Ethical Applications of Big Data-Driven AI on Social Systems: Literature Analysis and Example Deployment Use Case
Abstract
1. Introduction
- A critical analysis of the state of the art in social computing.
- An analysis of the dangers posed by Big Data use outside of controlled experiments.
- A discussion on the limitations of social computing without proper sociological and legal considerations.
- A review of social aspects that propel our use case (homelessness and loneliness).
- A methodology for ethically-aligned social computing research.
2. Big Data-Driven Ai for Social Systems
2.1. Social Computing: State of the Art
2.2. The “Big Data“ Fallacy
2.3. Limitations and Bottlenecks
3. Use-Case: Home Sharing to Combat Youth Homelessness
3.1. Motivating Problem 1: The Loneliness Epidemic
3.2. Motivating Problem 2: Youth Homelessness
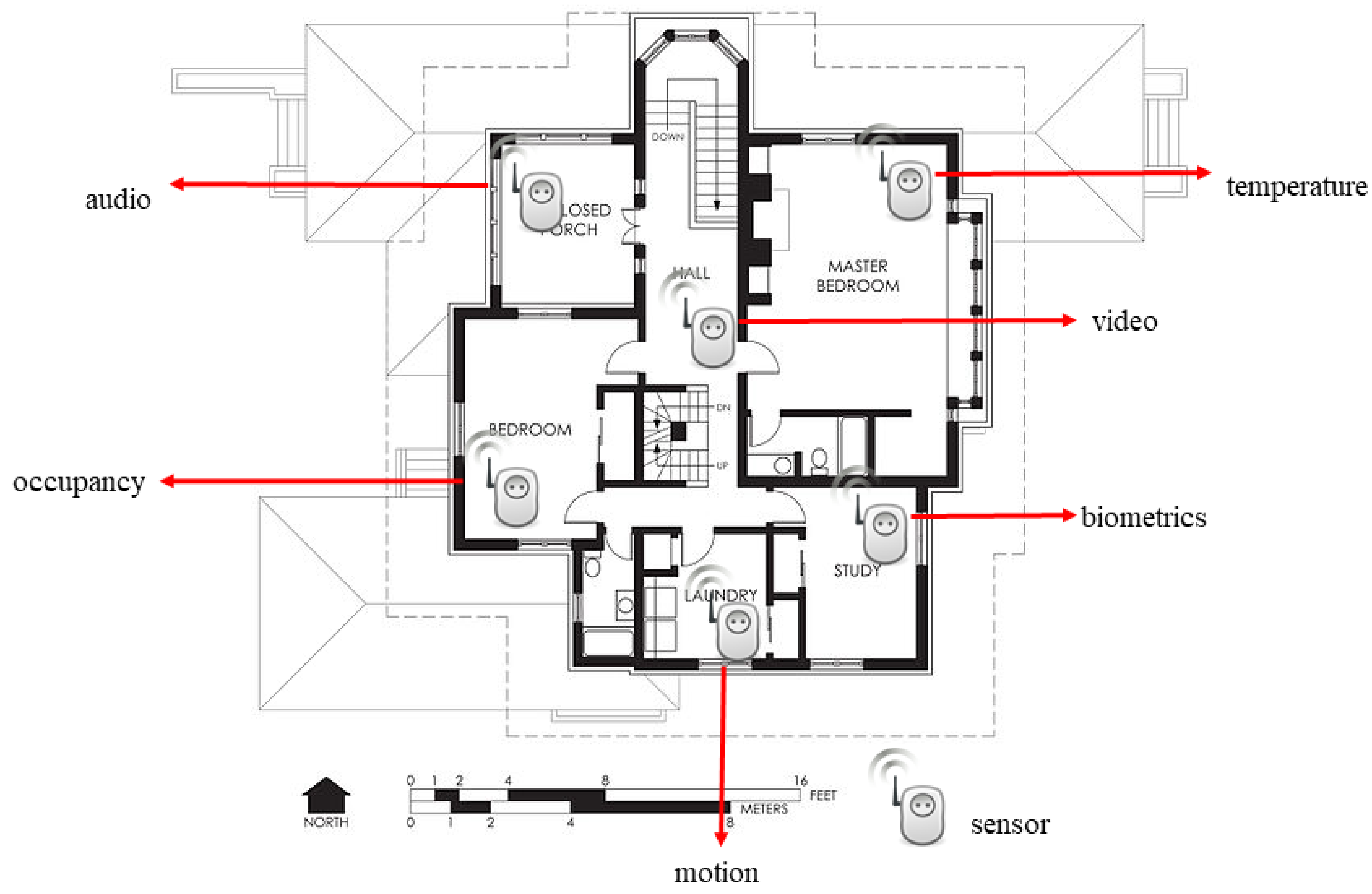
3.3. Ethical Social Computing: Use Case Description
- Determine the best strategies to pair and support the cohabitation of seniors and youth;
- Identify and understand diverse senior and youth perspectives on the use of third-party research technology (including, for example, ethnic-cultural minorities and LGBTQ+ seniors);
- Determine how best to use technology to support the safety and comfort of both populations;
- Assess changes in measures of quality of life and loneliness for both populations;
- Identify, classify and suggest recommendations to limit privacy implications; and
- Design, develop, and test AI training methodologies and sensing technology that uniquely fit our application domain.
