Location Privacy Protection Systems in Presence of Service Quality and Energy Constraints
Abstract
:1. Introduction
2. Related Work
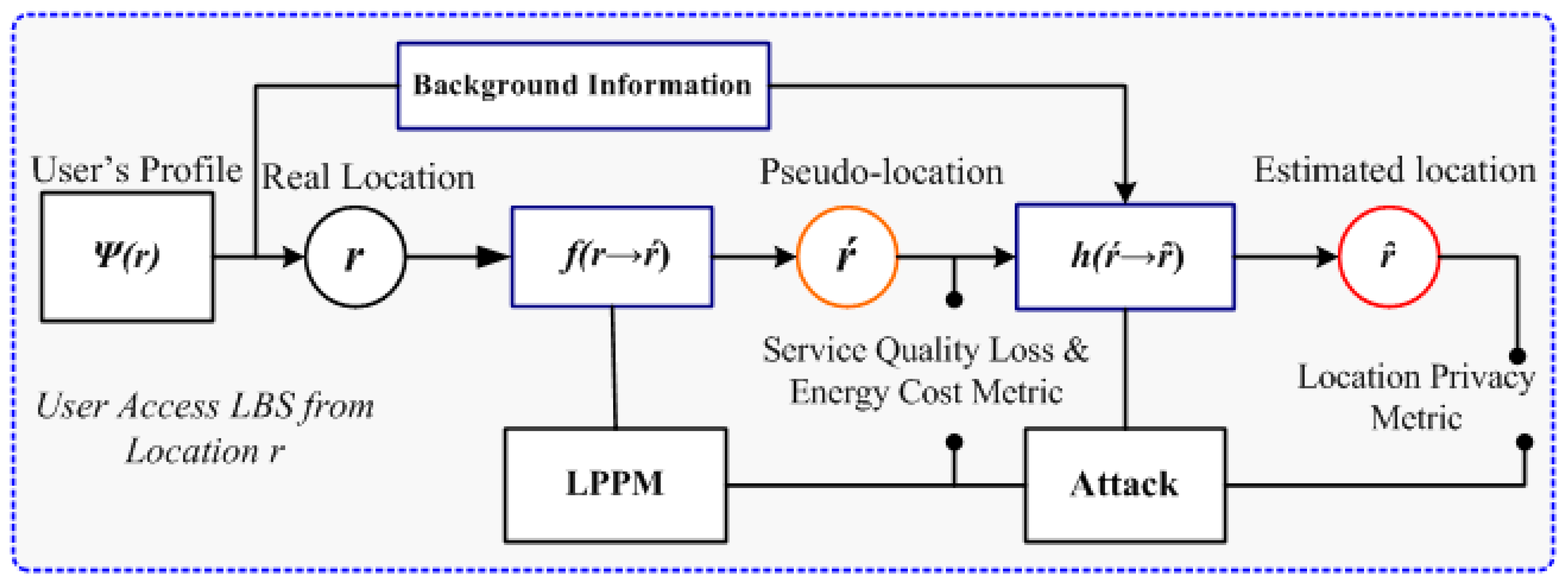
3. Privacy-Preserving System Framework
3.1. User and Adversary Consideration
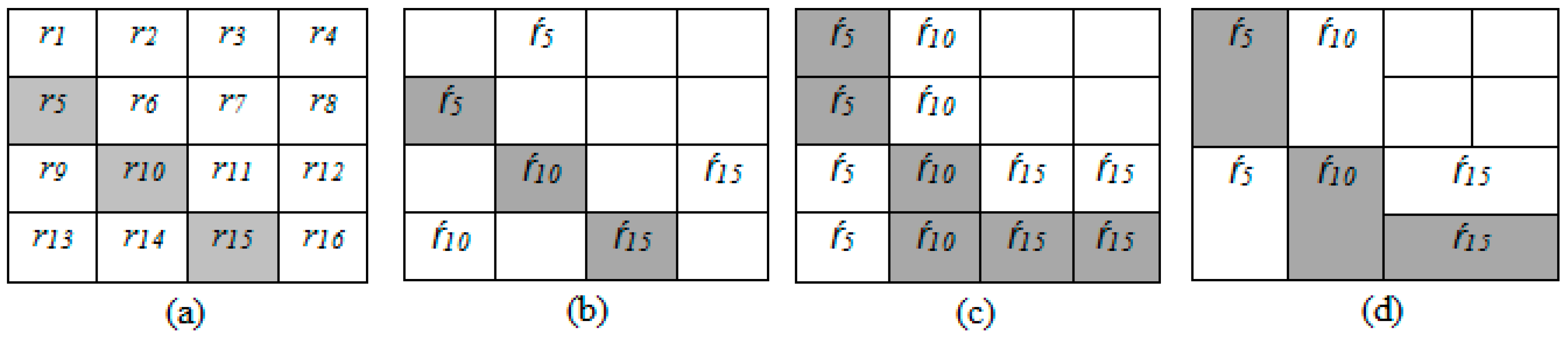
3.2. General Considerations for LPPMs
3.3. The Performance Metrics for Privacy Protection
3.3.1. Quality of Service Analysis and Evaluation System
3.3.2. Energy Consumption Analysis
3.3.3. Location-Privacy Leakage (Adversarial Estimation Error)
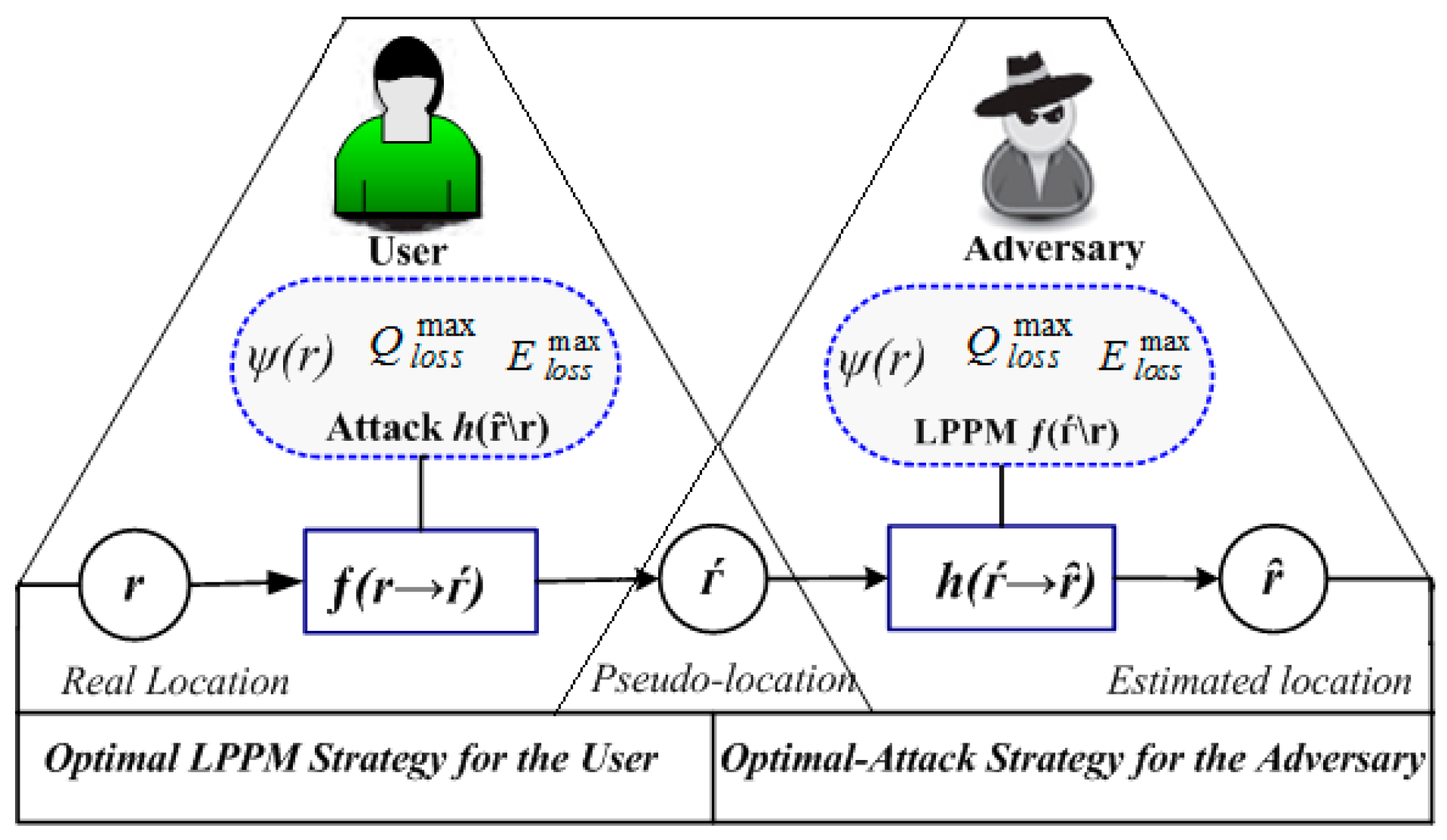
4. Privacy Game Formulation for Attack and Defense Mechanisms
4.1. The Problem Statement
4.2. Optimal Privacy Protection for the User
4.3. Optimal Inference Attack for the Adversary
5. Performance Evaluation and Results
5.1. Parameter Settings and Configuration
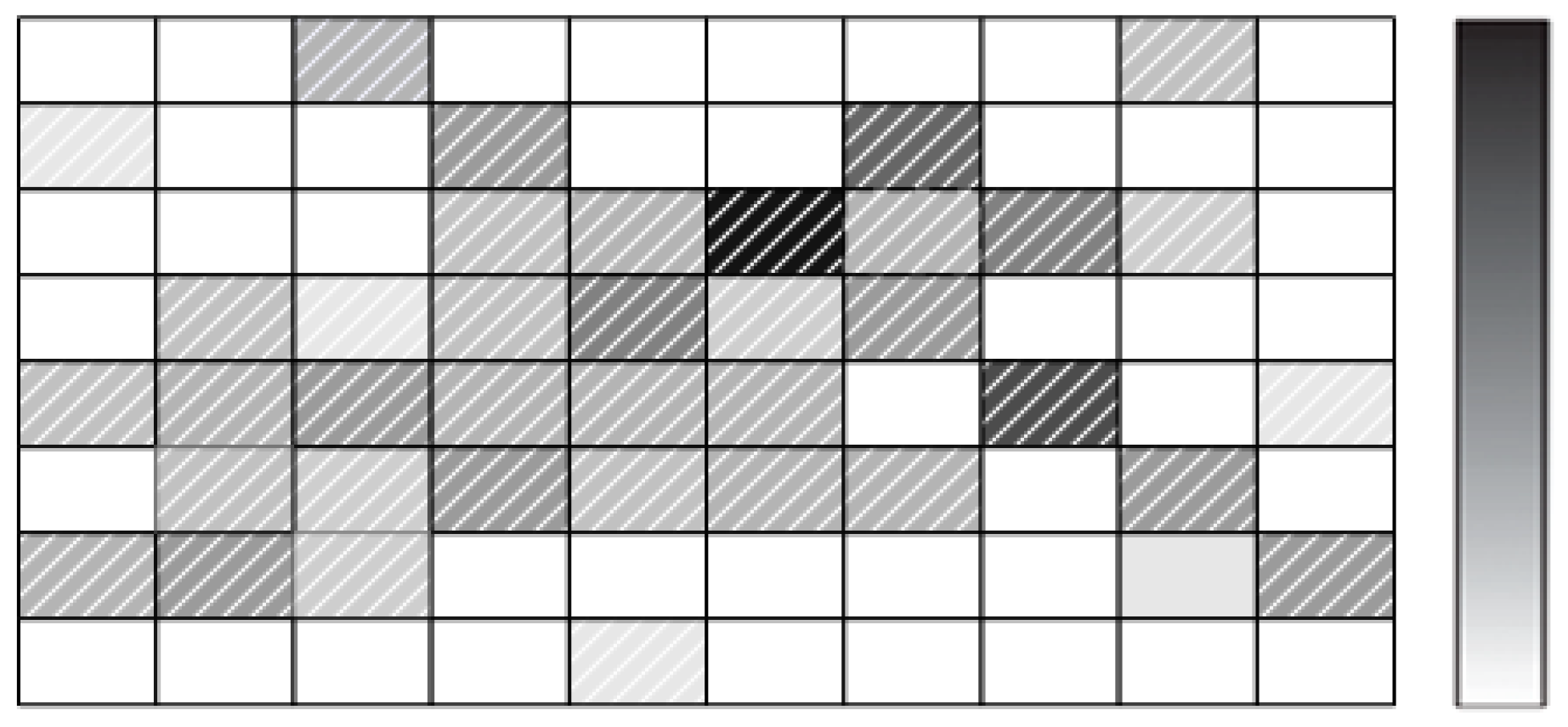
5.2. Modeling the Location Mobility Trace Based on POI Mining
5.3. Optimal Protection and Attack Strategies
5.4. Evaluation Results
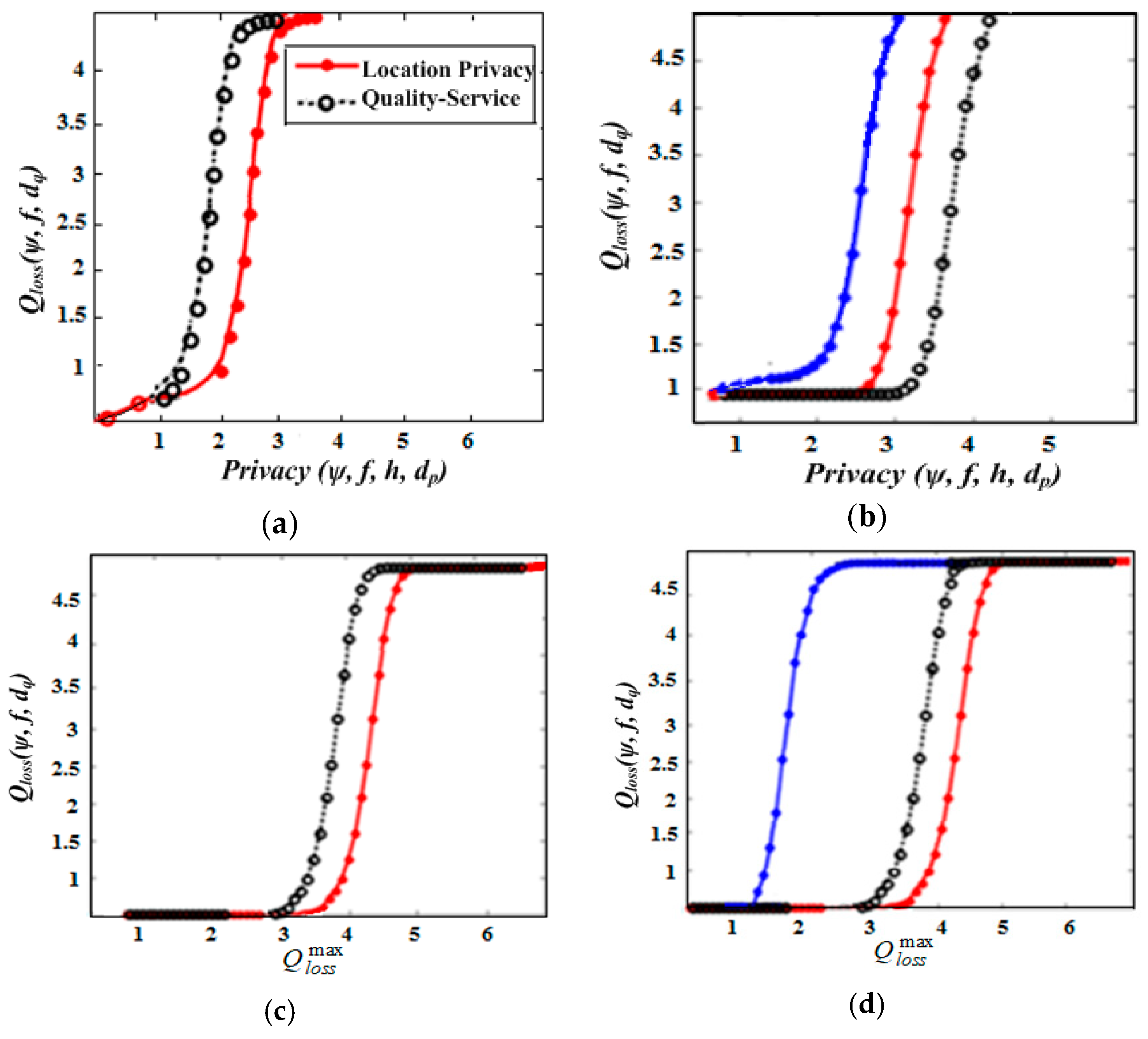
5.4.1. Privacy Protection under Quality-Loss Constraint
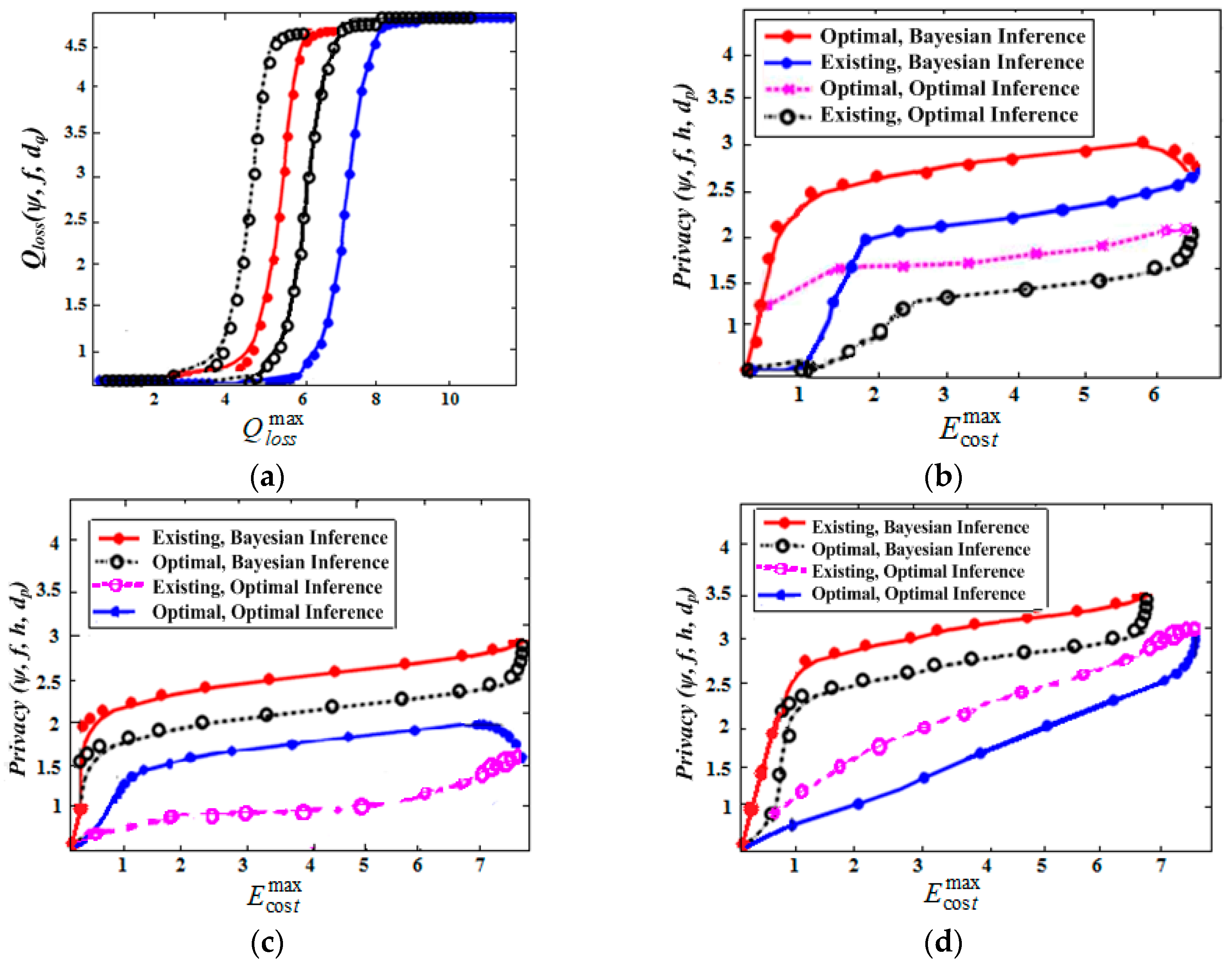
5.4.2. Performance of Existing and Optimal Strategies
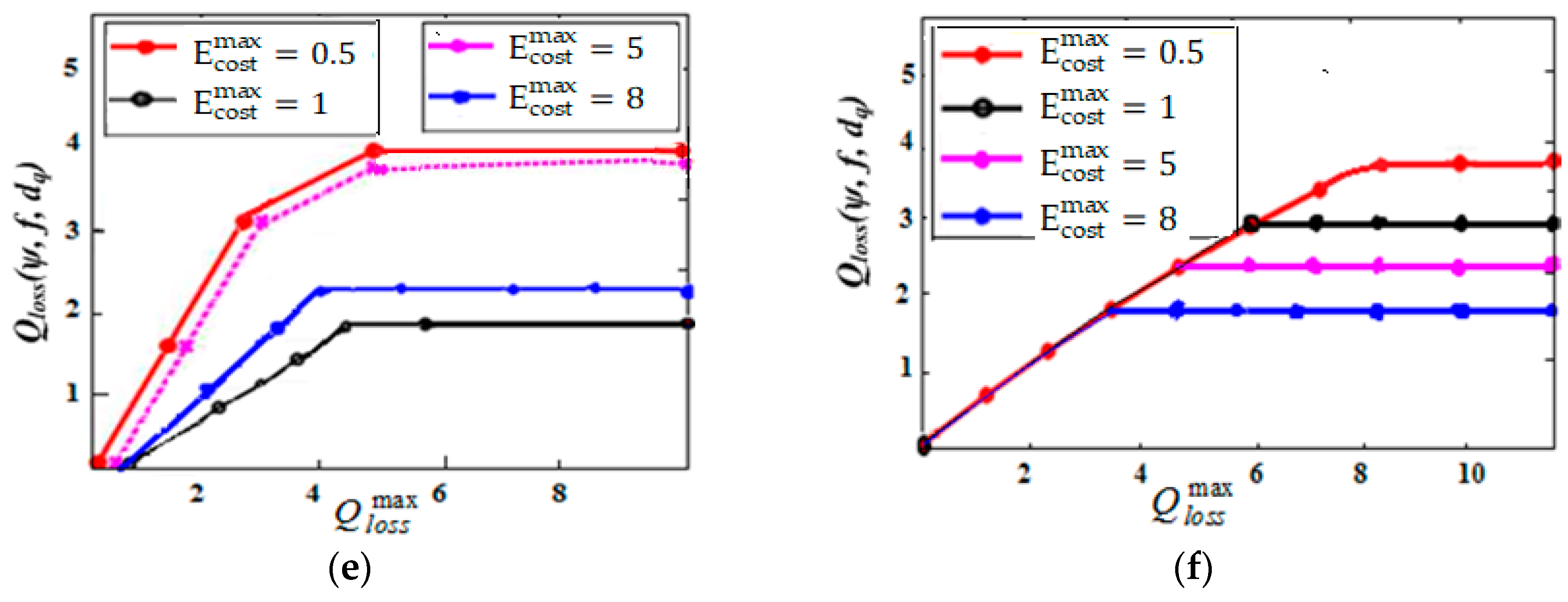
5.4.3. Effectiveness and Advantage of Optimal Protection
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Aditya, P.; Bhattacharjee, B.; Druschel, P.; Erdélyi, V.; Lentz, M. Brave new world: Privacy risks for mobile users. ACM Sigmobile Mob. Comput. Commun. Rev. 2015, 18, 49–54. [Google Scholar] [CrossRef]
- Yi, X.; Paulet, R.; Bertino, E.; Varadharajan, V. Practical approximate k nearest neighbor queries with location and query privacy. IEEE Trans. Knowl. Data Eng. 2016, 28, 1546–1559. [Google Scholar] [CrossRef]
