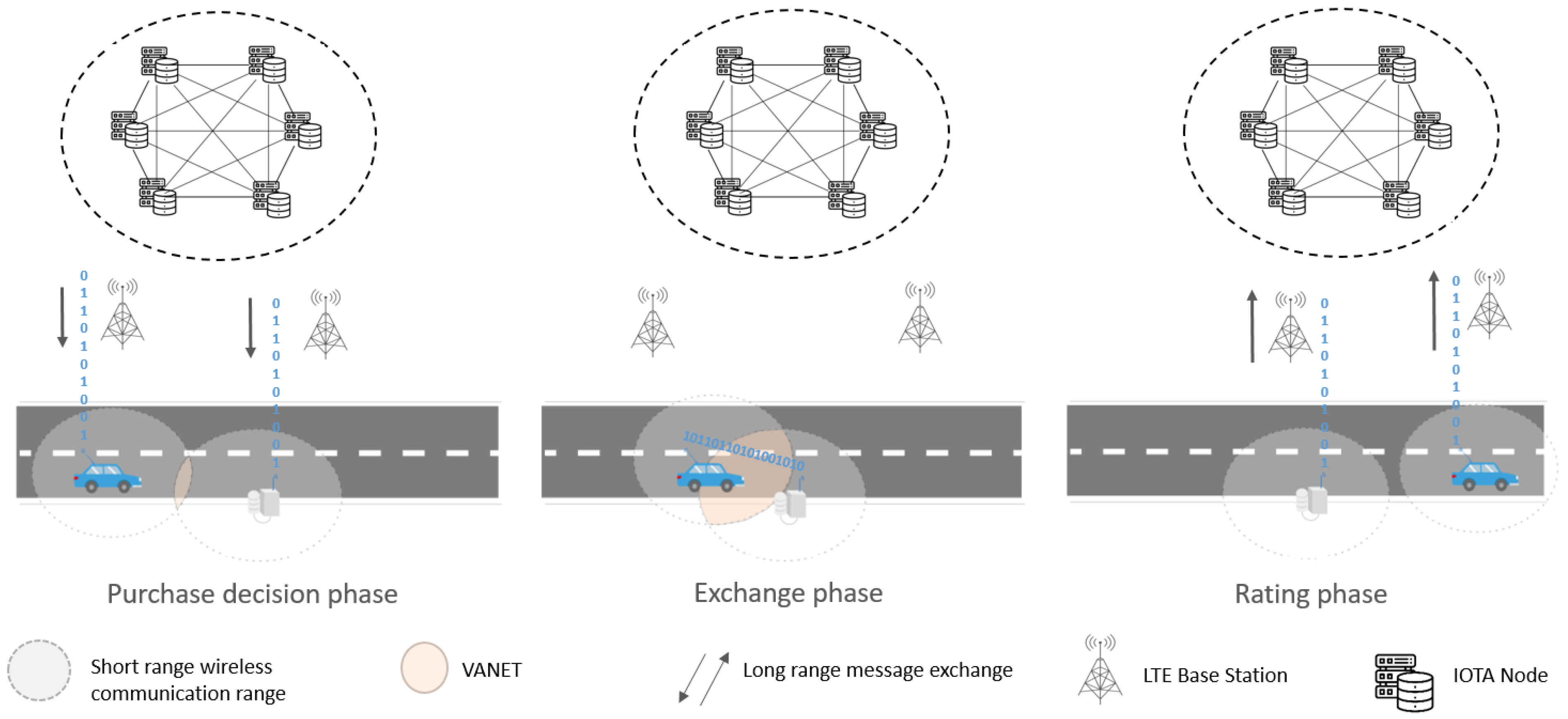
3.1.2. Data Trading Sessions
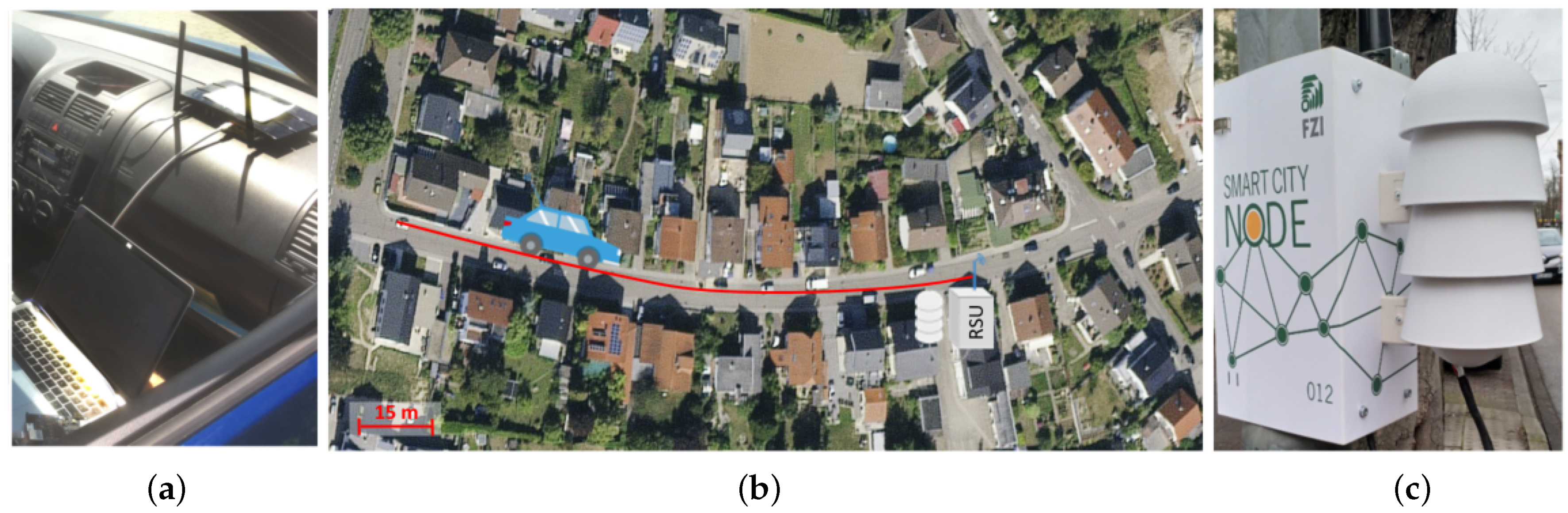
3.2. Prototypical Implementation
3.3. Security of the Data Trading System
3.3.1. Network Security
3.3.2. Concept Security
4. Viability Assessment of the Open Data Trading System
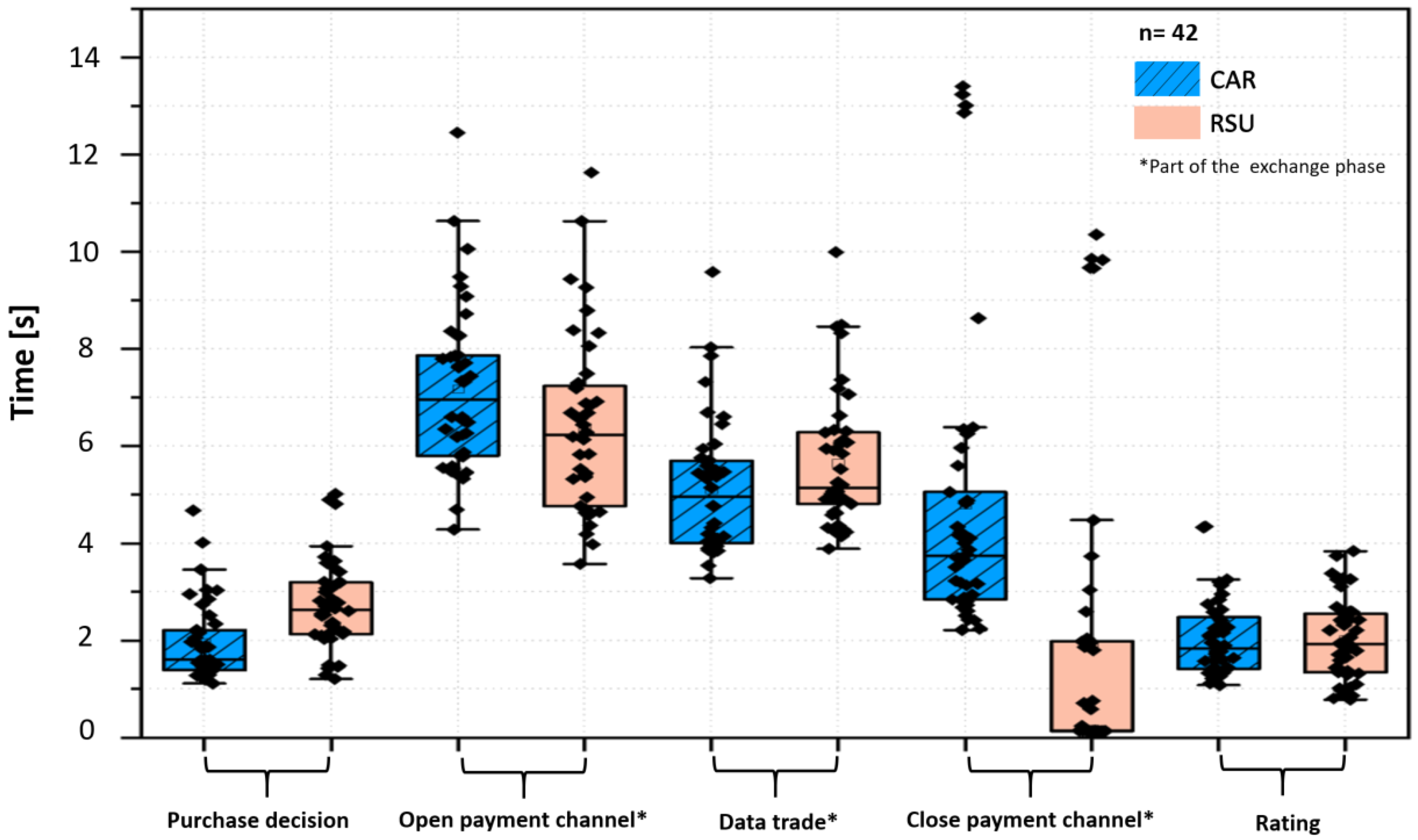
4.1. Communication Time
4.2. Data Trading Cost
5. Comparison with Related Work
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Fong, B.; Situ, L.; Fong, A. Smart Technologies and Vehicle-to-X (V2X) Infrastructures for Smart Mobility Cities: Foundations, Principles, and Applications. In Smart Cities: Foundations, Principles, and Applications; John Wiley & Sons: Hoboken, NJ, USA, 2017; pp. 181–208. [Google Scholar] [CrossRef]
- Bhavani, M.M.; Valarmathi, A. Smart city routing using GIS & VANET system. J. Ambient. Intell. Humaniz. Comput. 2020. [Google Scholar] [CrossRef]
