1. Introduction
With the rapid increase in the amount of data and the extensive use of network applications, the problem of network attacks in the field of network security is becoming more and more serious, and discovering abnormal problems in network traffic problems is now a critical problem to be solved. Abnormal network traffic refers to the phenomenon that the current state of network traffic deviates from the normal state of network traffic. Abnormal network traffic is (more often than not) brought on through malicious network attacks [
1], such as denial-of-service attacks [
2], port scanning [
3], password blasting, far-flung control, etc., as well as network configuration errors and other exceptions. Therefore, network traffic anomaly detection [
4,
5,
6,
7,
8,
9] is a necessary function to maintain security in cyberspace.
Anomaly detection of network traffic comes from outlier detection [
10]. The purpose of outlier detection is to identify objects that are significantly different from most data objects in the dataset. Therefore, outliers can be applied to the analysis of network behavior and detect anomalies that are generated in the network.
The previous methods for detecting network traffic anomalies relied too heavily on manual feature selection, lacked adaptability, and could not directly process the original network traffic. On the other hand, in the face of massive high-dimensional traffic data, they cannot handle the dynamic data flow, and it is difficult to effectively extract key features and meet the real-time requirements of the system.
To solve the above problems, Sketch Evolution is proposed for detecting abnormal network traffic. First, the historical network traffic is analyzed to build a normal behavioral model (Profile) of the network traffic, and then calculate the deviation of the contemporary network traffic from the behavioral model of the normal network traffic. Thus, it is decided whether the network traffic is abnormal or not.
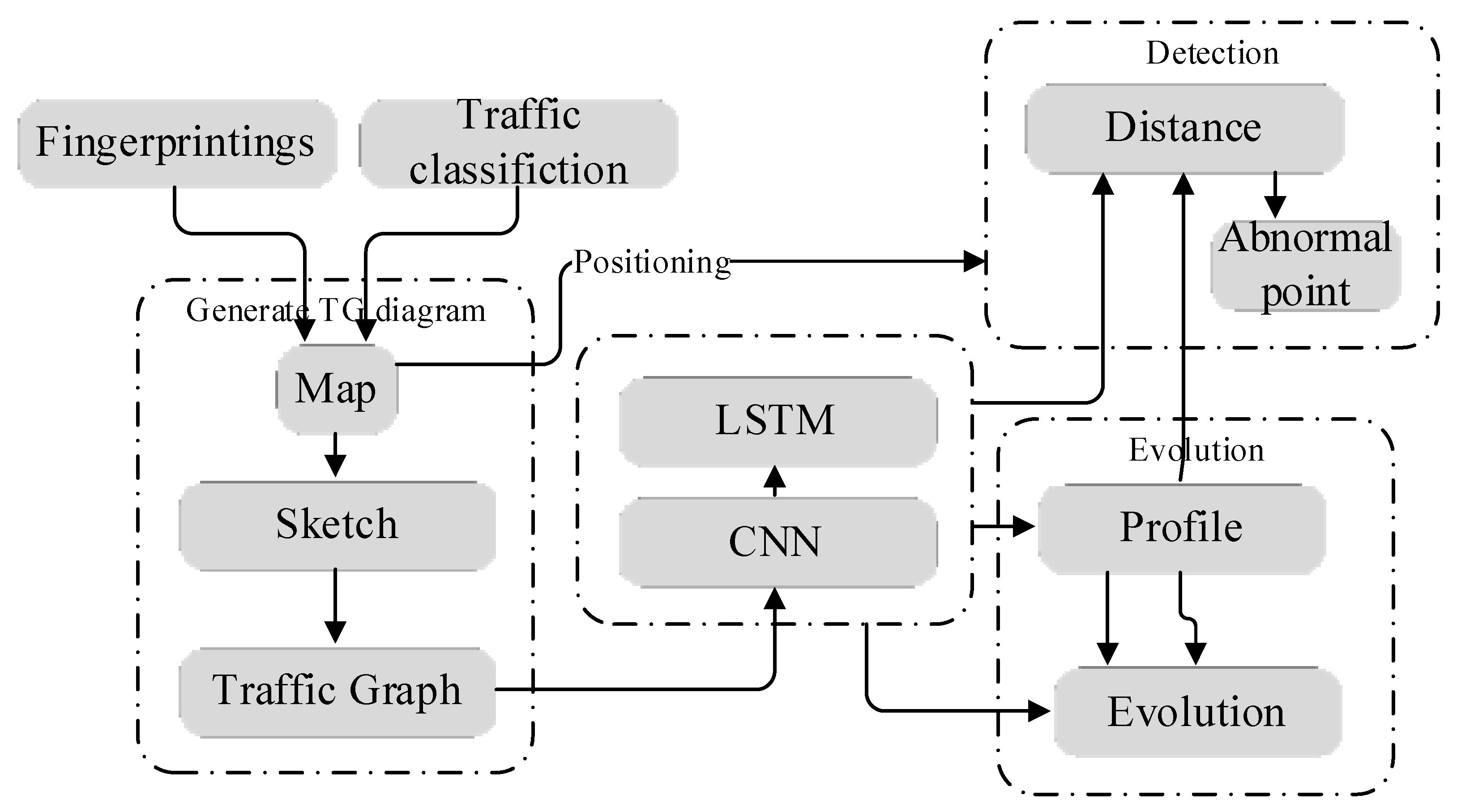
To solve the above problems, Sketch-based Profile Evolution (SPE) for network traffic anomaly detection is proposed. SPE algorithm mainly includes three parts. The first part is to analyze the historical network traffic, that is, generate the Traffic Graph (TG) based on Sketch. The second part is to build the normal behavior model (Profile) of network traffic, and use CNN and LSTM to extract the spatial and temporal behavior characteristics to generate profiles. The third part is to calculate the deviation between the current new network traffic and the normal network traffic behavior model to judge whether the network traffic is abnormal. Compare the newly obtained network data with the Profile to determine whether abnormal behavior exists. Profiles are not fixed due to the addition of new data. Profiles evolve when new data streams are generated.
The other contents of this paper are as follows: in the second part, the related work in the field of abnormal network traffic detection is presented. In the third part, we introduce the detection model, which is the generation process of the TG based on Sketch––that is, the structuring process of the network traffic, the modeling method of Profile, and the transition calculation process. The fourth part deals with the analysis of the experimental results, including the Profile analysis experiment and the network traffic volution analysis experiment. The fifth part describes the experimental conclusions and future work.
In addition, the technique proposed in this paper has established commercial co-operation with Beijing Esafenet Development Technology Co., Ltd. (Beijing, China). It has been applied in Esafenet’s DLP (Data Leakage Prevention) system to efficiently detect traffic with abnormal features in a continuous and dynamic network environment, and to provide it to the DLP system for defense measures in time.
2. Related Works
Anomaly detection is an important task in wireless network data evaluation and management, which helps to improve the intelligent management of the network and realize the optimal allocation of network resources. Network anomaly detection can be divided into four categories: statistics-based, time series-based, sketch-based, and machine learning-based network anomaly detection. The statistics and timeseries-based method is unsupervised and does not require labeling data, while the sketch and machine learning based method requires the detection system to train the detection model using labeling data, which is very time consuming but can achieve higher accuracy. In addition, the sketch-based method requires little memory in a fast and complex network environment, so it can store the characteristic information of network traffic in real time. Therefore, this paper applies the method based on Sketch for abnormal detections of network traffic.
Statistics-based methods are well suited for anomaly detection. Wang et al. [
11] proposed a network anomaly detection method (PCSS) that combines principal component analysis (PCA) and a single-stage headless face detection (SSH) algorithm. It solves the problem that the existing detection methods cannot learn regarding the spatio-temporal characteristics of the data, the classification accuracy is no longer high, and the detection time and accuracy are easily affected by redundant data in the sample. Patil et al. [
12] proposed an abnormal network traffic detection framework, which makes use of principal component analysis (PCA) with feature extraction and dimensionality reduction as the main purpose and makes use of a bidirectional generative adversarial network (BiGAN) model to detect abnormal network traffic. Ibrahim et al. [
13] propose a comprehensive entropy-based method for network traffic anomaly classification that protects in opposition to the deception of entropy detection capabilities through a novel protection mechanism. It analyzes changes in different entropy types and monitors the number of different elements in the feature distribution as a unique detection metric to achieve entropy deception protection mechanism. Then, based on multivariate analysis of entropy changes of multiple features and aggregation of complex feature combinations, an entropy-based anomaly classification rule is proposed, expanding the entropy-based anomaly detection method. Ren et al. [
14] propose an anomaly detection method based on dynamic Markov models. This method segments the sequence data using sliding windows. In the sliding window, the state of the data is defined by the value of the data, which creates a high-order Markov model with an appropriate order to balance the length of the memory attribute and keep up with the trend of the sequence. In addition, an anomaly replacement strategy is proposed to prevent the detected anomalies from affecting the model building and to maintain the continuity of anomaly detection.
