Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study
Abstract
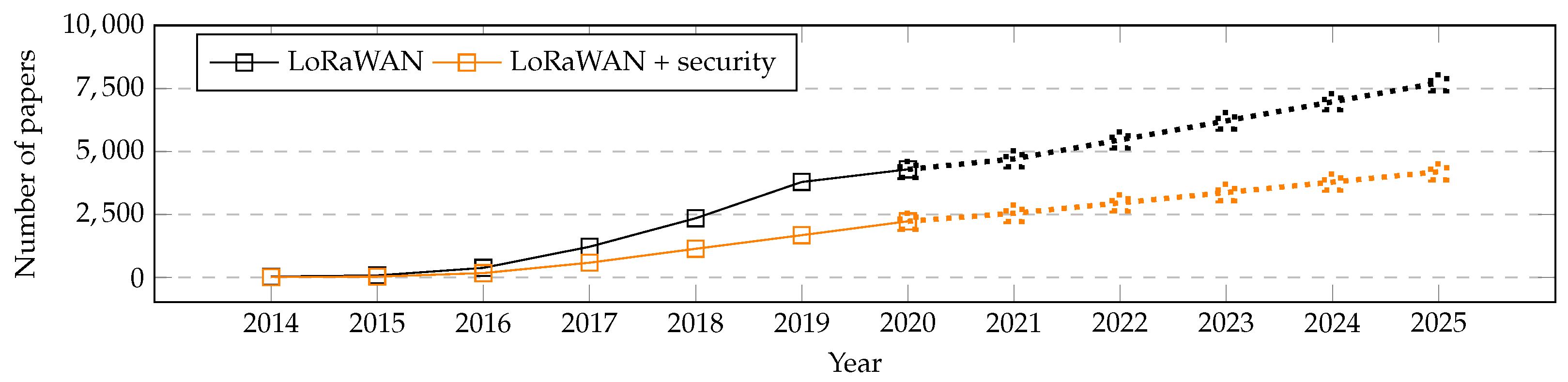
:1. Introduction
- We provide an overview of the state-of-the-art for cyber security for LoRaWAN technology.
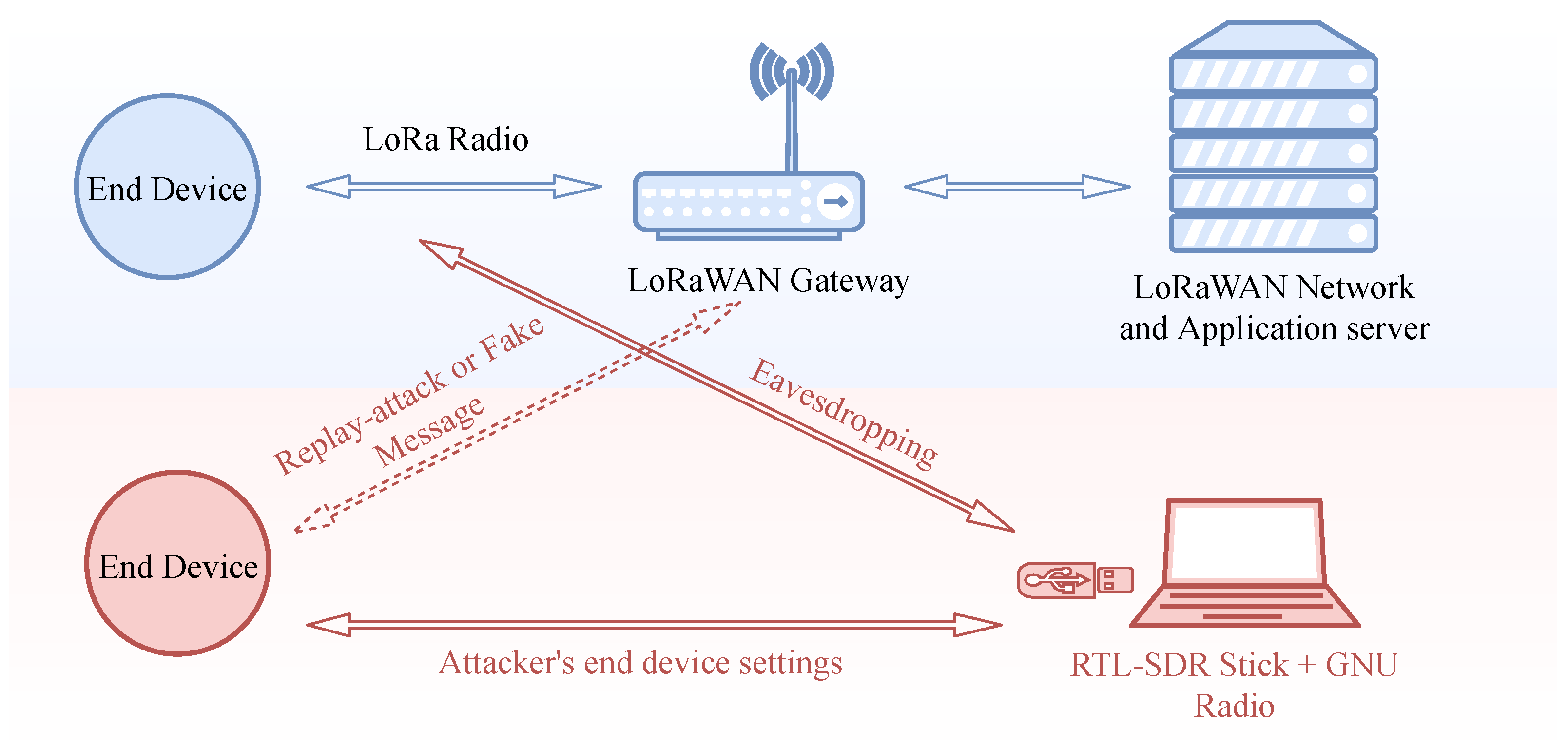
- We detail the design of an software-defined radio (SDR)-based testbed for trialing the LoRaWAN security in practice.
- We demonstrate the operation of the designed testbed through investigating the two practical LoRaWAN attacks, study their effects and discuss the possible ways to mitigate them. Specifically, we focus on replay and bit-flipping (i.e., change of message content) attacks. These two attacks have been selected due to their potential to have a devastating effect on infrastructure monitoring applications, which are among the core use case of LoRaWAN.
