A Blockchain-Enabled Distributed Advanced Metering Infrastructure Secure Communication (BC-AMI)
Abstract
:1. Introduction
- We integrate decentralized blockchain technology in smart meter secure communication to remove the need for conventional trusted authorities;
- We eliminate single point of failure and regulate communication in a flexible, trustworthy, and automated way;
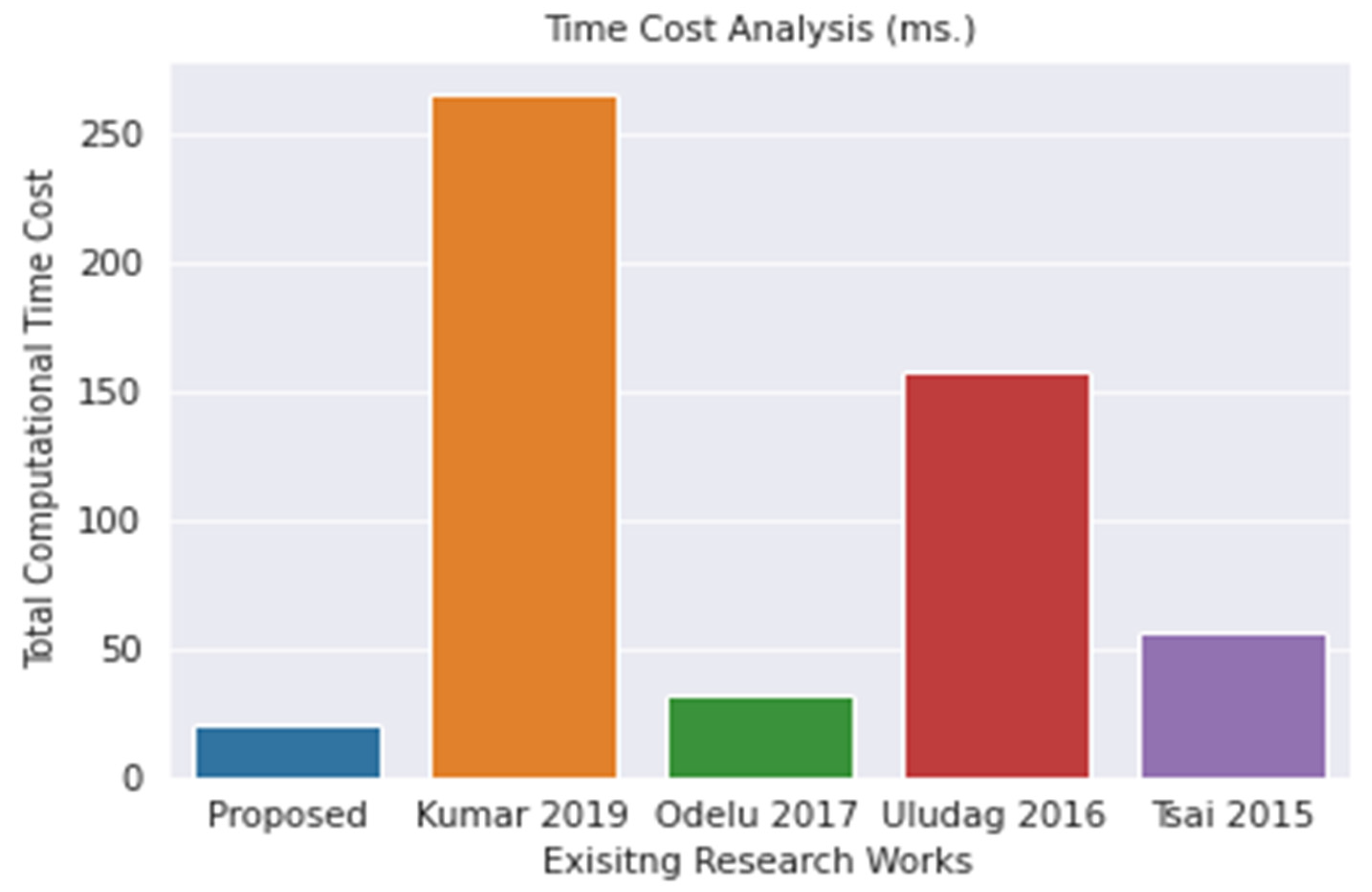
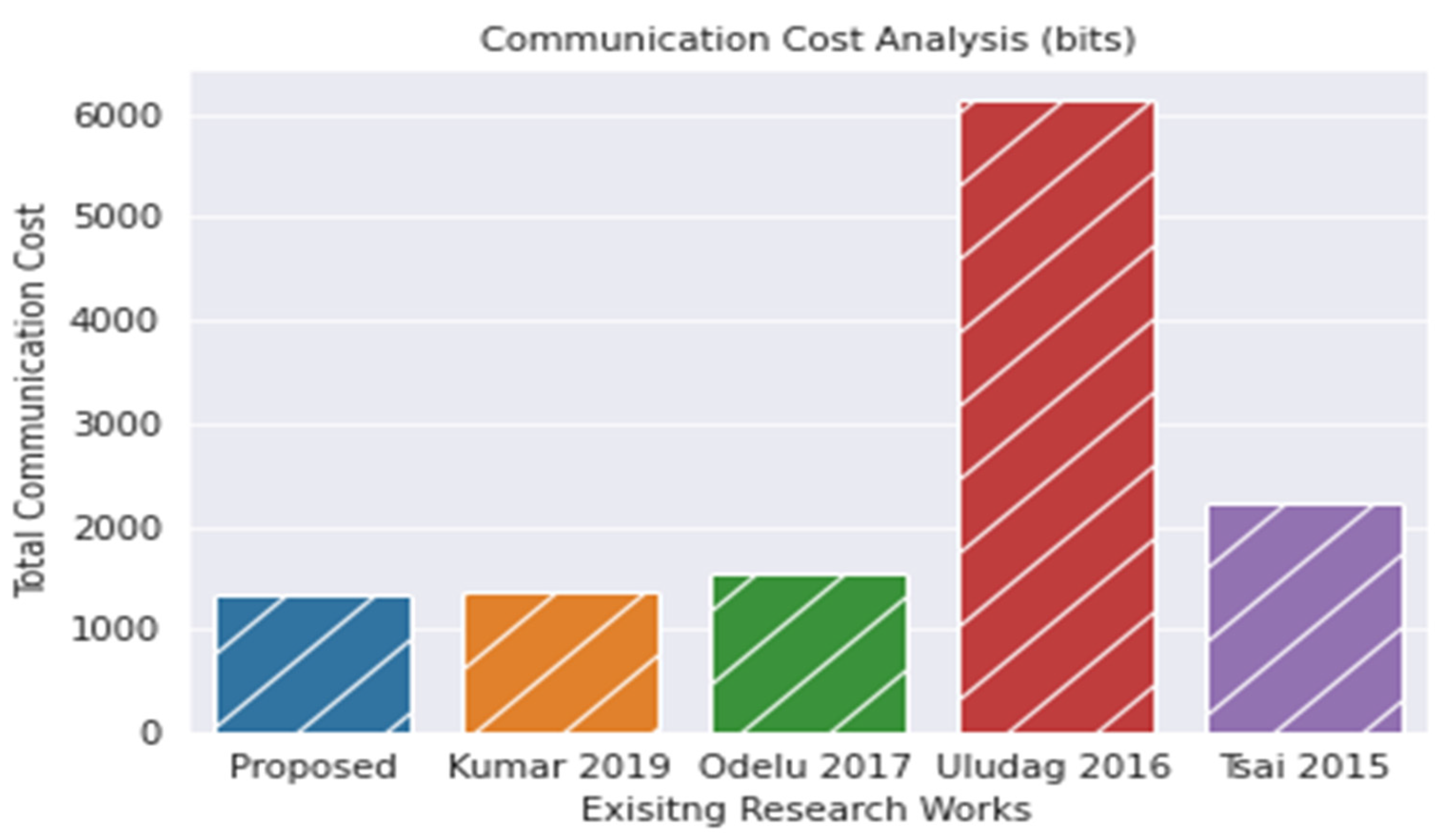
- The proposed scheme takes less time and expends less communication bit than other existing works;
- Finally, by an informal security discussion, we confirm that the proposed scheme is secure enough against the most common types of attacks.
2. Literature Survey
3. Background and Preliminaries
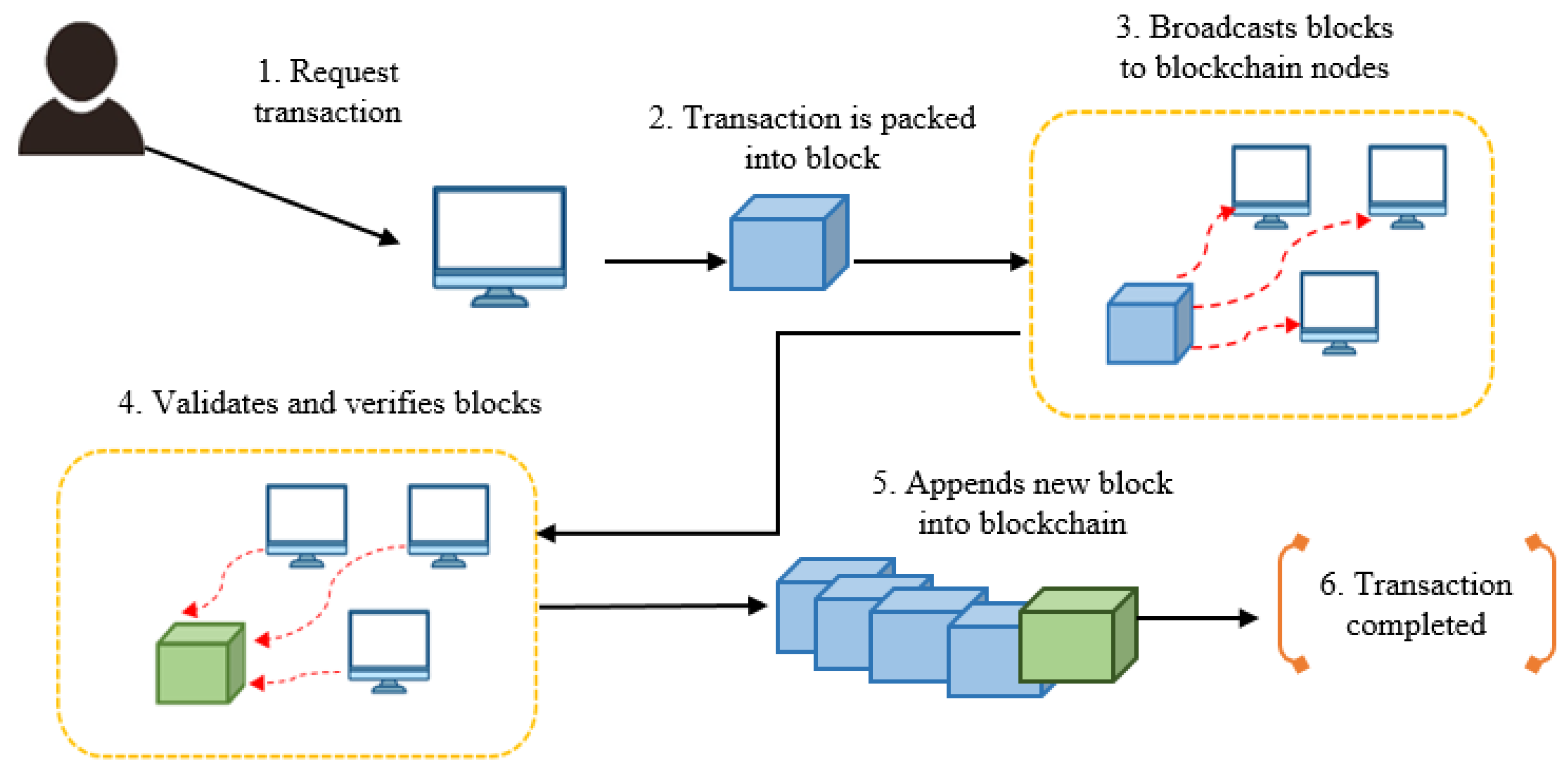
3.1. Blockchain