Strategies based on time series consist of autoregressive and moving average model (ARMA) regression, empirical mode decomposition (EMD) transform, wavelet transform [
15,
16], instantaneous frequency analysis, etc. These methods are suitable for network traffic data processing, which can meet the quantification requirements in network traffic anomaly detection and flexibly use signal processing techniques. Yu et al. [
17] proposed a traffic anomaly detection algorithm for wireless sensor networks (WSNs) based on the improved autoregressive integrated moving average (ARIMA) model, and they improved the traditional time series ARIMA model to detect traffic in WSNs, make predictions, and make judgments about traffic anomalies. Yang et al. [
18] proposed a threshold model based on Fractional Autoregressive Integrated Moving Averages (FARIMA) to describe SCN traffic and detect anomalies. Cao et al. [
19] proposed a network traffic anomaly detection model MPTCP-EMD based on the Multipath TCP(MPTCP) network. The model combines multi-scale detection and digital signal processing theory to realize anomaly detection based on the self-similarity of MPTCP network traffic. This method uses the empirical mode decomposition (EMD) method to decompose MPTCP traffic data, and reconstructs effective signals by removing high frequency noise and residual trend terms. This model exploits the idea of a sliding window to compare the changes in the Hurst exponent of the MPTCP network under different attack conditions and decide whether an anomaly exists or not.
The Sketch is a distributed profile data structure, which is widely used in network traffic anomaly detection and can process a large amount of data in a short time. Ippoliti et al. [
20] proposed and developed a dynamic method for enhanced network flow anomaly detection. We delineate the network state during the creation of the data flow, enabling threat detection for general purposes. We describe an efficient flow augmentation method based on a count-minute sketch that provides per-flow-, per-node-, and per-network-level statistics in parallel with flow record generation. Tong et al. [
21] first proposed a general architecture on FPGA to speed up Sketch and deployed it in two widely used Sketches: Count-min Sketch and Kary Sketch. For two key network anomaly detection tasks, we propose online sketch-based algorithms: Heavy-Hitter Detection and Heavy-Change Detection. We use the proposed Sketch general architecture to accelerate these online algorithms.
Machine learning methods mainly include classification, clustering, pattern recognition, neural networks, and decision trees. Machine learning-based methods can process large network traffic data briefly and correctly via self-learning methods. Pu et al. [
22] proposed an unsupervised anomaly detection method that combines Sub-Space Clustering (SSC) and One-Class Support Vector Machine (OCSVM), which can detect attacks without any prior knowledge. Baek et al. [
23] established a new attribute that can efficiently identify anomalous events using clustering, which allows us to construct label information for individual data points called estimated samples while preserving the local neighborhood information of the connections’ features by using the Laplacian eigenmap technique. Jain et al. [
24] proposed two techniques, an Error Rate Based Concept Drift Detection and Data Distribution Based Concept Drift Detection, and investigated their effects. In addition, a sliding window-based data collection and drift analysis combined with K-Means Clustering has been used to reduce the amount of data size and improve the training datasets. We have used the Support Vector Machine (SVM) classifier for anomaly detection, and retraining of the model was initiated based solely on statistical tests. Hwang et al. [
25] proposed an abnormal traffic detection method, namely, D-PACK, which consists of a Convolutional Neural Network (CNN) and an unsupervised deep learning model (e.g., Autoencoder) that can automatically analyze the traffic patterns and filter abnormal traffic. The CNN module can automatically extract features from the original network data. Garg et al. [
26] proposed a robust anomaly detection technique, Fuzzified Cuckoo-based Clustering Technique (F-CBCT), which is divided into two stages: the hybridization of Cuckoo Search Optimization and K-means clustering. The advantages and disadvantages of some of the above references are listed in
Table 1.
The two main parts of anomaly detection are model building and anomaly detection, with model building being the most important part of anomaly detection. The core idea of anomaly detection is to compare the new data pattern with the existing behavior. If the new data deviates from the existing behavior, it is classified as an anomaly. In the existing literature, the user model is generally defined as the Profile, which is an outline or overview of the normal behavioral characteristics. The main purpose of establishing the model is to “digitize” the profile by various methods so that the algorithm can process it. Numerous methods for modeling and migration computation have been proposed in the related literature, which can be broadly classified into three categories depending on the type of method: statistical-based method, Soft Computing (SC), and distance-based method.
The statistical-based approach is based on whether the sample obeys the global distribution. The network data flow to be processed in anomaly detection varies in scale and level. Although some literatures can deal with real network traffic, they mainly take the network data of large networks as the analysis target. For example, with Campus LAN [
29], trans-Pacific backbone [
30], Abilene and GÉANT networks, CER-NET [
31], etc., such anomaly detection mainly maintains the stable operation of large networks. The detected abnormal conditions are mostly related to a part of the network area, so it is difficult to obtain fine-grained abnormal behavior for a single user or IP address. Nowadays, the anomaly detection research tends to analyze anomalies for specific targets.
SC corresponds to traditional computation, which seeks exact solutions to problems. However, in practical applications, some problems do not have exact solutions, or even if there are exact solutions, they involve a lot of computational cost. Therefore, finding a feasible solution within acceptable computational cost is the most important feature of soft computing. SC includes many intelligent computations related to artificial intelligence, such as genetic algorithms, ant colony algorithms, and neural networks. Therefore, soft computing is also a commonly used method to establish a Profile for network traffic. D’angelo et al. [
32] preprocess data to generate Digital Signature of Network Segment using Flow Analysis (DSNSF), and 1440 samples were selected, crossed, and replicated by a genetic algorithm to create a Traffic Profile to describe traffic behavior. Hamamoto et al. [
33] improved the clustering algorithm and proposed the Linear Grouping Algorithm (LGA) to cluster the samples, and then combined it with the particle swarm optimization algorithm to optimize the resampling process and obtain more stable grouping results. This grouping result is used in the next step of Single-Hop Access Profile modeling.
The distance-based method, i.e., the method based on similarity [
34], classifies anomalies by the way of determining them and performs anomaly detection by calculating the degree of similarity between Profile and sample data. In the existing literature, there are many methods to calculate the distance, but some of them are the existing methods. For example, the Mahalanobis Distance [
35], the Weighted Jaccard Distance [
36], and the KL divergence [
37], and there is also a self-defined distance function Similarity search [
38]. Wang et al. [
39] used the Affinity Propagation (AP) clustering algorithm to cluster normal behaviors and detected anomalies by calculating the Euclidean distance between the samples and normal behavior clustering. The dataset used in the experiment was comprised only of HTTP packets. Vieira et al. [
40] apply the signal processing framework to anomaly detection believing that network traffic is similar to signal. Traffic is defined as a mixture of normal traffic, abnormal traffic, and noise, and traffic is modeled, and then anomaly detection is performed using intrinsic similarity. Bi et al. [
41] used n-dimensional vectors to represent each sample, and used cosine distance to calculate the cosine angle of two vectors to represent the similarity coefficient. Ding et al. [
42] used PCA to generate the digital features of network traffic and used Dynamic Time Warping (DTW) to calculate the similarity of two sequences in computing the similarity of network traffic. DTW is an algorithm used to find the optimal queue in speech recognition.
