Educational Warehouse: Modular, Private and Secure Cloudable Architecture System for Educational Data Storage, Analysis and Access
Abstract
1. Introduction
1.1. Data Revolution: Industry, Society and Education
1.2. Educational Context
1.3. Data-Related Issues
1.4. Balance between Punishment and Prevention
1.5. A Proposal for a Modular and Scalable Architecture
- allows storing, refining and analyzing educational data following the law and ethics in a way that respects all academic roles. Institutions have to be capable of applying and automating the law’s rigor in their educational solutions by default and design. Nonetheless, they should also be agile and flexible in applying their moral and ethical principles, as stated in their educational project’s mission, vision and scope, without breaking the legal regulation.
- gives the educational centers a choice between a local deployment or a cloud computing scheme but prioritizing local deployment. We propose that approach in detail in our Local Educational Data Analytics (LEDA) framework’s principles [60]. We expose the need to improve first local ad hoc solutions as an additional solution and to acknowledge the perks of using the aforementioned technological stack (big data, machine learning, artificial intelligence and cloud computing) on education yet refusing its malpractices. The seven principles of the LEDA Framework are (1) legality; (2) transparency, information and expiration; (3) data control; (4) anonymous transactions; (5) responsibility in the code; (6) interoperability; and (7) local first, where we advocate for this principle to be considered by every institution to increase the control over educational data.
2. Materials and Methods
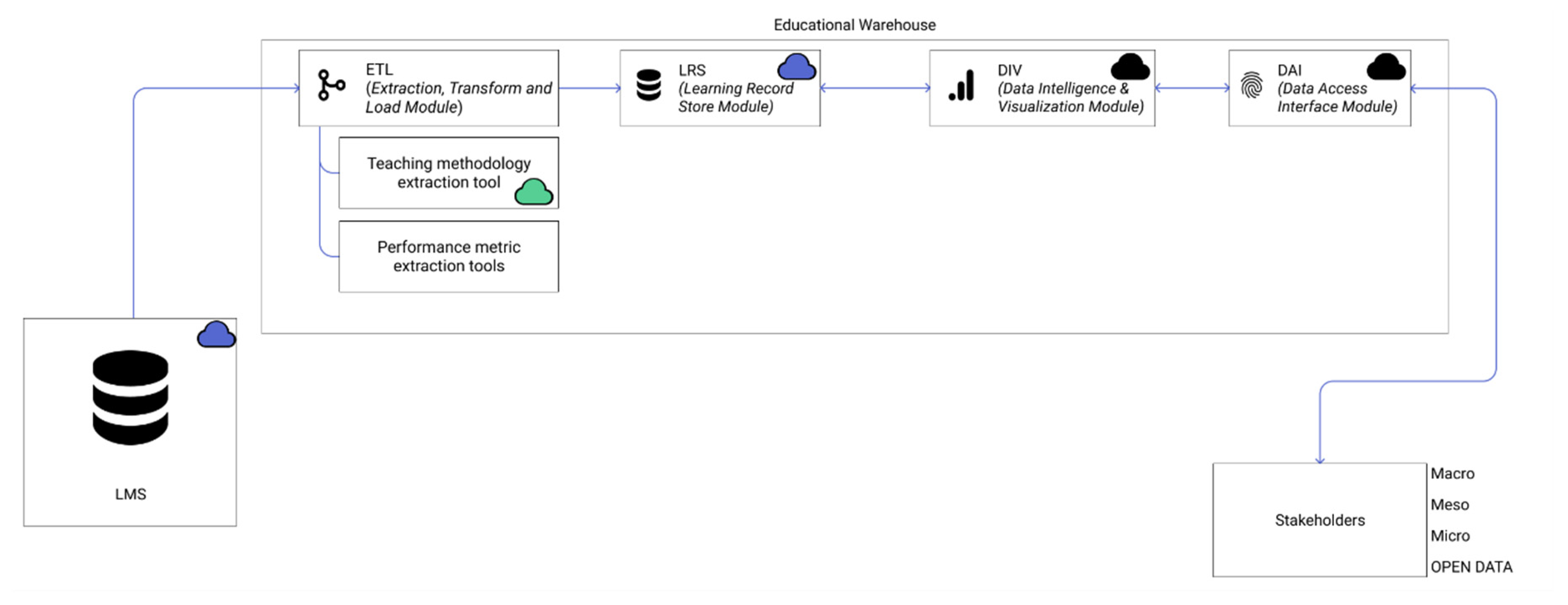
2.1. Educational Warehouse
- to be modular;
- to permit both a rigid and hybrid scenario (local or cloud computing) but with a “local first” approach;
- to use a decentralized scheme, totally or partially;
- to be scalable in terms of volume of data, processing capacity, and public and private access;
- to be technically adaptable to any educational context;
- to be private, permissioned and temporalized; and
- to automate law compliance to treat safety and privacy as transversal axes of the solution by default and by design.
- total control over data, both modular and local, once they get into the architecture. Our modular architecture performs as a data bunker with private, permissioned access. A modular architecture permits the distribution of responsibilities, privatizing access to known users and creating a taxonomy of roles and temporary permissions for acting in different parts of the architecture to limit the power of access. Moreover, the “local first” principle put in the first instance places this solution on the opposite side of cloud computing, hence ensuring an airtight space. In short, it provides local control of who or what has access to data, what for and for how long.
- a set of acceptable practices. Our modular architecture facilitates the integration of good practices further than required by law and in compliance with each institution’s morals and ethics. We will later describe a series of acceptable practices associated with each module of this architecture.
