Systematic Literature Review of Security Pattern Research
Abstract
1. Introduction
- Using an SLR to identify necessary facets, we created a comprehensive taxonomy. Our taxonomy characterizes security pattern research to help practitioners choose existing security pattern methods as well as tools. Besides, our taxonomy serves as a resource for the software security community to support communication and research in security pattern methods and tools.
- We surveyed and classified existing security pattern research and clarified state-of-the-art and future directions of security pattern research based on our taxonomy. These findings should stimulate and improve security pattern research, resulting in the improvement of the effectiveness of security patterns.
2. Related Work
3. Taxonomy Construction
- To determine the scope, we first defined our purpose and goals. The purpose is to support the classification, comparison, reuse, and extension of security pattern research. Our goals are to improve communications about security software stakeholders such as researchers, developers, and users and improve the research achievements’ availability. Thus, we aimed to develop a taxonomy to classify security patterns and standard terminology.
- Next, we conducted an SLR aiming to aggregate existing evidence to achieve the research goal and support the construction of evidence-based guidelines for practitioners and researchers [250]. The SLR used Scopus (https://www.scopus.com/) which is citation and abstract database provided by Elsevier, to search for papers about security pattern research. The search query was the following.TITLE-ABS-KEY‘‘security patter’’) AND( LIMIT-TO(SUBJAREA,‘‘COMP’’) OR LIMIT-TO(SUBJAREA,‘‘ENG’’) )Scopus was chosen because its effectiveness as a software engineering SLR has been demonstrated [244,251,252,253]. In addition, the results can be easily exported. On 23 October 2018, our query returned 484 papers published between 1992 and 2017. The following inclusion and exclusion criteria were subsequently used to compile research on security patterns:Inclusion criteria:
- Studies published in conference proceedings or journals in the form of papers employing security patterns for systems and software systems engineering.
Exclusion criteria:- Studies that do not employ any security pattern.
- Studies that introduce or propose security patterns without any further engineering activities such as application of patterns.
Each paper was initially read by one author to determine if it was within the scope of this study. If it fitted within the scope, the author analyzed it against known features used in [3] and identified additional characteristics. Then another author confirmed the assessment. If these classifications conflicted, all authors discussed to reach a consensus. This procedure returned 240 papers and their initial classification results (The list of 240 papers and their analysis details are available at http://www.washi.cs.waseda.ac.jp/security/.). - Afterward, the identified characteristics were merged using existing methods such as CWE (Common Weakness Enumeration) [254] and CVSS (Common Vulnerability Scoring System) [255] as well as critical concepts clarified in the Security and Privacy Metamodel [256] to form a feature diagram [257]. A feature diagram is a tree to visualize four types of relationships between a parent feature and its child features (subfeatures): The first is “Mandatory”, which indicates a required subfeature. The second is “Optional”, which denotes a voluntary feature. The third is “Or”, which requires at least one of the subfeatures. The fourth is “Alternative”, which means only one subfeature is selected among all possible subfeatures. Since a feature diagram essentially defines a taxonomy, feature diagrams have been used for defining taxonomies to classify papers and documents in literature reviews [258,259].
- Finally, the taxonomy was validated by classifying existing security pattern research identified in the SLR. Each subfeature was assigned to one of the authors to check initial classification results in terms of the assigned subfeature. If the author identified classification conflicts in terms of the assigned subfeature, all authors discussed to reach a consensus modify the taxonomy and/or classification results.
4. Constructed Taxonomy
5. Survey Results
5.1. Purpose
5.1.1. Topic
5.1.2. Phase of Lifecycle
5.2. Research Implementation
5.2.1. Platform
5.2.2. Tool and Automation
5.2.3. Evaluation Method
5.3. Quality
5.3.1. Vulnerability and Threat
5.3.2. Security Characteristic
5.3.3. Security Measurement
- In [5], security patterns found in 23 papers are grouped into 14 categories. Then the categories are evaluated using nine levels of quality standard classifications.
- In [26], forces and Solution are used to evaluate attribute, risk reduction frequency, risk reduction consequence, annual number of attacks, cost per attack, and cost solution. Furthermore, XSS (Cross Site Scripting) is evaluated as a case study.
- In [29], seven levels of security criteria are used to compare and evaluate nine security patterns. In addition, performance gain and loss is compared. The implementation cost and degree of security are also evaluated in three levels.
- In [37], the following three categories are used for evaluating security pattern description elements (problem and forces, structure description, structure image, behavior description, behavior image, consequences, and example): not provided, minimal, and satisfactory.
- In [39], measures against possible threats are evaluated using a graph.
- In [59], resource access restrictions granted to different roles are evaluated in terms of four operations: C (create), R (retrieve), U (update), and D (delete).
- Ref. [76] supports an aspect-oriented approach and proposes an evaluation using Object Constraint Language (OCL) for Account Lockout with Selective Logging (ALSEL) and IMAP system.
- In [116], nine levels of quality are used to evaluate nine concerns such as threats and attacks to be avoided, an attack pattern to be applied, threats to be passed, and security requirements.
- In [125], security patterns of eight categories such as accountability, confidentiality, and integrity are evaluated.
- In [152], security patterns of a distributed system are categorized and five quality indicators are evaluated.
- In [155], using the 6 approach, 12 security patterns are evaluated by 6 categories of undesirable properties.
- In [200], using its own unique evaluation formula, the applicability of patterns is calculated as rate.
- In [202], three indices (completeness, isolation, and verifiability) are used as the engineering principles of security kernel.
- Ref. [203] is related to security patterns of a grid system. Password and digital signature are expressed as graphic extension of Backus normal form (a.k.a. Backus–Naur form) in the authentication pattern.
- In [204], using an example of an ATM terminal, security objects, and patterns are described and evaluated in eight matrices.
- Ref. [205] categorizes patterns into three layers and evaluates them.
5.4. Security Related Patterns
5.4.1. Security Pattern
5.4.2. Attack Pattern
5.5. Method
5.5.1. Methodology
5.5.2. Pattern Modeling Notation
5.5.3. Relationship between Patterns
6. Validation and Use Case of Taxonomy
- Purpose: Three-quarters of the papers report security pattern applications targeting the earlier phases, including analysis and design.
- Research Implementation: Half of the papers use cloud as their application platform. Half mention tools. Evaluations of security patterns are limited to an example or a case study.
- Quality: Half of the papers mention vulnerabilities or threats. Only one paper refers to publicly available information regarding vulnerabilities and threats (i.e., STRIDE). All studies examine security characteristics based on the CIA. Only one paper adopts security measurements.
- Pattern: All papers focus on security patterns only.
- Method: Half of the papers describe some development methodologies. Three-quarters represent the pattern modeling notations, including UML as the most major one. None of the papers explicitly handle security pattern combinations.
- UC1 is to help practitioners select appropriate security pattern methods and tools. When practitioners want to reuse and eventually extend existing methods and tools, these must be compared prior to selecting the most appropriate one for the scenario. Selection should be based on how the methods and tools meet the intended objectives. The taxonomy helps compare criteria to assess methods and tools according to their characteristics.
- UC2 is to communicate research methods and tools to researchers. By incorporating the characteristics of security pattern research into a single structure, the taxonomy can serve as a framework to guide future communications and research on security pattern methods and the corresponding tools. For example, the taxonomy can serve as the basis to build an open repository of information of existing methods and tools. Moreover, the taxonomy should stimulate and improve security pattern research, resulting in improvement of the effectiveness of security patterns.
7. Limitation
8. Conclusions and Future Work
- Purpose: Most papers report applications of security patterns, development methodologies, and pattern classification. Research targets are skewed towards the earlier phases, including analysis and design.
- Research Implementation: Most papers use general platforms like the web, cloud, and distributed systems. Only around one third mention tools or automation. Evaluations of security pattern usage are an immature research area since it is often limited to a case study or referencing an example even if an evaluation is conducted.
- Quality: Vulnerabilities or threats are mentioned in only less than one-third of the papers. Many studies examine security characteristics, especially those based on the CIA. Only a few papers adopted security measurements to evaluate patterns.
- Pattern: There are attack patterns and security patterns, but most focus on security patterns and not attack patterns. Most papers mention a specific security pattern by name. There are more than 230 unique security patterns mentioned.
- Method: Around two-fifths describe some development methodologies, in which the model-driven approach is the most major one. About two-thirds represent the pattern modeling notations, including UML as the most major one. Security pattern combinations are often not considered.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Schumacher, M.; Fernández-Buglioni, E.B.; Hybertson, D.; Buschmann, F.; Sommerlad, P. Security Patterns—Integrating Security and Systems Engineering; Wiley: Hoboken, NJ, USA, 2005. [Google Scholar]
- Washizaki, H. Security patterns: Research direction, metamodel, application and verification. In Proceedings of the International Workshop on Big Data and Information Security, IWBIS 2017, Jakarta, Indonesia, 23–24 September 2017; pp. 1–4. [Google Scholar]
- Ito, Y.; Washizaki, H.; Yoshizawa, M.; Fukazawa, Y.; Okubo, T.; Kaiya, H.; Hazeyama, A.; Yoshioka, N.; Fernandez, E. Systematic Mapping of Security Patterns Research. In Proceedings of the 22nd Conference on Pattern Languages of Programs Conference (PLoP), Pittsburgh, PA, USA, 24–26 October 2015; pp. 1–7. [Google Scholar]
- Bouaziz, R.; Kallel, S.; Coulette, B. A Collaborative Process for Developing Secure Component Based Applications. In Proceedings of the 2014 IEEE 23rd International WETICE Conference, WETICE 2014, Parma, Italy, 23–25 June 2014; pp. 306–311. [Google Scholar]
- Alvi, A.K.; Zulkernine, M. A Comparative Study of Software Security Pattern Classifications. In Proceedings of the Seventh International Conference on Availability, Reliability and Security, Prague, Czech Republic, 20–24 August 2012; pp. 582–589. [Google Scholar]
- Uzunov, A.V.; Fernández, E.B.; Falkner, K. A Comprehensive Pattern-Driven Security Methodology for Distributed Systems. In Proceedings of the 23rd Australian Software Engineering Conference, ASWEC 2014, Milsons Point, Sydney, Australia, 7–10 April 2014; pp. 142–151. [Google Scholar]
- Uzunov, A.V.; Falkner, K.E.; Fernández, E.B. A comprehensive pattern-oriented approach to engineering security methodologies. Inf. Softw. Technol. 2015, 57, 217–247. [Google Scholar] [CrossRef]
- Bouaziz, R.; Kammoun, S. A Decision Support Map for Security Patterns Application. In Proceedings of the Computational Science and Its Applications—ICCSA 2015—15th International Conference, Banff, AB, Canada, 22–25 June 2015; pp. 750–759. [Google Scholar]
- Balopoulos, T.; Gymnopoulos, L.; Karyda, M.; Kokolakis, S.; Gritzalis, S.; Katsikas, S.K. A Framework for Exploiting Security Expertise in Application Development. In Proceedings of the Third International Conference, Trust and Privacy in Digital Business, TrustBus 2006, Krakow, Poland, 4–8 September 2006; pp. 62–70. [Google Scholar]
- Guan, H.; Wang, X.; Yang, H. A framework for security driven software evolution. In Proceedings of the 20th International Conference on Automation and Computing, ICAC 2014, Cranfield, Bedfordshire, UK, 12–13 September 2014; pp. 194–199. [Google Scholar]
- Singpant, P.; Prompoon, N. A Method for Web Security Context Patterns Development from User Interface Guidelines Based on Structural and Textual Analysis. In Information Science and Applications; Lecture Notes in Electrical Engineering; Kim, K., Ed.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 339, pp. 541–550. [Google Scholar]