- Gambs, S.; Killijian, M.O.; Cortez, M.N.D. Show me how you move and I will tell you who you are. In Proceedings of the 3rd ACM SIGSPATIAL International Workshop on Security and Privacy in GIS and LBS, San Jose, CA, USA, 2 November 2010; pp. 34–41. [Google Scholar]
- Song, C.; Qu, Z.; Blumm, N.; Barabási, A.L. Limits of predictability in human mobility. Science 2010, 327, 1018–1021. [Google Scholar] [CrossRef] [PubMed]
- Matsuo, Y.; Okazaki, N.; Izumi, K.; Nakamura, Y.; Nishimura, T.; Hasida, K.; Nakashima, H. Inferring Long-term User Properties Based on Users’ Location History. In Proceedings of the 20th International Joint Conference on Artificial Intelligence, IJCAI, Hyderabad, India, 6–12 January 2007; pp. 2159–2165. [Google Scholar]
- Shokri, R.; Theodorakopoulos, G.; Troncoso, C. Privacy games along location traces: A game-theoretic framework for optimizing location privacy. ACM Trans. Priv. Secur. (TOPS) 2017, 19, 11. [Google Scholar] [CrossRef]
- Freudiger, J.; Shokri, R.; Hubaux, J.P. On the optimal placement of mix zones. In Proceedings of the International Symposium on Privacy Enhancing Technologies Symposium, Seattle, WA, USA, 5–7 August 2009; Springer: Berlin/Heidelberg, Germany, 2009; pp. 216–234. [Google Scholar]
- Brunton, F.; Nissenbaum, H. Vernacular resistance to data collection and analysis: A political theory of obfuscation. First Monday 2011, 16. Available online: https://firstmonday.org/ojs/index.php/fm/article/view/ 3493/2955 (accessed on 2 April 2019). [CrossRef]
