SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks
Abstract
1. Introduction
2. Related Work
3. Design and Deployment of Our Flow-Based Proposal Thwarting DDoS Attacks
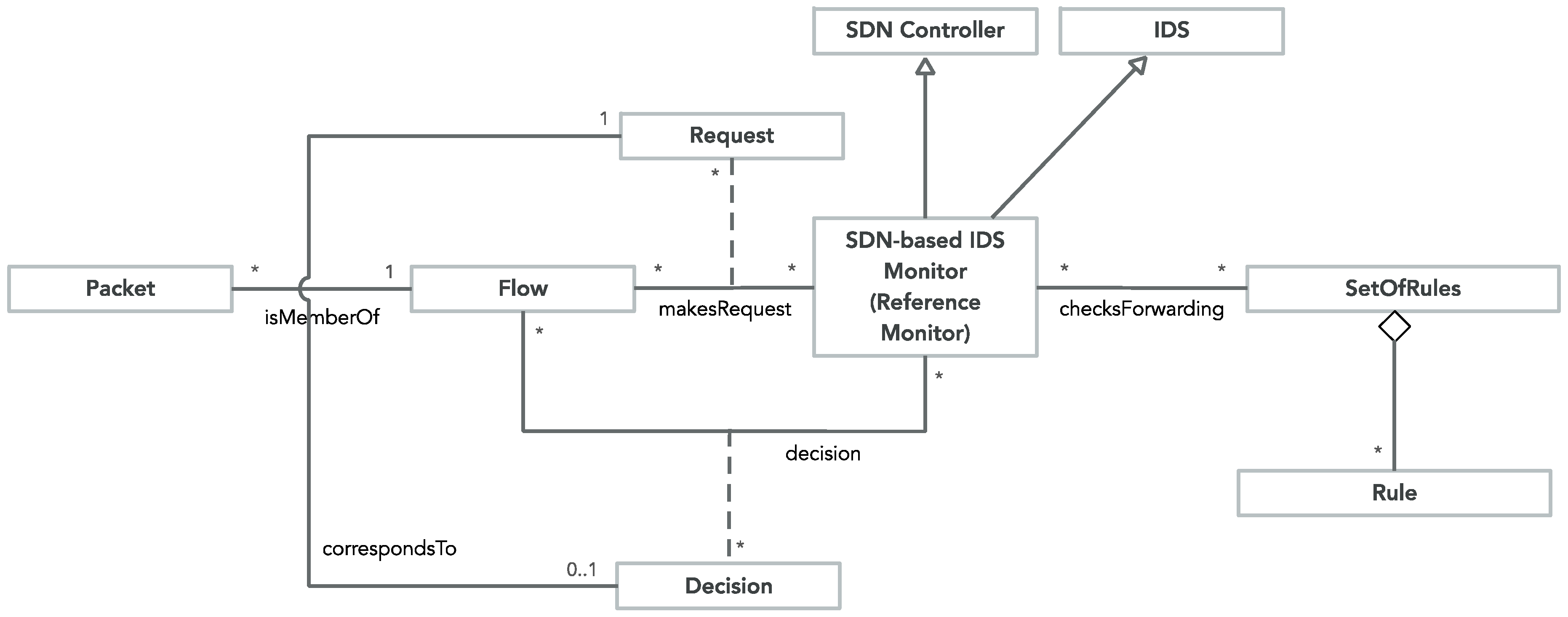
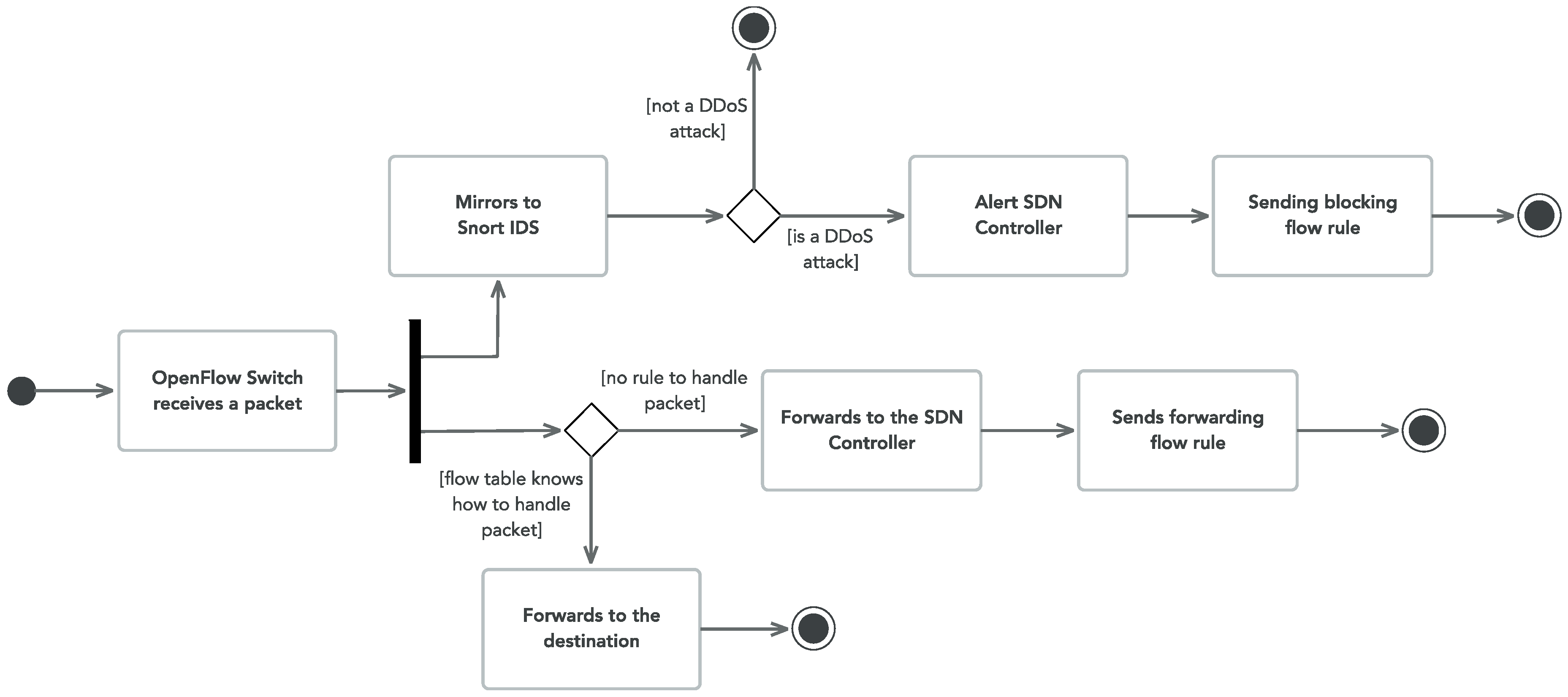
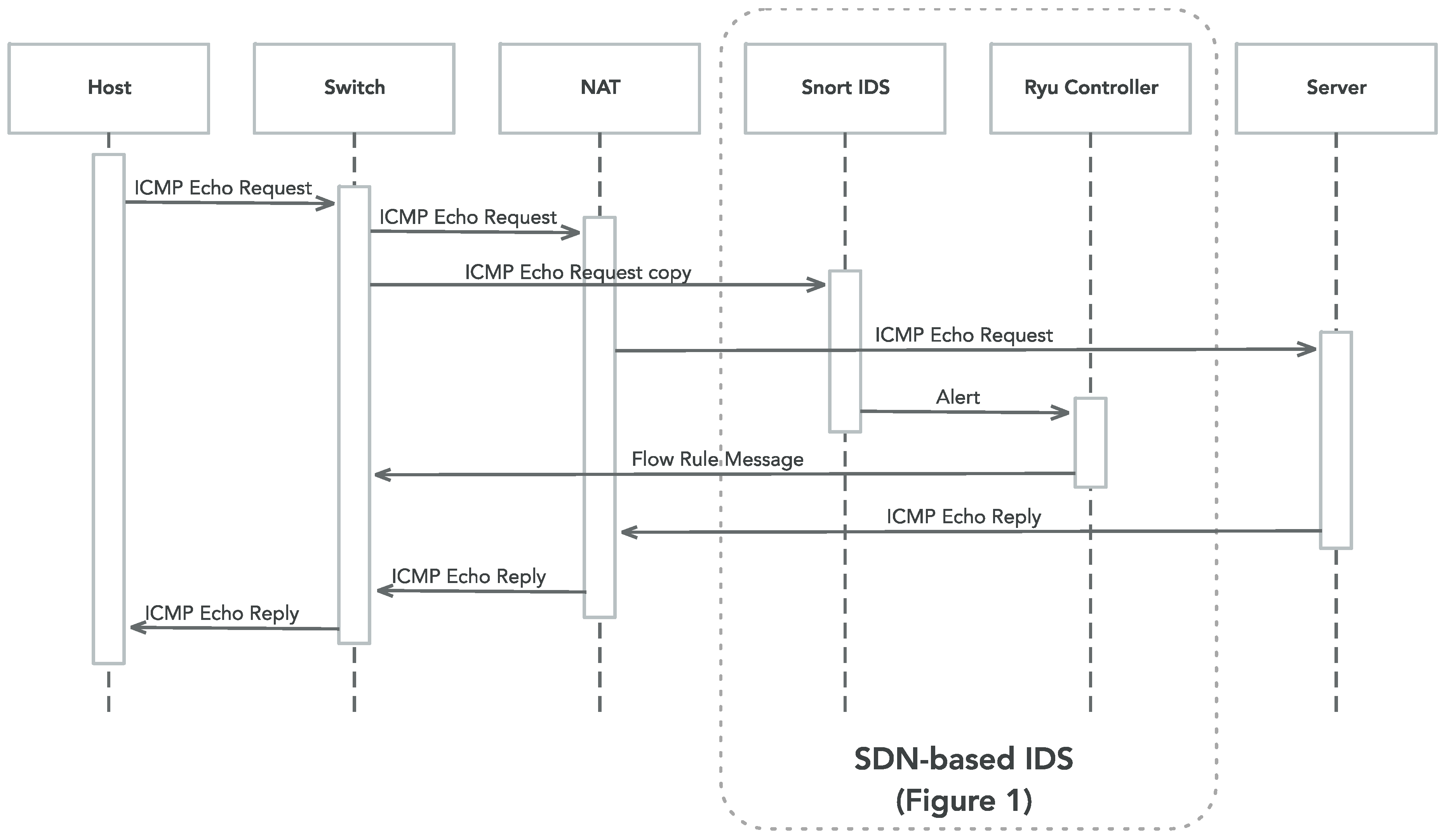
3.1. System Design
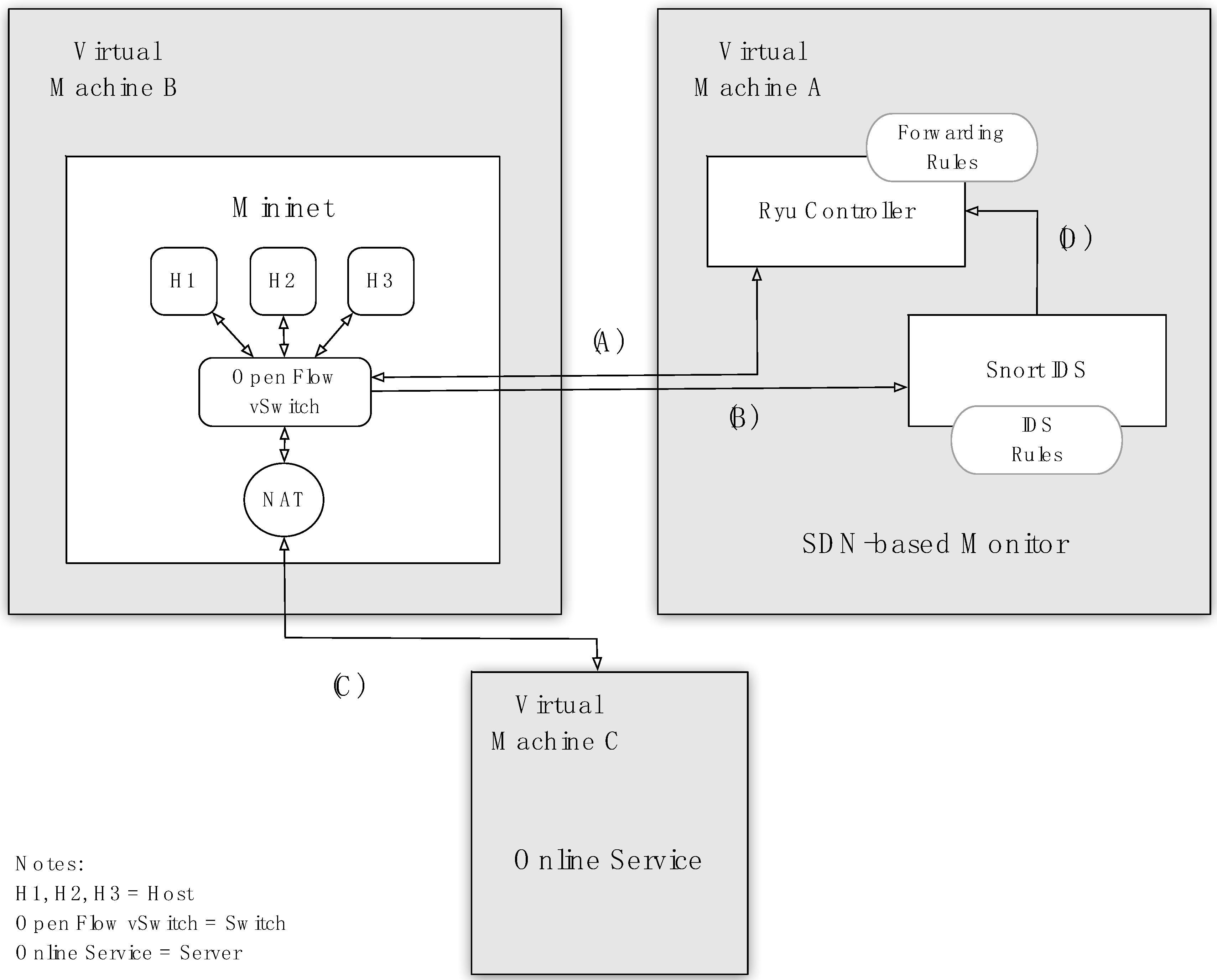
3.2. System Deployment
- Bi-directional link (A) between the OpenFlow switch and the SDN controller which exchanges control traffic between the data and control planes—the Southbound Application Programming Interface (API);
- Unidirectional link (B) between OpenFlow switch and Snort IDS which enables the switch to send all the mirrored traffic to the IDS for further analysis;
- Bi-directional link (C) which connects the local network domain (i.e., VMs A, B) to the remote service;
- Unidirectional link (D) which enables Snort IDS to notify the SDN controller (i.e., Ryu) about an ongoing DDoS attack through alert packets via the Unix Domain Socket.