- Abramov, J.; Anson, O.; Dahan, M.; Shoval, P.; Sturm, A. A methodology for integrating access control policies within database development. Comput. Secur. 2012, 31, 299–314. [Google Scholar] [CrossRef]
- Ryoo, J.; Laplante, P.A.; Kazman, R. A Methodology for Mining Security Tactics from Security Patterns. In Proceedings of the 43rd Hawaii International International Conference on Systems Science (HICSS-43 2010), Kauai, HI, USA, 5–8 January 2010; pp. 1–5. [Google Scholar]
- Fernandez, E.B.; Larrondo-Petrie, M.M.; Sorgente, T.; Vanhilst, M. A methodology to develop secure systems using patterns. In Integrating Security and Software Engineering: Advances and Future Visions; IGI Global: Hershey, PA, USA, 2006; pp. 107–126. [Google Scholar]
- Hamid, B.; Percebois, C. A Modeling and Formal Approach for the Precise Specification of Security Patterns. In Proceedings of the Engineering Secure Software and Systems—6th International Symposium, ESSoS 2014, Munich, Germany, 26–28 February 2014; Lecture Notes in Computer Science. Jürjens, J., Piessens, F., Bielova, N., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8364, pp. 95–112. [Google Scholar]
- VanHilst, M.; Fernández, E.B.; Braz, F.A. A Multi-Dimensional Classification for Users of Security Patterns. J. Res. Pract. Inf. Technol. 2009, 41, 87–118. [Google Scholar]
- Alvi, A.K.; Zulkernine, M. A Natural Classification Scheme for Software Security Patterns. In Proceedings of the IEEE Ninth International Conference on Dependable, Autonomic and Secure Computing, DASC 2011, Sydney, Australia, 12–14 December 2011; pp. 113–120. [Google Scholar]
- Mourad, A.; Otrok, H.; Baajour, L. A Novel Approach for the Development and Deployment of Security Patterns. In Proceedings of the 2010 IEEE Second International Conference on Social Computing, SocialCom/IEEE International Conference on Privacy, Security, Risk and Trust, PASSAT 2010, Minneapolis, MN, USA, 20–22 August 2010; pp. 914–919. [Google Scholar]
- Abramov, J.; Sturm, A.; Shoval, P. A Pattern Based Approach for Secure Database Design. In Proceedings of the Advanced Information Systems Engineering Workshops-CAiSE 2011 International Workshops, London, UK, 20–24 June 2011; pp. 637–651. [Google Scholar]
- Benameur, A.; Fenet, S.; Saïdane, A.; Sinha, S.K. A Pattern-Based General Security Framework: An eBusiness Case Study. In Proceedings of the 11th IEEE International Conference on High Performance Computing and Communications, HPCC 2009, Seoul, Korea, 25–27 June 2009; pp. 339–346. [Google Scholar]
- Schnjakin, M.; Menzel, M.; Meinel, C. A pattern-driven security advisor for service-oriented architectures. In Proceedings of the 6th ACM Workshop On Secure Web Services, SWS 2009, Chicago, IL, USA, 13 November 2009; pp. 13–20. [Google Scholar]
- Delessy, N.A.; Fernández, E.B. A Pattern-Driven Security Process for SOA Applications. In Proceedings of the The Third International Conference on Availability, Reliability and Security, ARES 2008, Technical University of Catalonia, Barcelona, Spain, 4–7 March 2008; pp. 416–421. [Google Scholar]
- Ratchakom, M.; Prompoon, N. A process model design and tool support for information assets access control using security patterns. In Proceedings of the 2011 Eighth International Joint Conference on Computer Science and Software Engineering (JCSSE), Nakhon Pathom, Thailand, 11–13 May 2011; pp. 307–312. [Google Scholar]
- Halkidis, S.T.; Chatzigeorgiou, A.; Stephanides, G. A qualitative analysis of software security patterns. Comput. Secur. 2006, 25, 379–392. [Google Scholar] [CrossRef]
- Ruiz, J.F.; Rudolph, C.; Maña, A.; Arjona, M. A security engineering process for systems of systems using security patterns. In Proceedings of the IEEE International Systems Conference, SysCon 2014, Ottawa, ON, Canada, 31 March—3 April 2014; pp. 8–11. [Google Scholar]
- Varela-Vaca, A.J.; Warschofsky, R.; Gasca, R.M.; Pozo, S.; Meinel, C. A Security Pattern-Driven Approach toward the Automation of Risk Treatment in Business Processes. In Proceedings of the International Joint Conference CISIS’12-ICEUTE’12-SOCO’12 Special Sessions, Ostrava, Czech Republic, 5–7 September 2012; pp. 13–23. [Google Scholar]
- Fernández, E.B.; Monge, R. A security reference architecture for cloud systems. In Proceedings of the WICSA 2014 Companion Volume, Sydney, Australia, 7–11 April 2014; pp. 3:1–3:5. [Google Scholar]
- Tekbacak, F.; Tuglular, T.; Dikenelli, O. A Semantic Based Certification and Access Control Approach Using Security Patterns on SEAGENT. In Proceedings of the Twentieth International Conference on Software Engineering & Knowledge Engineering (SEKE’2008), San Francisco, CA, USA, 1–3 July 2008; pp. 741–744. [Google Scholar]
- Rosado, D.G.; Fernández-Medina, E.; Piattini, M.; Gutiérrez, C. A Study of Security Architectural Patterns. In Proceedings of the The First International Conference on Availability, Reliability and Security, ARES 2006, The International Dependability Conference—Bridging Theory and Practice, Vienna, Austria, 20–22 April 2006; pp. 358–365. [Google Scholar]
- Uzunov, A.V. A survey of security solutions for distributed publish/subscribe systems. Comput. Secur. 2016, 61, 94–129. [Google Scholar] [CrossRef]
- Ahmed, N.; Matulevicius, R. A taxonomy for assessing security in business process modelling. In Proceedings of the IEEE 7th International Conference on Research Challenges in Information Science, RCIS 2013, Paris, France, 29–31 May 2013; pp. 1–10. [Google Scholar]
- Bergmann, G.; Massacci, F.; Paci, F.; Tun, T.T.; Varró, D.; Yu, Y. A Tool for Managing Evolving Security Requirements. In Proceedings of the IS Olympics: Information Systems in a Diverse World-CAiSE Forum 2011, London, UK, 20–24 June 2011; pp. 110–125. [Google Scholar]
- Fernández, E.B.; Sorgente, T.; Larrondo-Petrie, M.M. A UML-Based Methodology for Secure Systems: The Design Stage. In Proceedings of the 3rd International Workshop on Security in Information Systems, WOSIS 2005, Miami, FL, USA, 24–25 May 2005; Fernández-Medina, E., Castro, J.C.H., Castro, L.J.G., Eds.; INSTICC Press: Rua dos Lusiadas/Lisboa, Portugal, 2005; pp. 207–216. [Google Scholar]
- Fernandez, E.B.; Washizaki, H.; Yoshioka, N. Abstract Security Patterns. In Proceedings of the 15th Conference on Pattern Languages of Programs; Association for Computing Machinery: New York, NY, USA, 2008. [Google Scholar]
- Fernández, E.B.; Yoshioka, N.; Washizaki, H.; Yoder, J.W. Abstract security patterns for requirements specification and analysis of secure systems. In Proceedings of the Anais do WER14—Workshop em Engenharia de Requisitos, Pucón, Chile, 23–25 April 2014. [Google Scholar]
- Busnel, P.; Khoury, P.E.; Giroux, S.; Li, K. Achieving Socio-technical Confidentiality Using Security Pattern in Smart Homes. In Proceedings of the Second International Conference on Future Generation Communication and Networking, FGCN 2008, Sanya, China, 13–15 December 2008; Volume 2, pp. 447–452. [Google Scholar]
- Heyman, T.; Yskout, K.; Scandariato, R.; Joosen, W. An Analysis of the Security Patterns Landscape. In Proceedings of the Third International Workshop on Software Engineering for Secure Systems, SESS 2007, Minneapolis, MN, USA, 20–26 May 2007; p. 3. [Google Scholar]
- Bouaziz, R.; Kallel, S.; Coulette, B. An Approach for Security Patterns Application in Component Based Models. In Proceedings of the Computational Science and Its Applications—ICCSA 2014—14th International Conference, Guimarães, Portugal, 30 June–33 July 2014; pp. 283–296. [Google Scholar]
- Fernández, E.B.; Washizaki, H.; Yoshioka, N.; VanHilst, M. An Approach to Model-based Development of Secure and Reliable Systems. In Proceedings of the Sixth International Conference on Availability, Reliability and Security, ARES 2011, Vienna, Austria, 22–26 August 2011; pp. 260–265. [Google Scholar]
- Serrano, D.; Na, A.M.; Soria-Rodríguez, P.; nuela, A.P.; Sotirious, A.D. An Architecture for secure ambient intelligence environments. In Advances in Soft Computing, Proceedings of the 3rd Symposium of Ubiquitous Computing and Ambient Intelligence 2008; Corbacho, J.M., Tapia y JoséBravo, D.I., Eds.; Springer: Berlin/Heidelberg, Germeny, 2009; pp. 21–29. [Google Scholar]
- Bunke, M.; Sohr, K. An Architecture-Centric Approach to Detecting Security Patterns in Software. In Proceedings of the Engineering Secure Software and Systems—Third International Symposium, ESSoS 2011, Madrid, Spain, 9–10 February 2011; pp. 156–166. [Google Scholar]
- Mouheb, D.; Talhi, C.; Mourad, A.; Lima, V.; Debbabi, M.; Wang, L.; Pourzandi, M. An Aspect-Oriented Approach for Software Security Hardening: From Design to Implementation. In Proceedings of the New Trends in Software Methodologies, Tools and Techniques—Proceedings of the Eighth SoMeT 2009, Prague, Czech Republic, 23–25 September 2009; IOS Press: Amsterdam, The Netherlands, 2009; pp. 203–222. [Google Scholar]
- Mourad, A.; Laverdière, M.; Debbabi, M. An aspect-oriented approach for the systematic security hardening of code. Comput. Secur. 2008, 27, 101–114. [Google Scholar] [CrossRef]
- Alebrahim, A.; Tun, T.T.; Yu, Y.; Heisel, M.; Nuseibeh, B. An Aspect-Oriented Approach to Detecting Security Patterns in Approach to Relating Security Requirements and Access Control. In Proceedings of the CAiSE’12 Forum at the 24th International Conference on Advanced Information Systems Engineering (CAiSE), Gdansk, Poland, 28 June 2012; pp. 15–22. [Google Scholar]
- He, K.; Feng, Z.; Li, X. An Attack Scenario Based Approach for Software Security Testing at Design Stage. In Proceedings of the 2008 International Symposium on Computer Science and Computational Technology, ISCSCT 2008, Shanghai, China, 20–22 December 2008; Volume 2, pp. 782–787. [Google Scholar]
- Bouaziz, R.; Kallel, S.; Coulette, B. An Engineering Process for Security Patterns Application in Component Based Models. In Proceedings of the 2013 Workshops on Enabling Technologies: Infrastructure for Collaborative Enterprises, Hammamet, Tunisia, 17–20 June 2013; Reddy, S., Jmaiel, M., Eds.; IEEE Computer Society: Piscataway, NJ, USA, 2013; pp. 231–236. [Google Scholar]
- Alaküla, M.; Matulevicius, R. An Experience Report of Improving Business Process Compliance Using Security Risk-Oriented Patterns. In Proceedings of the Practice of Enterprise Modeling—8th IFIP WG 8.1. Working Conference, PoEM 2015, Valencia, Spain, 10–12 November 2015; pp. 271–285. [Google Scholar]
- Noël, R.; Pedraza-Garcia, G.; Astudillo, H.; Fernández, E.B. An exploratory comparison of security patterns and tactics to harden systems. In Proceedings of the XVII Iberoamerican Conference on Software Engineering, CIbSE 2014, Pucon, Chile, 23–25 April 2014; Curran Associates: Red Hook, NY, USA, 2014; pp. 378–391. [Google Scholar]
- Khoury, P.E.; Mokhtari, A.; Coquery, E.; Hacid, M. An Ontological Interface for Software Developers to Select Security Patterns. In Proceedings of the 19th International Workshop on Database and Expert Systems Applications (DEXA 2008), Turin, Italy, 1–5 September 2008; pp. 297–301. [Google Scholar]
- Guan, H.; Yang, H.; Wang, J. An ontology-based approach to security pattern selection. Int. J. Autom. Comput. 2016, 13, 168–182. [Google Scholar] [CrossRef]
- Hwang, G.; Chang, T. An operational model and language support for securing XML documents. Comput. Secur. 2004, 23, 498–529. [Google Scholar] [CrossRef]
- Ortiz, R.; Garzás, J.; Fernández-Medina, E. Analysis of Application of Security Patterns to Build Secure Systems. In Proceedings of the Advanced Information Systems Engineering Workshops - CAiSE 2011 International Workshops, London, UK, 20–24 June 2011; pp. 652–659. [Google Scholar]
- Li, T.; Horkoff, J.; Mylopoulos, J. Analyzing and Enforcing Security Mechanisms on Requirements Specifications. In Proceedings of the Requirements Engineering: Foundation for Software Quality—21st International Working Conference, REFSQ 2015, Essen, Germany, 23–26 March 2015; pp. 115–131. [Google Scholar]
- Ortiz, R.; Moral-García, S.; Moral-Rubio, S.; Vela, B.; Garzás, J.; Fernández-Medina, E. Applicability of Security Patterns. In Proceedings of the On the Move to Meaningful Internet Systems: OTM 2010—Confederated International Conferences: CoopIS, IS, DOA and ODBASE, Hersonissos, Crete, Greece, 25–29 October 2010; pp. 672–684. [Google Scholar]
- Changadwech, C.; Prompoon, N. Applying information retrieval technique for security requirements verification based on security patterns. In Proceedings of the Lecture Notes in Engineering and Computer Science, Hong Kong, China, 16–18 March 2016; Volume 1, pp. 467–472. [Google Scholar]
- Bouaziz, R.; Coulette, B. Applying Security Patterns for Component Based Applications Using UML Profile. In Proceedings of the 15th IEEE International Conference on Computational Science and Engineering, CSE 2012, Paphos, Cyprus, 5–7 December 2012; pp. 186–193. [Google Scholar]
- Halkidis, S.T.; Tsantalis, N.; Chatzigeorgiou, A.; Stephanides, G. Architectural Risk Analysis of Software Systems Based on Security Patterns. IEEE Trans. Dependable Secur. Comput. 2008, 5, 129–142. [Google Scholar] [CrossRef]
- Uzunov, A.V.; Fernández, E.B.; Falkner, K.E. ASE: A comprehensive pattern-driven security methodology for distributed systems. Comput. Stand. Interfaces 2015, 41, 112–137. [Google Scholar] [CrossRef]
- Steinegger, R.; Schäfer, J.; Vogler, M.; Abeck, S. Attack surface reduction for web services based on authorization patterns. In Proceedings of the SECURWARE 2014—8th International Conference on Emerging Security Information, Systems and Technologies, Lisbon, Portugal, 24–28 March 2014; pp. 194–201. [Google Scholar]
- Warschofsky, R.; Menzel, M.; Meinel, C. Automated Security Service Orchestration for the Identity Management in Web Service Based Systems. In Proceedings of the IEEE International Conference on Web Services, ICWS 2011, Washington, DC, USA, 4–9 July 2011; pp. 596–603. [Google Scholar]