- Shen, H.; Bai, G.; Yang, M.; Wang, Z. Protecting trajectory privacy: A user-centric analysis. J. Netw. Comput. Appl. 2017, 82, 128–139. [Google Scholar] [CrossRef]
- Wang, Y.; Xia, Y.; Hou, J.; Gao, S.; Nie, X.; Wang, Q. A fast privacy-preserving framework for continuous location-based queries in road networks. J. Netw. Comput. Appl. 2015, 53, 57–73. [Google Scholar] [CrossRef]
- Lu, H.; Jensen, C.S.; Yiu, M.L. Pad: Privacy-area aware, dummy-based location privacy in mobile services. In Proceedings of the Seventh ACM International Workshop on Data Engineering for Wireless and Mobile Access, Vancouver, BC, Canada, 13 June 2008; pp. 16–23. [Google Scholar]
- Shokri, R.; Theodorakopoulos, G.; Papadimitratos, P.; Kazemi, E.; Hubaux, J.P. Hiding in the mobile crowd: Location privacy through collaboration. IEEE Trans. Dependable Secur. Comput. 2014, 11, 266–279. [Google Scholar]
- Niu, B.; Li, Q.; Zhu, X.; Li, H. A fine-grained spatial cloaking scheme for privacy-aware users in location-based services. In Proceedings of the 2014 23rd International Conference on Computer Communication and Networks (ICCCN), Shanghai, China, 4–7 August 2014; pp. 1–8. [Google Scholar]
- Niu, B.; Li, Q.; Zhu, X.; Cao, G.; Li, H.; Li, Q.; Zhu, X.; Cao, G.; Li, H. Enhancing privacy through caching in location-based services. In Proceedings of the 2015 IEEE Conference on Computer Communications (INFOCOM), Kowloon, Hong Kong, 26 April–1 May 2015; pp. 1017–1025. [Google Scholar]
- Wang, Y.; Xu, D.; He, X.; Zhang, C.; Li, F.; Bin, X. L2P2: Location-aware location privacy protection for location-based services. In Proceedings of the 2012 Proceedings IEEE INFOCOM, Orlando, FL, USA, 25–30 March 2012; pp. 1996–2004. [Google Scholar]
