1. Introduction
Security plays an important role in payment system applications and is directly connected to customer’s credibility. An integrated circuit (IC) chip is usually chosen to provide stable security as it offers high performance, data storage, and application processing. Europay, MasterCard and VISA (EMV) are examples. For personal identification number transaction security, physical and logical security requirements are required simultaneously for full payment security. To satisfy physical security requirements, some countermeasures [
1,
2,
3,
4,
5,
6,
7,
8,
9,
10,
11,
12,
13] against side channel analysis [
14,
15,
16,
17,
18,
19] (This article is an extended version of the paper [
19] accepted in Information Security and Cryptology (ICISC) 2017). The security of the financial IC card protocol will also be evaluated after expanding upon a previous suggestion.) or fault injection should be employed. Alternatively, there are some payment system applications that are only applied in their domestic markets. In the Republic of Korea, a specific payment system [
20] is employed when using a credit or debit card. Specifically, the authentication protocol below (
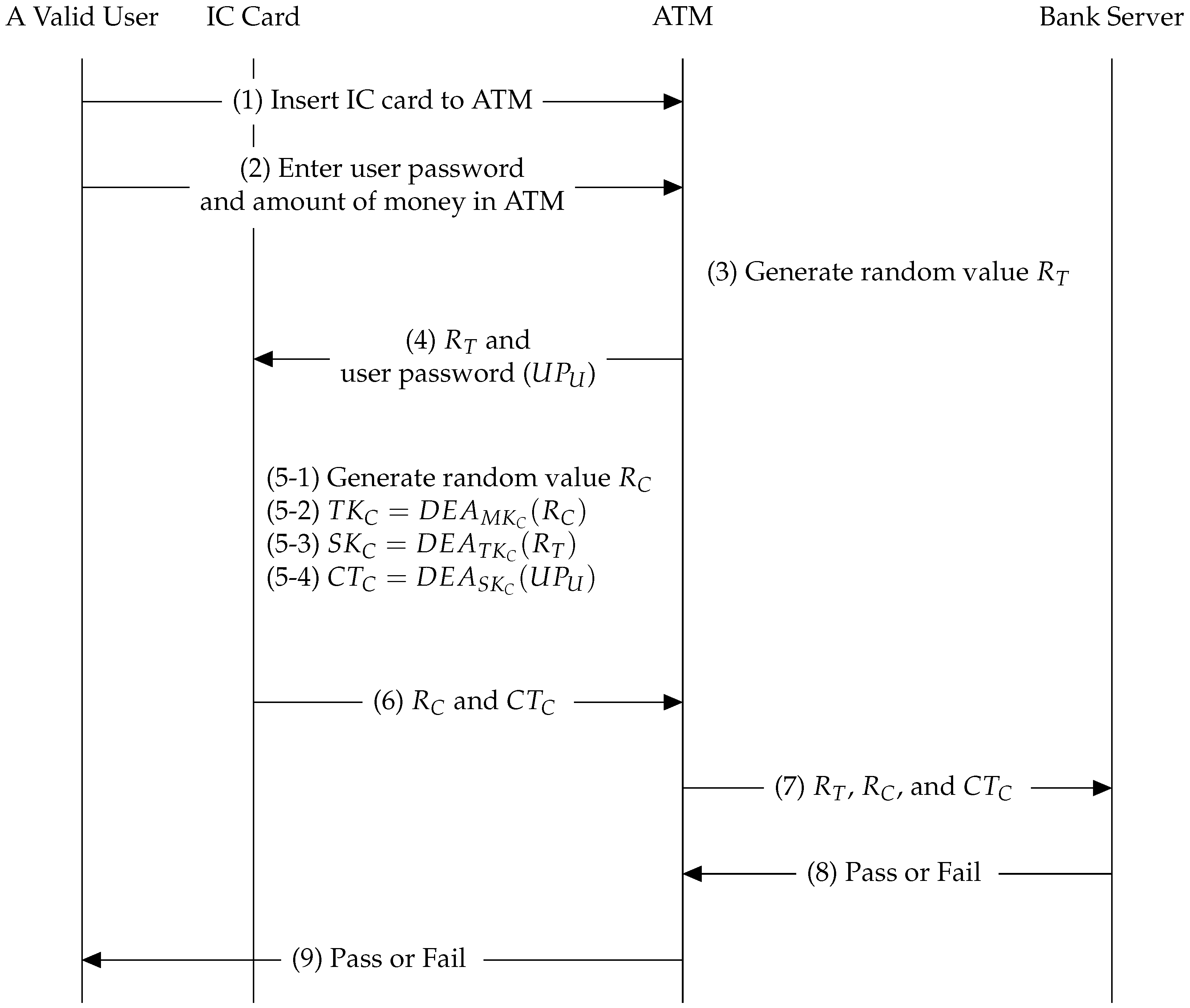
Figure 1), which is called the financial IC card protocol in this paper, is carried out when withdrawing cash from an automated teller machine (ATM) in the domestic market.
Here, Data Encryption Algorithm (
) indicates block cipher SEED [
21];
indicates user password;
means that the encryption function
takes a key
K and plaintext
P as input and produces a ciphertext
C, and all inputs and outputs in the encryption function consist of 128 bits except for
. However,
is encoded to 128 bits using a padding scheme [
20]. Moreover, the subscripts
U,
C, and
T for all variables indicate user, IC chip, and ATM, respectively.
- (1)
A valid user inserts an IC card into an ATM in the baking system of the Republic of Korea.
- (2)
A valid user enters the user password and amount of desired cash through the ATM interface.
- (3)
The ATM generates a random number, , which is composed of 128 bits.
- (4)
The ATM transfers and the user password to the IC card.
- (5-1)
The IC chip generates a random value, , which consists of 128 bits, for the financial IC card protocol.
- (5-2)
In the IC chip, is encrypted to under a fixed key, , stored in the secure memory.
- (5-3)
In the same way, is encrypted to under non-fixed key generated from (5-1).
- (5-4)
Finally, is encrypted to under non-fixed key generated from (5-2).
- (6)
The IC chip passes and to the ATM.
- (7)
The bank server receives the and from the ATM.
- (8)
The bank server possesses keys and , which are identical to and , respectively. Therefore, by performing a scheme identical to (5-1)∼(5-4), it can determine the truth of this protocol.
