A Robust and Hybrid Cryptosystem for Identity Authentication
Abstract
1. Introduction
2. Related Work
3. Methodology
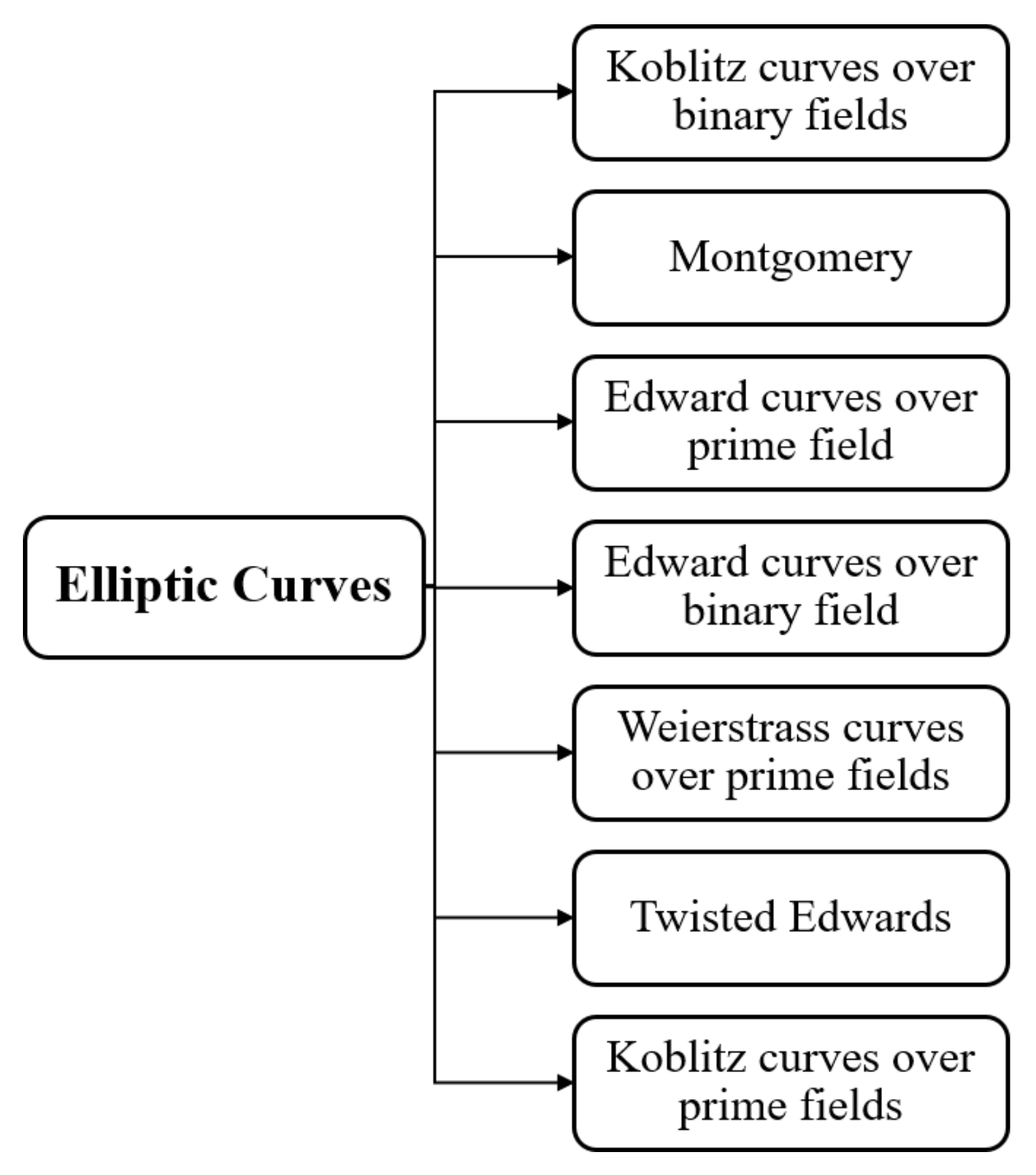
3.1. Elliptic Curve Cryptosystem (ECC)
- (1)
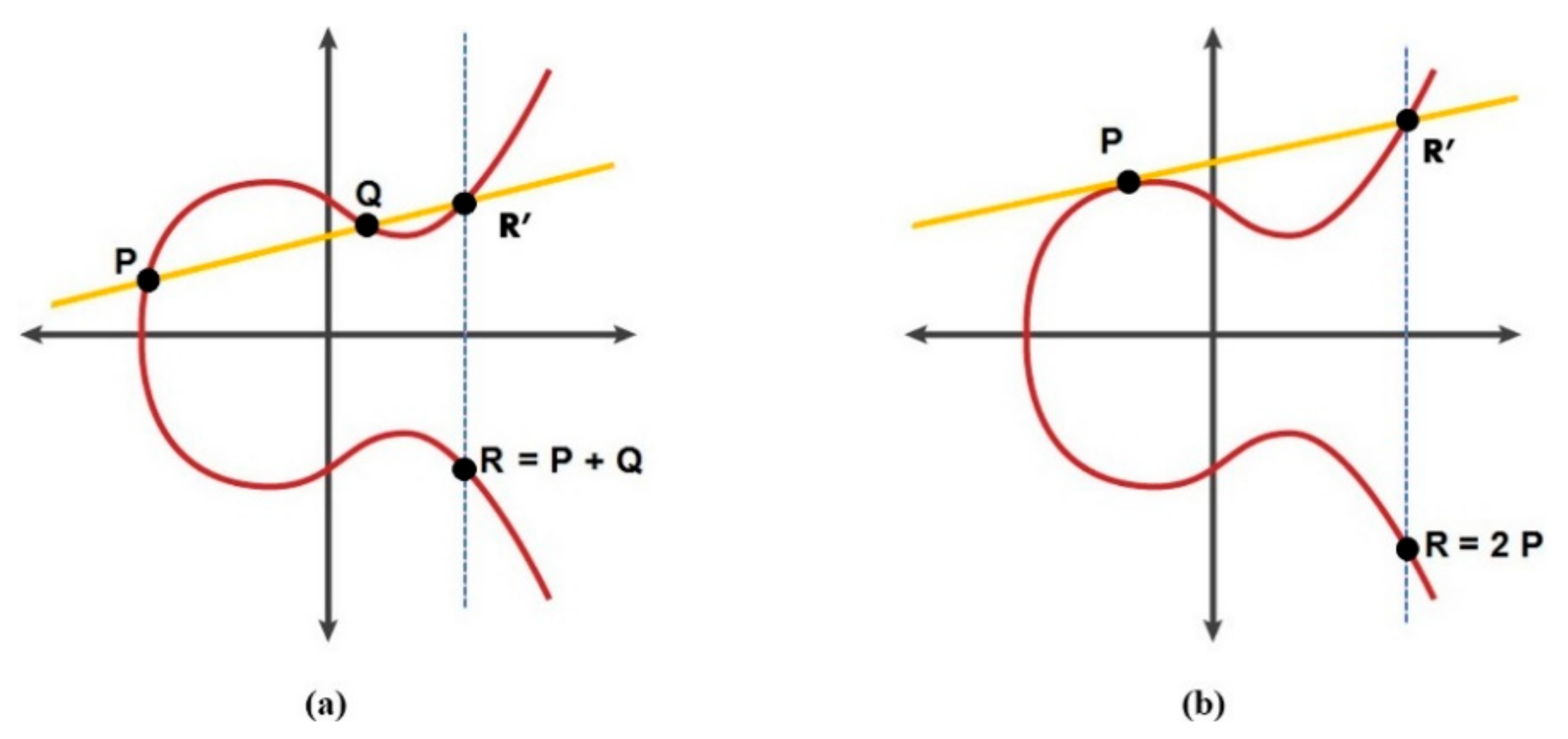
- If P > Q: R = P + Q, which can be calculated by drawing a line passing through P and Q, then R is the mirror point of the third intersection point (R′), as shown in Figure 2a.
- (2)
- If P = Q: R = 2Q, which can be estimated by drawing a tangent line through Q, then the doubling point R is the mirror point of the second intersection point, as clarified in Figure 2b.wherex3 = µ2 − x1 − x2 mod pandy3 = µ (x1 − x3) − y1 mod p
3.2. OSS Signature Scheme
3.3. Logistic Map and Cyclic Group
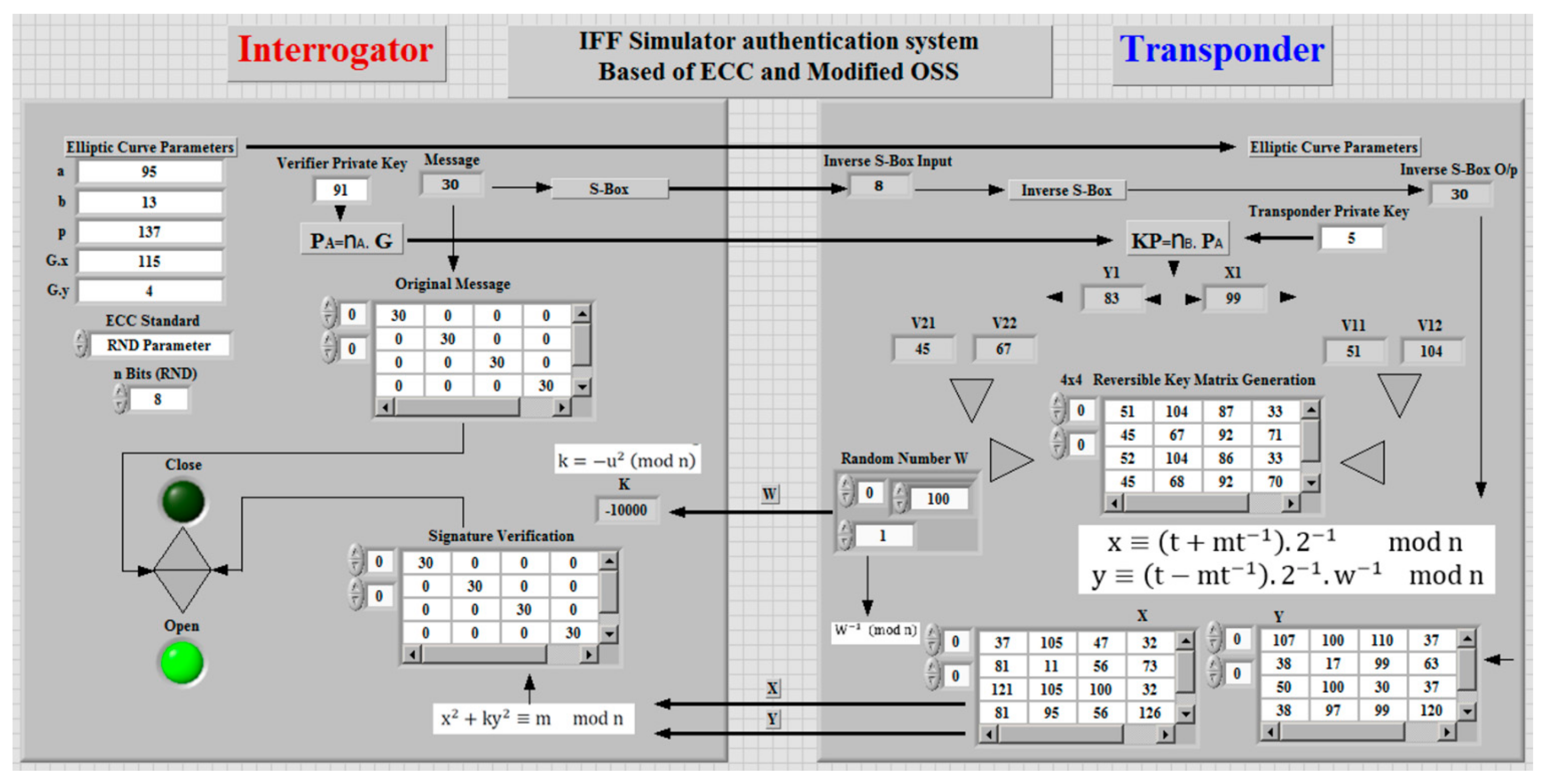
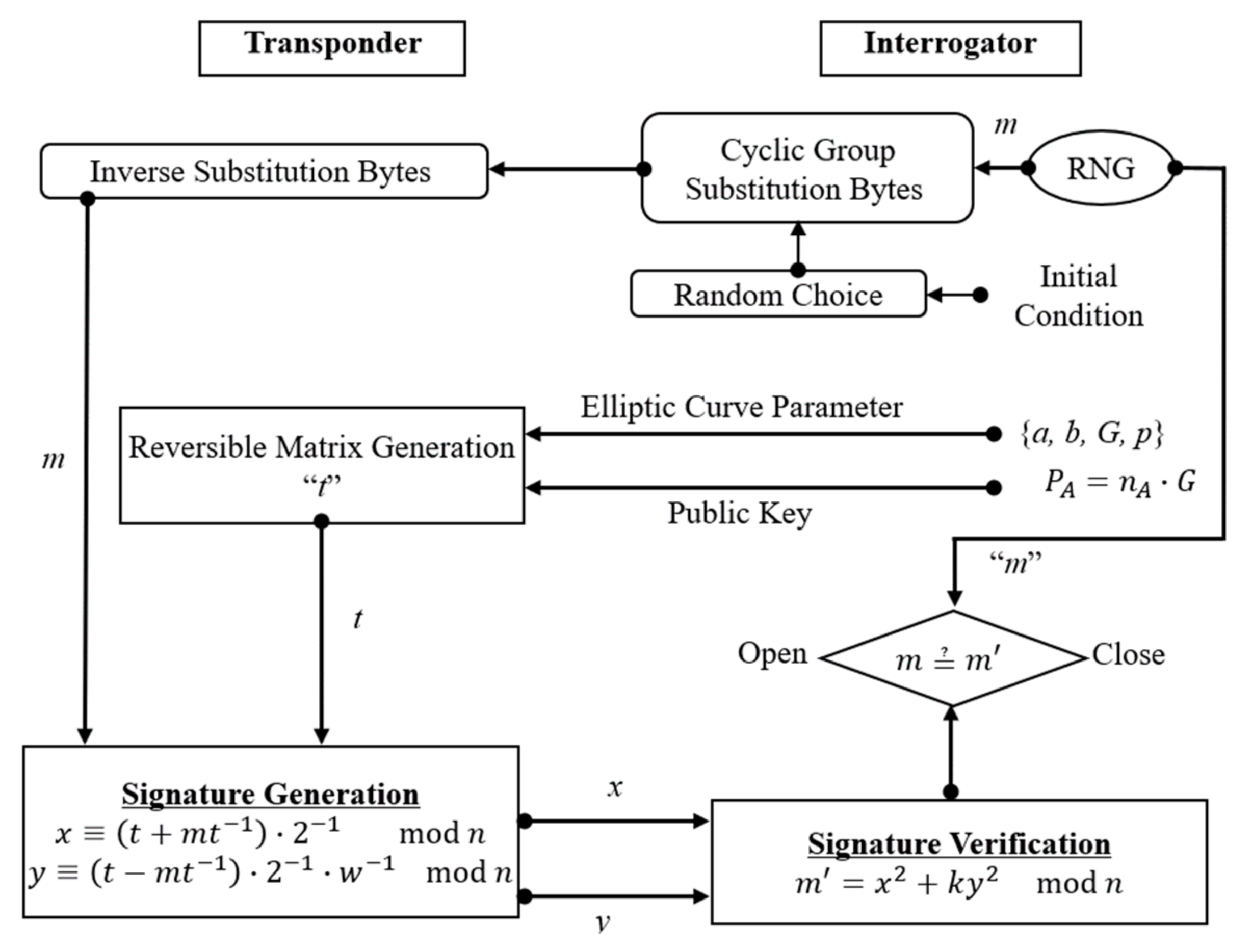
4. The Proposed Oss–ECC Digital Signature
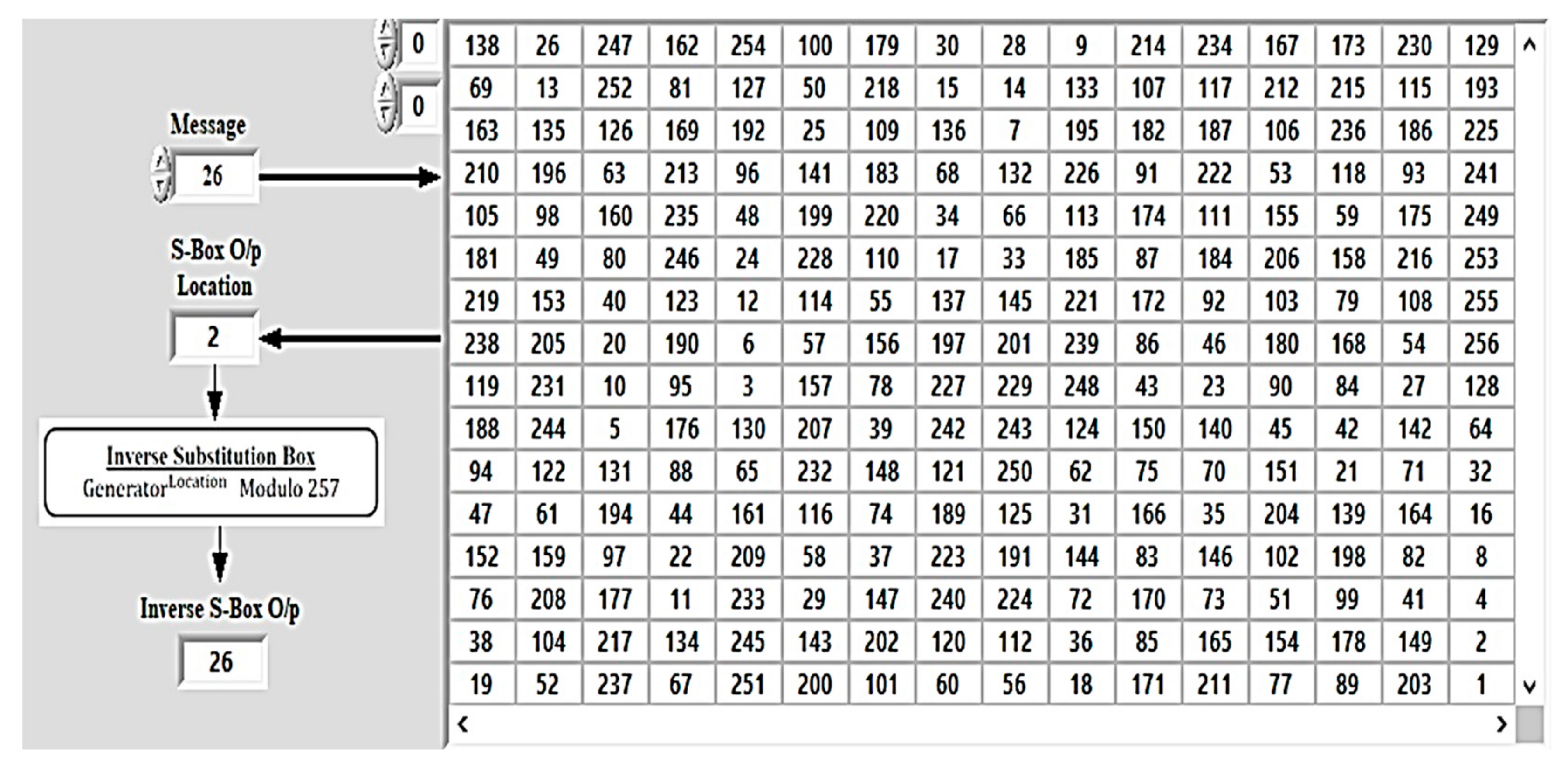
4.1. Substitution-Box (S-Box) Construction
4.2. Random Choice
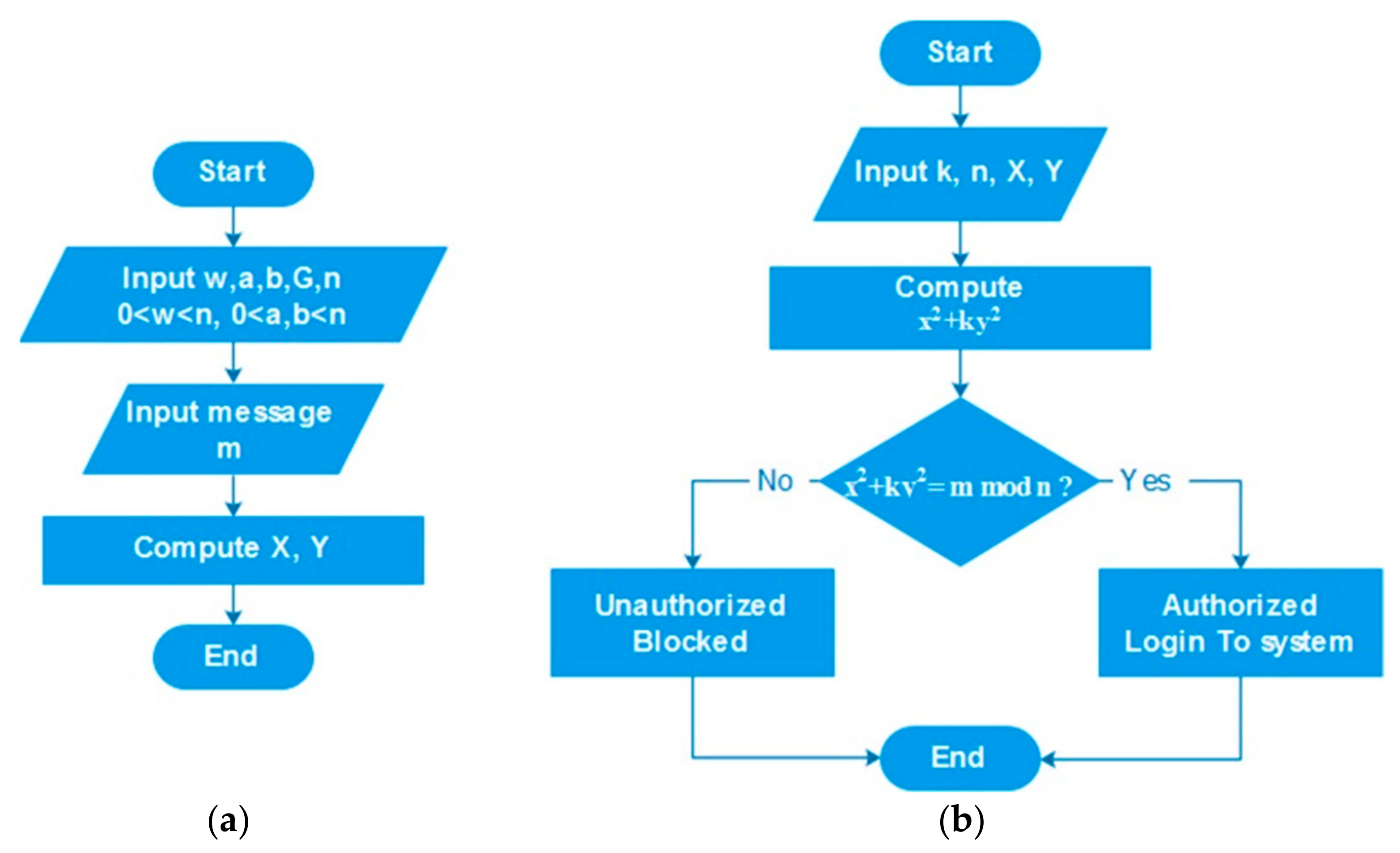
4.3. Signature Generation and Verification
- Transponder and interrogator agree on parameters of the elliptic curve function;
- The transponder sends a signal with digital signature to interrogator;
