Abstract
A transitive signature scheme enables anyone to obtain the signature on edge by combining the signatures on edges and , but it suffers from signature theft and signature abuse. The existing work has solved these problems using a universal designated verifier transitive signature (UDVTS). However, the UDVTS scheme only enables the designated verifier to authenticate signatures, which provides a simple way for the signer to deny having signed some messages. The fact that the UDVTS is not publicly verifiable prevents the verifier from seeking help arbitrating the source of signatures. Based on this problem, this paper proposes a traceable universal designated verifier transitive signature (TUDVTS) and its security model. We introduce a tracer into the system who will trace the signature back to its true source after the verifier has submitted an application for arbitration. To show the feasibility of our primitive, we construct a concrete scheme from a bilinear group pair of prime order and prove that the scheme satisfies unforgeability, privacy, and traceability.
1. Introduction
In today’s information age, network information security is a hot topic all over the world. As a cryptographic technique to provide authentication services for electronic data, digital signatures allow a signer who has generated a public/private key pair to sign a message, and any other entity who knows the public key can verify the integrity and the source of data.
However, using traditional digital signatures to authenticate graph-based big data with chain relationships can result in significant communication costs. Given an administrative domain that involves four nodes, as depicted in Figure 1, A and B both belong to the same administrative domain if the edge is authentic. If both the edge and the edge are authentic, then A and C are in the same administrative domain. We need to provide two signatures ( and ) when disclosing the relationship between A and C to others using traditional digital signatures. Such an authentication method is very costly with big data. In 2002, Micali and Rivest [1] proposed the concept of a transitive signature, where anyone can compute a valid signature of the edge , from the signatures of two edges and .
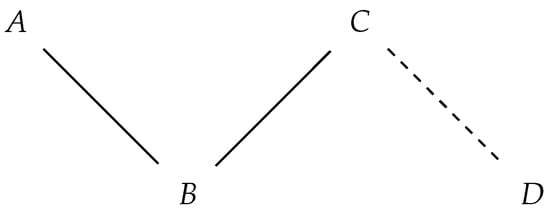
Figure 1.
An administrative domain. (Solid lines represent actual edges in the administrative domain, while dotted lines represent non-existent edges).
This method greatly reduces communication costs, but it creates the problem that transitive signatures may be abused, i.e., the signer cannot control who verifies the data, as the signature is publicly verifiable, allowing any entity to verify its validity.
To remove the public verifiability of transitive signatures, Hou et al. [2] introduced a universal designated verifier transitive signature (UDVTS), where only the designated verifier authenticates signatures. The verifier is designated by the combiner who combines transitive signatures. However, disputes may arise regarding the source of a signature. There are two cases: (1) the signer denies the signature generated by himself, e.g., we assume the edge is signed by a signer in Figure 1. B can convince the verifier (not in the same administrative domain as B) that A and C are in the same administrative domain. The signer denies that he had signed the edge when the private information was leaked. (2) The signer did not sign an edge , but the verifier framed the signer by using a simulated signature to make it appear as if the signer had signed the edge. This is because the non-transferability of the designated verifier signature requires the verifier to generate a signature that is indistinguishable from a designated verifier signature. It is also clear that, in the dispute, no arbitration service whatsoever is provided.
The above issues arise from the lack of public verifiability in the UDVTS. Arbitration service is, therefore, a closely watched issue in designated verifier signatures.
1.1. Our Contributions
While transitive signature disputes are easily resolved, the public verifiability also facilitates verifiers leaking signatures to a third party. Furthermore, UDVTS implementation sacrifices the public verifiability of transitive signatures to control the verifier (only the designated verifier can authenticate signatures). To achieve both the goal of controlling the verifier and arbitrability, this paper introduces the concept of a traceable universal designated verifier transitive signature (TUDVTS). Meanwhile, in order to avoid creating a huge arbitration institution, this article mandates a single individual with tracking and arbitration abilities, known as the tracer. The tracer can determine whether the disputed signature originated from the signer.
The specific contributions of this paper are as follows:
- (1)
- Our goal is to substitute the public verifiability of transitive signatures with single entity verifiability, where the entity is trusted. Therefore, we adopt the UDVTS proposed by [2]. Considering that the common issue of designated verifier signatures is that arbitration service cannot be provided when there is a signature dispute, we have introduced a tracer into the system that can find the true source of the signature.
- (2)
- We propose the concept of TUDVTS. We introduce to the UDVTS a tracer who is responsible for arbitrating any disputed data, and the chain relationships in the graphic remain hidden from other entities except the tracer. Therefore, this scheme protects the rights and interests of the signer and the verifier.