- (9)
The ATM informs the user whether a cash withdrawal is possible or not.
For a detailed description of this protocol, refer to [
20]. In particular, the security features for the financial IC card protocol are clearly stated in Chapter I.8. This document states that there should be resilience to power analysis, timing analysis, electromagnetic leak, fault injection, TEMPEST, etc. This is due to security threats, such as the risk of IC chip duplication. There is currently only one study [
22] on the side channel leakage in the financial IC card protocol. Moreover, that study only found a single byte of round key against block cipher SEED without countermeasure, because a countermeasure was not mandatory at the time.
Our Contributions. This paper examines side channel leakage in the financial IC card of the Republic of Korea. As of 2008, financial IC chips must be resilient to state-of-the-art power analysis. However, side channel leakages have not been considered in the financial IC card protocol since 2008. Three main contributions are made by this paper. The first is that it offers the only challenge to the security evaluation of the Korean financial IC card protocol since 2008. Even though the first round key is retrieved via side channel analysis, the master key cannot be recovered in reasonable time. Therefore, the recovery logic of the master key is established. For this, a black box model (the black box model means that an adversary only knows the public information while performing the general protocol, in particular, it makes sense even if a fake ATM is employed, because a fake ATM never damages the financial IC card protocol) is fundamentally employed, i.e., it assumes that the adversary does not have knowledge of the detailed countermeasures. Therefore, underlying schemes such as first-order analysis and second-order analysis can be performed.
The second contribution is that the resilience for the state-of-the-art attack technique [
19] is investigated to evaluate the security of financial IC card protocol. Furthermore, we demonstrate that the correct key can be revealed by expanding upon the suggestion of [
19]. That is, novel combinations are found in this paper, differing from the original suggestion [
19]. Specifically, novel combinations induce that four bits of eight bits are related to second-order leakage, whereas the original combination suggested in [
19] derives only two bits of eight bits.
Finally, this study recovered the round key as well as the master key for the financial IC card protocol for the first time, although the countermeasure for state-of-the-art attack techniques should be mandatory. Consequently, the master key dedicated in the IC chip can be sufficiently recovered using our suggested method in reasonable time.
Extension. As written in the footnote of this title, this paper is an extended version of our paper [
19] presented at ICISC 2017. In our paper [
19], we demonstrated that the diffusion layer of block cipher SEED is vulnerable to our suggestion, although first-order Boolean masking and partial shuffling countermeasures are applied. Furthermore, we found a two-bit correlation between the diffusion layer and confusion layer outputs in terms of second-order leakage. We also implemented our method on simulated trace and a well-leaked board in terms of power analysis (the board is used in academic articles because the power source is well-leaked and the platform is easy to use; detailed information can be found at
http://wiki.newae.com.). However, in this paper, we show two differences compared to the previous paper [
19]. One is that we extend our previously suggested equation, as shown in the present
Appendix A. Therefore, we show four-bit correlation between the diffusion layer and confusion layer outputs rather than two-bit correlation for some special diffusion outputs (refer to Cases 2 and 5 in
Appendix A). The other is that we apply our suggestion to the latest smart card. Additionally, the adversary assumption is even a black-box model. Therefore, we propose an attack scheme of financial IC card in terms of side channel analysis as well as the recovery mechanism of the master key in this paper.
2. Preliminaries
In this section, existing knowledge regarding details of the financial IC card, a countermeasure for block cipher SEED, and the side channel analysis for block cipher SEED’s countermeasure are presented.
2.1. Known and Unknown Information on Financial IC Card Protocol
If an invalid user acquires a certain IC card, some information can be revealed without significant effort. That is, a fake ATM can be constructed by the invalid user, ignoring the bank server. In other words, a fake ATM transfers and values to the IC chip ( indicates invalid value). Moreover, a valid value is not required, as our goal is to recover the master key, not a valid value. The following summarizes the known or unknown information when a financial IC card protocol is performed by an invalid user:
Known information: , , , and
Unknown information: , , and
The important point here is that cannot be controlled by an invalid user. Due to this fact, a chosen plaintext attack cannot be applied to the financial IC card protocol. Furthermore, a non-profiled attack cannot be performed on second and third operations, because and are changed whenever this protocol is conducted. In other words, assuming a non-profiled attack, the main target is naturally the first operation. More precisely, the first round of the foremost operation is definitely the main target, since is unknown information.
2.2. Countermeasure for Block Cipher SEED
The countermeasure of block cipher SEED [
21] is analogous to that of the block cipher Advanced Encryption Standard (AES) [
23] in terms of S-box operation. However, other countermeasures are required because block cipher SEED is constructed with
and
operations. A few countermeasures to protect the
operation are suggested in [
2]. Moreover, many suggestions [
24,
25,
26,
27,
28,
29,
30,
31,
32] have been proposed with respect to the
operation.
When compared with the higher-order masking scheme in software implementation, hiding schemes, such as shuffling and dummy methods, are adequately applied to reasonable countermeasures. Furthermore, the dummy operation can sometimes be employed because the number of S-boxes is four in the G-function of block cipher SEED.
In software implementation, it is sometimes considered reasonable to combine first-order masking, shuffling, and dummy operation schemes [
11]. In particular, the application of this combination is relevant to the DPA contest [
33].
2.3. Side Channel Analysis for Countermeasure of Block Cipher SEED
A Boolean masking scheme is normally employed, since most block ciphers can be comfortably applied in this case. However, the
-th order attack theoretically allows the leakage of the master key, even though the
d-th order Boolean masking scheme is adopted. Thus, to improve security strength, the Boolean masking scheme is sometimes combined with a hiding countermeasure, such as shuffling and dummy operation. As previously stated, first-order Boolean masking, shuffling, and dummy schemes can be simultaneously selected as a realistic countermeasure, considering the time performance and read-only memory/random access memory (ROM/RAM) size. Some attacks have been proposed to evaluate the security of these countermeasures [
13,
19,
33]. In general, a single signal is shuffled to
p signals when a shuffling countermeasure is applied. Moreover, more
traces are required to retrieve the secret key in comparison to the number required in non-shuffled traces. In [
13], more
p traces were only required when performing windowing attacks. That is, the shuffling complexity was decreased to
from
p. However, there are some barriers of realistic attack in order to perform a windowing attack. After performing the windowing scheme that derives the constant size from the original trace, the points of interest should be overlapped in each trace. Therefore, sometimes numerous traces may have to be compared in terms of theoretical complexity.