- Li, W.; Niu, B.; Li, H.; Li, F. Privacy-preserving strategies in service quality aware location-based services. In Proceedings of the 2015 IEEE International Conference on Communications (ICC), London, UK, 8–12 June 2015; pp. 7328–7334. [Google Scholar]
- Theodorakopoulos, G.; Shokri, R.; Troncoso, C.; Hubaux, J.P.; le Boudec, J.Y. Prolonging the hide-and-seek game: Optimal trajectory privacy for location-based services. In Proceedings of the 13th Workshop on Privacy in the Electronic Society, Scottsdale, AZ, USA, 3 November 2014; pp. 73–82. [Google Scholar]
- Shokri, R.; Theodorakopoulos, G.; Troncoso, C.; Hubaux, J.P.; le Boudec, J.Y. Protecting location privacy: Optimal strategy against localization attacks. In Proceedings of the 2012 ACM Conference on Computer and Communications Security, Raleigh, NC, USA, 16–18 October 2012; pp. 617–627. [Google Scholar]
- Ghinita, G. Private queries and trajectory anonymization: A dual perspective on location privacy. Trans. Data Priv. 2009, 2, 3–19. [Google Scholar]
- Hwang, R.-H.; Hsueh, Y.-L.; Chung, H.-W. A novel time-obfuscated algorithm for trajectory privacy protection. IEEE Trans. Serv. Comput. 2014, 7, 126–139. [Google Scholar] [CrossRef]
- Shokri, R. Privacy games: Optimal user-centric data obfuscation. Proc. Priv. Enhanc. Technol. 2015, 2015, 299–315. [Google Scholar] [CrossRef]
- Chatzikokolakis, K.; Palamidessi, C.; Panangaden, P. Anonymity protocols as noisy channels. Inf. Comput. 2008, 206, 378–401. [Google Scholar] [CrossRef]
- Shokri, R. Quantifying and protecting location privacy. IT-Inf. Technol. 2015, 57, 257–263. [Google Scholar] [CrossRef]