2. Background
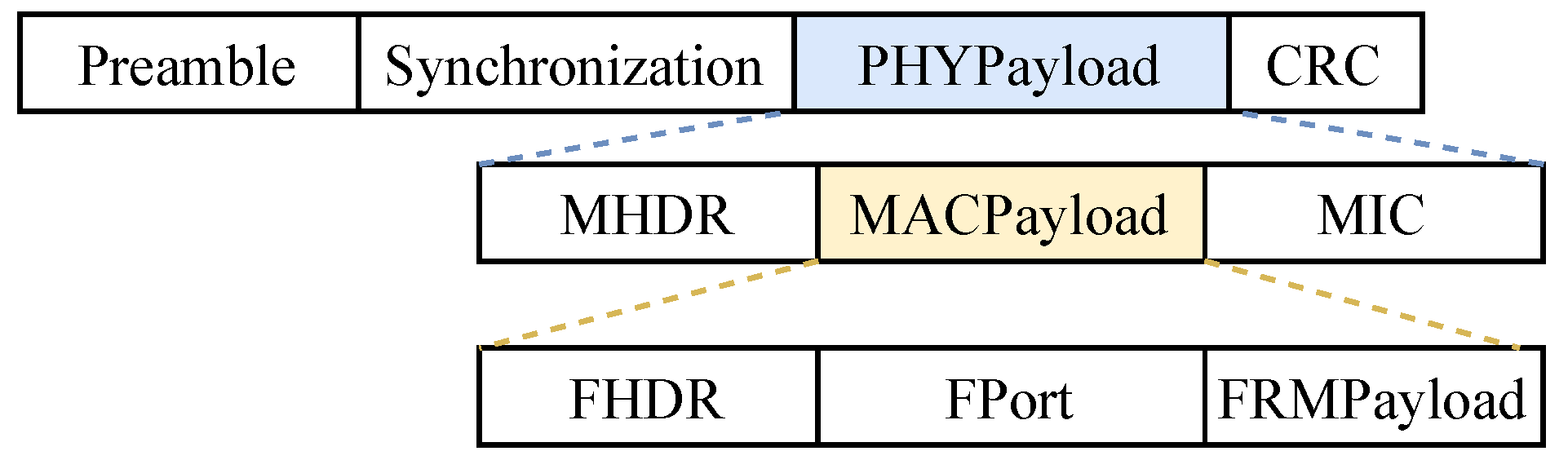
2.1. LoRa and LoRaWAN Basics
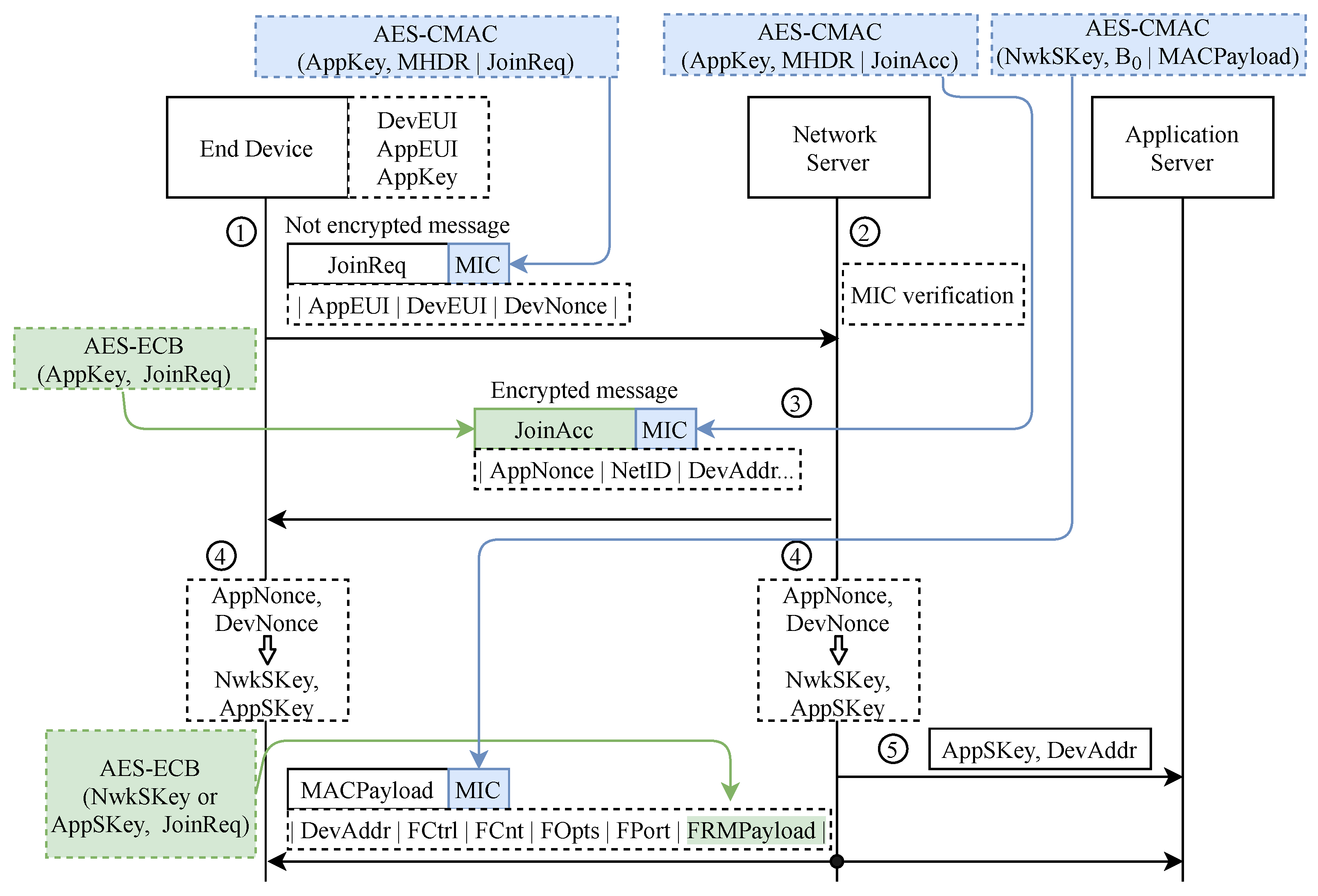
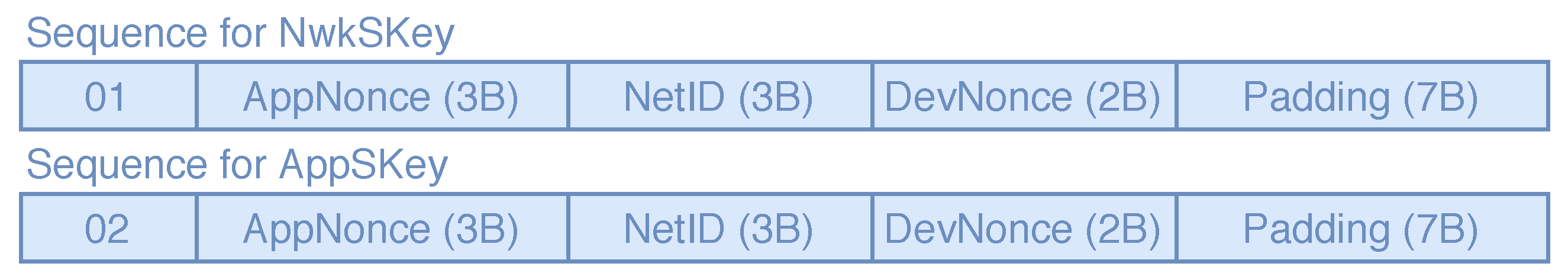
2.1.1. Encryption Algorithms
2.1.2. Activation Procedure
2.2. Related Works
3. Testbed Design and Test Cases
3.1. Testbed Design
3.1.1. End Devices
- A device built around the LoRaWAN module RHF PS01509 [30] acting as an authorized user (i.e., the “victim”) has been used in our experiments. Note that this device can be replaced by any other LoRaWAN-compatible transducer or commercial product.
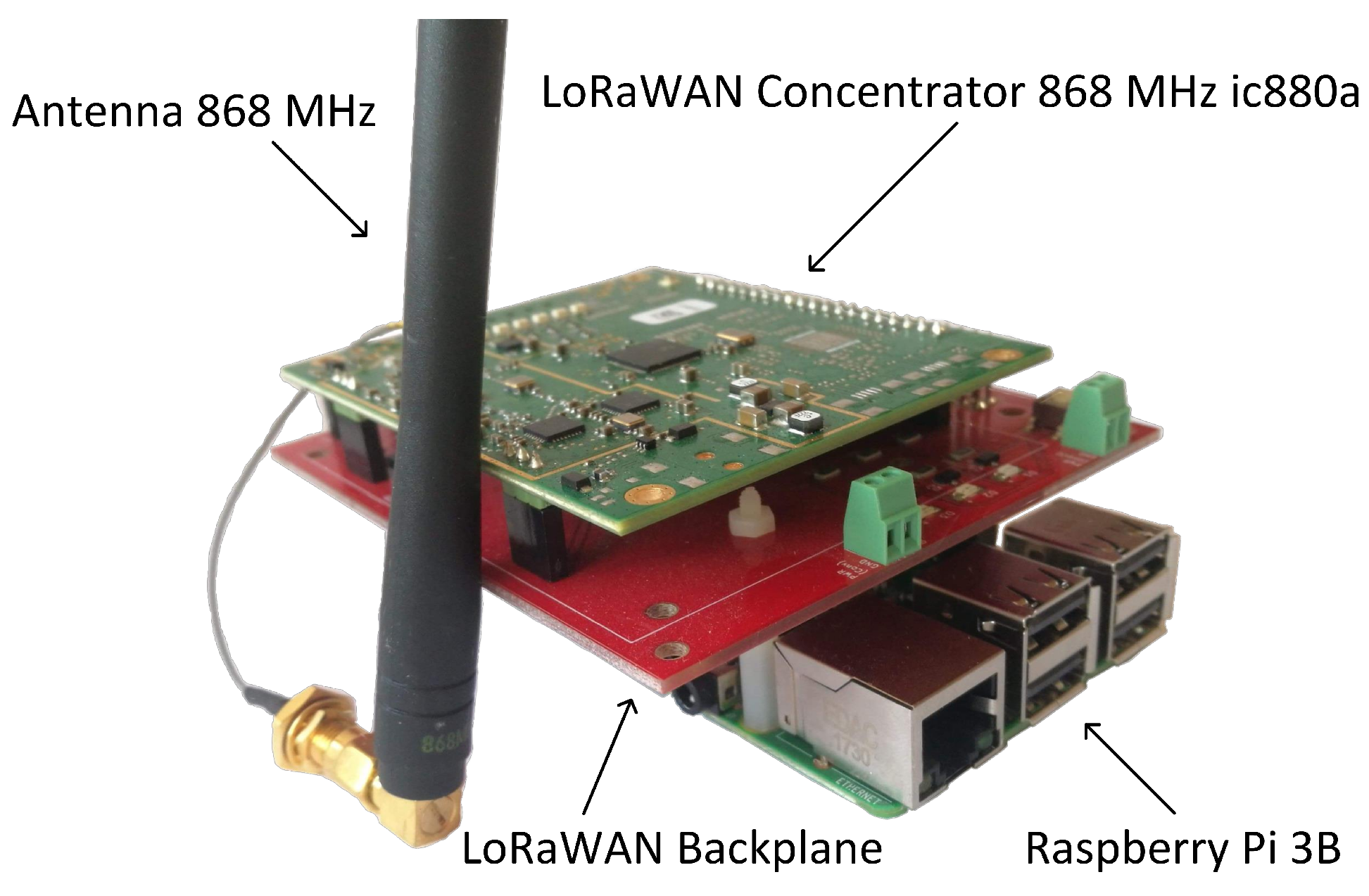
3.1.2. Gateway
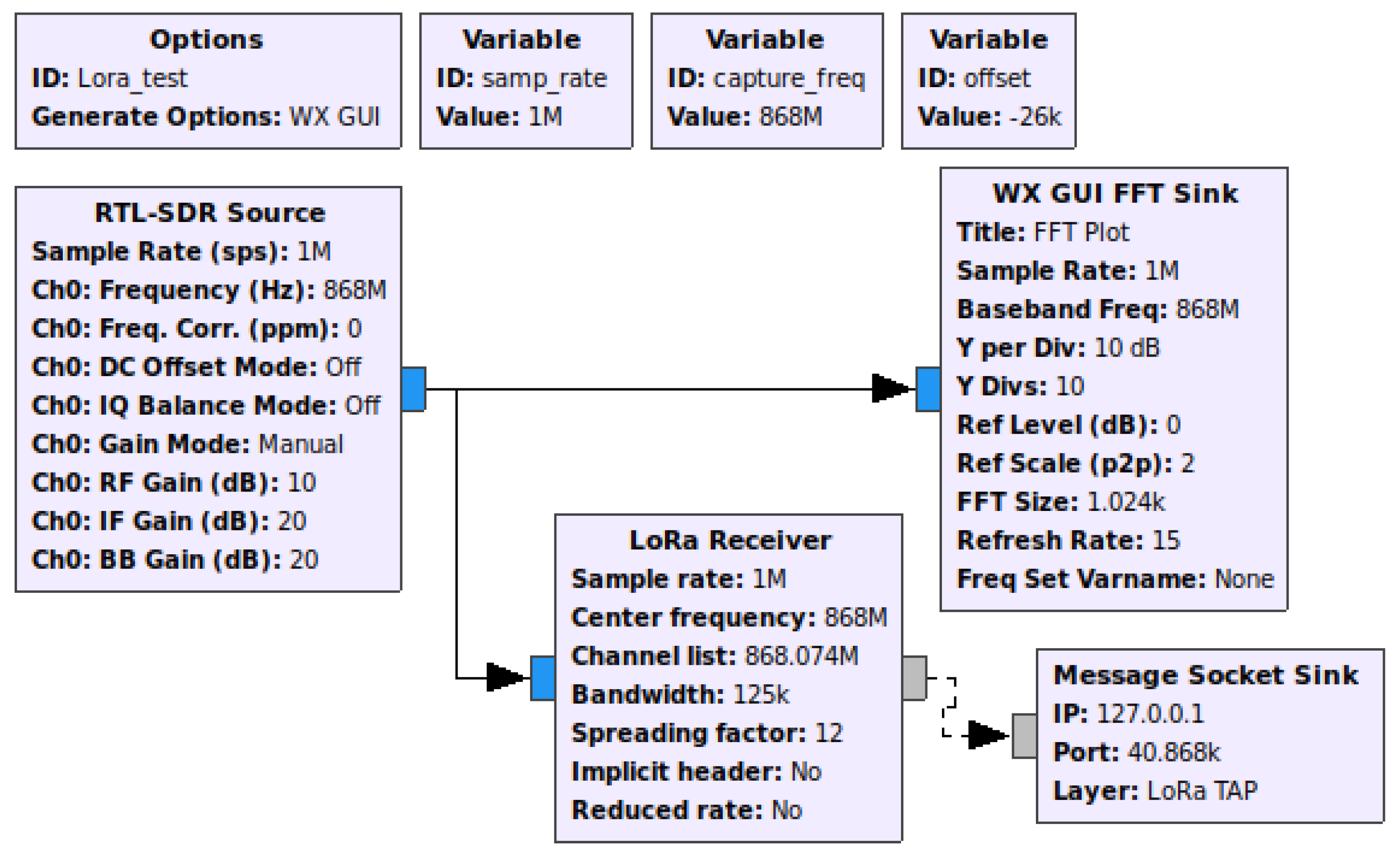
3.1.3. SDR Environment
3.2. Emulated Attack Scenarios
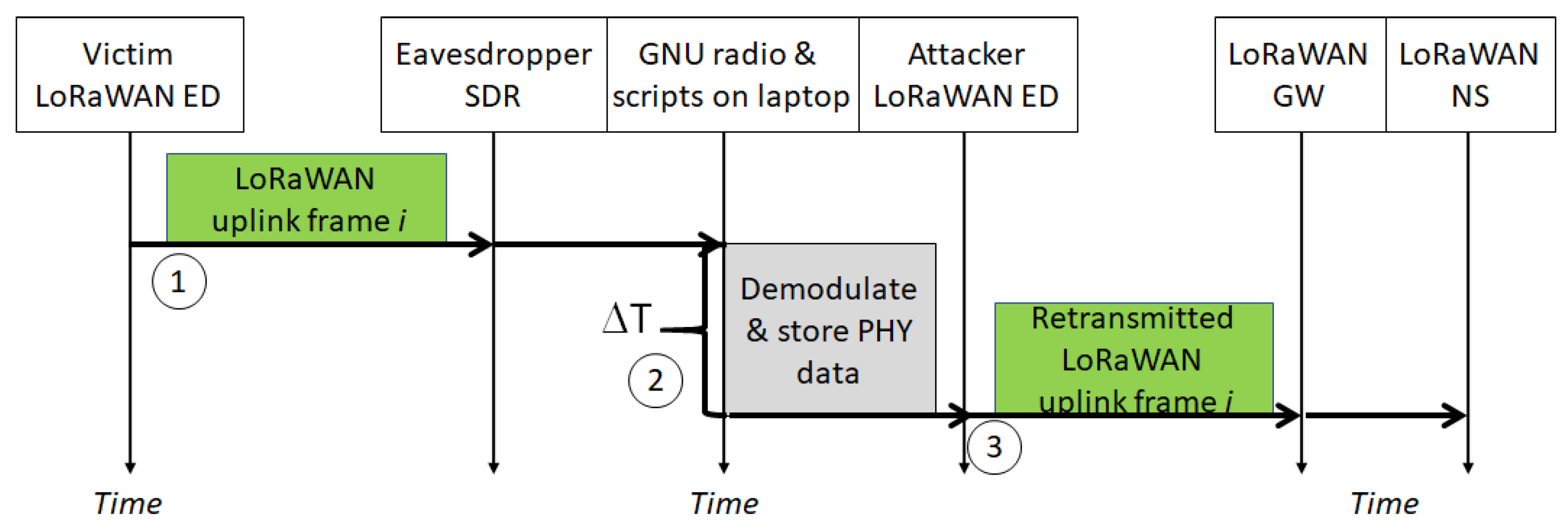
- The replay attack. This trial is carried out by an attacker intercepting the transmission between ED and GW. Specifically, the attacker eavesdrops a message from the ED and sends it via its own malicious device to the GW. The success of this attack depends on whether the frame counter on NS is activated or not. In case the frame counter is activated, the first step is to jam the ED before it can deliver the eavesdropped message to the GW [21] and then proceed with the attack. When the frame counter is not activated (which is common in many commercial networks to enable ABP devices re-joining the network after a power-down or reboot), the attack can be carried out without any jamming. The time sequence of this attack can be seen in Figure 6.
