Attack Categorisation for IoT Applications in Critical Infrastructures, a Survey
Abstract
1. Introduction
Structure
2. Background
2.1. Critical Infrastructures
2.2. Wireless Communications
2.3. Internet of Things (IoT)
2.4. Categorisation
3. Preliminary Discussion
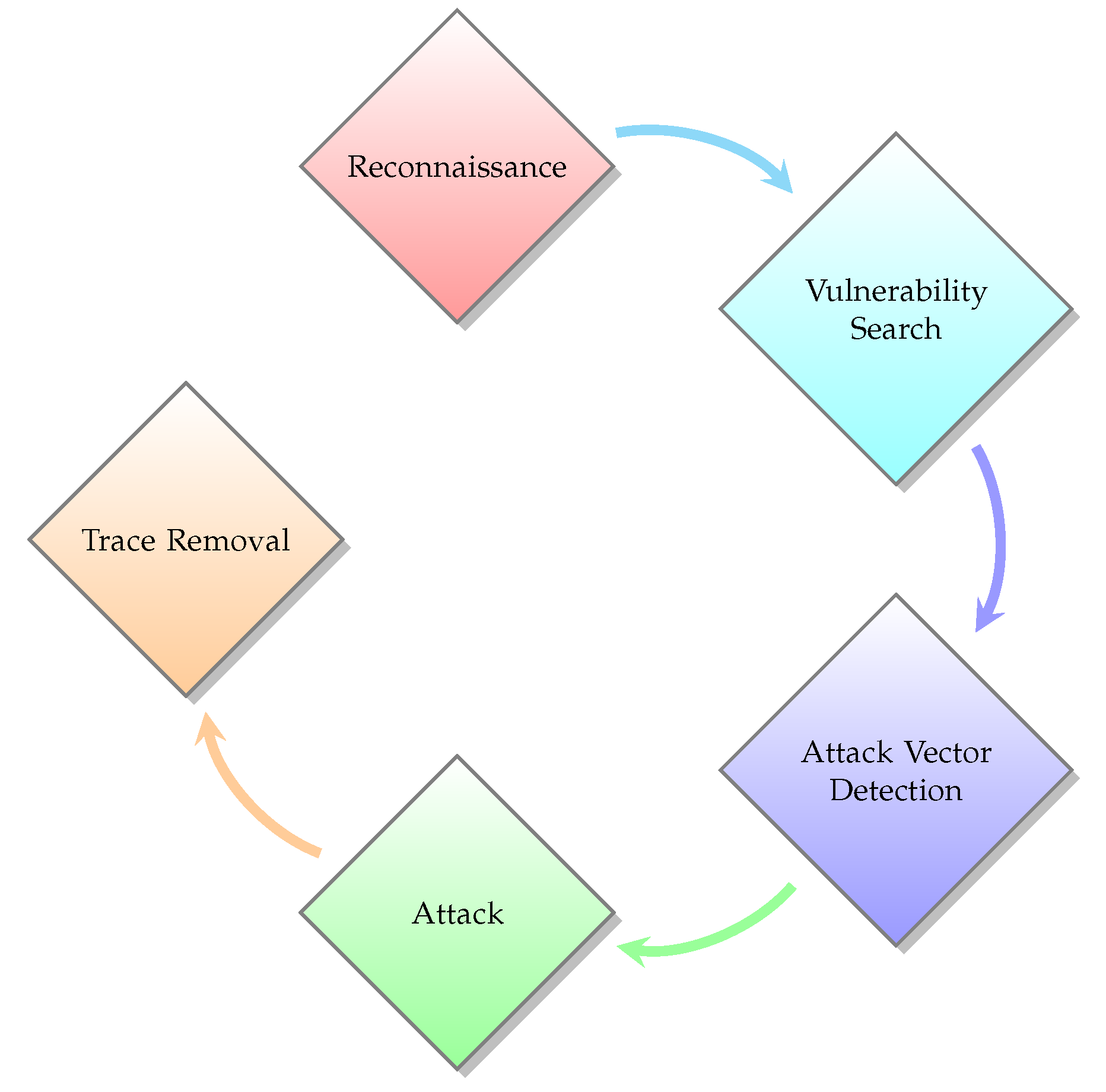
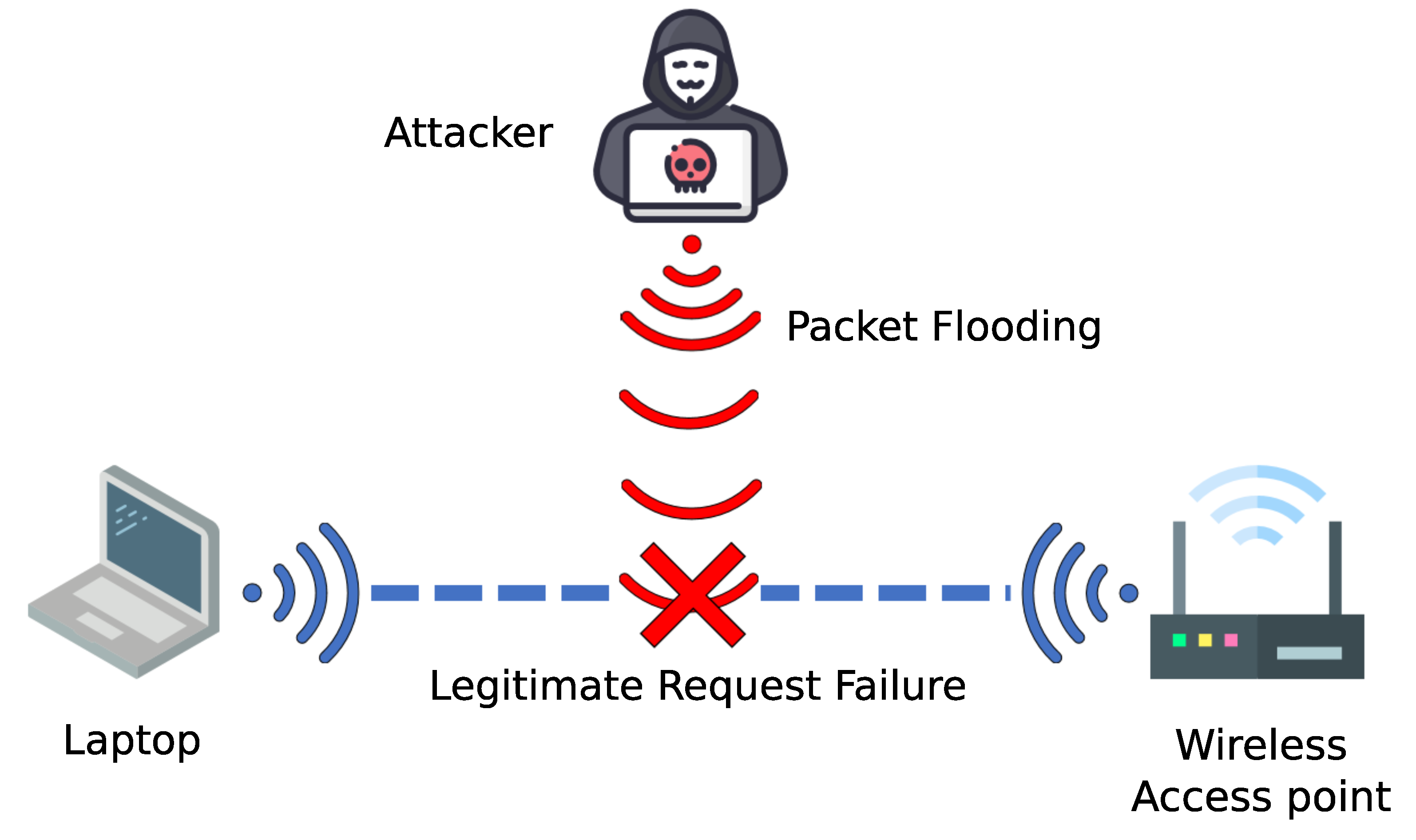
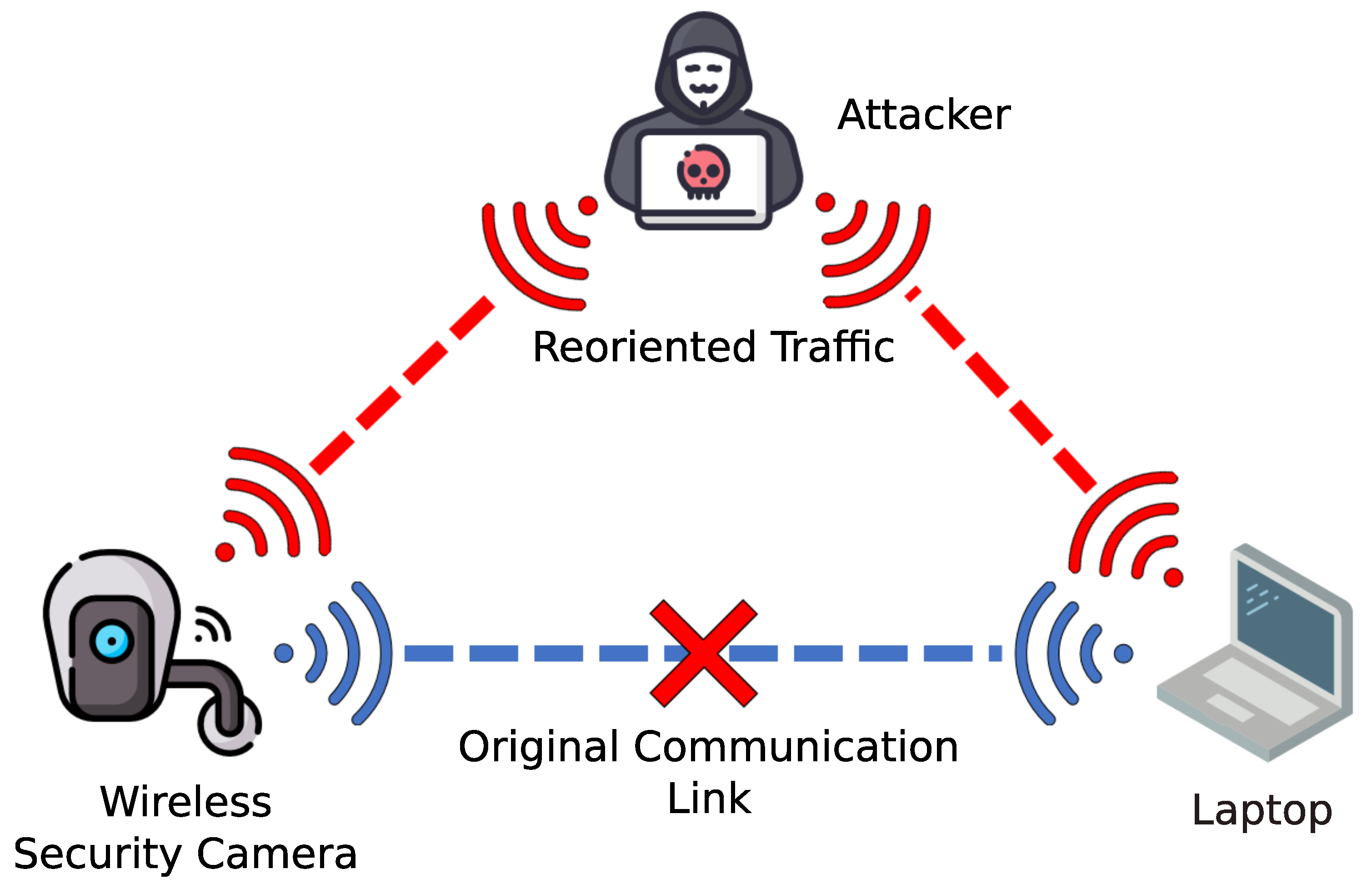
3.1. Cyber Attacks
3.1.1. Reconnaissance