- Beresford, A.R.; Stajano, F. Mix zones: User privacy in location-aware services. In Proceedings of the Second IEEE Annual Conference on Pervasive Computing and Communications Workshops, Orlando, FL, USA, 14–17 March 2004; pp. 127–131. [Google Scholar]
- Shokri, R.; Freudiger, J.; Jadliwala, M.; Hubaux, J.P. A distortion-based metric for location privacy. In Proceedings of the 8th ACM Workshop on Privacy in the Electronic Society, Chicago, IL, USA, 9 November 2009; pp. 21–30. [Google Scholar]
- Shokri, R.; Theodorakopoulos, G.; Danezis, G.; Hubaux, J.P.; le Boudec, J.Y. Quantifying location privacy: The case of sporadic location exposure. In Proceedings of the International Symposium on Privacy Enhancing Technologies Symposium, Waterloo, ON, Canada, 27–29 July 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 57–76. [Google Scholar]
- Shokri, R.; Theodorakopoulos, G.; le Boudec, J.Y.; Hubaux, J.P. Quantifying location privacy. In Proceedings of the 2011 IEEE Symposium on Security and Privacy (SP), Berkeley, CA, USA, 22–25 May 2011; pp. 247–262. [Google Scholar]
- Liu, X.; Liu, K.; Guo, L.; Li, X.; Fang, Y. A game-theoretic approach for achieving k-anonymity in Location Based Services. In Proceedings of the 2013 Proceedings IEEE INFOCOM, Turin, Italy, 14–19 April 2013. [Google Scholar]
- Herrmann, M.; Troncoso, C.; Diaz, C.; Preneel, B. Optimal sporadic location privacy preserving systems in presence of bandwidth constraints. In Proceedings of the 12th ACM Workshop on Workshop on Privacy in the Electronic Society, Berlin, Germany, 4 November 2013; pp. 167–178. [Google Scholar]
- Zhang, X.; Gui, X.; Tian, F.; Yu, S.; An, J. Privacy quantification model based on the Bayes conditional risk in Location-based services. Tsinghua Sci. Technol. 2014, 19, 452–462. [Google Scholar] [CrossRef]