4. Results
4.1. Tests’ Description
4.2. Results Presentation and Discussion
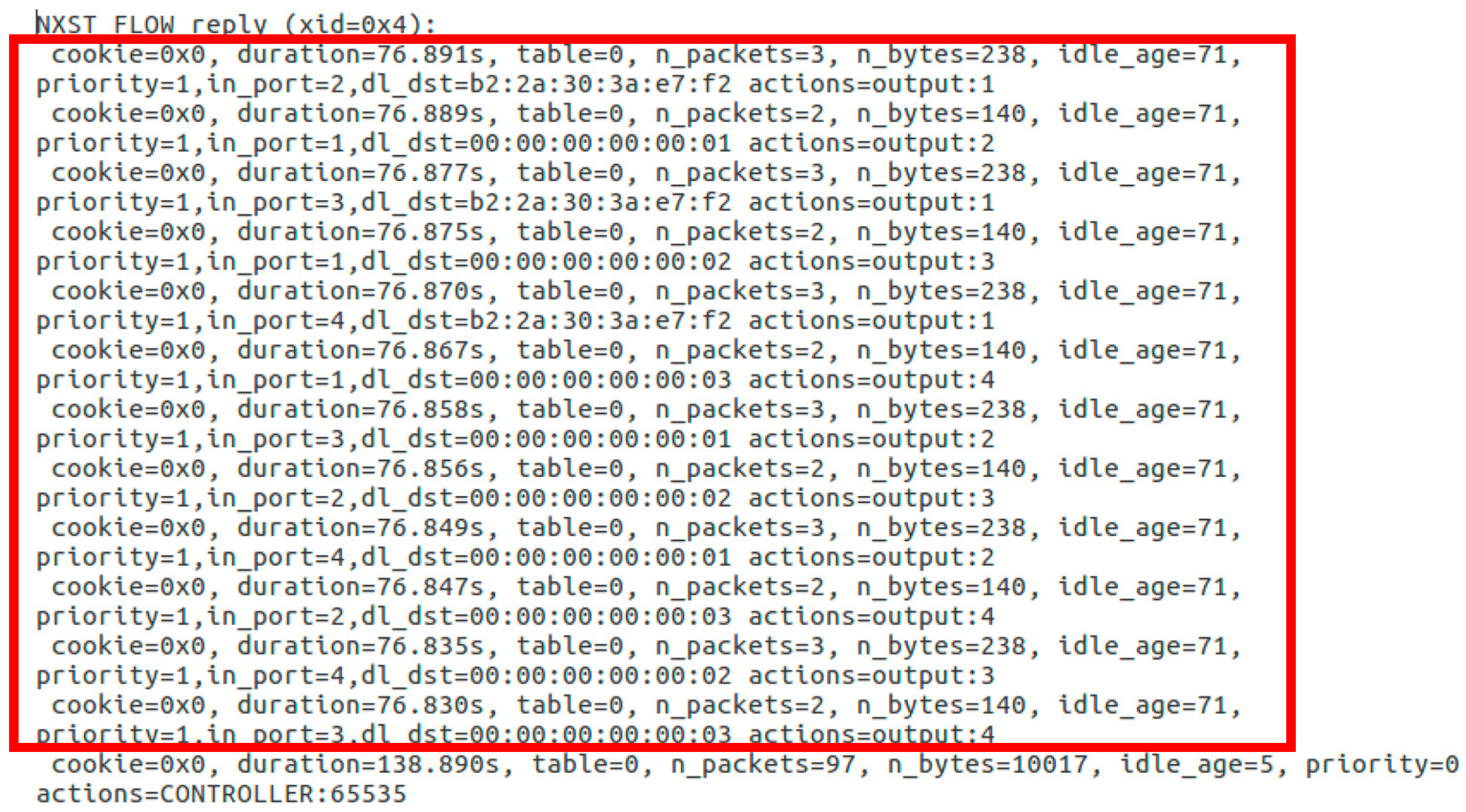
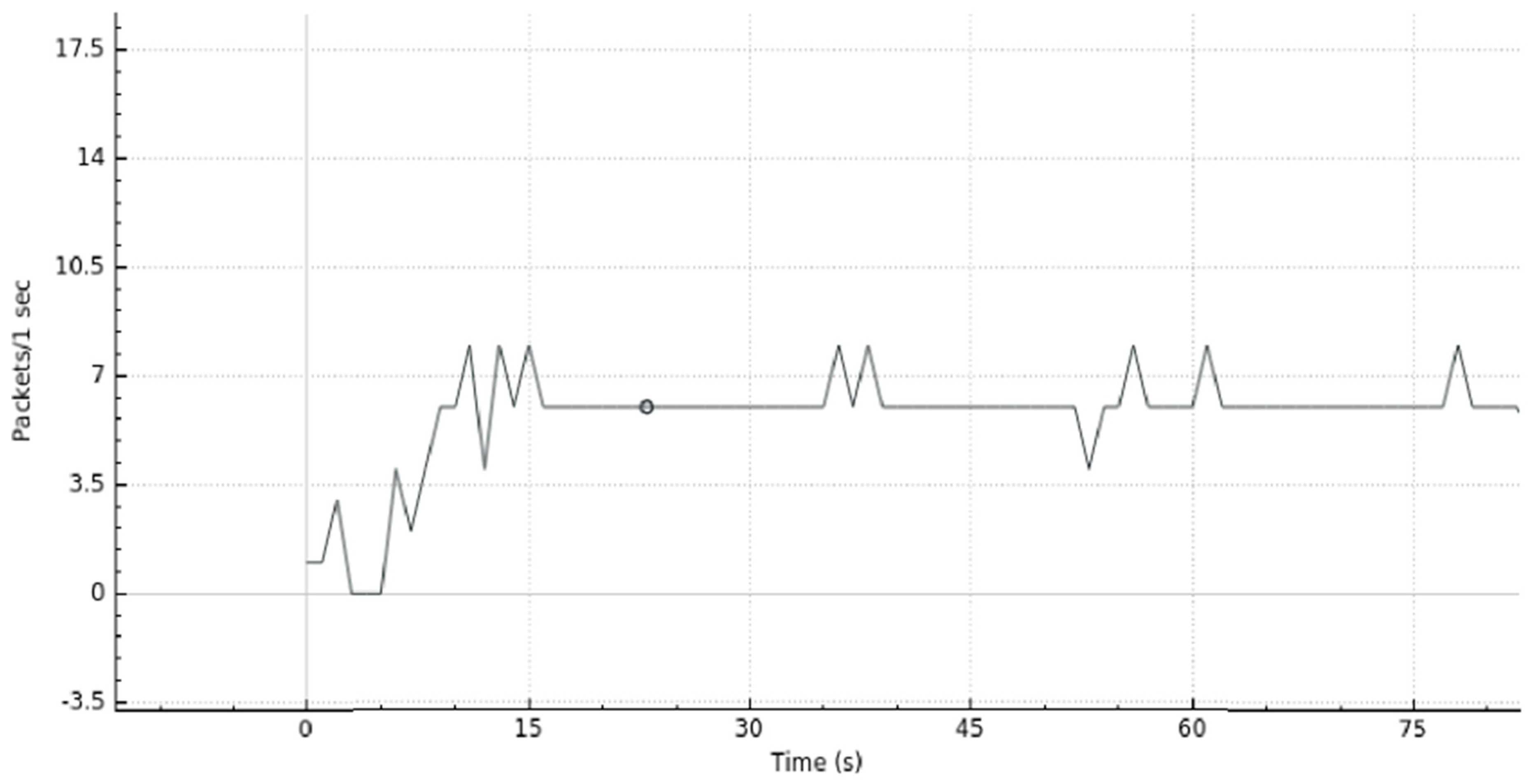
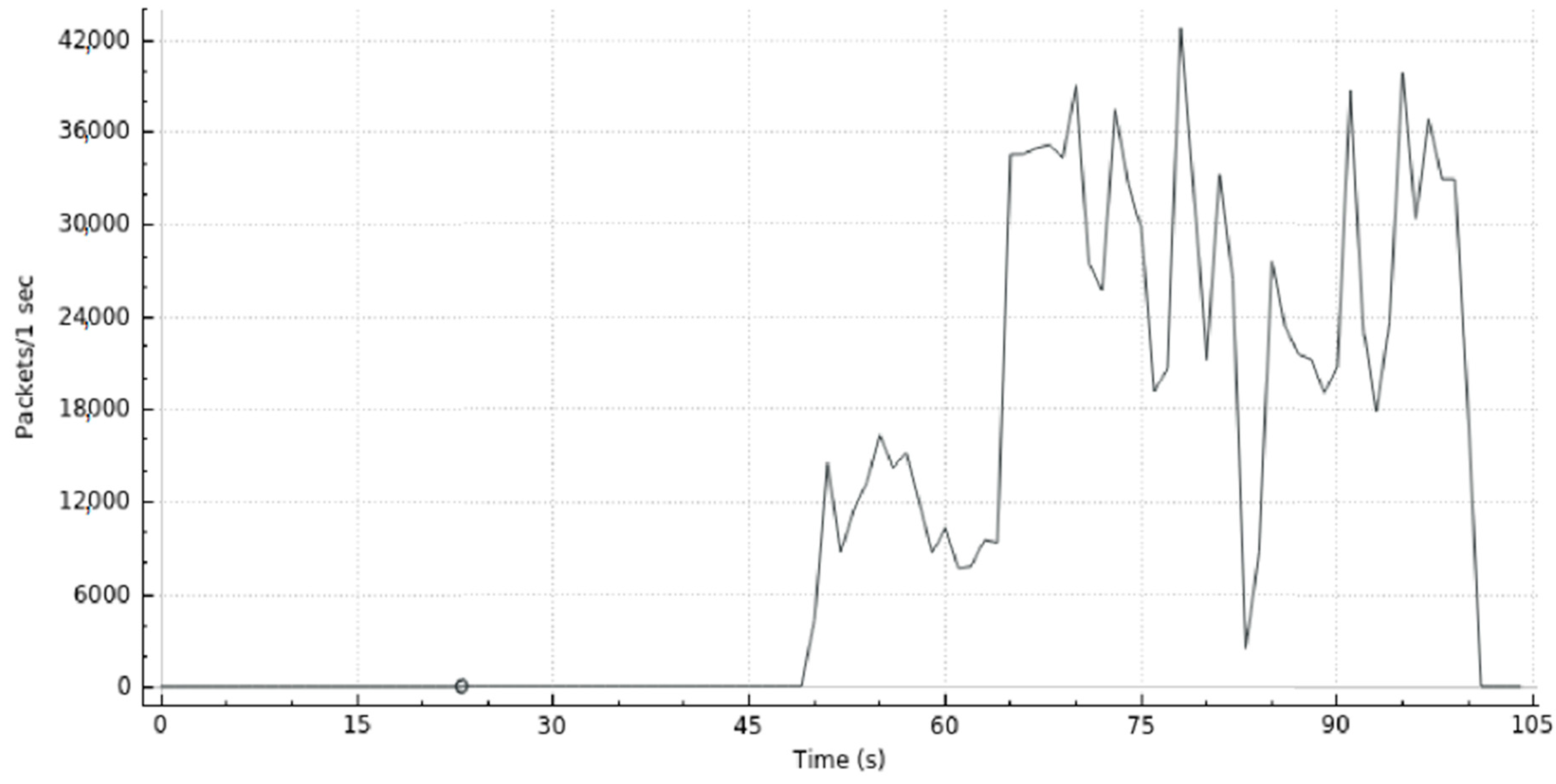
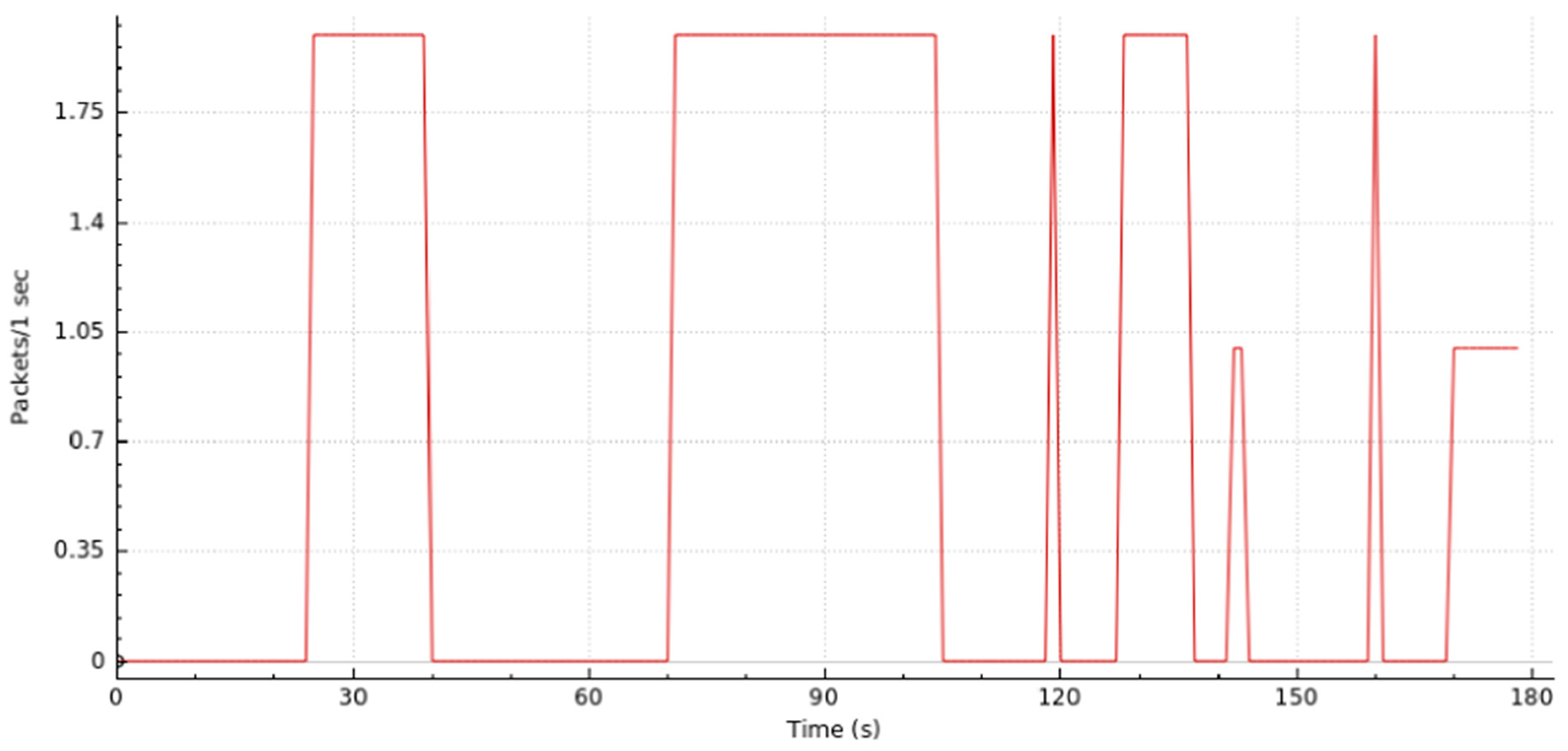
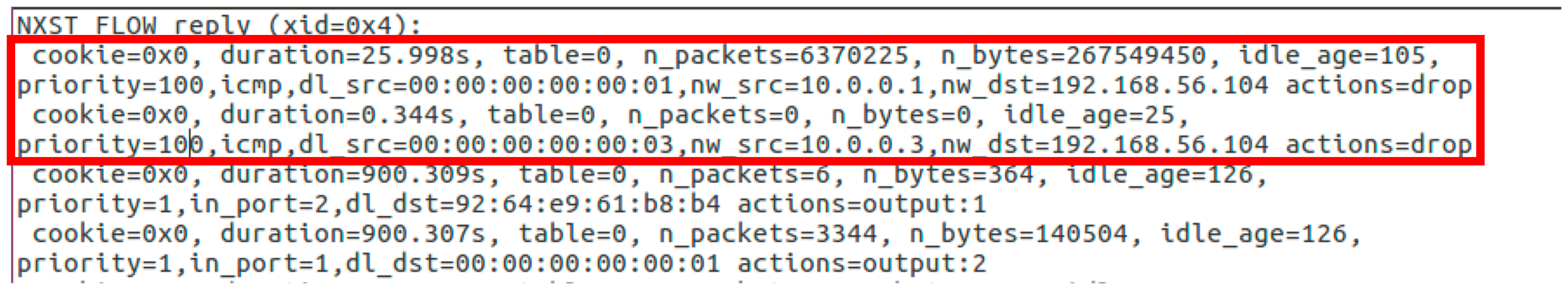
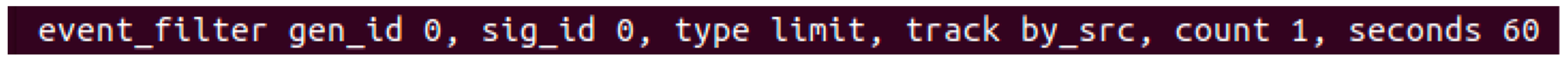
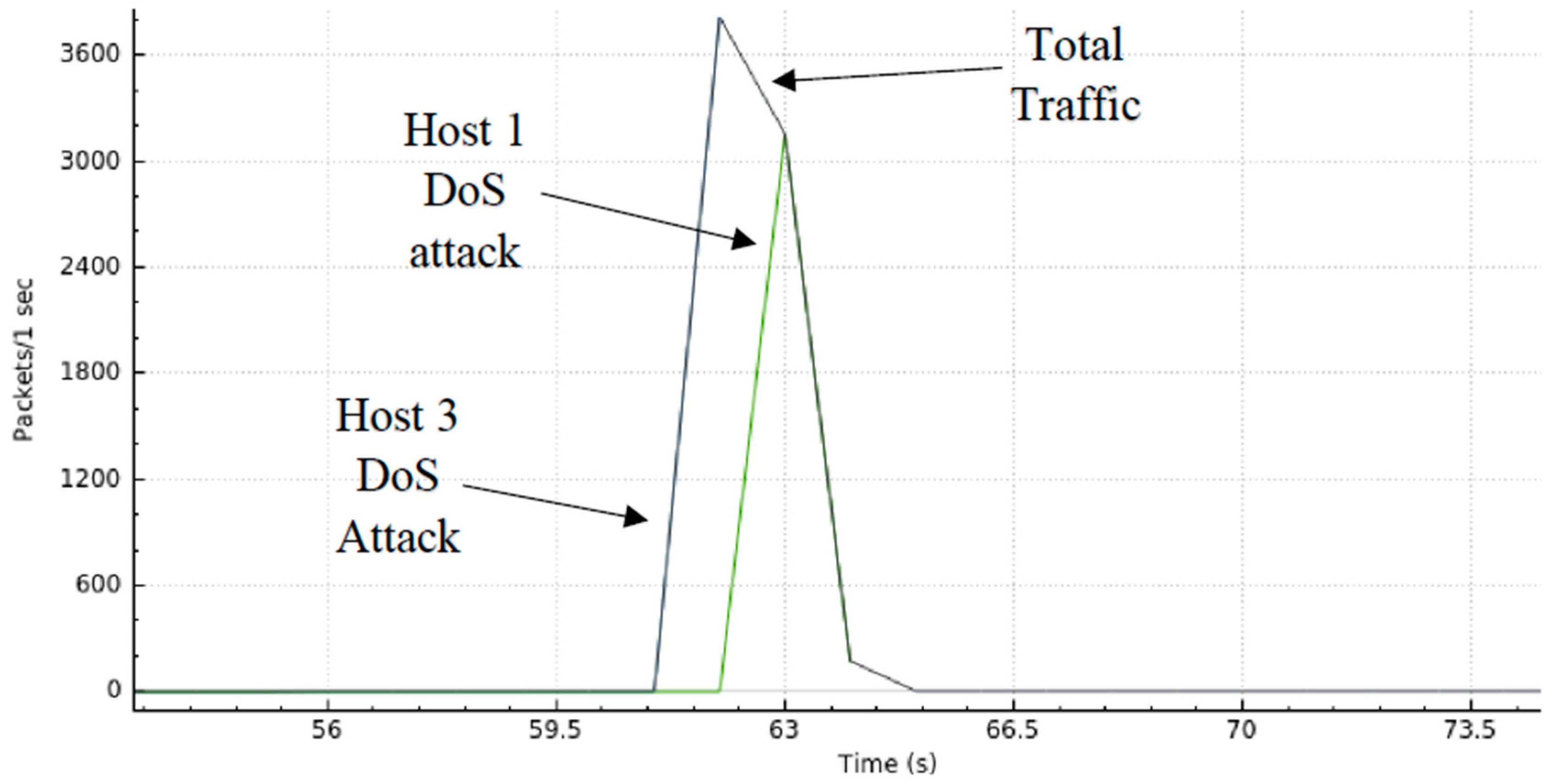
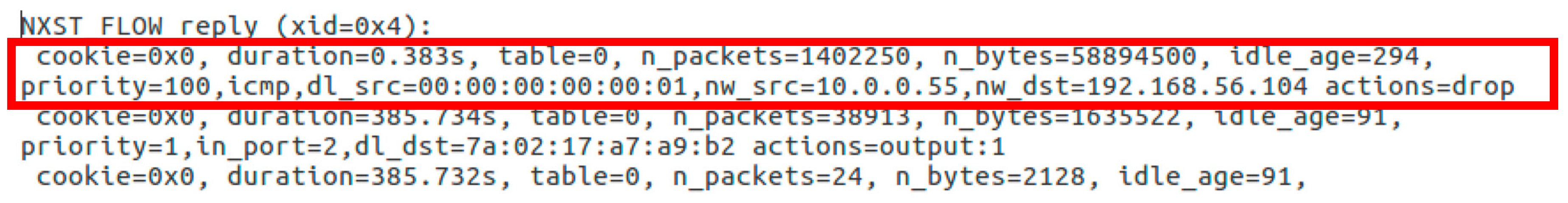
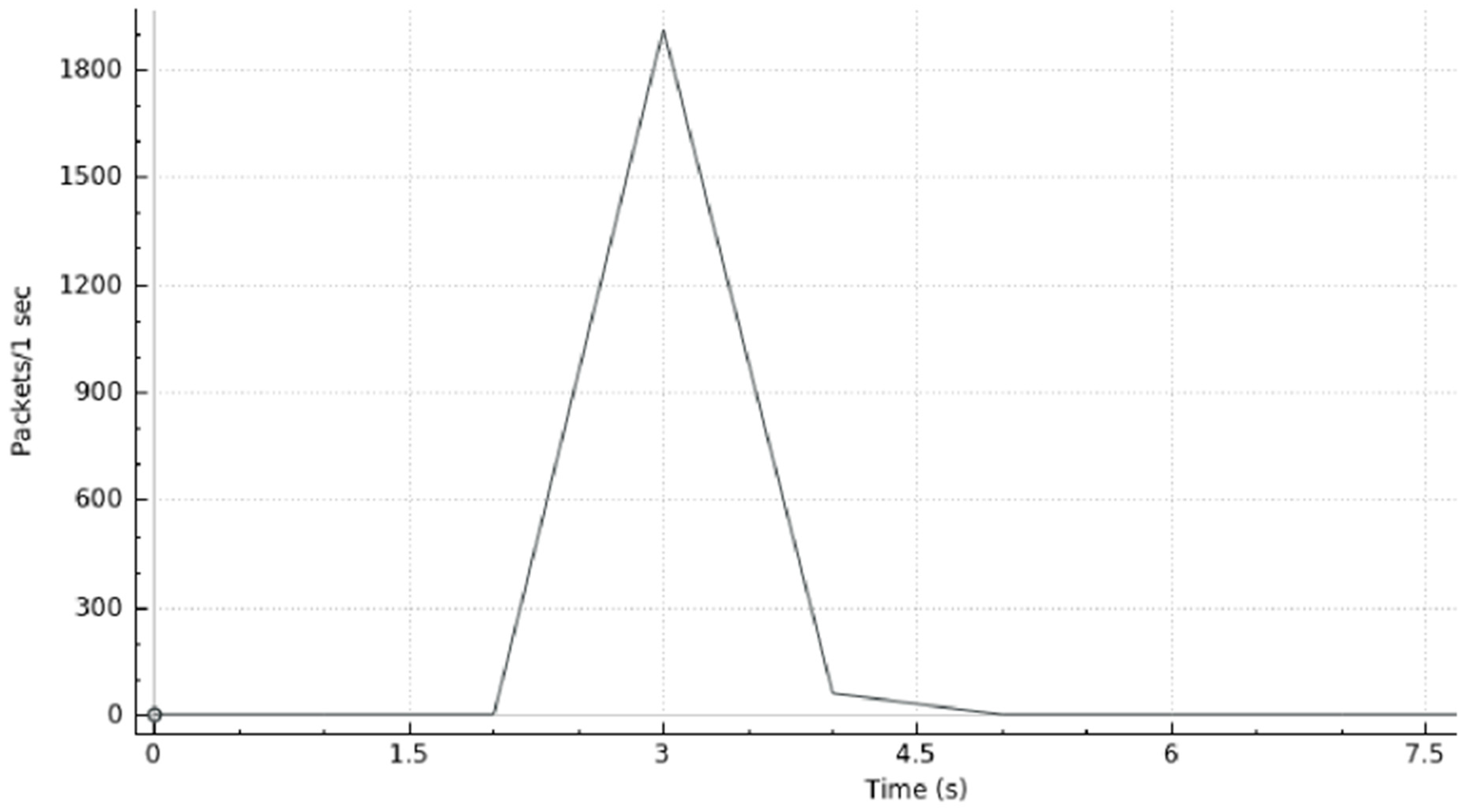
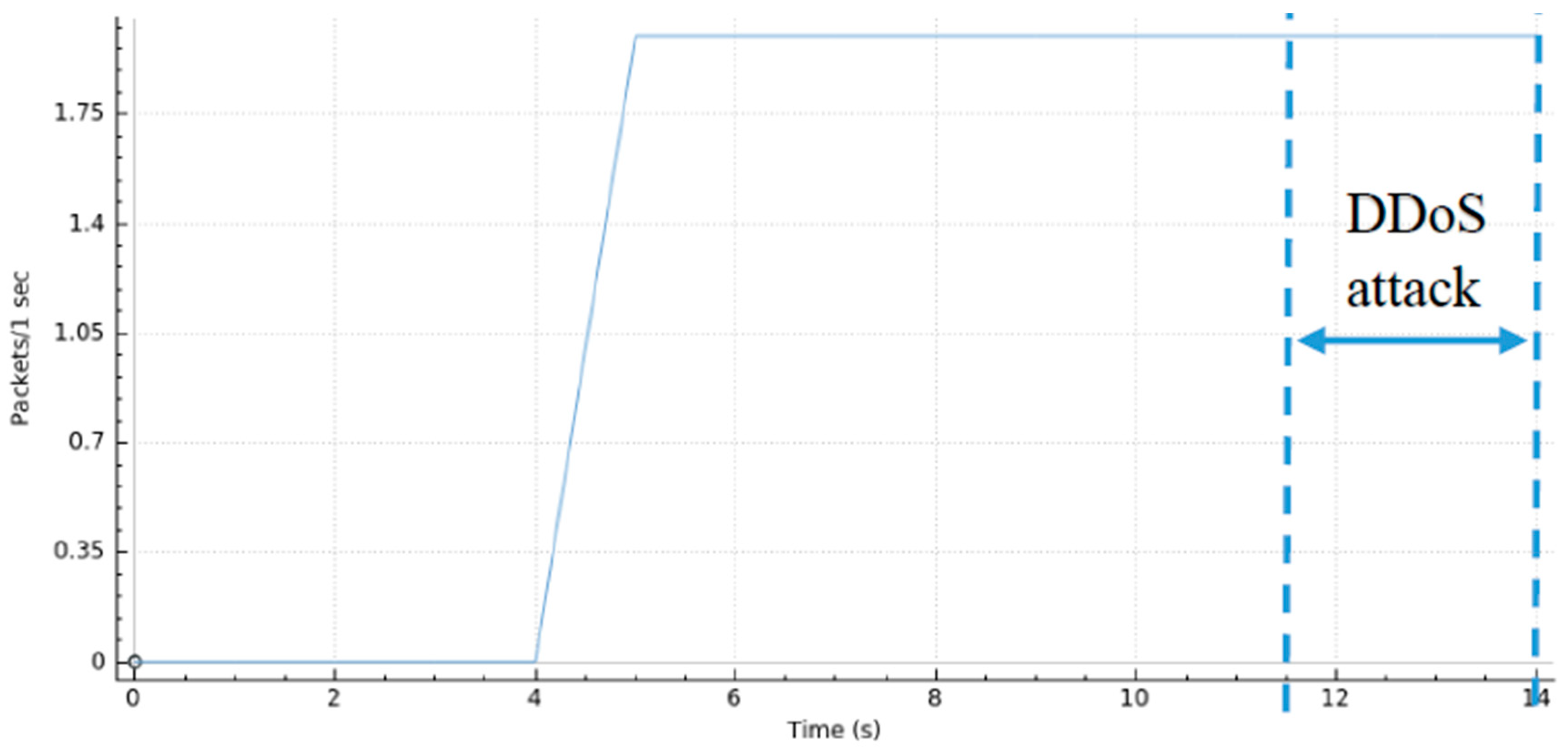
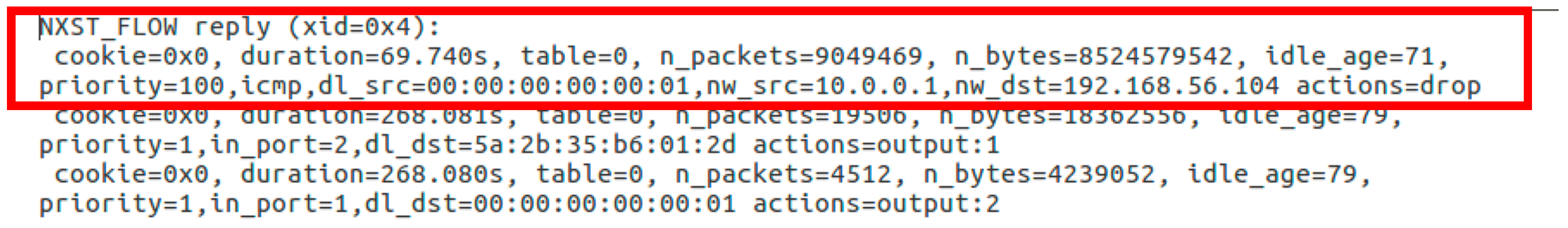
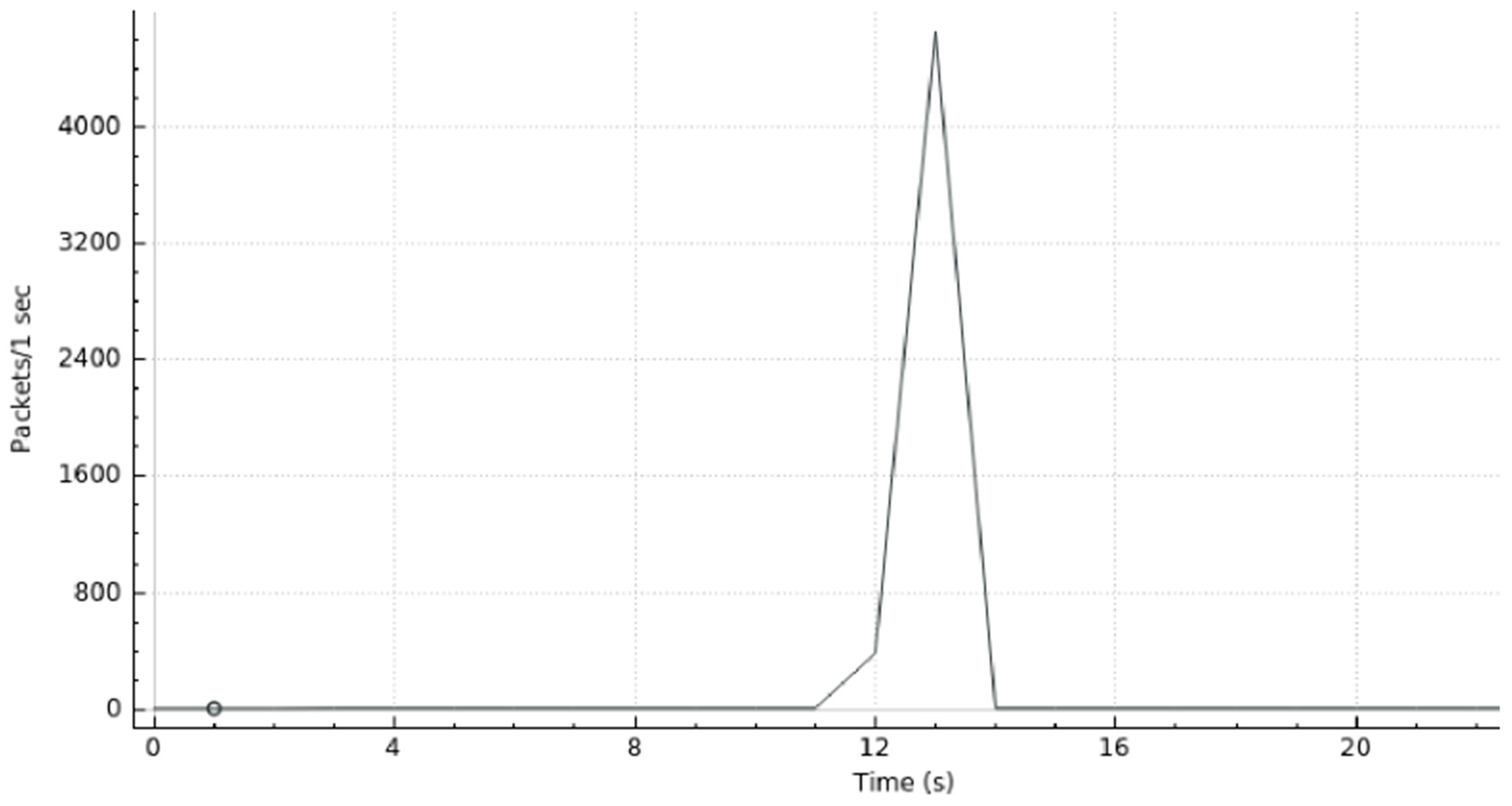
4.2.1. Scenario I
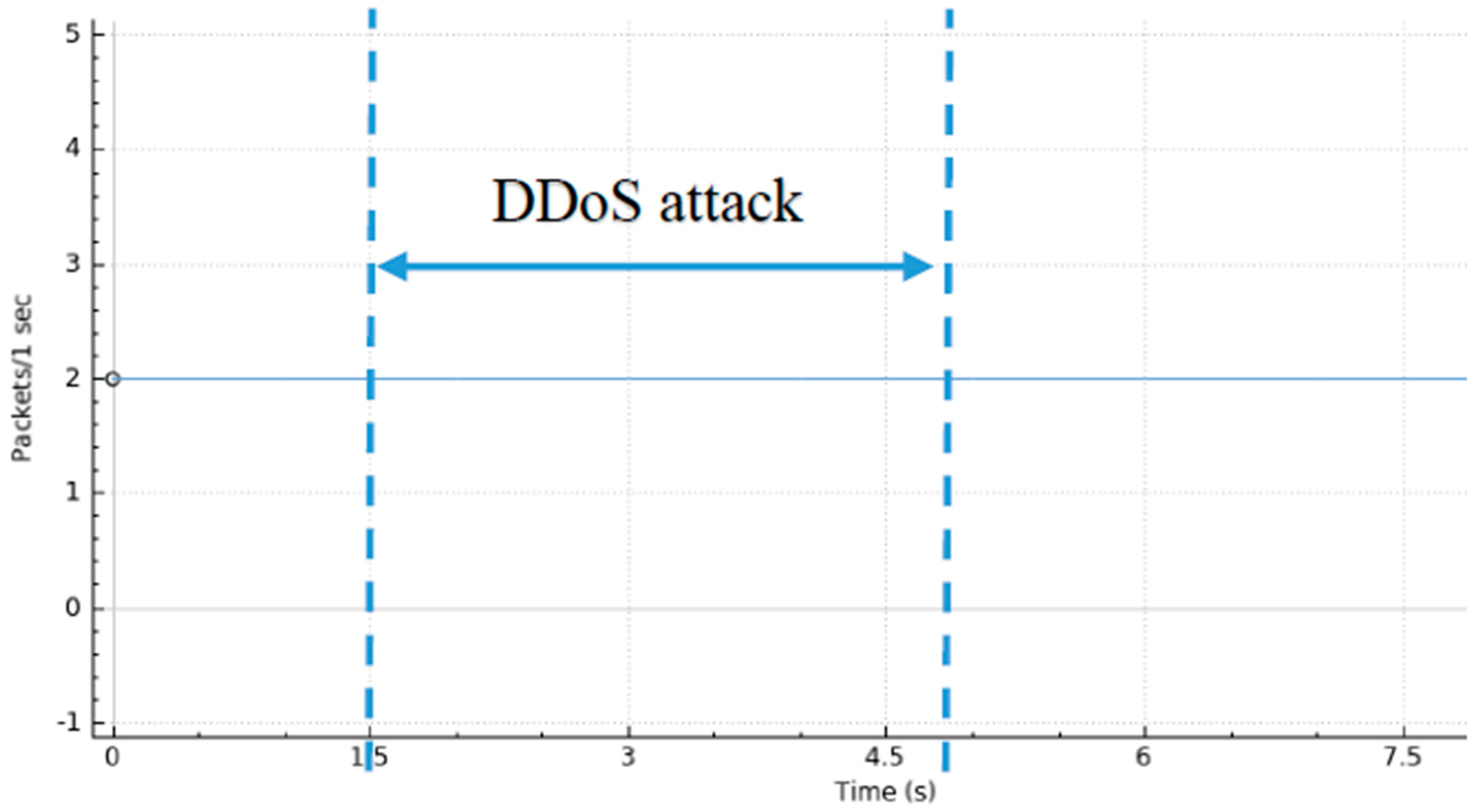
4.2.2. Scenario II
4.2.3. Scenario III
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Internet World Stats World Internet Users Statistics and 2018 World Population Stats. Available online: https://www.internetworldstats.com/stats.htm (accessed on 6 March 2019).
- Nordrum, A. Popular Internet of Things Forecast of 50 Billion Devices by 2020 Is Outdated. Available online: https://spectrum.ieee.org/tech-talk/telecom/internet/popular-internet-of-things-forecast-of-50-billion-devices-by-2020-is-outdated (accessed on 6 March 2019).
- Cisco Cisco Visual Networking Index: Forecast and Trends, 2017–2022. Available online: https://www.cisco.com/c/en/us/solutions/collateral/service-provider/visual-networking-index-vni/white-paper-c11-741490.html (accessed on 6 March 2019).
- Newman, L.H. What We Know About Friday’s Massive East Coast Internet Outage. Available online: https://www.wired.com/2016/10/internet-outage-ddos-dns-dyn/ (accessed on 6 March 2019).
- Kreutz, D.; Ramos, F.M.V.; Veríssimo, P.E.; Rothenberg, C.E.; Azodolmolky, S.; Uhlig, S. Software-Defined Networking: A Comprehensive Survey. Proc. IEEE 2015, 103, 14–76. [Google Scholar] [CrossRef]