3.1.2. Vulnerability Search
3.1.3. Attack Vector Detection
3.1.4. Attack
3.1.5. Trace Removal
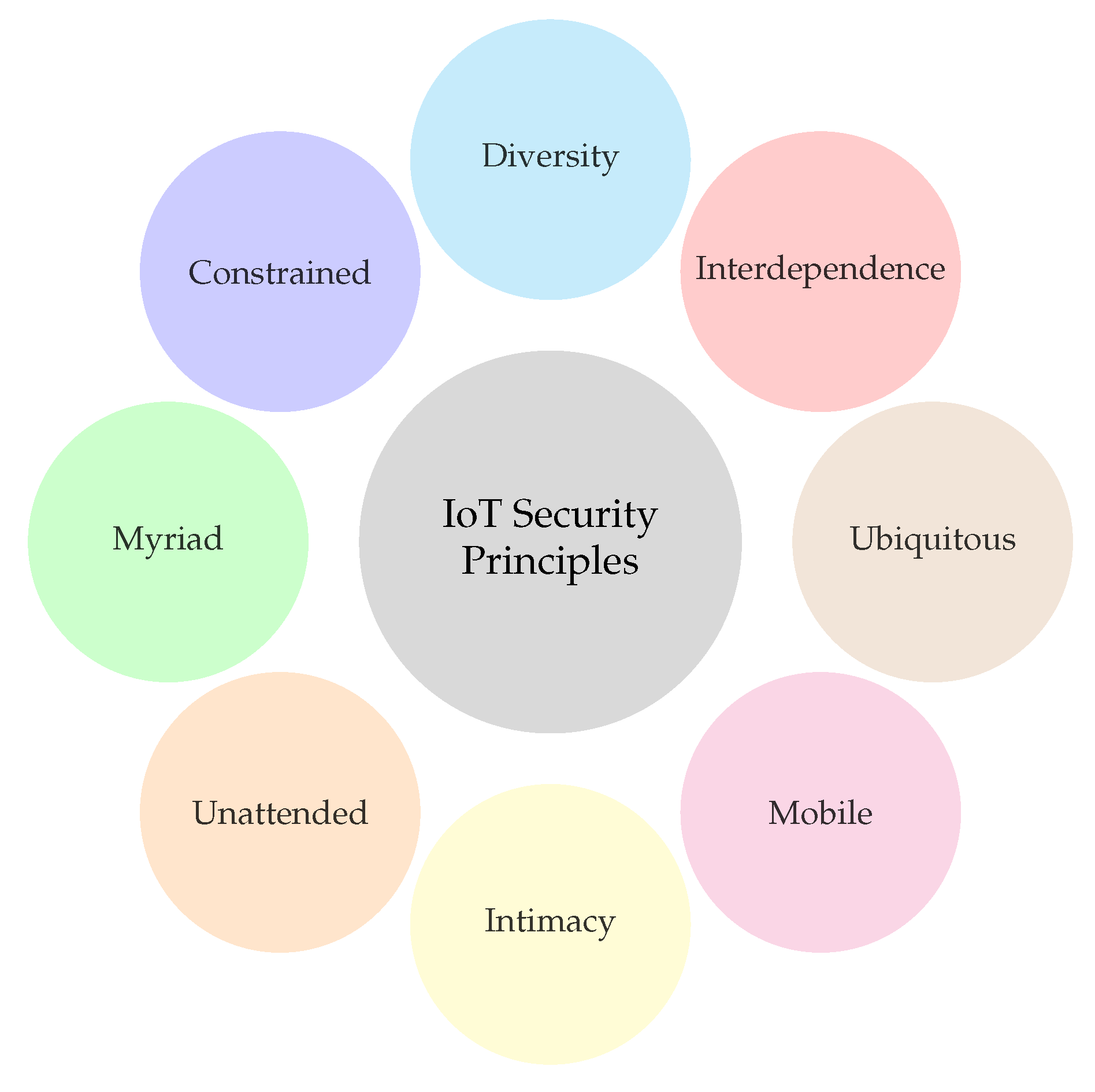
3.2. IoT Security Principles
3.2.1. Interdependence
3.2.2. Diversity
3.2.3. Constrained
3.2.4. Myriad
3.2.5. Unattended
3.2.6. Intimacy
3.2.7. Mobile
3.2.8. Ubiquitous
3.3. Need for Categorisation
4. Attack Categorisation
4.1. Attack Severity
4.2. Access Type
4.3. Attack Type