- Dong, J.; Peng, T.; Zhao, Y. Automated verification of security pattern compositions. Inf. Softw. Technol. 2010, 52, 274–295. [Google Scholar] [CrossRef]
- Gunawan, L.A.; Kraemer, F.A.; Herrmann, P. Behavioral Singletons to Consistently Handle Global States of Security Patterns. In Proceedings of the Distributed Applications and Interoperable Systems—12th IFIP WG 6.1 International Conference, DAIS 2012, Stockholm, Sweden, 13–16 June 2012; pp. 73–86. [Google Scholar]
- Tatsubori, M.; Imamura, T.; Nakamura, Y. Best-Practice Patterns and Tool Support for Configuring Secure Web Services Messaging. In Proceedings of the IEEE International Conference on Web Services (ICWS’04), San Diego, CA, USA, 6–9 June 2004; pp. 244–251. [Google Scholar]
- Fernández, E.B.; Monge, R.; Hashizume, K. Building a security reference architecture for cloud systems. Requir. Eng. 2016, 21, 225–249. [Google Scholar] [CrossRef]
- Rimba, P. Building high assurance secure applications using security patterns for capability-based platforms. In Proceedings of the 35th International Conference on Software Engineering, ICSE ’13, San Francisco, CA, USA, 18–26 May 2013; pp. 1401–1404. [Google Scholar]
- Fernández, E.B.; Mujica, S. Building Secure Systems: From Threats to Security Patterns. In Proceedings of the XXIX International Conference of the Chilean Computer Science Society, SCCC 2010, Antofagasta, Chile, 15–19 November 2010; pp. 66–70. [Google Scholar]
- Bayley, I. Challenges for a Formal Framework for Patterns. In Cyberpatterns, Unifying Design Patterns with Security and Attack Patterns; Blackwell, C., Zhu, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; pp. 47–55. [Google Scholar]
- Slavin, R.; Shen, H.; Niu, J. Characterizations and boundaries of security requirements patterns. In Proceedings of the Second IEEE International Workshop on Requirements Patterns, RePa 2012, Chicago, IL, USA, 24 September 2012; pp. 48–53. [Google Scholar]
- Fernández, E.B.; Washizaki, H.; Yoshioka, N.; Kubo, A.; Fukazawa, Y. Classifying Security Patterns. In Proceedings of the Progress in WWW Research and Development, 10th Asia-Pacific Web Conference, APWeb 2008, Shenyang, China, 26–28 April 2008; pp. 342–347. [Google Scholar]
- Rimba, P.; Zhu, L.; Bass, L.; Kuz, I.; Reeves, S. Composing Patterns to Construct Secure Systems. In Proceedings of the 11th European Dependable Computing Conference, EDCC 2015, Paris, France, 7–11 September 2015; pp. 213–224. [Google Scholar]
- Alzahrani, A.A.H.; Eden, A.H.; Yafi, M.Z. Conformance checking of single access point pattern in JAAS using codecharts. In Proceedings of the 2015 World Congress on Information Technology and Computer Applications, WCITCA 2015, Hammamet, Tunisia, 11–13 June 2015. [Google Scholar]
- Schmidt, H.; Jürjens, J. Connecting Security Requirements Analysis and Secure Design Using Patterns and UMLsec. In Proceedings of the Advanced Information Systems Engineering—23rd International Conference, CAiSE 2011, London, UK, 20–24 June 2011; pp. 367–382. [Google Scholar]
- Ouedraogo, W.F.; Biennier, F.; Silva, C.F.D.; Ghodous, P. Context-aware Security@run.time Deployment. In Proceedings of the 5th International Conference on Cloud Computing and Services Science, CLOSER 2015, Lisbon, Portugal, 20–22 May 2015; SciTePress: Setubal, Portugal, 2015; pp. 276–283. [Google Scholar]
- Bouaziz, R.; Krichen, F.; Coulette, B. C-SCRIP: Collaborative Security Pattern Integration Process. Int. J. Inf. Technol. Web Eng. 2015, 10, 31–46. [Google Scholar] [CrossRef]
- Li, T.; Horkoff, J. Dealing with Security Requirements for Socio-Technical Systems: A Holistic Approach. In Proceedings of the Advanced Information Systems Engineering—26th International Conference, CAiSE 2014, Thessaloniki, Greece, 16–20 June 2014; pp. 285–300. [Google Scholar]
- Tian, K.; Cooper, K.M.L.; Feng, K.; Tang, Y. Defining Re-usable Composite Aspect Patterns: An FDAF Based Approach. In Proceedings of the On the Move to Meaningful Internet Systems: OTM 2008 Workshops, OTM Confederated International Workshops and Posters, ADI, AWeSoMe, COMBEK, EI2N, IWSSA, MONET, OnToContent + QSI, ORM, PerSys, RDDS, SEMELS, and SWWS 2008, Monterrey, Mexico, 9–14 November 2008; pp. 384–395. [Google Scholar]
- Rosado, D.G.; Gutiérrez, C.; Fernández-Medina, E.; Piattini, M. Defining Security Architectural Patterns Based on Viewpoints. In Proceedings of the Computational Science and Its Applications—ICCSA 2007, International Conference, Part III, Kuala Lumpur, Malaysia, 26–29 August 2007; pp. 262–272. [Google Scholar]
- Rosado, D.G.; Gutiérrez, C.; Fernández-Medina, E.; Piattini, M. Defining Viewpoints for Security Architectural Patterns. In Proceedings of the SECRYPT 2006, Proceedings of the International Conference on Security and Cryptography, Setúbal, Portugal, 7–10 August 2006; INSTICC Press: Lisboa, Portugal, 2006; pp. 419–424. [Google Scholar]
- Fernández, E.B.; Larrondo-Petrie, M.M. Designing Secure SCADA Systems Using Security Patterns. In Proceedings of the 43rd Hawaii International International Conference on Systems Science (HICSS-43 2010), Kauai, HI, USA, 5–8 January 2010; pp. 1–8. [Google Scholar]
- Gymnopoulos, L.; Karyda, M.; Balopoulos, T.; Dritsas, S.; Kokolakis, S.; Lambrinoudakis, C.; Gritzalis, S. Developing a security patterns repository for secure applications design. In Proceedings of the 5th European Conference on Information Warfare and Security 2006, ECIW 2006, Helsinki, Finland, 1–2 June 2006; pp. 51–60. [Google Scholar]
- Serrano, D.; Ruíz, J.F.; Muñoz, A.; Maña, A.; Armenteros, A.; Crespo, B.G. Development of applications based on security patterns. In Proceedings of the 2009 2nd International Conference on Dependability, DEPEND 2009, Athens/Glyfada, Greece, 18–23 June 2009; pp. 111–116. [Google Scholar]
- Yskout, K.; Scandariato, R.; Joosen, W. Do Security Patterns Really Help Designers? In Proceedings of the 37th IEEE/ACM International Conference on Software Engineering, ICSE 2015, Florence, Italy, 16–24 May 2015; pp. 292–302. [Google Scholar]
- Yskout, K.; Scandariato, R.; Joosen, W. Does organizing security patterns focus architectural choices? In Proceedings of the 34th International Conference on Software Engineering, ICSE 2012, Zurich, Switzerland, 2–9 June 2012; pp. 617–627. [Google Scholar]
- Gandhi, R.A.; Rahmani, M. Early security patterns: A collection of constraints to describe regulatory security requirements. In Proceedings of the Second IEEE International Workshop on Requirements Patterns, RePa 2012, Chicago, IL, USA, 24 September 2012; pp. 17–22. [Google Scholar]
- Okubo, T.; Kaiya, H.; Yoshioka, N. Effective Security Impact Analysis with Patterns for Software Enhancement. In Proceedings of the Sixth International Conference on Availability, Reliability and Security, ARES 2011, Vienna, Austria, 22–26 August 2011; pp. 527–534. [Google Scholar]
- Mathew, G. Elements of application security in the cloud computing environment. In Proceedings of the 2012 IEEE Conference on Open Systems, ICOS 2012, Kuala Lumpur, Malaysia, 21–24 October 2012. [Google Scholar]
- Braz, F.A.; Fernández, E.B.; VanHilst, M. Eliciting Security Requirements through Misuse Activities. In Proceedings of the 19th International Workshop on Database and Expert Systems Applications (DEXA 2008), Turin, Italy, 1–5 September 2008; pp. 328–333. [Google Scholar]
- Solinas, M.; Fernández, E.B.; Antonelli, L. Embedding Security Patterns into a Domain Model. In Proceedings of the Database and Expert Systems Applications, DEXA, International Workshops, Linz, Austria, 31 August–4 September 2009; pp. 176–180. [Google Scholar]
- Yu, Y.; Kaiya, H.; Washizaki, H.; Xiong, Y.; Hu, Z.; Yoshioka, N. Enforcing a security pattern in stakeholder goal models. In Proceedings of the 4th ACM Workshop on Quality of Protection, QoP 2008, Alexandria, VA, USA, 27 October 2008; pp. 9–14. [Google Scholar]
- Khoury, P.; Busnel, P.; Giroux, S. Enforcing security in smart homes using security patterns. Int. J. Smart Home 2009, 3, 57–70. [Google Scholar]
- Uzunov, A.V.; Fernández, E.B.; Falkner, K. Engineering Security into Distributed Systems: A Survey of Methodologies. J. Univ. Comput. Sci. 2012, 18, 2920–3006. [Google Scholar]
- Katt, B.; Gander, M.; Breu, R.; Felderer, M. Enhancing Model Driven Security through Pattern Refinement Techniques. In Proceedings of the Formal Methods for Components and Objects, 10th International Symposium, FMCO 2011, Turin, Italy, 3–5 October 2011; pp. 169–183. [Google Scholar]
- Supaporn, K.; Prompoon, N.; Rojkangsadan, T. Enterprise Assets Security Requirements Construction from ESRMG Grammar based on Security Patterns. In Proceedings of the 14th Asia-Pacific Software Engineering Conference (APSEC 2007), Nagoya, Japan, 5–7 December 2007; pp. 112–119. [Google Scholar]
- Moral-García, S.; Moral-Rubio, S.; Fernández, E.B.; Fernández-Medina, E. Enterprise security pattern: A model-driven architecture instance. Comput. Stand. Interfaces 2014, 36, 748–758. [Google Scholar] [CrossRef]
- Moral-García, S.; Moral-Rubio, S.; Rosado, D.G.; Fernández, E.B.; Fernández-Medina, E. Enterprise security pattern: A new type of security pattern. Secur. Commun. Netw. 2014, 7, 1670–1690. [Google Scholar] [CrossRef]
- Faily, S.; Parkin, S.; Lyle, J. Evaluating the Implications of Attack and Security Patterns with Premortems. In Cyberpatterns, Unifying Design Patterns with Security and Attack Patterns; Blackwell, C., Zhu, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; pp. 199–209. [Google Scholar]
- Abramov, J.; Sturm, A.; Shoval, P. Evaluation of the Pattern-based method for Secure Development (PbSD): A controlled experiment. Inf. Softw. Technol. 2012, 54, 1029–1043. [Google Scholar] [CrossRef]
- Dalai, A.K.; Jena, S.K. Evaluation of web application security risks and secure design patterns. In Proceedings of the 2011 International Conference on Communication, Computing & Security, ICCCS 2011, Odisha, India, 12–14 February 2011; pp. 565–568. [Google Scholar]
- Hafiz, M.; Johnson, R.E. Evolution of the MTA architecture: The impact of security. Softw. Pract. Exp. 2008, 38, 1569–1599. [Google Scholar] [CrossRef]
- van Veenstra, A.F.; Ramilli, M. Exploring Information Security Issues in Public Sector Inter-organizational Collaboration. In Proceedings of the Electronic Government–10th IFIP WG 8.5 International Conference, EGOV 2011, Delft, The Netherlands, 28 August–2 September 2011; pp. 355–366. [Google Scholar]
- Savic, D.; Simic, D.; Vlajic, S. Extended Software Architecture Based on Security Patterns. Informatica 2010, 21, 229–246. [Google Scholar] [CrossRef]
- Robinson, P. Extensible Security Patterns. In Proceedings of the 18th International Workshop on Database and Expert Systems Applications (DEXA 2007), Regensburg, Germany, 3–7 September 2007; pp. 729–733. [Google Scholar]
- Muñoz, A.; Maña, A. Facilitating the Use of TPM Technologies Using the Serenity Framework. In Proceedings of the Autonomic and Trusted Computing—8th International Conference, ATC 2011, Banff, AB, Canada, 2–4 September 2011; pp. 164–174. [Google Scholar]
- Near, J.P.; Jackson, D. Finding security bugs in web applications using a catalog of access control patterns. In Proceedings of the 38th International Conference on Software Engineering, ICSE 2016, Austin, TX, USA, 14–22 May 2016; pp. 947–958. [Google Scholar]
- Ruamjinda, P.; Prompoon, N. Framwork for information security standards storage and retrieval using security patterns. In Proceedings of the IEEE International Conference on Software Engineering and Service Sciences, ICSESS, Beijing, China, 23–25 May 2013; pp. 296–300. [Google Scholar]
- Horvath, V.; Dörges, T. From security patterns to implementation using petri nets. In Proceedings of the Fourth International Workshop on Software Engineering for Secure Systems, SESS 2008, Leipzig, Germany, 17–18 May 2008; pp. 17–24. [Google Scholar]
- Hafiz, M.; Adamczyk, P.; Johnson, R.E. Growing a pattern language (for security). In Proceedings of the ACM Symposium on New Ideas in Programming and Reflections on Software, Onward! 2012, part of SPLASH ’12, Tucson, AZ, USA, 21–26 October 2012; pp. 139–158. [Google Scholar]
- Dikanski, A.; Steinegger, R.; Abeck, S. Identification and implementation of authentication and authorization patterns in the spring security framework. In Proceedings of the SECURWARE 2012—6th International Conference on Emerging Security Information, Systems and Technologies, Rome, Italy, 19–24 August 2012; pp. 14–20. [Google Scholar]
- Patu, V.; Yamamoto, S. Identifying and Implementing Security Patterns for a Dependable Security Case—From Security Patterns to D-Case. In Proceedings of the 16th IEEE International Conference on Computational Science and Engineering, CSE 2013, Sydney, Australia, 3–5 December 2013; pp. 138–142. [Google Scholar]
- Yoshizawa, M.; Washizaki, H.; Fukazawa, Y.; Okubo, T.; Kaiya, H.; Yoshioka, N. Implementation Support of Security Design Patterns Using Test Templates. Information 2016, 7, 34. [Google Scholar] [CrossRef]
- Edge, C.; Mitropoulos, F. Improving security design patterns with aspect-oriented strategies. In Proceedings of the 50th Annual Southeast Regional Conference, 2012, Tuscaloosa, AL, USA, 29–31 March 2012; pp. 24–29. [Google Scholar]
- Washizaki, H.; Fernández, E.B.; Maruyama, K.; Kubo, A.; Yoshioka, N. Improving the Classification of Security Patterns. In Proceedings of the Database and Expert Systems Applications, DEXA, International Workshops, Linz, Austria, 31 August–4 September 2009; pp. 165–170. [Google Scholar]