- Shin, S.; Yegneswaran, V.; Porras, P.; Gu, G. AVANT-GUARD: Scalable and Vigilant Switch Flow Management in Software-Defined Networks. In Proceedings of the 2013 ACM SIGSAC Conference on Computer & Communications Security - CCS ’13, Berlin, Germany, 4–8 November 2013; pp. 413–424. [Google Scholar]
- Piedrahita, A.; Rueda, S.; Mattos, D.; Duarte, O. FlowFence: A Denial of Service Defense System for Software Defined Networking. J. Infect. Dis. 2016, 167, 759–762. [Google Scholar]
- Ombase, P.M.; Scholar, P.G.; Bagade, S.T.; Kulkarni, N.P.; Mhaisgawali, A. V DoS Attack Mitigation Using Rule Based and Anomaly Based Techniques in Software Defined Networking. In Proceedings of the 2017 International Conference on Inventive Computing and Informatics (ICICI), Coimbatore, India, 23–24 November 2017; pp. 469–475. [Google Scholar]
- You, X.; Feng, Y.; Sakurai, K. Packet_In message based DDoS attack detection in SDN network using OpenFlow. In Proceedings of the 2017 5th International Symposium on Computing and Networking, Aomori, Japan, 19–22 November 2017; Volume 2018, pp. 522–528. [Google Scholar]
- Kia, M. Early Detection and Mitigation of DDoS Attacks In Software Defined Networks. Master’s Thesis, Ryerson University, Toronto, ON, Canada, 2015. [Google Scholar]
- Mousavi, S.M.; St-Hilaire, M. Early Detection of DDoS Attacks against SDN Controllers. In Proceedings of the 2015 International Conference on Computing, Networking and Communications (ICNC 2015), Garden Grove, CA, USA, 16–19 February 2015; pp. 77–81. [Google Scholar]
- Xing, T.; Huang, D.; Xu, L.; Chung, C.; Khatkar, P. Snort-flow: A OpenFlow-based Intrusion Prevention System in Cloud Environment. In Proceedings of the 2013 Second GENI Research and Educational Experiment Workshop, Salt Lake City, UT, USA, 20–22 March 2013; pp. 89–92. [Google Scholar]