- Eagle, N.; Pentland, A.S.; Lazer, D. Inferring friendship network structure by using mobile phone data. Proc. Natl. Acad. Sci. USA 2009, 106, 15274–15278. [Google Scholar] [CrossRef] [PubMed]
- Piórkowski, M. Sampling urban mobility through on-line repositories of GPS tracks. In Proceedings of the 1st ACM International Workshop on Hot Topics of Planet-Scale Mobility Measurements, Kraków, Poland, 22 June 2009; p. 1. [Google Scholar]
- Zheng, Y.; Wang, L.; Zhang, R.; Xie, X.; Ma, W.Y. GeoLife: Managing and understanding your past life over maps. In Proceedings of the 9th International Conference on Mobile Data Management, MDM’08, Beijing, China, 27–30 April 2008; pp. 211–212. [Google Scholar]
- Piorkowski, M.; Sarafijanovic-Djukic, N.; Grossglauser, M. A parsimonious model of mobile partitioned networks with clustering. In Proceedings of the 2009 First International Communication Systems and Networks and Workshops, Bangalore, India, 5–10 January 2009; pp. 1–10. [Google Scholar]
- Bracciale, L.; Bonola, M.; Loreti, P.; Bianchi, G.; Amici, R.; Rabuffi, A. CRAWDAD Dataset Roma/Taxi (v. 2014-07-17). July 2014. Available online: https://crawdad.org/roma/taxi/20140717 (accessed on 18 October 2018). [CrossRef]
- Chen, X.; Pang, J.; Xue, R. Constructing and comparing user mobility profiles for location-based services. In Proceedings of the 28th Annual ACM Symposium on Applied Computing, Coimbra, Portugal, 18–22 March 2013; pp. 261–266. [Google Scholar]