- Netter, M.; Pernul, G. Integrating Security Patterns into the Electronic Invoicing Process. In Proceedings of the Database and Expert Systems Applications, DEXA, International Workshops, Linz, Austria, 31 August–4 September 2009; pp. 150–154. [Google Scholar]
- Li, T.; Horkoff, J.; Mylopoulos, J. Integrating Security Patterns with Security Requirements Analysis Using Contextual Goal Models. In Proceedings of the The Practice of Enterprise Modeling—7th IFIP WG 8.1 Working Conference, PoEM 2014, Manchester, UK, 12–13 November 2014; pp. 208–223. [Google Scholar]
- Filho, A.E.S.; Smith, P.; Mauthe, A.; Hutchison, D. Management Patterns for Network Resilience: Design and Verification of Policy Configurations. In Cyberpatterns, Unifying Design Patterns with Security and Attack Patterns; Blackwell, C., Zhu, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; pp. 85–95. [Google Scholar]
- Fernández, E.B.; Yoshioka, N.; Washizaki, H.; Van Hilst, M. Measuring the Level of Security Introduced by Security Patterns. In Proceedings of the ARES 2010, Fifth International Conference on Availability, Reliability and Security, Krakow, Poland, 15–18 February 2010; pp. 565–568. [Google Scholar]
- Dong, J.; Peng, T.; Zhao, Y. Model Checking Security Pattern Compositions. In Proceedings of the Seventh International Conference on Quality Software (QSIC 2007), Portland, OR, USA, 11–12 October 2007; pp. 80–89. [Google Scholar]
- Shiroma, Y.; Washizaki, H.; Fukazawa, Y.; Kubo, A.; Yoshioka, N. Model-Driven Security Patterns Application Based on Dependences among Patterns. In Proceedings of the ARES 2010, Fifth International Conference on Availability, Reliability and Security, Krakow, Poland, 15–18 February 2010; pp. 555–559. [Google Scholar]
- Nguyen, P.H.; Klein, J.; Traon, Y.L. Model-Driven Security with A System of Aspect-Oriented Security Design Patterns. In Proceedings of the 2nd Workshop on View-Based, Aspect-Oriented and Orthographic Software Modelling, VAO@STAF 2014, York, UK, 22 July 2014; pp. 51–54. [Google Scholar]
- Li, T.; Mylopoulos, J. Modeling and Applying Security Patterns Using Contextual Goal Models. In Proceedings of the Seventh International i* Workshop co-located with the 26th International Conference on Advanced Information Systems Engineering (CAiSE 2014), Thessaloniki, Greece, 16–17 June 2014. [Google Scholar]
- Dai, L.; Cooper, K.M.L. Modeling and performance analysis for security aspects. Sci. Comput. Program. 2006, 61, 58–71. [Google Scholar] [CrossRef][Green Version]
- Asnar, Y.; Paja, E.; Mylopoulos, J. Modeling Design Patterns with Description Logics: A Case Study. In Proceedings of the Advanced Information Systems Engineering—23rd International Conference, CAiSE 2011, London, UK, 20–24 June 2011; pp. 169–183. [Google Scholar]
- Fernández, E.B.; Yoshioka, N.; Washizaki, H. Modeling Misuse Patterns. In Proceedings of the The Forth International Conference on Availability, Reliability and Security, ARES 2009, Fukuoka, Japan, 16–19 March 2009; pp. 566–571. [Google Scholar]
- Mouratidis, H.; Weiss, M.; Giorgini, P. Modeling Secure Systems Using an Agent-oriented Approach and Security Patterns. Int. J. Softw. Eng. Knowl. Eng. 2006, 16, 471. [Google Scholar] [CrossRef]
- Weiss, M. Modelling security patterns using NFR analysis. In Integrating Security and Software Engineering: Advances and Future Visions; IGI Global: Hershey, PA, USA, 2006; pp. 127–141. [Google Scholar]
- Halkidis, S.T.; Chatzigeorgiou, A.; Stephanides, G. Moving from Requirements to Design Confronting Security Issues: A Case Study. In Proceedings of the On the Move to Meaningful Internet Systems: OTM 2009, Confederated International Conferences, CoopIS, DOA, IS, and ODBASE 2009, Part II, Vilamoura, Portugal, 1–6 November 2009; pp. 798–814. [Google Scholar]
- Mourad, A.; Otrok, H.; Baajour, L. New Approach Targeting Security Patterns Development and Deployment. Inf. Secur. J. A Glob. Perspect. 2011, 20, 231–244. [Google Scholar] [CrossRef]
- Fernández, E.B.; Wu, J.; Larrondo-Petrie, M.M.; Shao, Y. On building secure SCADA systems using security patterns. In Proceedings of the Fifth Cyber Security and Information Intelligence Research Workshop, CSIIRW’09, Knoxville, TN, USA, 13–15 April 2009; p. 17. [Google Scholar]
- Bunke, M. On the description of software security patterns. In Proceedings of the 19th European Conference on Pattern Languages of Programs, EuroPLoP 2014, Irsee, Germany, 9–13 July 2014; pp. 34:1–34:10. [Google Scholar]
- Hafiz, M.; Adamczyk, P.; Johnson, R.E. Organizing Security Patterns. IEEE Softw. 2007, 24, 52–60. [Google Scholar] [CrossRef]
- Dove, R. Pattern qualifications and examples of next-generation agile system-security strategies. In Proceedings of the International Carnahan Conference on Security Technology, San Jose, CA, USA, 5–8 October 2010; pp. 71–80. [Google Scholar]
- Rrenja, A.; Matulevicius, R. Pattern-Based Security Requirements Derivation from Secure Tropos Models. In Proceedings of the Practice of Enterprise Modeling—8th IFIP WG 8.1. Working Conference, PoEM 2015, Valencia, Spain, 10–12 November 2015; pp. 59–74. [Google Scholar]
- Fernández, E.B.; Pernul, G.; Larrondo-Petrie, M.M. Patterns and Pattern Diagrams for Access Control. In Proceedings of the Trust, Privacy and Security in Digital Business, 5th International Conference, TrustBus 2008, Turin, Italy, 4–5 September 2008; pp. 38–47. [Google Scholar]
- Fernández, E.B.; Yoshioka, N.; Washizaki, H. Patterns for security and privacy in cloud ecosystems. In Proceedings of the 2nd IEEE Workshop on Evolving Security and Privacy Requirements Engineering, ESPRE 2015, Ottawa, ON, Canada, 25 August 2015; pp. 13–18. [Google Scholar]
- Hafiz, M.; Adamczyk, P.; Johnson, R.E. Patterns Transform Architectures. In Proceedings of the 9th Working IEEE/IFIP Conference on Software Architecture, WICSA 2011, Boulder, CO, USA, 20–24 June 2011; pp. 242–251. [Google Scholar]
- Thomsen, D. Practical policy patterns. In Proceedings of the First ACM Conference on Data and Application Security and Privacy, CODASPY 2011, San Antonio, TX, USA, 21–23 February 2011; pp. 225–230. [Google Scholar] [CrossRef]
- Hazeyama, A.; Saito, M. Preliminary Evaluation of a Software Security Learning Environment. Int. J. Softw. Innov. 2014, 2, 26–39. [Google Scholar] [CrossRef]
- Fernández, E.B. Preventing and unifying threats in cyberphysical systems. In Proceedings of the 17th IEEE International Symposium on High Assurance Systems Engineering, HASE 2016, Orlando, FL, USA, 7–9 January 2016; pp. 292–293. [Google Scholar]
- Romanosky, S.; Acquisti, A.; Hong, J.; Cranor, L.F.; Friedman, B. Privacy patterns for online interactions. In Proceedings of the PLoP 2006—PLoP Pattern Languages of Programs 2006 Conference Proceedings, Portland, OR, USA, 21–23 October 2006. [Google Scholar]
- Alebrahim, A.; Heisel, M. Problem-oriented security patterns for requirements engineering. In Proceedings of the 19th European Conference on Pattern Languages of Programs, EuroPLoP 2014, Irsee, Germany, 9–13 July 2014; pp. 9:1–9:17. [Google Scholar]
- Halkidis, S.T.; Chatzigeorgiou, A.; Stephanides, G. Quantitative Evaluation of Systems with Security Patterns Using a Fuzzy Approach. In Proceedings of the On the Move to Meaningful Internet Systems 2006: OTM 2006 Workshops, OTM Confederated International Workshops and Posters, AWeSOMe, CAMS, COMINF, IS, KSinBIT, MIOS-CIAO, MONET, OnToContent, ORM, PerSys, OTM Academy Doctoral Consortium, RDDS, SWWS, and SeBGIS 2006 Part I, Montpellier, France, 29 October–3 November 2006; pp. 554–564. [Google Scholar]
- Hafner, M.; Breu, R. Realizing Model Driven Security for Inter-organizational Workflows with WS-CDL and UML 2.0. In Proceedings of the 8th International Conference, MoDELS 2005, Model Driven Engineering Languages and Systems, Montego Bay, Jamaica, 2–7 October 2005; pp. 39–53. [Google Scholar]
- Netter, M.; Fernández, E.B.; Pernul, G. Refining the Pattern-Based Reference Model for Electronic Invoices by Incorporating Threats. In Proceedings of the ARES 2010, Fifth International Conference on Availability, Reliability and Security, Krakow, Poland, 15–18 February 2010; pp. 560–564. [Google Scholar]
- Heyman, T.; Scandariato, R.; Joosen, W. Reusable Formal Models for Secure Software Architectures. In Proceedings of the 2012 Joint Working IEEE/IFIP Conference on Software Architecture and European Conference on Software Architecture, WICSA/ECSA 2012, Helsinki, Finland, 20–24 August 2012; pp. 41–50. [Google Scholar]
- Fernández, E.B.; Astudillo, H.; Pedraza-Garcia, G. Revisiting Architectural Tactics for Security. In Proceedings of the Software Architecture - 9th European Conference, ECSA 2015, Dubrovnik/Cavtat, Croatia, 7–11 September 2015; pp. 55–69. [Google Scholar]
- Bouaziz, R.; Kammoun, S. SCRIStUDIO: A security pattern integration tool. In Proceedings of the 2016 International Conference on Information Technology for Organizations Development, IT4OD 2016, Fez, Morocco, 30 March–1 April 2016. [Google Scholar]
- Bergmann, G.; Massacci, F.; Paci, F.; Tun, T.T.; Varró, D.; Yu, Y. SeCMER: A Tool to Gain Control of Security Requirements Evolution. In Proceedings of the Towards a Service-Based Internet—4th European Conference, ServiceWave 2011, Poznan, Poland, 26–28 October 2011; pp. 321–322. [Google Scholar]
- Hafner, M.; Breu, R.; Agreiter, B.; Nowak, A. Sectet: An extensible framework for the realization of secure inter-organizational workflows. Internet Res. 2006, 16, 491–506. [Google Scholar] [CrossRef]
- Bouaziz, R.; Coulette, B. Secure Component Based Applications through Security Patterns. In Proceedings of the 2012 IEEE International Conference on Green Computing and Communications, Conference on Internet of Things, and Conference on Cyber, Physical and Social Computing, GreenCom/iThings/CPSCom 2012, Besancon, France, 20–23 November 2012; pp. 749–754. [Google Scholar]
- Ruiz, J.F.; Arjona, M.; Mana, A.; Carstens, N. Secure Engineering and Modelling of a Metering Devices System. In Proceedings of the 2013 International Conference on Availability, Reliability and Security, ARES 2013, Regensburg, Germany, 2–6 September 2013; pp. 418–427. [Google Scholar]
- Fernández, E.B.; Yuan, X. Securing analysis patterns. In Proceedings of the 45th Annual Southeast Regional Conference, 2007, Winston-Salem, NC, USA, 23–24 March 2007; pp. 288–293. [Google Scholar]
- Uzunov, A.V.; Fernández, E.B.; Falkner, K. Securing distributed systems using patterns: A survey. Comput. Secur. 2012, 31, 681–703. [Google Scholar] [CrossRef]
- Sohn, J.; Ryoo, J. Securing Web Applications with Better “Patches”: An Architectural Approach for Systematic Input Validation with Security Patterns. In Proceedings of the 10th International Conference on Availability, Reliability and Security, ARES 2015, Toulouse, France, 24–27 August 2015; pp. 486–492. [Google Scholar]
- Armenteros, Á.; Muñoz, A.; Maña, A.; Serrano, D. Security and Dependability in Ambient Intelligence Scenarios—The Communication Prototype. In Proceedings of the ICEIS 2009—Proceedings of the 11th International Conference on Enterprise Information Systems, Volume ISAS, Milan, Italy, 6–10 May 2009; pp. 49–56. [Google Scholar]
- Laverdière, M.; Mourad, A.; Hanna, A.; Debbabi, M. Security Design Patterns: Survey and Evaluation. In Proceedings of the Canadian Conference on Electrical and Computer Engineering, CCECE 2006, Ottawa Congress Centre, Ottawa, ON, Canada, 7–10 May 2006; pp. 1605–1608. [Google Scholar]
- Memon, M.; Menghwar, G.D.; Depar, M.H.; Jalbani, A.A.; Mashwani, W.M. Security modeling for service-oriented systems using security pattern refinement approach. Softw. Syst. Model. 2014, 13, 549–572. [Google Scholar] [CrossRef]
- Duncan, I.; de Muijnck-Hughes, J. Security Pattern Evaluation. In Proceedings of the 8th IEEE International Symposium on Service Oriented System Engineering, SOSE 2014, Oxford, UK, 7–11 April 2014; pp. 428–429. [Google Scholar]
- Sarmah, A.; Hazarika, S.M.; Sinha, S.K. Security Pattern Lattice: A Formal Model to Organize Security Patterns. In Proceedings of the 19th International Workshop on Database and Expert Systems Applications (DEXA 2008), Turin, Italy, 1–5 September 2008; pp. 292–296. [Google Scholar]
- Moral-García, S.; Moral-Rubio, S.; Fernández-Medina, E. Security Pattern Mining: Systematic Review and Proposal. In Proceedings of the WOSIS 2011—Proceedings of the 8th International Workshop on Security in Information Systems, In conjunction with ICEIS 2011, Beijing, China, 8–9 June 2011; SciTePress: Setubal, Portugal, 2011; pp. 13–24. [Google Scholar]
- Fernández, E.B. Security Patterns and A Methodology to Apply them. In Security and Dependability for Ambient Intelligence; Advances in Information Security; Kokolakis, S., Gómez, A.M., Spanoudakis, G., Eds.; Springer: Berlin/Heidelberg, Germany, 2009; Volume 45, pp. 37–46. [Google Scholar]
- Rosado, D.G.; Gutiérrez, C.; Fernández-Medina, E.; Piattini, M. Security patterns and requirements for internet-based applications. Internet Res. 2006, 16, 519–536. [Google Scholar] [CrossRef]
- Fernández, E.B. Security Patterns and Secure Systems Design. In Proceedings of the Dependable Computing, Third Latin-American Symposium, LADC 2007, Morella, Mexico, 26–28 September 2007; pp. 233–234. [Google Scholar]
- Cuevas, Á.; Khoury, P.E.; Gomez, L.; Laube, A. Security Patterns for Capturing Encryption-Based Access Control to Sensor Data. In Proceedings of the Second International Conference on Emerging Security Information, Systems and Technologies, SECURWARE 2008, Cap Esterel, France, 25–31 August 2008; pp. 62–67. [Google Scholar]
- Mouratidis, H.; Weiss, M.; Giorgini, P. Security Patterns Meet Agent Oriented Software Engineering: A Complementary Solution for Developing Secure Information Systems. In Proceedings of the Conceptual Modeling—ER 2005, 24th International Conference on Conceptual Modeling, Klagenfurt, Austria, 24–28 October 2005; pp. 225–240. [Google Scholar]