- Zahmatkesh, H.; Saber, M.; Malekpour, M. A New Method for Urban Travel Rout Planning Based on Air Pollution Sensor Data. Curr. World Environ. 2015, 10, 699–704. [Google Scholar] [CrossRef]
- Celikkaya, N.; Papapanagiotou, E.; Busch, F. TUM Living Lab Connected Mobility State of the Art Report Eco-Sensitive Traffic Eco-Sensitive Traffic Management; Technical University of Munich: Munich, Germany, 2016. [Google Scholar]
- Ramachandran, G.S.; Ji, X.; Navaney, P.; Zheng, L.; Martinez, M.; Krishnamachari, B. MOTIVE: Micropayments for trusted vehicular services. arXiv 2019, arXiv:1904.01630. [Google Scholar]
- Park, Y.; Sur, C.; Kim, H.; Rhee, K.H. A Reliable Incentive Scheme Using Bitcoin on Cooperative Vehicular Ad Hoc Networks. IT Converg. Pract. (INPRA) 2017, 5, 34–41. [Google Scholar]
- Zhang, X.; Bai, X.; Liu, Q. A Research of Vehicle Ad Hoc Network Incentive Mechanism. In Proceedings of the IEEE 8th International Conference on Electronics Information and Emergency Communication, Beijing, China, 15–17 June 2018; pp. 175–179. [Google Scholar] [CrossRef]
- Ensor, A.; Schefer-Wenzl, S.; Miladinovic, I. Blockchains for IoT Payments: A Survey. In Proceedings of the IEEE Globecom Workshops, Abu Dhabi, United Arab Emirates, 9–13 December 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Missier, P.; Bajoudah, S.; Capossele, A.; Gaglione, A.; Nati, M. Mind My Value: A decentralized infrastructure for fair and trusted IoT data trading. ACM Int. Conf. Proc. Ser. 2017. [Google Scholar] [CrossRef]
- Visa Inc. Visa U.S.A. Interchange Reimbursement Fees. Available online: https://usa.visa.com/dam/VCOM/download/merchants/visa-usa-interchange-reimbursement-fees.pdf (accessed on 9 January 2021).