3.4. Risk Analysis
3.5. Projected Rewards
4. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Katz, J.E.; Rice, R.E.; Aspden, P. The Internet, 1995–2000: Access, civic involvement, and social interaction. Am. Behav. Sci. 2001, 45, 405–419. [Google Scholar] [CrossRef]
- Allcott, H.; Gentzkow, M. Social media and fake news in the 2016 election. J. Econ. Perspect. 2017, 31, 211–236. [Google Scholar] [CrossRef]
- Swan, M. Blockchain: Blueprint for a New Economy; O’Reilly Media, Inc.: Sevastopol, CA, USA, 2015. [Google Scholar]
- Katsiampa, P. Volatility estimation for Bitcoin: A comparison of GARCH models. Econ. Lett. 2017, 158, 3–6. [Google Scholar] [CrossRef]
- Jonassen, D.H.; Howland, J.; Moore, J.; Marra, R.M. Learning to Solve Problems with Technology: A Constructivist Perspective. Comput. Sci. 2003. Available online: https://www.semanticscholar.org/paper/Learning-to-Solve-Problems-with-Technology%3A-A-Jonassen-Howland/30d2e65772455f25f70fcbaaa749c740a1491197 (accessed on 24 April 2020).
- Rip, A.; Misa, T.J.; Schot, J. Managing Technology in Society; Pinter Publishers: London, UK, 1995. [Google Scholar]
- Cohen, D.J.; Lippert, S.K. The lure of technology: Panacea or pariah? J. Manag. Educ. 1999, 23, 743–746. [Google Scholar] [CrossRef]
- McGrath, J.E.; Hollingshead, A.B. Groups Interacting with Technology: Ideas, Evidence, Issues, and an Agenda; Sage Publications, Inc: Southend Oaks, CA, USA, 1994. [Google Scholar]
- Lin, W.; Dou, W.; Zhou, Z.; Liu, C. A cloud-based framework for Home-diagnosis service over big medical data. J. Syst. Softw. 2015, 102, 192–206. [Google Scholar] [CrossRef]
- Kim, R.D.; Kapur, V.K.; Redline-Bruch, J.; Rueschman, M.; Auckley, D.H.; Benca, R.M.; Foldvary-Schafer, N.R.; Iber, C.; Zee, P.C.; Rosen, C.L.; et al. An economic evaluation of home versus laboratory-based diagnosis of obstructive sleep apnea. Sleep 2015, 38, 1027–1037. [Google Scholar] [CrossRef]
- National Highway Traffic Safety Administration. Automated Driving Systems 2.0: A Vision for Safety; US Department of Transportation: Washington, DC, USA, 2017; Volume 812, p. 442. [Google Scholar]
- Cook, D.J.; Duncan, G.; Sprint, G.; Fritz, R.L. Using smart city technology to make healthcare smarter. Proc. IEEE 2018, 106, 708–722. [Google Scholar] [CrossRef]
- Tàbara, J.D.; Takama, T.; Mishra, M.; Hermanus, L.; Andrew, S.K.; Diaz, P.; Ziervogel, G.; Lemkow, L. Micro-solutions to global problems: Understanding social processes to eradicate energy poverty and build climate-resilient livelihoods. Clim. Chang. 2019, 1–15. [Google Scholar] [CrossRef]
- Kremez, Z.; Frazer, L.; Weaven, S.; Quach, S. Ecommerce structures for retail and service franchises: Ecommerce implementation in mature franchise systems. Asia Pac. J. Mark. Logist. 2019. [Google Scholar] [CrossRef]
- Zervas, G.; Proserpio, D.; Byers, J.W. The rise of the sharing economy: Estimating the impact of Airbnb on the hotel industry. J. Mark. Res. 2017, 54, 687–705. [Google Scholar] [CrossRef]
- Khan, N.Z.; Luxton-Reilly, A. Is computing for social good the solution to closing the gender gap in computer science? In Proceedings of the Australasian Computer Science Week Multiconference, Canberra, Australia, 2–5 February 2016; ACM: New York, NY, USA, 2016; p. 17. [Google Scholar]
- Goldweber, M. Computer science education for social good. ACM SIGCAS Comput. Soc. 2015, 45, 29–30. [Google Scholar] [CrossRef]