- Hamid, B.; Gürgens, S.; Fuchs, A. Security patterns modeling and formalization for pattern-based development of secure software systems. Innov. Syst. Softw. Eng. 2016, 12, 109–140. [Google Scholar] [CrossRef][Green Version]
- Yoshioka, N.; Honiden, S.; Finkelstein, A. Security Patterns: A Method for Constructing Secure and Efficient Inter-Company Coordination Systems. In Proceedings of the 8th International Enterprise Distributed Object Computing Conference (EDOC 2004), Monterey, CA, USA, 20–24 September 2004; pp. 84–97. [Google Scholar]
- Bandara, A.; Shinpei, H.; Jurjens, J.; Kaiya, H.; Kubo, A.; Laney, R.; Mouratidis, H.; Nhlabatsi, A.; Nuseibeh, B.; Tahara, Y.; et al. In Proceedings of the Security patterns: Comparing modeling approaches. In Software Engineering for Secure Systems: Industrial and Research Perspectives; Mouratidis, H., Ed.; IGI Global: Hershey, PA, USA, 2010; pp. 75–111. [Google Scholar]
- Menzel, M.; Thomas, I.; Meinel, C. Security Requirements Specification in Service-Oriented Business Process Management. In Proceedings of the The Forth International Conference on Availability, Reliability and Security, ARES 2009, Fukuoka, Japan, 16–19 March 2009; pp. 41–48. [Google Scholar]
- Uzunov, A.V.; Fernández, E.B.; Falkner, K. Security solution frames and security patterns for authorization in distributed, collaborative systems. Comput. Secur. 2015, 55, 193–234. [Google Scholar] [CrossRef]
- Hasheminejad, S.M.H.; Jalili, S. Selecting proper security patterns using text classification. In Proceedings of the 2009 International Conference on Computational Intelligence and Software Engineering, CiSE 2009, Wuhan, China, 11–13 December 2009. [Google Scholar]
- Serrano, D.; Maña, A.; Llarena, R.; Crespo, B.G.; Li, K. In Proceedings of the SERENITY Aware System Development Process. In Security and Dependability for Ambient Intelligence; Advances in Information Security; Kokolakis, S., Gómez, A.M., Spanoudakis, G., Eds.; Springer: Berlin/Heidelberg, Germany, 2009; Volume 45, pp. 165–179. [Google Scholar]
- Sánchez-Cid, F.; Maña, A. SERENITY Pattern-Based Software Development Life-Cycle. In Proceedings of the 19th International Workshop on Database and Expert Systems Applications (DEXA 2008), Turin, Italy, 1–5 September 2008; pp. 305–309. [Google Scholar]
- Sánchez-Cid, F.; Muñoz, A.; Serrano, D.; Gago, M.C. Software engineering techniques applied to AmI: Security patterns. In Proceedings of the Developing Ambient Intelligence—Proceedings of the First International Conference on Ambient Intelligence Developments, AmID 2006, Sophia Antipolis, France, 20–22 September 2006; pp. 108–123. [Google Scholar]
- Tryfonas, T.; Kearney, B. Standardising business application security assessments with pattern-driven audit automations. Comput. Stand. Interfaces 2008, 30, 262–270. [Google Scholar] [CrossRef]
- Alzahrani, A.A.H.; Eden, A.H.; Yafi, M.Z. Structural Analysis of the Check Point Pattern. In Proceedings of the 8th IEEE International Symposium on Service Oriented System Engineering, SOSE 2014, Oxford, UK, 7–11 April 2014; pp. 404–408. [Google Scholar]
- Babar, M.A.; Wang, X.; Gorton, I. Supporting Security Sensitive Architecture Design. In Proceedings of the Quality of Software Architectures and Software Quality, First International Conference on the Quality of Software Architectures, QoSA 2005 and Second International Workshop on Software Quality, SOQUA 2005, Erfurt, Germany, 20–22 September 2005; Lecture Notes in Computer Science. pp. 140–154. [Google Scholar]
- Hazeyama, A. Survey on Body of Knowledge Regarding Software Security. In Proceedings of the 13th ACIS International Conference on Software Engineering, Artificial Intelligence, Networking and Parallel/Distributed Computing, SNPD 2012, Kyoto, Japan, 8–10 August 2012; pp. 536–541. [Google Scholar]
- Porekar, J.; Saljic, S.; Klobucar, T.; Jerman-Blazic, A. Technical Patterns for Long Term Trusted Archiving. In Proceedings of the Third International Conference on the Digital Society (ICDS 2009), Cancun, Mexico, 1–7 February 2009; pp. 241–246. [Google Scholar]
- Kobashi, T.; Yoshizawa, M.; Washizaki, H.; Fukazawa, Y.; Yoshioka, N.; Okubo, T.; Kaiya, H. TESEM: A Tool for Verifying Security Design Pattern Applications by Model Testing. In Proceedings of the 8th IEEE International Conference on Software Testing, Verification and Validation, ICST 2015, Graz, Austria, 13–17 April 2015; pp. 1–8. [Google Scholar]
- Morrison, P.; Fernandez, E.B. The credentials pattern. In Proceedings of the PLoP 2006—PLoP Pattern Languages of Programs 2006 Conference Proceedings, Irsee, Germany, 5–9 July 2006. [Google Scholar]
- Ciria, J.C.; Domínguez, E.; Escario, I.; Francés, A.R.; Lapeña, M.J.; Zapata, M.A. The history-based authentication pattern. In Proceedings of the 19th European Conference on Pattern Languages of Programs, EuroPLoP 2014, Irsee, Germany, 9–13 July 2014; pp. 30:1–30:9. [Google Scholar]
- Alkussayer, A.; Allen, W.H. The ISDF framework: Integrating security patterns and best practices. In Communications in Computer and Information Science; Springer: Berlin/Heidelberg, Germany, 2009; Volume 36, pp. 17–28. [Google Scholar]
- Hafiz, M.; Adamczyk, P. The nature of order: From security patterns to a pattern language. In Proceedings of the Conference on Systems, Programming, and Applications: Software for Humanity, SPLASH ’12, Tucson, AZ, USA, 21–25 October 2012; pp. 75–76. [Google Scholar]
- Gutiérrez, C.; Rosado, D.G.; Fernández-Medina, E. The practical application of a process for eliciting and designing security in web service systems. Inf. Softw. Technol. 2009, 51, 1712–1738. [Google Scholar] [CrossRef]
- Shahzad, A.; Musa, S.; Aborujilah, A.; Irfan, M. The Security Survey and Anaylsis on supervisory control and Data Acquisition Communication. J. Comput. Sci. 2014, 10, 2006–2019. [Google Scholar] [CrossRef]
- Heyman, T.; Yskout, K.; Scandariato, R.; Schmidt, H.; Yu, Y. The Security Twin Peaks. In Proceedings of the Engineering Secure Software and Systems—Third International Symposium, ESSoS 2011, Madrid, Spain, 9–10 February 2011; pp. 167–180. [Google Scholar]
- de Muijnck-Hughes, J.; Duncan, I. Thinking Towards a Pattern Language for Predicate Based Encryption Crypto-Systems. In Proceedings of the Sixth International Conference on Software Security and Reliability, SERE 2012, Gaithersburg, MD, USA, 20–22 June 2012; pp. 27–32. [Google Scholar]
- Okubo, T.; Wataguchi, Y.; Kanaya, N. Threat and countermeasure patterns for cloud computing. In Proceedings of the 4th IEEE International Workshop on Requirements Patterns, RePa 2014, Karlskrona, Sweden, 26 August 2014; pp. 43–46. [Google Scholar]
- Anand, P.; Ryoo, J.; Kim, H.; Kim, E. Threat Assessment in the Cloud Environment: A Quantitative Approach for Security Pattern Selection. In Proceedings of the 10th International Conference on Ubiquitous Information Management and Communication, IMCOM 2016, Danang, Vietnam, 4–6 January 2016; pp. 5:1–5:8. [Google Scholar]
- Bouaziz, R.; Hamid, B.; Desnos, N. Towards a Better Integration of Patterns in Secure Component-Based Systems Design. In Proceedings of the Computational Science and Its Applications-ICCSA 2011—International Conference Part V, Santander, Spain, 20–23 June 2011; pp. 607–621. [Google Scholar]
- Graziano, A.; Dearden, A.; Seaton, J.W.; Williams, L.A. Towards a classification framework for security patterns. In Proceedings of the 6th International Network Conference, INC 2006, Plymouth, UK, 19–21 June 2006; pp. 237–244. [Google Scholar]
- Blackwell, C. Towards a Conceptual Framework for Security Patterns. In Cyberpatterns, Unifying Design Patterns with Security and Attack Patterns; Blackwell, C., Zhu, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; pp. 17–34. [Google Scholar]
- Fuchs, A.; Gürgens, S.; Rudolph, C. Towards a Generic Process for Security Pattern Integration. In Proceedings of the Database and Expert Systems Applications, DEXA, International Workshops, Linz, Austria, 31 August–4 September 2009; pp. 171–175. [Google Scholar] [CrossRef]
- Hafner, M.; Alam, M.; Breu, R. Towards a MOF/QVT-Based Domain Architecture for Model Driven Security. In Proceedings of the Model Driven Engineering Languages and Systems, 9th International Conference, MoDELS 2006, Genova, Italy, 1–6 October 2006; pp. 275–290. [Google Scholar]
- Ortiz, R.; Moral-Rubio, S.; Garzás, J.; Fernández-Medina, E. Towards a Pattern-based Security Methodology to Build Secure Information Systems. In Proceedings of the WOSIS 2011—Proceedings of the 8th International Workshop on Security in Information Systems, In conjunction with ICEIS 2011, Beijing, China, 8–9 June 2011; SciTePress: Setubal, Portugal, 2011; pp. 59–69. [Google Scholar]
- Fernández, E.B.; Yimam, D. Towards Compliant Reference Architectures by Finding Analogies and Overlaps in Compliance Regulations. In Proceedings of the SECRYPT 2015—Proceedings of the 12th International Conference on Security and Cryptography, Colmar, Alsace, France, 20–22 July 2015; SciTePress: Setubal, Portugal, 2015; pp. 435–440. [Google Scholar]
- Kozlovs, D.; Cjaputa, K.; Kirikova, M. Towards Continuous Information Security Audit. In Proceedings of the Joint Proceedings of REFSQ-2016 Workshops, Doctoral Symposium, Research Method Track, and Poster Track co-located with the 22nd International Conference on Requirements Engineering: Foundation for Software Quality (REFSQ 2016), Gothenburg, Sweden, 14 March 2016. [Google Scholar]
- Alebrahim, A.; Heisel, M. Towards Developing Secure Software Using Problem-Oriented Security Patterns. In Proceedings of the Availability, Reliability, and Security in Information Systems—IFIP WG 8.4, 8.9, TC 5 International Cross-Domain Conference, CD-ARES 2014 and 4th International Workshop on Security and Cognitive Informatics for Homeland Defense, SeCIHD 2014, Fribourg, Switzerland, 8–12 September 2014; pp. 45–62. [Google Scholar]
- Serrano, D.; Maña, A.; Sotirious, A. Towards Precise Security Patterns. In Proceedings of the 19th International Workshop on Database and Expert Systems Applications (DEXA 2008), Turin, Italy, 1–5 September 2008; pp. 287–291. [Google Scholar]
- Ferreira, A.; Rusu, C.; Roncagliolo, S. Usability and Security Patterns. In Proceedings of the Second International Conference on Advances in Computer-Human Interaction, ACHI 2009, Cancun, Mexico, 1–7 February 2009; pp. 301–305. [Google Scholar]
- Fernández, E.B.; Delessy, N.A. Using Patterns to Understand and Compare Web Services Security Products and Standards. In Proceedings of the Advanced International Conference on Telecommunications and International Conference on Internet and Web Applications and Services (AICT/ICIW 2006), Guadeloupe, French Caribbean, 19–25 February 2006; p. 157. [Google Scholar]
- Heckman, M.R.; Schell, R.R. Using Proven Reference Monitor Patterns for Security Evaluation. Information 2016, 7, 23. [Google Scholar] [CrossRef]
- Aziz, B.; Blackwell, C. Using Security Patterns for Modelling Security Capabilities in Grid Systems. In Proceedings of the 8th IEEE International Symposium on Service Oriented System Engineering, SOSE 2014, Oxford, UK, 7–11 April 2014; pp. 422–427. [Google Scholar]
- Heyman, T.; Scandariato, R.; Huygens, C.; Joosen, W. Using Security Patterns to Combine Security Metrics. In Proceedings of the The Third International Conference on Availability, Reliability and Security, ARES 2008, Technical University of Catalonia, Barcelona, Spain, 4–7 March 2008; pp. 1156–1163. [Google Scholar]
- Fernandez, E.B.; Yoshioka, N.; Washizaki, H.; Jurjens, J.; Van Hilst, M.; Pernu, G. Using security patterns to develop secure systems. In Software Engineering for Secure Systems: Industrial and Research Perspectives; Mouratidis, H., Ed.; IGI Global: Hershey, PA, USA, 2010; pp. 16–31. [Google Scholar]
- Wagner, R.; Fontoura, L.M.; Fontoura, A.B. Using Security Patterns to Tailor Software Process. In Proceedings of the 23rd International Conference on Software Engineering & Knowledge Engineering (SEKE’2011), Eden Roc Renaissance, Miami Beach, FL, USA, 7–9 July 2011; pp. 672–677. [Google Scholar]
- Fernandez, E.B.; Petrie, M.M.L. Using UML and security patterns to teach secure systems design. In Proceedings of the ASEE Annual Conference and Exposition, Portland, OR, USA, 12–15 June 2005; pp. 15511–15520. [Google Scholar]
- Kobashi, T.; Yoshioka, N.; Okubo, T.; Kaiya, H.; Washizaki, H.; Fukazawa, Y. Validating Security Design Patterns Application Using Model Testing. In Proceedings of the 2013 International Conference on Availability, Reliability and Security, ARES 2013, Regensburg, Germany, 2–6 September 2013; pp. 62–71. [Google Scholar]
- Yoshizawa, M.; Kobashi, T.; Washizaki, H.; Fukazawa, Y.; Okubo, T.; Kaiya, H.; Yoshioka, N. Verifying Implementation of Security Design Patterns Using a Test Template. In Proceedings of the Ninth International Conference on Availability, Reliability and Security, ARES 2014, Fribourg, Switzerland, 8–12 September 2014; pp. 178–183. [Google Scholar]
- Anand, P.; Ryoo, J.; Kazman, R. Vulnerability-Based Security Pattern Categorization in Search of Missing Patterns. In Proceedings of the Ninth International Conference on Availability, Reliability and Security, ARES 2014, Fribourg, Switzerland, 8–12 September 2014; pp. 476–483. [Google Scholar]
- Okubo, T.; Tanaka, H. Web security patterns for analysis and design. In Proceedings of the PLoP08—15th Conference on Pattern Languages of Programs, Nashville, TN, USA, 18–20 October 2008. [Google Scholar]