Most of the existing anomaly detection methods are related to intrusion detection datasets, and a small fraction of anomaly detection methods based on traffic statistics cannot solve the fine-grained anomaly problem for a single IP user. The Sketch-based Traffic modeling method proposed in this paper is a distance-based method that maps the network traffic to specific areas according to the structuring process of network traffic to form a Traffic Graph (TG), so that the abnormal method can directly deal with the original network traffic and generate fine-grained features. Then, CNN and LSTM neural networks are used to extract the Profile of network traffic behavior to realize the evolution behavior modeling. The corresponding distance formula and TG are used to determine the position of outliers, and the fine-grained detection of outliers is realized. The anomaly detection model improves the existing anomaly detection and enables the direct processing of the original network data, but the analysis of the type of anomaly requires further research.
3. Sketch-Based Profile Evolution for Network Traffic Abnormal Detection
The difficulty in analyzing network behavior lies in modeling dynamic traffic behavior. Traffic is characterized by few attributes, a large amount of data, a large number of human influence factors, and no typical behavior characteristics. The existing anomaly detection has many characteristics, but is built on a specific system. When the scope is extended to the actual communication data in the network, anomaly detection cannot be applied. Based on the analysis of the most common network packets in the network, this paper generates a Profile of user behavior through the network traffic structuring process, including Profile Evolution to describe the change of user behavior. Finally, the anomaly detection is completed by calculating the offset.
3.1. Detection Model
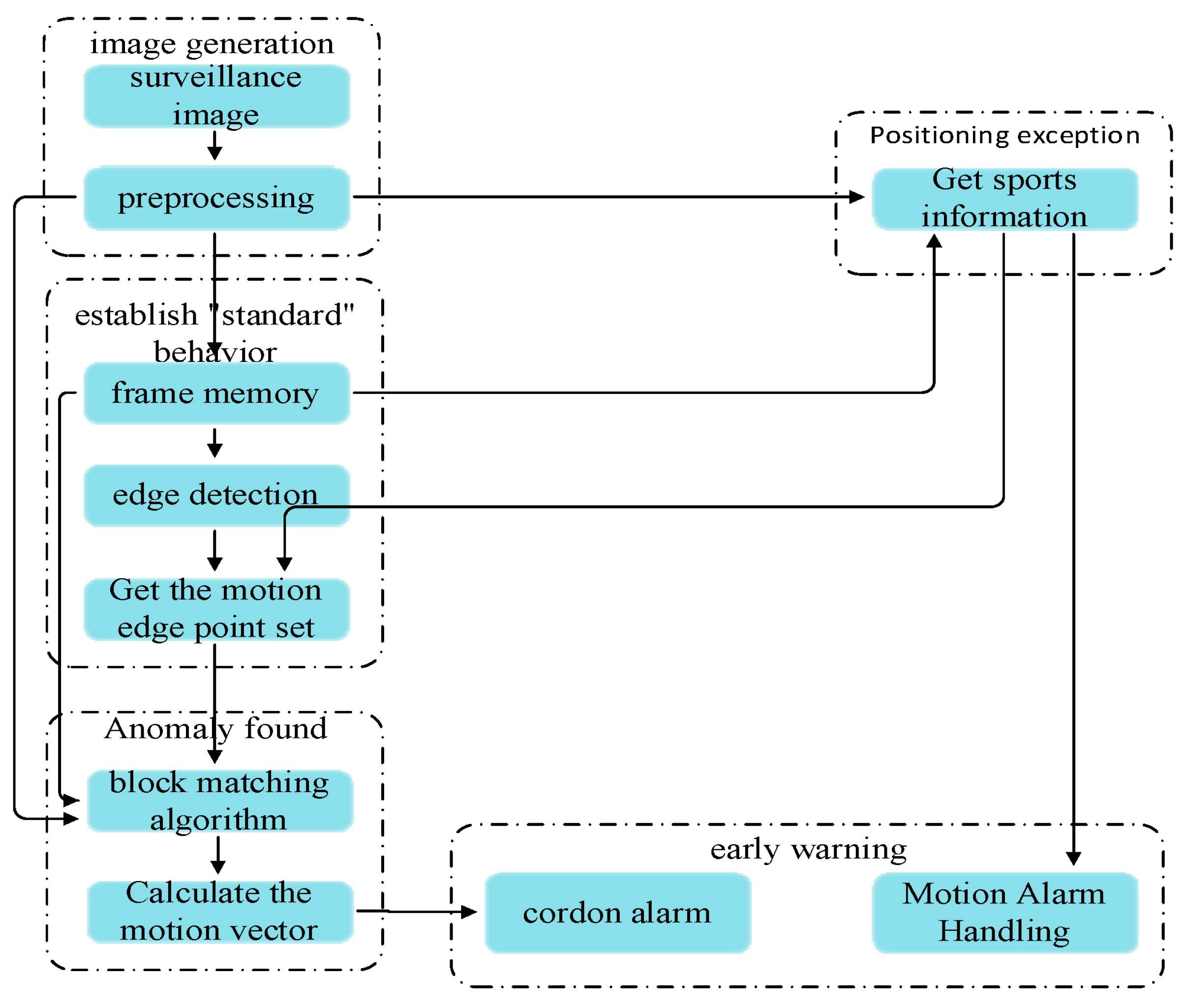
The word detection comes from motion detection [
43]. The key is to detect changes in images, and it is commonly used in automatic alarm systems and unattended monitoring systems. Detection models can dynamically deal with changing objects as well as detect and locate anomalies. It is characterized by dynamically capturing images over an ex-tended period of time, detecting abnormal conditions by comparing before and after images, and providing early warning of unusual location motion detection used in network traffic analysis. The network data flow is converted into the TG map of traffic behavior via the Sketch method, which corresponds to the actual image captured by the aid of the camera. The Profile of traffic behavior is generated through modeling to detect anomalies and locate them in the data flow. The core idea of motion detection is to automatically determine anomalies through image changes, so the detection model needs to have two characteristics: one is to process dynamically changing targets, and the other is to detect and locate anomalies to take follow-up processing. Motion detection can be divided into the following five parts: image generation, determination of “default” behavior, anomaly detection, anomaly localization, and early warning, as shown in
Figure 1.
We introduce the concept of motion detection in daily life monitoring into traffic monitoring in a network environment to realize the modeling and anomaly analysis of network behavior. The anomaly detection model for motion detection in the network environment should solve the following two problems:
The model needs to have the ability to process dynamic data. In actual monitoring, static analysis is not performed after collecting a segment of the image. To ensure security, image acquisition and analysis must be performed in real time. The detection model in this paper is based on the anomaly detection method. Since previous literature on anomaly detection has been analyzed based on static datasets, there is no dynamic anomaly detection for original network packets. Therefore, based on the network structuring results, this paper uses the Sketch method to generate a TG to complete the network traffic structuring process, realize the dynamic processing of network data flow, and provide features for the generation of Profile and model transitions in the next step. In addition, the generation of a TG can retain information on network traffic, which is equivalent to the abstraction in data flow mining. When an anomaly is found, the location of the anomaly can be located according to the TG, which is very important for practical applications. Since the data generated by network traffic is too large, manually searching for the anomaly will take a lot of time. Therefore, it is very necessary to store the summary information of network traffic in the form of TG.
Since the modeling of network traffic behavior in the existing literature is focused on anomaly detection and the processed data are static data, which is mostly modeled using statistics and probability distributions, the problem to be solved in this paper is how to establish a Profile based on the dynamic network traffic and change the Profile based on new data in real time. Therefore, this paper takes the original network data obtained as the analysis target, which is the Sketch-based method is used to generate the TG, and based on the TG, CNN and LSTM neural networks are used to extract spatial and temporal features and generate profiles. If the newly generated network traffic does not exceed the threshold for determining outliers, the Profile Evolution is based on the Profile and the newly generated network traffic.
3.2. Sketch-Based Network Traffic Structuring Process
Abnormal network traffic detection requires a Sketch-based network traffic structuring process to generate a TG. The network traffic structuring process first takes the original network traffic as the analysis target, extracts the features of the original network traffic by analyzing the communication sessions (i.e., applies the fingerprint), classifies the obtained traffic, and finally generates the TG according to the obtained application fingerprint and classification results.