4.4. Attacker Position
4.5. Attacker Implication
4.6. Objective Oriented
4.7. Network Layer Oriented
4.8. Use Case Specific
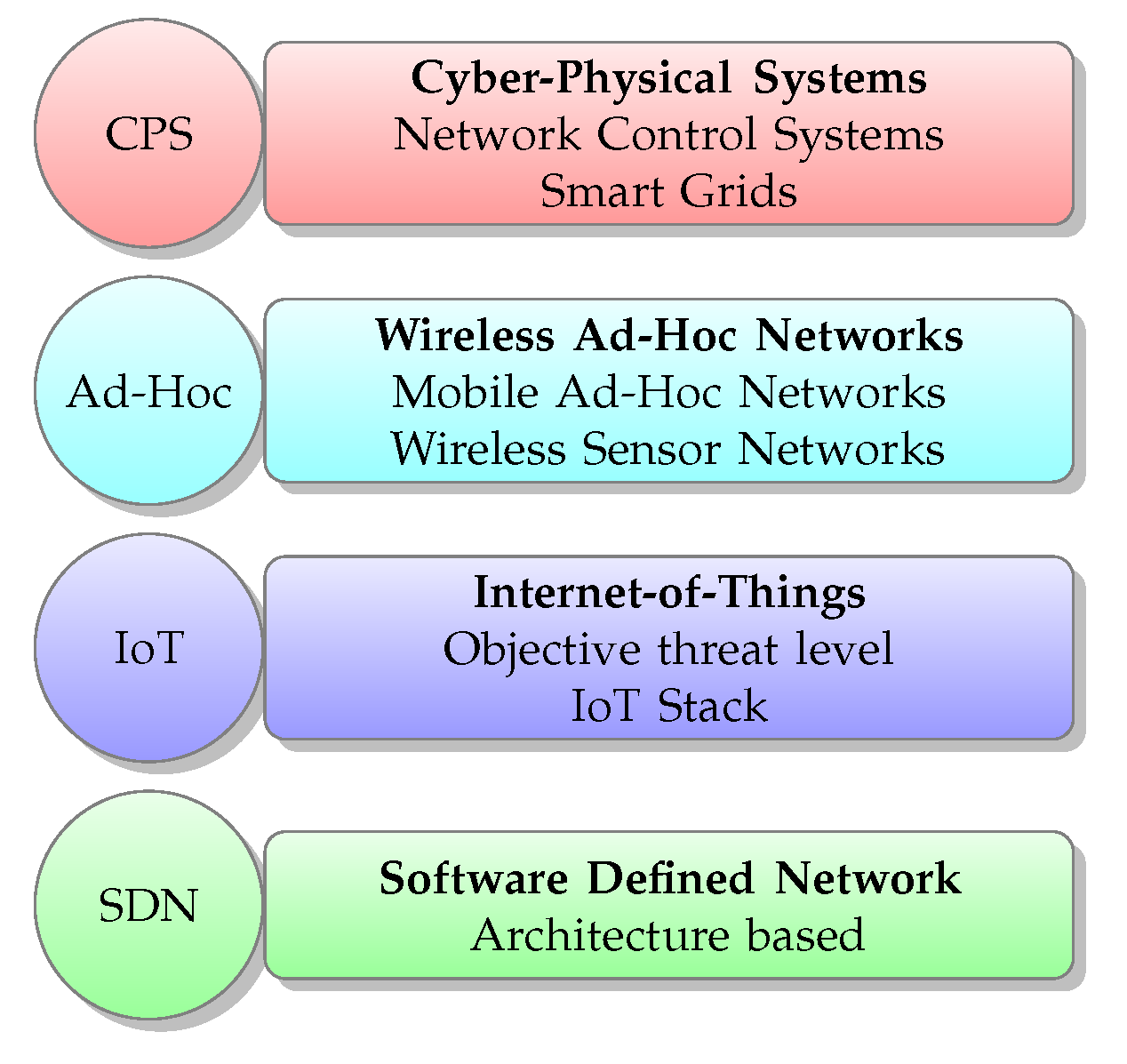
4.8.1. Cyber-Physical System
4.8.2. Smart Grids
4.8.3. Wireless Ad-Hoc Networks
- Black-Hole Attack, which influences routing decisions to force all messages to transit to the compromised node itself to then be dropped, resulting in a DoS of varying intensity [98].