- King, A.C.; Subramanian, K.; Kanhaa, V. Wireless Information security system via role based access control pattern use case design. In Proceedings of the 2008 International Conference on Computing, Communication and Networking, ICCCN 2008, Tamil Nadu, India, 18–20 December 2008. [Google Scholar]
- Barhoom, T.S.; Zhang, S.S. XML context’s security patterns language: Description and syntax. Inf. Technol. J. 2007, 6, 996–1004. [Google Scholar] [CrossRef][Green Version]
- Regainia, L.; Salva, S.; Ecuhcurs, C. A classification methodology for security patterns to help fix software weaknesses. In Proceedings of the 13th IEEE/ACS International Conference of Computer Systems and Applications, AICCSA 2016, Agadir, Morocco, 29 November–2 December 2016; pp. 1–8. [Google Scholar]
- Trubiani, C.; Ghabi, A.; Egyed, A. Exploiting traceability uncertainty between software architectural models and extra-functional results. J. Syst. Softw. 2017, 125, 15–34. [Google Scholar] [CrossRef]
- Motii, A.; Hamid, B.; Lanusse, A.; Bruel, J. Guiding the Selection of Security Patterns for Real-Time Systems. In Proceedings of the 21st International Conference on Engineering of Complex Computer Systems, ICECCS 2016, Dubai, United Arab Emirates, 6–8 November 2016; pp. 155–164. [Google Scholar]
- Anand, P.; Ryoo, J.; Kim, H. Addressing Security Challenges in Cloud Computing—A Pattern-Based Approach. In Proceedings of the 1st International Conference on Software Security and Assurance, ICSSA 2015, Suwon, Korea, 27 July 2015; pp. 13–18. [Google Scholar]
- Regainia, L.; Salva, S. A Methodology of Security Pattern Classification and of Attack-Defense Tree Generation. In Proceedings of the 3rd International Conference on Information Systems Security and Privacy, ICISSP 2017, Porto, Portugal, 19–21 February 2017; Mori, P., Furnell, S., Camp, O., Eds.; SciTePress: Setubal, Portugal, 2017; pp. 136–146. [Google Scholar]
- Amorim, T.; Martin, H.; Ma, Z.; Schmittner, C.; Schneider, D.; Macher, G.; Winkler, B.; Krammer, M.; Kreiner, C. Systematic Pattern Approach for Safety and Security Co-engineering in the Automotive Domain. In Proceedings of the Computer Safety, Reliability, and Security—36th International Conference, SAFECOMP 2017, Trento, Italy, 13–15 September 2017; pp. 329–342. [Google Scholar]
- Nafees, T.; Coull, N.; Ferguson, R.I.; Sampson, A.T. Idea-Caution Before Exploitation: The Use of Cybersecurity Domain Knowledge to Educate Software Engineers Against Software Vulnerabilities. In Proceedings of the Engineering Secure Software and Systems—9th International Symposium, ESSoS 2017, Bonn, Germany, 3–5 July 2017; pp. 133–142. [Google Scholar]
- Shin, M.E.; Gomaa, H.; Pathirage, D. Model-based Design of Reusable Secure Connectors. In Proceedings of the MODELS 2017 Satellite Event: Workshops (ModComp, ME, EXE, COMMitMDE, MRT, MULTI, GEMOC, MoDeVVa, MDETools, FlexMDE, MDEbug), Posters, Doctoral Symposium, Educator Symposium, ACM Student Research Competition, and Tools and Demonstrations co-located with ACM/IEEE 20th International Conference on Model Driven Engineering Languages and Systems (MODELS 2017), Austin, TX, USA, 17 September 2017. [Google Scholar]
- Salva, S.; Regainia, L. Using Data Integration for Security Testing. In Proceedings of the Testing Software and Systems—29th IFIP WG 6.1 International Conference, ICTSS 2017, St. Petersburg, Russia, 9–11 October 2017; Lecture Notes in Computer Science. Yevtushenko, N., Cavalli, A.R., Yenigün, H., Eds.; Springer: Berlin/Heidelberg, Germany, 2017; Volume 10533, pp. 178–194. [Google Scholar]
- Argyropoulos, N.; Mouratidis, H.; Fish, A. Supporting Secure Business Process Design via Security Process Patterns. In Proceedings of the Enterprise, Business-Process and Information Systems Modeling—18th International Conference, BPMDS 2017, Essen, Germany, 12–13 June 2017; Volume 287, pp. 19–33. [Google Scholar]
- Ruiz, J.F.; Arjona, M.; Maña, A.; Rudolph, C. Security knowledge representation artifacts for creating secure IT systems. Comput. Secur. 2017, 64, 69–91. [Google Scholar] [CrossRef]
- Sheta, M.A.; El Salam El Hadad, K.A.; AboelseoudM, H.; Zaki, M. Anti-spyware security design patterns. In Proceedings of the 2016 6th International Conference on Instrumentation and Measurement, Computer, Communication and Control, IMCCC 2016, Harbin, China, 21–23 July 2016; pp. 465–470. [Google Scholar]
- Mazo, R.; Feltus, C. Framework for Engineering Complex Security Requirements Patterns. In Proceedings of the 6th International Conference on IT Convergence and Security, ICITCS 2016, Prague, Czech Republic, 26 September 2016; pp. 1–5. [Google Scholar]
- Fernandez, E.B. Threat Modeling in Cyber-Physical Systems. In Proceedings of the 2016 IEEE 14th International Conference on Dependable, Autonomic and Secure Computing, DASC 2016, Auckland, New Zealand, 8–12 August 2016; pp. 448–453. [Google Scholar]
- ur Rehman, O.; Zivic, N. Secure Design Patterns for Security in Smart Metering Systems. In Proceedings of the 2015 IEEE European Modelling Symposium, EMS 2015, Madrid, Spain, 6–8 October 2015; pp. 278–283. [Google Scholar]
- Washizaki, H.; Fukumoto, S.; Yamamoto, M.; Yoshizawa, M.; Fukazawa, Y.; Kato, T.; Ogata, S.; Kaiya, H.; Fernández, E.B.; Kanuka, H.; et al. A Metamodel for Security and Privacy Knowledge in Cloud Services. In Proceedings of the IEEE World Congress on Services, SERVICES 2016, San Francisco, CA, USA, 27 June–2 July 2016; pp. 142–143. [Google Scholar]
- Fernández, E.B. Building Secure Cloud Architectures Using Patterns. In Proceedings of the 2016 IEEE International Conference on Cloud Engineering Workshop, IC2E Workshops, Berlin, Germany, 4–8 April 2016; p. 194. [Google Scholar]
- Ponde, P.; Shirwaikar, S.; Kreiner, C. An analytical study of security patterns. In Proceedings of the 21st European Conference on Pattern Languages of Programs, EuroPLoP 2016, Kaufbeuren, Germany, 6–10 July 2016; p. 33. [Google Scholar]
- Fernández, E.B.; Yoshioka, N.; Washizaki, H.; Syed, M.H. Modeling and Security in Cloud Ecosystems. Future Internet 2016, 8, 13. [Google Scholar] [CrossRef]
- He, X.; Fu, Y. Modeling and Analyzing Security Patterns Using High Level Petri Nets. In Proceedings of the 28th International Conference on Software Engineering and Knowledge Engineering, SEKE 2016, Redwood City, San Francisco Bay, CA, USA, 1–3 July 2016; Gou, J., Ed.; Knowledge Systems Institute Graduate School: Skokie, IL, USA, 2016; pp. 623–627. [Google Scholar]
- Motii, A.; Hamid, B.; Lanusse, A.; Bruel, J. Towards the integration of security patterns in UML component-based applications. In Proceedings of the Second International Workshop on Patterns in Model Engineering and the Fifth International Workshop on the Verification of Model Transformation, PAME/VOLT 2016, co-located with ACM/IEEE 19th International Conference on Model Driven Engineering Languages and Systems (MoDELS 2016), Saint-Malo, France, 2–3 October 2016; pp. 2–6. [Google Scholar]
- Motii, A.; Lanusse, A.; Hamid, B.; Bruel, J. Model-Based Real-Time Evaluation of Security Patterns: A SCADA System Case Study. In Proceedings of the Computer Safety, Reliability, and Security—SAFECOMP 2016 Workshops, ASSURE, DECSoS, SASSUR, and TIPS, Trondheim, Norway, 20 September 2016; Volume 9923, pp. 375–389. [Google Scholar]
- Horcas, J.; Pinto, M.; Fuentes, L. Automatic Enforcement of Security Properties. In Proceedings of the Trust, Privacy and Security in Digital Business—13th International Conference, TrustBus 2016, Porto, Portugal, 7–8 September 2016; pp. 19–31. [Google Scholar]
- Lee, K.H.; Park, Y.B. Adaption of integrated secure guide for secure software development lifecycle. Int. J. Secur. Its Appl. 2016, 10, 145–154. [Google Scholar] [CrossRef]
- Bunke, M. Software-security patterns: Degree of maturity. In Proceedings of the 20th European Conference on Pattern Languages of Programs, EuroPLoP 2015, Kaufbeuren, Germany, 8–12 July 2015; pp. 42:1–42:17. [Google Scholar]
- Motii, A.; Hamid, B.; Lanusse, A.; Bruel, J. Guiding the selection of security patterns based on security requirements and pattern classification. In Proceedings of the 20th European Conference on Pattern Languages of Programs, EuroPLoP 2015, Kaufbeuren, Germany, 8–12 July 2015; pp. 10:1–10:17. [Google Scholar]
- Atymtayeva, L.; Abdel-Aty, M. Improvement of security patterns strategy for information security audit applications. In Proceedings of the BMSD 2015—Proceedings of the 5th International Symposium on Business Modeling and Software Design, Milan, Italy, 6–8 July 2015; pp. 199–204. [Google Scholar]
- Rimba, P.; Zhu, L.; Xu, X.; Sun, D. Building Secure Applications Using Pattern-Based Design Fragments. In Proceedings of the 34th IEEE Symposium on Reliable Distributed Systems Workshop, SRDS 2015 Workshop, Montreal, QC, Canada, 28 September–1 October 2015; pp. 19–24. [Google Scholar]
- Yoshioka, N.; Washizaki, H.; Maruyama, K. A survey on security patterns. Prog. Inform. 2008, 5, 35–47. [Google Scholar] [CrossRef]
- Kearney, B.; Tryfonas, T. Security Patterns for Automated Continuous Auditing. Inf. Secur. J. A Glob. Perspect. 2008, 17, 13–25. [Google Scholar] [CrossRef]
- Washizaki, H.; Ogata, S.; Hazeyama, A.; Okubo, T.; Fernandez, E.B.; Yoshioka, N. Landscape of Architecture and Design Patterns for IoT Systems. IEEE Internet Things J. 2020, 7, 10091–10101. [Google Scholar] [CrossRef]
- Rajmohan, T.; Nguyen, P.H.; Ferry, N. Research Landscape of Patterns and Architectures for IoT Security: A Systematic Review. In Proceedings of the 46th Euromicro Conference on Software Engineering and Advanced Applications, SEAA 2020, Portoroz, Slovenia, 26–28 August 2020; pp. 463–470. [Google Scholar]
- Babar, M.; Zhang, H. Systematic literature reviews in software engineering: Preliminary results from interviews with researchers. In Proceedings of the Third International Symposium on Empirical Software Engineering and Measurement (ESEM), Lake Buena Vista, FL, USA, 15–16 October 2009; pp. 346–355. [Google Scholar]
- Washizaki, H.; Xia, T.; Kamata, N.; Fukazawa, Y.; Ogata, S.; Kaiya, H.; Tanaka, T.; Kanuka, H.; Yamaoto, D.; Yoshino, M.; et al. Taxonomy and literature survey of security pattern research. In Proceedings of the 2018 IEEE Conference on Application, Information and Network Security, AINS 2018, Langkawi, Malaysia, 21–22 November 2018; pp. 87–92. [Google Scholar]
- Unterkalmsteiner, M.; Feldt, R.; Gorschek, T. A Taxonomy for Requirements Engineering and Software Test Alignment. ACM Trans. Softw. Eng. Methodol. 2014, 23, 16:1–16:38. [Google Scholar] [CrossRef]
- Glass, R.L. Sorting Out Software Complexity. Commun. ACM 2002, 45, 19–21. [Google Scholar] [CrossRef]
- Kitchenham, B.; Brereton, O.P.; Budgen, D.; Turner, M.; Bailey, J.; Linkman, S. Systematic Literature Reviews in Software Engineering - A Systematic Literature Review. Inf. Softw. Technol. 2009, 51, 7–15. [Google Scholar] [CrossRef]
- dos Santos Marques, A.B.; Rodrigues, R.; Conte, T. Systematic Literature Reviews in Distributed Software Development: A Tertiary Study. In Proceedings of the 2012 IEEE Seventh International Conference on Global Software Engineering, Porto Alegre, Rio Grande do Sul, Brazil, 27–30 August 2012; pp. 134–143. [Google Scholar]
- Dadwal, A.; Washizaki, H.; Fukazawa, Y.; Iida, T.; Mizoguchi, M.; Yoshimura, K. Prioritization in Automotive Software Testing: Systematic Literature Review. In Proceedings of the 6th International Workshop on Quantitative Approaches to Software Quality co-located with 25th Asia-Pacific Software Engineering Conference (APSEC 2018), Nara, Japan, 4 December 2018; pp. 52–58. [Google Scholar]
- Washizaki, H.; Uchida, H.; Khomh, F.; Guéhéneuc, Y. Studying Software Engineering Patterns for Designing Machine Learning Systems. In Proceedings of the 10th International Workshop on Empirical Software Engineering in Practice, IWESEP 2019, Tokyo, Japan, 13–14 December 2019; pp. 49–54. [Google Scholar]
- The MITRE Corporation. Common Weakness Enumeration Version 3.1. 2018. Available online: https://cwe.mitre.org/ (accessed on 15 January 2021).
- FIRST.Org. Common Vulnerability Scoring System v3.0: Specification Document. 2015. Available online: https://www.first.org/cvss/ (accessed on 15 January 2021).
- Xia, T.; Washizaki, H.; Kato, T.; Kaiya, H.; Ogata, S.; Fernández, E.B.; Kanuka, H.; Yoshino, M.; Yamamoto, D.; Okubo, T.; et al. Cloud Security and Privacy Metamodel-Metamodel for Security and Privacy Knowledge in Cloud Services. In Proceedings of the 6th International Conference on Model-Driven Engineering and Software Development, MODELSWARD 2018, Funchal, Madeira, Portugal, 22–24 January 2018; SciTePress: Setubal, Portugal, 2018; pp. 379–386. [Google Scholar]
- Kang, K.C.; Cohen, S.G.; Hess, J.A.; Novak, W.E.; Peterson, A.S. Feature-Oriented Domain Analysis (FODA) Feasibility Study; Technical Report CMU/SEI-90-TR-21; Universitas Carnegie Mellon: Pittsburgh, PA, USA, 1990; pp. 1–148. [Google Scholar]
- Czarnecki, K.; Helsen, S. Classification of Model Transformation Approaches. In Proceedings of the OOPSLA Workshop on Generative Techniques in the Context of Model-Driven Architecture, Anaheim, CA, USA, 27 October 2003; pp. 1–17. [Google Scholar]
- Washizaki, H.; Guéhéneuc, Y.; Khomh, F. ProMeTA: A taxonomy for program metamodels in program reverse engineering. Empir. Softw. Eng. 2018, 23, 2323–2358. [Google Scholar] [CrossRef]
- Shostack, A. (Ed.) Threat Modeling: Designing for Security, 1st ed.; Wiley: Hoboken, NJ, USA, 2014. [Google Scholar]
- The MITRE Corporation. Common Vulnerability and Exposures. 2018. Available online: https://cve.mitre.org/ (accessed on 15 January 2021).
- The MITRE Corporation. Common Attack Pattern Enumeration and Classification. 2018. Available online: https://capec.mitre.org/ (accessed on 15 January 2021).