- Sahay, R.; Blanc, G.; Zhang, Z. Towards Autonomic DDoS Mitigation using Software Defined Networking. In Proceedings of the SENT 2015: NDSS Workshop on Security of Emerging Networking Technologies, San Diego, CA, USA, 8 February 2015; pp. 1–7. [Google Scholar]
- Chowdhary, A.; Pisharody, S.; Alshamrani, A.; Huang, D. Dynamic Game based Security framework in SDN-enabled Cloud Networking Environments. In Proceedings of the ACM International Workshop on Security in Software Defined Networks & Network Function Virtualization - SDN-NFVSec ’17, Scottsdale, AZ, USA, 24 March 2017; pp. 53–58. [Google Scholar]
- Jevtic, S.; Lotfalizadeh, H.; Kim, D.S. Toward Network-based DDoS Detection in Software-defined Networks. In Proceedings of the 12th International Conference on Ubiquitous Information Management and Communication - IMCOM ’18, Langkawi, Malaysia, 5–7 January 2018; pp. 1–8. [Google Scholar]
- Suh, J.; Choi, H.; Yoon, W.; You, T.; Kwon, T.T.; Choi, Y. Implementation of Content-Oriented Networking Architecture (CONA): A Focus on DDoS Countermeasure. In Proceedings of the 1st European NetFPGA Developers Workshop, Cambridge, UK, 9–10 September 2010; pp. 1–5. [Google Scholar]
- Braga, R.; Mota, E.; Passito, A. Lightweight DDoS Flooding Attack Detection Using NOX/OpenFlow. In Proceedings of the IEEE Local Computer Network Conference, Denver, CO, USA, 10–14 October 2010; pp. 408–415. [Google Scholar]
- Huong, T.T.; Thanh, N.H. Software Defined Networking-based One-Packet DDoS Mitigation Architecture. In Proceedings of the 11th International Conference on Ubiquitous Information Management and Communication - IMCOM ’17, Beppu, Japan, 5–7 January 2017; pp. 1–7. [Google Scholar]