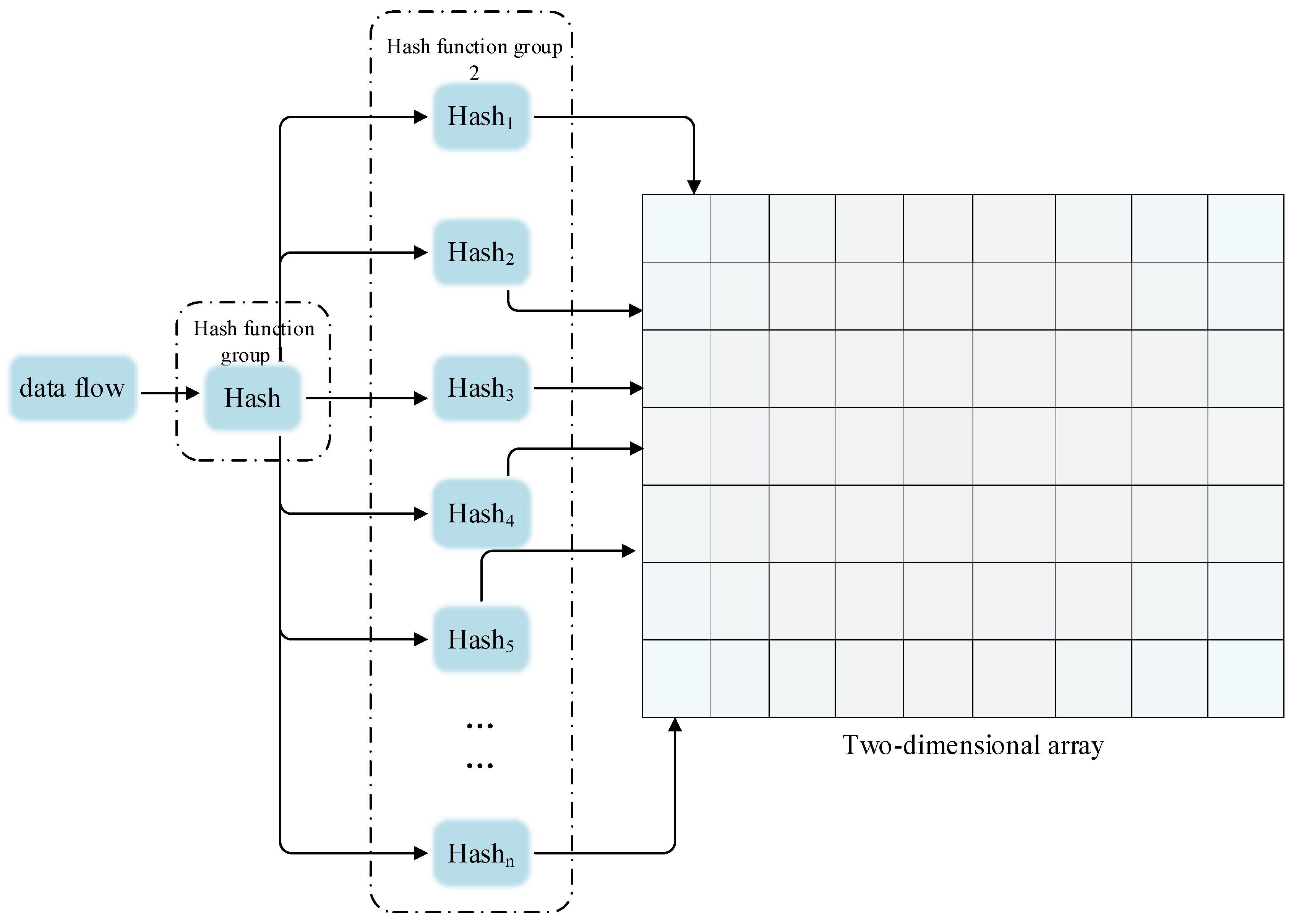
In data stream mining, the data stream is generated continuously, which consumes a lot of memory, and it is also very resource intensive when searching for historical data, so the Sketch method is introduced. The Sketch data structure [
44] can quickly query the data that passes through a large amount of traffic in sequence, i.e., it can provide real-time up-to-date summary data about the data stream and answer the user’s query quickly with a certain accuracy guarantee. It can also store the characteristic information of the traffic in the network in real time in a high-speed and complicated network environment, and it takes up little space.
In addition, it is possible to compress a large amount of information into a smaller data structure using hash functions, i.e., mapping the data stream into a two-dimensional space [
45] to create an abbreviated version of the dataset. The specific method is to first extract keywords from the captured data stream to form a vector, and then to use two sets of hash functions to map the keyword vector into a two-dimensional array to complete the compression of the data stream. In doing so, the two groups of hash functions can choose different mapping methods.
For the hash function [
46] given two datasets,
X and
Y, the mapping relation between datasets
X and
Y is
R, which is usually represented by a function:
. When using the network measurement method based on Sketch, the conflict problem to be addressed is the stable state of network traffic behavior, that is, the era of identical data flow shows that the behavior has not changed at this time, and due to the fact that the generated TG map is continuously stored, it can search for information and locate anomalies in historical data.
Figure 2 is the Sketch data flow summary method.
When anomaly analysis is carried out on a single user in a network environment, network traffic is primarily affected by humans. However, if we extend the consideration to a macro perspective, such as the backbone network or the network of an ISP Internet carrier provider, the human factor is almost erased. In large networks, the characteristics of the overall network are not affected by changes in individual users but change over time. Therefore, to eliminate the influence of the human factor on the behavior modeling and generate a TG for the behavior over this period, the concept of “structured” is proposed.
The concrete embodiment of network traffic is a continuously generated packet stream. The original attributes of each packet are few, including IP address, format, size, time, etc. According to these attributes, the features that can be analyzed in a fine granularity can be extracted, and the data stream can be processed quickly to prevent being annihilated by a large number of packets. In this paper, the original network traffic is directly taken as the analysis object, and the behavior of the mobile terminal is obtained without analyzing the content of the packet. Moreover, due to the huge amount of data, it is impossible to adopt the manual analysis method in practical application, and the fine-grained application behavior characteristics of the mobile terminal [
47]—the application fingerprint––can be obtained online in real-time through the principle of the communication session. The specific methods to extract application fingerprints are as follows: first, we use IP Address Transition (IAT) to divide network traffic, find the “breakpoints” of network traffic, divide network traffic according to communication sessions, and obtain a complete application fingerprint. Then, combine with the natural language processing method the tf-idf algorithm and N-gram model to calculate the utility of the applied fingerprint and an N-gram model-based “tree” to save the candidate set, and then extract the applied fingerprint from the structure of the “tree” to achieve the non-artificial dynamic extraction of the applied fingerprint.
The structuring process needs to use the acquired application fingerprint. Let the network traffic be
, the
N application fingerprints
extracted from the network traffic, with
M apps
. The relationship is shown in Equation (1):
The structured process also requires the classification of the traffic received. In a network environment, the packet exchange between two communication parties is a continuous process. The type, length, and IP address of packets is constantly obtained. The packet length is taken as an important feature analysis, and the Gaussian mixture model is used to solve the duplication problem of fingerprint application. By limiting clustering, the fingerprints of the same application with similar lengths are divided into the same cluster as far as possible to realize the traffic classification of different states. The same fingerprint is clustered according to its length, and the probability distribution of the fingerprint with a similar length is calculated to complete the classification of the same fingerprint. In restricted clustering, the fingerprints of the same IP address should be divided into a cluster as far as possible, so that the fingerprints in the same cluster are similar, which may come from the same application, to improve the classification effect.