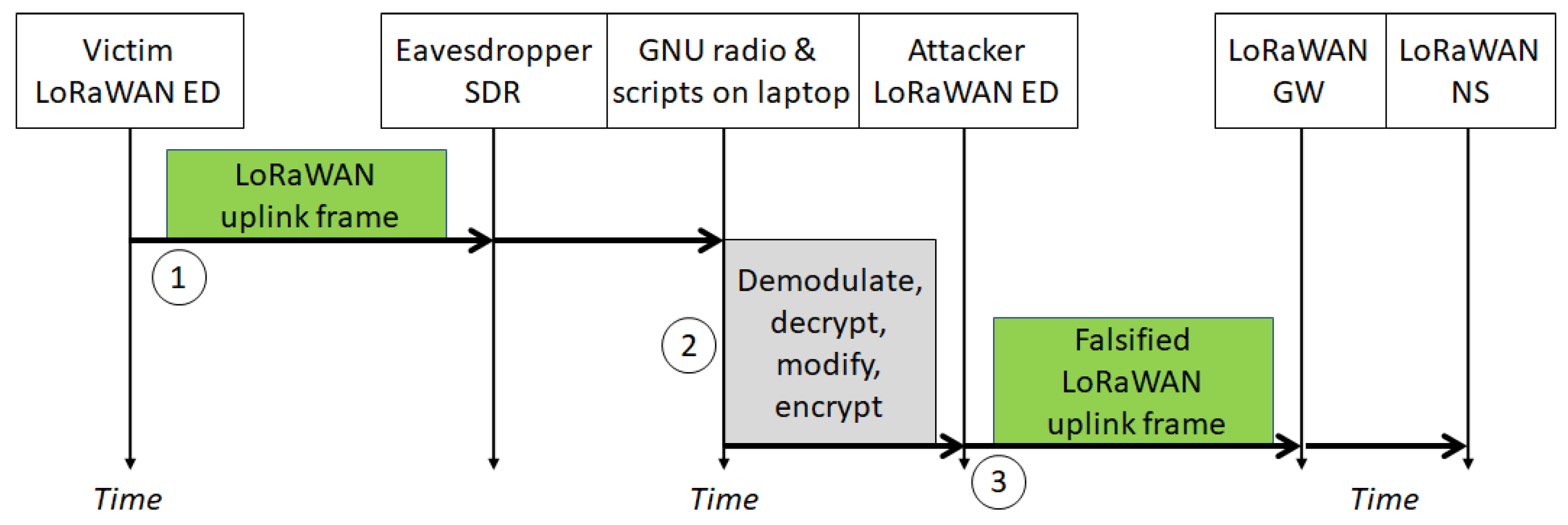
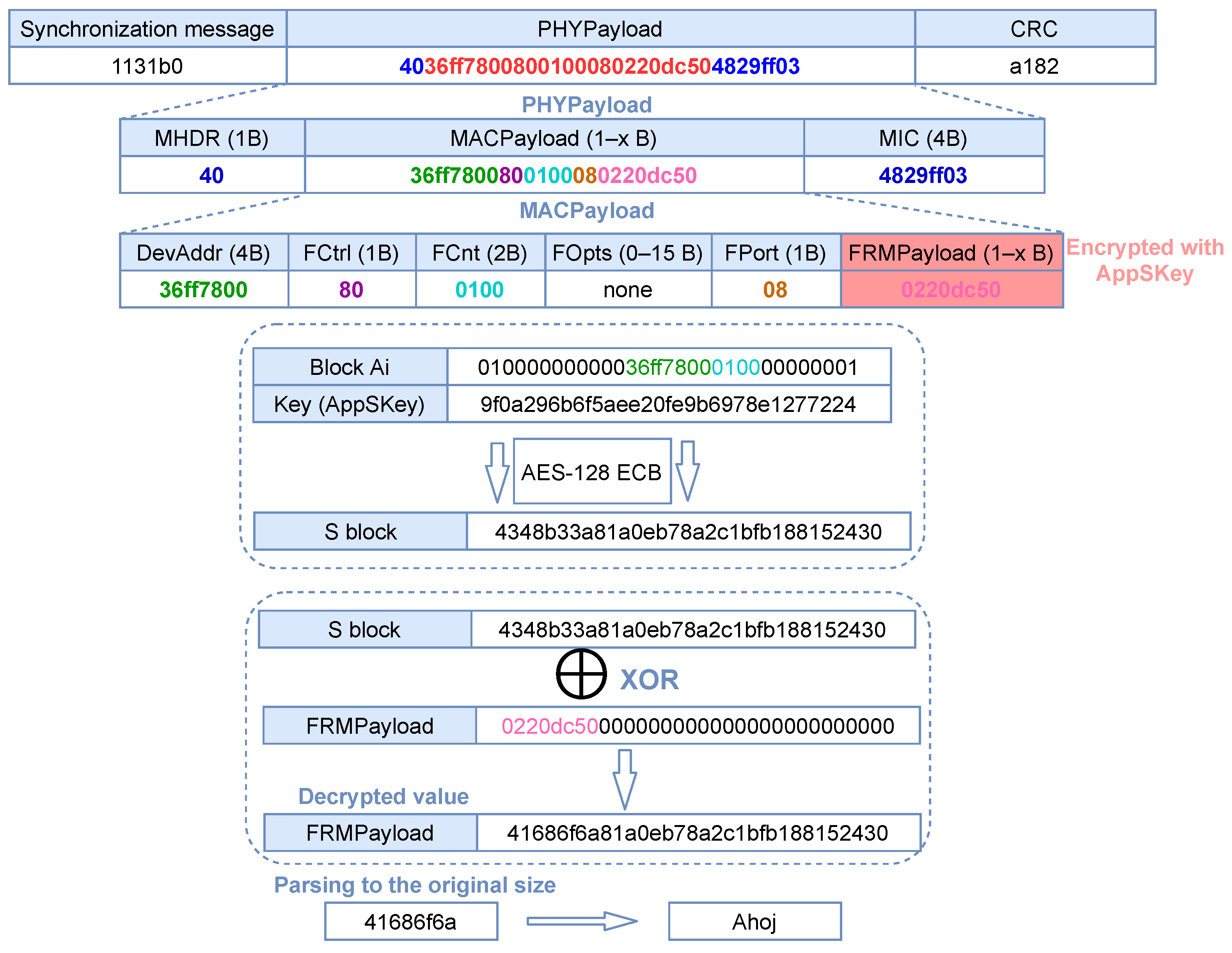
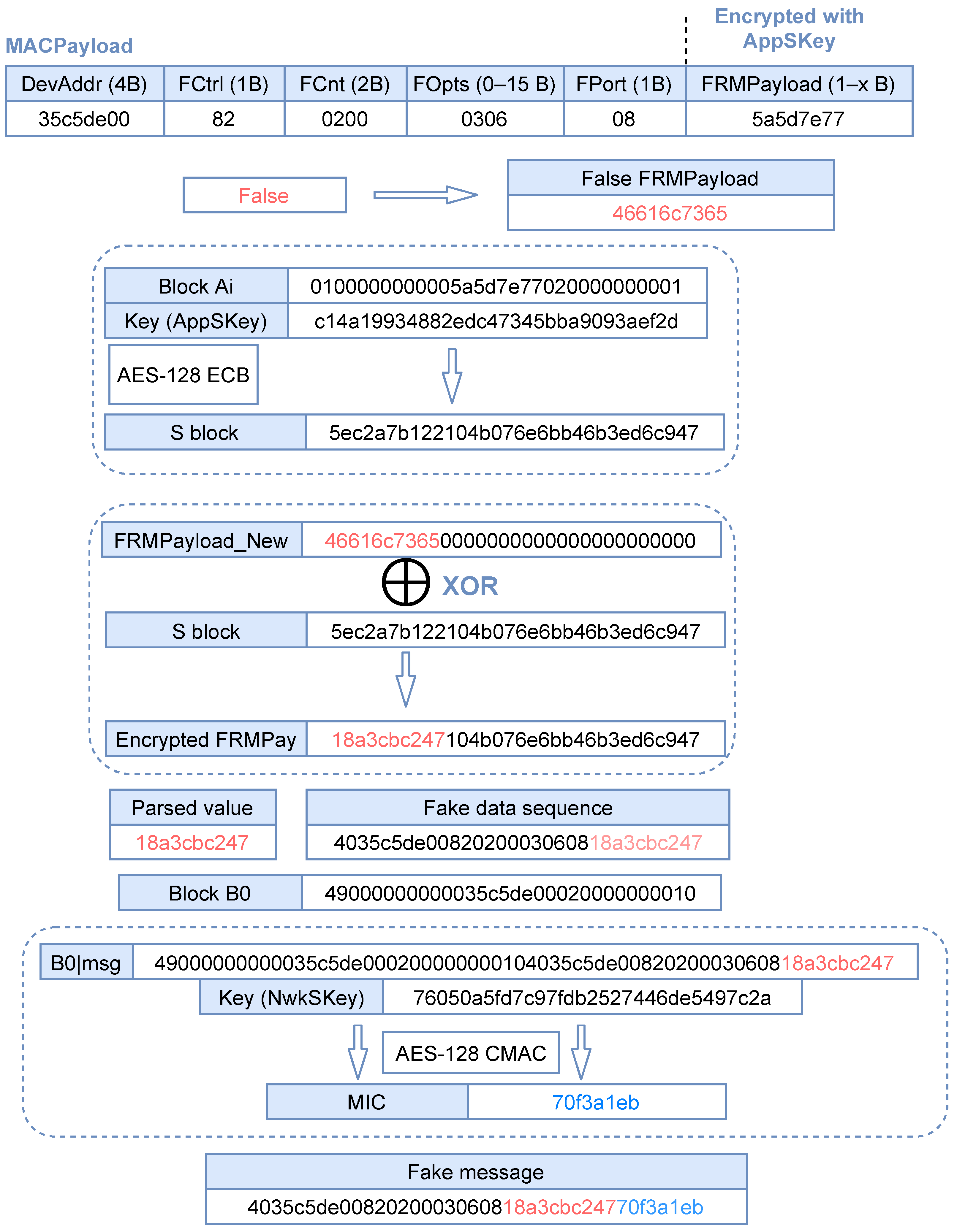
- The bit-flipping attack. The attacker intercepts the message and decrypts it, modifies it, encrypts it again and sends it to the GW. This attack allows an attacker to change all the information in the message. The time sequence of this attack can be seen in Figure 7.