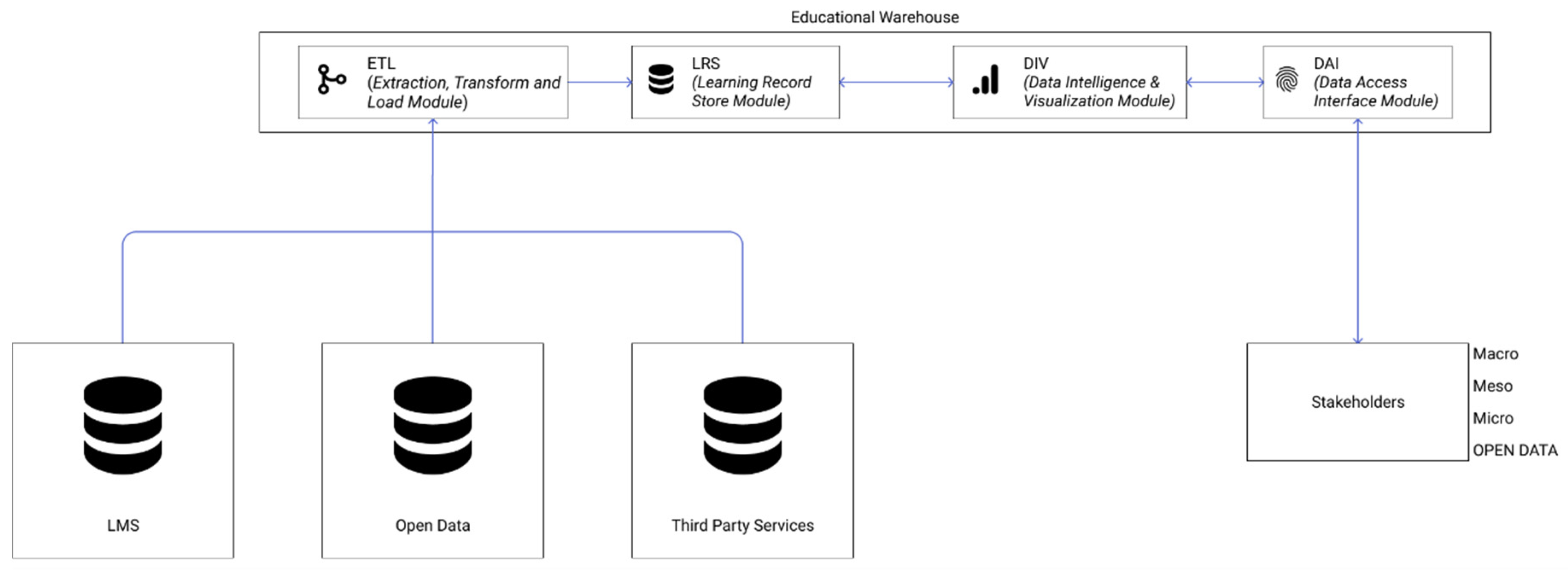
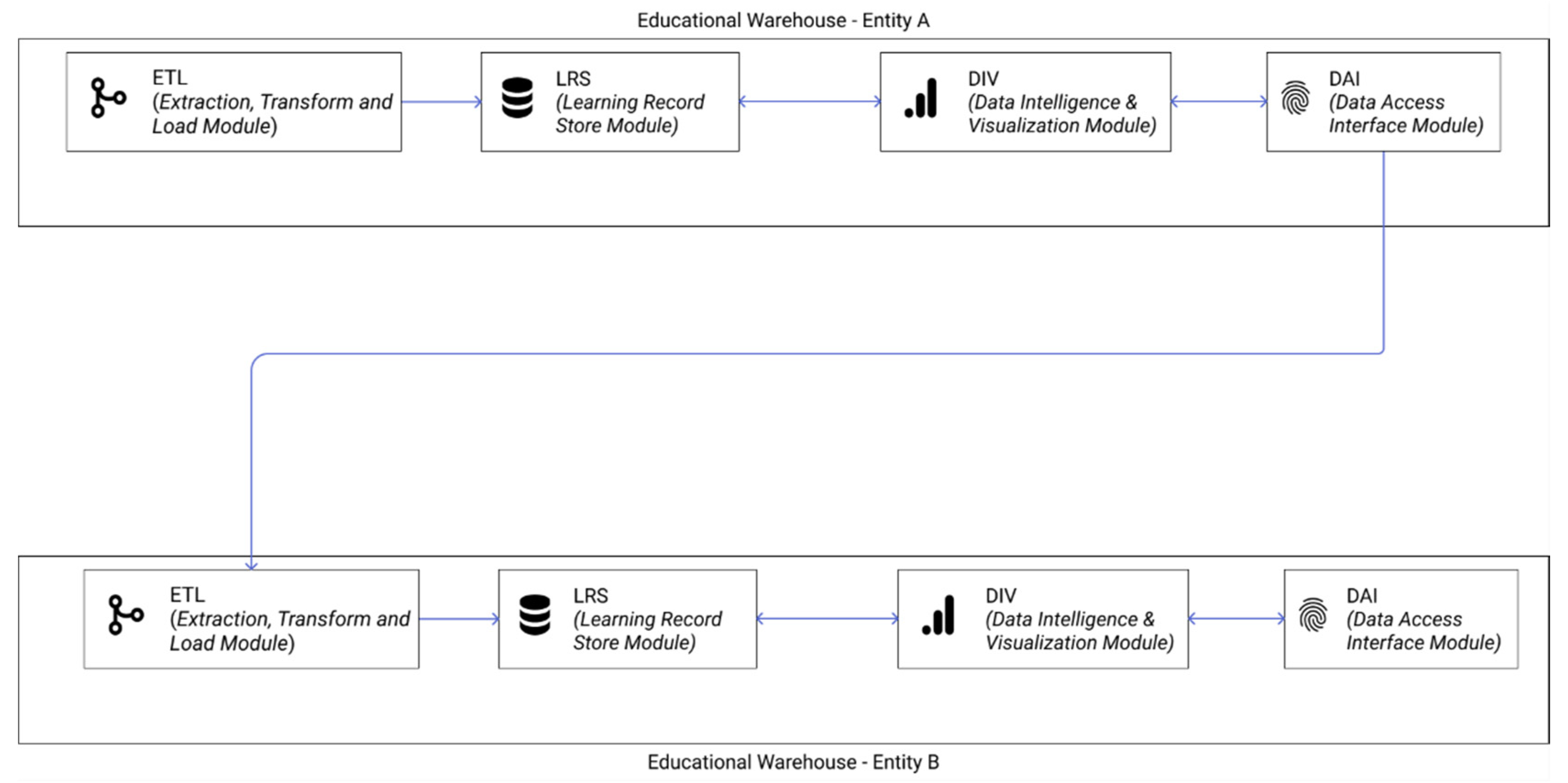
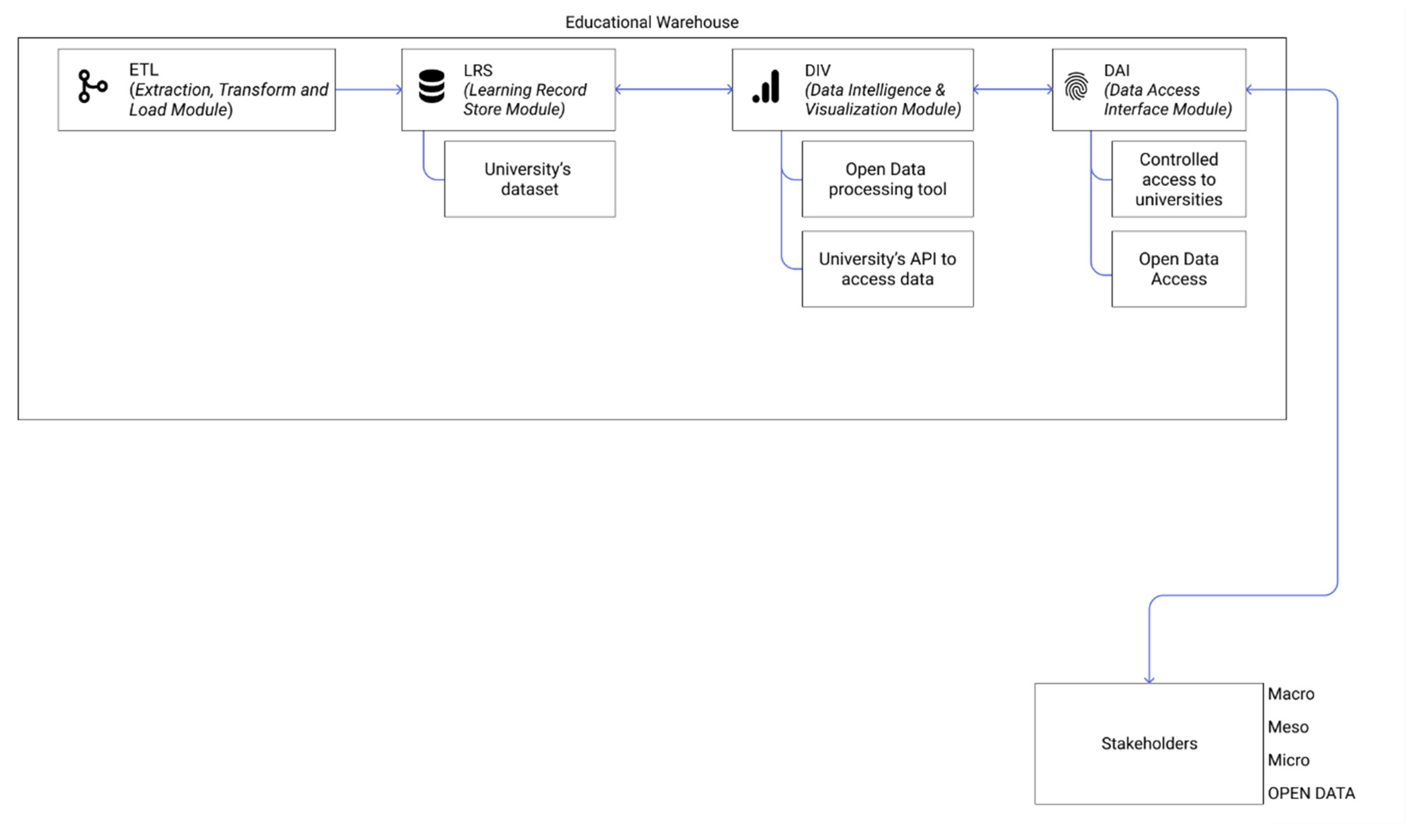
2.1.1. Basic System Architecture
- ETL: This is the module that allows importing data from abroad. It contains the software and hardware in charge of importing data from different data sources (management and educational software of the institution, EdTech, LMS, etc.). The content imported to the ETL module can be of an encrypted and anonymized nature. Once stored, it cannot be identified by any entity but the users involved, i.e., using Pretty Good Privacy (PGP) encryption technology [62]. It can also be managed securely by employing secure connections, such as Secure Shell (SSH), Secure Socket Layer (SSL) or Virtual Private Network (VPN). Regarding data management, data registries can be transferred entirely and removed from their origin, just as data from users that have not offered or consented to processing their data can be excluded as well. In the LMS or EdTech, the educational warehouse administrators may not have management competencies. However, they may demand the same good practices to ensure PICSDMPD or other more convenient ones. For instance, in the Moodle LMS, some of the authors managed to encrypt the user table since most of the personal data reside there and used a set of views that allow decryption or encryption at convenience. This measure can be complemented by ensuring students’ anonymity through second identities with the Protected Users plugin [32], thus not exporting data that can be used to identify people. The entire database can also be encrypted with a double user control system where not even the administrator can access or decrypt the data. Some of the authors of this paper conceived such a system and named it AuthChecker [35]; simple authentications, private and permissioned Application Program Interfaces (API), and Learning Tools Interoperability (LTI) technologies are recommended to ensure data access by manually specified roles.