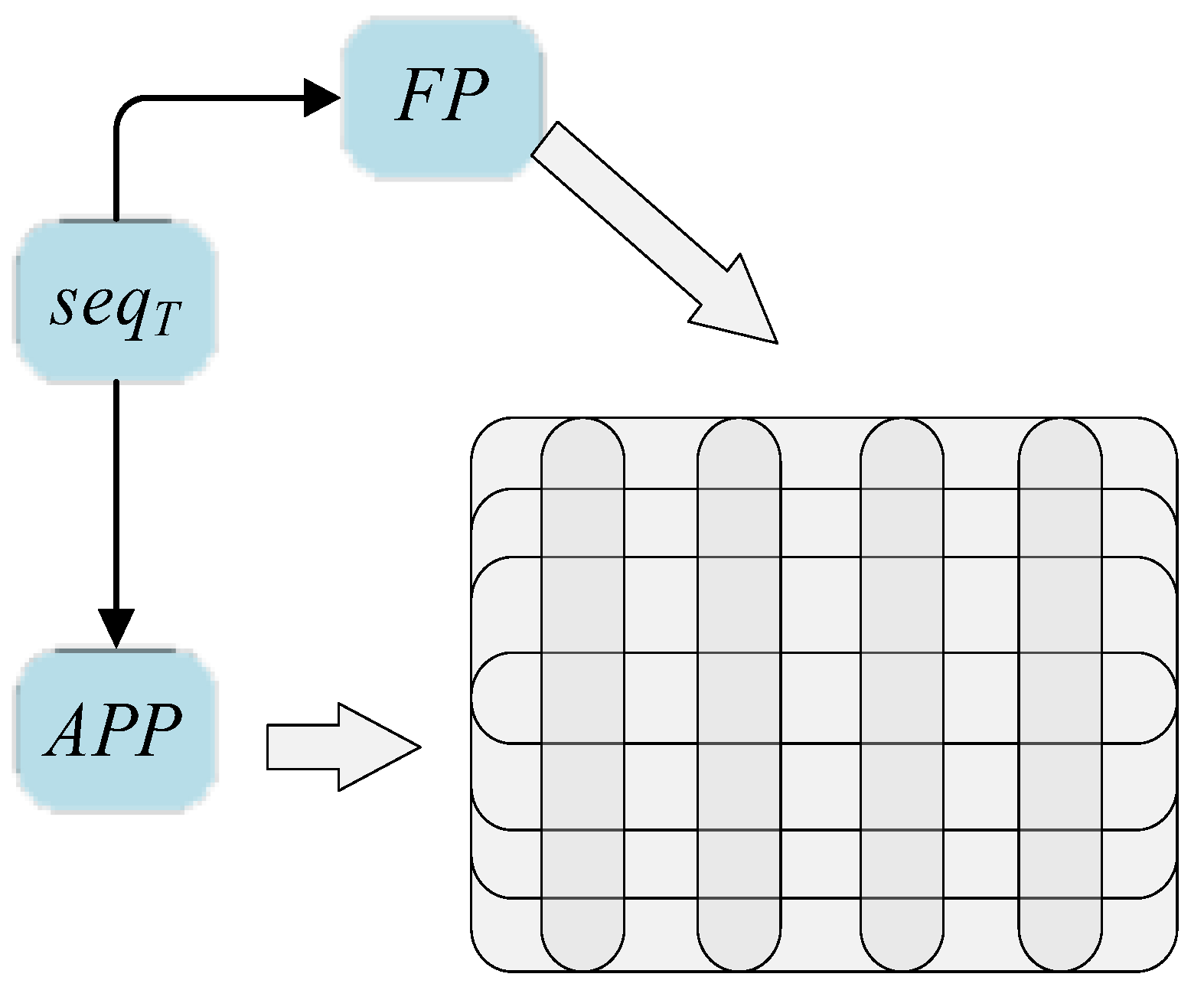
The TG map is generated through the network traffic structuring process, and an image can be generated according to
, as shown in
Figure 3:
3.3. Network Spatiotemporal Feature Extraction Based on CNN-LSTM
When detecting network traffic anomalies, transition anomaly detection is also required. The Sketch method is utilized to continuously extract TGs to obtain a set of TGs, and then uses this set of TGs to generate behavior models. Generated behavior models preprocess TGs in time and space to generate profiles through CNN and LSTM neural networks. Finally, the new data stream is processed by the transition method to realize the Profile Evolution.
Use the Sketch method to continuously extract the TG map to obtain a set of TG maps, and then use this set of TG maps to generate a behavior model. However, to generate a behavior model, the TG map needs to be preprocessed in time and space through CNN and LSTM neural networks.
The network data stream [
48] is formed by the continuously generated data packet
and the data packet
is converted into some characteristic fingerprint combinations
, and then the application fingerprint is mapped to the specified interval according to the Sketch-based method to generate a TG map:
The elements of the matrix are all represented by the length of the data packet.
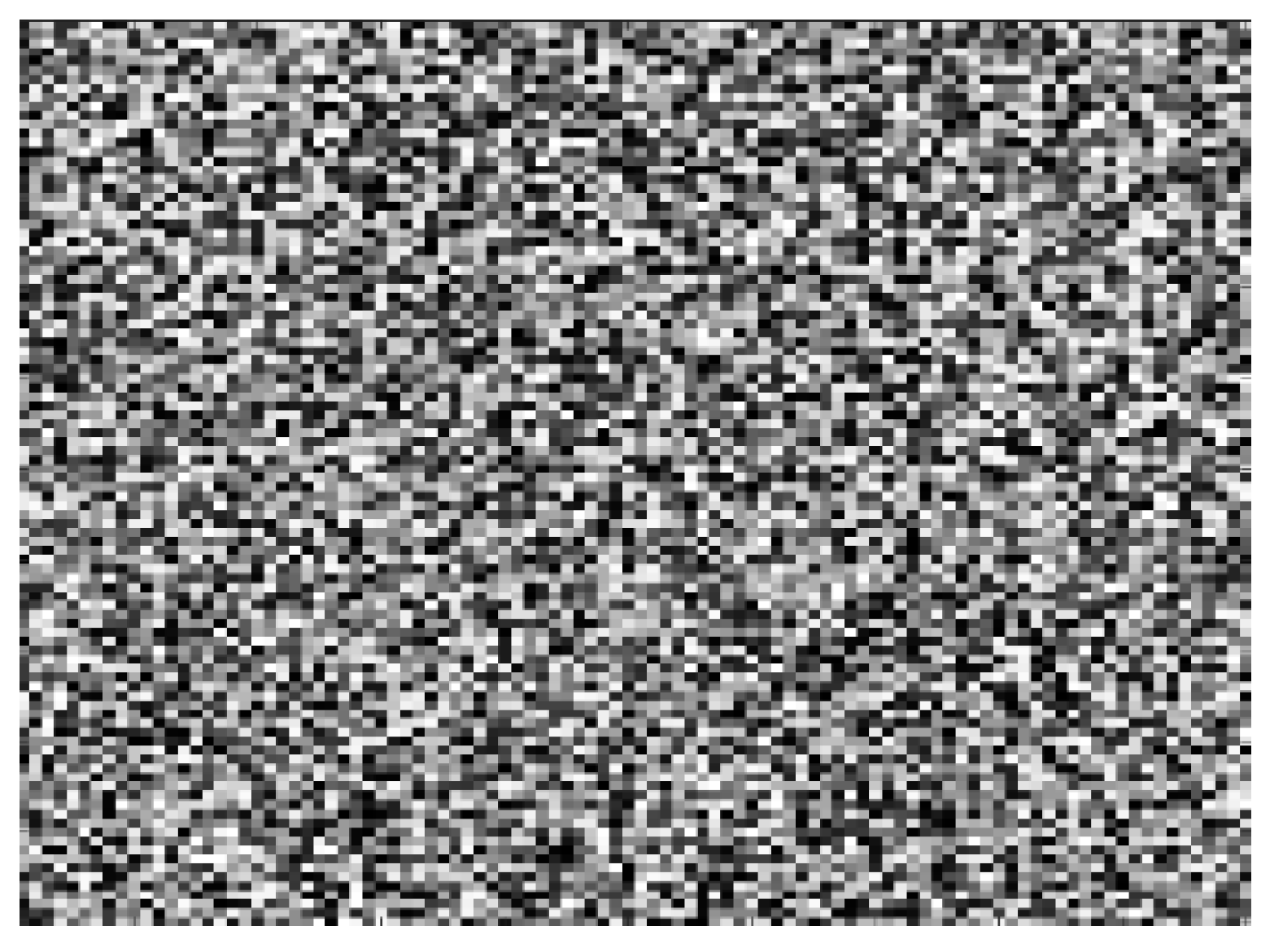
Figure 4 is a TG image represented by a gray scale image:
According to the obtained behavioral TG map, CNN [
49] is used to obtain the user’s spatial features due to its excellent ability to extract features from images.