- Wormhole Attack, which creates an unauthorised long distance link between two compromised nodes, forwarding data from one end of the network to the other, disrupting routing efficiency as nodes on one end believe they are closer to nodes on the other end than they are [99].
- Gray-Hole Attack, which functions in a similar fashion to black-hole, except, instead of dropping all passing messages, only a select few will be dropped, dependant on various metrics from random to specific message types [62].
4.8.4. IoT
4.8.5. Software Defined Networking (SDN)
- Reconnaissance, where the attacker can observe and analyse various vulnerabilities in the SDN system, allowing them to possibly penetrate into the system.
- Data Exfiltration Attack, where, once the attacker has gained access to the system, they can recover and extract compromising data as well as security credentials to the rest of the system.
5. Analysis of the Categorisation Methodologies
6. Discussion
6.1. Challenges
6.1.1. Intrusion Detection Systems
6.1.2. IoT
Interdependence
Diversity
Constrained
Myriad
Unattended
Intimacy
Mobile
Ubiquitous
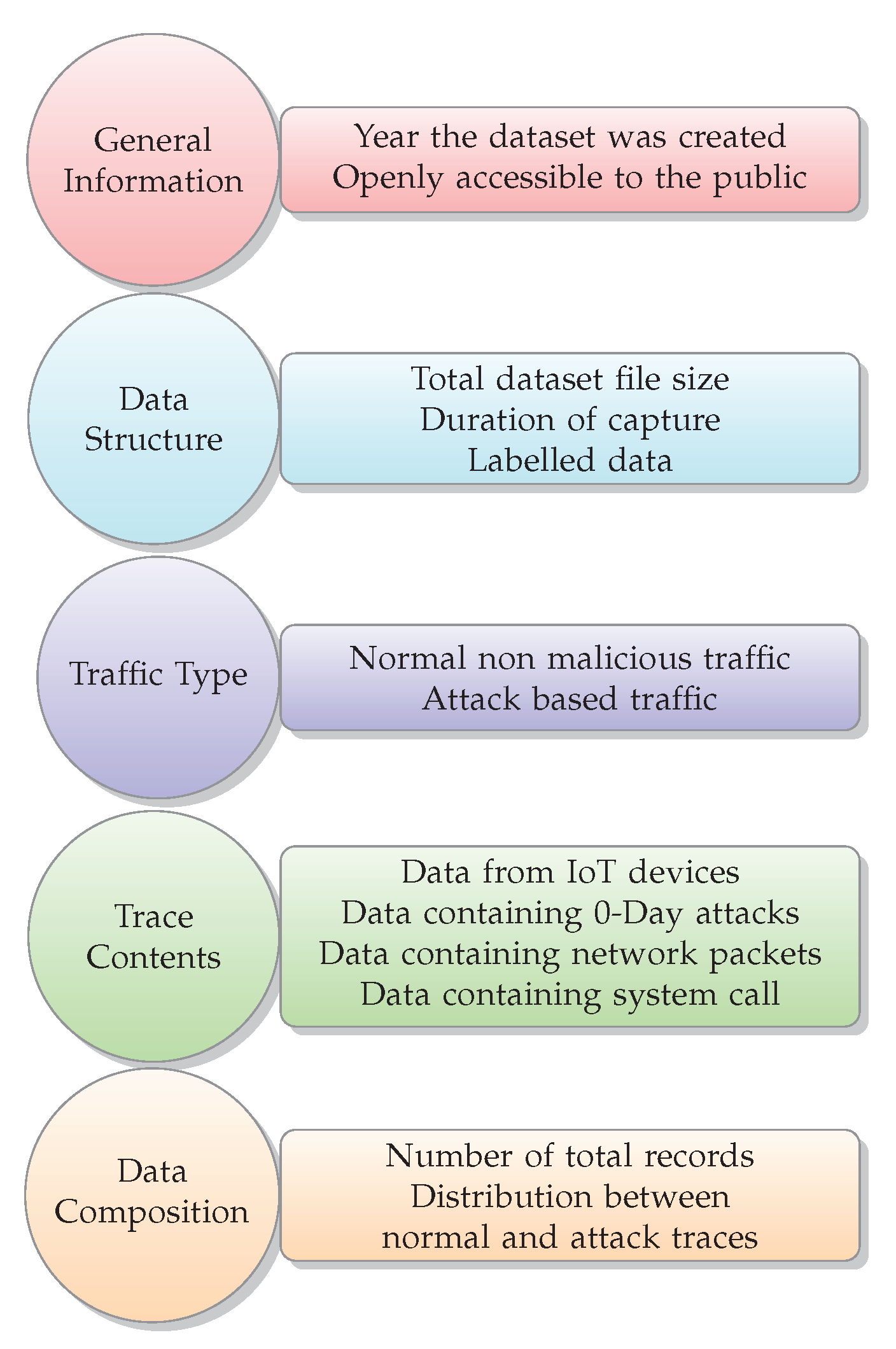
6.2. Data Sets
6.2.1. General Information
6.2.2. Data Structure
6.2.3. Traffic Type
6.2.4. Trace Contents
6.2.5. Data Composition
6.2.6. Data Set Analysis
7. Lessons Learned
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- CSRC. Glossary-Cyber Attack Definition. 2010. Available online: https://csrc.nist.gov/glossary/term/Cyber_Attack (accessed on 26 August 2020).
- McCurry, J. South Korean nuclear operator hacked amid cyber-attack fears. Guardian. 2014. Available online: https://www.theguardian.com/world/2014/dec/22/south-korea-nuclear-power-cyber-attack-hack (accessed on 2 August 2021).
- Perlroth, N.; Krauss, C. A cyber attack in Saudi Arabia failed to cause carnage, but the next attempt could be deadly. Independent. 2018. Available online: https://www.independent.co.uk/news/long_reads/cyber-warfare-saudi-arabia-petrochemical-security-america-a8258636.html (accessed on 2 August 2021).