3.2. Smart Contract
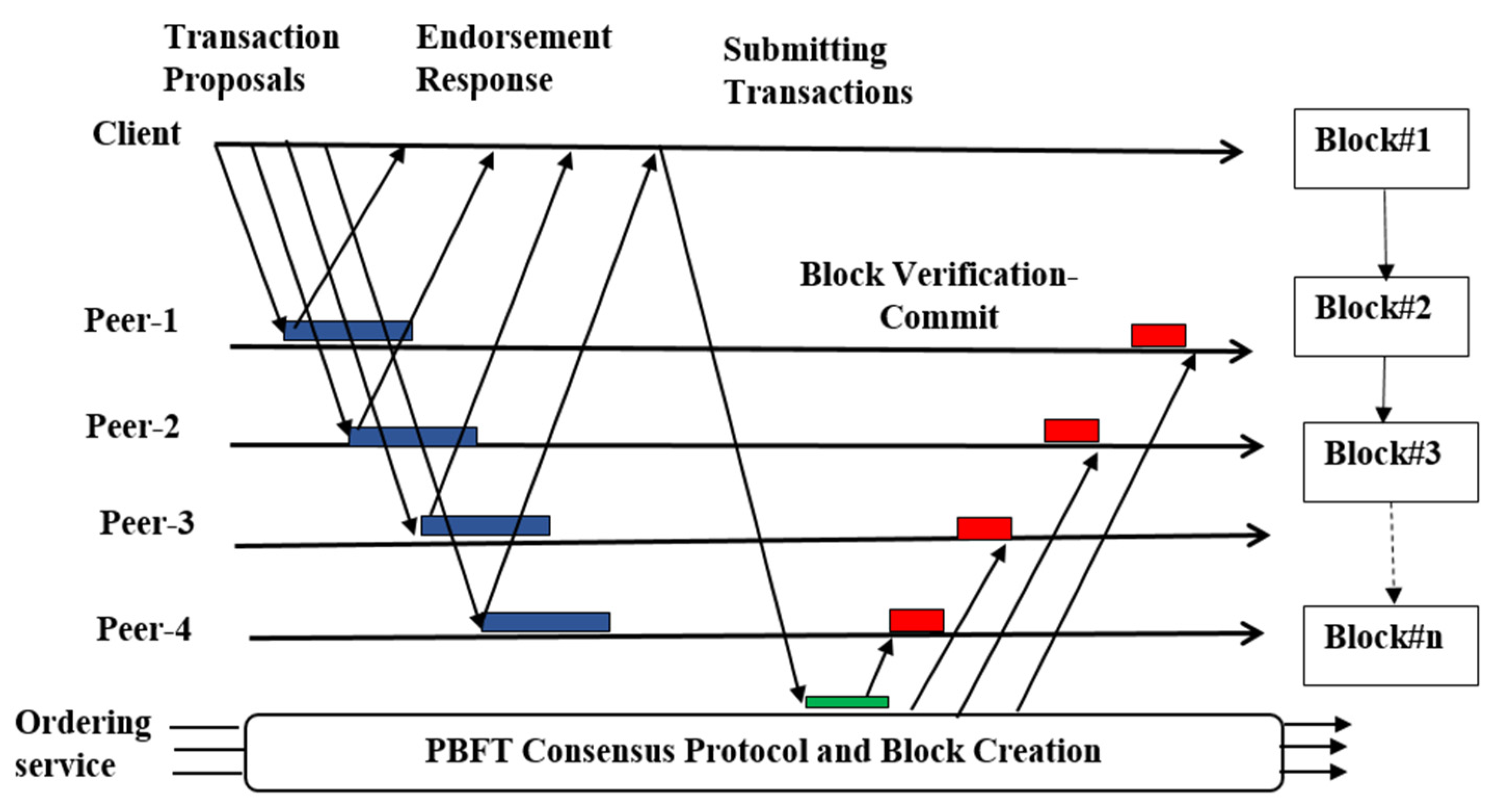
3.3. Hyperledger Fabric with Practical Byzantine Fault Tolerance
4. System Methodology
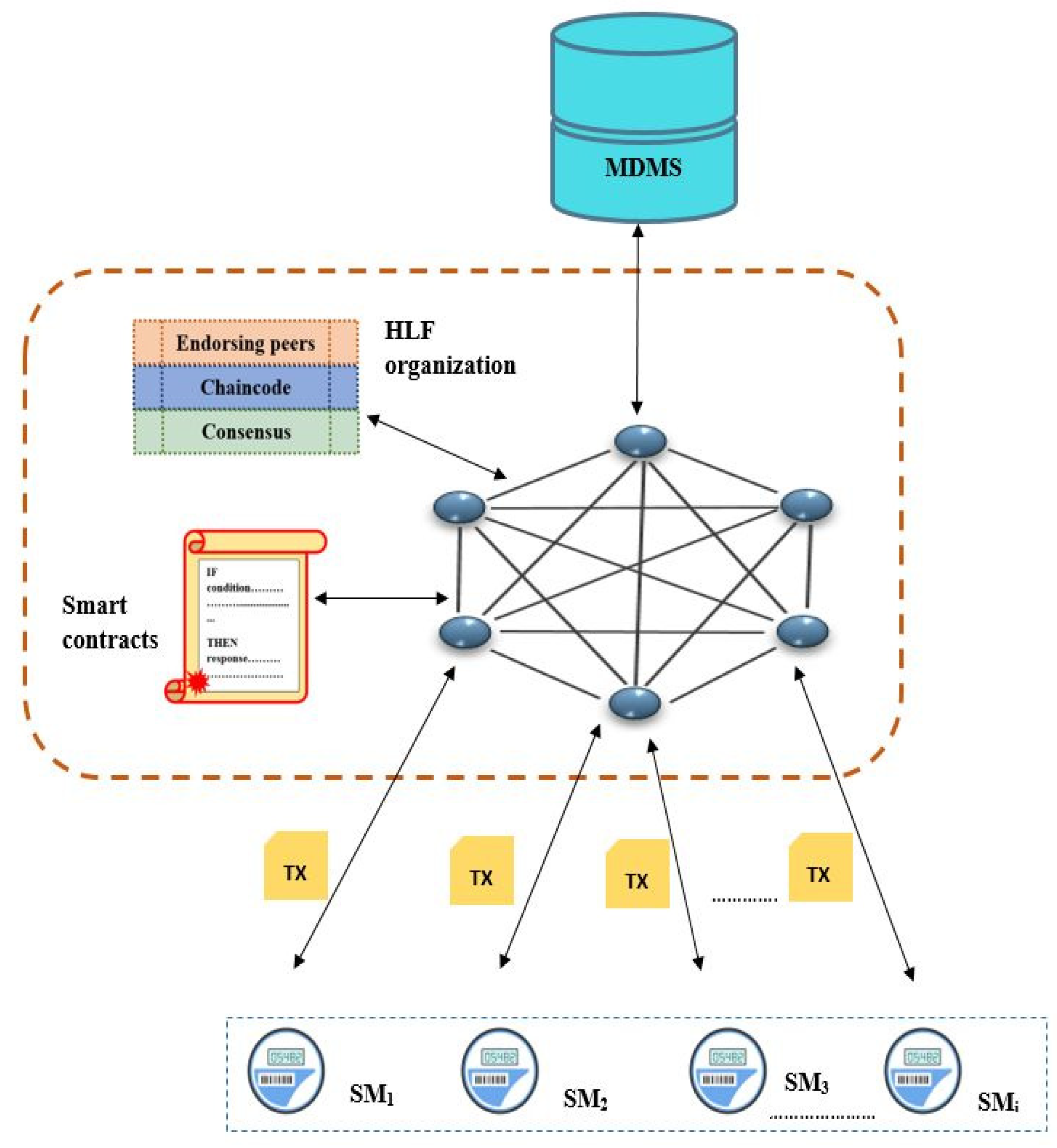
4.1. System Overview
4.2. Proposed System Workflow
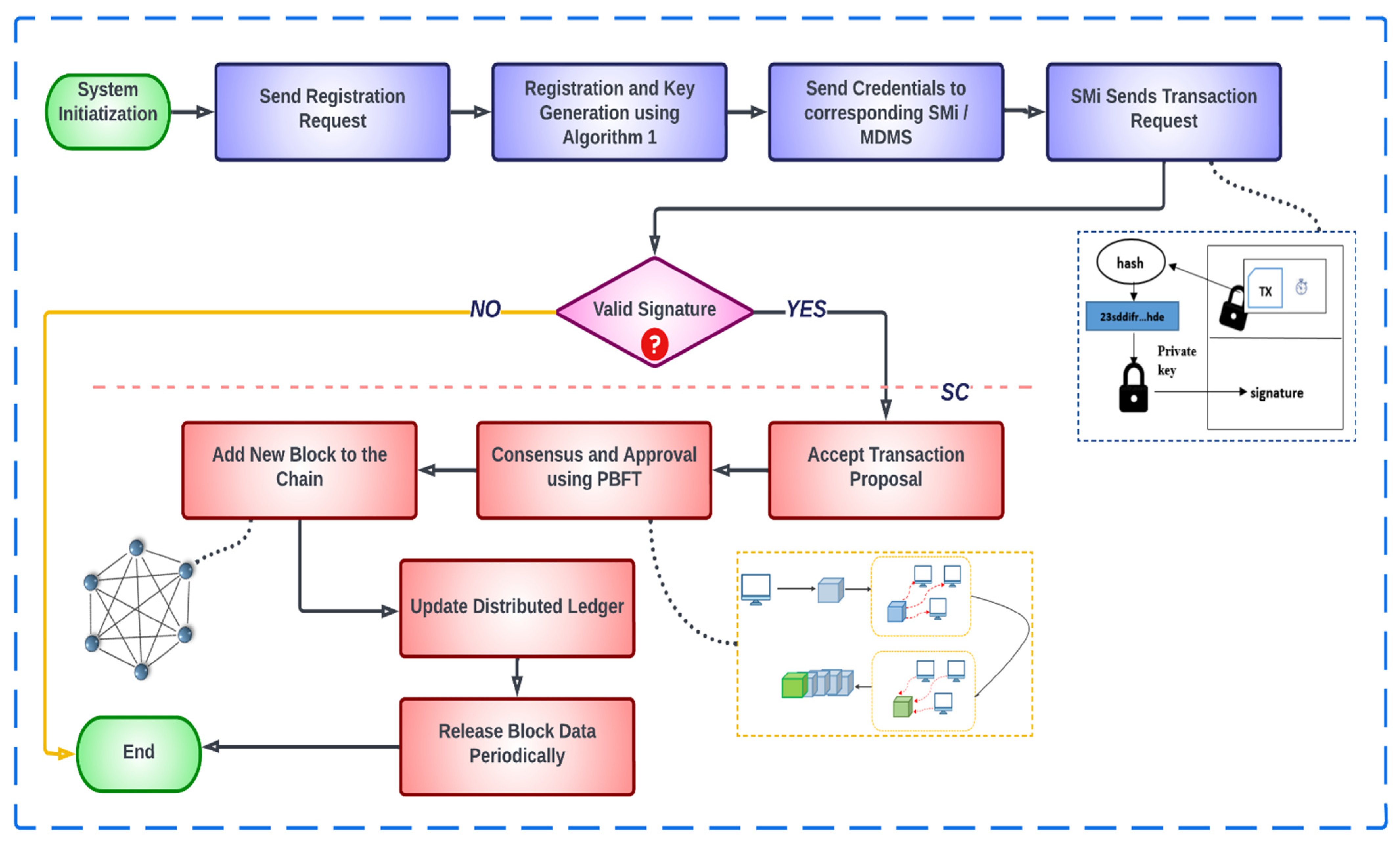
4.2.1. Phase 1: System Initialization
4.2.2. Phase 2: Registration and Key Generation
- Both SMi and MDMS are registered in the blockchain using their hash identities in this phase. SMi computes its HIDSMi and sends a registration request message to DCj to obtain its public and private key pair. Here, request message = (HIDSMi, reg_req);
- DCj relays the request message to the smart contract. Smart contract executes a query in the database to verify if HIDSMi = HIDSMi’. If the HIDSMi exists, then the registration is executed to generate the