- LRS: This is the module where data are stored. It contains all that software and hardware needed to store the data in the original format or as the result of transformations and analyses. The private and secure nature of data can be guaranteed by defining temporary and regulated accesses, with users generated by a previous contract with the institution; by storing encrypted data; by or applying change control protocols (integrations through high-level log systems, definition of non-editable data, etc.), among other practices.
- DIV: This module analyses and visualizes information internally. It contains all the software and hardware in charge of performing the institution’s analytical approaches and the data visualization tools. Information given to those systems can be pseudo-anonymized or anonymized. Their response, being equally masked, can be integrated into the LRS module as far as no correlation of data with real identities is guaranteed. Modularity allows LRS to be hosted locally while DIV resides in cloud computing, making it necessary to encrypt the roaming data or to even use private connections such as SSH, SSL or VPN.
- DAI: This module controls access to data according to legal regulations. It contains all the software and hardware that permits internal solutions and other educational institutions, government and administrations, partners and third-party collaborators to access data under a private and regulated regime. At the same time, it could serve as open data for public benefit. It manages access to the information securely. A set of essential, contractual permissions can be defined automatically in the user creation process. This is the case of accessing one’s action history or the acceptance or rejection of data transfer agreements. Each user profile may request an extension of its capabilities under a manual review process; this process may generate a set of legal bonds that will detail the relationship between the user and the system. The reviewers, i.e., the data privacy officer in the case of GDPR, may reject the request. A set of permissions that do not require an extensive legal bond can also be offered using under-request automatic approval procedures, allowing easy access to research data and collaboration for open data consortiums.