- (3)
- We describe definitions of TUDVTS and its security model. The security requirements of TUDVTS include unforgeability, privacy, and traceability. The unforgeability of TUDVTS means that any adversary cannot forge a transitive signature or a designated verifier signature even if it is allowed to obtain signatures on many other messages and public keys of its choice. The TUDVTS scheme encompasses two distinct forms of privacy: the non-transferability of TUDVTS and the privacy of transitive signatures. The former means that there is no way for anyone to distinguish between the two designated verifier signatures produced by the combiner or the verifier. The latter means that there is no way for anyone to distinguish between the two transitive signatures produced by the signer or the combiner. The traceability implies that the tracer can determine whether the signer signed the message.
- (4)
- We construct a TUDVTS scheme. By incorporating traceability, our scheme not only achieves the goal of controlling the verifier but also provides an arbitration service when signature disputes arise. We have conducted proofs to establish that our scheme satisfies the unforgeability, privacy, and traceability.
1.2. Related Works
We recall transitive signatures and universally designated verifier signatures in this section.
- Transitive Signatures (TS). The earliest transitive signature schemes, DLTS and RSATS-1, were proposed by Micali and Rivest [1], where their security relies on the discrete logarithm problem and the RSA assumption, respectively. Note that the former can resist adaptive chosen-message attacks, while the latter can only resist non-adaptive chosen-message attacks. In the same year, Bellare and Neven [3] proposed the “node certification paradigm” and constructed two schemes based on RSA assumption and factoring, respectively. In addition, they proposed other new schemes based on the one-more discrete logarithm problem and one-more gap Diffie-Hellman problem [4]. By employing braid groups, Wang et al. [5] designed a transitive signature scheme that was not susceptible to quantum attacks at the time. Previous schemes required special hash functions, which made them less efficient. Lin et al. [6] introduced a scheme that utilizes general hash functions to achieve improved efficiency by reducing computational time.
Hou et al. [2] proposed the UDVTS scheme to solve the problem of transitive signatures being stolen or abused; only the designated verifier has the ability to authenticate the signature. To serve more scenarios, Zhu et al. [7] proposed a transitive signature scheme with multiple verifiers designated and named it UDMVTS. Lin et al. [8] proposed a more efficient UDVTS scheme based on RSA assumption. Geontae et al. [9] designed the first lattice-based transitive signature scheme, which has the advantage of being resistant to quantum attacks. Then, Geontae et al. [10] designed the first identity-based transitive signature scheme.
All the above schemes are only applicable to undirected graphs. Currently, there are no proposed transitive signature schemes for general directed graphs. In fact, Hohenberger [11] shared that it is difficult to construct a general transitive signature scheme for directed graphs because it requires a special Abel TGII group, and there is no construction of such a group yet. Kuwakado and Tanaka [12] first proposed a TS scheme for directed trees but did not provide a concrete proof. Yi et al. [13] pointed out that Kuwakado’s scheme was not secure and then constructed a directed transitive signature scheme provably secure under the standard model. Neven et al. [14] designed a simpler transitive signature scheme to reduce the signature size. Camacho and Hcvia [15] constructed a scheme using a hash function with a common-prefix proof. Xu et al. [16] constructed a scheme using the RSA accumulator that preserves the composed signature size and protects its path information.
- Universal Designated Verifier Signatures (UDVS). Steinfeld et al. [17] introduced the concept of UDVS: only the verifier designated by the signature holder is allowed to authenticate signatures. Steinfeld et al. [17] proposed the first UDVS scheme by utilizing a BLS [18] short signature in the same year. They then combined the standard RSA and Schnor schemes to propose two identity-based UDVS schemes [19]. Ng et al. [20] proposed another scheme with multiple verifiers designated, allowing multiple verifiers to authenticate the signature. Zhang et al. [21] use the model proposed by Steinfeld et al. [17] to design two new identity-based UDVS schemes. The security of the above schemes all rely on the random oracle model. Zhang et al. [22] designed the first UDVS scheme that is provably secure in the standard model. Shahandashti et al. [23] provided a generic construction of UDVS from standard digital signatures. Since then, a multitude of UDVS schemes with distinct features have been put forward, such as multi-signer and multiple designated verifiers UDVS [24], UDVS without delegatability [25], universal designated verifier ring signatures [26], and universal designated multi-verifiers content extraction signatures [27]. To resist quantum attacks, Li et al. [28] constructed the first lattice-based UDVS scheme. Moreover, Tang et al. [29] pointed out that the strong privacy in traditional universal designated verifier signature schemes leads to the problem of unfairness to the verifier and, thus, designed a traceable universal designated verifier signature proof scheme.
2. Preliminaries
This section first gives a description of related symbols and introduces some basic concepts and related knowledge.
2.1. Notations
The notation means that an element a is randomly sampled from the set A. A (probabilistic polynomial-time) algorithm means that the algorithm is both probabilistic and runs in polynomial time. We define as a random oracle that responds to every unique query with a random response chosen uniformly from its output domain. If a query is repeated, it responds the same way every time that query is submitted. The notation denotes the probability of event X happening. We equate the notion of “negligible probability” with probabilities smaller than any inverse polynomial in n.