- Interrogator verifies the signature.
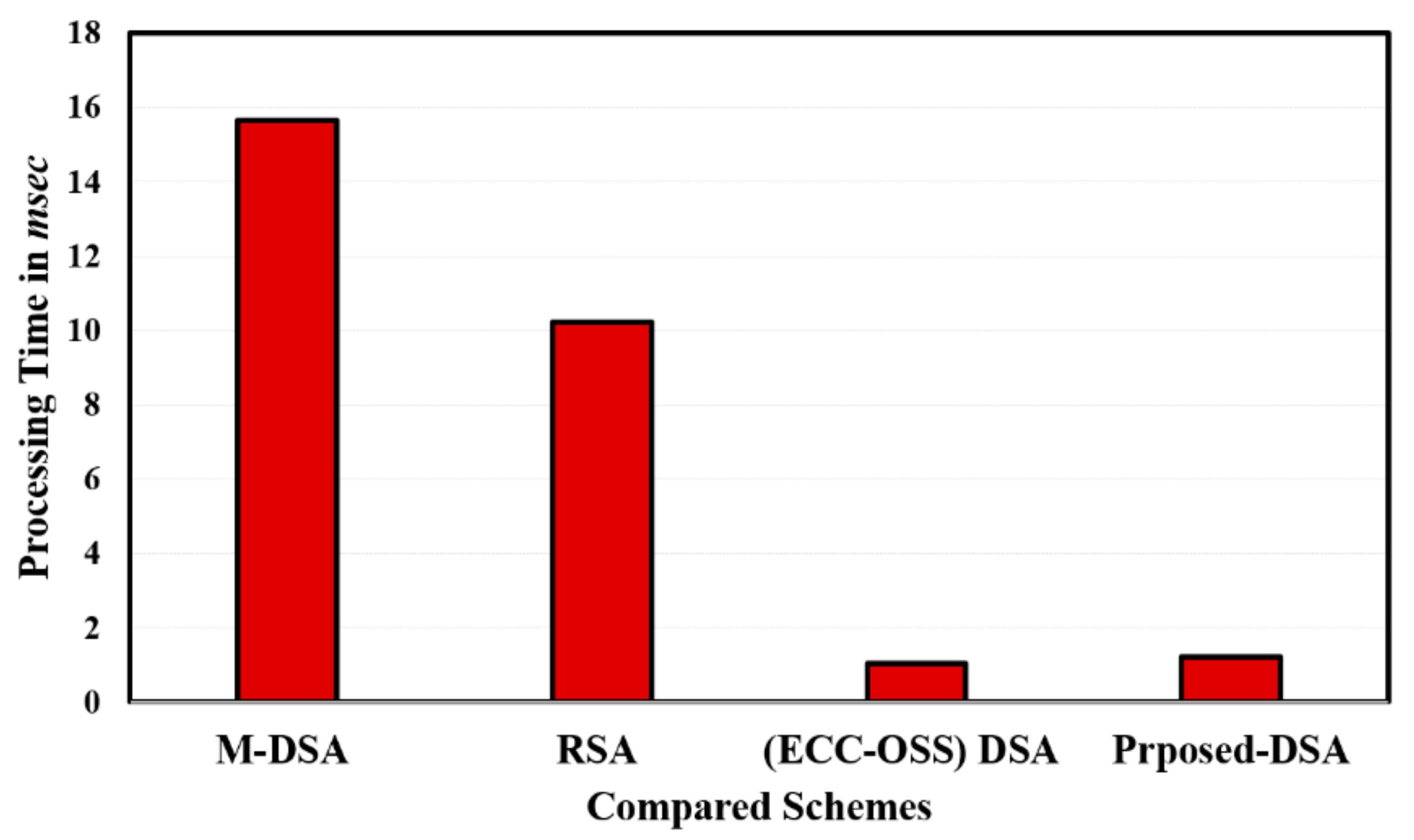
5. Experimental Results and Discussion
| Algorithm 1 Steps for calculating quadratic equation roots |
| 1. Given n = P × Q, where {P, Q} are unknown prime numbers; |
| 2. Choose w and Compute w−1(mod n); |
| 3. Scheme A: requires signatures of random messages (m) to run, and m must be signed using the private key w−1; |
| 4. Recall Scheme (A) using the signatures and the public keys {k, n}; |
| 5. w′ is computed by scheme (A) as follows: |
| 6. With a probability of, the are the two prime numbers {P, Q}; |
| 7. According to the previous steps, if, then choose another (w) and reiterate all steps; |
| 8. After (n) rounds, the possibility of computing the factorization is. |
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| DLP | Discrete Logarithm Problem |
| DSA | Digital Signature Algorithm |
| ECC | Elliptic Curve Cryptography |
| ECDLP | Elliptic Curve Discrete Logarithm Problem |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| GCD | Great Common Divisor |
| IFP | Integer Factorization Problem |
| IOT | Internet of Things |
| IP | Internet Protocol |
| KP | Key Pair |