- Liu, J.; Lai, Y.; Zhang, S. FL-GUARD: A Detection and Defense System for DDoS Attack in SDN. In Proceedings of the 2017 International Conference on Cryptography, Security and Privacy, Wuhan, China, 17–19 March 2017; pp. 107–111. [Google Scholar]
- Lu, Y.; Wang, M. An Easy Defense Mechanism Against Botnet-based DDoS Flooding Attack Originated in SDN Environment Using sFlow. In Proceedings of the 11th International Conference on Future Internet Technologies, Nanjing, China, 15–17 June 2016; pp. 14–20. [Google Scholar]
- Ahmed, M.; Naser Mahmood, A.; Hu, J. A survey of network anomaly detection techniques. J. Netw. Comput. Appl. 2016, 60, 19–31. [Google Scholar] [CrossRef]
- Chandola, V.; Banerjee, A.; Kumar, V. Anomaly detection: A survey. ACM Comput. Surv. 2009, 41, 1–58. [Google Scholar] [CrossRef]
- Kaur, P.; Kumar, M.; Bhandari, A. A review of detection approaches for distributed denial of service attacks. Syst. Sci. Control Eng. 2017, 5, 301–320. [Google Scholar] [CrossRef]
- Fernandez-Buglioni, E. Security Patterns in Practice: Designing Secure Architectures Using Software Patterns, 1st ed.; Wiley Publishing: Hoboken, NJ, USA, 2013; ISBN 9781119998945. [Google Scholar]
- Ryu Project Team Ryu SDN Framework. Available online: https://osrg.github.io/ryu/ (accessed on 6 March 2019).
- Cisco Snort—Network Intrusion Detection & Prevention System. Available online: https://www.snort.org/ (accessed on 6 March 2019).
- Mininet Team Mininet: An Instant Virtual Network on your Laptop (or other PC). Available online: http://mininet.org/ (accessed on 6 March 2019).
- Bhandari, A.; Sangal, A.L.; Kumar, K. Characterizing flash events and distributed denial-of-service attacks: An empirical investigation. Secur. Commun. Netw. 2016, 9, 2222–2239. [Google Scholar] [CrossRef]
- Tsai, C.F.; Hsu, Y.F.; Lin, C.Y.; Lin, W.Y. Intrusion detection by machine learning: A review. Expert Syst. Appl. 2009, 36, 11994–12000. [Google Scholar] [CrossRef]