3. Evaluation Methodology for the Financial IC Card Protocol
In this section, the process of evaluating the security of the financial IC card protocol is explained. The ultimate aim of this study was to retrieve the entire master key, not just a part of it. First, the evaluation system that was constructed as a fake ATM is described. Then, the analysis methodology under the black box model is explained in order to recover the whole master key.
3.1. Construction of Side Channel Analysis for Financial IC Card Protocol
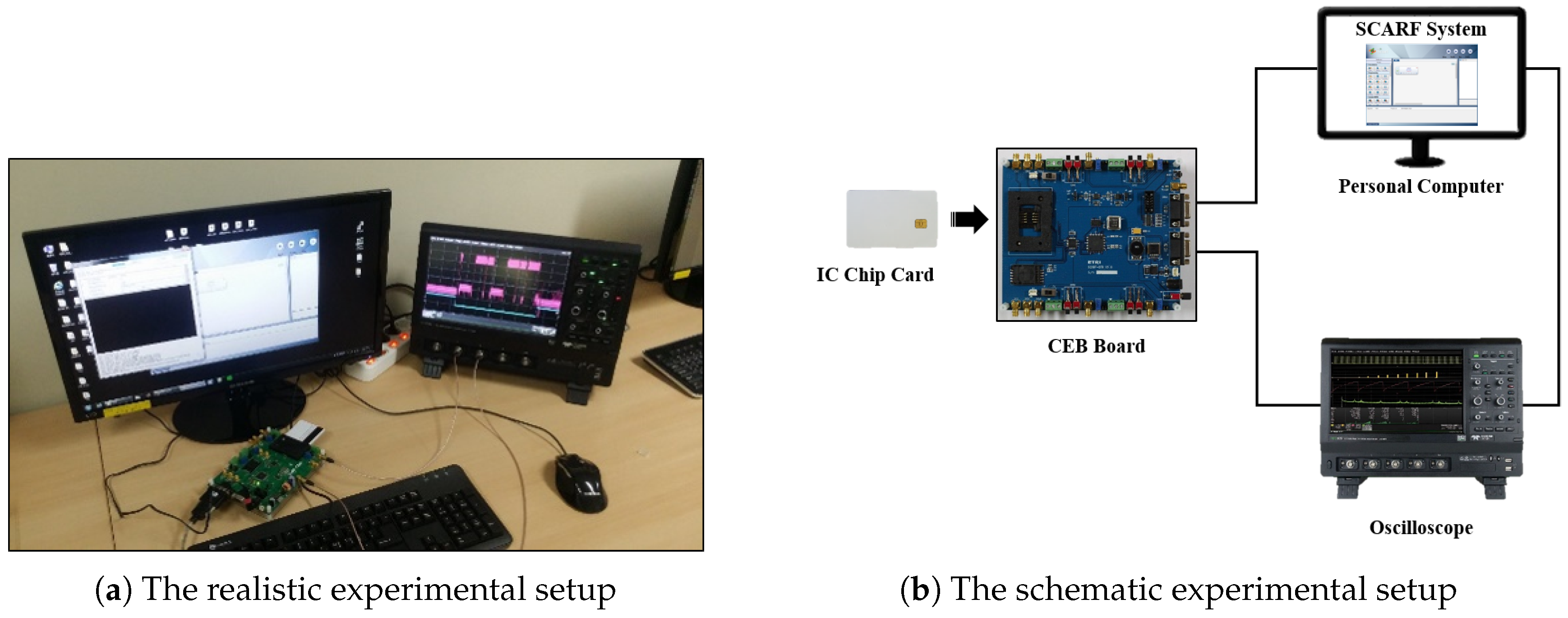
As previously stated in
Section 2.1, a fake ATM can be constructed to communicate with an IC chip card. The related experimental setup can be provided via the SCARF system (Version 4.0.0.17153 (64 bit), Electronics and Telecommunications Research Institute (ETRI), Daejeon metropolitan city, Republic of Korea) [
34].
As shown in
Figure 2, the CEB board (this board is provided by SCARF system), which plays the role of a fake ATM in the financial IC card protocol, is controlled by the SCARF system. As previously described,
and
were generated from script language in the SCARF system. That is, these values can take the desired form, between fixed or random values.
3.2. Security Evaluation Methodology of Side Channel Analysis Under Black Box Model
Before describing the security evaluation methodology, the intermediate variables were enumerated, depending on the side channel attack schemes. Basically, the intermediate variables in the first round of the foremost should be the main targets, due to the constraint of public information. In other words, the second and third s cannot be considered major objectives under a non-profiling attack, owing to protocol features. Moreover, the last round of the foremost cannot be an available intermediate variable, because is an unknown information in the usual protocol.
The master key can also be leaked. For this, two round keys should be recovered through side channel analysis, and a brute force attack is required.
3.2.1. Enumeration For Intermediate Variables
To evaluate the security against side channel analysis, the underlying scheme is performed as first and second-order analyses. Thus, the intermediate variables should be enumerated.
First-order correlation power analysis is a fundamental attack when the countermeasure is not applied. Sometimes the first-order leakage may be exposed in spite of applying the countermeasure, due to unintended phenomena, such as optimization in the computer language compiler and human error. Therefore, item 1a should be required. Additionally, the four S-boxes in the G-function should be chosen as intermediate variables to recover the single round key.
To conduct second-order correlation power analysis, pre-processing logic must be employed [
18]. In addition, two intermediate variables should be required to release the leakage of the round key. In particular, the identical masking value is usually applied to each of the S-boxes to reduce the cost of pre-computed tables when assuming the general first-order Boolean masking scheme. For this reason, item 2a is needed to disclose the masking information. Moreover, the novel leakage in connection with block cipher SEED was recently suggested in [
19]. According to this proposal, second-order leakage can be revealed with low attack-complexity, despite first-order Boolean masking and restricted shuffling countermeasures being employed, although a main target is the output of G-function. In other words, first-order Boolean masking and shuffling countermeasures can usually be utilized as reasonable countermeasures in software implementation due to certain merits, such as time performance, memory size, and security. However, in terms of block cipher SEED, side channel leakage can occur via 2b. In particular, authors in [
19] only explained that one combination of total six cases was showed.