- Freudiger, J.; Shokri, R.; Hubaux, J.P. Evaluating the privacy risk of location-based services. In Proceedings of the International Conference on Financial Cryptography and Data Security, Gros Islet, Saint Lucia, 28 February–4 March 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 31–46. [Google Scholar]
- Ye, Y.; Zheng, Y.; Chen, Y.; Feng, J.; Xie, X. Mining individual life pattern based on location history. In Proceedings of the Tenth International Conference on Mobile Data Management: Systems, Services and Middleware, MDM’09, Taipei, Taiwan, 18–20 May 2009. [Google Scholar]
| Symbol | Meaning |
|---|---|
| r, ŕ, | User’s real-location, observed (pseudo-location), and an adversary’s estimate location, respectively. |
| , Ŕ | Set of real and pseudo-locations, respectively. |
| ψ(r) | Probability of accessing LBS from location r, (user’s profile). |
| f(ŕ\r) | The user’s location privacy-protection function to transform r as ŕ at observation time t. |
| h(ȓ\ŕ) | The probability attacks function for adversary to estimate location ȓ closing to the real-location of the users under their observed location ŕ. |
| dq(ŕ, r), dE(ŕ, r) | Distance error functions between the real-location r and pseudo-location ŕ, which determines the user’s LBS loss of service-quality and energy constraints. |
| Distance error function between the location ȓ estimated by the attacker, and the user’s real location r, which can measure the location privacy leakage of the user, or equivalently the adversary’s expected error. | |
| Qloss(ѱ, f, dq) | Function of expected service-quality loss, given the user’s mobility profile ψ(r) and an obfuscation function f(r) at time t. |
| Ecost(ѱ, f, dE) | Function of expected energy cost, given the user’s profile ψ(r) and location obfuscation function f(r) at time t. |