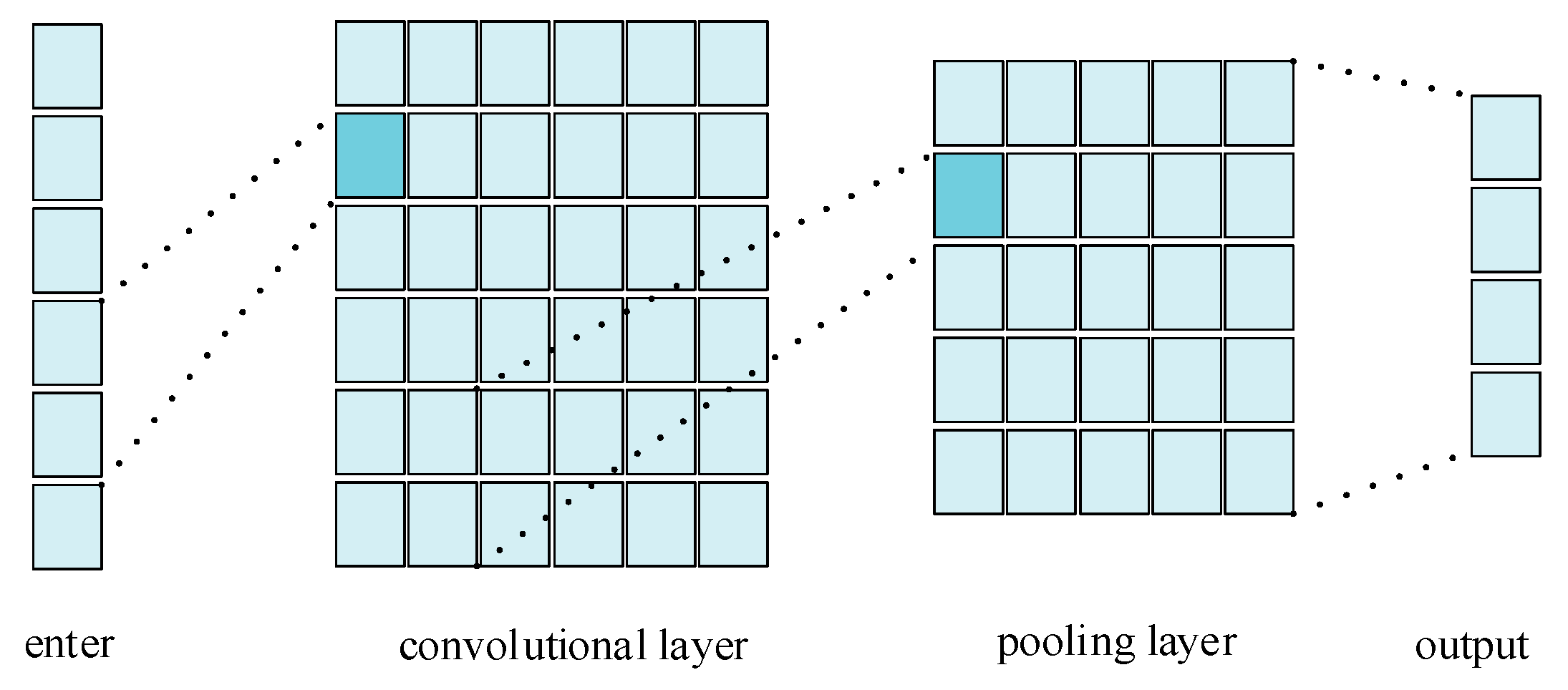
Figure 5 is a structural diagram of a CNN.
The main functional modules of the deep convolutional neural network CNN can be divided into two categories: a feature learning module and classification module. The feature learning module is mainly composed of a convolution layer and a pooling layer. The convolution layer performs a convolution operation on the obtained behavior TG to extract the features of the local area. This process uses a filter to analyze the image and extract the corresponding feature information. Assuming that the filter is a square matrix of order
, let
in
, and
is the number of new features,
is the weight of the filter, and
is the bias vector, as shown in Equation (3):
Combine the generated new feature vectors, as showed in Equation (4):
Pooling layers can reduce the number of parameters and reduce the possibility of overfitting. Pooling functions include average pooling and max pooling. Here, the operation of maximum pooling on vector
generates a new feature vector, as shown in Equation (5):
The network data stream generates a TG through the structured process of the Sketch summary method and then extracts the feature vector of the space through CNN. The data stream is continuously generated, and the user’s behavior is also affected by the change in time. Therefore, the LSTM [
50] recurrent neural network is used to extract temporal characteristics of the network data stream
.
The LSTM network has the characteristic that its current state is affected by the previous state, and it has the ability to choose to save or forget information. Its structure is shown in
Figure 6, which is composed of three gates: Forget Gate
ft, Input Gate
, and Output Gate
.
is the current state of the cell,
is the state of the hidden layer, and
is the input data.
The Forget Gate is to selectively discard the historical information of the cell state. As shown in Equation (6), the output of the Forget Gate
is determined by the state
and input data
of the previously hidden layer,
is the sigmoid function, and
and
are Forget Gate weights and biases:
The Input Gate selectively saves new information into the cell unit state and updates the state information, as shown in Equations (7)–(9); the current state
of the LSTM network will be affected by the previous state;
,
, and
are the weights and biases of the Input Gate;
and
are the weights and biases of the cell state; and
is the state of the candidate cell:
The Output Gate determines the output information according to the united state of the cell, as shown in Equations (10) and (11), and
and
are the weights and biases of the Output Gate:
The network continuously generates new data streams, extracts a new spatial feature vector through the CNN network, inputs the vector R as the input data into the LSTM network structure, and obtains the output vector , which is used to describe the user behavior over time.
3.4. Behavior Pattern Detection Method Based on Profile Evolution
During a period, the user’s behavior is relatively stable. When performing anomaly detection, the user’s Profile needs to be established first. Suppose the vector extracted by the CNN-LSTM network feature is
, and the Base of the user behavior Profile
. Equation (12) linearly expresses the relationship between
T and
B:
The basis generation problem is expressed according to the calculation of the basis set with the smallest reconstruction error, as shown in Equation (13), where
T is the input signal and
is the weight vector
. Equation (13) is to obtain the
minimized parameters
w,
b:
The vector of the newly generated network data stream is
. Equation (14) is obtained according to Equation (13):
Equation (14) can be refactored into a new objective function to solve the minimization problem:
Singular value decomposition [
51] (SVD) is performed on Equation (15), and the feature continuously generated by the CNN-LSTM network is
, as shown in Equation (16):
Perform SVD on
, as shown in Equation (17):
Among them,
is a unitary matrix,
is a diagonal matrix, as shown in Equation (18):
Because
is a diagonal matrix, the SVD of
can also be written as shown in Equation (19):
Convert Equation (17) to
, and associate
U = B (the energy of
U is concentrated on the diagonal) to obtain the corresponding weight
, as shown in Equation (20):
Therefore, the user’s Profile is shown in Equation (21):
Assuming that the newly extracted feature vector is
, set a threshold
, and the distance between the new feature and the Profile is calculated by Power Distance [
52], as shown in Equation (22):
Power is a distance measure of the distance between two vectors of length i. It is usually expressed as the physical distance of two locations in three-dimensional space, but can be applied to vectors of any dimension when the data type is numeric. The specific distance metric is determined according to the values of and . For example, if , Equation (22) becomes the Euclidean distance. If the calculated distance is greater than , it will become an abnormal point.
The newly acquired sample vector not only needs to calculate the distance from the Profile for anomaly detection but also has an impact on the Profile. The new data flow will evolve the old Basis into a new Basis, so the detection model will follow the data flow. The change affects the evolution of the Profile, the newly generated vector
, and a new Profile
is generated according to Equation (23):
Among them, is the basis generated by the newly generated vector , and the parameter is the measure, which shows the degree of influence of the new data on the Profile.
The steps of the SPE algorithm are as follows:
Input: data stream , , , p, r
Output:
Extract the characteristics of the data stream and apply the fingerprint: ;
Generate TG according to :;
Use CNN to extract the spatial features of the TG map: ;
Extract the temporal features of users according to LSTM:
Calculate the weight
according to (13), and obtain the user’s Profile as:
Calculate the abnormal point according to the distance:
The specific implementation process of SPE algorithm is showed in
Figure 7.