- Rezaeibagha, F.; Mu, Y. Efficient micropayment of cryptocurrency from blockchains. Comput. J. 2019, 62, 507–517. [Google Scholar] [CrossRef]
- Ali, S.T.; Clarke, D.; McCorry, P. The nuts and bolts of micropayments: A survey. arXiv 2017, arXiv:1710.02964v1. [Google Scholar]
- Manvi, S.S.; Tangade, S. A survey on authentication schemes in VANETs for secured communication. Veh. Commun. 2017, 9, 19–30. [Google Scholar] [CrossRef]
- Li, Q.; Malip, A.; Martin, K.M.; Ng, S.; Zhang, J. A Reputation-Based Announcement Scheme for VANETs. IEEE Trans. Veh. Technol. 2012, 61, 4095–4108. [Google Scholar] [CrossRef]
- Demmel, S.; Lambert, A.; Gruyer, D.; Rakotonirainy, A.; Monacelli, E. Empirical IEEE 802.11p performance evaluation on test tracks. In Proceedings of the 2012 IEEE Intelligent Vehicles Symposium, Madrid, Spain, 3–7 June 2012; pp. 837–842. [Google Scholar] [CrossRef]
- Shrestha, R.; Bajracharya, R.; Shrestha, A.P.; Nam, S.Y. A new type of blockchain for secure message exchange in VANET. Digit. Commun. Netw. 2019, 6, 177–186. [Google Scholar] [CrossRef]
- Kannengießer, N.; Lins, S.; Dehling, T.; Sunyaev, A. Trade-offs between Distributed Ledger Technology Characteristics. ACM Comput. Surv. 2020, 53. [Google Scholar] [CrossRef]
- Deng, X.; Gao, T. Electronic Payment Schemes Based on Blockchain in VANETs. IEEE Access 2020, 8, 38296–38303. [Google Scholar] [CrossRef]
- Park, Y.; Sur, C.; Rhee, K.H. A Secure Incentive Scheme for Vehicular Delay Tolerant Networks Using Cryptocurrency. Secur. Commun. Netw. 2018, 2018, 5932183. [Google Scholar] [CrossRef]
- Lwin, M.T.; Yim, J.; Ko, Y.B. Blockchain-based lightweight trust management in mobile ad hoc networks. Sensors 2020, 20, 698. [Google Scholar] [CrossRef]
- Lu, Z.; Wang, Q.; Qu, G.; Liu, Z. BARS: A Blockchain-Based Anonymous Reputation System for Trust Management in VANETs. In Proceedings of the 17th IEEE International Conference on Trust, Security and Privacy in Computing and Communications and 12th IEEE International Conference on Big Data Science and Engineering, New York, NY, USA, 1–3 August 2018; pp. 98–103. [Google Scholar] [CrossRef]
- IOTA Foundation. Data Marketplace. Available online: https://docs.iota.org/docs/blueprints/0.1/data-marketplace/overview (accessed on 9 January 2021).
- Wagner, M.; McMillin, B. Cyber-physical transactions: A method for securing VANETs with Blockchains. In Proceedings of the IEEE 24th Pacific Rim International Symposium on Dependable Computing 2019, Kyoto, Japan, 1–3 December 2019; pp. 64–73. [Google Scholar] [CrossRef]
- Kim, S. Impacts of Mobility on Performance of Blockchain in VANET. IEEE Access 2019, 7, 68646–68655. [Google Scholar] [CrossRef]
- Mohammad, S.A.; Rasheed, A.; Qayyum, A. VANET Architectures and Protocol Stacks: A Survey. In Communication Technologies for Vehicles; Strang, T., Festag, A., Vinel, A., Mehmood, R., Rico Garcia, C., Röckl, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 95–105. [Google Scholar]
- Eze, E.C.; Zhang, S.J.; Liu, E.J.; Eze, J.C. Advances in vehicular ad hoc networks (VANETs): Challenges and road-map for future development. Int. J. Autom. Comput. 2016, 13, 1–18. [Google Scholar] [CrossRef]
- Jiang, R.; Zhu, Y. Wireless Access in Vehicular Environment. In Encyclopedia of Wireless Networks; Shen, X.S., Lin, X., Zhang, K., Eds.; Springer International Publishing: Cham, Switzerland, 2019; pp. 1–5. [Google Scholar] [CrossRef]
- Federal Communications Commission. Dedicated Short Range Communications (DSRC) Service. Available online: https://www.fcc.gov/wireless/bureau-divisions/mobility-division/dedicated-short-range-communications-dsrc-service (accessed on 9 January 2021).