- Huntsman. Critical Infrastructure Cyber Security Solutions. 2015. Available online: https://www.huntsmansecurity.com/industries/critical-infrastructure/ (accessed on 17 December 2020).
- Viganò, E.; Loi, M.; Yaghmaei, E. Cybersecurity of critical infrastructure. In The Ethics of Cybersecurity; Springer: Cham, Switzerland, 2020; pp. 157–177. [Google Scholar]
- Vanhoef, M.; Piessens, F. Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2. In Proceedings of the 24th ACM Conference on Computer and Communications Security (CCS), Dallas, TX, USA, 30 October–3 November 2017. [Google Scholar]
- Zhang, L.; Ding, G.; Wu, Q.; Zou, Y.; Han, Z.; Wang, J. Byzantine Attack and Defense in Cognitive Radio Networks: A Survey. IEEE Commun. Surv. Tutor. 2015, 17, 1342–1363. [Google Scholar] [CrossRef]
- Rodofile, N.R.; Radke, K.; Foo, E. Framework for SCADA Cyber-Attack Dataset Creation. In Proceedings of the Australasian Computer Science Week Multiconference, Geelong, Australia, 30 January–3 February 2017. [Google Scholar]
- Sanghvi, H.; Dahiya, M. Cyber reconnaissance: An alarm before cyber attack. Int. J. Comput. Appl. 2013, 63. [Google Scholar] [CrossRef]
- CSRCN. Glossary-Vulnerability Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/vulnerability (accessed on 26 August 2020).
- Sullivan, J.E.; Kamensky, D. How cyber-attacks in Ukraine show the vulnerability of the U.S. power grid. Electr. J. 2017, 30, 30–35. [Google Scholar] [CrossRef]
- Joaquín, R. CIPSEC-Most Common Attack Vectors over Critical Infrastructures. 2018. Available online: https://www.cipsec.eu/content/most-common-attack-vector-over-critical-infrastructures (accessed on 26 August 2020).
- Mahmoud, R.; Yousuf, T.; Aloul, F.; Zualkernan, I. Internet of Things (IoT) Security: Current Status, Challenges and Prospective Measures. In Proceedings of the 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 14–16 December 2015; pp. 336–341. [Google Scholar]
- Zhou, W.; Jia, Y.; Peng, A.; Zhang, Y.; Liu, P. The Effect of IoT New Features on Security and Privacy: New Threats, Existing Solutions, and Challenges Yet to Be Solved. IEEE Internet Things J. 2019, 6, 1606–1616. [Google Scholar] [CrossRef]
- New Cyber Attack Categorisation System to Improve UK Response to Incidents. 2018. Available online: https://www.ncsc.gov.uk/news/new-cyber-attack-categorisation-system-improve-uk-response-incidents (accessed on 23 September 2020).
- Giraldo, J.; Sarkar, E.; Cardenas, A.A.; Maniatakos, M.; Kantarcioglu, M. Security and Privacy in Cyber-Physical Systems: A Survey of Surveys. IEEE Des. Test 2017, 34, 7–17. [Google Scholar] [CrossRef]
- Smith, R. Assault on California Power Station Raises Alarm on Potential for Terrorism. Wall Street J. 2014. Available online: https://www.wsj.com/articles/SB10001424052702304851104579359141941621778 (accessed on 4 August 2021).
- Wood, A.D.; Stankovic, J.A. Denial of service in sensor networks. Computer 2002, 35, 54–62. [Google Scholar] [CrossRef]
- Ahmed, M.; Mahmood, A.N.; Hu, J. A survey of network anomaly detection techniques. J. Netw. Comput. Appl. 2016, 60, 19–31. [Google Scholar] [CrossRef]
- Raiyn, J. A survey of cyber attack detection strategies. Int. J. Secur. Appl. 2014, 8, 247–256. [Google Scholar] [CrossRef]
- Khraisat, A.; Gondal, I.; Vamplew, P.; Kamruzzaman, J. Survey of Intrusion Detection Systems: Techniques, Datasets and Challenges. Cybersecurity 2019, 2, 20. [Google Scholar] [CrossRef]
- Ahmed, M. Intelligent Big Data Summarization for Rare Anomaly Detection. IEEE Access 2019, 7, 68669–68677. [Google Scholar] [CrossRef]
- Diro, A.A.; Chilamkurti, N. Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Stiawan, D.; Idris, M.Y.; Malik, R.F.; Nurmaini, S.; Alsharif, N.; Budiarto, R. Investigating Brute Force Attack Patterns in IoT Network. J. Electr. Comput. Eng. 2019, 2019, 1–13. [Google Scholar] [CrossRef]
- Mahfouz, A.M.; Venugopal, D.; Shiva, S.G. Comparative Analysis of ML Classifiers for Network Intrusion Detection. In Fourth International Congress on Information and Communication Technology; Springer: Singapore, 2020; pp. 193–207. [Google Scholar]
- Conti, M.; Dragoni, N.; Lesyk, V. A Survey of Man In The Middle Attacks. IEEE Commun. Surv. Tutor. 2016, 18, 2027–2051. [Google Scholar] [CrossRef]
- Whalen, S. An Introduction to Arp Spoofing. Node99 [Online Document]. April. 2001. Available online: http://index-of.es/Networking/arpspoof.pdf (accessed on 2 August 2021).
- Kim, H.; Huh, J. Detecting DNS-poisoning-based phishing attacks from their network performance characteristics. Electron. Lett. 2011, 47, 656–658. [Google Scholar] [CrossRef]
- CSRCN. Glossary-Brute Force Attack Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/brute_force_attack (accessed on 21 September 2020).