| Maximum achievable loss quality of service. | |
| Maximum tolerable energy cost imposed by users. | |
| Privacy(ѱ,f,h,dp) | User’s expected location privacy with mobility profile ψ(r) using obfuscation function f(r) against inference attack function h(r). |
| Pr | Represents the probability density functions (PDFs), which are sub-indexed by the corresponding random variable in case of uncertainty. For example, denotes the probability value of function Pr at ŕ and Pr(r\ŕ) denotes posterior probability values for r, given a status of nature in ŕ. |
| Parameters | Value |
|---|---|
| Real mobility traces of taxi cabs | 320 |
| User’s moving area | 8 km × 10 km (≈ 80 km2) |
| Total Number of regions | 20 × 16 (= 320) |
| Most considered regions | 20 |
| Number of users selected | 5 |
| Length of considered times | 1 h, 2 h, 3 h |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tefera, M.K.; Yang, X. Location Privacy Protection Systems in Presence of Service Quality and Energy Constraints. Information 2019, 10, 121. https://doi.org/10.3390/info10040121
Tefera MK, Yang X. Location Privacy Protection Systems in Presence of Service Quality and Energy Constraints. Information. 2019; 10(4):121. https://doi.org/10.3390/info10040121
Chicago/Turabian StyleTefera, Mulugeta Kassaw, and Xiaolong Yang. 2019. "Location Privacy Protection Systems in Presence of Service Quality and Energy Constraints" Information 10, no. 4: 121. https://doi.org/10.3390/info10040121
APA StyleTefera, M. K., & Yang, X. (2019). Location Privacy Protection Systems in Presence of Service Quality and Energy Constraints. Information, 10(4), 121. https://doi.org/10.3390/info10040121