corresponding key pair (PrSMi, PuSMi). Otherwise, the request is declined. The key pair is derived from ECC curve [29] as described in Algorithm 1;
- The registration process of MDMS is similar to SMi. After successful registration, the HIDSMi is provided to the MDMS along with the key pair (PrMS, PuMS).
| Algorithm 1: Smart contract-based registration and key generation |
| Input:HID of SMi/MDMS |
| Requires: Pre-stored HID’ of SMi/MDMS in DB |
| Output: (Pr, Pu) for registered SMi/MDMS |
| 1: For each SMi/MDMS do |
| 2: Query for HID’ records in DB |
| 3: If HID == HID’ then |
| 4: Execute registration () {select random number x € Zp//using ECC curve |
| 5: Pr = x |
| 6: Pu = x.G |
| 7: Return (Pr, Pu)} |
| 8: Else |
| 9: Decline |
4.2.3. Phase 3: Data Transaction and Validation
- Create Transaction: Each SMi collects electricity usage data (UD) and creates an electricity usage report with the timestamp, τ. The formatted usage report is encrypted using the public key of MDMS. The final transaction is created using the encrypted usage report E(UD), its hash, timestamp, HIDSMi, and the ECDSA signature of the sender SMi. Table 2 provides the final transaction format of the collected usage data;
- Transaction Request Validation: DCj passes the message again to SC after receiving the transaction request message. SC checks the HIDSMi to ensure the sender’s pre-registration and verifies the signature. If the signature is verified, DCj sends the encrypted message to the peers for endorsement. Peers respond to the proposal, append signature as an endorsement, and send it back to the DCj. After receiving the response, DCj sends the encrypted transaction to the ordering service with the peer endorsement. The ordering service validates the transaction using PBFT consensus algorithm;
- In the ordering phase, after receiving a transaction request, the leader node generates a new block with the transaction information, which is considered a candidate block. For verification as well as auditing, the leader node broadcasts the block to other nodes. Nodes audit the block data after receiving it and broadcast the results with a hash to the rest of the network. Each node compares the audit results with the others. Nodes reach a consensus on the candidate block and send the audit and comparison results back to the leader. If the leader obtains 2f + 1 responses, then the candidate block is finalized and appended as a new block in the blockchain.