| MSP | Machine Service Provider |
| OSS | Ong, Schnorr, and Shamir |
| RNG | Random Generator |
| RSA | Rivest, Shamir, and Adleman |
| S-Box | Substitution Box |
| TTV | The Tree of Trust |
References
- El-hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. A survey of internet of things (IoT) Authentication schemes. Sensors 2019, 19, 1141. [Google Scholar] [CrossRef] [PubMed]
- Samaila, M.G.; Neto, M.; Fernandes, D.A.; Freire, M.M.; Inácio, P.R. Challenges of securing Internet of Things devices: A survey. Secur. Priv. 2018, 1, e20. [Google Scholar] [CrossRef]
- Symanovich, S. The future of IoT: 10 predictions about the internet of things. Cyber Secur. Blog Nort. Symantec Accessed 2019, 2–17. Available online: https://us.norton.com/internetsecurity-iot-5-predictions-for-the-future-of-iot.html (accessed on 8 February 2021).
- Naeem, M.; Chaudhry, S.A.; Mahmood, K.; Karuppiah, M.; Kumari, S. A scalable and secure RFID mutual authentication protocol using ECC for Internet of Things. Int. J. Commun. Syst. 2019, 33, e3906. [Google Scholar] [CrossRef]
- Berndt, S.; Li’skiewicz, M. Algorithm Substitution Attacks from a Steganographic Perspective. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017; pp. 1649–1660. [Google Scholar]