- Hameed Mir, Z.; Filali, F. LTE and IEEE 802.11p for vehicular networking: A performance evaluation. Eurasip J. Wirel. Commun. Netw. 2014, 2014, 1–15. [Google Scholar] [CrossRef]
- Abuelsamid, S. Volkswagen Adds ‘Vehicle-To-Everything’ Communications to Revamped Golf with NXP Chips. Available online: https://www.forbes.com/sites/samabuelsamid/2019/10/28/volkswagen-includes-nxp-v2x-communications-in-8th-gen-golf/#5a213ae016bc (accessed on 23 December 2020).
- Popov, S. IOTA whitepaper v1.4.3. New Yorker 2018, 81, 1–28. [Google Scholar]
- Silvano, W.F.; Marcelino, R. Iota Tangle: A cryptocurrency to communicate Internet-of-Things data. Future Gener. Comput. Syst. 2020, 112, 307–319. [Google Scholar] [CrossRef]
- IOTA Foundation. Proof of Work. Available online: https://docs.iota.org/docs/getting-started/0.1/transactions/proof-of-work (accessed on 11 November 2020).
- Lücking, M.; Kannengießer, N.; Kilgus, M.; Riedel, T.; Beigl, M.; Sunyaev, A.; Stork, W. The Merits of a Decentralized Pollution-Monitoring System Based on Distributed Ledger Technology. IEEE Access 2020, 8, 189365–189381. [Google Scholar] [CrossRef]
- World Wide Web Consortium (W3C). Decentralized Identifiers (DIDs) v1.0. Available online: https://w3c.github.io/did-core/#design-goals (accessed on 11 December 2020).
- World Wide Web Consortium (W3C). Decentralized Identifiers (DIDs) v1.0—Core Architecture, Data Model, and Representations. Available online: https://w3c.github.io/did-core/ (accessed on 11 November 2020).
- Mühle, A.; Grüner, A.; Gayvoronskaya, T.; Meinel, C. A survey on essential components of a self-sovereign identity. Comput. Sci. Rev. 2018, 30, 80–86. [Google Scholar] [CrossRef]
- World Wide Web Consortium (W3C). Verifiable Claims Data Model and Representations. Available online: https://www.w3.org/TR/2017/WD-verifiable-claims-data-model-20170803/ (accessed on 11 December 2020).
- Lee, Y.J.; Lee, K.M.; Lee, S.H. Blockchain-based reputation management for custom manufacturing service in the peer-to-peer networking environment. Peer- Netw. Appl. 2020, 13, 671–683. [Google Scholar] [CrossRef]
- Kim, C.H.; Bae, I.H. A Misbehavior-Based Reputation Management System for VANETs. In Embedded and Multimedia Computing Technology and Service; Park, J.J.J.H., Jeong, Y.S., Park, S.O., Chen, H.C., Eds.; Springer: Dordrecht, The Netherlands, 2012; pp. 441–450. [Google Scholar]
- Huynh, T.D.; Jennings, N.R.; Shadbolt, N.R. Certified reputation: How an agent can trust a stranger. Proc. Int. Conf. Auton. Agents 2006, 2006, 1217–1224. [Google Scholar] [CrossRef]
- Dziembowski, S.; Eckey, L.; Faust, S.; Malinowski, D. Perun: Virtual payment hubs over cryptocurrencies. In Proceedings of the IEEE Symposium on Security and Privacy, San Francisco, CA, USA, 19–23 May 2019; pp. 106–123. [Google Scholar] [CrossRef]
- McCorry, P.; Möser, M.; Shahandasti, S.F.; Hao, F. Towards Bitcoin Payment Networks. In Proceedings of the Australasian Conference on Information Security and Privacy, Melbourne, Australia, 4–6 July 2016; pp. 57–76. [Google Scholar] [CrossRef]
- Asgaonkar, A.; Krishnamachari, B. Solving the Buyer and Seller’s Dilemma: A Dual-Deposit Escrow Smart Contract for Provably Cheat-Proof Delivery and Payment for a Digital Good without a Trusted Mediator. In Proceedings of the IEEE 1st International Conference on Blockchain and Cryptocurrency, Seoul, Korea, 14–17 May 2019; pp. 262–267. [Google Scholar] [CrossRef]
- Lamberti, R.; Fries, C.; Lücking, M.; Manke, R.; Kannengießer, N.; Sturm, B.; Komarov, M.M.; Stork, W.; Sunyaev, A. An Open Multimodal Mobility Platform Based on Distributed Ledger Technology. In Internet of Things, Smart Spaces, and Next Generation Networks and Systems; Springer International Publishing: Cham, Switzerland, 2019; pp. 41–52. [Google Scholar]
- ABmushi. IOTA: Multisig Explained. Available online: https://medium.com/@abmushi/iota-multisig-explained-bca334d250a2 (accessed on 11 January 2021).