4. Experimental Results
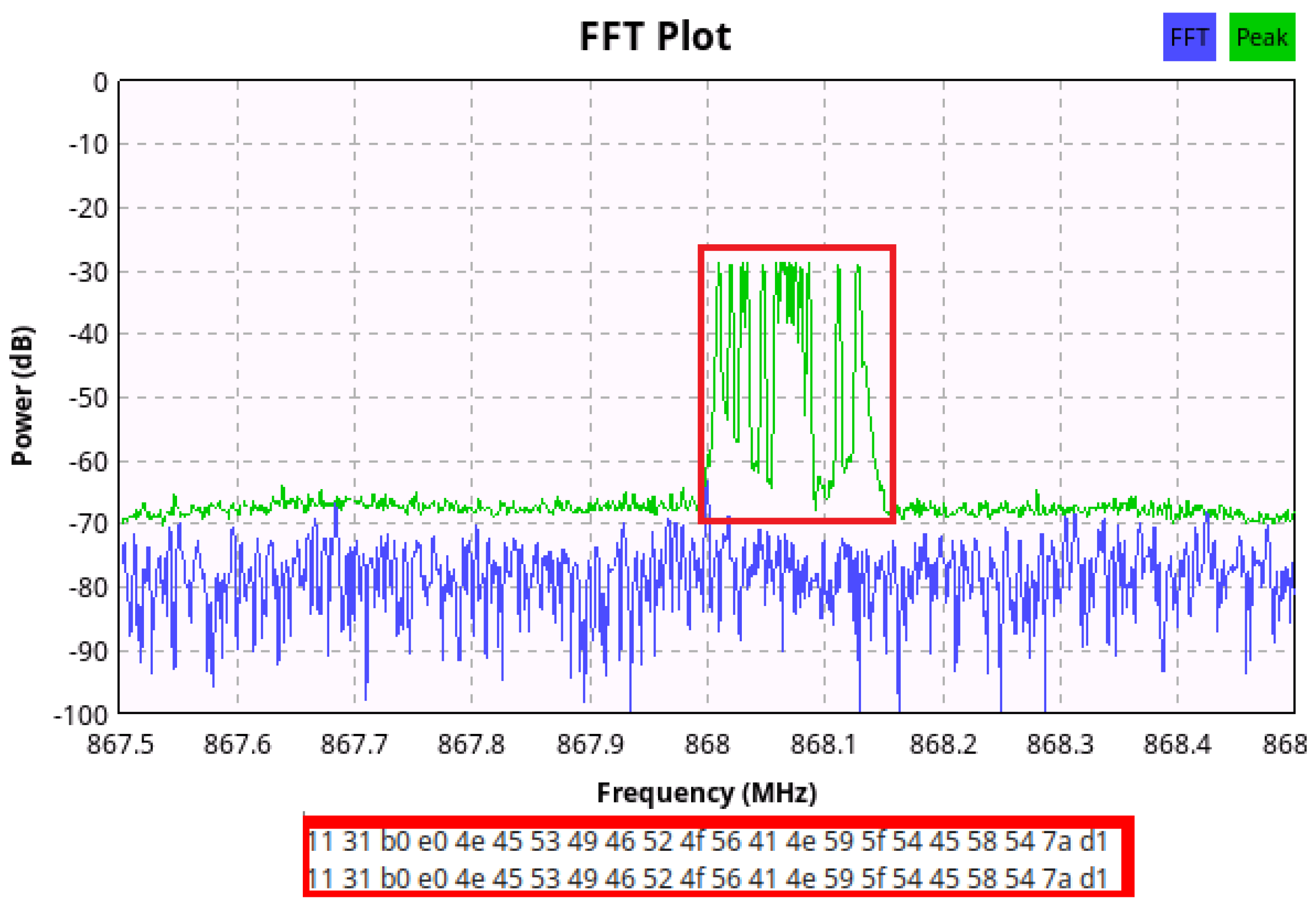
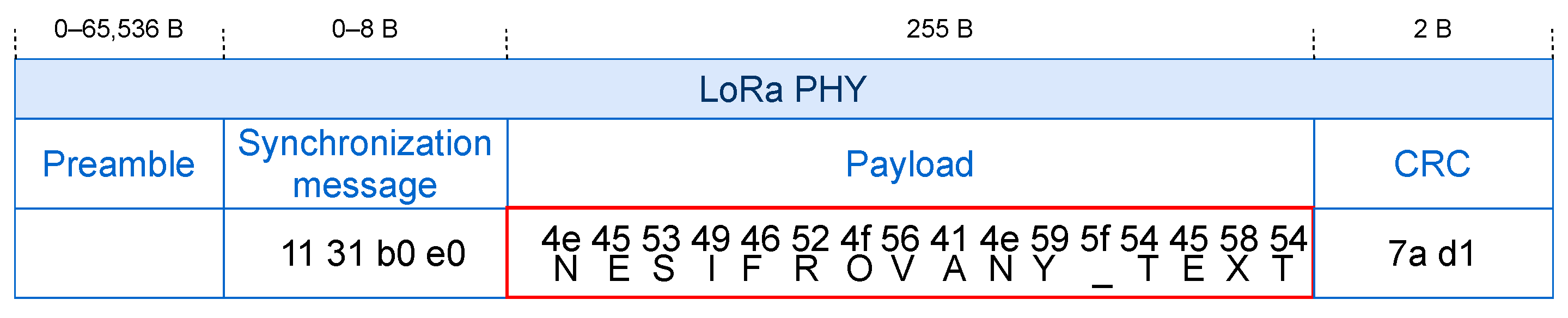
4.1. LoRa PHY Intercepting and Decoding
4.2. LoRaWAN MAC Interception and Decryption
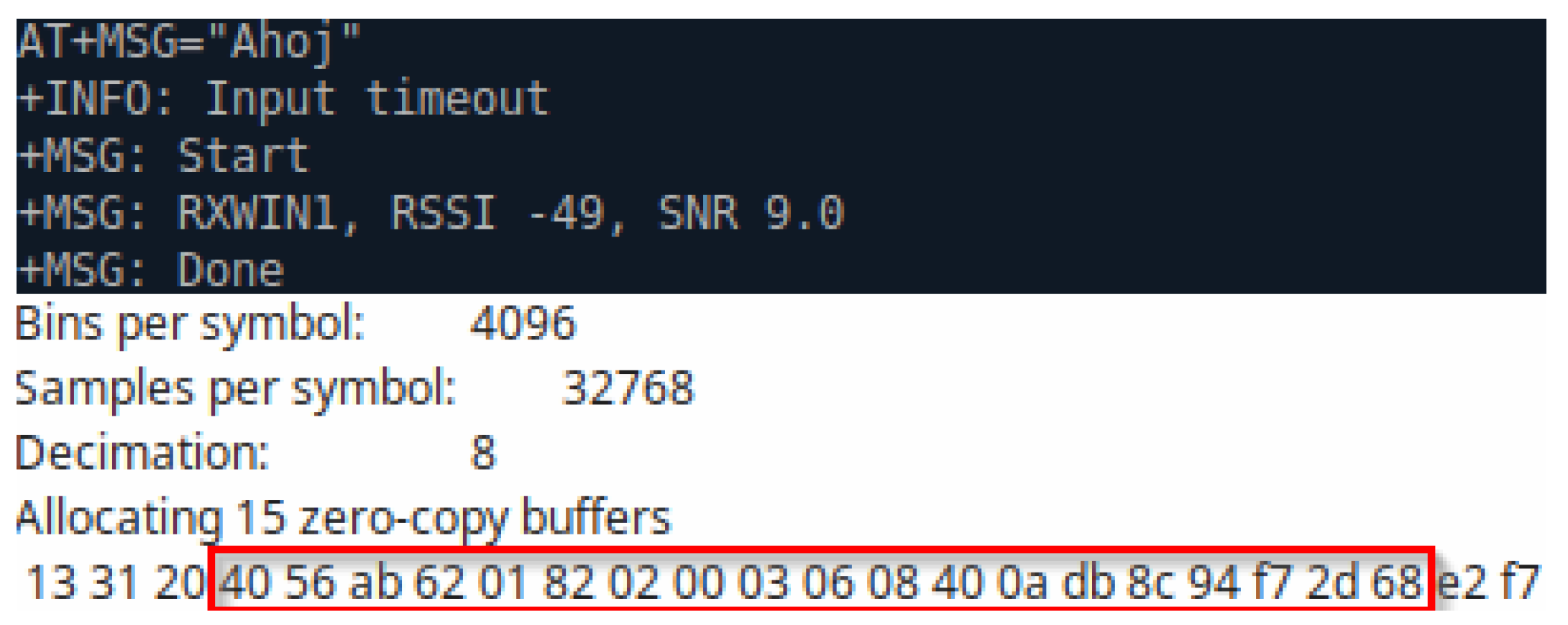
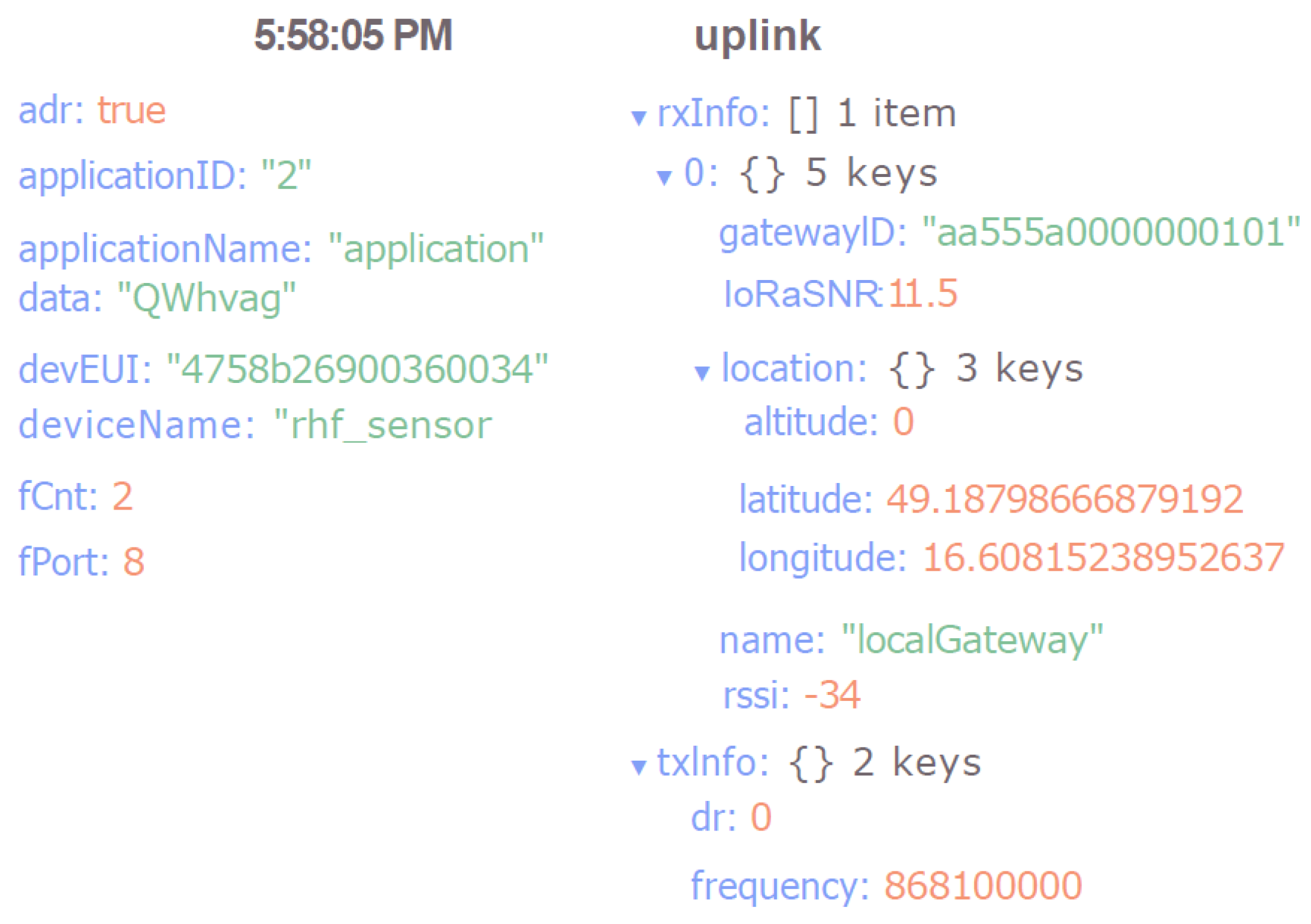
4.3. Replay Attack
| Listing 1: Packet sent by the attacker |
Radio.SetTxConfig( MODEM_LORA, 14, 0, 0, 12, 1, 8, false, true, 0, 0, false, 3000 ); Radio.SetChannel( 868100000 ); uint8_t buf[100]; buf[0] = 0x40; buf[1] = 0x56; buf[2] = 0xab; buf[3] = 0x62; buf[4] = 0x01; buf[5] = 0x82; buf[6] = 0x02; buf[7] = 0x00; buf[8] = 0x03; buf[9] = 0x06; buf[10] = 0x08; buf[11] = 