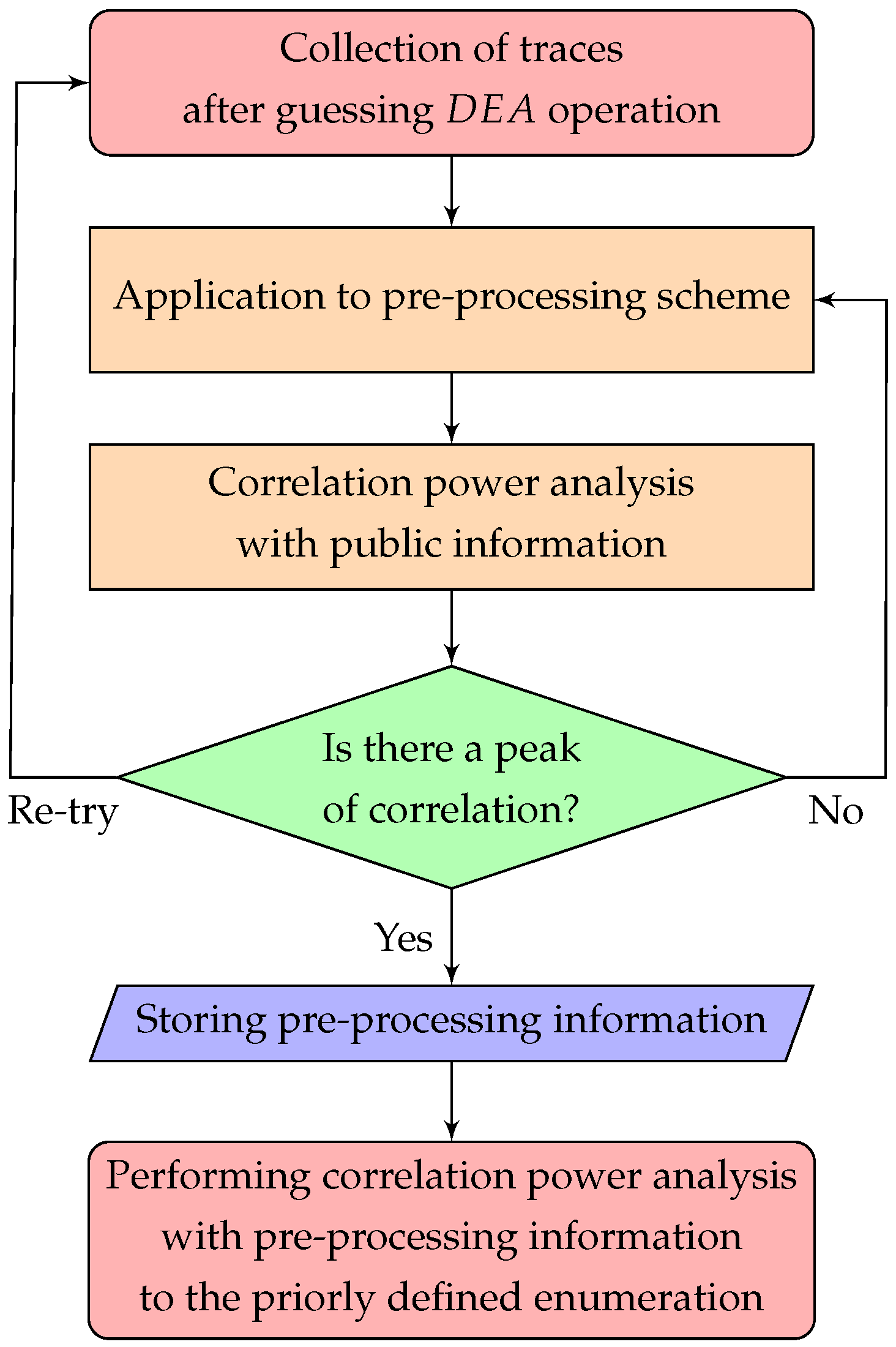
3.2.2. Security Evaluation Methodology
In this section, the evaluation methodology used to perform side channel analysis under the black box model is described. The black box model assumes that the detailed countermeasure applied to block cipher SEED in the IC chip cannot be known. The first part of the approach is to observe public information such as or , not the intermediate variable related to the secret key. This approach allows for the acquisition of two features. The first is that the operation position of block cipher SEED can be found in the whole protocol. The second is the establishment of the best solution for pre-processing information, such as compression method, compression rate, the number of traces, etc.
Before analyzing the enumeration defined in
Section 3.2.1, it should be identified whether the public information can be revealed or not. The enumeration has the potential to reveal a secret key if the public information can be disclosed in traces. Moreover, the best solution for the pre-processing scheme can be found.
Applied pre-processing scheme: none, Correlation value when performing correlation power analysis: 0.03
Applied pre-processing scheme: average compression 30, Correlation value when performing correlation power analysis: 0.15
Applied pre-processing scheme: average compression 50, Correlation value when performing correlation power analysis: 0.05
Here, the average compression N indicates that N points are compressed to 1 point by calculating the average.
The best solution is the average compression 30 scheme, because its correlation value is the highest among the three cases. Subsequently, side channel analysis can be performed using the stored pre-processing information.
3.2.3. Recovering the Master Key via Some Round Keys
The brute force attack for recovery of the master key after retrieving two round keys via side channel analysis is introduced here. Yoo et al. [
35] explains how to recover the master key when 1 round and 16 round keys are already known. In the current study, this suggestion is not sufficient, since only 1 and 2 round keys are retrieved via side channel analysis. Therefore, it is necessary to properly apply the suggestion presented in [
35] to the current context. Moreover, the recovery scheme of the master key is represented at the appropriate algorithmic level.