- Picard, R.W. Affective computing: From laughter to IEEE. IEEE Trans. Affect. Comput. 2010, 1, 11–17. [Google Scholar] [CrossRef]
- Ning, H.; Liu, H.; Ma, J.; Yang, L.T.; Huang, R. Cybermatics: Cyber–physical–social–thinking hyperspace based science and technology. Future Gener. Comput. Syst. 2016, 56, 504–522. [Google Scholar] [CrossRef]
- Johnson, D.; Deterding, S.; Kuhn, K.A.; Staneva, A.; Stoyanov, S.; Hides, L. Gamification for health and wellbeing: A systematic review of the literature. Internet Interv. 2016, 6, 89–106. [Google Scholar] [CrossRef] [PubMed]
- Fogg, B.J. Persuasive technology: Using computers to change what we think and do. Ubiquity 2002, 2002, 5. [Google Scholar] [CrossRef]
- Calvo, R.A.; Dinakar, K.; Picard, R.; Maes, P. Computing in mental health. In Proceedings of the 2016 CHI Conference Extended Abstracts on Human Factors in Computing Systems, San Jose, CA, USA, 7–12 May 2016; ACM: New York, NY, USA, 2016; pp. 3438–3445. [Google Scholar]
- Cambria, E. Affective computing and sentiment analysis. IEEE Intell. Syst. 2016, 31, 102–107. [Google Scholar] [CrossRef]
- Asad, M.; Le Dantec, C.A. Illegitimate civic participation: Supporting community activists on the ground. In Proceedings of the 18th ACM Conference on Computer Supported Cooperative Work & Social Computing, Vancouver, BC, Canada, 14–18 March 2015; ACM: New York, NY, USA, 2015; pp. 1694–1703. [Google Scholar]
- Dombrowski, L.; Harmon, E.; Fox, S. Social justice-oriented interaction design: Outlining key design strategies and commitments. In Proceedings of the 2016 ACM Conference on Designing Interactive Systems, Brisbane, QLD, Australia, 4–8 June 2016; ACM: New York, NY, USA, 2016; pp. 656–671. [Google Scholar]
- Ning, Z.; Xia, F.; Ullah, N.; Kong, X.; Hu, X. Vehicular social networks: Enabling smart mobility. IEEE Commun. Mag. 2017, 55, 16–55. [Google Scholar] [CrossRef]
- Bowers, K.M.; Hariri, R.H.; Price, K.A. 3CAP: Categorizing the cognitive capabilities of Alzheimer’s patients in a smart home environment. In Proceedings of the 4th ACM SIGSOFT International Workshop on NLP for Software Engineering, Lake Buena Vista, FL, USA, 4 November 2018; ACM: New York, NY, USA, 2018; pp. 34–37. [Google Scholar]
- Liu, L.; Stroulia, E.; Nikolaidis, I.; Miguel-Cruz, A.; Rincon, A.R. Smart homes and home health monitoring technologies for older adults: A systematic review. Int. J. Med. Inform. 2016, 91, 44–59. [Google Scholar] [CrossRef]
- Boise, L.; Wild, K.; Mattek, N.; Ruhl, M.; Dodge, H.H.; Kaye, J. Willingness of older adults to share data and privacy concerns after exposure to unobtrusive in-home monitoring. Gerontechnology 2013, 11, 428–435. [Google Scholar] [CrossRef]
- Mihailidis, A.; Cockburn, A.; Longley, C.; Boger, J. The acceptability of home monitoring technology among community-dwelling older adults and baby boomers. Assist. Technol. 2008, 20, 1–12. [Google Scholar] [CrossRef] [PubMed]
- Steele, R.; Lo, A.; Secombe, C.; Wong, Y.K. Elderly persons’ perception and acceptance of using wireless sensor networks to assist healthcare. Int. J. Med. Inform. 2009, 78, 788–801. [Google Scholar] [CrossRef] [PubMed]
- Wild, K.; Boise, L.; Lundell, J.; Foucek, A. Unobtrusive in-home monitoring of cognitive and physical health: Reactions and perceptions of older adults. J. Appl. Gerontol. 2008, 27, 181–200. [Google Scholar] [CrossRef] [PubMed]