- Smite, D.; Wohlin, C.; Galvina, Z.; Prikladnicki, R. An Empirically Based Terminology and Taxonomy for Global Software Engineering. Empir. Softw. Eng. 2014, 19, 105–153. [Google Scholar] [CrossRef]
- Amato, F.; Mazzocca, N.; Moscato, F. Model driven design and evaluation of security level in orchestrated cloud services. J. Netw. Comput. Appl. 2018, 106, 78–89. [Google Scholar] [CrossRef]
- Alwakeel, A.M.; Alnaim, A.K.; Fernandez, E.B. A Survey of Network Function Virtualization Security. In Proceedings of the IEEE Southeastcon, St. Petersburg, FL, USA, 19–22 April 2018. [Google Scholar]
- Ali, I.; Asif, M. Applying security patterns for authorization of users in IoT based applications. In Proceedings of the 2018 International Conference on Engineering and Emerging Technologies, ICEET 2018, Lahore, Pakistan, 22–23 February 2018. [Google Scholar]
- Li, T.; Horkoff, J.; Mylopoulos, J. Holistic security requirements analysis for socio-technical systems. Softw. Syst. Model. 2018, 17, 1253–1285. [Google Scholar] [CrossRef]
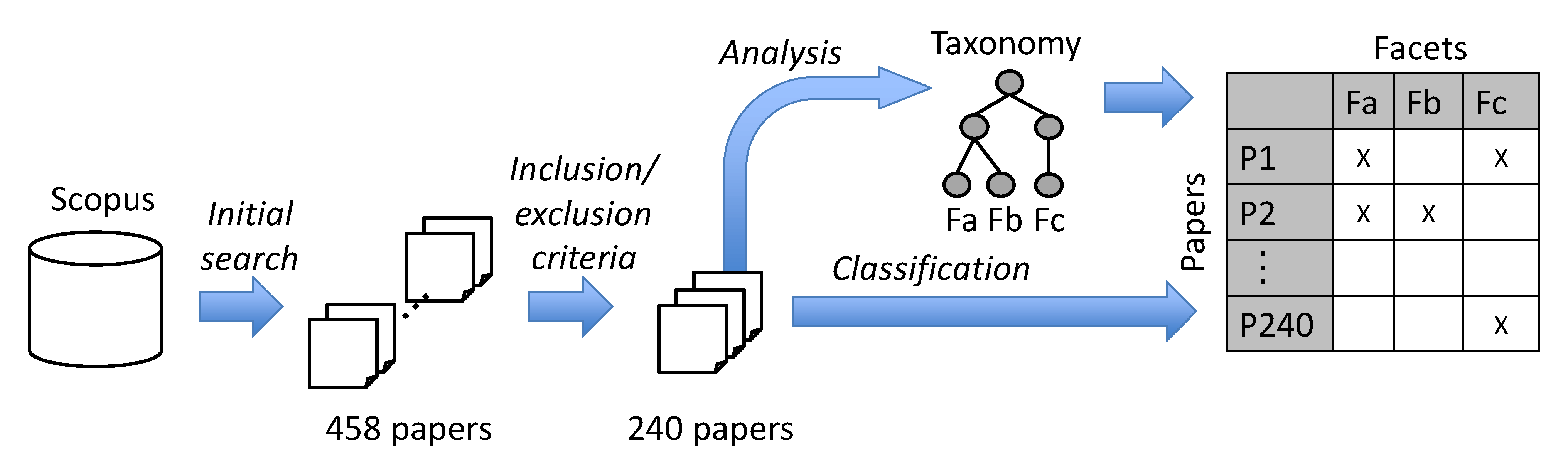
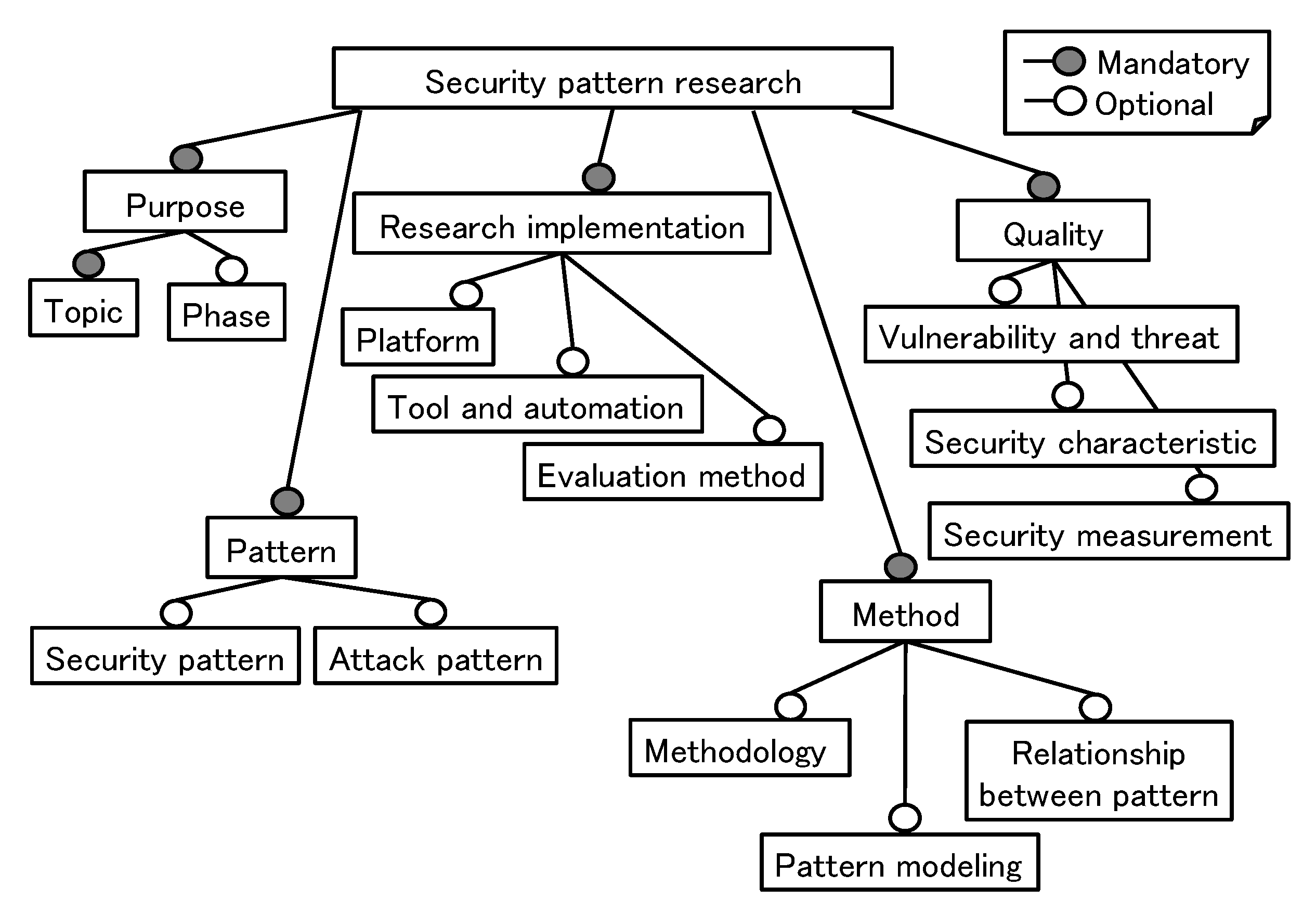
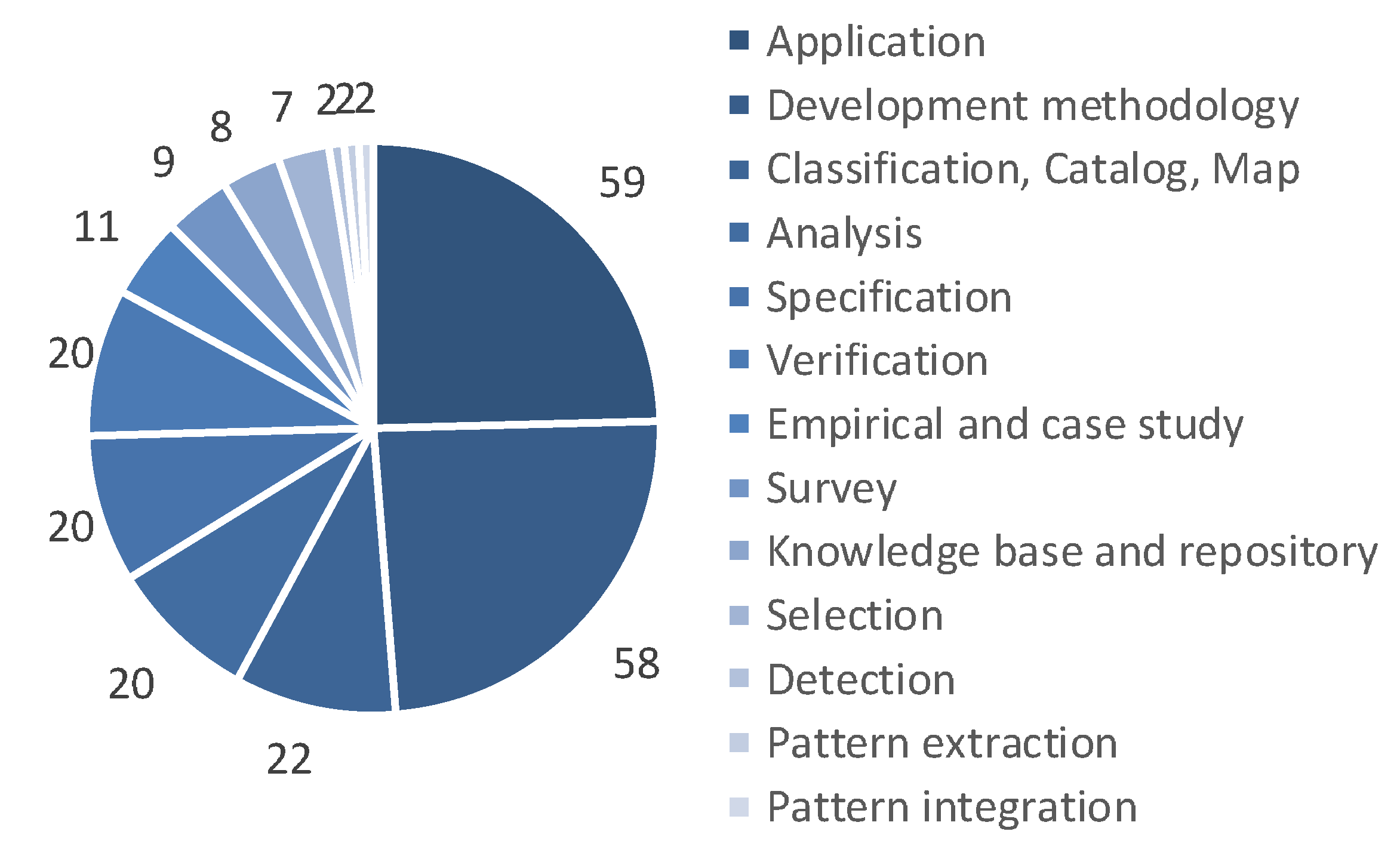
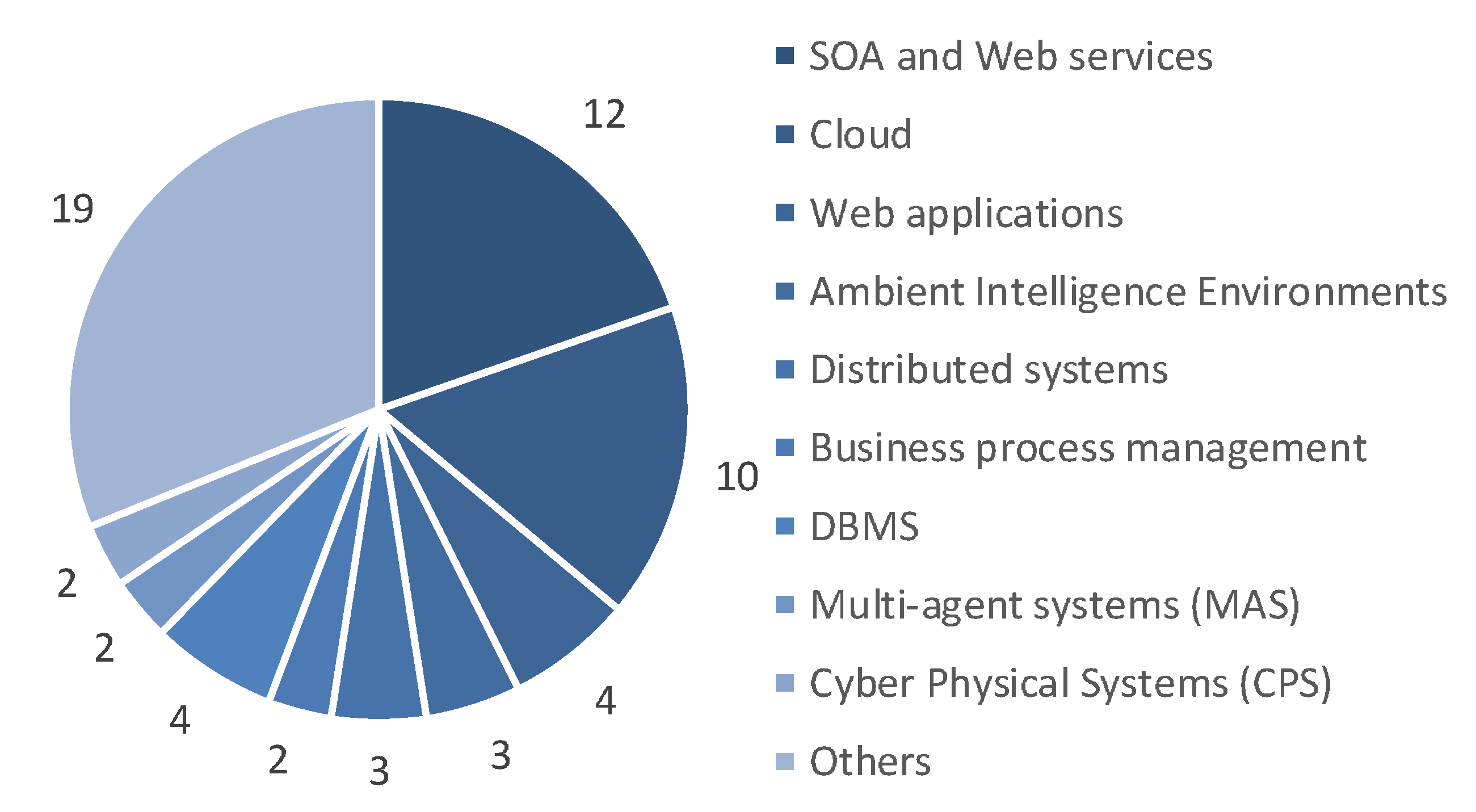
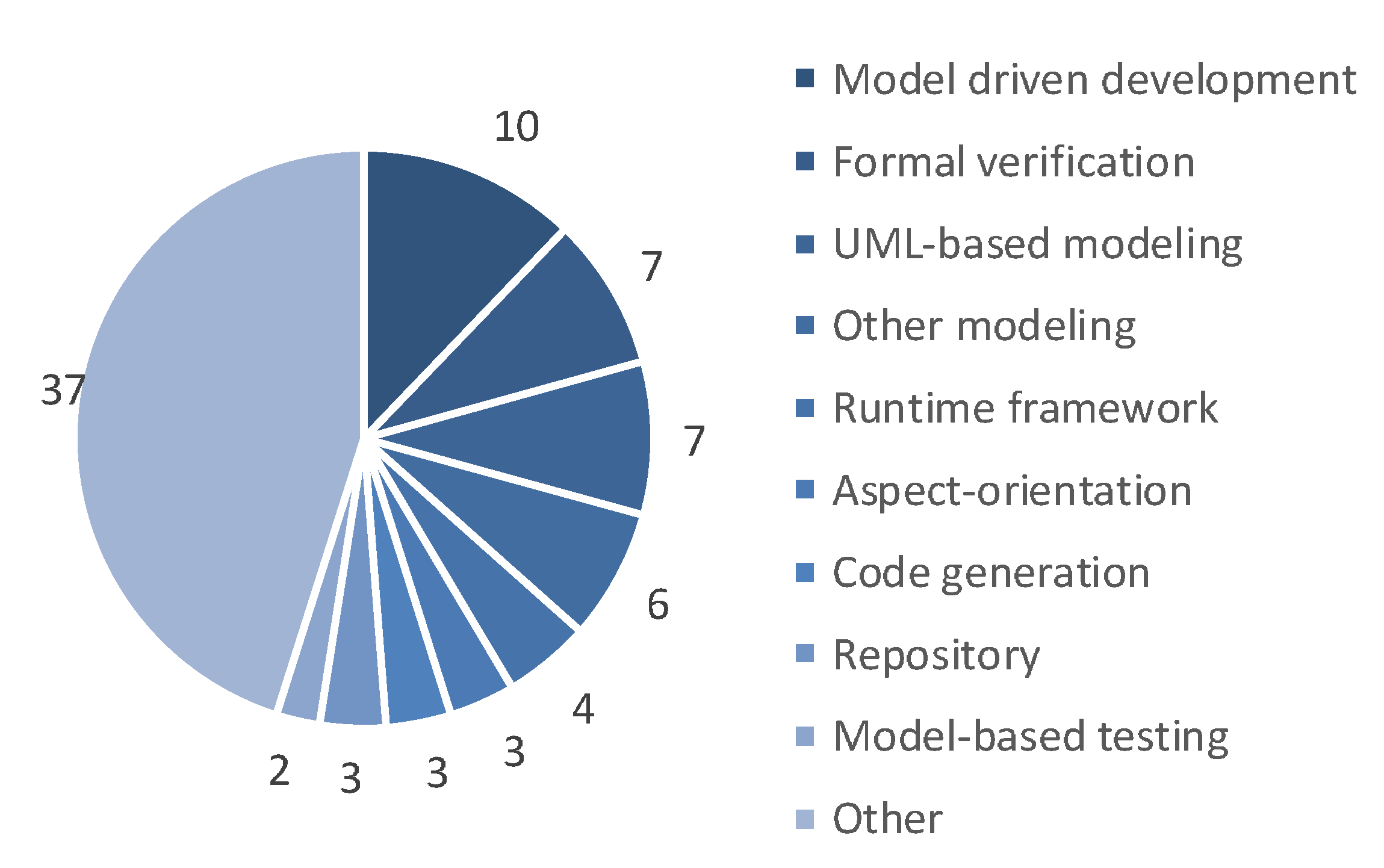
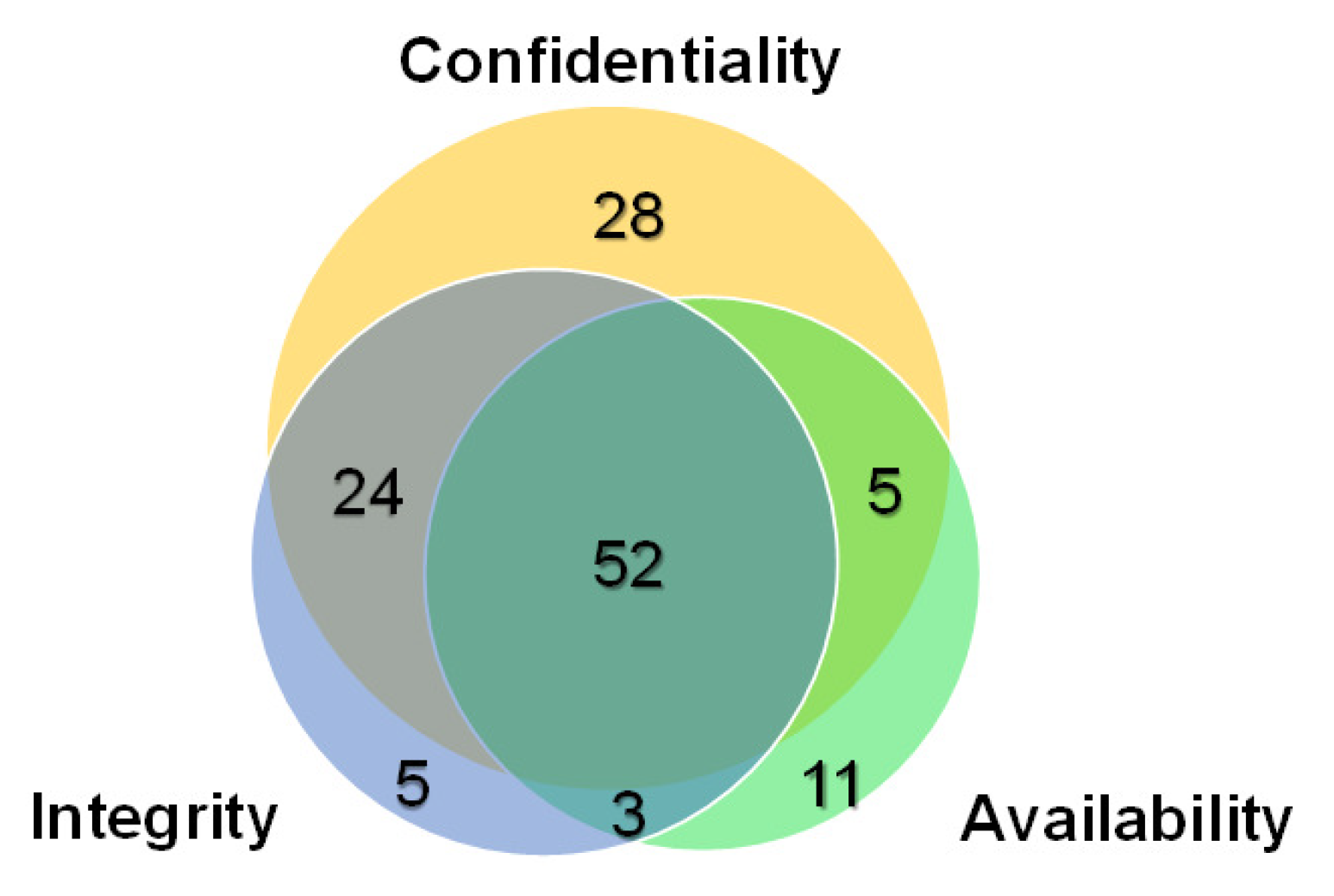
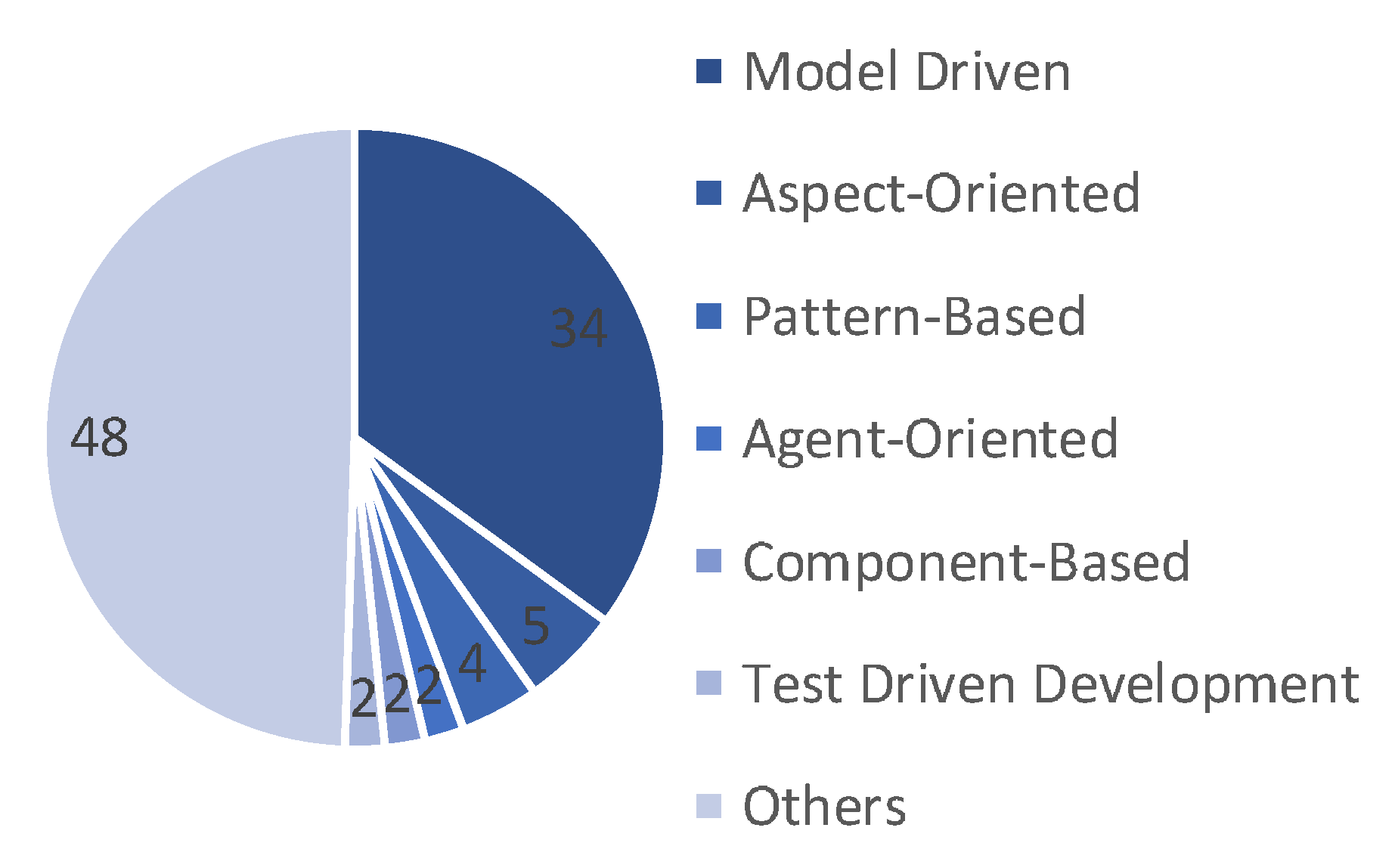
| Phase | Number of Papers |
|---|---|
| Design | 123 |
| Analysis | 68 |
| Implementation | 37 |
| Any | 18 |
| Development | 14 |
| Test | 7 |
| Operation | 6 |
| Maintenance | 5 |
| Modeling | 5 |
| Run | 4 |
| Deployment | 3 |
| Evolution | 3 |
| Verification | 2 |
| Evaluation | 1 |
| Integration | 1 |
| Disposal | 1 |
| Security Pattern | Number of Appearances |
|---|---|
| Role-Based Access Control (RBAC) | 49 |
| Authorization | 34 |
| Authentication | 23 |
| Access control | 21 |
| Authenticator | 21 |
| Secure logger | 19 |
| Check point | 17 |
| Reference monitor | 15 |
| Secure pipe | 14 |
| Single access point | 13 |
| Authentication enforcer | 11 |
| Attribute-Based Access Control (ABAC) | 10 |
| Encrypted Storage | 10 |
| Firewall | 10 |
| Replicated system | 10 |
| Attack Pattern | Number of Appearances |
|---|---|
| Spoofing | 6 |
| Denial-of-service (DoS) | 5 |
| Misuse | 5 |
| Information disclosure | 4 |
| Injection | 4 |
| Tampering | 4 |
| Malicious Virtual Machine Migration | 3 |
| Elevation of privilege | 2 |
| Integrity | 2 |
| Message secrecy violation | 2 |
| Repudiation | 2 |
| Resource usage monitoring | 2 |
| Session state poisoning | 2 |
| Theft of services | 2 |
| Group | Example | Number of Papers |
|---|---|---|
| UML | Class/Activity diagram | 104 (43.3%) |
| Goal oriented | i* (i-star), KAOS, threat tree | 13 (5.4%) |
| Formal | Z notation, formula | 12 (5.0%) |