Note that notation of all variables used in Algorithm 1 is given in [
21,
35]. The size of all variables is 32 bits, with the exception of the variable
.
indicates the
n-th significant byte of 32-bit
X.
means from the
n-th significant byte to the
m-th significant byte. Additionally,
is the inverse of the G-function.
| Algorithm 1 Recovery of the master key under two round keys , |
| Input: 1 round key and , and 2 round key and |
| Output: Candidates for a master key |
| |
| | ▷Calculating the inverse of G-function and constant value |
| 1: | |
| 2: | |
| 3: | |
| 4: | |
| |
| | ▷Guessing a part of A and B for master key |
| 5: | for to do |
| 6: | |
| 7: | |
| 8: | if = then |
| 9: | Storing a pair |
| 10: | end if |
| 11: | end for |
| 12: | for to do |
| 13: | |
| 14: | |
| 15: | if = then |
| 16: | Storing a pair |
| 17: | end if |
| 18: | end for |
| |
| | ▷Filtering temporary keys |
| 19: | if = then |
| 20: | if = then |
| 21: | |
| 22: | Storing candidate |
| 23: | end if |
| 24: | end if |
| 25: | return Candidate |
The procedures are divided into three steps in Algorithm 1. In addition, the recovery algorithm can be performed in reverse order of generation for the round key. In particular, the first step is directly related to its reverse order, allowing it to be easily computed. Subsequently, the second step is that a part of A and B for the master key can be guessed. Moreover, and are identical to and , respectively, because the 2 round key is derived from the rotation of 1 round key. There are 256 candidates until the second step, since and depend on the size of a single byte. In the third step, a part of is equal to part of , due to the rotation in the generation of a round key. Finally, the number of candidates for the master key is less than 256.
In order to acquire only one master key, a correct single pair (, , , ) in the financial IC card protocol is required. Then, the master key can be determined by proceeding with an exhaustive attack.
4. Experimental Results
The security strength against side channel analysis was evaluated to protect against the leakage of private information. Based on
Section 3, the security can be evaluated for a specific IC card. For this, a recent IC card issued in the Republic of Korea was used. The expiration date of this specific IC card was 2023, because the issuance date was 2018. In other words, the master key dedicated to the IC chip should not be able to be revealed by any attacks, according to ChapterI.8 of [
20].
As previously stated, the public information in the collected traces was first identified, and then the pre-processing information was stored. Afterwards, security evaluation was conducted against the novel side channel analysis for the defined enumeration in
Section 3.2.1. Finally, the master key was recovered via the brute force attack defined in Algorithm 1.
4.1. Identifying the Public Information
This section elaborates upon the security evaluation methodology defined in
Figure 3, except for the defined enumeration. For this, the experimental setup described in
Figure 2 was utilized.
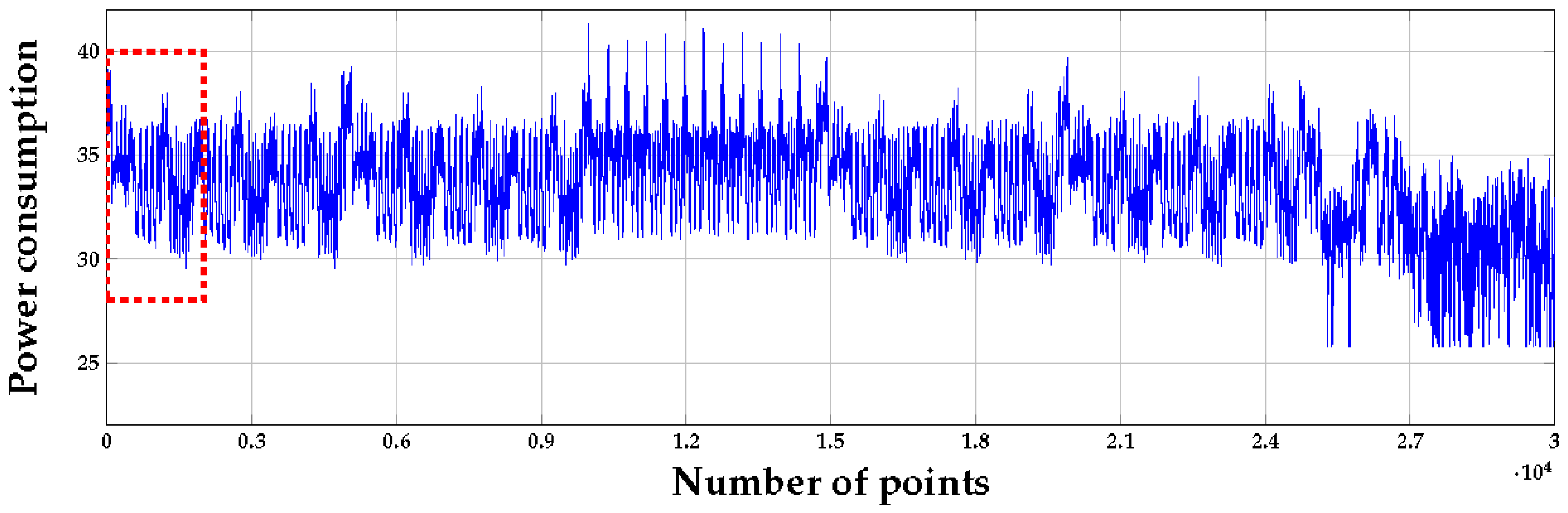
In
Figure 4, three identical areas should be identified, due to the
algorithm being computed three times in the financial IC card protocol. Therefore, when performing correlation power analysis, the plaintext or ciphertext information was searched through until the occurrence of a peak. Due to time and memory limitations, not all points can be collected simultaneously. Thus, a proportion of all points should be measured after estimating the plaintext/cipher operation. Finally, the
algorithm operation in the red box of
Figure 4 was found.
In particular, block cipher SEED was composed of 16 rounds. However, 16 identical rounds cannot be found in
Figure 5. It can be estimated that the area of dimensions
to
is divided into 12 identical areas. There are also two identical areas in the front and rear of the middle part. Therefore, it can be estimated that some countermeasures are applied to 1, 2, 15, and 16 rounds. Additionally, the plaintext information was revealed in the front part in
Figure 6. The detailed description is given in the next section.
In order to analyze the plaintext operation, the front part of the
algorithm operation was re-collected. Additionally, as shown in
Figure 3, the plaintext operation was analyzed by repeating trial-and-error to obtain the best solution.
The best solution is as follows.