4.2.4. Phase 4: Release Block Data
5. Implementation and Performance Analysis
5.1. Experimental Environment
5.2. Dataset Description
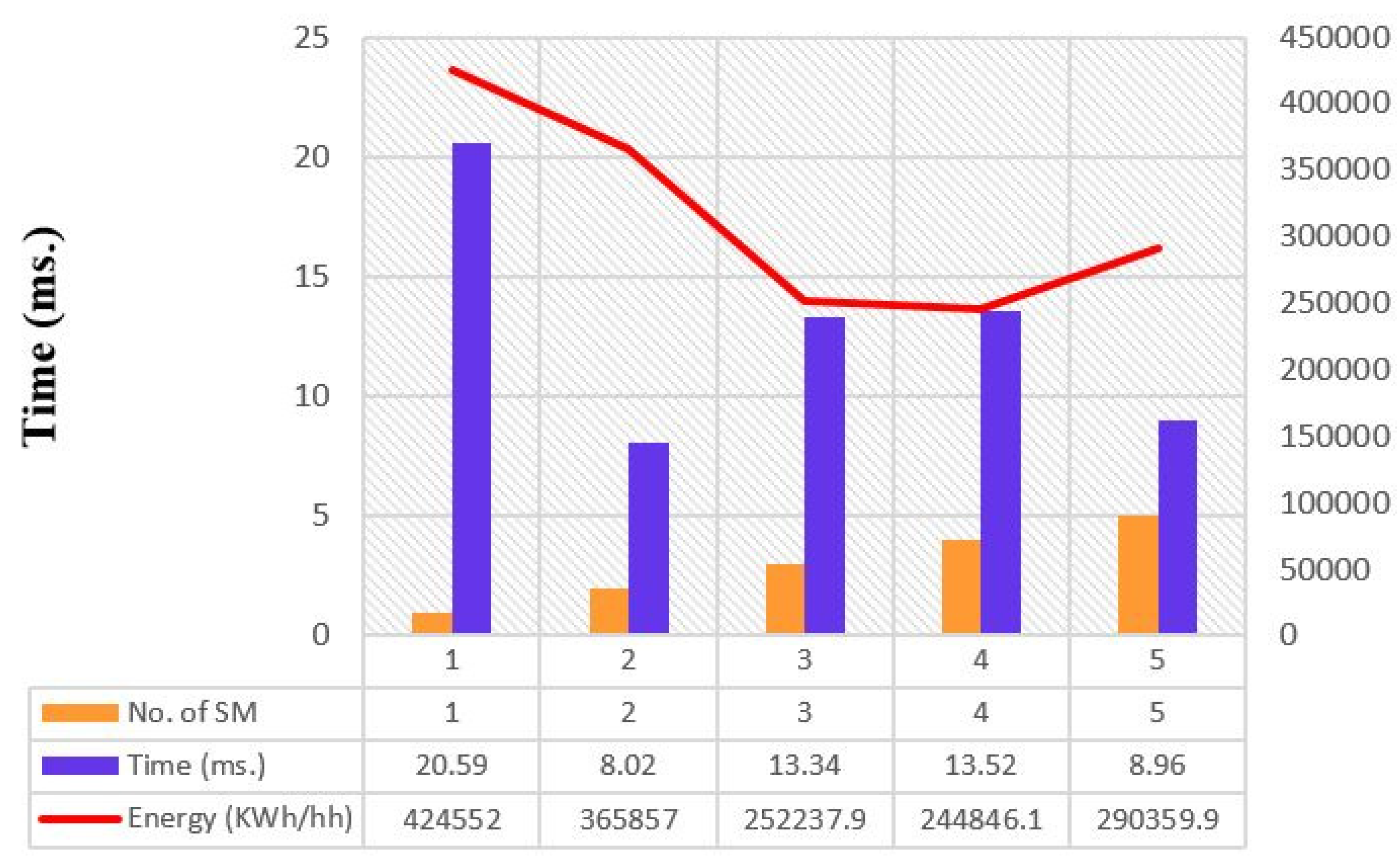
5.3. Communication and Time Cost Analysis
5.3.1. Communication Cost
5.3.2. Time Cost
5.4. Informal Security Discussion
5.4.1. Perfect Forward Secrecy (PFS) and Key Replacement Attack
5.4.2. Message Integrity, Authentication, and Signature Correctness
5.4.3. Man-in-the-Middle (MITM), Impersonation, and Replay Attack
5.4.4. Byzantine Fault Tolerance and 51% Attack
5.5. Comparative Study
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Ghosal, A.; Conti, M. Key Management Systems for Smart Grid Advanced Metering Infrastructure: A Survey. IEEE Commun. Surv. Tutor. 2019, 21, 2831–2848. [Google Scholar] [CrossRef] [Green Version]
- Alves, B. Domestic Electricity Meter Types in Operation Great Britain. Available online: https://www.statista.com/statistics/791967/domestic-electricity-meter-types-in-operation-great-britain/ (accessed on 5 June 2022).