- Meso-level analytics operates at the institution level through business intelligence. The objective of this level is, among other institutional aspects, the improvement of the different educational processes at the institutional level and strategic business decision-making, for example, to identify those courses that are more effective or functional. Its benefits are linked to the optimization of decision-making at the administrative level, the increment of educational “production” and even improvements in resource allocation.
- Micro-level analytics: This level addresses the analysis of the interactions carried out by every student, both independently and as a part of a group. These analytical processes include personal and sensitive student data, such as book loans, geolocations, financial data, social media conversations or even the clickstream of virtual learning environments. The benefits of this level result in a system that can identify students at risk, alert of possible dropouts and even provide students with conclusions and advice that can help them improve. The micro level is intended to be introduced to coordinators and instructors who deliver content to students and evaluate their work.
- Open-data analytics: all educational institutions are likely to generate anonymized data. Making them public in a raw format or even in a processed format evokes a desire for transparency and open knowledge that can be advantageous to society. This open level of data is accessible to any independent person, research group, third party or citizen who requires access to data that educational institutions, especially public ones, can make available without violating student data privacy or security.
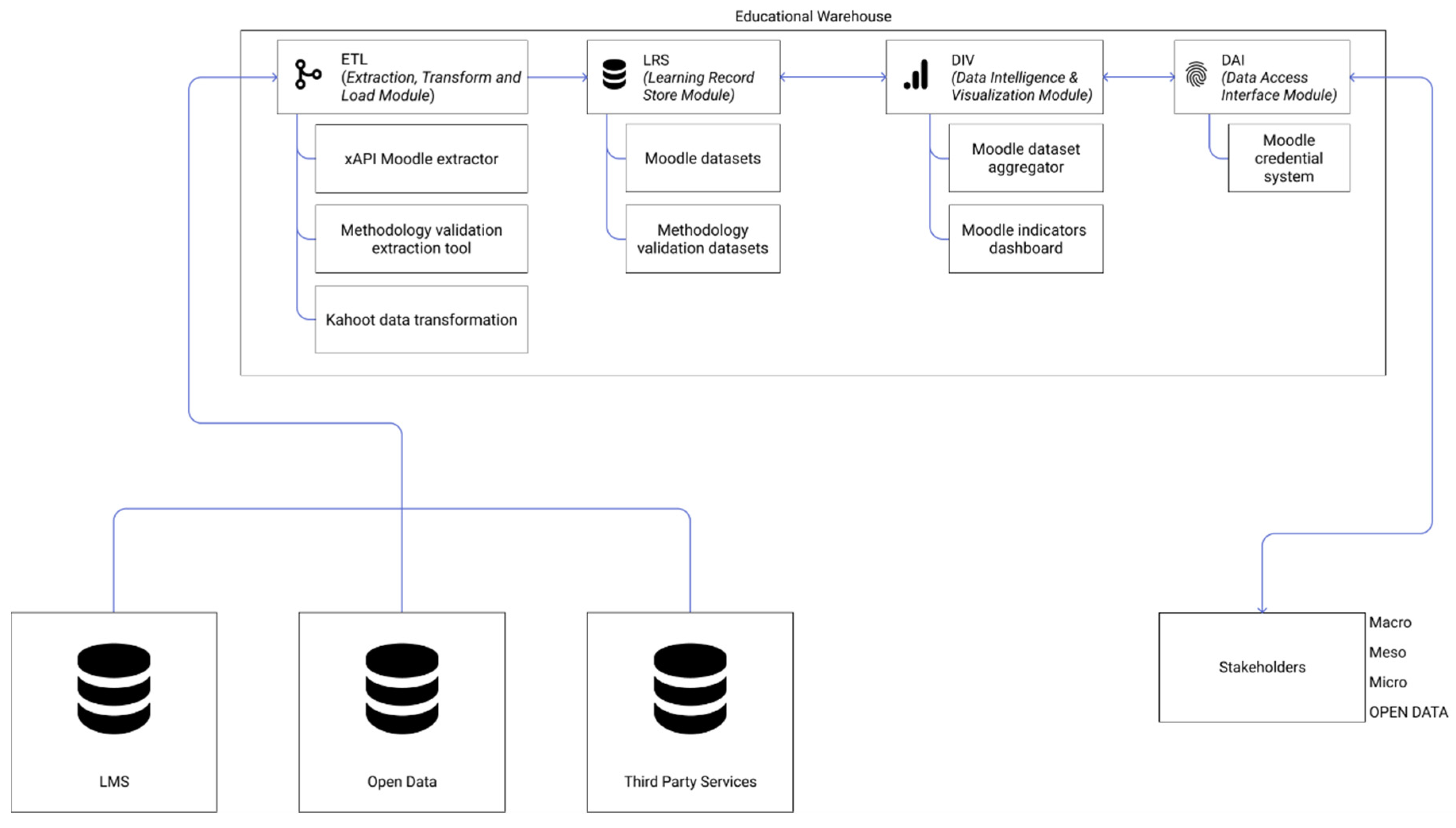
2.1.2. Use Cases
3. Results
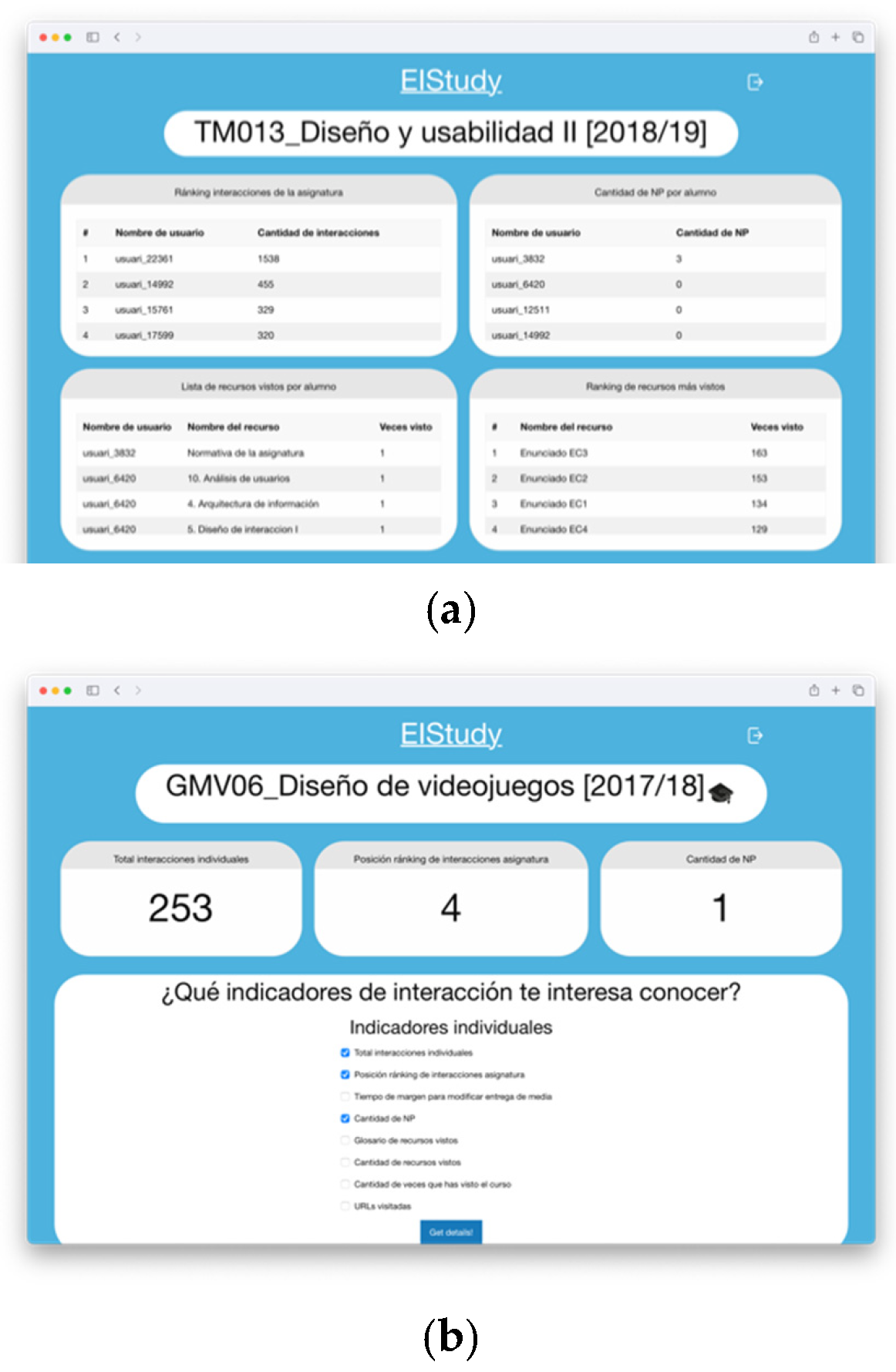
Moodle’s Executive Interaction Board
- ETL and LRS modules: Initially, the loaded data are based on the Moodle reports. Thanks to Moodle’s relational model, information can be extracted that describes user’s interactions with the platform using different levels of detail.
- DIV module: This solution offers a micro-level analysis using students’ highly detailed, sensitive, personal and behavioral data. The data are anonymized to preserve the student’s identities while presenting related information.
- DAI module: This interface’s development to access data considers the LMS user roles (see Figure 6). The user is offered a set of indicators depending on whether they are a teacher or a student (see Figure 7). A teacher had access to viewing the data of the students in the course. A student has access to only their data but not that of other classmates in the course, thus avoiding privacy conflicts.