The sum of squares scheme indicates that N points were squared and summed up to a single point, where N implies the compression ratio. All 16 bytes of plaintext were analyzed at the front part of the foremost operation. The alignment based on correlation was performed as a default pre-processing scheme with extensive trial-and-error. Finally, the best solution was obtained. Afterwards, the best solution was utilized to perform side channel analysis for a main target.
4.2. Security Evaluation for Financial IC Card Protocol
As shown in
Figure 3, the security for a financial IC card, including state-of-the-art attack schemes described in
Section 3.2.1, was evaluated. Before performing the side channel analysis defined in
Section 3.2.1, the applied countermeasure was estimated in block cipher SEED by investigating some power traces.
As discussed in
Section 4.1, it can be estimated that some countermeasures may be applied to only 1, 2, 15, and 16 rounds in the
operation of
Figure 5, since the middle part can be divided into 12 rounds. Additionally, 1, 2, 15 and 16 rounds were thicker than the middle part. The first round can be split into three parts, due to the identical operation being repeated three times in 1 round. Therefore, the first part of 1 round can refer to the red box in
Figure 5.
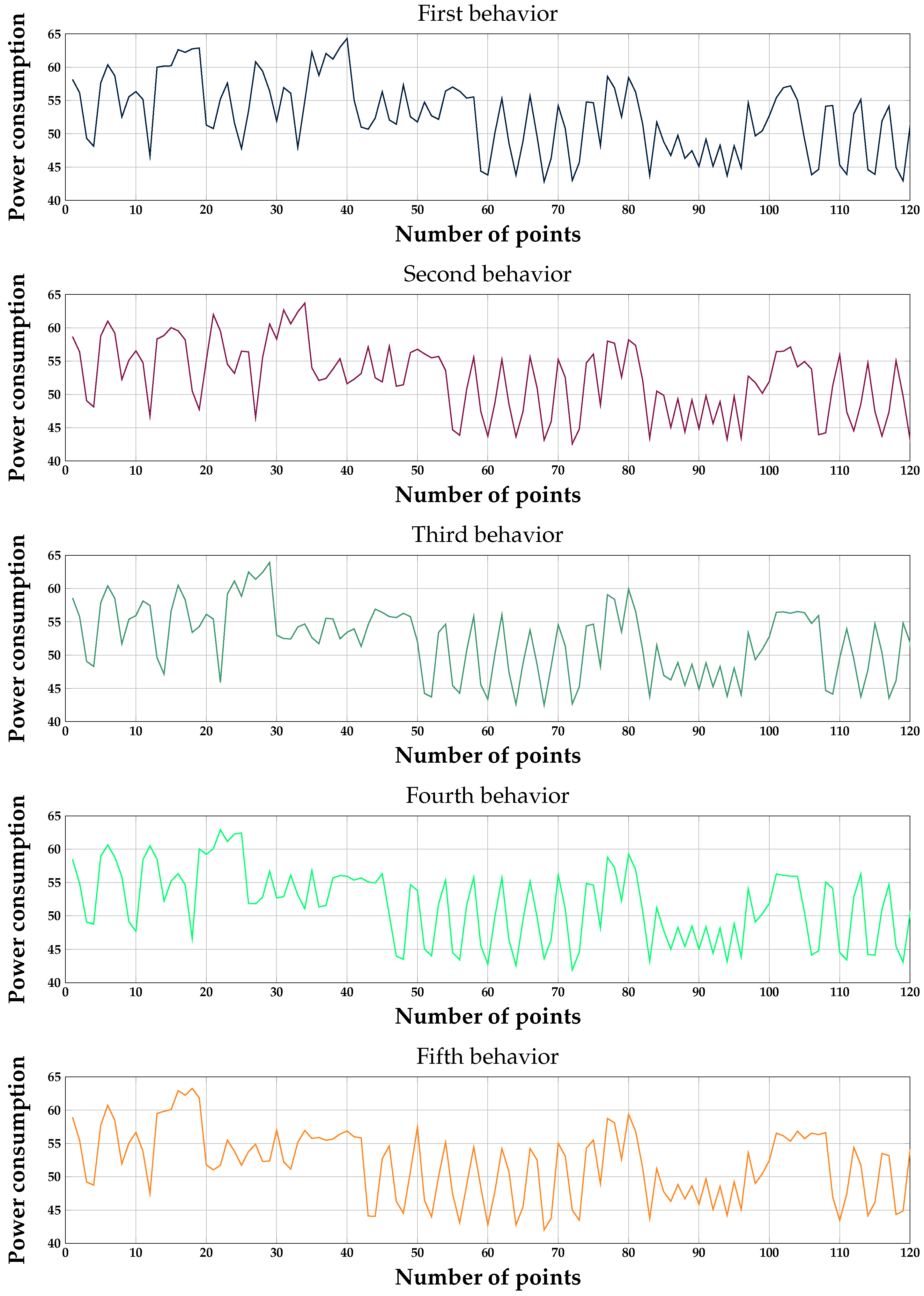
Five different behaviors were also confirmed in all the collected traces. As seen in
Figure 7, the different points are the middle part of the five behaviors. The middle part of the first behavior is composed of four negative peaks. By the same logic, the middle part of the fifth behavior consists of eight negative peaks. The second, third, and fourth behaviors also have same features. Naturally, it was predicted that these behaviors may be connected to S-box operation, since the G-function of the first round has four S-box operations. It seems that the random dummy operation may be applied to that if this computation is a real S-box operation. Two possible criteria for obtaining some leakages in order to perform side channel analysis are the back and forth of S-box operations. In other words, there are two alignment points. The result of the alignment to the back of S-box operations is shown in
Figure 7.