| Natural language | Text, structured document | 12 (5.0%) |
| Original | Original notations | 6 (2.5%) |
| Others | Process model, XML, OWL | 65 (27.1%) |
| Not specified | 77 (32.1%) |
| Paper | Topic | Phase | Platform | Tool | Evaluation |
|---|---|---|---|---|---|
| [264] | Application | Design | Cloud | Model-driven development | Example |
| [265] | Survey | Design | Cloud | – | – |
| [266] | Application | Design | IoT | – | – |
| [267] | Application | Analysis | – | Goal-oriented modeling | Case study |
| Paper | Vulnerability | Characteristic | Measurement |
|---|---|---|---|
| [264] | – | Integrity, Availability | Security level |
| [265] | Vulnerabilities, threats | Confidentiality, Integrity, Availability | – |
| [266] | – | Confidentiality | – |
| [267] | STRIDE, threats | Confidentiality, Integrity, Availability | – |
| Paper | Security Pattern | Attack Pattern |
|---|---|---|
| [264] | Protection Reverse Proxy | – |
| [265] | Authorization, Authentication, Logging/Auditing | – |
| [266] | Reference Monitor, Role Based Access Control (RBAC), Remote Authenticator/Authorizer, Matrix Authentication, File Authentication | – |
| [267] | Alternative service, Client Checking, Separation of Duty, Certification authority, Supervision Relation, Access Control, Auditing, Input Guard, Server sandbox, Firewall, Replicated System, Load Balancer, Limited View, Full View with Errors, Secure Access Layer, Secure Pipe, Storage Encryption, Equipment siting and protection, Supporting Utility, Physical Entry Control, Cabling security | – |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Washizaki, H.; Xia, T.; Kamata, N.; Fukazawa, Y.; Kanuka, H.; Kato, T.; Yoshino, M.; Okubo, T.; Ogata, S.; Kaiya, H.; et al. Systematic Literature Review of Security Pattern Research. Information 2021, 12, 36. https://doi.org/10.3390/info12010036
Washizaki H, Xia T, Kamata N, Fukazawa Y, Kanuka H, Kato T, Yoshino M, Okubo T, Ogata S, Kaiya H, et al. Systematic Literature Review of Security Pattern Research. Information. 2021; 12(1):36. https://doi.org/10.3390/info12010036
Chicago/Turabian StyleWashizaki, Hironori, Tian Xia, Natsumi Kamata, Yoshiaki Fukazawa, Hideyuki Kanuka, Takehisa Kato, Masayuki Yoshino, Takao Okubo, Shinpei Ogata, Haruhiko Kaiya, and et al. 2021. "Systematic Literature Review of Security Pattern Research" Information 12, no. 1: 36. https://doi.org/10.3390/info12010036
APA StyleWashizaki, H., Xia, T., Kamata, N., Fukazawa, Y., Kanuka, H., Kato, T., Yoshino, M., Okubo, T., Ogata, S., Kaiya, H., Hazeyama, A., Tanaka, T., Yoshioka, N., & Priyalakshmi, G. (2021). Systematic Literature Review of Security Pattern Research. Information, 12(1), 36. https://doi.org/10.3390/info12010036