4. Discussion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Marciano, A.; Nicita, A.; Ramello, G.B. Puzzles in the big data revolution: An introduction. Eur. J. Law Econ. 2020, 1–6. [Google Scholar] [CrossRef]
- Gong, C.; Liu, J.; Zhang, Q.; Chen, H.; Gong, Z. The characteristics of cloud computing. In Proceedings of the International Conference on Parallel Processing Workshops, San Diego, CA, USA, 13–16 September 2010; pp. 275–279. [Google Scholar]
- Pallis, G. Cloud computing: The new frontier of internet computing. IEEE Internet Comput. 2010, 14, 70–73. [Google Scholar] [CrossRef]
- Chang, V.; Bacigalupo, D.; Wills, G.; De Roure, D. A categorisation of cloud computing business models. In Proceedings of the CCGrid 2010—10th IEEE/ACM International Conference on Cluster, Cloud, and Grid Computing, Melbourne, VIC, Australia, 17–20 May 2010; pp. 509–512. [Google Scholar]
- Marston, S.; Li, Z.; Bandyopadhyay, S.; Zhang, J.; Ghalsasi, A. Cloud computing—The business perspective. Decis. Support Syst. 2011, 51, 176–189. [Google Scholar] [CrossRef]
- Qiu, T.; Chi, J.; Zhou, X.; Ning, Z.; Atiquzzaman, M.; Wu, D.O. Edge Computing in Industrial Internet of Things: Architecture, Advances and Challenges. IEEE Commun. Surv. Tutor. 2020. [Google Scholar] [CrossRef]
- Morrar, R.; Arman, H.; Mousa, S. The fourth industrial revolution (Industry 4.0): A social innovation perspective. Technol. Innov. Manag. Rev. 2017, 7, 12–20. [Google Scholar] [CrossRef]
- Perc, M.; Ozer, M.; Hojnik, J. Social and juristic challenges of artificial intelligence. Palgrave Commun. 2019, 5, 1–7. [Google Scholar] [CrossRef]
- Bechmann, A.; Kim, J.Y. Big Data. In Handbook of Research Ethics and Scientific Integrity; Iphofen, R., Ed.; Springer International Publishing: Cham, Switzerland, 2020; pp. 427–444. ISBN 978-3-030-16759-2. [Google Scholar]
- Dixon-Román, E.; Parisi, L. Data capitalism and the counter futures of ethics in artificial intelligence. Commun. Public 2020. [Google Scholar] [CrossRef]
- Coghlan, S.; Miller, T.; Paterson, J. Good proctor or “Big Brother”? AI Ethics and Online Exam Supervision Technologies. arXiv 2020, arXiv:2011.07647. [Google Scholar]
- Michie, D.; Spiegelhalter, D.J.; Taylor, C.C. Machine learning. Neural Stat. Classif. 1994, 13, 1–298. [Google Scholar]
- Murphy, B.; Rocchi, M. Ethics and Cloud Computing. In Data Privacy and Trust in Cloud Computing; Palgrave Macmillan: Cham, Switzerland, 2021; pp. 105–128. [Google Scholar]
- Data Privacy and Trust in Cloud Computing. Available online: https://library.oapen.org/handle/20.500.12657/42922 (accessed on 30 November 2020).