- U.S. Smart Meter Data Management Market. Available online: https://www.alliedmarketresearch.com/us-smart-meter-data-management-market (accessed on 5 June 2022).
- Global Smart Electricity Meters Market Trends Report. 2020. Available online: https://www.grandviewresearch.com/industry-analysis/smart-meters-market (accessed on 7 December 2021).
- Islam, N.; Sultana, I.; Rahman, M.S. HKMS-AMI: A Hybrid Key Management Scheme for AMI Secure Communication. In Proceedings of the International Conference on Trends in Computational and Cognitive Engineering, Online, 21–22 October 2021; pp. 383–392. [Google Scholar]
- Merkle Charles, R. Secrecy, Authentication, and Public Key Systems; Stanford University: Stanford, CA, USA, 1979. [Google Scholar]
- Haber, S.; Stornetta, W.S. How to time-stamp a digital document. In Proceedings of the Conference on the Theory and Application of Cryptography, Aarhus, Denmark, 21–24 May 1990; pp. 437–455. [Google Scholar]
- Tsai, J.L.; Lo, N.W. Secure anonymous key distribution scheme for smart grid. IEEE Trans. Smart Grid 2015, 7, 906–914. [Google Scholar] [CrossRef]
- Uludag, S.; Lui, K.-S.; Ren, W.; Nahrstedt, K. Secure and scalable data collection with time minimization in the smart grid. IEEE Trans. Smart Grid 2016, 7, 43–54. [Google Scholar] [CrossRef] [Green Version]
- Alishahi, M.; Farhadi, M.; Jafari, S.; Taghavi, M.; Moosavi, H.; Mohajerzadeh, A. An efficient and light asymmetric cryptography to secure communication in smart grid. In Proceedings of the 2017 IEEE International Conference on Smart Energy Grid Engineering (SEGE), Oshawa, ON, Canada, 14–17 August 2017; pp. 248–252. [Google Scholar]
- Khasawneh, S.; Kadoch, M. Hybrid Cryptography Algorithm with Precomputation for Advanced Metering Infrastructure Networks. Mob. Netw. Appl. 2018, 23, 982–993. [Google Scholar] [CrossRef]
- Odelu, V.; Das, A.K.; Kumari, S.; Huang, X.; Wazid, M. Provably secure authenticated key agreement scheme for distributed mobile cloud computing services. Future Gener. Comput. Syst. 2017, 68, 74–88. [Google Scholar] [CrossRef]
- Kumar, N.; Aujla, G.S.; Das, A.K.; Conti, M. ECCAuth: A Secure Authentication Protocol for Demand Response Management in a Smart Grid System. IEEE Trans. Ind. Inform. 2019, 15, 6572–6582. [Google Scholar] [CrossRef]
- Yan, L.; Chang, Y.; Zhang, S. An efficiency batch authentication scheme for smart grid using binary authentication tree. Int. Arab J. Inf. Technol. 2019, 16, 435–441. [Google Scholar]
- Qi, M.; Chen, J. Two-Pass Privacy Preserving Authenticated Key Agreement Scheme for Smart Grid. IEEE Syst. J. 2020, 15, 3201–32077. [Google Scholar] [CrossRef]
- Olivares-Rojas, J.C.; Reyes-Archundia, E.; Gutiérrez-Gnecchi, J.A.; Cerda-Jacobo, J.; González-Murueta, J.W. A novel multitier blockchain architecture to protect data in smart metering systems. IEEE Trans. Eng. Manag. 2019, 67, 1271–1284. [Google Scholar] [CrossRef]
- Zhang, H.; Wang, J.; Ding, Y. Blockchain-based decentralized and secure keyless signature scheme for smart grid. Energy 2019, 180, 955–967. [Google Scholar] [CrossRef]
- Abou El Houda, Z.; Hafid, A.; Khoukhi, L. Blockchain meets AMI: Towards secure advanced metering infrastructures. In Proceedings of the ICC 2020-2020 IEEE International Conference on Communications (ICC), Dublin, Ireland, 7–11 June 2020. [Google Scholar]
- Zhang, L.; Li, J.; Hu, F.; Huang, Y.; Bai, J. Smart grid data access control scheme based on blockchain. Comput. Intell. 2020, 36, 1773–1784. [Google Scholar] [CrossRef]
- Melo, W.; Machado, R.C.S.; Peters, D.; Moni, M. Public-Key Infrastructure for Smart Meters using Blockchains. In Proceedings of the 2020 IEEE International Workshop on Metrology for Industry 4.0 & IoT, Roma, Italy, 3–5 June 2020. [Google Scholar]
- Zhong, Y.; Zhou, M.; Li, J.; Chen, J.; Liu, Y.; Zhao, Y.; Hu, M. Distributed Blockchain-Based Authentication and Authorization Protocol for Smart Grid. Wirel. Commun. Mob. Comput. 2021, 2021, 5560621. [Google Scholar] [CrossRef]
- Aggarwal, S.; Chaudhary, R.; Aujla, G.S.; Kumar, N.; Choo, K.K.R.; Zomaya, A.Y. Blockchain for smart communities: Applications, challenges and opportunities. J. Netw. Comput. Appl. 2019, 144, 13–48. [Google Scholar] [CrossRef]