2.2. Graphs
This paper considers an undirected graph , where V is a points set and is an edges set. represents the transitive closure of G. It means that if and only if G contains a path from i to j. represents the transitive reduction in G. It is the graph with the minimum number of edges that possesses the equivalent transitive closure as G.
2.3. Admissible Bilinear Pairing
Let , be two groups of prime order p and let g be a generator of . An admissible bilinear mapping has the following properties:
- (1)
- Bilinearity: , for all .
- (2)
- Non-degeneracy: .
- (3)
- Computability: is efficiently computable for all .
2.4. Complexity Assumptions
Definition 1
(One-more Bilinear Diffie–Hellman (BDH) problem [30]). Let be a bilinear mapping, where and are groups of prime order p, and g is a generator of . Let , where . Given and the following two oracles:
- (1)
- The oracle : inputs a point , returns a random point .
- (2)
- The CDH oracle : inputs a point , returns a point .
An adversary is said to have solved the one-more BDH problem if it successfully computes n values of when the number of has queried strictly less than n.
3. Traceable Universal Designated Verifier Transitive Signature Scheme
The following describes the definitions and security model of the TUDVTS scheme. Hou et al. [2] proposed a universal designated verifier transitive signature (UDVTS). As a special case of UDVTS, the idea of the TUDVTS scheme is to allow the combiner to convert a composed signature into a translated signature before designating a verifier. Translation is performed by using the tracer’s public key. After the verification, the tracer can seek the true source of a designated verifier signature by using his own secret key. A TUDVTS scheme consists of ten efficient algorithms as follows:
- . The initialization algorithm that takes as input the security parameter k, outputs the public parameters .
- . The key generation algorithm that takes as input the public parameters , outputs all users’ public/secret key pairs .
- . The transitive signing algorithm that takes as input the signer’s secret key and nodes and outputs an original signature of edge relative to .
- . The verification algorithm that takes as input the signer’s public key , nodes , and a candidate signature , which outputs 1 if accepting the signature or 0 for rejecting it.
- . The composition algorithm that takes as input the signer’s public key ,nodes , and two signatures , which outputs the composed signature or the symbol ⊥to indicate failure.
- . The translation algorithm that takes as input the tracer’s public key and a transitive signature of edge and outputs a translated signature . In addition, the combiner selects and saves a secret value t.
- . The signature holder’s designation algorithm that takes as input the verifier’s public key , nodes , a secret value t, and a translated signature , which outputs a designated verifier signature .
- . The transcript simulation algorithm that takes as input the signer’s public key , the tracer’s public key , the verifier’s secret key , nodes , and the translated signature , which outputs a simulated signature .
- . The designated verifying algorithm that takes as input the signer’s public key , the verifier’s secret key , nodes , and a designated verifier signature , which outputs 1 if accepting the signature or 0 for rejecting it.
- . The tracing algorithm that takes as input the tracer’s secret key and the translated signature , which outputs the transitive signature .
- Correctness: we require five obvious correctness properties in TUDVTS. The first four points are the correctness requirements of UDVTS. Algorithm TVry checks the correctness of TSign and Comp. Algorithm DV checks the correctness of DS and Sim. Algorithm Trans checks the correctness of Trace.
- Correctness of TSign: If , then
- Correctness of Comp: If , thenwhere are legitimate signatures (the signature is either obtained by the signer or by running Comp on legitimate signatures).
- Correctness of DS: If , then
- Correctness of Sim: If , then
- Correctness of Trace: If , then .
Security Models
A secure TUDVTS scheme satisfies unforgeability, privacy, and traceability. The following are definitions of these security properties.
- Unforgeability: the unforgeability of TUDVTS is similar to the unforgeability of UDVTS. TUDVTS encompasses two distinct forms of unforgeability. The first property refers to the fact that any adversary cannot output a forgery even if it is allowed to obtain transitive signatures on many other messages of its choice, i.e., the transitive signature unforgeability (TS-unforgeability). The second property refers to the impossibility for any adversary to forge a valid designated verifier signature even if they possess a valid translated signature from before, i.e., the designated verifier signature unforgeability (DV-unforgeability). Note that it is possible that the translated signature in DV-unforgeability is forged. As described in reference [29], we only consider this case where the translated signature is sent by the designator.
TS-unforgeability requires that any adversary cannot output a transitive signature on a disconnected edge. A disconnected edge is one that does not belong to the transitive closure of the graph composed of all pairs signed by the signer.
We let denote an execution of the experiment for a given TUDVTS and adversary . The experiment is defined as follows:
- Setup: the public parameters and the signer’s public/secret key-pair are generated by running Setup and KGen, respectively. Then, it is sent to .
- TSign Query: picks an edge . Then, the transitive signature is generated by running TSign and sent to .
In the end, outputs an edge and its signature . The experiment outputs 1 if and , where is the transitive closure of the graph G composed of all pairs submitted to TSign Query.
The advantage of in the is defined as
Definition 2
(TS-Unforgeability). The transitive signature is unforgeable under adaptive chosen-message attacks if is negligible for any adversary .