- Bellamy Foster, J. Surveillance Capitalism. Mon. Rev. 2014, 66, 1–31. [Google Scholar] [CrossRef]
- West, S.M. Data Capitalism: Redefining the Logics of Surveillance and Privacy. Bus. Soc. 2019, 58, 20–41. [Google Scholar] [CrossRef]
- Zuboff, S. Surveillance Capitalism and the Challenge of Collective Action. In Proceedings of the New Labor Forum; SAGE Publications: Los Angeles, CA, USA, 2019; Volume 28, pp. 10–29. [Google Scholar]
- Onik, M.M.H.; Kim, C.S.; Yang, J. Personal Data Privacy Challenges of the Fourth Industrial Revolution. In Proceedings of the International Conference on Advanced Communication Technology, ICACT, PyeongChang, Korea, 17–20 February 2019; Volume 2019, pp. 635–638. [Google Scholar]
- Zuboff, S. Big other: Surveillance capitalism and the prospects of an information civilization. J. Inf. Technol. 2015, 30, 75–89. [Google Scholar] [CrossRef]
- Shahroom, A.A.; Hussin, N. Industrial Revolution 4.0 and Education. Int. J. Acad. Res. Bus. Soc. Sci. 2018, 8, 314–319. [Google Scholar] [CrossRef]
- Celaa Saluda la Alianza de Grandes Empresas para Innovar en la Educación. Available online: https://www.lavanguardia.com/vida/20201029/4968492825/celaa-saluda-la-alianza-de-grandes-empresas-para-innovar-en-la-educacion.html (accessed on 30 November 2020).
- Realising the Potential of Technology in Education. Available online: https://www.gov.uk/government/publications/realising-the-potential-of-technology-in-education (accessed on 30 November 2020).
- Ainley, P. The new ‘market-state’and education. J. Educ. Policy 2004, 19, 497–514. [Google Scholar] [CrossRef]
- Mathur, K. State, Market and Governance of Higher Education. Gov. Manag. High. Educ. India 2020, 25–43. [Google Scholar]
- Nazarenko, M.A.; Khronusova, T.V. Big data in modern higher education. Benefits and criticism. In Proceedings of the 2017 International Conference “Quality Management, Transport and Information Security, Information Technologies” (IT and QM and IS), St. Petersburg, Russia, 24–30 September 2017; pp. 676–679. [Google Scholar]
- Picciano, A. Big Data and Learning Analytics in Blended Learning Environments: Benefits and Concerns. Int. J. Interact. Multimed. Artif. Intell. 2014, 2, 35. [Google Scholar] [CrossRef]
- Ekong, E.E.; Adiat, Q.E.; Ejemeyovwi, J.O.; Alalade, A.M. Harnessing big data technology to benefit effective delivery and performance maximization in pedagogy. Int. J. Civ. Eng. Technol. 2019, 10, 2170–2178. [Google Scholar]
- Cavazos, J.G.; Jonathon Phillips, P.; Castillo, C.D.; O’Toole, A.J. Accuracy comparison across face recognition algorithms: Where are we on measuring race bias? arXiv 2019, arXiv:1912.07398. [Google Scholar] [CrossRef]
- Schrag, F. Review of Weapons of Math Destruction: How Big Data Increases Inequality and Threatens Democracy; Broadway Books: New York, NY, USA, 2017; Volume 24. [Google Scholar]
- Lessons from the A-Levels Fiasco: Putting Culture and Values at the Heart of Policymaking. Available online: https://blogs.lse.ac.uk/politicsandpolicy/culture-values-policymaking/ (accessed on 10 September 2020).
- Amo Filva, D. Privacidad y Gestión de la Identidad en Procesos de Analítica de Aprendizaje. Programa de Doctorado Formación en la Sociedad del Conocimiento. Available online: https://repositorio.grial.eu/handle/grial/1951 (accessed on 31 January 2020).
- Amo, D.; Alier, M.; García-Peñalvo, F.J.; Fonseca, D.; Casañ, M.J. Protected Users: A Moodle Plugin to Improve Confidentiality and Privacy Support through User Aliases. Sustainability 2020, 12, 2548. [Google Scholar] [CrossRef]
- Amo, D.; Alier, M.; García-Peñalvo, F.; Fonseca, D.; Casañ, M.J. Privacidad, seguridad y legalidad en soluciones educativas basadas en Blockchain: Una Revisión Sistemática de la Literatura. RIED. Rev. Iberoam. Educ. Distancia 2020, 23, 213. [Google Scholar] [CrossRef]
- Amo, D.; Alier, M.; Fonseca, D.; García-Peñalvo, F.-J.; Casañ, M.J.; Navarro, J. Evaluation of the importance of ethics, privacy and security in Learning Analytics studies, under the LAK conferences. In Proceedings of the CINAIC, Madrid, Spain, 9–11 October 2019. [Google Scholar]
- Amo, D.; Alier, M.; García-Peñalvo, F.J.; Fonseca, D.; Casany, M.J. GDPR security and confidentiality compliance in LMS’ a problem analysis and engineering solution proposal. In Proceedings of the ACM International Conference Proceeding Series; Conde, M.Á., Rodríguez, F.J., Fernández, C., García-Peñalvo, F.J., Eds.; ACM: New York, NY, USA, 2019; pp. 253–259. [Google Scholar]
- Pearson Data Breach: Details of Hundreds of Thousands of U.S. Students Hacked. Available online: https://www.fastcompany.com/90384759/pearson-data-breach-details-of-hundreds-of-thousands-of-u-s-students-hacked (accessed on 20 February 2019).