- Liu, Z.; Luong, N.C.; Wang, W.; Niyato, D.; Wang, P.; Liang, Y.-C.; Kim, D.I. A survey on applications of game theory in blockchain. arXiv 2019, arXiv:1902.10865. [Google Scholar]
- Wang, S.; Ouyang, L.; Yuan, Y.; Ni, X.; Han, X.; Wang, F.Y. Blockchain-enabled smart contracts: Architecture, applications, and future trends. IEEE Trans. Syst. Man Cybern. Syst. 2019, 49, 2266–2277. [Google Scholar] [CrossRef]
- Gamage, H.T.M.; Weerasinghe, H.D.; Dias, N.G.J. Survey on blockchain technology concepts, applications, and issues. SN Comput. Sci. 2020, 1, 114. [Google Scholar] [CrossRef] [Green Version]
- Graf, M.; Küsters, R.; Rausch, D. Accountability in a permissioned blockchain: Formal analysis of hyperledger fabric. In Proceedings of the 2020 IEEE European Symposium on Security and Privacy (EuroS&P), Genoa, Italy, 7–11 September 2020. [Google Scholar]
- Saad, M.; Spaulding, J.; Njilla, L.; Kamhoua, C.; Shetty, S.; Nyang, D.; Mohaisen, D. Exploring the attack surface of blockchain: A comprehensive survey. IEEE Commun. Surv. Tutor. 2020, 22, 1977–2008. [Google Scholar] [CrossRef]
- Zhang, S.; Lee, J.-H. Analysis of the main consensus protocols of blockchain. ICT Express 2020, 6, 93–97. [Google Scholar] [CrossRef]
- Nino, C.A.L.; Perez, A.D.; Sandoval, M.M. Elliptic curve lightweight cryptography: A survey. IEEE Access 2018, 6, 72514–72550. [Google Scholar] [CrossRef]
- Smart Meters in London. Available online: https://www.kaggle.com/datasets/jeanmidev/smart-meters-in-london/discussion?select=halfhourly_dataset.zip (accessed on 15 February 2022).
- NIST Special Publication 1108r3. Available online: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.1108r3.pdf (accessed on 7 November 2021).

| Notations | Definition |
|---|---|
| Blockchain database | |
| A non-singular elliptic curve
over finite field | |
| A large prime number | |
| , a finite field | |
| τ | Timestamp |
| Collision resistant one-way hash function, where | |
| Hashed identity | |
| Private and public key pair | |
| ECDSA digital signature | |
| Length of private and public keys | |
| Length of ECDSA signature | |
| Length of timestamp | |
| Timestamp generation time | |
| Transaction encryption time | |
| Signature generation time |
| Transaction Header |
|---|
| Encrypted usage report, E(UD) = {PrSMi (UD || τ)}; Hash of E(UD); Sender’s hash identity, HIDSMi; ECDSA signature, SigSMi; Timestamp, τ; |
| Cryptography Operations | SM1 | SM2 | SM3 | SM4 | SM5 |
|---|---|---|---|---|---|
| Timestamp generation (Tτ) | 0.02 | 0.01 | 0.01 | 0.01 | 0.01 |
| Transaction encryption (Ttx) | 13.18 | 4.38 | 5.83 | 5.79 | 4.01 |
| Signature generation (Tsign) | 7.39 | 3.63 | 7.50 | 7.72 | 4.94 |
| Total time cost for each SM (ms) | 20.59 | 8.023 | 13.34 | 13.52 | 8.96 |
| Study | F1 | F2 | F3 | F4 | F5 | F6 | F7 | F8 | F9 | F10 |
|---|---|---|---|---|---|---|---|---|---|---|
| [19] | × | √ | √ | √ | √ | √ | √ | √ | × | × |
| [20] | × | √ | √ | √ | √ | √ | √ | √ | × | × |
| Proposed | √ | √ | √ | √ | √ | √ | √ | √ | √ | √ |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Islam, N.; Rahman, M.S.; Mahmud, I.; Sifat, M.N.A.; Cho, Y.-Z. A Blockchain-Enabled Distributed Advanced Metering Infrastructure Secure Communication (BC-AMI). Appl. Sci. 2022, 12, 7274. https://doi.org/10.3390/app12147274
Islam N, Rahman MS, Mahmud I, Sifat MNA, Cho Y-Z. A Blockchain-Enabled Distributed Advanced Metering Infrastructure Secure Communication (BC-AMI). Applied Sciences. 2022; 12(14):7274. https://doi.org/10.3390/app12147274
Chicago/Turabian StyleIslam, Nahida, Md. Sazzadur Rahman, Imtiaz Mahmud, Md. Nur Amin Sifat, and You-Ze Cho. 2022. "A Blockchain-Enabled Distributed Advanced Metering Infrastructure Secure Communication (BC-AMI)" Applied Sciences 12, no. 14: 7274. https://doi.org/10.3390/app12147274
APA StyleIslam, N., Rahman, M. S., Mahmud, I., Sifat, M. N. A., & Cho, Y.-Z. (2022). A Blockchain-Enabled Distributed Advanced Metering Infrastructure Secure Communication (BC-AMI). Applied Sciences, 12(14), 7274. https://doi.org/10.3390/app12147274