DV-unforgeability requires that any adversary cannot output a designated verifier signature on an edge using the designated verifier’s public key, where the edge and the public key have not been used as input to query the designated verifier signature.
We let denote an execution of the experiment for a given TUDVTS and adversary . The experiment is defined as follows:
- Setup: the public parameters and all users’ public/secret key-pairs are generated by running Setup and KGen, respectively. Then, it is sent to .
- Trans Query: picks an edge . The transitive signature is first generated by running TSign. Then, the translated signature is generated by running Trans and sent to . The secret value t is kept private.
- DS Query: picks an edge (), a verifier’s public key and the corresponding translated signature . He initially acquires the signature using the aforementioned procedure in the absence of the translated signature. Then, is generated by running DS and sent to .
- DV Query: requests the verification result of () using the chosen public key . The verification result is generated by running DV and sent to .
- SKey Query: picks a verifier’s public key . Then, the corresponding private key is sent to .
In the end, it returns a forgery on edge with chosen by himself. The experiment outputs 1 if:
- -
- DV().
- -
- has never been submitted to DS Query.
- -
- has never been submitted to SKey Query.
The advantage of in the is defined as
Definition 3
(DV-Unforgeability). A TUDVTS scheme is unforgeable under adaptive chosen-message and chosen-public-key attacks if is negligible for any adversary , where invokes at most Trans Query, DS Query, DV Query and SKey Query in time t.
The main difference between the above definition and [2] is that here, queries the translated signature instead of the transitive signature.
Privacy: the privacy has been systematically discussed by Hou et al. in [2]. There are two types of privacy in the TUDVTS scheme: non-transferability of TUDVTS and privacy of transitive signature. As stated in [17], the designated verifier has the capability to produce a signature that cannot be distinguished from the signature generated by the signature holder. That is, the verifier is unable to provide convincing evidence to others that the signer has indeed signed the message. As stated in [1], The second condition states that a transitive signature and a composed signature on the same edge cannot be distinguished. This implies that the Comp algorithm can operate properly even if its input was generated using Comp itself.
The non-transferability of TUDVTS requires that any distinguisher cannot distinguish a designated verifier signature and the corresponding simulated signature.
We let denote an execution of the experiment for a given TUDVTS and distinguisher . The experiment is defined as follows:
- Setup: the public parameters and all users’s public/secret key-pairs are generated by running Setup and KGen, respectively. Then, it is sent to .
- Stage 1: the distinguisher adaptively makes Trans Query, DS Query, DV Query, Sim Query, SKey Query: it responds to in the same way as in game .
- -
- Sim Query: assuming that requests a simulated signature on edge () using the chosen public key , he initially acquires the signature using the aforementioned procedure in the absence of the translated signature. Then, the simulated signature is generated by running Sim and sent to .
- Challenge stage: returns and that satisfy the following conditions:
- -
- .
- -
- has never been submitted to DS Query and Sim Query.
- -
- has never been submitted to SKey Query.
In reply, the experiment randomly samples . If , then the signature is generated by running DS and returned to . Otherwise, the signature is generated by running Sim and returned to . - Stage 2. Upon the receipt of the signature, can still proceed with the query in stage 1. However, he cannot choose for DS Query or Sim Query.
- Guess stage. outputs his guess .
If , then wins the game. The advantage of in the is defined as
Definition 4
(Non-Transferability of TUDVTS). If is negligible for any distinguisher , then the TUDVTS scheme is non-transferable under adaptive chosen-message and chosen-public-key attacks.
Privacy of transitive signatures requires that any distinguisher cannot distinguish between transitive signatures and composed signatures on the same edges.
Definition 5
(Privacy of Transitive Signature). If the input of Comp is legitimate signatures, then the distributions that the composed signature and the signature generated by the signer follow are statistically indistinguishable.
- Traceability: as stated in [29], in order to determine whether the signer signed the message, we introduce a tracer in UDVTS. The tracer can restore the translated signature to its corresponding transitive signature . According to TV-unforgeability, only the signer and the combiner have the ability to obtain valid transitive signatures. Thus, the tracer can track the identity of the translated signature generator by checking whether the transitive signature is valid.
Definition 6
(Traceability). If the translated signature is calculated by the combiner, then the transitive signature can be recovered by the tracer.
4. Our TUDVTS Scheme
In this section, we present a concrete construction of the TUDVTS scheme and its security results.
4.1. Construction
Our scheme TUDVTS = (Setup, KGen, TSign, TVry, Comp, Trans, DS, DV, Sim, Trace) is constructed as follows: Given a group generator GGen that takes as input and outputs a triple , where p is a lagre prime and are two p-order multiplicative cyclic groups. Denote and as two hash functions.
- Setup(): this algorithm first obtains by running GGen. Then, it generates a bilinear map and a generator g of and outputs the public parameters ).
- KGen(): this algorithm takes as input the public parameters . It computes , where . It outputs three pairs of public/secret keys , which denote the signer, the verifier, and the tracer, respectively.