- Raikwar, M.; Gligoroski, D.; Kralevska, K. SoK of Used Cryptography in Blockchain. IEEE Access 2019, 7, 148550–148575. [Google Scholar] [CrossRef]
- Al-Mahmud, A.; Morogan, M. Identity-based Authentication and Access Control in Wireless Sensor Networks. Int. J. Comput. Appl. 2012, 41, 18–24. [Google Scholar] [CrossRef]
- Malik, M.; Dutta, M.; Granjal, J. A survey of key bootstrapping protocols based on public key cryptography in the Internet of Things. IEEE Access 2019, 7, 27443–27464. [Google Scholar] [CrossRef]
- Chen, L.Y.; Reiser, H.P. Distributed Applications and Interoperable Systems; Springer: Berlin/Heidelberg, Germany, 2017. [Google Scholar]
- Ghofar, A.; Hardi, M.; Firdaus, M.N.; Shidik, G.F. Digital Signature Based on PlayGamal Algorithm. In Proceedings of the 2017 International Seminar on Application for Technology of Information and Communication (iSemantic), Semarang, Indonesia, 7–8 October 2017; IEEE: New York, NY, USA, 2017; pp. 58–65. [Google Scholar]
- Rabah, K. Security of the Cryptographic Protocols Based on Discrete Logarithm Problem. J. Appl. Sci. 2005, 5, 1692–1712. [Google Scholar] [CrossRef][Green Version]