The aim of alignment to the front of the S-box operations is to analyze the plaintext and S-box operations. Furthermore, the purpose of the other alignment is to analyze the output of G-function and S-box operations. This is directly related to the suggestion of [
19]. To sum up, the notations are defined as below, according to the following alignment criteria:
Result of Performing Side Channel Analysis Defined in Enumeration
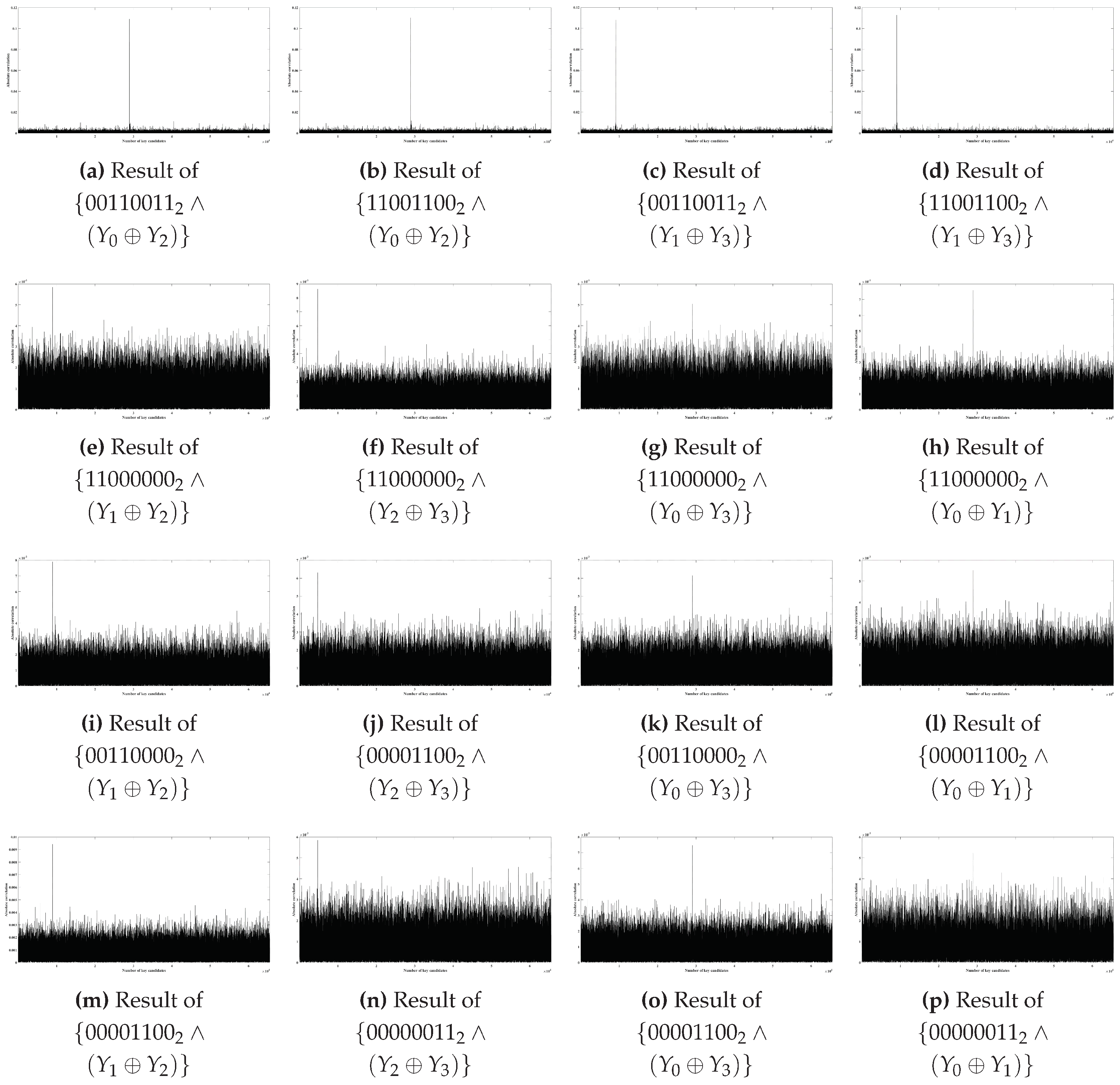
This section describes the side channel analysis performed using the defined scheme in
Section 3.2.1. As a result, we cannot identify any secret information for Alignment 1. Therefore, it is represented to all results for Alignment 2 in this section. None of the first-order leakage on the collect traces was revealed, and the second-order leakage of the combination between each of the S-boxes was also not exposed. However, by performing item 2b, two round keys can be retrieved as shown in
Table 1.
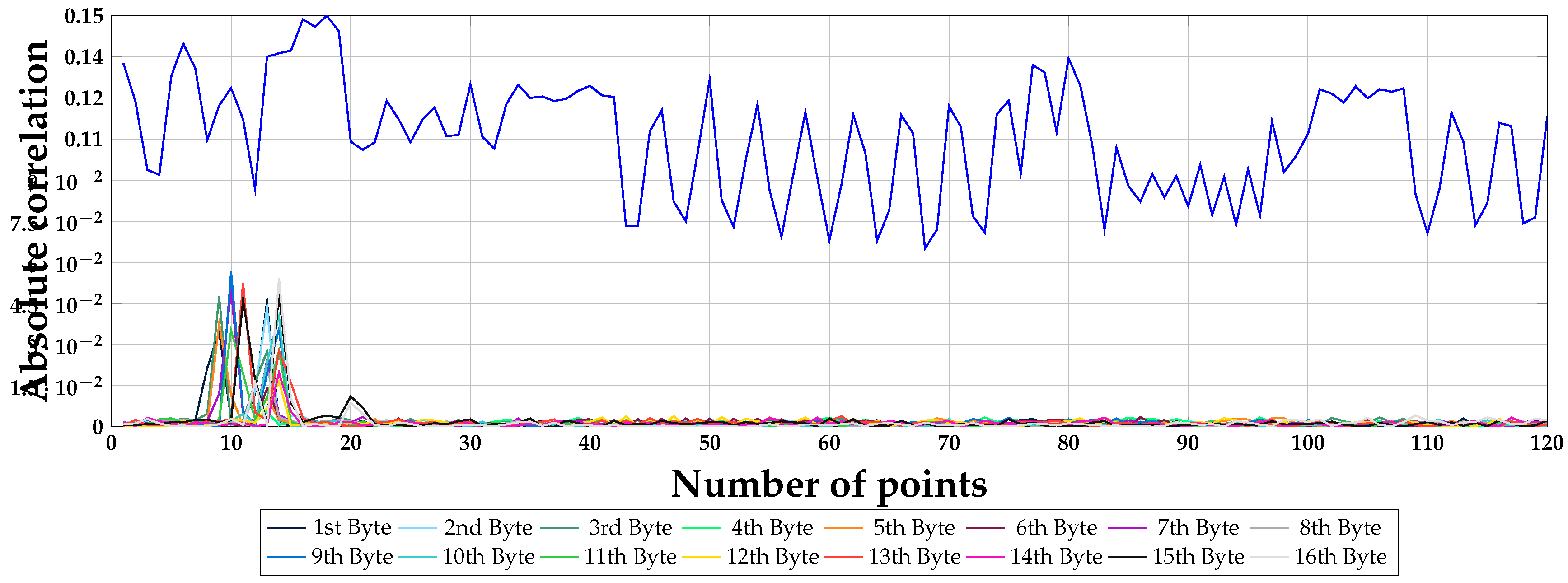
Figure 8 represents the result for the first G-function of 1 round based on all combinations in
Appendix A. Additionally, the
x-axis and
y-axis indicate the absolute correlation and key candidates, respectively. In general, the key candidate with the highest value is considered to be the correct key.