- TSign(): this algorithm takes as input the signer’s secret key a and nodes . It computes if , where . If , swap i and j.
- TVry(): this algorithm takes as input the signer’s public key A, nodes , and a signature . If , then it outputs 1 (accept). Otherwise, it outputs 0 (reject).
- Comp(): this algorithm takes as input the signer’s public key A, nodes , and two signatures of and of . If and are both valid signatures, then it outputs the composed signature of . Otherwise, it outputs ⊥.
- Trans(): this algorithm takes as input the tracer’s public key D and the signature of . The combiner computes , where . He outputs the translated signature .
- DS(): this algorithm takes as input the verifier’s public key B and the translated signature . The combiner randomly chooses , and calculates and Then, he outputs the designated verifier signature .
- Sim(): this algorithm takes as input the signer’s public key A, the tracer’s public key D and notes . The verifier randomly picks , and calculates and Then, he outputs a simulated signature .
- DV(): this algorithm takes as input the signer’s public key A, the tracer’s public key D, notes and the signature . The designated verifier calculates and checks whether . If this holds, then the algorithm outputs 1 (accept). Otherwise, it outputs 0 (reject).
- Trace(): this algorithm takes as input the translated signature . The tracer computes and checks whether . If this holds then is legitimate.
4.2. Correctness
Here, we show five correctness properties in our TUDVTS.
- Correctness of TSign: if , where , then
- Correctness of Comp: If , where , then
- Correctness of DS: if andthen .
- Correctness of Sim: If andthen .
- Correctness of Trace: if , then
4.3. Security Analysis
Here, we show the following theorems and provide rigorous formal proofs.
Theorem 1
(DV-Unforgeability). Assuming the one-more BDH assumption holds in () using the public parameters , we can conclude that the TUDVTS scheme satisfies DV-unforgeability under adaptive chosen-message and chosen-public-key attacks, with parameters ().
Proof.
Suppose there are n verifiers in the system. If there exist a adversary for breaking DV-unforgeability of TUDVTS with , we construct a challenger for solving one-more BDH problem with , such that
Given an instance of one-more BDH problem, a public parameter D, and , where . ’s aim is to output n values of , under the requirement that has been made less than n queries. Denote the set that comprises all queried vertices as V. Denote the function that stores all queried edge signatures as . performs the simulation work according to this instance as follows with adversary :
- Setup:
- 1.
- sets A as the signer’s public key and sets D as the tracer’s public key.
- 2.
- computes as the public key of the verifier , where is his private key. For , sets B as his public key. Then, maintains a list L and adds all the pairs () to L, where .
- 3.
- sends () to .
- Query:
- 1.
- maintains a list to record the hash values output by calling .
- 2.
- When queries , completes the following:
- -
- If , then ; ; ; ; .
- -
- returns to .
- Query:
- 1.
- maintains a list to record the hash values output by oracle. randomly picks a verifier’s public key and a number and computes .
- 2.
- When queries , completes the following:
- -
- Firstly, obtains and as above if the two hash values do not exist.
- -
- Returns to . Then, adds all the message/value pairs to .
- Trans Query: assuming that requests a translated signature on an edge () that he has chosen. In reply, firstly obtains the signature if is empty. performs the following (assume ):
- 1.
- If or , invokes to obtain or .
- 2.
- If is empty, then; .
- 3.
- For all ,If is empty, then ; .If is empty, then ; .
- 4.
- .
- 5.
- randomly picks , computes and . maintains a list and stores all the random numbers t to .
- 6.
- Returns () to , and stores the corresponding t in .
- DS Query: assuming that requests a designated verifier signature on edge () using the chosen public key , firstly obtains the translated signature as above if the signature does not exist. Then, randomly selects and calculates and , returns to adversary .
- DV Query: assuming that requests a verification result of () using the chosen public key , calculates , returns 1 if , otherwise returns 0.
- SKey Query: assuming that requests the corresponding private key using the chosen public key , outputs the corresponding private key if . Otherwise, the operation aborts. The probability of not aborting is .
- Forgery: eventually, takes as input and , obtains by asking for the oracle, when the edge and the verifier’s public key chosen by himself. Then, he obtains a translated signature by Trans Query and computes . In the end, returns a forgery signature . If , then the operation aborts. The probability of not aborting is . We assume , otherwise can query the by himself. Let the graph be composed of all pairs submitted to Trans Query and let be the transitive closure of G. is valid if it satisfies the following:
- -
- DV().
- -
- has never been submitted to DS Query.
- -
- has never been submitted to SKey Query.
can compute the BDH values of all vertices in V by using . V is decomposed into m disjoint subsets , which is intended to separate and . Let but . For all , picks a reference node . The BDH values for all nodes in can be calculated by performing the following steps:
- 1.
- .
- 2.
- .For all ,
- 3.
- .
- 4.
- .
Otherwise, the BDH values for all nodes in can be calculated by performing the following steps:
- 1.