- Singh, J.; Kaur, S.; Kaur, G.; Kaur, G. A Detailed Survey and Classification of Commonly Recurring Cyber Attacks. Int. J. Comput. Appl. 2016, 975, 8887. [Google Scholar] [CrossRef]
- Rughoobur, P.; Nagowah, L. A lightweight replay attack detection framework for battery depended IoT devices designed for healthcare. In Proceedings of the 2017 International Conference on Infocom Technologies and Unmanned Systems (Trends and Future Directions) (ICTUS), Dubai, United Arab Emirates, 18–20 December 2017; pp. 811–817. [Google Scholar]
- Yang, Q.; An, D.; Min, R.; Yu, W.; Yang, X.; Zhao, W. On Optimal PMU Placement-Based Defense Against Data Integrity Attacks in Smart Grid. IEEE Trans. Inf. Forensics Secur. 2017, 12, 1735–1750. [Google Scholar] [CrossRef]
- Liu, Y.; Ning, P.; Reiter, M.K. False Data Injection Attacks against State Estimation in Electric Power Grids. ACM Trans. Inf. Syst. Secur. 2011, 14, 21–32. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Yang, X.; Xu, G.; Zhao, W. On False Data Injection Attacks against Distributed Energy Routing in Smart Grid. In Proceedings of the 2012 IEEE/ACM Third International Conference on Cyber-Physical Systems, Beijing, China, 17–19 April 2012; pp. 183–192. [Google Scholar]
- Ding, D.; Han, Q.L.; Xiang, Y.; Ge, X.; Zhang, X.M. A Survey on Security Control and Attack Detection for Industrial Cyber-Physical Systems. Neurocomputing 2018, 275, 1674–1683. [Google Scholar] [CrossRef]
- Mahmoud, M.S.; Hamdan, M.M.; Baroudi, U.A. Modeling and control of Cyber-Physical Systems subject to cyber attacks: A survey of recent advances and challenges. Neurocomputing 2019, 338, 101–115. [Google Scholar] [CrossRef]
- Zeng, Y.; Zhang, R. Active eavesdropping via spoofing relay attack. In Proceedings of the 2016 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Shanghai, China, 20–25 March 2016; pp. 2159–2163. [Google Scholar]
- Jakobsson, M.; Wetzel, S.; Yener, B. Stealth attacks on ad-hoc wireless networks. In Proceedings of the 2003 IEEE 58th Vehicular Technology Conference, Orlando, FL, USA, 6–9 October 2003; Volume 3, pp. 2103–2111. [Google Scholar]
- Ling, Z.; Liu, K.; Xu, Y.; Jin, Y.; Fu, X. An End-to-End View of IoT Security and Privacy. In Proceedings of the 2017 IEEE Global Communications Conference, Singapore, 4–8 December 2017; pp. 1–7. [Google Scholar]
- Al-Alami, H.; Hadi, A.; Al-Bahadili, H. Vulnerability scanning of IoT devices in Jordan using Shodan. In Proceedings of the 2017 2nd International Conference on the Applications of Information Technology in Developing Renewable Energy Processes Systems (IT-DREPS), Piscataway, NJ, USA, 6–8 December 2017; pp. 1–6. [Google Scholar]
- Kaushik, A.K.; Pilli, E.S.; Joshi, R.C. Network forensic system for port scanning attack. In Proceedings of the 2010 IEEE 2nd International Advance Computing Conference (IACC), Patiala, India, 19–20 February 2010; pp. 310–315. [Google Scholar]
- Mitropoulos, D.; Spinellis, D. Fatal injection: A survey of modern code injection attack countermeasures. PeerJ Comput. Sci. 2017, 3, e136. [Google Scholar] [CrossRef]
- Yan, R.; Xiao, X.; Hu, G.; Peng, S.; Jiang, Y. New deep learning method to detect code injection attacks on hybrid applications. J. Syst. Softw. 2018, 137, 67–77. [Google Scholar] [CrossRef]
- Cazorla, L.; Alcaraz, C.; Lopez, J. Cyber Stealth Attacks in Critical Information Infrastructures. IEEE Syst. J. 2018, 12, 1778–1792. [Google Scholar] [CrossRef]
- Douceur, J.R. The Sybil Attack. In Peer-to-Peer Systems; Springer: Berlin/Heidelberg, Germany, 2002; pp. 251–260. [Google Scholar]
- Jan, M.A.; Nanda, P.; He, X.; Liu, R.P. A Sybil attack detection scheme for a forest wildfire monitoring application. Future Gener. Comput. Syst. 2018, 80, 613–626. [Google Scholar] [CrossRef]
- Kaur, M.; Singh, A. Detection and Mitigation of Sinkhole Attack in Wireless Sensor Network. In Proceedings of the 2016 International Conference on Micro-Electronics and Telecommunication Engineering (ICMETE), Ghaziabad, India, 22 September 2016; pp. 217–221. [Google Scholar]
- Schirrmacher, N.B.; Ondrus, J.; Tan, F.T.C. Towards a Response to Ransomware: Examining Digital Capabilities of the Wanna Cry Attack; PACIS: Yokohama, Japan, 2018; p. 210. [Google Scholar]
- Richardson, R.; North, M.M. Ransomware: Evolution, mitigation and prevention. Int. Manag. Rev. 2017, 13, 10. [Google Scholar]
- Mohurle, S.; Patil, M. A brief study of Wannacry threat: Ransomware attack 2017. Int. J. Adv. Res. Comput. Sci. 2017, 8, 1938–1940. [Google Scholar]
- CSRCN. Glossary-Virus Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/virus (accessed on 23 September 2020).
- CSRCN. Glossary-Spyware Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/spyware (accessed on 23 September 2020).
- CSRCN. Glossary-Cryptanalysis Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/cryptanalysis (accessed on 23 September 2020).
- CSRCN. Glossary-Side Channel Attack Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/Side_Channel_Attack (accessed on 23 September 2020).
- Deogirikar, J.; Vidhate, A. Security attacks in IoT: A survey. In Proceedings of the 2017 International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), Palladam, India, 10–11 February 2017; pp. 32–37. [Google Scholar]
- Chelli, K. Security Issues in Wireless Sensor Networks: Attacks and Countermeasures. In Proceedings of the World Congress on Engineering, London, UK, 3–8 July 2015. [Google Scholar]
- Inria. Cybersecurity: Current Challenges and Inria’s Research Directions; Technical Report 3; Inria: Villeneuve-d’Ascq, France, 2019. [Google Scholar]
- Goyal, P.; Parmar, V.; Rishi, R. Manet: Vulnerabilities, challenges, attacks, application. IJCEM Int. J. Comput. Eng. Manag. 2011, 11, 32–37. [Google Scholar]
- Flauzac, O.; González, C.; Hachani, A.; Nolot, F. SDN Based Architecture for IoT and Improvement of the Security. In Proceedings of the 2015 IEEE 29th International Conference on Advanced Information Networking and Applications Workshops, Gwangiu, Korea, 24–27 March 2015; pp. 688–693. [Google Scholar]
- Shahzad, F.; Pasha, M.; Ahmad, A. A Survey of Active Attacks on Wireless Sensor Networks and their Countermeasures. CoRR 2017, CoRR, 54–65. [Google Scholar]
- Ahmad, K. Classification of Internet Security Attacks. In Proceedings of the 5th National Conference INDIACom-2011Bharti Vidyapeeth’s Institute of Computer Applications and Management, New Dehli, India, 10–11 February 2011; pp. 973–7529. [Google Scholar]
- Shanmuganathan, V.; Anand, T. A survey on gray hole attack in manet. IRACST Int. J. Comput. Netw. Wirel. Commun. (IJCNWC) 2012, 2, 647–650. [Google Scholar]
- Apthorpe, N.; Reisman, D.; Sundaresan, S.; Narayanan, A.; Feamster, N. Spying on the smart home: Privacy attacks and defenses on encrypted IoT traffic. arXiv 2017, arXiv:1708.05044. [Google Scholar]
- Hernández Marcano, N.; Sørensen, C.; Cabrera G., J.; Wunderlich, S.; Lucani, D.; Fitzek, F. On Goodput and Energy Measurements of Network Coding Schemes in the Raspberry Pi. Electronics 2016, 5, 66. [Google Scholar] [CrossRef]
- CSRCN. Glossary-Covert Channel Definition. 2018. Available online: https://csrc.nist.gov/glossary/term/covert_channel (accessed on 23 September 2020).
