Security Policy Scheme for an Efficient Security Architecture in Software-Defined Networking
Abstract
:1. Introduction
2. Related Work
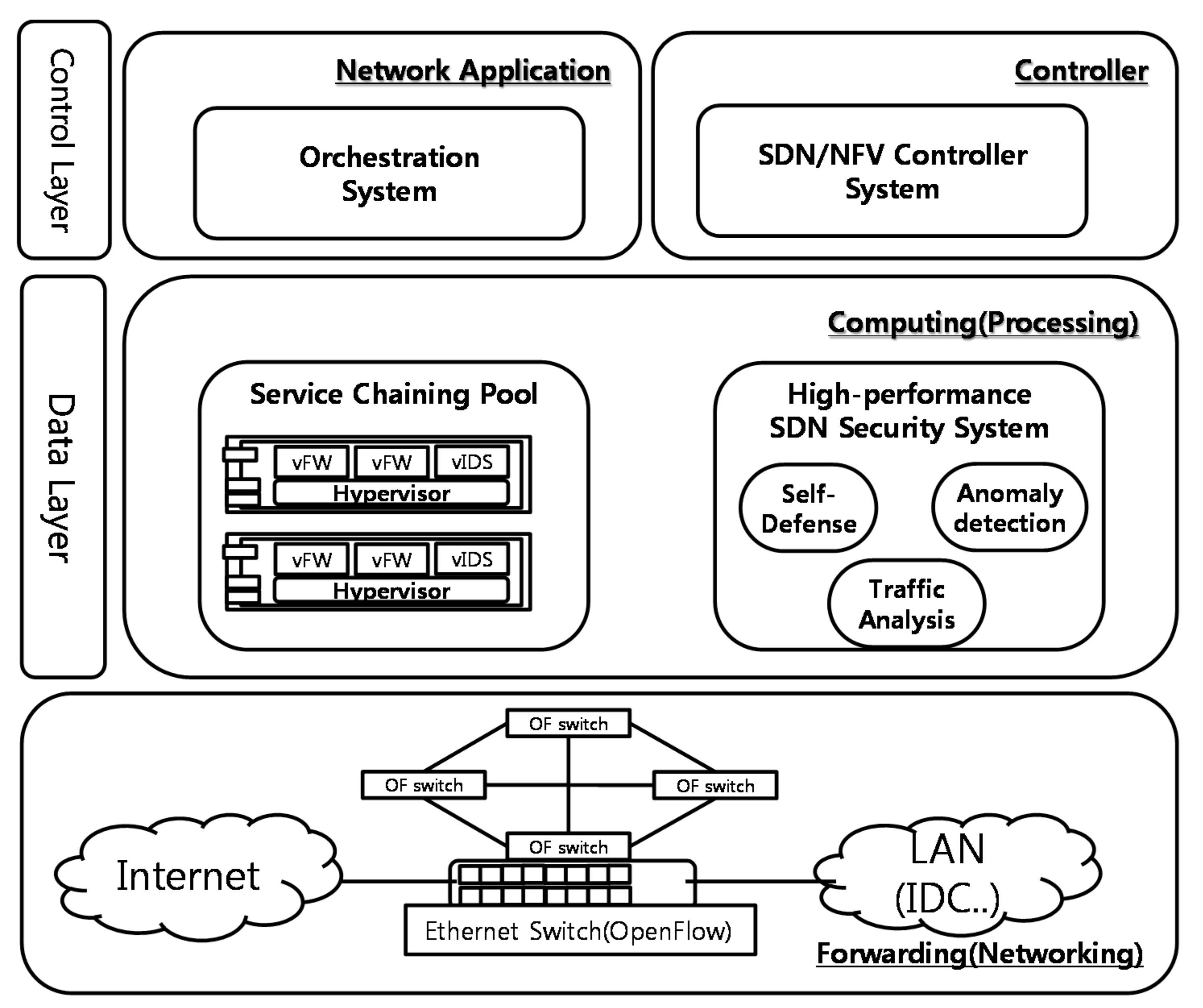
3. Background
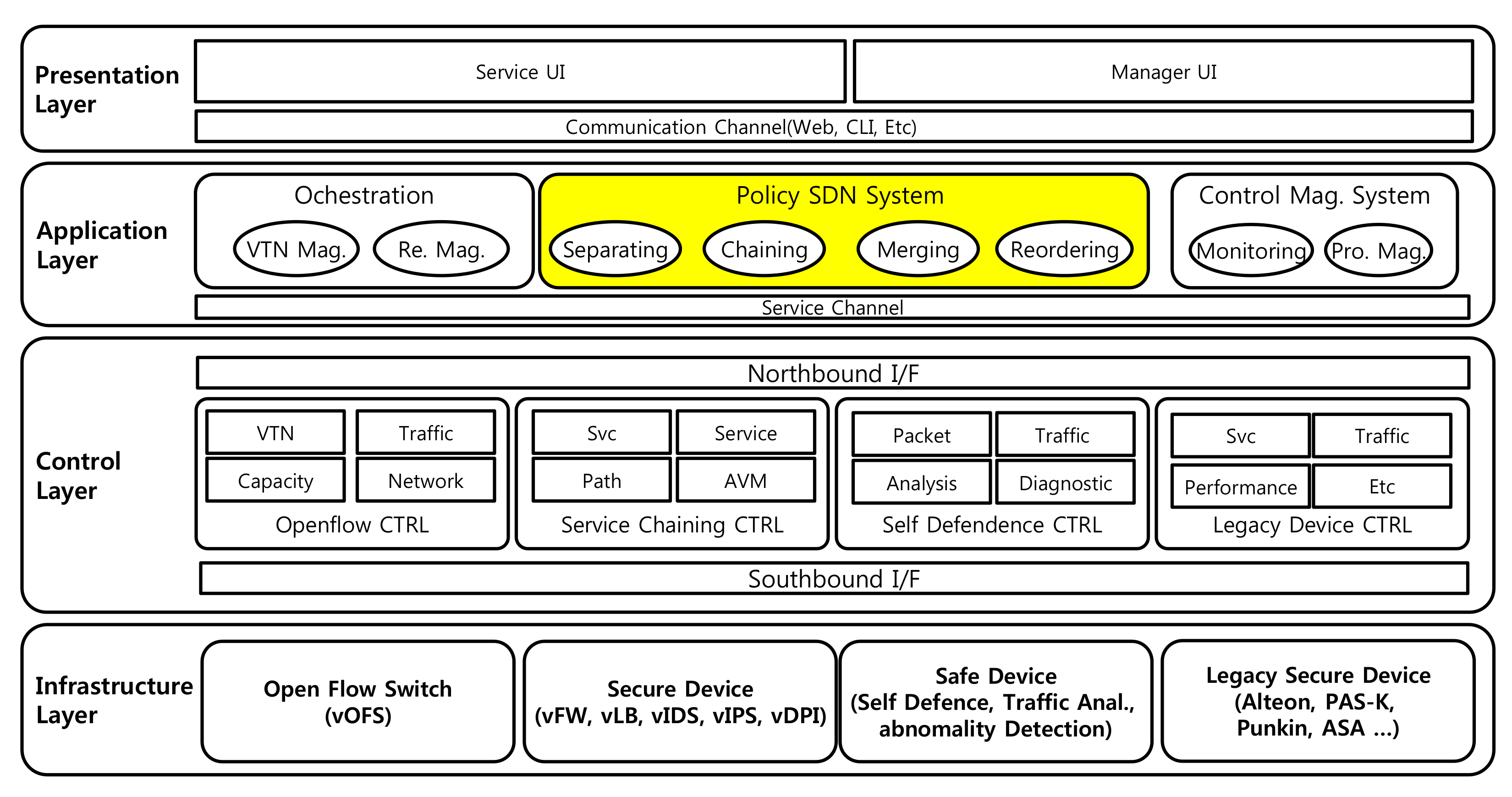
4. Security Policy Scheme Security Architecture
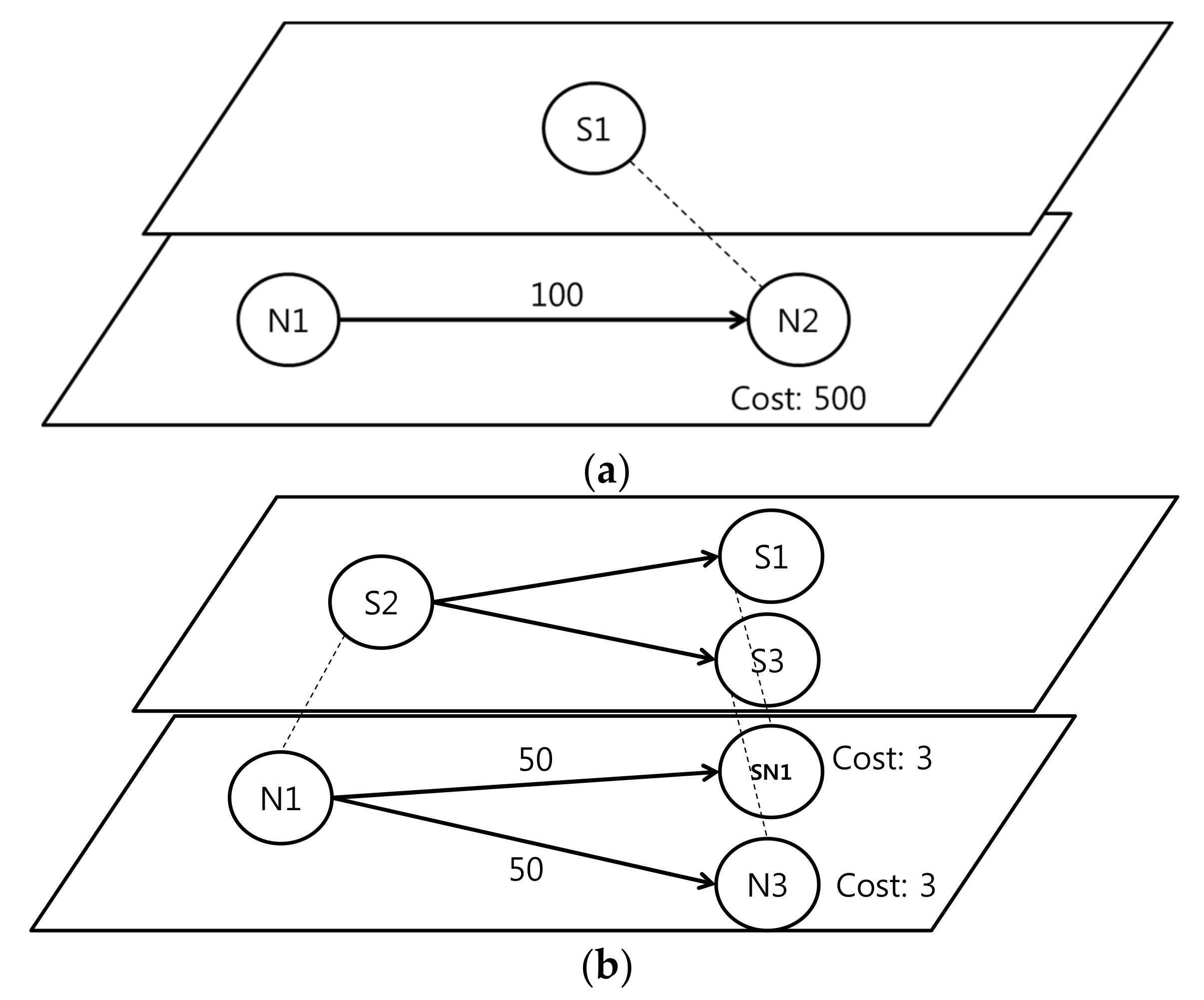