- Farah, M.A.B.; Farah, A.; Farah, T. An Image Encryption Scheme Based on a New Hybrid Chaotic Map and Optimized Substitution Box. Nonlinear. Dyn. 2020, 99, 3041–3064. [Google Scholar] [CrossRef]
- Guesmi, R.; Farah, M.; Kachouri, A.; Samet, M. Chaos-Based Designing of a Highly Nonlinear S-Box Using Boolean Functions. In Proceedings of the 2015 IEEE 12th International Multi-Conference on Systems, Signals & Devices (SSD15), Mahdia, Tunisia, 16–19 March 2015; pp. 1–5. [Google Scholar] [CrossRef]
- Roy, S.; Khatwani, C. Cryptanalysis and improvement of ECC based authentication and key exchanging protocols. Cryptography 2017, 1, 9. [Google Scholar] [CrossRef]
- Khatoon, S.; Rahman, S.M.M.; Alrubaian, M.; Alamri, A. Privacy-Preserved, Provable Secure, Mutually Authenticated Key Agreement Protocol for Healthcare in a Smart City Environment. IEEE Access 2019, 7, 47962–47971. [Google Scholar] [CrossRef]
- Nikooghadam, M.; Amintoosi, H. Cryptanalysis of Khatoon et al.’s ECC-based Authentication Protocol for Healthcare Systems. arXiv 2019, arXiv:1906.08424. [Google Scholar]