- Mishra, P.; Varadharajan, V.; Tupakula, U.; Pilli, E.S. A Detailed Investigation and Analysis of using Machine Learning Techniques for Intrusion Detection. IEEE Commun. Surv. Tutor. 2018, 1–46. [Google Scholar] [CrossRef]
- Behal, S.; Kumar, K.; Sachdeva, M. D-FACE: An anomaly based distributed approach for early detection of DDoS attacks and flash events. J. Netw. Comput. Appl. 2018, 111, 49–63. [Google Scholar] [CrossRef]

| Arguments | Description |
|---|---|
| -i | Indicates the interface to use |
| -flood | Sends packets as fast as possible without taking care to show incoming replies |
| -1 | Uses ICMP mode |
| -a | Sets a fake IP address |
| -d | Defines the size of each packet |
| Scenario | Description | Parameters Evaluated | Hping3 Arguments |
|---|---|---|---|
| I | A Distributed Denial of Service (DDoS) attack is simulated with two malign hosts while a benign host has its normal access to the online service. | DDoS Mitigation Time; Average RTT (Round Trip Time); Packet loss. | --flood |
| II | A DDoS attack with a spoofed IP address is simulated with one malign host while two benign hosts have their normal access to the online service. | DDoS Mitigation Time; Average RTT; Packet loss. | -a; --flood |
| III | A DDoS attack with packet’s size manipulation is simulated with one malign host while two benign hosts have their normal access to the online service. | DDoS Mitigation Time; Average RTT; Packet loss. | -d; --flood |
| Test Id. | Host 1 | Host 2 | Host 3 | |||
|---|---|---|---|---|---|---|
| Average RTT (ms) | Packet Loss (%) | Average RTT (ms) | Packet Loss (%) | Average RTT (ms) | Packet Loss (%) | |
| 1 | 0.588 | 0 | 0.439 | 0 | 0.765 | 0 |
| 2 | 0.756 | 0 | 1.274 | 0 | 0.712 | 0 |
| 3 | 0.493 | 0 | 0.463 | 0 | 0.593 | 0 |