- Separating: this divides the virtual services and decreases the size of the attack flows using the load balancer.
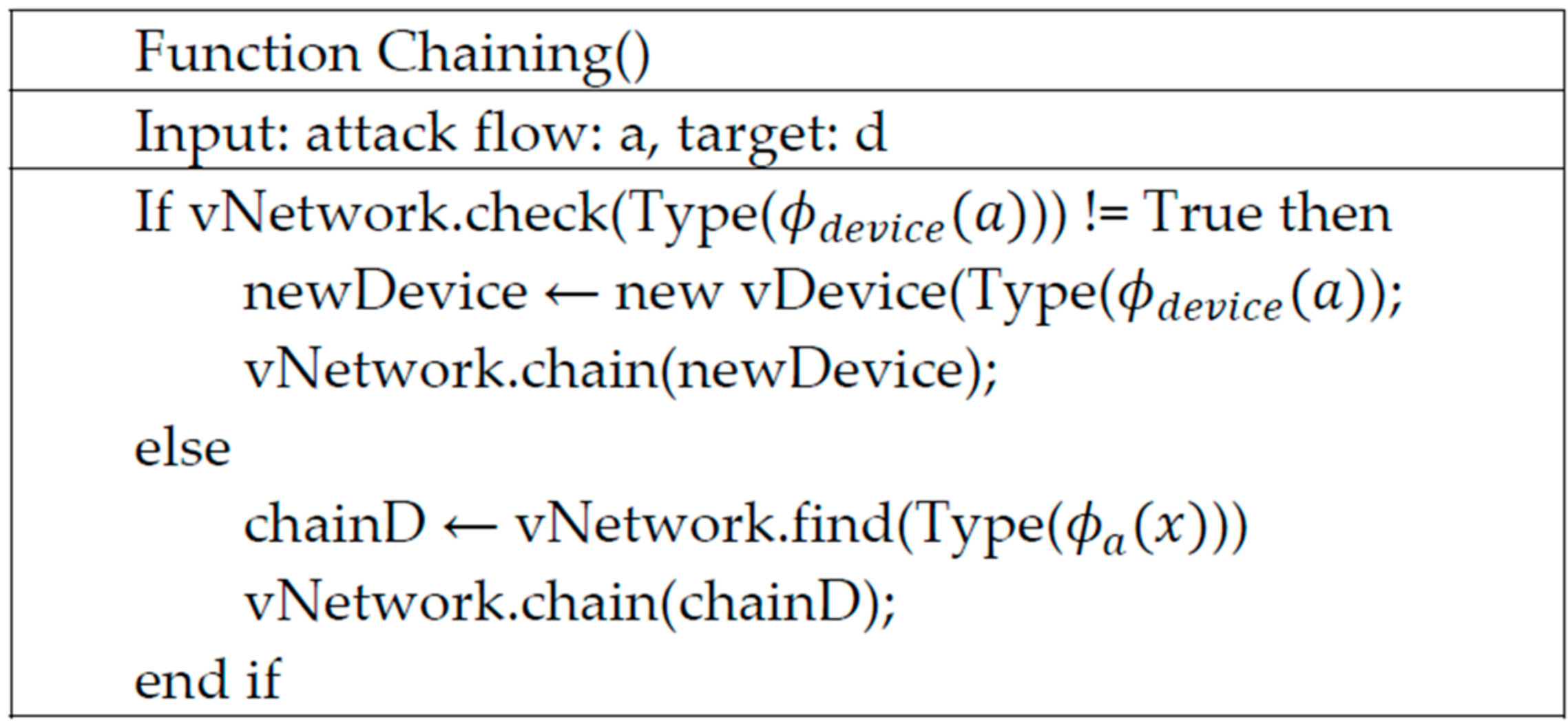
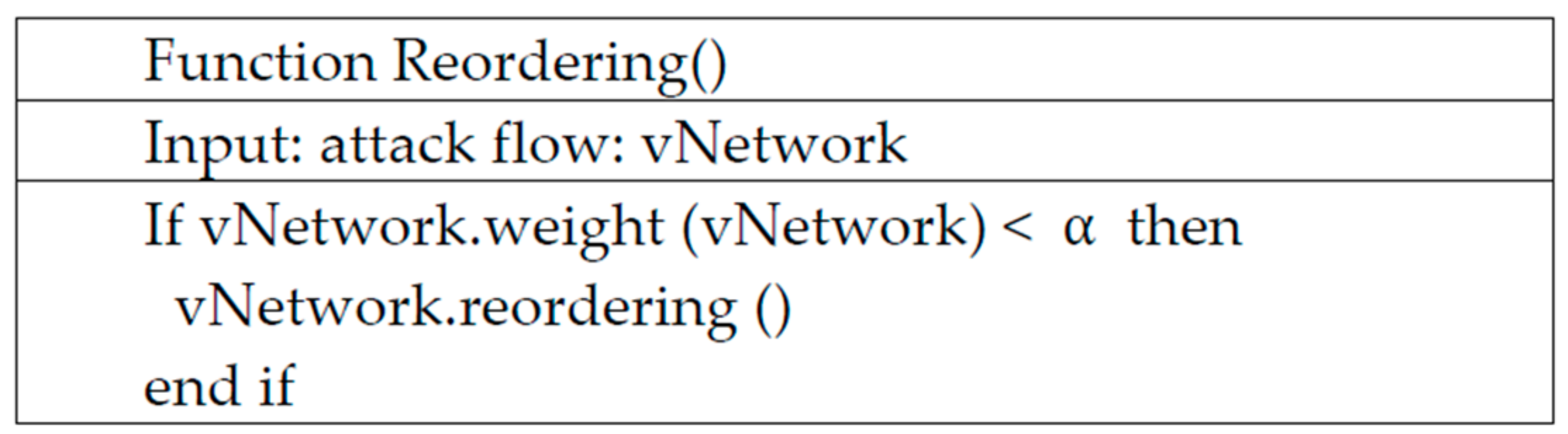
- Chaining: this links many VNFs to prevent various attack flows and constructs big security systems.