When considering all combinations, there are 20 results. As shown in
Figure 8, the result is only represented if the correct key is retrieved. As described in
Appendix A, the performance is superior to that of the previous proposal [
19], owing to the fact that results
Figure 8a–d have higher correlation. In order to analyze all combinations, 1,000,000 traces were collected. However, only 20,000 traces were required to recover the correct key in results
Figure 8a–d.
By analyzing the first G-function of 1 round, the xored key
can be acquired. Therefore, it is necessary to analyze the second G-function of 1 round, the first G-function of 2 round, and the second G-function of 2 round to obtain two round keys. All results are analogous to
Figure 8.
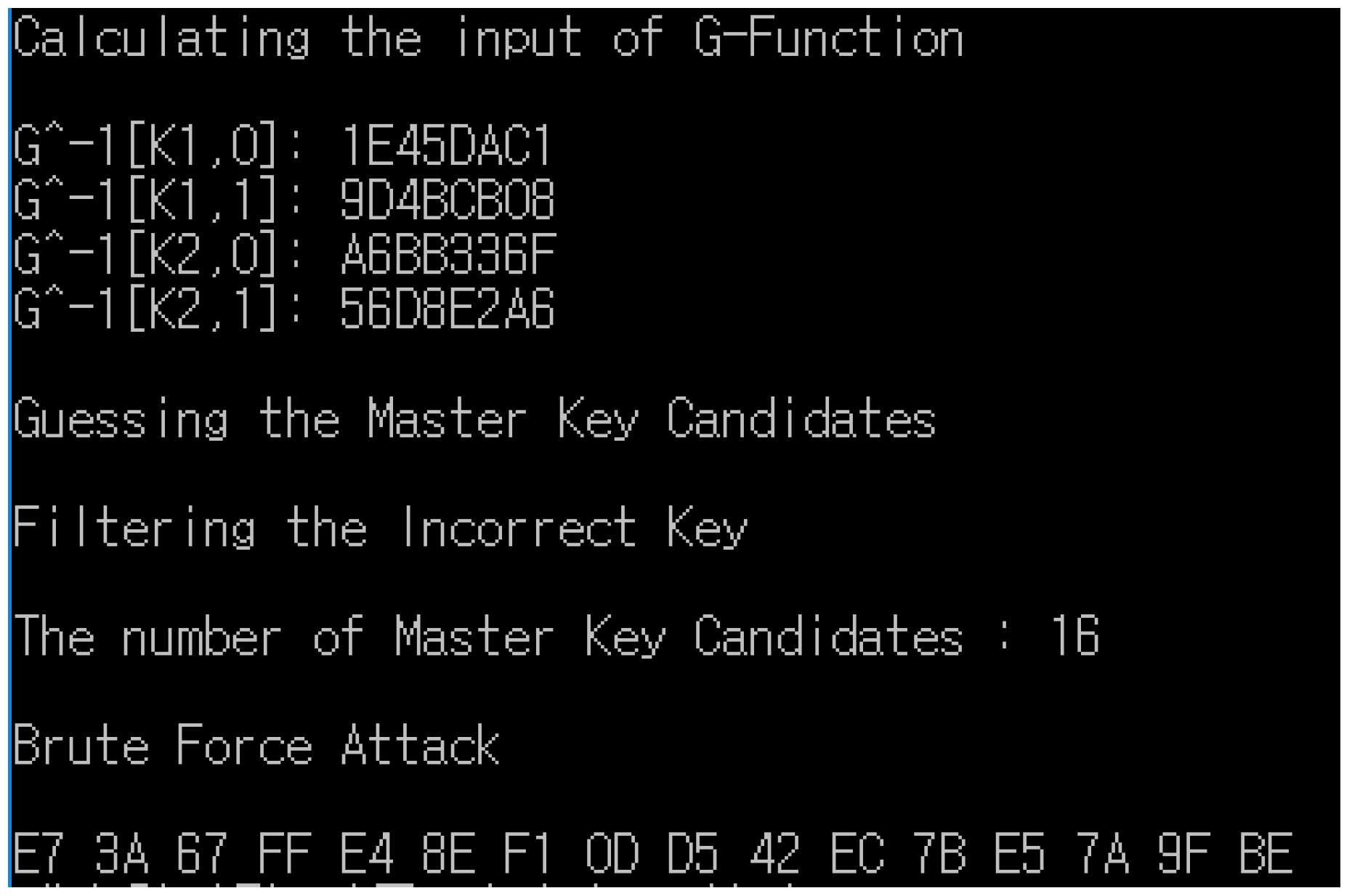
4.3. Recovering the Master Key via Two Round Keys
Two round keys were already retrieved to recover the master key. At first, the G-function in 1 round, the , is used for the G-function. Therefore, it was necessary to perform side channel analysis for the second G-function in order to recover each and . By the same logic, the second round key can be recovered.
To calculate the master key, a correct single pair should be acquired in the financial IC card protocol. Afterwards, Algorithm 1 is operated to recover a correct master key.
As mentioned earlier, and were controlled by the adversary, utilizing a fake ATM. Therefore, we set to the fixed zero value. The result of performing Algorithm 1 is as follows.
As shown in
Figure 9, the number of filtering temporary keys is 16. Finally, the analyzed master key (0xE73A67FFE48EF10DD542EC7BE57A9FBE) could be recovered by utilizing a correct pair defined in
Table 2.