- Rahim, R.; Pranolo, A.; Hadi, R.; Asyidah, R.R.; Nurdiyanto, H.; Napitupulu, D.; Ahmar, A.; Abdillah, L.; Abdullah, D. Digital Signature Security in Data Communication. Adv. Intell. Syst. Res. (AISR) 2017, 144, 172–177. [Google Scholar]
- Pollard, J.; Schnorr, C. An efficient solution of the congruence x2 + ky2 = m(mod n). IEEE Trans. Inf. Theory 1987, 33, 702–709. [Google Scholar] [CrossRef]
- Biswas, S. Enhancing the Privacy of Decentralized Identifiers with Ring Signatures. Master’s Thesis, Aalto University, Espoo, Finland, 2020. [Google Scholar]
- Shingala, K. An Alternative to the Public Key Infrastructure for the Internet of Things. Master’s Thesis, Norges Teknisk-Naturvitenskaplige Universitet, Trondheim, Norway, 2019. [Google Scholar]
- Shuo, C.; Ma, M.; Luo, Z. An authentication scheme with identity-based cryptography for M2M security in cyber-physical systems. Secur. Commun. Netw. 2016, 9, 1146–1157. [Google Scholar]
- Singh, A.K.; Solanki, A.; Nayyar, A.; Qureshi, B. Elliptic Curve Signcryption-Based Mutual Authentication Protocol for Smart Cards. Appl. Sci. 2020, 10, 8291. [Google Scholar] [CrossRef]
- Maletsky, K. RSA vs. ECC Comparison for Embedded Systems. 2015. Available online: http://ww1.microchip.com/ (accessed on 8 February 2021).