| 4 | 0.766 | 0 | 0.904 | 0 | 1.37 | 0 |
| 5 | 2.004 | 0 | 0.402 | 0 | 0.447 | 0 |
| Average | 0.922 | 0 | 0.696 | 0 | 0.777 | 0 |
| # Tests | DDoS Mitigation Time (s) | Average RTT (ms) | Packet Loss (%) |
|---|---|---|---|
| 1 | 3 | 0.619 | 0 |
| 2 | 4 | 0.547 | 0 |
| 3 | 5 | 0.561 | 0 |
| 4 | 5 | 0.484 | 0 |
| 5 | 7 | 0.767 | 0 |
| Average | 4.8 | 0.596 | 0 |
| # Tests | DDoS Mitigation Time (s) | Average RTT (ms) | Packet Loss (%) |
|---|---|---|---|
| 1 | 3 | 0.504 | 0 |
| 2 | 2 | 0.460 | 0 |
| 3 | 2 | 0.557 | 0 |
| 4 | 2 | 0.513 | 0 |
| 5 | 2 | 0.523 | 0 |
| Average | 2.2 | 0.511 | 0 |
| # Tests | DDoS Mitigation Time (s) | Average RTT (ms) | Packet Loss (%) |
|---|---|---|---|
| 1 | 3 | 0.674 | 0 |
| 2 | 2 | 0.480 | 0 |
| 3 | 2 | 0.430 | 0 |
| 4 | 2 | 0.449 | 0 |
| 5 | 2 | 0.547 | 0 |
| Average | 2.2 | 0.516 | 0 |
| Scenario | DDoS Mitigation Time (s) | AVG RTT (ms) | Packet Loss (%) |
|---|---|---|---|
| Normal Usage | - | 0.798 | 0 |
| Scenario I | 4.80 | 0.596 | 0 |
| Scenario II | 2.20 | 0.511 | 0 |
| Scenario III | 2.20 | 0.516 | 0 |
| Average | 3.07 | 0.541 | 0 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Manso, P.; Moura, J.; Serrão, C. SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks. Information 2019, 10, 106. https://doi.org/10.3390/info10030106
Manso P, Moura J, Serrão C. SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks. Information. 2019; 10(3):106. https://doi.org/10.3390/info10030106
Chicago/Turabian StyleManso, Pedro, José Moura, and Carlos Serrão. 2019. "SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks" Information 10, no. 3: 106. https://doi.org/10.3390/info10030106
APA StyleManso, P., Moura, J., & Serrão, C. (2019). SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks. Information, 10(3), 106. https://doi.org/10.3390/info10030106