4. Experiment and Result Analysis
The experimental dataset is the network data captured in the actual environment through Wireshark [
53]. The captured devices are two Android smart phones. Mobile phones are hooked up to video software such as Douyin (v4.2.0) and Tencent Video (v7.1.0.19832), news software programs such as Weibo (v9.4.0) and Toutiao (v7.1.3), communication software programs such as WeChat (v7.0.3) and QQ (v7.9.2), and life software programs such as Meituan (v9.11.802) and Ctrip (v8.1.0). We conducted long-term dataset collection in these running environments, and then cut specific time interval data packets from these datasets to obtain the dataset used in the experiment. The specific values of the dataset are shown in
Table 2:
The Background is the number of data packets captured by the mobile phone without any application running, and is mainly the data sent by the system itself and pushed by some applications. As can be viewed from
Table 2, 932 data packets are obtained after 15 min of rest, which is the same as the number of data packets with other applications running, and is negligible. Video, News, Communication, and Life are the traffic conditions obtained by running only video software, news software, communication software, and life software, respectively. Mix1, Mix2, and Mix3 are the mixed flow statuses obtained via running all the software programs of the mobile phone for 5, 10, and 15 min, respectively.
At the same time, in order to simulate the situation of receiving abnormal traffic during actual use, we make the above datasets into abnormal traffic datasets with abnormal characteristics by sending malicious code to the device that is grabbing traffic packets irregularly.
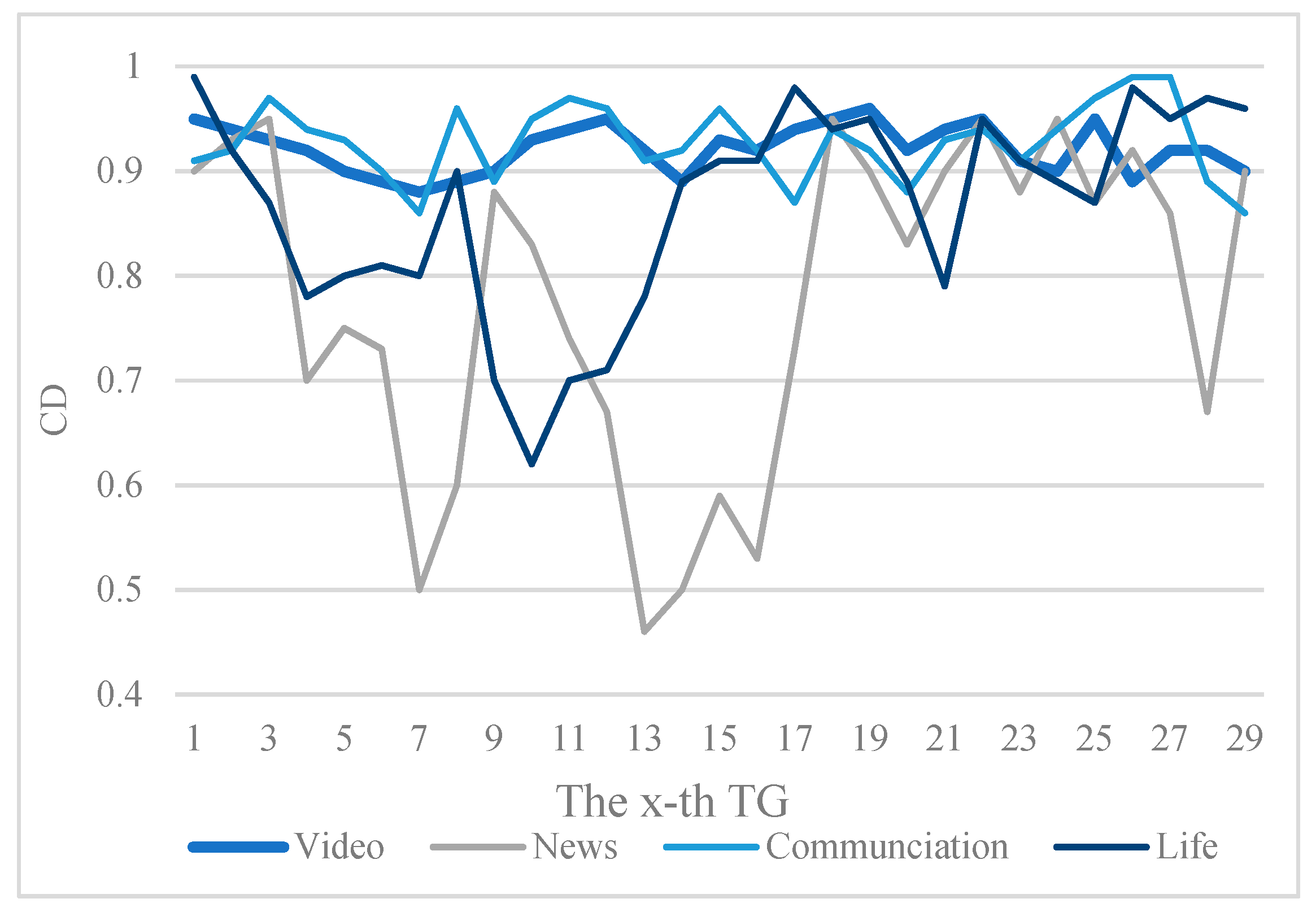
To evaluate the performance of the SPE algorithm, we conducted the following three parts of the experiment as follows:
The first part of the experiment is to study the performance of the TG generated by the structured network traffic. Consistency Degree (
CD) is used to measure the stability and sensitivity of the TG. The similarity of the TG formed by the same type of network traffic is relatively high. The similarity of TGs formed by different types of network traffic is relatively low, as shown in Equation (28):
where
and
are the mean values of the pixels of
a and
b in the graph,
and
are the variances of
a and
b,
is the covariance of
a and
b,
and
are the stabilization parameters, and scale is the range of pixels.
Figure 8 shows the continuity of the datasets for Video, News, Communication, and Life, respectively. Each dataset generates a TG every 10 s to calculate the continuity of adjacent images. The
X-axis represents the generated x-th TG.
According to the curve in
Figure 8, the continuity of the TG of video traffic is not much different, and the curve fluctuation is relatively small because the data packets captured from video applications are relatively similar. News applications include pictures, meanwhile, and there are various types of data such as video and text, so the fluctuation range of the TG is relatively large and the continuity is relatively low, indicating that the Profile of network traffic has changed.