- Schneble, C.O.; Elger, B.S.; Shaw, D.M. Google’s Project Nightingale highlights the necessity of data science ethics review. EMBO Mol. Med. 2020. [Google Scholar]
- Yin, G.; Zhang, C.; Yang, Z. Biostatistics pitfalls: Lessons learned from analysis of medical data. Contemp. Clin. Trials 2019, 87, 105875. [Google Scholar] [CrossRef]
- Valentine, S. Impoverished algorithms: Misguided governments, flawed technologies, and social control. Fordham Urb. LJ 2019, 46, 364. [Google Scholar]
- Madson, G.J.; Hillygus, D.S. All the best polls agree with me: Bias in evaluations of political polling. Political Behav. 2019, 1–18. [Google Scholar] [CrossRef]
- Economou, P.; Batsidis, A.; Tzavelas, G.; Alexopoulos, P.; Initiative, A.D.N. Berkson’s paradox and weighted distributions: An application to Alzheimer’s disease. Biom. J. 2020, 62, 238–249. [Google Scholar] [CrossRef]
- Berkson, J. Limitations of the application of fourfold table analysis to hospital data. Biom. Bull. 1946, 2, 47–53. [Google Scholar] [CrossRef]
- Zou, J.; Schiebinger, L. AI can be sexist and racist—it’s time to make it fair. Nature 2018, 559, 324–326. [Google Scholar] [CrossRef]
- Woelfer, J.P.; Hendry, D.G. Designing ubiquitous information systems for a community of homeless young people: Precaution and a way forward. Pers. Ubiquitous Comput. 2011, 15, 565–573. [Google Scholar] [CrossRef]
- Kim, K.J.; Shin, D.H. An acceptance model for smart watches: Implications for the adoption of future wearable technology. Internet Res. 2015, 25, 527–541. [Google Scholar] [CrossRef]
- Shin, D.H. Understanding user acceptance of DMB in South Korea using the modified technology acceptance model. Intl. J. Hum. Interact. 2009, 25, 173–198. [Google Scholar] [CrossRef]
- Luo, Y.; Hawkley, L.C.; Waite, L.J.; Cacioppo, J.T. Loneliness, health, and mortality in old age: A national longitudinal study. Soc. Sci. Med. 2012, 74, 907–914. [Google Scholar] [CrossRef] [PubMed]
- Austin, J.; Dodge, H.H.; Riley, T.; Jacobs, P.G.; Thielke, S.; Kaye, J. A smart-home system to unobtrusively and continuously assess loneliness in older adults. IEEE J. Transl. Eng. Health Med. 2016, 4, 1–11. [Google Scholar] [CrossRef] [PubMed]
- King, M. Working to Address the Loneliness Epidemic: Perspective-Taking, Presence, and Self-Disclosure. Am. J. Health Promot. 2018, 1315–1317. [Google Scholar] [CrossRef]
- Khosravi, P.; Rezvani, A.; Wiewiora, A. The impact of technology on older adults’ social isolation. Comput. Hum. Behav. 2016, 63, 594–603. [Google Scholar] [CrossRef]
- Picard, A. All the Lonely People. UC Observer, June 2016. [Google Scholar]
- IFA. Current and Emerging Issues Facing Older Canadians; IFA: Toronto, ON, Canada, 2012. [Google Scholar]
- Cornwell, E.Y.; Waite, L.J. Social disconnectedness, perceived isolation, and health among older adults. J. Health Soc. Behav. 2009, 50, 31–48. [Google Scholar] [CrossRef]
- Weldrick, R.; Grenier, A. Social isolation in later life: Extending the conversation. Can. J. Aging/La Rev. Can. Du Vieil. 2018, 37, 76–83. [Google Scholar] [CrossRef]
- Tang, J.; Galbraith, N.; Truong, J. Living Alone in Canada; Statistics Canada/Statistique Canada: Ottawa, ON, Canada, 2019. [Google Scholar]
- Employment and Social Development Canada. Report on Housing Needs of Seniors. 2010. Available online: https://www.canada.ca/en/employment-social-development/corporate/seniors/forum/report-seniors-housing-needs.html (accessed on 24 April 2020).