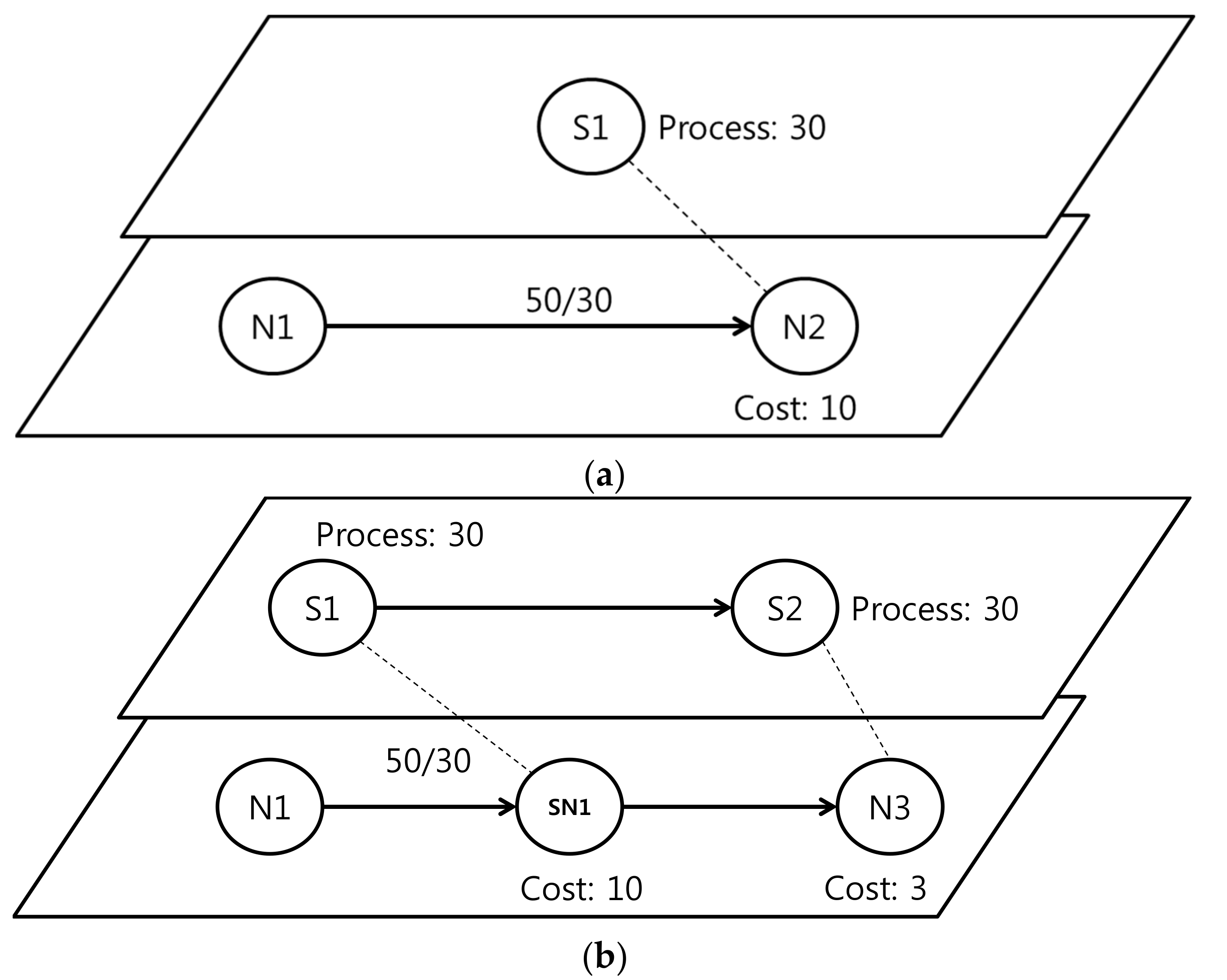
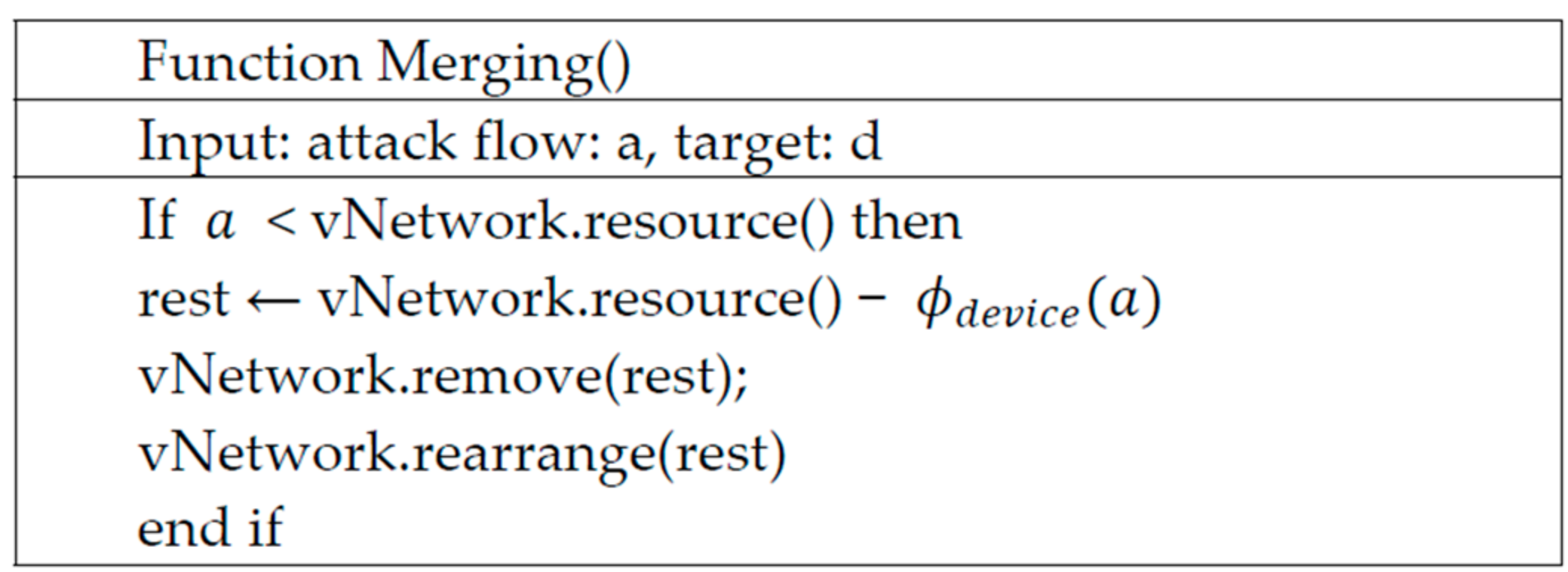
- Merging: this combines unnecessary VNFs to optimize the security system and the system’s resources.