0x40; buf[12] = 0x0a; buf[13] = 0xdb; buf[14] = 0x8c; buf[15] = 0x94; buf[16] = 0xf7; buf[17] = 0x2d; buf[18] = 0x68; Radio.Send( buf, 19 );
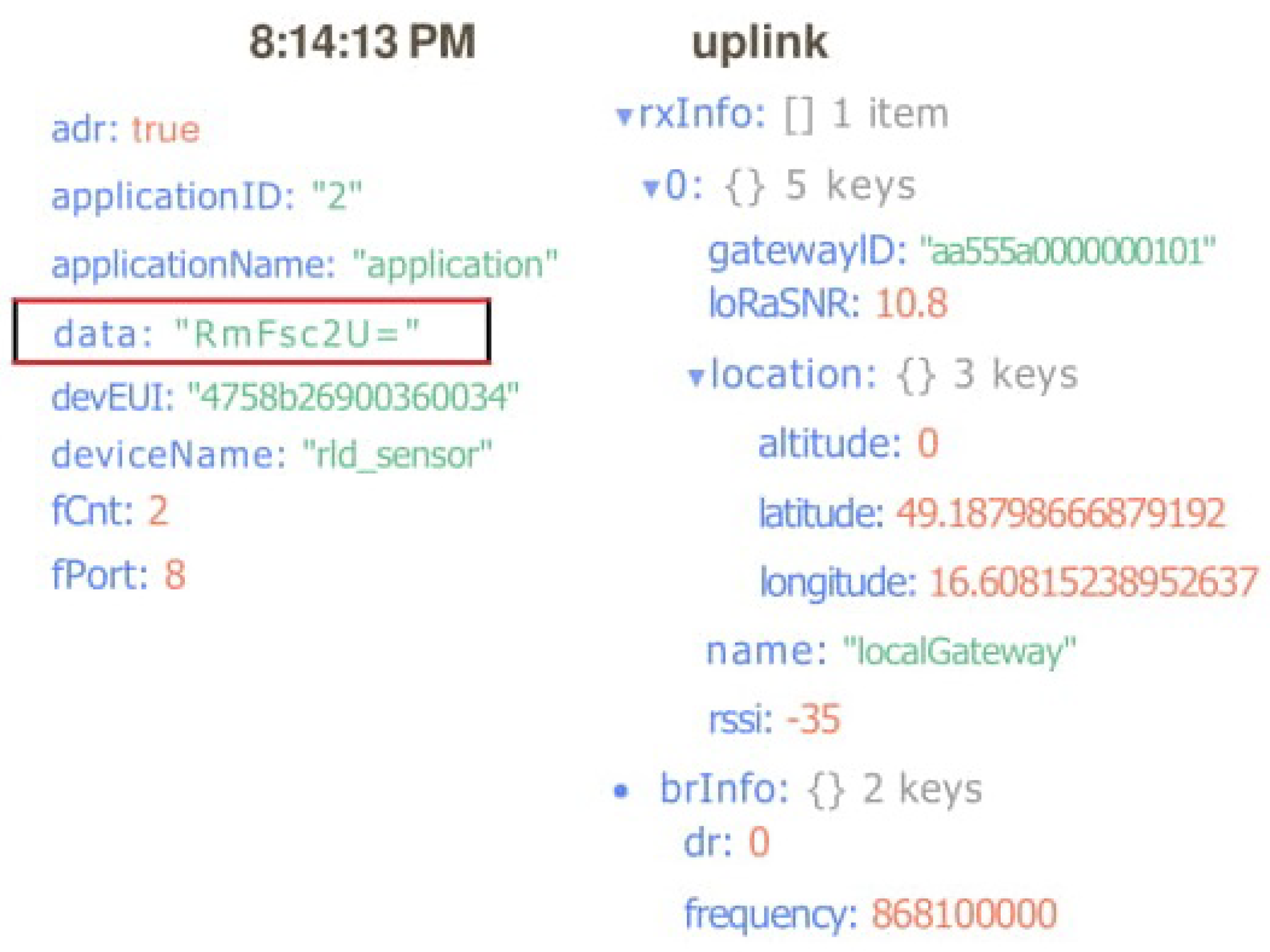
4.4. Bit-Flipping Attack
5. Conclusions
- Development of the algorithms and tools (if needed—inclusive of the dedicated hardware devices) to detect and classify the on-air attacks in LoRaWAN. Specifically, the algorithms can be based on monitoring the re-connection patterns of the individual devices, their traffic patterns and variation of their radio-channel parameters (e.g., RSSI and signal-to-noise ratio (SNR), as discussed by Sung et al. [22]).