- Drachsler, H.; Greller, W. Privacy and analytics: It’s a DELICATE issue a checklist for trusted learning analytics. In Proceedings of the Sixth International Conference on Learning Analytics & Knowledge, Edinburgh, Scotland, 25–29 April 2016; pp. 89–98. [Google Scholar]
- US Schools Have Lost 24.5 Million Records in Breaches Since 2005. Available online: https://www.techrepublic.com/article/us-schools-have-lost-24-5-million-records-in-breaches-since-2005/ (accessed on 3 July 2020).
- Student Loans Company Criticised over Data Breaches. Available online: https://www.bbc.com/news/education-27587152 (accessed on 3 July 2020).
- Una Brecha de Datos deja Expuesta Información Personal de Millones de Padres y Alumnos de Madrid. Available online: https://www.elplural.com/autonomias/fallo-informatico-deja-expuestos-datos-personales-millones-padres-alumnos-madrid_252050102 (accessed on 21 November 2020).
- El Web de la Generalitat Exposa més de 5.000 Dades que Inclouen Correus i Contrasenyes. Available online: https://elmon.cat/politica/web-generalitat-exposa-5000-dades-inclouen-correus-contrasenyes-187168/ (accessed on 30 November 2020).
- Amo, D.; Alier, M.; Casan, M.J.; Casañ, M.J. The student’s progress snapshot a hybrid text and visual learning analytics dashboard. Int. J. Eng. Educ. 2018, 34, 990–1000. [Google Scholar]
- Lafarre, A.; Van der Elst, C. Legal tech and blockchain for corporate governance and shareholders. In Research Handbook in Data Science and Law; Edward Elgar Publishing: Cheltenham, UK, 2018; ISBN 9781788111294. [Google Scholar]
- Tracol, X. “Schrems II”: The return of the Privacy Shield. Comput. Law Secur. Rev. 2020, 39, 105484. [Google Scholar] [CrossRef]
- Schrems, M. The Privacy Shield is a Soft Update of the Safe Harbor. Eur. Data Prot. Law Rev. 2017, 2, 148–150. [Google Scholar] [CrossRef]
- Tzanou, M. Schrems I and Schrems II: Assessing the Case for the Extraterritoriality of EU Fundamental Rights. 2020. Available online: https://ssrn.com/abstract=3710539 (accessed on 15 January 2021).
- Kuner, C. Reality and Illusion in EU Data Transfer Regulation Post Schrems. SSRN Electron. J. 2018, 18, 881–918. [Google Scholar] [CrossRef]
- Greenleaf, G.; Systems, I. International Data Privacy Agreements after the GDPR and Schrems. Priv. Laws Bus. Int’l Rep. 2016, 139, 12–15. [Google Scholar]
- Bräutigam, T. The Land of Confusion: International Data Transfers between Schrems and the GDPR. 2016, pp. 143–177. Available online: https://ssrn.com/abstract=2920181 (accessed on 15 January 2021).
- Weiss, M.A.; Archick, K.U.S. EU data privacy: From safe harbor to privacy shield. Eur. Union Chall. Prospect. 2016, 113–135. [Google Scholar]
- Regulation (EU) 2016/679 GDPR. Available online: https://eur-lex.europa.eu/eli/reg/2016/679/oj (accessed on 27 June 2019).
- Rothstein, M.A.; Tovino, S.A. California Takes the Lead on Data Privacy Law. Hastings Cent. Rep. 2019, 49, 4–5. [Google Scholar] [CrossRef]
- Data Protection & Privacy. Available online: https://practiceguides.chambers.com/practice-guides/data-protection-privacy-2020/australia (accessed on 30 November 2020).
- New Analysis Shows How Facebook and Google Push Users into Sharing Personal Data. Available online: https://www.forbrukerradet.no/side/facebook-and-google-manipulate-users-into-sharing-personal-data/ (accessed on 30 November 2020).
- New Study: Google Manipulates Users into Constant Tracking. Available online: https://www.forbrukerradet.no/side/google-manipulates-users-into-constant-tracking/ (accessed on 30 November 2020).
- Use of Google Chromebook and G Suite for Education (and other Cloud Services) in Elementary School. Available online: https://www.datatilsynet.no/personvern-pa-ulike-omrader/skole-barn-unge/bruk-av-google-chromebook-og-g-suite-for-education-og-andre-skytjenester-i-grunnskolen/ (accessed on 30 November 2020).
- Buchholtz, G. Artificial Intelligence and Legal Tech: Challenges to the Rule of Law. In Regulating Artificial Intelligence; Wischmeyer, T., Rademacher, T., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 175–198. ISBN 978-3-030-32361-5. [Google Scholar]
- Hildebrandt, M. 10. ‘Legal by Design’ or ‘Legal Protection by Design’? In Law for Computer Scientists and Other Folk; Oxford University Press: Oxford, UK, 2019; pp. 251–283. [Google Scholar]
- Hildebrandt, M.; Tielemans, L. Data protection by design and technology neutral law. Comput. Law Secur. Rev. 2013, 29, 509–521. [Google Scholar] [CrossRef]
- Amo, D.; Torres, R.; Canaleta, X.; Herrero-Martín, J.; Rodríguez, C.; Fonseca, D. Seven principles to foster privacy and security in educational tools: Local Educational Data Analytics. In Proceedings of the Technological Ecosystems for Enhancing Multiculturality, TEEM’20, Online Conference, 21–23 October 2020; Available online: https://2020.teemconference.eu/papers-in-video/ (accessed on 23 October 2020).
- Amo, D.; Fonseca, D.; Alier, M.; García-Peñalvo, F.J.; Casañ, M.J.; Alsina, M. Personal Data Broker: A Solution to Assure Data Privacy in EdTech. In Proceedings of the HCII: International Conference on Human-Computer Interaction. Learning and Collaboration Technologies, Orlando, FL, USA, 26–31 July 2019; Designing Learning Experience.. Zaphiris, P., Loannou, A., Eds.; 2019; Volume 11590 LNCS, pp. 3–14. [Google Scholar]
- Zimmermann, P.R.; Zimmermann, P.R. The Official PGP User’s Guide; MIT Press: Cambridge, UK, 1995; Volume 5. [Google Scholar]
- Prinsloo, P. Stuck in the middle? Making sense of the impact of micro, meso and macro institutional, structural and organisational factors on implementing learning analytics. In Proceedings of the Exploring the Micro, Meso and Macro Proceedings of the European Distance and E-Learning Network 2018 Annual Conference, Genoa, Italy, 17–20 June 2018; pp. 17–20. [Google Scholar]
- Learning Analytics: Policy Briefing. Available online: http://iite.unesco.org/files/policy_briefs/pdf/en/learning_analytics.pdf (accessed on 13 February 2019).