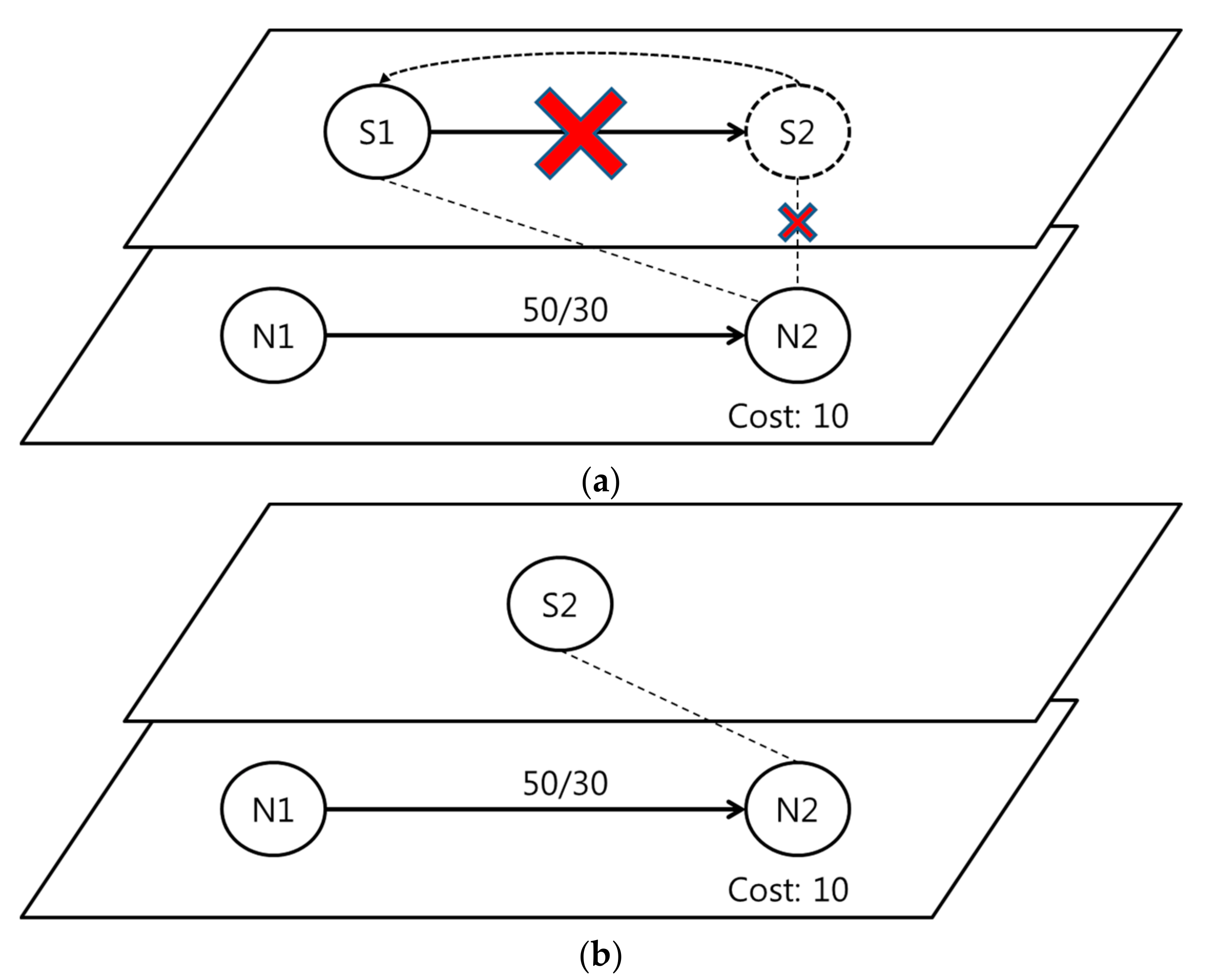
- Reordering: this reorders current VNFs depending on the type and strength of the current attack flows.
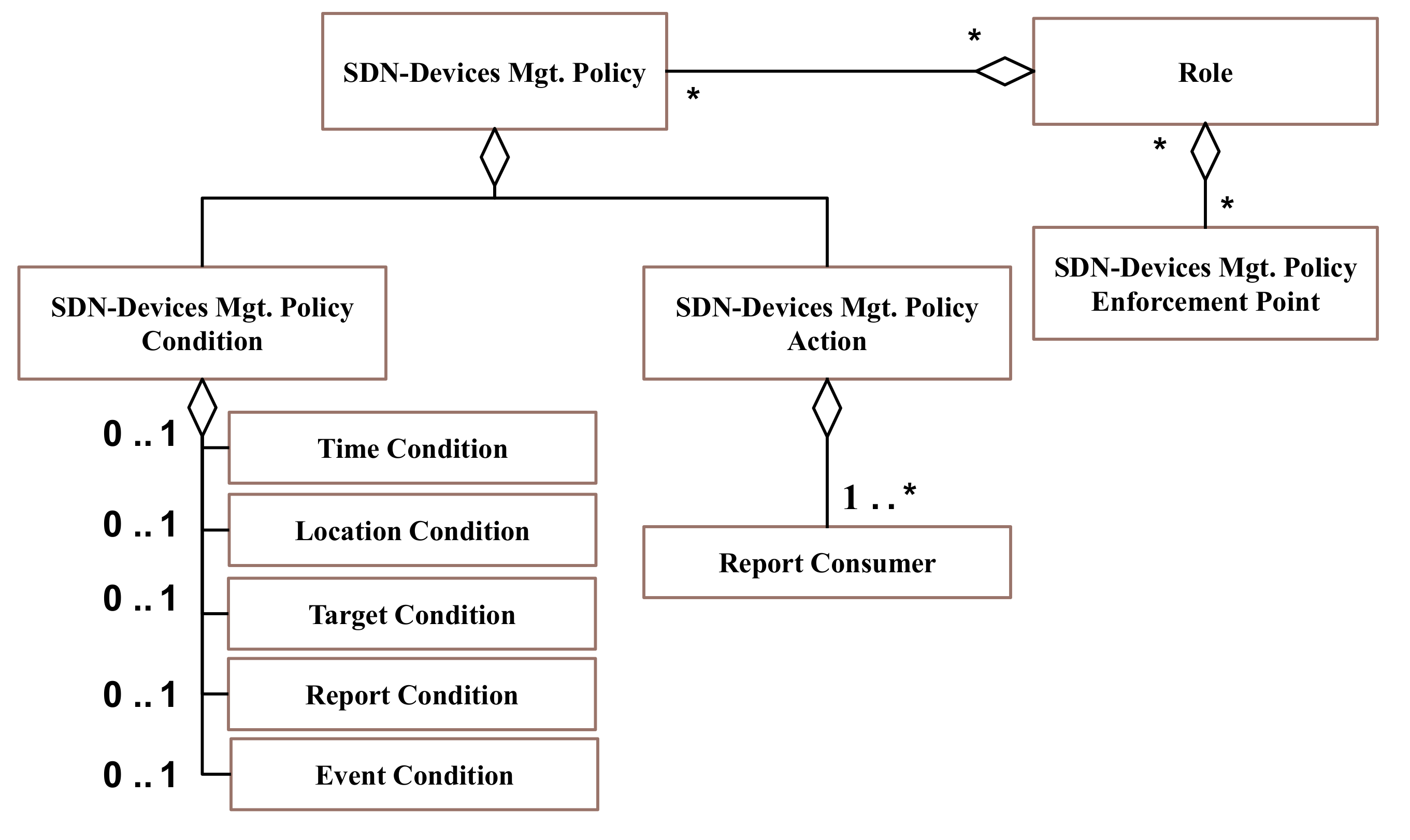
5. Security Policy Meta-Model
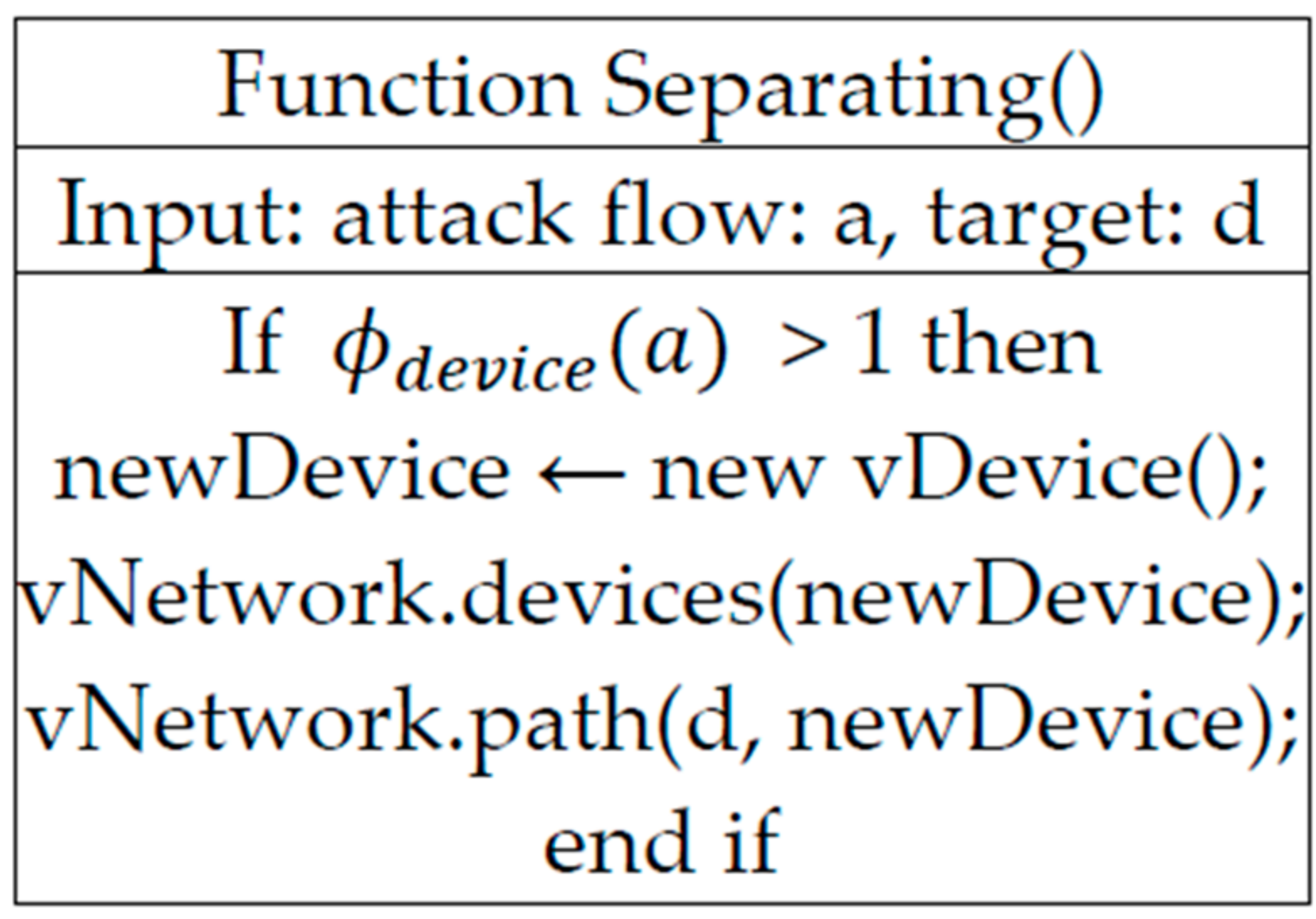
6. Security Policy Schemes
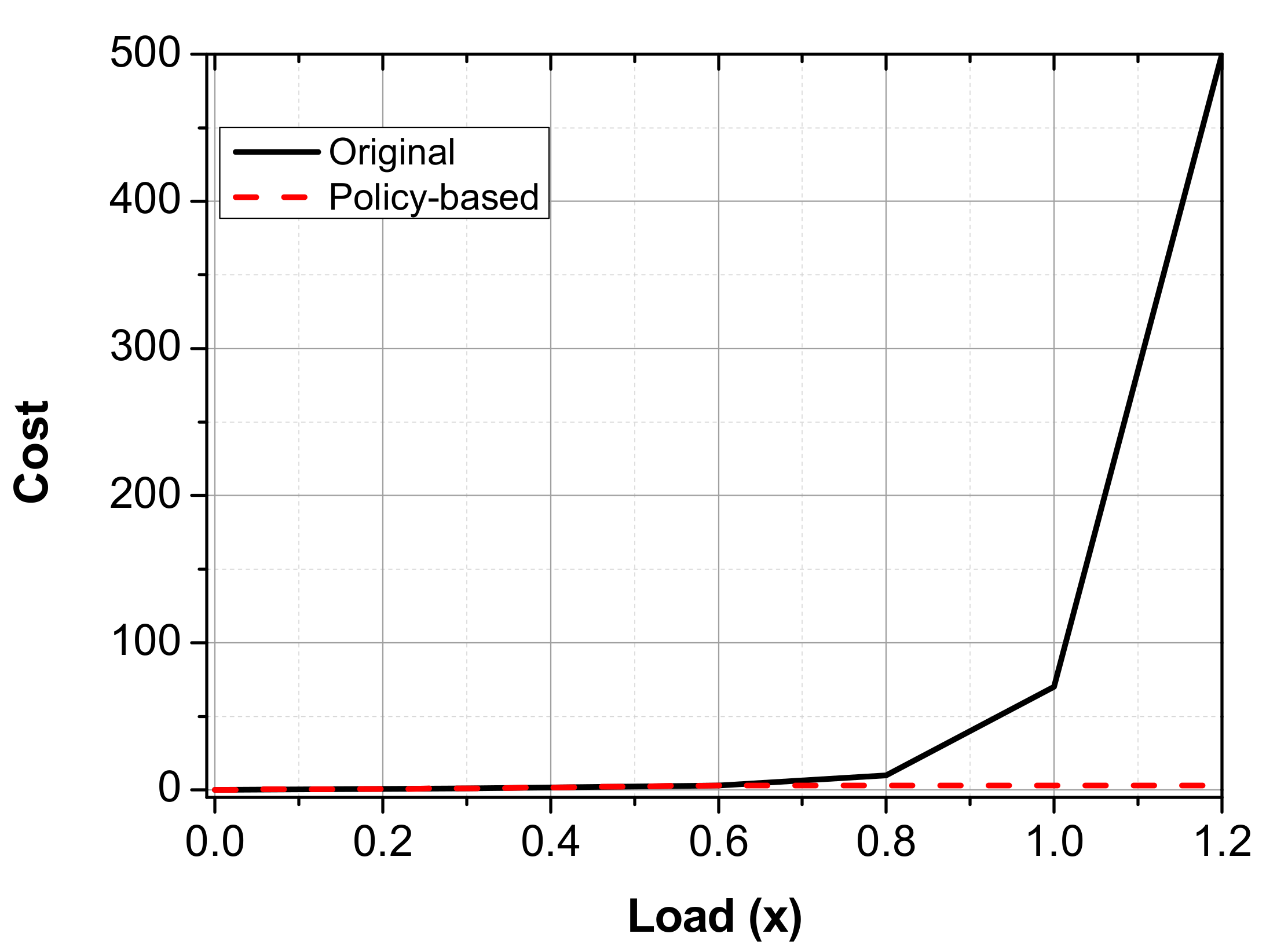
7. Theoretical Analysis
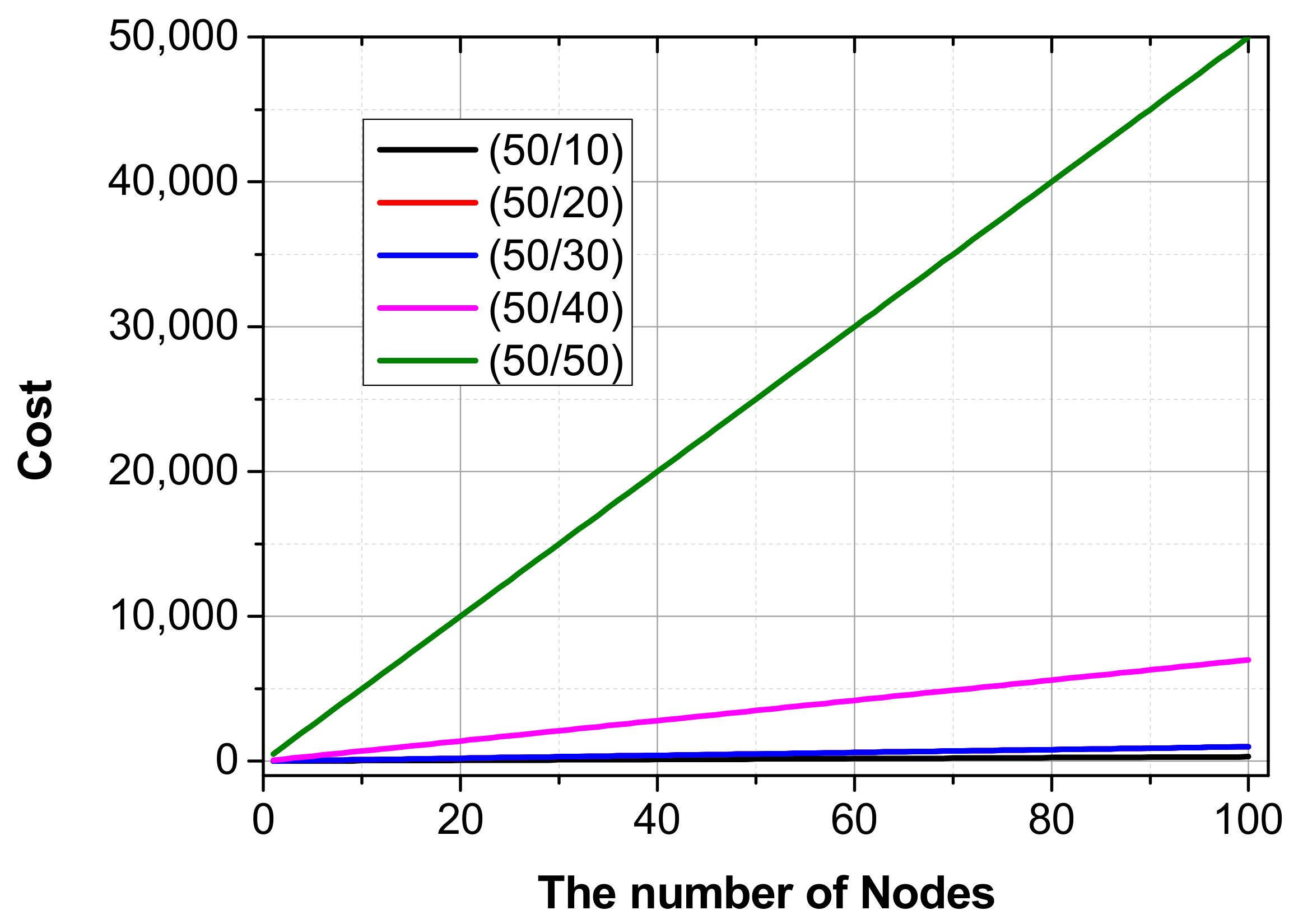
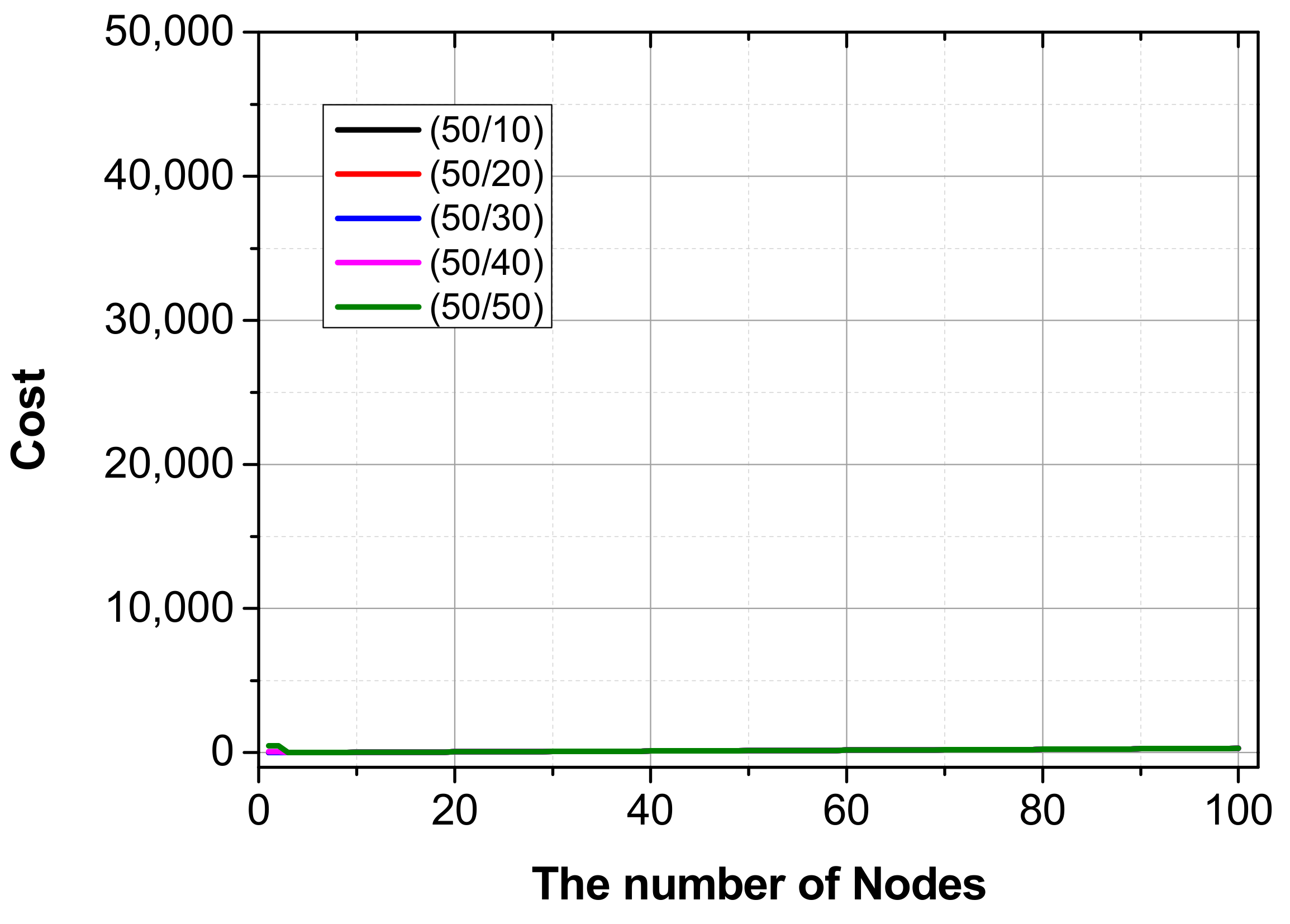
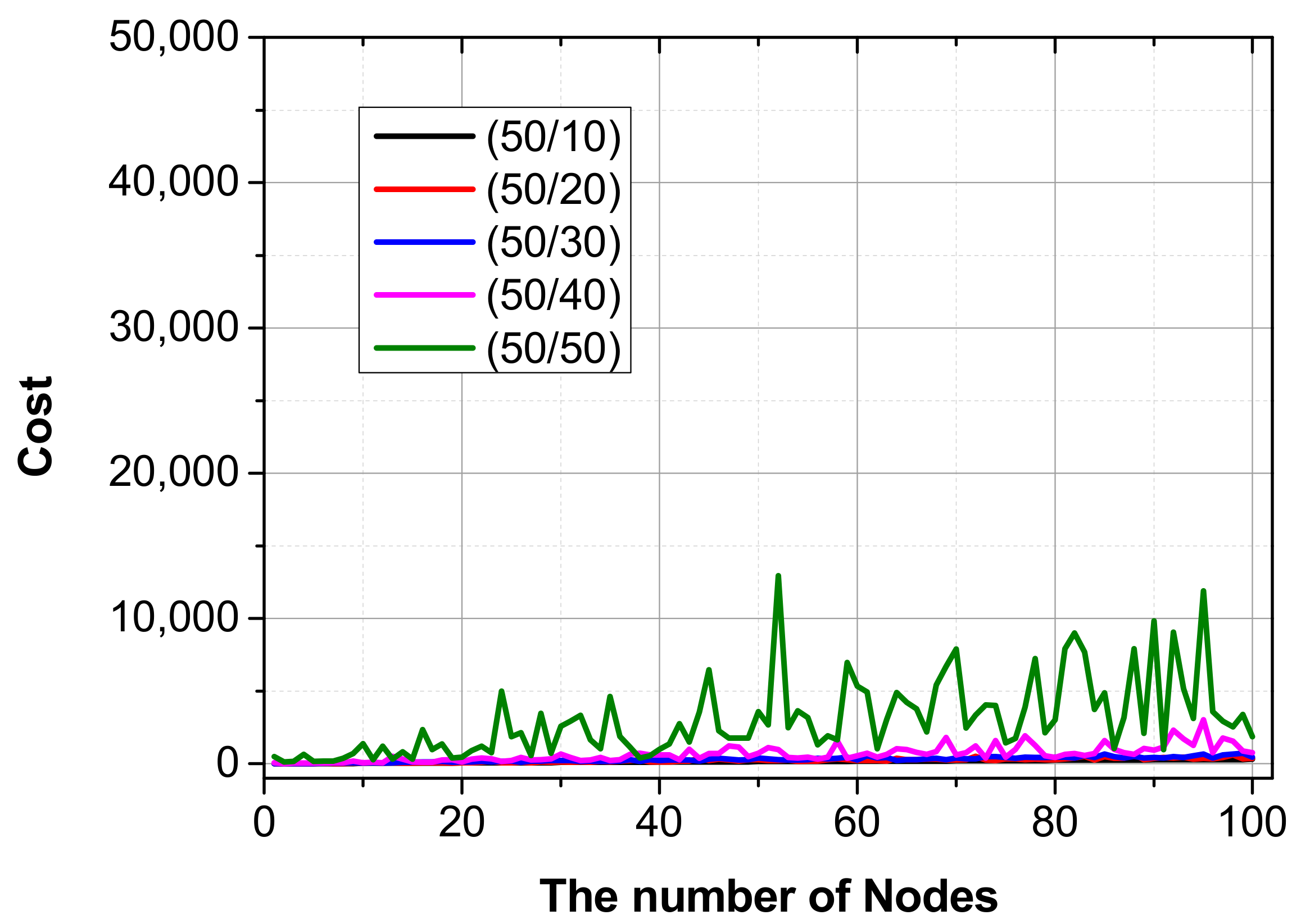
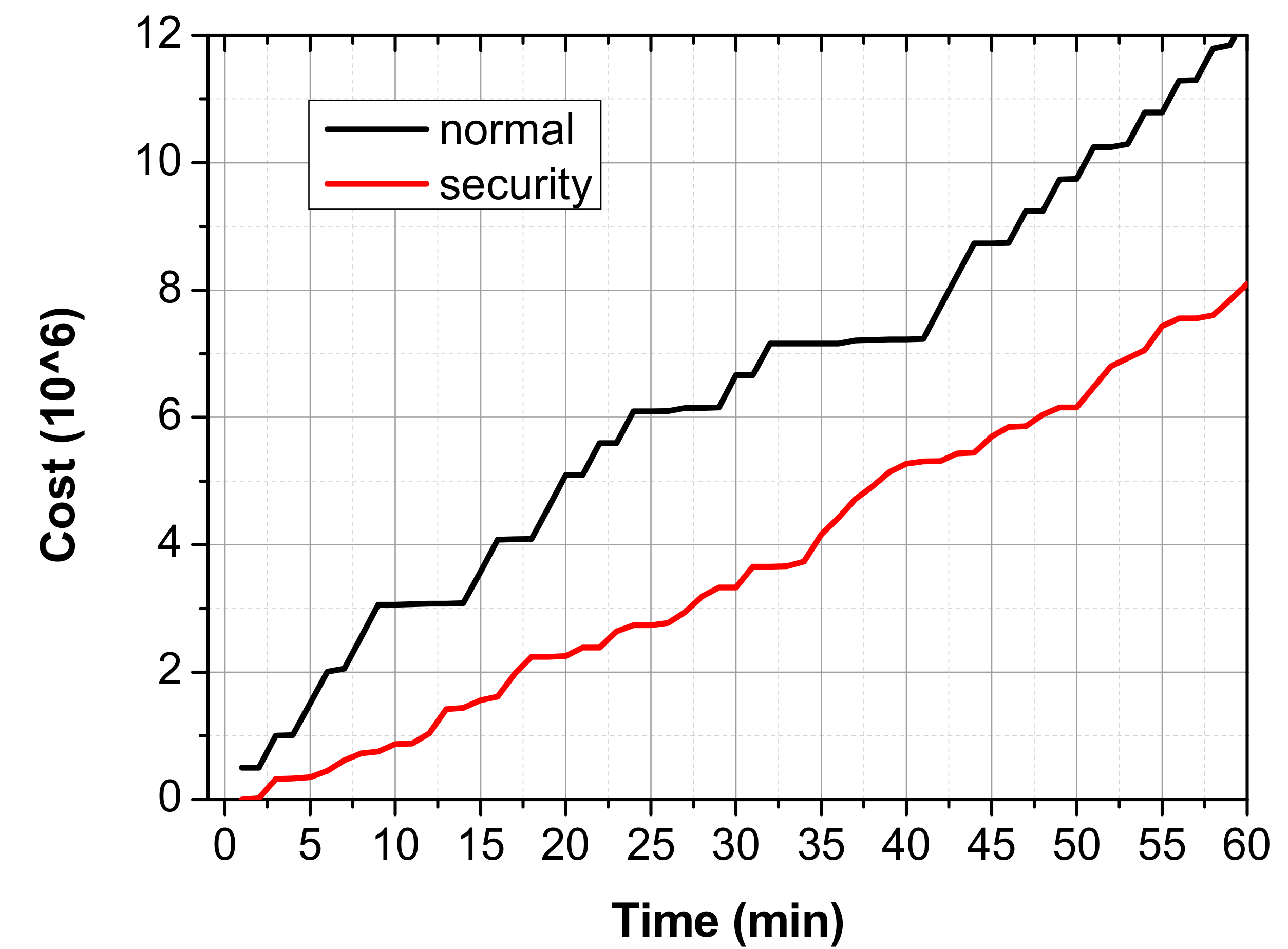
8. Experimental Result through Simulation