- OBD-II PIDs. Available online: https://en.wikipedia.org/wiki/OBD-II_PIDs#Service_01 (accessed on 11 January 2021).
- Jung, K.K.; Choi, W.S. Estimation of Vehicle’s CO2 Emission using OBD-II Interface. J. Korea Soc. Comput. Inf. 2011, 16, 167–174. [Google Scholar] [CrossRef]
- Khaled, Y.; Tsukada, M.; Santa, J.; Ernst, T. The role of communication technologies in vehicular applications. In Advances in Vehicular Ad-Hoc Networks: Developments and Challenges; IGI Globa: Pennsylvania, PA, USA, 2010; pp. 37–58. [Google Scholar] [CrossRef]
- Theodorakopoulos, G.; Baras, J.S. On trust models and trust evaluation metrics for ad hoc networks. IEEE J. Sel. Areas Commun. 2006, 24, 318–328. [Google Scholar] [CrossRef]
- Padmavathi, B.; Kumari, S.R. A Survey on Performance Analysis of DES, AES and RSA Algorithm along with LSB Substitution Technique. Int. J. Sci. Res. (IJSR) 2013, 2, 170–174. [Google Scholar]
- Klingler, F. OpenC2X-Standalone. Available online: https://github.com/florianklingler/OpenC2X-standalone/blob/master/config/openc2x_dcc (accessed on 11 January 2021).
- TP-Link. TP Link WDR 3600 Datasheet. Available online: https://www.tp-link.com/us/support/download/tl-wdr3600/ (accessed on 20 January 2021).
- Klingler, F.; Pannu, G.S.; Sommer, C.; Bloessl, B.; Dressler, F. Poster: Field testing vehicular networks using OpenC2X. In Proceedings of the 15th Annual International Conference on Mobile Systems, Applications, and Services, Niagara Falls, NY, USA, 19–23 June 2017; p. 178. [Google Scholar] [CrossRef]
- Matsumoto, A.; Yoshimura, K.; Aust, S.; Ito, T.; Kondo, Y. Performance evaluation of IEEE 802.11n devices for vehicular networks. In Proceedings of the IEEE 34th Conference on Local Computer Networks, Zurich, Switzerland, 20–23 October 2009; pp. 669–670. [Google Scholar] [CrossRef]
- Festag, A. Standards for vehicular communication—From IEEE 802.11p to 5G. Elektrotechnik Informationstechnik 2015, 132, 409–416. [Google Scholar] [CrossRef]
- ABI Research. V2X System Cost Analysis DSRC+LTE and C-V2X+LTE. Available online: https://unex.com.tw/public/uploads/shortcuts/ABI-DSRC-price-comparison.pdf (accessed on 17 January 2021).
- Laux, S.; Pannu, G.S.; Schneider, S.; Tiemann, J.; Klingler, F.; Sommer, C.; Dressler, F. Demo: OpenC2X—An open source experimental and prototyping platform supporting ETSI ITS-G5. IEEE Veh. Netw. Conf. VNC 2016, 16–17. [Google Scholar] [CrossRef]
- Santa, J.; Pereñíguez, F.; Moragón, A.; Skarmeta, A.F. Experimental evaluation of CAM and DENM messaging services in vehicular communications. Transp. Res. Part C Emerg. Technol. 2014, 46, 98–120. [Google Scholar] [CrossRef]
- Radiocommunication Study Groups. Intelligent Transport Systems (ITS) Usage in ITU Member States; Technical Report; International Telecommunication Union: Geneva, Switzerland, 2017. [Google Scholar]
- Schiener, D. The Anatomy of a Transaction. Available online: https://domschiener.gitbooks.io/iota-guide/content/chapter1/transactions-and-bundles.html (accessed on 6 January 2021).
- Pototschnig, T. PiDiver 1.3 Documentation. Available online: https://gitlab.com/microengineer18/pidiver1.3/-/wikis/home (accessed on 11 November 2020).
- Xilinx. Zynq-7000 SoC. Available online: https://www.xilinx.com/products/silicon-devices/soc/zynq-7000.html (accessed on 5 December 2020).