- Gaetz, S.A.; Bill, O.; Kidd, S.; Schwan, K. Without a Home: The National Youth Homelessness Survey; Canadian Observatory on Homelessness Press: Toronto, ON, Canada, 2016. [Google Scholar]
- Gaetz, S.; Ward, A.; Kimura, L. Youth homelessness and housing stability: What outcomes should we be looking for? Healthc. Manag. Forum 2019, 32, 73–77. [Google Scholar] [CrossRef] [PubMed]
- Balagot, C.; Lemus, H.; Hartrick, M.; Kohler, T.; Lindsay, S.P. The homeless Coordinated Entry System: The VI-SPDAT and other predictors of establishing eligibility for services for single homeless adults. J. Soc. Distress Homeless 2019, 28, 149–157. [Google Scholar] [CrossRef]
- Eubanks, V. High-Tech Homelessness. Am. Sci. 2018, 106, 230–233. [Google Scholar] [CrossRef]
- Jakob, A.; Collier, L. Sensory enrichment for people living with dementia: Increasing the benefits of multisensory environments in dementia care through design. Des. Health 2017, 1, 115–133. [Google Scholar] [CrossRef]
- Berg, I.A.; Khorev, O.E.; Matvevnina, A.I.; Prisjazhnyj, A.V. Machine learning in smart home control systems-Algorithms and new opportunities. In AIP Conference Proceedings; AIP Publishing: Melville, NY, USA, 2017; Volume 1906, p. 070007. [Google Scholar]
- Lee, J.H.; Kim, H. Security and privacy challenges in the internet of things [security and privacy matters]. IEEE Consum. Electron. Mag. 2017, 6, 134–136. [Google Scholar] [CrossRef]
- Bandeen-Roche, K.; Seplaki, C.L.; Huang, J.; Buta, B.; Kalyani, R.R.; Varadhan, R.; Xue, Q.L.; Walston, J.D.; Kasper, J.D. Frailty in older adults: A nationally representative profile in the United States. J. Gerontol. Ser. A 2015, 70, 1427–1434. [Google Scholar] [CrossRef]
- Watts, B.; Fitzpatrick, S.; Johnsen, S. Controlling homeless people? Power, interventionism and legitimacy. J. Soc. Policy 2018, 47, 235–252. [Google Scholar] [CrossRef]
- Novák, M.; Jakab, F.; Lain, L. Anomaly detection in user daily patterns in smart-home environment. J. Sel. Areas Health Inf. 2013, 3, 1–11. [Google Scholar]
- Amershi, S.; Conati, C.; Maclaren, H. Using feature selection and unsupervised clustering to identify affective expressions in educational games. In Proceedings of the Intelligent Tutoring Systems Workshop on Motivational and Affective Issues in ITS (ITS 2006), Jhongli, Taiwan, 26–30 June 2006. [Google Scholar]

© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Garcia, P.; Darroch, F.; West, L.; BrooksCleator, L. Ethical Applications of Big Data-Driven AI on Social Systems: Literature Analysis and Example Deployment Use Case. Information 2020, 11, 235. https://doi.org/10.3390/info11050235
Garcia P, Darroch F, West L, BrooksCleator L. Ethical Applications of Big Data-Driven AI on Social Systems: Literature Analysis and Example Deployment Use Case. Information. 2020; 11(5):235. https://doi.org/10.3390/info11050235
Chicago/Turabian StyleGarcia, Paulo, Francine Darroch, Leah West, and Lauren BrooksCleator. 2020. "Ethical Applications of Big Data-Driven AI on Social Systems: Literature Analysis and Example Deployment Use Case" Information 11, no. 5: 235. https://doi.org/10.3390/info11050235
APA StyleGarcia, P., Darroch, F., West, L., & BrooksCleator, L. (2020). Ethical Applications of Big Data-Driven AI on Social Systems: Literature Analysis and Example Deployment Use Case. Information, 11(5), 235. https://doi.org/10.3390/info11050235