- A network with only physical equipment that does not have any security policy;
- A network environment where the attack flow is cleaned based on the security policy;
- A network environment that processes attack packets through a security chain based on the number of attack flows divided by 5;
- A comparison of a network with and without a security policy, in an environment where the normal packet/attack packet changes randomly over time.
9. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Bradai, A.; Singh, K.; Ahmed, T.; Rasheed, T. Cellular software defined networking: A framework. IEEE Commun. Mag. 2015, 53, 36–43. [Google Scholar] [CrossRef]
- Bo, H.; Gopalakrishnan, V.; Lusheng, J.; Seungjoon, L. Network function virtualization: Challenges and opportunities for innovations. IEEE Commun. Mag. 2015, 53, 90–97. [Google Scholar] [CrossRef]
- Lee, W.; Choi, Y.; Kim, N. Study on virtual service chain for secure software-defined networking. Adv. Sci. Technol. Lett. 2013, 29, 177–180. [Google Scholar] [CrossRef]
- Cisco. Cisco Nexus 1000V Switch and Cisco vPath 2.5 Virtual Services Ecosystem. White Pap. 2014. Available online: http://www.cisco.com/c/en/us/products/collateral/switches/nexus-7000-series-switches/white-paper-c11-730475.html (accessed on 13 June 2017).
- Quinn, P. Service Function Chaining Creating a Service Plane Using Network Service Header. Computer 2014, 47, 38–44. [Google Scholar]
- Jiang, Y.; Li, H.; Wei, H. An architecture of service chaining. Internet-Draft. 2013. Available online: https://tools.ietf.org/html/draft-jiang-service-chaining-arch-00 (accessed on 13 June 2017).