- .
- 2.
- .For all ,
- 3.
- .
- 4.
- .
Now outputs the BDH values for all . For each , queried times to compute the signature (the number of edges in a minimal spanning tree of ), and queried once to compute , the number of for each is summed to . For , did not need the additional query to compute the . Therefore, outputs BDH values using CDH oracle and, hence, solves the one-more BDH problem.
Below, we consider the probability of not aborting. If does not abort, the following conditions must be satisfied:
- -
- has never been submitted to SKey Query.
- -
- In the output forgery, chooses the public key B.
Obviously, the probability that both conditions are satisfied is greater than ; hence,
This completes the proof. □
Theorem 2
(TS-Unforgeability). Assuming the one-more BDH assumption holds in the bilinear group pair () using the public parameters , we can conclude that the transitive signature is unforgeable under an adaptive chosen-message attack.
Proof.
Given an instance of one-more BDH problem, oracle and the CDH oracle . ’s aim is to output n values of , but the CDH oracle has been made strictly less than n queries. Let V denote the set that comprises all queried vertices. performs the simulation work according to this instance as follows with adversary :
- Setup: sets A as the signer’s public key and returns to .
- TSign Query: assuming that requests a signature on an edge () that he has chosen. In reply, performs the following (Assume ):
- 1.
- If or , invokes to obtain or .
- 2.
- If is empty, then; .
- 3.
- For all ,If is empty, then ; .If is empty, then ; .
- 4.
- .
- 5.
- Returns to .
- Then, adaptively invokes the oracle. responds to in the same way as in the proof above.
In the end, outputs an edge and the signature . If and , then is said to be a valid forgery.
The one-more BDH problem is solved based on this forgery, as in the proof of the Theorem 1 method. is used to find the BDH value of vertex . Thus, solving for the BDH values of all vertices in V, queries at most . This completes the proof. □
Theorem 3
(Non-Transferability of TUDVTS). Our scheme satisfies the non-transferability of TUDVTS against the adaptive chosen-message and chosen-public-key distinguisher .
Proof.
Suppose is a challenger. ’s goal is to distinguish between a designated verifier signature and its corresponding simulated signature.
- Setup:
- 1.
- sets as the public key of the signer and the tracer, respectively, where .
- 2.
- sets as the ith () verifier’s public/private key-pair, where . Then, maintains a list L and adds all the public/private key-pairs to L.
- 3.
- sends () to .
- Stage 1: the distinguisher adaptively invokes Query, Query, Trans Query, DS Query, DV Query, Sim Query, SKey Query. It responds to in the same way as in game .
- -
- SKey Query: if requests the private key associated with a chosen public key , verifies the list L and provides the matching private key in response.
- -
- Sim Query: assuming that requests a simulated signature on edge () using the chosen public key , firstly obtains the translated signature as above if the signature does not exist. Then, randomly selects and calculates and , returns to distinguisher .
- Challenge stage: returns and that satisfy the following conditions:
- -
- .
- -
- has never been submitted to DS Query and Sim Query.
- -
- has never been submitted to SKey Query.
In reply, randomly samples . If , then the signature is generated by running DS and returned to . Otherwise, the signature is generated by running Sim and returned to . - Stage 2: upon the receipt of the signature, can still proceed with the query in Stage 1. However, he cannot query the translated signature on edge , and cannot choose for DS Query or Sim Query.
- Guess stage: outputs his guess .
Suppose is a valid designated verifier signature, since
where . Similarly,
where .
Therefore, the designated verifier signature and the simulated signature on the same edge and public key are statistically indistinguishable. This completes the proof. □
Theorem 4
(Privacy of Transitive Signature). If the input of Comp is legitimate signatures, then the distributions of the composed signature and the signature generated by the signer are statistically indistinguishable.
Proof.
Let and be the legitimate signatures of edge and edge with respect to the public key A. Then, and , where . Taking as input Comp, it outputs the composed signature
Hence, the signature generated by the signer and the composed signature on the same edge are statistically indistinguishable. This completes the proof. □
Theorem 5
(Traceability). The TUDVTS scheme is traceable, which can check whether the signer signed the message.
Proof.
Suppose the verifier sends a translated signature to the tracer. The tracer can calculate:
Then, the tracer checks whether holds. If this holds then is legitimate, i.e., the signer signed the edge. This completes the proof. □
5. Efficiency Analysis
Since no other TUDVTS schemes have been proposed, we mainly discuss the size of the signature generated by the scheme and the time cost of its sub-algorithms and compare its efficiency with UDVTS. Let denote the bit length of the element in and , respectively. Let be the time cost of performing one exponentiation, pairing, hash, inverse, and multiply operation, respectively. We have the following Table 1 and Table 2.

Table 1.
Signature size.

Table 2.
Time cost.