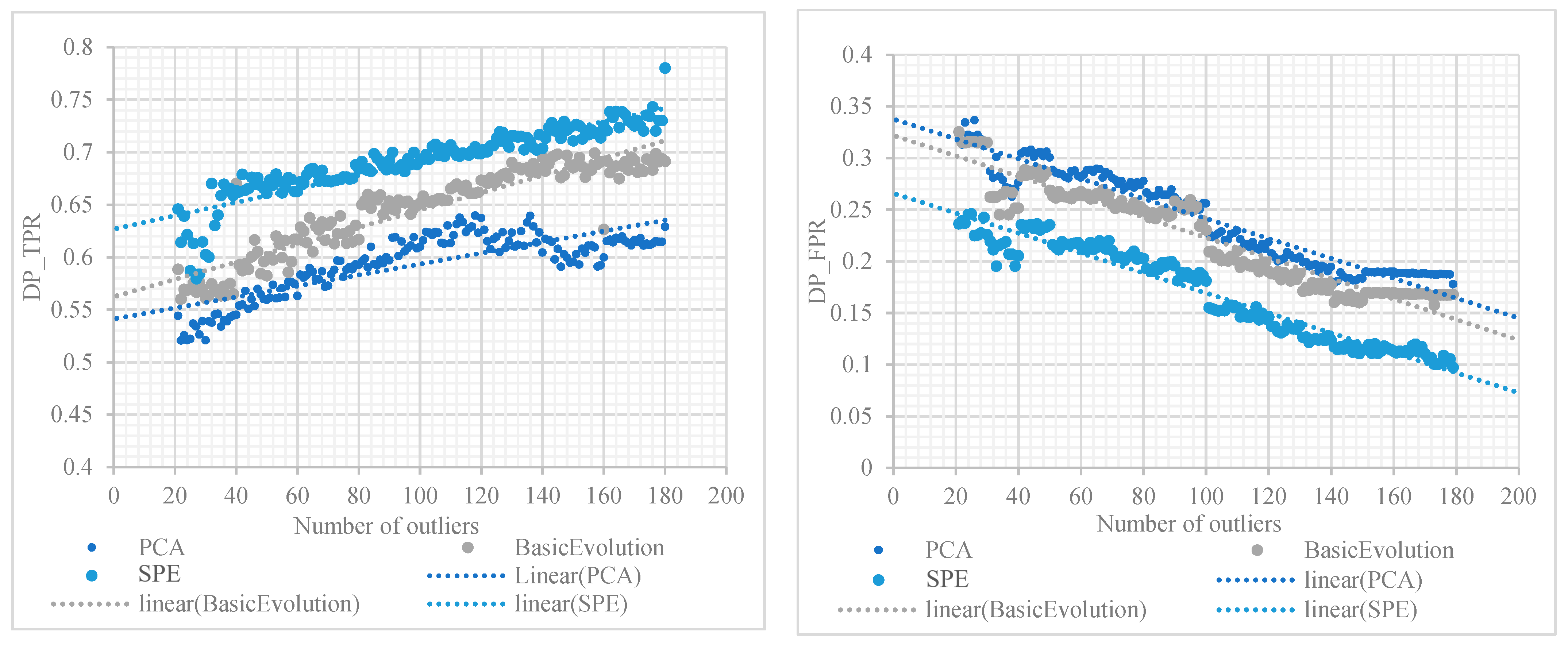
The second part is the analysis experiment of the TG generation Profile, which is compared with PCA [
54] and Basic Evolution [
55], two algorithms for generating traffic characteristics. Among them, PCA converts the original data into a set of linearly independent vectors by finding the eigenvectors of the matrix. Basic Evolution divides the data flow by time, uses the size of network traffic as the feature of anomaly analysis, and, finally, uses SVD for anomaly detection. PCA is a widely used feature extraction method, and Basic Evolution has been proposed and proven to have a lower error rate in recent years. Therefore, we chose to compare SPE with them through experiments.
This experiment uses a synthetic dataset [
56] because it is difficult to perform artificial outlier analysis on real network traffic. Therefore, in the Mix3 dataset, points are randomly selected, and the order of the data packets is adjusted, or part of the data are replaced to obtain a synthetic dataset.
The detection probability of outliers is used as an evaluation criterion, as shown in (29), where the number of outliers is detected correctly.
The proportion of incorrectly detected non-abnormal points is used as another evaluation criterion, as shown in (30), where
is the number of non-abnormal points detected by the algorithm and
is the number of abnormal points detected by the algorithm:
Figure 9 shows the comparative experimental results of the three algorithms PCA, Basic Evolution, and SPE.
Figure 9 suggests the outlier detection effects of the three algorithms PCA, Basic Evolution, and SPE. The detection probability of outliers and the proportion of non-outliers wrongly detected by the SPE algorithm are superior to the other two algorithms. With the increase in the number of outliers, the detection probability of outliers keeps increasing, while the proportion of non-outliers wrongly detected keeps decreasing. When the number of outliers reaches a certain size, the percentage of non-outliers varies very little between Basic Evolution and SPE, while the SPE algorithm continues to decrease, so the ability of the SPE algorithm to detect the percentage of non-outliers in error is far superior to the other two algorithms. Since the position of the abnormal point is random, the
DP_TPR and
DP_FPR of different abnormal points will change, which suggests that the abnormal position will affect the detection effect.
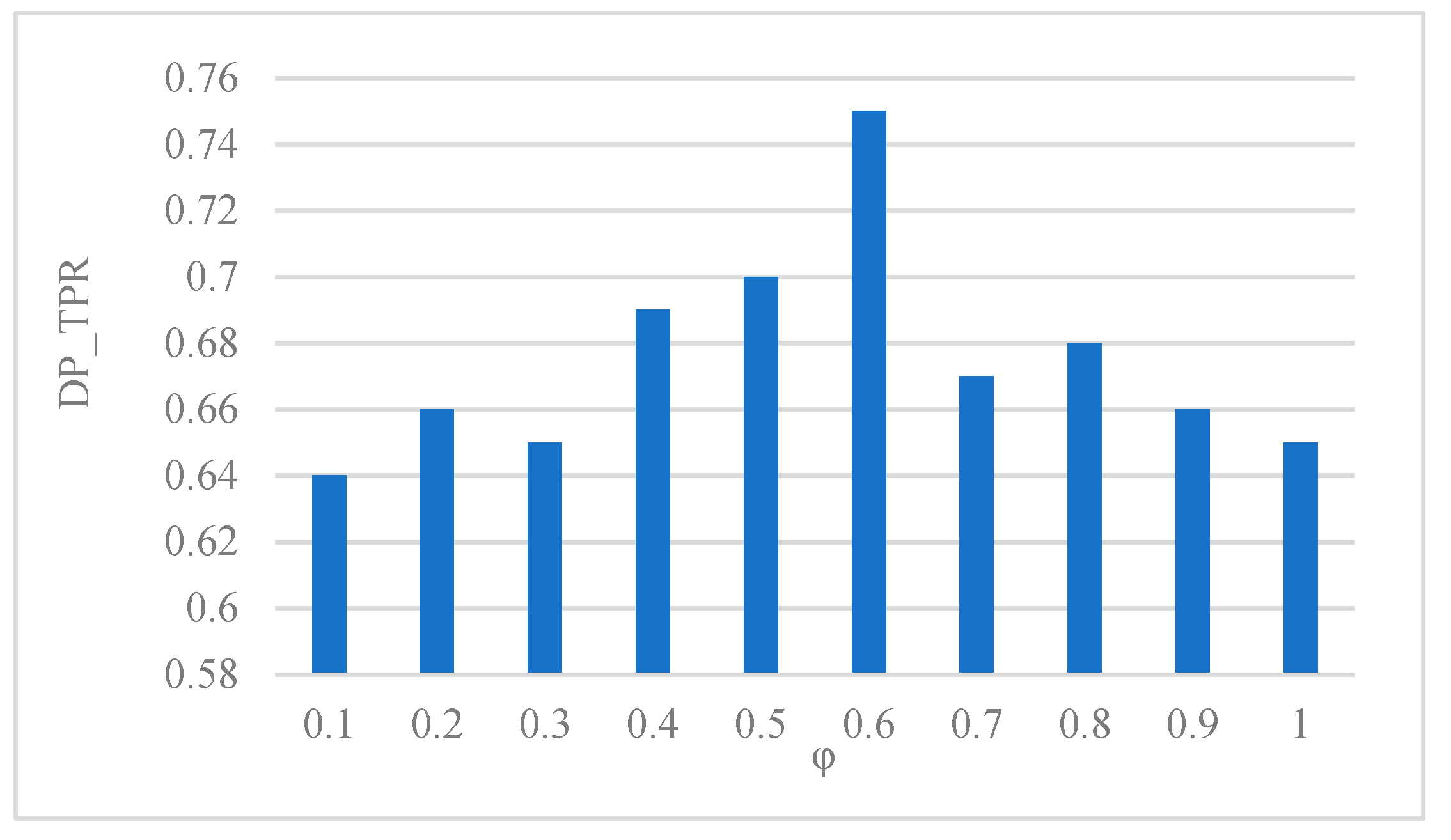
The third part is the influence of Profile Evolution parameters on outlier detection. A total of 100 outliers are selected and the value is between [0.1, 1]. The results of each experiment are measured using the value of
DP_TPR. The results of the experiments are shown in
Figure 10:
The result of anomaly detection is affected by the value of
. According to the Equation (23),
is the result generated by the new data stream, so the value
determines the impact of the new data stream on the Profile. When the value
is small, the impact of the new data stream on the Profile is relatively small, and when the value
φ is large, the Profile will approximate the behavior of the new data stream. As shown in
Figure 10, when
= 0.6, the value of
DP_TPR is the largest, and the effect is the best for the selected 100 outliers. In reality, the behavior of a new data stream is subject to change, and the value of
should be selected according to the actual situation.