- Seok, B.; Park, J.; Park, J. A Lightweight Hash-Based Blockchain Architecture for Industrial IoT. Appl. Sci. 2019, 9, 3740. [Google Scholar] [CrossRef]
- Alzahrani, B.A.; Chaudhry, S.A.; Barnawi, A.; Al-Barakati, A.; Shon, T. An Anonymous Device to Device Authentication Protocol Using ECC and Self Certified Public Keys Usable in Internet of Things Based Autonomous Devices. Electronics 2020, 9, 520. [Google Scholar] [CrossRef]
- Liu, Z.; Liu, D.; Zou, X.; Lin, H.; Cheng, J. Design of an elliptic curve cryptography processor for rfid tag chips. Sensors 2014, 14, 17883–17904. [Google Scholar] [CrossRef]
- Satapathy, U.; Mohanta, B.K.; Jena, D.; Sobhanayak, S. An Ecc Based Lightweight Authentication Protocol for Mobile Phone in Smart Home. In Proceedings of the 2018 IEEE 13th International Conference on Industrial and Information Systems (ICIIS), Rupnagar, India, 1–2 December 2018; IEEE: New York, NY, USA, 2018; pp. 303–308. [Google Scholar]
- Das, A. Computational Number Theory; CRC Press: Boca Raton, FL, USA, 2013. [Google Scholar]
- Azarderakhsh, R.; Reyhani-Masoleh, A. Efficient FPGA implementations of point multiplication on binary Edwards and generalized Hessian curves using Gaussian normal basis. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2011, 20, 1453–1466. [Google Scholar] [CrossRef]
- Wohlwend, J. Elliptic Curve Cryptography: Pre and Post Quantum; Technical Report; MIT, Tech. Rep: Atlanta, GA, USA, 2016. [Google Scholar]
- Coppersmith, D.; Stern, J.; Vaudenay, S. Attacks on the Birational Permutation Signature Schemes. In Annual International Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 1993; pp. 435–443. [Google Scholar]
- Ong, H.; Schnorr, C.P.; Shamir, A. An Efficient Signature Scheme Based on Quadratic Equations. In Proceedings of the Sixteenth Annual ACM Symposium on Theory of Computing, New York, NY, USA, 30 April–2 May 1984; pp. 208–216. [Google Scholar]
- Wang, Y.; Liu, Z.; Ma, J.; He, H. A pseudorandom number generator based on piecewise logistic map. Nonlinear Dyn. 2016, 83, 2373–2391. [Google Scholar] [CrossRef]
- Logachev, O.A.; Salnikov, A.A.; Yashchenko, V.V. Boolean Functions in Coding Theory and Cryptography; American Mathematical Soc.: North Providence, RI, USA, 2012; Volume 241. [Google Scholar]
- Ruming, Y.; Jian, Y.; Jian, W.; Xiuming, S.; Xiqin, W. Designing key-dependent chaotic S-box with larger key space. Chaos Solitons Fractals 2009, 42, 2582–2589. [Google Scholar]
- Guo, C.; Yong, C.; Xiaofeng, L. An extended method for obtaining S-boxes based on three-dimensional chaotic Baker maps. Chaos Solitons Fractals 2007, 31, 571–579. [Google Scholar]
- Ullah, I.; Hayat, U.; Bustamante, M.D. Image Encryption Using Elliptic Curves and Rossby/Drift Wave Triads. Entropy 2020, 22, 454. [Google Scholar] [CrossRef]
- Al-sewadi, H.A.; Rifaat, M.M. Reduced time complexity variant of digital signature algorithm. J. Theor. Appl. Inf. Technol. 2018, 96, 1–94. [Google Scholar]
- Bafandehkar, M.; Yasin, S.M.; Mahmod, R.; Hanapi, Z.M. Comparison of ECC and RSA Algorithm in Resource Constrained Devices. In Proceedings of the 2013 International Conference on IT Convergence and Security (ICITCS), Macao, China, 16–18 December 2013; IEEE: New York, NY, USA, 2013; pp. 1–3. [Google Scholar]
- Conrad, E.; Misenar, S.; Feldman, J. CISSP Study Guide; Newnes: New South Wales, Australia, 2012. [Google Scholar]
- Standaert, F.X.; Piret, G.; Quisquater, J.J. Cryptanalysis of Block Ciphers: A Survey; UCL Crypto Group: Louvain-la-Neuve, Belgium, 2003. [Google Scholar]
- Ren, J.; Chen, S. Cryptanalysis of Reduced-Round SPECK. IEEE Access 2019, 7, 63045–63056. [Google Scholar] [CrossRef]
- Heys, H.M. A tutorial on linear and differential cryptanalysis. Cryptologia 2002, 26, 189–221. [Google Scholar] [CrossRef]
- Van Tilborg, H.C.; Jajodia, S. Encyclopedia of Cryptography and Security; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2014. [Google Scholar]