- Development of algorithms and procedures enabling EDs to detect bogus GWs/NS.
- Engineering the mechanisms and procedures allowing re-connection and re-establishment of control over the hijacked sensors and the EDs suffering an attack (e.g., connected to a bogus NS).
- Addressing the novel types of attacks, specific for the IoT networks (e.g., the energy-depletion attack [39]).
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| ABP | Activation By Personalization |
| AES | Advanced Encryption Standard |
| AS | Application Server |
| ASCII | American Standard Code for Information Interchange |
| CBC | Cipher Block Chaining |
| CMAC | Cipher Based Message Authentication Code |
| ECB | Electronic Code Book |
| ED | End Device |
| GNU | The GNU Project |
| GW | Gateway |
| IP | Internet Protocol |
| IoT | Internet of Things |
| JS | Join Server |
| LL | Link Layer |
| LPWA | Low Power Wide Area |
| LPWAN | LPWA Network |
| LR-FHSS | Long Range-Frequency Hopping Spread Spectrum |
| LTE | Long Term Evolution |
| MitM | Man in the Middle |
| MAC | Media Access Control layer |
| MIC | Message Integrity Code |
| mMTC | massive Machine Type Connectivity |
| NS | Network Server |
| NWK | Network Layer |
| OTAA | Over the Air Activation |
| PHY | Physical layer |
| RAT | Radio Access Technology |
| RSSI | Received Signal Strength Indication |
| SDR | Software-Defined Radio |
| SF | Spreading Factor |
| SNR | Signal-to-Noise Ratio |
| USIM | Universal Subscriber Identity Module |
References
- Chettri, L.; Bera, R. A Comprehensive Survey on Internet of Things (IoT) Toward 5G Wireless Systems. IEEE IoT J. 2019, 7, 16–32. [Google Scholar] [CrossRef]
- Semtech LoRa Technology Overview|Semtech. Available online: https://www.semtech.com/lora (accessed on 25 February 2021).
- Shanmuga Sundaram, J.P.; Du, W.; Zhao, Z. A survey on lora networking: Research problems, current solutions, and open issues. IEEE Commun. Surv. Tutor. 2019, 22, 371–388. [Google Scholar] [CrossRef] [Green Version]
- McPherson, R.; Irvine, J. Secure decentralised deployment of LoRaWAN sensors. IEEE Sens. J. 2020, 21, 725–732. [Google Scholar] [CrossRef]
- Fujdiak, R.; Mikhaylov, K.; Stusek, M.; Masek, P.; Ahmad, I.; Malina, L.; Porambage, P.; Voznak, M.; Pouttu, A.; Mlynek, P. Security in Low Power Wide Area Networks: State-of-the-Art and Development towards the 5G. In LPWAN Technologies for IoT and M2M Applications; Academic Press: Cambridge, MA, USA, 2020; pp. 373–396. [Google Scholar]
- Sornin, N.; Luis, M.; Eirich, T.; Kramp, T.; Hersent, O. Lorawan Specification. Available online: https://lora-alliance.org/resource_hub/lorawan-specification-v1-0/ (accessed on 19 August 2021).
- Kim, S.; Heonkook, L.; Jeon, S. An Adaptive Spreading Factor Selection Scheme for a Single Channel LoRa Modem. Sensors 2020, 20, 1008. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Croce, D.; Gucciardo, M.; Mangione, S.; Santaromita, G.; Tinnirello, I. Impact of LoRa imperfect orthogonality: Analysis of link-level performance. IEEE Commun. Lett. 2018, 22, 796–799. [Google Scholar] [CrossRef] [Green Version]
- Miller, R. Lora security: Building a secure lora solution. In MWR Labs Whitepaper; F-Secure Cyber Security Limited: Basingstoke, UK, 2016; pp. 1–18. [Google Scholar]
- Aras, E.; Ramachandran, G.S.; Lawrence, P.; Hughes, D. Exploring the security vulnerabilities of LoRa. In Proceedings of the 3rd International Conference on Cybernetics (CYBCONF), Exeter, UK, 21–23 June 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–6. [Google Scholar] [CrossRef] [Green Version]
- Oniga, B.; Dadarlat, V.; De Poorter, E.; Munteanu, A. Analysis, design and implementation of secure LoRaWAN sensor networks. In Proceedings of the 13th International Conference on Intelligent Computer Communication and Processing (ICCP), Cluj-Napoca, Romania, 7–9 September 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 421–428. [Google Scholar] [CrossRef] [Green Version]
- Butun, I.; Pereira, N.; Gidlund, M. Security risk analysis of LoRaWAN and future directions. Future Internet 2019, 11, 3. [Google Scholar] [CrossRef] [Green Version]
- Naoui, S.; Dadarlat, V.; Elhdhili, M.E.; Munteanu, A. Enhancing the security of the IoT LoraWAN architecture. In Proceedings of the International Conference on Performance Evaluation and Modeling in Wired and Wireless Networks (PEMWN), Paris, France, 22–25 November 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–7. [Google Scholar] [CrossRef]
- Kim, J.; Song, J. A dual key-based activation scheme for secure LoRaWAN. Adv. Wirel. Commun. Mob. Comput. Technol. Internet Things 2017, 2017, 1–12. [Google Scholar] [CrossRef] [Green Version]
- Oniga, B.; Dadarlat, V.; De Poorter, E.; Saidane, L.A. A secure LoRaWAN sensor network architecture. In Proceedings of the 2017 IEEE SENSORS, Glasgow, UK, 29 October–1 November 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–3. [Google Scholar] [CrossRef] [Green Version]
- Lin, J.; Shen, Z.; Miao, C.; Liu, S. Using blockchain to build trusted LoRaWAN sharing server. Int. J. Crowd Sci. 2017, 1, 270–280. [Google Scholar] [CrossRef] [Green Version]
- Sanchez-Iborra, R.; Sánchez-Gómez, J.; Pérez, S.; Fernández, P.J.; Santa, J.; Hernández-Ramos, J.L.; Skarmeta, A.F. Enhancing lorawan security through a lightweight and authenticated key management approach. Sensors 2018, 18, 1833. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Navarro-Ortiz, J.; Chinchilla-Romero, N.; Ramos-Munoz, J.J.; Munoz-Luengo, P. Improving Hardware Security for LoRaWAN. In Proceedings of the Conference on Standards for Communications and Networking (CSCN), Granada, Spain, 16 December 2019; IEEE: Piscataway, NJ, USA, 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Ribeiro, V.; Holanda, R.; Ramos, A.; Rodrigues, J.J. Enhancing Key Management in LoRaWAN with Permissioned Blockchain. Sensors 2020, 20, 3068. [Google Scholar] [CrossRef]
- Tsai, K.; Leu, F.; Hung, L.; Ko, C. Secure Session Key Generation Method for LoRaWAN Servers. IEEE Access 2020, 8, 54631–54640. [Google Scholar] [CrossRef]
- Kim, J.; Song, J. A simple and efficient replay attack prevention scheme for LoRaWAN. In Proceedings of the 7th International Conference on Communication and Network Security, Tokyo, Japan, 24–26 November 2017; ACM: New York, NY, USA, 2017; pp. 32–36. [Google Scholar] [CrossRef]
- Sung, W.; Ahn, H.; Kim, J.; Choi, S. Protecting end-device from replay attack on LoRaWAN. In Proceedings of the 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon-si, Gangwon-do, Korea, 11–14 February 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 167–171. [Google Scholar] [CrossRef]