- Aziz, A.A.; Jusoh, J.A.; Hassan, H.; Rizhan Wan Idris, W.M.; Md Zulkifli, A.P.; Mohamed Yusof, S.A. A framework for educational data warehouse (EDW) architecture using business intelligence (BI) technologies. J. Theor. Appl. Inf. Technol. 2014, 69, 50–58. [Google Scholar]
- Flanagan, B.; Ogata, H. Integration of learning analytics research and production systems while protecting privacy. In Proceedings of the ICCE 2017—25th International Conference on Computers in Education: Technology and Innovation: Computer-Based Educational Systems for the 21st Century, Workshop Proceedings, Christchurch, New Zeland, 4–8 December 2017; pp. 355–360. [Google Scholar]
- Kahoot Kahoot! Learning Games & Make Learning Awesome! Available online: http://kahoot.it (accessed on 20 January 2018).
- Alsina, M.; Canaleta, X.; Cubeles, A.; Torres, R. Self Directed Based Learning, una Metodología de Aprendizaje para Programas no Presenciales. In Proceedings of the Actas del V Congreso Internacional sobre Aprendizaje, Innovación y Cooperación, CINAIC 2019, Madrid, España, 9–11 October 2019; pp. 325–330. [Google Scholar]
- L’Heureux, A.; Grolinger, K.; Elyamany, H.F.; Capretz, M.A.M. Machine Learning with Big Data: Challenges and Approaches. IEEE Access 2017, 5, 7776–7797. [Google Scholar] [CrossRef]
- Marciano, A.; Nicita, A.; Ramello, G.B. Big data and big techs: Understanding the value of information in platform capitalism. Eur. J. Law Econ. 2020, 50, 345–358. [Google Scholar] [CrossRef]
- Luhn, H.P. The Automatic Creation of Literature Abstracts. IBM J. Res. Dev. 1958, 2, 159–165. [Google Scholar] [CrossRef]
- Luhn, H.P. A Business Intelligence System. IBM J. Res. Dev. 1958, 2, 314–319. [Google Scholar] [CrossRef]
- Gore, A. The Information Highway. Exec. Educ. 1994, 16, 30–31. [Google Scholar]
- Wiggins, R. Al Gore and the creation of the Internet. First Monday 2000, 5. [Google Scholar] [CrossRef]
- Romero, C.; Ventura, S. Data mining in education. Wiley Interdiscip. Rev. Data Min. Knowl. Discov. 2013, 3, 12–27. [Google Scholar] [CrossRef]
- Siemens, G. Learning Analytics: The Emergence of a Discipline. Am. Behav. Sci. 2013, 57, 1380–1400. [Google Scholar] [CrossRef]
- Duval, E. Learning Analytics and Educational Data Mining. Available online: https://erikduval.wordpress.com/2012/01/30/learning-analytics-and-educational-data-mining/ (accessed on 24 July 2018).
- Siemens, G.; d Baker, R.S.J. Learning analytics and educational data mining: Towards communication and collaboration. In Proceedings of the 2nd International Conference on Learning Analytics and Knowledge, Vancouver, BC, Canada, 29 April–2 May 2012; pp. 252–254. [Google Scholar]
- Merceron, A.; Blikstein, P.; Siemens, G. Learning Analytics: From Big Data to Meaningful Data. J. Learn. Anal. 2016, 2, 4–8. [Google Scholar] [CrossRef]
- Berners-Lee, T.; Fielding, R.; Frystyk, H. Hypertext Transfer Protocol--HTTP/1.0 1996. Available online: http://www.hjp.at/doc/rfc/rfc1945.html (accessed on 20 July 2020).
- Slade, S.; Prinsloo, P. Learning Analytics: Ethical Issues and Dilemmas. Am. Behav. Sci. 2013, 57, 1510–1529. [Google Scholar] [CrossRef]
- A Flawed Algorithm Led the UK to Deport Thousands of Students. Available online: https://qz.com/1268231/a-toeic-test-led-the-uk-to-deport-thousands-of-students/ (accessed on 30 November 2020).
- Bakharia, A.; Kitto, K.; Pardo, A.; Gaševíc, D.; Dawson, S. Recipe for Success—Lessons learnt from using xAPI within the connected learning analytics toolkit. In Proceedings of the ACM International Conference Proceeding Series, Edinburgh, Scotland, 25–29 April 2016; pp. 378–382. [Google Scholar]
- Herrero-Martín, J.; Canaleta, X.; Fonseca, D.; Merino, C.R.; Kinnear, L.; Amo, D. Designing a Multi-Scale and Multi-Dimensional Assessment for a New National Educational Context. In Proceedings of the Technological Ecosystems for Enhancing Multiculturality, TEEM’20, Online Conference, 21–23 October 2020; Available online: https://youtu.be/Qu7xAO3Om28 (accessed on 23 October 2020).

Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Amo, D.; Gómez, P.; Hernández-Ibáñez, L.; Fonseca, D. Educational Warehouse: Modular, Private and Secure Cloudable Architecture System for Educational Data Storage, Analysis and Access. Appl. Sci. 2021, 11, 806. https://doi.org/10.3390/app11020806
Amo D, Gómez P, Hernández-Ibáñez L, Fonseca D. Educational Warehouse: Modular, Private and Secure Cloudable Architecture System for Educational Data Storage, Analysis and Access. Applied Sciences. 2021; 11(2):806. https://doi.org/10.3390/app11020806
Chicago/Turabian StyleAmo, Daniel, Pablo Gómez, Luis Hernández-Ibáñez, and David Fonseca. 2021. "Educational Warehouse: Modular, Private and Secure Cloudable Architecture System for Educational Data Storage, Analysis and Access" Applied Sciences 11, no. 2: 806. https://doi.org/10.3390/app11020806
APA StyleAmo, D., Gómez, P., Hernández-Ibáñez, L., & Fonseca, D. (2021). Educational Warehouse: Modular, Private and Secure Cloudable Architecture System for Educational Data Storage, Analysis and Access. Applied Sciences, 11(2), 806. https://doi.org/10.3390/app11020806