| 3 | 5 | 6 | 7 | 10 | 12 | 14 | 19 | 20 | 24 | 27 |
| 28 | 33 | 37 | 38 | 39 | 40 | 41 | 43 | 45 | 47 | 48 |
| 51 | 53 | 54 | 55 | 56 | 63 | 65 | 66 | 69 | 71 | 74 |
| 75 | 76 | 77 | 78 | 80 | 82 | 83 | 85 | 86 | 87 | 90 |
| 91 | 93 | 94 | 96 | 97 | 101 | 102 | 103 | 105 | 106 | 107 |
| 108 | 125 | 109 | 110 | 112 | 115 | 119 | 126 | 127 | 130 | 131 |
| 132 | 138 | 142 | 145 | 147 | 148 | 149 | 150 | 151 | 152 | 154 |
| 155 | 156 | 160 | 161 | 163 | 164 | 166 | 167 | 170 | 171 | 172 |
| 174 | 175 | 177 | 179 | 180 | 181 | 182 | 183 | 186 | 188 | 191 |
| 192 | 194 | 201 | 202 | 203 | 204 | 206 | 209 | 210 | 212 | 214 |
| 216 | 217 | 218 | 219 | 220 | 224 | 229 | 230 | 233 | 237 | 238 |
| 243 | 245 | 247 | 250 | 251 | 252 | 254 | ||||
| RSA | (OSS–ECC) DSA | Modified OSS–ECC | |||
|---|---|---|---|---|---|
| KL | Time | KL | Time | KL | Time |
| 1024 | 0.01 | 163 | 0.12452 | 163 | 0.125002 |
| 2240 | 0.15 | 233 | 0.13548 | 233 | 0.173998 |
| 7680 | 1.53 | 409 | 0.30213 | 409 | 0.326002 |
| 15,360 | 9.2 | 571 | 0.41568 | 571 | 0.483925 |
| Scheme | Security | Complexity | Domain | Key Creator | Execution Time | Verify | Sign |
|---|---|---|---|---|---|---|---|
| RSA | High | Integer Factorization Problem (IFP) | PC, Laptops, and Super Computers | Medium | Slow | High | High |
| ECDSA | High | Discrete Logarithm Problem (DLP) | Lightweight Devices | High | High | Slow | High |
| OSS–ECC | High | (IFP–DLP) | Lightweight Devices | Higher | Highest | High | Higher |
| Modified OSS–ECC | High | (IFP–DLP) | Lightweight Devices | Higher | Highest | High | Higher |
| Output Difference | ||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 → 15 | 0 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 0 | 4 |
| 16 → 31 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 4 |
| 32 → 47 | 0 | 0 | 2 | 0 | 0 | 0 | 4 | 0 | 2 | 0 | 4 | 0 | 0 | 0 | 0 | 0 |
| 48 → 63 | 0 | 4 | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 4 | 0 | 0 |
| 64 → 79 | 22 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 8 | 0 | 14 | 0 | 0 | 0 | 0 | 0 |
| 80 → 95 | 0 | 0 | 0 | 0 | 0 | 0 | 8 | 0 | 0 | 8 | 0 | 8 | 0 | 0 | 0 | 0 |
| 96 → 111 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 2 | 0 | 0 | 0 | 0 | 0 |
| 112 → 127 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 8 | 0 | 0 | 0 | 0 | 0 | 0 | 6 | 6 |
| 128 → 143 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 0 | 4 |
| 144 → 159 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 4 |
| 160 → 175 | 0 | 0 | 4 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 0 | 0 |
| 176 → 191 | 2 | 4 | 0 | 4 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 0 |
| 192 → 207 | 6 | 6 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 8 | 4 | 8 | 0 | 0 |
| 208 → 223 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 224 → 239 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 6 | 0 | 8 | 0 | 0 | 0 |
| 240 → 255 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 8 | 0 | 0 | 0 | 0 | 0 | 0 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Takieldeen, A.; Abd Elkhalik, S.H.; Samra, A.S.; Mohamed, M.A.; Khalifa, F. A Robust and Hybrid Cryptosystem for Identity Authentication. Information 2021, 12, 104. https://doi.org/10.3390/info12030104
Takieldeen A, Abd Elkhalik SH, Samra AS, Mohamed MA, Khalifa F. A Robust and Hybrid Cryptosystem for Identity Authentication. Information. 2021; 12(3):104. https://doi.org/10.3390/info12030104
Chicago/Turabian StyleTakieldeen, Ali, Said H. Abd Elkhalik, Ahmed S. Samra, Mohamed A. Mohamed, and Fahmi Khalifa. 2021. "A Robust and Hybrid Cryptosystem for Identity Authentication" Information 12, no. 3: 104. https://doi.org/10.3390/info12030104
APA StyleTakieldeen, A., Abd Elkhalik, S. H., Samra, A. S., Mohamed, M. A., & Khalifa, F. (2021). A Robust and Hybrid Cryptosystem for Identity Authentication. Information, 12(3), 104. https://doi.org/10.3390/info12030104