- Dolev, D.; Yao, A.C. On the Security of Public Key Protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Walker, J. Chapter 7—Internet Security. In Computer and Information Security Handbook; Vacca, J.R., Ed.; Morgan Kaufmann: Boston, MA, USA, 2009; pp. 93–117. [Google Scholar] [CrossRef]
- Bohacek, S.; Hespanha, J.P.; Lee, J.; Lim, C.; Obraczka, K. A new TCP for persistent packet reordering. IEEE/ACM Trans. Netw. 2006, 14, 369–382. [Google Scholar] [CrossRef]
- Condo Neira, E. Antenna Evaluation for VehicularApplications in Multipath Environment. Ph.D. Thesis, Chalmers University of Technology, Gothenburg, Sweden, 2017. [Google Scholar]
- Boban, M.; Vinhoza, T.T.V.; Ferreira, M.; Barros, J.; Tonguz, O.K. Impact of Vehicles as Obstacles in Vehicular Ad Hoc Networks. IEEE J. Sel. Areas Commun. 2011, 29, 15–28. [Google Scholar] [CrossRef]
- Schmidt, R.K.; Köllmer, T.; Leinmüller, T.; Böddeker, B.; Schäfer, G. Degradation of Transmission Range in VANETs caused by Interference. PIK Prax. Der Informationsverarbeitung Und Kommun. 2010, 32. [Google Scholar] [CrossRef]
- Mobile Broadband Prices in Europe. p. 87. Available online: https://op.europa.eu/en/publication-detail/-/publication/5a9b64f1-02c8-11eb-8919-01aa75ed71a1/language-en (accessed on 4 January 2021). [CrossRef]
- Eurostat. Electricity Prices (Including Taxes) for Household Consumers, First Half 2020. Available online: https://ec.europa.eu/eurostat/statistics-explained/index.php/Electricity_price_statistics (accessed on 4 January 2021).
- Khan, N.; State, R. Lightning Network: A Comparative Review of Transaction Fees and Data Analysis. In Blockchain and Applications; Springer International Publishing: Cham, Switzerland, 2019; pp. 11–18. [Google Scholar] [CrossRef]
- Robert, J.; Kubler, S.; Ghatpande, S. Enhanced Lightning Network (off-chain)-based micropayment in IoT ecosystems. Future Gener. Comput. Syst. 2020, 112, 283–296. [Google Scholar] [CrossRef]
- Tan, H.; Chung, I. Secure Authentication and Key Management with Blockchain in VANETs. IEEE Access 2020, 8, 2482–2498. [Google Scholar] [CrossRef]
- Chen, L.; Lit, Q.; Martin, K.M.; Ng, S.L. A privacy-aware reputation-based announcement scheme for VANETs. In Proceedings of the IEEE 5th International Symposium on Wireless Vehicular Communications, WiVeC 2013, Dresden, Germany, 2–3 June 2013; Volume 61, pp. 4095–4108. [Google Scholar] [CrossRef]
- Lu, Z.; Wang, Q.; Qu, G.; Zhang, H.; Liu, Z. A Blockchain-Based Privacy-Preserving Authentication Scheme for VANETs. IEEE Trans. Very Large Scale Integr. Syst. 2019, 27, 2792–2801. [Google Scholar] [CrossRef]
- Xu, J.; Xue, K.; Tian, H.; Hong, J.; Wei, D.S.; Hong, P. An Identity Management and Authentication Scheme Based on Redactable Blockchain for Mobile Networks. IEEE Trans. Veh. Technol. 2020, 69, 6688–6698. [Google Scholar] [CrossRef]
- Lux, Z.A.; Thatmann, D.; Zickau, S.; Beierle, F. Distributed-Ledger-based Authentication with Decentralized Identifiers and Verifiable Credentials. In Proceedings of the 2nd Conference on Blockchain Research and Applications for Innovative Networks and Services, BRAINS, Paris, France, 28–30 September 2020; pp. 71–78. [Google Scholar] [CrossRef]
- Kchaou, A.; Ayed, S.; Abassi, R.; Fatmi, S.G.E. Smart Contract-Based Access Control for the Vehicular Networks. In Proceedings of the 2020 International Conference on Software, Telecommunications and Computer Networks (SoftCOM), Hvar, Croatia, 17–19 September 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Ma, Z.; Zhang, J.; Guo, Y.; Liu, Y.; Liu, X.; He, W. An Efficient Decentralized Key Management Mechanism for VANET With Blockchain. IEEE Trans. Veh. Technol. 2020, 69, 5836–5849. [Google Scholar] [CrossRef]