6. Conclusions
This paper introduces the concept of traceable universal designated verifier transitive signatures (TUDVTS) and formally depicts the framework of TUDVTS and its security model. In the new framework, the tracer can find the true source of the disputed signature. We next construct a concrete scheme in the random oracle model, whose unforgeability relies on the one-more BDH assumption. The public key, the transitive signature, the translated signature, and the designated verifier signature in our construction are bits, bits, bits, and bits, respectively.
Author Contributions
Conceptualization, S.H., C.L. and S.Y.; methodology, S.H., C.L. and S.Y.; writing—original draft preparation, S.H.; writing—review and editing, C.L. and S.Y.; supervision, C.L. and S.Y.; project administration, S.Y. All authors have read and agreed to the published version of the manuscript.
Funding
This work is supported by the National Natural Science Foundation of China (62032005, 62172096, 62272104), Natural Science Foundation of Fujian Province, China (2020J02016).
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
No new data were created or analyzed in this study. Data sharing is not applicable to this article.
Conflicts of Interest
The authors declare no conflicts of interest.
References
- Micali, S.; Rivest, R.L. Transitive Signature Schemes. In Topics in Cryptology—CT-RSA 2002; Preneel, B., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; pp. 236–243. [Google Scholar]
- Hou, S.; Huang, X.; Liu, J.K.; Li, J.; Xu, L. Universal Designated Verifier Transitive Signatures for Graph-Based Big Data. Inf. Sci. 2015, 318, 144–156. [Google Scholar] [CrossRef]
- Bellare, M.; Neven, G. Transitive Signatures Based on Factoring and RSA. In Advances in Cryptology—ASIACRYPT 2002; Zheng, Y., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; pp. 397–414. [Google Scholar]
- Bellare, M.; Neven, G. Transitive Signatures: New Schemes and Proofs. IEEE Trans. Inf. Theory 2005, 51, 2133–2151. [Google Scholar] [CrossRef]
- Wang, L.; Cao, Z.; Zheng, S.; Huang, X.; Yang, Y. Transitive Signatures from Braid Groups. In Progress in Cryptology—INDOCRYPT 2007; INDOCRYPT’07; Springer: Berlin/Heidelberg, Germany, 2007; pp. 183–196. [Google Scholar]
- Lin, C.; Zhu, F.; Wu, W.; Liang, K.; Choo, K.K.R. A New Transitive Signature Scheme. In Network and System Security; Chen, J., Piuri, V., Su, C., Yung, M., Eds.; Springer: Cham, Switzerland, 2016; pp. 156–167. [Google Scholar]
- Zhu, F.; Zhang, Y.; Lin, C.; Wu, W.; Meng, R. A Universal Designated Multi-Verifier Transitive Signature Scheme. In Information Security and Cryptology; Chen, X., Lin, D., Yung, M., Eds.; Springer: Cham, Switzerland, 2018; pp. 180–195. [Google Scholar]
- Lin, C.; Wu, W.; Huang, X.; Xu, L. A New Universal Designated Verifier Transitive Signature Scheme for Big Graph Data. J. Comput. Syst. Sci. 2017, 83, 73–83. [Google Scholar] [CrossRef]
- Noh, G.; Jeong, I.R. Transitive Signature Schemes for Undirected Graphs from Lattices. KSII Trans. Internet Inf. Syst. 2019, 13, 3316–3332. [Google Scholar]
- Noh, G.; Chun, J.Y. Identity-Based Transitive Signature Scheme from Lattices. J. Korea Inst. Inf. Secur. Cryptol. 2021, 31, 509–516. [Google Scholar]
- Rivest, R.; Hohenberger, S. The Cryptographic Impact of Groups with Infeasible Inversion. Doctoral Dissertation, Massachusetts Institute of Technology, Cambridge, MA, USA, 2003. [Google Scholar]
- Kuwakado, H.; Tanaka, H. Transitive Signature Scheme for Directed Trees. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 2003, 86-A, 1120–1126. [Google Scholar]
- Yi, X. Directed Transitive Signature Scheme. In Topics in Cryptology—CT-RSA 2007, The Cryptographers’ Track at the RSA Conference 2007, San Francisco, CA, USA, 5–9 February 2007, Proceedings; Abe, M., Ed.; Springer: Berlin/Heidelberg, Germnay, 2007; Volume 4377, pp. 129–144. [Google Scholar]
- Neven, G. A Simple Transitive Signature Scheme for Directed Trees. Theor. Comput. Sci. 2008, 396, 277–282. [Google Scholar] [CrossRef][Green Version]
- Camacho, P.; Hevia, A. Short Transitive Signatures for Directed Trees. In Topics in Cryptology—CT-RSA 2012; Dunkelman, O., Ed.; CT-RSA 2012. Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7178, pp. 35–50. [Google Scholar]