- Krombholz, K.; Hobel, H.; Huber, M.; Weippl, E. Advanced social engineering attacks. J. Inf. Secur. Appl. 2015, 22, 113–122. [Google Scholar] [CrossRef]
- Williams, E.J.; Hinds, J.; Joinson, A.N. Exploring susceptibility to phishing in the workplace. Int. J. Hum.-Comput. Stud. 2018, 120, 1–13. [Google Scholar] [CrossRef]
- Alwan, Z.S.; Younis, M.F. Detection and prevention of SQL injection attack: A survey. Int. J. Comput. Sci. Mob. Comput. 2017, 6, 5–17. [Google Scholar]
- Wang, C.; Zheng, X.; Chen, Y.; Yang, J. Locating Rogue Access Point Using Fine-Grained Channel Information. IEEE Trans. Mob. Comput. 2017, 16, 2560–2573. [Google Scholar] [CrossRef]
- Gupta, A.; Jha, R.K. Security Threats of Wireless Networks: A Survey. In Proceedings of the International Conference on Computing, Communication Automation, Greater Noida, India, 15–16 May 2015; pp. 389–395. [Google Scholar]
- Surman, G. Understanding Security Using the OSI Model. In SANS Institute Reading Room; Cyber Security Training, Certifications, Degrees and Resources: Boston, MA, USA, 2002. [Google Scholar]
- Wenyuan, X.; Ma, K.; Trappe, W.; Yanyong Zhang, Y. Jamming sensor networks: Attack and defense strategies. IEEE Netw. 2006, 20, 41–47. [Google Scholar] [CrossRef]
- Kolahi, S.S.; Treseangrat, K.; Sarrafpour, B. Analysis of UDP DDoS flood cyber attack and defense mechanisms on Web Server with Linux Ubuntu 13. In Proceedings of the 2015 International Conference on Communications, Signal Processing, and their Applications (ICCSPA’15), Piscataway, NJ, USA, 16–19 February 2015; pp. 1–5. [Google Scholar]
- Karchowdhury, S.; Sen, M. Survey on Attacks on Wireless Body Area Network. Int. J. Comput. Intell. IoT Forthcom. 2019, pp. 638–644. Available online: https://ssrn.com/abstract=3358378 (accessed on 2 August 2021).
- CSRCN. Glossary-Cyber-Physical System(s). 2020. Available online: https://csrc.nist.gov/glossary/term/cyber_physical_systems (accessed on 25 September 2020).
- Yang, C.; Shi, Z.; Zhang, H.; Wu, J.; Shi, X. Multiple Attacks Detection in Cyber-Physical Systems Using Random Finite Set Theory. IEEE Trans. Cybern. 2019, 50, 4066–4075. [Google Scholar] [CrossRef] [PubMed]
- Karnouskos, S. Stuxnet worm impact on industrial cyber-physical system security. In Proceedings of the IECON 2011-37th Annual Conference of the IEEE Industrial Electronics Society, Melbourne, Australia, 7–10 November 2011; pp. 4490–4494. [Google Scholar]
- Farwell, J.P.; Rohozinski, R. Stuxnet and the Future of Cyber War. Survival 2011, 53, 23–40. [Google Scholar] [CrossRef]
- Zhang, X.; Han, Q.; Ge, X.; Ding, D.; Ding, L.; Yue, D.; Peng, C. Networked control systems: A survey of trends and techniques. IEEE/CAA J. Autom. Sin. 2020, 7, 1–17. [Google Scholar] [CrossRef]
- Mousavinejad, E.; Yang, F.; Han, Q.; Vlacic, L. A Novel Cyber Attack Detection Method in Networked Control Systems. IEEE Trans. Cybern. 2018, 48, 3254–3264. [Google Scholar] [CrossRef] [PubMed]
- Slay, J.; Miller, M. Lessons Learned from the Maroochy Water Breach. In Critical Infrastructure Protection; Springer: Boston, MA, USA, 2008; pp. 73–82. [Google Scholar]
- Sahoo, S.; Mishra, S.; Peng, J.C.; Dragičević, T. A Stealth Cyber-Attack Detection Strategy for DC Microgrids. IEEE Trans. Power Electron. 2019, 34, 8162–8174. [Google Scholar] [CrossRef]
- Kurt, M.N.; Ogundijo, O.; Li, C.; Wang, X. Online Cyber-Attack Detection in Smart Grid: A Reinforcement Learning Approach. IEEE Trans. Smart Grid 2019, 10, 5174–5185. [Google Scholar] [CrossRef]
- Berghel, H. Wireless Infidelity I: War Driving. Commun. ACM 2004, 47, 21–26. [Google Scholar] [CrossRef]
- Nurjahan, N.; Nizam, F.; Chaki, S.; Al Mamun, S.; Kaiser, M.S. Attack Detection and Prevention in the Cyber Physical System. In Proceedings of the 2016 International Conference on Computer Communication and Informatics (ICCCI), Coimbatore, India, 7–9 January 2016; pp. 1–6. [Google Scholar]
- Liang, G.; Weller, S.R.; Zhao, J.; Luo, F.; Dong, Z.Y. The 2015 Ukraine Blackout: Implications for False Data Injection Attacks. IEEE Trans. Power Syst. 2017, 32, 3317–3318. [Google Scholar] [CrossRef]
- Elbez, G.; Keller, H.B.; Hagenmeyer, V. A New Classification of Attacks Against the Cyber-Physical Security of Smart Grids. In Proceedings of the 13th International Conference on Availability, Reliability and Security, Hamburg, Germany, 27–30 August 2018; pp. 63:1–63:6. [Google Scholar]
- Sakhnini, J.; Karimipour, H.; Dehghantanha, A. Smart Grid Cyber Attacks Detection Using Supervised Learning and Heuristic Feature Selection. In Proceedings of the 2019 IEEE 7th International Conference on Smart Energy Grid Engineering (SEGE), Ontario, ON, Canada, 12–14 August 2019; pp. 108–112. [Google Scholar]
- CSRCN. Glossary-Buffer Overflow. 2020. Available online: https://csrc.nist.gov/glossary/term/buffer_overflow (accessed on 10 September 2020).