- Wan, K.; Chang, R. Engineering of a global defense infrastructure for DDoS attacks. In Proceedings of the 10th IEEE International Conference on Networks, Singapore, Singapore, 27–30 August 2002; pp. 419–427. [Google Scholar]
- Khatua, S.; Ghosh, A.; Mukherjee, N. Optimizing the utilization of virtual resources in Cloud environment. In Proceedings of the 2010 IEEE International Conference on Virtual Environments Human-Computer Interfaces and Measurement Systems (VECIMS), Taranto, Italy, 6–8 September 2010; pp. 82–87. [Google Scholar]
- Alicherry, M.; Lakshman, T.V. Optimizing data access latencies in cloud systems by intelligent virtual machine placement. In Proceedings of the IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 647–655. [Google Scholar]
- Fischer, A.; Botero, J.F.; Beck, M.T.; Meer, H.; Hesselbach, X. Virtual network embedding: A survey. IEEE Commun. Surv. Tutor. 2013, 15, 1888–1906. [Google Scholar] [CrossRef]
- Chowdhury, N.M.M.K.; Rahman, M.R.; Boutaba, R. Virtual network embedding with coordinated node and link mapping. In Proceedings of the IEEE INFOCOM, Rio de Janeiro, Brazil, 19–25 April 2009; pp. 783–791. [Google Scholar]
- Chowdhury, M.; Samuel, F.; Boutaba, R. PolyViNE: Policy-based virtual network embedding across multiple domains. J. Internet Serv. Appl. 2010, 4, 49–56. [Google Scholar] [CrossRef]
- Jo, J.Y.; Lee, S.Y.; Kong, J.U.; Kim, J.W. A centralized network policy controller for SDN-based service overlay networking. J. Korea Inf. Commun. Soc. 2013, 38, 266–278. [Google Scholar] [CrossRef]
- Sazena, M.; Kumar, R. A recent trends in software defined networking (SDN) security. In Proceedings of the Computing for Sustainable Global Development, New Delhi, India, 16–18 March 2016; pp. 16–18. [Google Scholar]
- Satasiya, D.; Raviya, R.; Kumar, H. Enhanced SDN security using firewall in a distributed scenario. In Proceedings of the Advanced Communication Control and Computing Technologies, Ramanathapuram, India, 25–27 May 2016; pp. 25–27. [Google Scholar]
- Shin, S.; Xu, L.; Hong, S.; Gu, G. Enhancing network security through software defined networking (SDN). In Proceedings of the International Conference on Computer Communication and Networks, Waikoloa, HI, USA, 1–4 August 2016; pp. 1–4. [Google Scholar]
- Husssein, A.; Elhajj, I.H.; Chehab, A.; Kayssi, A. SDN security plane: An architecture for resilient security services. In Proceedings of the IEEE International Conference on Cloud Engineering Workshop, Luxembourg, Luxembourg, 12–15 December 2016; pp. 4–8. [Google Scholar]
- Cox, J.H.; Clark, R.J.; Owen, H.L. Leveraging SDN for ARP security. In Proceedings of the SoutheastCon, Norfolk, VA, USA, 30 March–3 April 2016; pp. 1–8. [Google Scholar]
- Ranjbar, A.; Komu, M.; Salmela, P.; Aura, T. An SDN-based approach to enhance the end-to-end security: SSL/TLS case study. In Proceedings of the IEEE/IFIP Network Operations and Management Symposium, Istanbul, Turkey, 25–29 April 2016; pp. 25–29. [Google Scholar]
- Yao, L.; Dong, P.; Zheng, T.; Zhang, H.; Du, X.; Guizani, M. Network security analyzing and modeling based on petri net and attack tree for SDN. In Proceedings of the International Conference on Computing Networking and Communications, Kauai, HI, USA, 15–18 February 2016; pp. 15–18. [Google Scholar]
- Pisharody, S.; Chowdhary, A.; Huang, D. Security policy checking in distributed SDN based clouds. In Proceedings of the IEEE Communications and Network Security, Philadelphia, PA, USA, 17–19 October 2016; pp. 17–19. [Google Scholar]
- Martins, J.S.B.; Cmpos, M.B. A security architecture proposal for detection and response to threats in SDN networks. In Proceedings of the IEEE ANDESCON, Arequipa, Peru, 19–21 October 2016; pp. 19–21. [Google Scholar]
- Patel, P.; Tiwari, V.; Abhishek, M.K. SDN and NFV integration in openstack cloud to improve network services and security. In Proceedings of the International Conference on Advanced Communication Control and Computing Technologies, Ramanathapuram, India, 25–27 May 2016; pp. 25–27. [Google Scholar]
- Rupasinghe, P.L.; Kulatunga, K.M.D.S.B.; Murry, L.; Keseva, K. SDN based security solution for legislative email communications: Safe guarding communication. In Proceedings of the International Conference on Computing, Communication and Automation, Greater Noida, India, 29–30 April 2016; pp. 29–30. [Google Scholar]
- Ammar, M.; Rizk, M.; Hamid, A.A.; Seoud, A.K.A. A framework for security enhancement in SDN-based datacenters. In Proceedings of the IFIP International Conference on New Technologies Mobility and Security, Larnaca, Cyprus, 21–23 November 2016; pp. 21–23. [Google Scholar]
- Liu, Y.; Guo, Z.; Shou, G.; Hu, Y. To achieve a security service chain by integration of NFV and SDN. In Proceedings of the International Conference on Instrumentation and Measurement, Computer, Communication and Control, Harbin, China, 21–23 July 2016; pp. 21–23. [Google Scholar]
- Wilczewski, D. Security considerations for equipment controllers and SDN. In Proceedings of the IEEE International Telecommunications Energy Conference, Austin, TX, USA, 23–27 October 2016; pp. 23–27. [Google Scholar]
- Bull, P.; Austin, R.; Popov, E.; Sharma, M.; Watson, R. Flow based security for IoT Devices using an SDN gateway. In Proceedings of the IEEE 4th International Conference on Future Internet of Things and Cloud, Vienna, Austria, 22–24 August 2016; pp. 22–24. [Google Scholar]
- Gonzaiez, C.; Charfadine, S.M.; Flauzac, O.; Nolot, F. SDN-based security framework for the IoT in distributed grid. In Proceedings of the International Multidisciplinary Conference on Computer and Energy Science, Split, Croatia, 13–15 July 2016; pp. 13–15. [Google Scholar]
- Huq, S. Hardening the SDN optical transport network security—Is it a pleonasm or oxymoron? In Proceedings of the Optical Fiber Communications Conference and Exhibition, Anaheim, CA, USA, 20–24 March 2016; pp. 20–24. [Google Scholar]
- Basit, A.; Ahmed, N. Path diversity for inter-domain routing security. In Proceedings of the International Bhurban Conference on Applied Sciences and Technology, Islamabad, Pakistan, 10–14 January 2017; pp. 10–14. [Google Scholar]
- Rawat, D.B.; Reddy, S.R. Software defined networking architecture, security and energy efficiency: A survey. IEEE Commun. Surv. Tutor. 2017, 19, 325–346. [Google Scholar] [CrossRef]
- Dacier, M.C.; Konig, H.; Cwalinski, R.; Kargi, F.; Dietrich, S. Security challenges and opportunities of software-defined networking. IEEE Secur. Priv. 2017, 15, 96–100. [Google Scholar] [CrossRef]
- Li, C.; Qin, Z.; Novak, E.; Li, Q. Securing SDN infrastructure of IoT-Fog network from MitM Attacks. IEEE Internet Things J. 2017. Available online: http://ieeexplore.ieee.org/document/7883928/ (accessed 13 June 2017).
- Koo, S.K. Cyber security in South Korea: The threat within. The Diplomat. 2013. Available online: http://thediplomat.com/2013/08/cyber-security-in-south-korea-the-threat-within/ (accessed on 13 June 2017).
- Fortz, B.; Thorup, M. Internet traffic engineering by optimizing OSPF weights. INFOCOM 2000, 2, 519–528. [Google Scholar] [CrossRef]
- Zargar, S.T.; Joshi, J.; Tipper, D. A survey of defense mechanisms against distributed denial of service (DDoS) flooding attacks. IEEE Commun. Surv. Tutor. 2013, 15, 2046–2069. [Google Scholar] [CrossRef]
| Min. | Max. | Cost |
|---|---|---|
| 0 | 1/3 | 1 |
| 3/1 | 2/3 | 3 |
| 2/3 | 9/10 | 10 |
| 9/10 | 1 | 70 |
| 1 | 11/10 | 500 |
| 11/10 | ∞ | 5000 |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lee, W.; Kim, N. Security Policy Scheme for an Efficient Security Architecture in Software-Defined Networking. Information 2017, 8, 65. https://doi.org/10.3390/info8020065
Lee W, Kim N. Security Policy Scheme for an Efficient Security Architecture in Software-Defined Networking. Information. 2017; 8(2):65. https://doi.org/10.3390/info8020065
Chicago/Turabian StyleLee, Woosik, and Namgi Kim. 2017. "Security Policy Scheme for an Efficient Security Architecture in Software-Defined Networking" Information 8, no. 2: 65. https://doi.org/10.3390/info8020065
APA StyleLee, W., & Kim, N. (2017). Security Policy Scheme for an Efficient Security Architecture in Software-Defined Networking. Information, 8(2), 65. https://doi.org/10.3390/info8020065