- Xu, J.; Chang, E.; Zhou, J. Directed Transitive Signature on Directed Tree. In Proceedings of the Singapore Cyber-Security Conference (SG-CRC) 2016-Cyber-Security by Design, Singapore, 14–15 January 2016; Cryptology and Information Security Series. Mathur, A., Roychoudhury, A., Eds.; IOS Press: Amsterdam, The Netherlands, 2016; Volume 14, pp. 91–98. [Google Scholar]
- Steinfeld, R.; Bull, L.; Wang, H.; Pieprzyk, J. Universal Designated-Verifier Signatures. In Advances in Cryptology—ASIACRYPT 2003; Laih, C.S., Ed.; ASIACRYPT 2003. Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2894, pp. 523–542. [Google Scholar]
- Boneh, D.; Lynn, B.; Shacham, H. Short Signatures from the Weil Pairing. In Advances in Cryptology—ASIACRYPT 2001; Boyd, C., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; pp. 514–532. [Google Scholar]
- Steinfeld, R.; Wang, H.; Pieprzyk, J. Efficient Extension of Standard Schnorr/RSA Signatures into Universal Designated-Verifier Signatures. In Public Key Cryptography-PKC 2004, 7th International Workshop on Theory and Practice in Public Key Cryptography, Singapore, 1–4 March 2004; Lecture Notes in Computer Science; Bao, F., Deng, R.H., Zhou, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 2947, pp. 86–100. [Google Scholar]
- Ng, C.Y.; Susilo, W.; Mu, Y. Universal Designated Multi Verifier Signature Schemes. In Proceedings of the 11th International Conference on Parallel and Distributed Systems, ICPADS 2005, Fuduoka, Japan, 20–22 July 2005; pp. 305–309. [Google Scholar]
- Zhang, F.; Susilo, W.; Mu, Y.; Chen, X. Identity-Based Universal Designated Verifier Signatures. In Embedded and Ubiquitous Computing-EUC 2005 Workshops, EUC 2005 Workshops: UISW, NCUS, SecUbiq, USN, and TAUES, Nagasaki, Japan, 6–9 December 2005, Proceedings; Lecture Notes in Computer Science; Enokido, T., Yan, L., Xiao, B., Kim, D., Dai, Y., Yang, L.T., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3823, pp. 825–834. [Google Scholar]
- Zhang, R.; Furukawa, J.; Imai, H. Short Signature and Universal Designated Verifier Signature Without Random Oracles. In Applied Cryptography and Network Security, Third International Conference, ACNS 2005, New York, NY, USA, 7–10 June 2005, Proceedings; Lecture Notes in Computer Science; Ioannidis, J., Keromytis, A.D., Yung, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3531, pp. 483–498. [Google Scholar]
- Shahandashti, S.F.; Safavi-Naini, R. Generic Constructions for Universal Designated-Verifier Signatures and Identitybased Signatures from Standard Signatures. IET Inf. Secur. 2009, 3, 152–176. [Google Scholar] [CrossRef]
- Chang, T.Y. An ID-Based Multi-Signer Universal Designated Multi-Verifier Signature Scheme. Inf. Comput. 2011, 209, 1007–1015. [Google Scholar] [CrossRef]
- Huang, X.; Susilo, W.; Mu, Y.; Wu, W. Universal Designated Verifier Signature Without Delegatability. In Information and Communications Security, 8th International Conference, ICICS 2006, Raleigh, NC, USA, 4–7 December 2006, Proceedings; Lecture Notes in Computer Science; Ning, P., Qing, S., Li, N., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4307, pp. 479–498. [Google Scholar]
- Li, J.; Wang, Y. Universal Designated Verifier Ring Signature (Proof) Without Random Oracles. In Emerging Directions in Embedded and Ubiquitous Computing, EUC 2006 Workshops: NCUS, SecUbiq, USN, TRUST, ESO, and MSA, Seoul, Korea, 1–4 August 2006, Proceedings; Lecture Notes in Computer Science; Zhou, X., Sokolsky, O., Yan, L., Jung, E., Shao, Z., Mu, Y., Lee, D.C., Kim, D., Jeong, Y., Xu, C., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4097, pp. 332–341. [Google Scholar]
- Wang, M.; Zhang, Y.; Ma, J.; Wu, W. A Universal Designated Multi Verifiers Content Extraction Signature Scheme. Int. J. Comput. Sci. Eng. 2020, 21, 49–59. [Google Scholar] [CrossRef]
- Li, B.H.; Liu, Y.Z.; Yang, S. Lattice-Based Universal Designated Verifier Signatures. In Proceedings of the 15th International Conference on e-Business Engineering, ICEBE, Xi’an, China, 12–14 October 2018; IEEE Computer Society. pp. 329–334. [Google Scholar]
- Tang, F.; Ma, S.; Ma, C.L. Traceable Universal Designated Verifier Signature Proof Scheme. Ruan Jian Xue Bao/J. Softw. 2022, 33, 4305. [Google Scholar]
- Gao, W.; Wang, G.; Wang, X.; Li, F. Round-Optimal ID-Based Blind Signature Schemes without ROS Assumption. J. Commun. 2012, 7, 909–920. [Google Scholar] [CrossRef][Green Version]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).