- Mühlbauer, R.; Kleinschmidt, J.H. Bring your own reputation: A feasible trust system for vehicular ad hoc networks. J. Sens. Actuator Netw. 2018, 7, 37. [Google Scholar] [CrossRef]
- Sabater, J.; Sierra, C. Review on computational trust and reputation models. Artif. Intell. Rev. 2005, 24, 33–60. [Google Scholar] [CrossRef]
- Huang, Z.; Ruj, S.; Cavenaghi, M.A.; Stojmenovic, M.; Nayak, A. A social network approach to trust management in VANETs. Peer Netw. Appl. 2014, 7, 229–242. [Google Scholar] [CrossRef]
- Sadiq, A.; Javaid, N.; Samuel, O.; Khalid, A.; Haider, N.; Imran, M. Efficient Data Trading and Storage in Internet of Vehicles using Consortium Blockchain. In Proceedings of the 2020 International Wireless Communications and Mobile Computing, Limassol, Cyprus, 15–19 June 2020; pp. 2143–2148. [Google Scholar] [CrossRef]
- Breu, J.; Brakemeier, A.; Menth, M. Analysis of cooperative awareness message rates in VANETs. In Proceedings of the 13th International Conference on ITS Telecommunications, Tampere, Finland, 5–7 November 2013; pp. 8–13. [Google Scholar] [CrossRef]
- Ahmed, H.; Pierre, S.; Quintero, A. A flexible testbed architecture for VANET. Veh. Commun. 2017, 9, 115–126. [Google Scholar] [CrossRef]
- Hassija, V.; Chamola, V.; Gupta, V.; Chalapathi, G.S. A Framework for Secure Vehicular Network using Advanced Blockchain. In Proceedings of the 2020 International Wireless Communications and Mobile Computing, Limassol, Cyprus, 15–19 June 2020; pp. 1260–1265. [Google Scholar] [CrossRef]
| Exchange | ||||||
|---|---|---|---|---|---|---|
| Direction | Advertisement | Purchase Decision | Open Payment Channel | Data Trade | Close Payment Channel | Rating |
| Sent by car to RSU | 10.0% | 76.4% | 93.9% | 95.7% | 97.3% | - |
| Sent by RSU to car | 2.1% | 37.5% | 52.8% | 80.1% | 89.7% | - |
| Data Trading Phases | Description of the Main Task in Each Phase | Download [kB] | Upload [kB] |
|---|---|---|---|
| Purchase decision | Request and download of verifiable claims | 10.90 | 5.73 |
| Open payment channel * | Create multi-signature address | 11.43 | 24.43 |
| Data trade * | Ad hoc data exchange | 0.00 | 0.00 |
| Close payment channel * | Resolve multi-signature address | 11.42 | 19.04 |
| Rating | Attesting the trading partner’s reputation claim | 3.50 | 13.32 |
| Total data traffic per X-Node | 37.3 | 62.5 | |
| * Part of the exchange phase. | |||
| Hardware Module | Minimum [W] | Average [W] | Maximum [W] |
|---|---|---|---|
| Computing unit | 3.9 | 4.9 | 5.2 |
| Short-range communication module | 3.5 | 4.3 | 4.9 |
| FPGA-based PoW accelerator | 3.1 | 3.1 | 3.1 |
| Long-range communication module | 5.2 | 5.2 | 5.2 |
| Sum | 15.7 | 17.5 | 18.4 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lücking, M.; Kretzer, F.; Kannengießer, N.; Beigl, M.; Sunyaev, A.; Stork, W. When Data Fly: An Open Data Trading System in Vehicular Ad Hoc Networks. Electronics 2021, 10, 654. https://doi.org/10.3390/electronics10060654
Lücking M, Kretzer F, Kannengießer N, Beigl M, Sunyaev A, Stork W. When Data Fly: An Open Data Trading System in Vehicular Ad Hoc Networks. Electronics. 2021; 10(6):654. https://doi.org/10.3390/electronics10060654
Chicago/Turabian StyleLücking, Markus, Felix Kretzer, Niclas Kannengießer, Michael Beigl, Ali Sunyaev, and Wilhelm Stork. 2021. "When Data Fly: An Open Data Trading System in Vehicular Ad Hoc Networks" Electronics 10, no. 6: 654. https://doi.org/10.3390/electronics10060654
APA StyleLücking, M., Kretzer, F., Kannengießer, N., Beigl, M., Sunyaev, A., & Stork, W. (2021). When Data Fly: An Open Data Trading System in Vehicular Ad Hoc Networks. Electronics, 10(6), 654. https://doi.org/10.3390/electronics10060654