- Gao, S.; Li, X.; Ma, M. A Malicious Behavior Awareness and Defense Countermeasure Based on LoRaWAN Protocol. Sensors 2019, 19, 5122. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Thomas, J.; Cherian, S.; Chandran, S.; Pavithran, V. Man in the Middle Attack Mitigation in LoRaWAN. In Proceedings of the International Conference on Inventive Computation Technologies (ICICT), Coimbatore, India, 26–28 February 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 353–358. [Google Scholar] [CrossRef]
- Torres, N.; Pinto, P.; Lopes, S.I. Security Vulnerabilities in LPWANs—An Attack Vector Analysis for the IoT Ecosystem. Appl. Sci. 2021, 11, 3176. [Google Scholar] [CrossRef]
- Yang, X.; Karampatzakis, E.; Doerr, C.; Kuipers, F.A. Security Vulnerabilities in LoRaWAN. In Proceedings of the Third International Conference on Internet-of-Things Design and Implementation (IoTDI), Orlando, FL, USA, 17–20 April 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 129–140. [Google Scholar] [CrossRef] [Green Version]
- Tomasin, S.; Zulian, S.; Vangelista, L. Security analysis of lorawan join procedure for internet of things networks. In Proceedings of the IEEE Wireless Communications and Networking Conference Workshops (WCNCW), San Francisco, CA, USA, 19–22 March 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Hessel, F.; Almon, L.; Álvarez, F. ChirpOTLE: A Framework for Practical LoRaWAN Security Evaluation. In Proceedings of the 13th ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec’20), Linz, Austria, 8–10 July 2020; Association for Computing Machinery: New York, NY, USA, 2020; pp. 306–316. [Google Scholar] [CrossRef]
- Orne Brocaar. ChirpStack Network Server. Available online: https://github.com/brocaar/chirpstack-network-server (accessed on 25 August 2020).
- RHF-PS01509, Lorawanclass a/cat Command Specification. Available online: https://m5stack.oss-cn-shenzhen.aliyuncs.com/resource/docs/datasheet/module/lorawan_class_ac_at_command_specification_-_v4.4.pdf (accessed on 25 February 2021).
- Sub-GModule Data Sheet, BP-ABZ-C. Available online: https://wireless.murata.com/pub/RFM/data/type_abz.pdf (accessed on 25 August 2020).
- I-CUBE-LRWAN, STM32 LoRa® Software Expansion for STM32Cube. Available online: https://www.st.com/resource/en/data_brief/i-cube-lrwan.pdf (accessed on 25 August 2020).
- Raspberry Pi 3 Model B+. Available online: https://static.raspberrypi.org/files/product-briefs/Raspberry-Pi-Model-Bplus-Product-Brief.pdf (accessed on 25 August 2020).
- WiMOD iC880A, Datasheet. Available online: https://webshop.ideetron.nl/Files/3/1000/1211/Attachments/Product/IB4c6A1J5Uh6Ej5D3i6cQ88q1P2D1404.pdf (accessed on 25 August 2020).
- IC880A LoRaWAN Gateway Backplane v2.0. Available online: https://shop.coredump.ch/product/ic880a-lorawan-gateway-backplane/ (accessed on 25 August 2020).
- Robyns, P. Gr-Lora. Available online: https://github.com/rpp0/gr-lora (accessed on 25 August 2020).
- R820T High Performance Low Power Advanced Digital TV Silicon Tuner Datasheet. Available online: https://rtl-sdr.com/wp-content/uploads/2013/04/R820T_datasheet-Non_R-20111130_unlocked.pdf (accessed on 25 August 2020).
- Processing Standards Publication 197, Advanced Encryption Standard (AES). Available online: https://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.197.pdf (accessed on 25 August 2020).
- Mikhaylov, K.; Fujdiak, R.; Pouttu, A.; Voznak, M.; Malina, L.; Mlynek, P. Energy Attack in LoRaWAN: Experimental Validation. In Proceedings of the 14th International Conference on Availability, Reliability and Security (ARES), Canterbury, UK, 26–29 August 2019; ACM: New York, NY, USA, 2019; pp. 1–6. [Google Scholar] [CrossRef]
- LoRaWAN Protocol Expands Network Capacity with New Long Range—Frequency Hopping Spread Spectrum Technology. 2021. Available online: https://blog.semtech.com/lorawan-protocol-expands-network-capacity-with-new-long-range-frequency-hopping-spread-spectrum-technology (accessed on 25 February 2021).
| Work | Description |
|---|---|
| Category: General description of security and possible vulnerabilities | |
| Millere 2016 [9] | Possible vulnerabilities and attacks in LoRaWAN 1.0.x network. |
| Aras et al., 2017 [10] | Susceptibility of LoRaWAN to jamming, replay attack and wormhole. |
| Oniga et al., 2017 [11] | Analysis of security aspects of LoRaWAN and discussion of security options based on certificates. |
| Butun et al., 2018 [12] | Summary of security threats in LoRaWAN versions 1.0 and 1.1. |
| Category: Improving security of LoRaWAN | |
| Naoui et al., 2017 [13] | A solution that improves the security of the LoRaWAN 1.0 network by making better use of the relational key between the ED and NS. |
| Kim et al., 2017 [14] | Description of security gaps in key generation, and design of a new activation scheme based on a dual key. |
| Oniga et al., 2017 [15] | Security analysis of the LoRaWAN protocol and suggestion of a public key infrastructure. |
| Lin et al., 2017 [16] | Design of an open, trusted decentralized tamper-resistant system within LoRaWAN using blockchain technology. |
| Sanchez-Iborra et al., 2018 [17] | Security risk assessment for key management within LoRaWAN and design of a key management method based on ephemeral Diffie–Hellman over COSE. |
| Navarro-Ortiz et al., 2019 [18] | Hardware improvement of LoRaWAN security using USIM cards as cryptographic chips. |
| Ribeiro et al., 2020 [19] | Improved key management within the LoRaWAN architecture using Blockchain technology. |
| Tsai et al., 2020 [20] | Establishing relation using elliptic curves and AES algorithms to boost the security of S2KG communication between servers. |
| Category: Attack prevention | |
| Kim et al., 2017 [21] | Design of a prevention scheme for replay attack. |
| Sung et al., 2018 [22] | Protection against replay attack using RSSI and handshaking. |
| Gao et al., 2019 [23] | Design of SPT model to detect and protect against replay attack. |
| Thomas et al., 2020 [24] | Man-in-the-middle attack mitigation based on cryptographic Galois counter mode. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Pospisil, O.; Fujdiak, R.; Mikhaylov, K.; Ruotsalainen, H.; Misurec, J. Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study. Appl. Sci. 2021, 11, 7642. https://doi.org/10.3390/app11167642
Pospisil O, Fujdiak R, Mikhaylov K, Ruotsalainen H, Misurec J. Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study. Applied Sciences. 2021; 11(16):7642. https://doi.org/10.3390/app11167642
Chicago/Turabian StylePospisil, Ondrej, Radek Fujdiak, Konstantin Mikhaylov, Henri Ruotsalainen, and Jiri Misurec. 2021. "Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study" Applied Sciences 11, no. 16: 7642. https://doi.org/10.3390/app11167642
APA StylePospisil, O., Fujdiak, R., Mikhaylov, K., Ruotsalainen, H., & Misurec, J. (2021). Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study. Applied Sciences, 11(16), 7642. https://doi.org/10.3390/app11167642