- Caballero, J.; Grieco, G.; Marron, M.; Nappa, A. Undangle: Early Detection of Dangling Pointers in Use-after-Free and Double-Free Vulnerabilities. In Proceedings of the 2012 International Symposium on Software Testing and Analysis. Association for Computing Machinery, Amsterdam, The Netherlands, 11–17 July 2012; pp. 133–143. [Google Scholar]
- CSRCN. Glossary-Trojan Horse. 2020. Available online: https://csrc.nist.gov/glossary/term/trojan_horse (accessed on 10 September 2020).
- Geer, D. Malicious bots threaten network security. Computer 2005, 38, 18–20. [Google Scholar] [CrossRef]
- Nardone, R.; Rodríguez, R.J.; Marrone, S. Formal security assessment of Modbus protocol. In Proceedings of the 2016 11th International Conference for Internet Technology and Secured Transactions (ICITST), Barcelona, Spain, 5–7 July 2016; pp. 142–147. [Google Scholar]
- IEEE Standards Association. Standard for Electric Power Systems Communications-Distributed Network Protocol (DNP3). 2012, pp. 1–821. Available online: https://ieeexplore.ieee.org/document/5518537 (accessed on 2 August 2021).
- Akyildiz, I.F.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar] [CrossRef]
- Dey, N.; Ashour, A.S.; Shi, F.; Fong, S.J.; Sherratt, R.S. Developing residential wireless sensor networks for ECG healthcare monitoring. IEEE Trans. Consum. Electron. 2017, 63, 442–449. [Google Scholar] [CrossRef]
- Geetha, A.; Sreenath, N. Byzantine Attacks and its Security Measures in Mobile Adhoc Networks. Int. J. Comput. Commun. Instrum. Eng. (IJCCIE) 2016, 3, 42–47. [Google Scholar]
- Tamilselvan, L.; Sankaranarayanan, V. Prevention of Blackhole Attack in MANET. In Proceedings of the 2nd International Conference on Wireless Broadband and Ultra Wideband Communications (AusWireless 2007), Sydney, Australia, 27–30 August 2007; p. 21. [Google Scholar]
- Mahajan, V.; Natu, M.; Sethi, A. Analysis of wormhole intrusion attacks in MANETS. In Proceedings of the MILCOM 2008–2008 IEEE Military Communications Conference, San Diego, CA, USA, 16–19 November 2008; pp. 1–7. [Google Scholar]
- Khan, M.A.; Salah, A. IoT security: Review, blockchain solutions, and open challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- Wang, K.; Du, M.; Sun, Y.; Vinel, A.; Zhang, Y. Attack Detection and Distributed Forensics in Machine-to-Machine Networks. IEEE Netw. 2016, 30, 49–55. [Google Scholar] [CrossRef]
- Anbalagan, G. NetSupport RAT Installed via Fake Update Notices. 2019. Available online: https://www.zscaler.com/blogs/research/netsupport-rat-installed-fake-update-notices, (accessed on 15 October 2020).
- Gallais, A.; Hedli, T.; Loscri, V.; Mitton, N. Denial-of-Sleep Attacks against IoT Networks. In Proceedings of the 2019 6th International Conference on Control, Decision and Information Technologies (CoDIT), Paris, France, 23–26 August 2019; pp. 1025–1030. [Google Scholar]
- Bhattasali, T.; Chaki, R.; Sanyal, S. Sleep Deprivation Attack Detection in Wireless Sensor Network. CoRR 2012, abs/1203.0231, 19–25. [Google Scholar] [CrossRef]
- Pongle, P.; Chavan, G. A survey: Attacks on RPL and 6LoWPAN in IoT. In Proceedings of the 2015 International Conference on Pervasive Computing (ICPC), Pune, India, 8–10 January 2015; pp. 1–6. [Google Scholar]
- Jan, S.; Nguyen, C.D.; Briand, L.C. Automated and Effective Testing of Web Services for XML Injection Attacks. In Proceedings of the ISSTA 2016, Association for Computing Machinery, Saarbrücken, Germany, 18–20 July 2016; pp. 12–23. [Google Scholar]
- Dhem, J.F.; Koeune, F.; Leroux, P.A.; Mestré, P.; Quisquater, J.J.; Willems, J.L. A Practical Implementation of the Timing Attack. In Smart Card Research and Applications; Springer: Berlin/Heidelberg, Germany, 2000; pp. 167–182. [Google Scholar]
- Mohamad Noor, M.; Hassan, W.H. Current research on Internet of Things (IoT) security: A survey. Comput. Netw. 2019, 148, 283–294. [Google Scholar] [CrossRef]
- ONF. OpenFlow Switch Specification. In ONF Specification Version 1.5.1 (Protocol version 0x06); Open Networking Foundation: Menlo Park, CA, USA, 2015; pp. 1–283. [Google Scholar]
- Tayyaba, S.K.; Shah, M.A.; Khan, O.A.; Ahmed, A.W. Software Defined Network (SDN) Based Internet of Things (IoT): A Road Ahead. In Proceedings of the International Conference on Future Networks and Distributed Systems. Association for Computing Machinery, Cambridge, UK, 19–20 July 2017. [Google Scholar]
- Ge, M.; Cho, J.H.; Ishfaq, B.; Kim, D.S. Modeling and Analysis of Integrated Proactive Defense Mechanisms for Internet-of-Things. In Modeling and Design of Secure Internet of Things; John Wiley & Sons, Ltd.: Chichester, UK, 2020. [Google Scholar]
- Xu, Y.; Liu, Y. DDoS attack detection under SDN context. In Proceedings of the IEEE INFOCOM 2016-The 35th Annual IEEE International Conference on Computer Communications, San Francisco, CA, USA, 10–15 April 2016; pp. 1–9. [Google Scholar]
- Mousavi, S.M.; St-Hilaire, M. Early detection of DDoS attacks against SDN controllers. In Proceedings of the 2015 International Conference on Computing, Networking and Communications (ICNC), Garden Grove, CA, USA, 16–19 February 2015; pp. 77–81. [Google Scholar]
- Scott-Hayward, S.; O’Callaghan, G.; Sezer, S. SDN Security: A Survey. In Proceedings of the 2013 IEEE SDN for Future Networks and Services (SDN4FNS), Trento, Italy, 11–13 November 2013; pp. 1–7. [Google Scholar]
- Blial, O.; Ben Mamoun, M.; Benaini, R. An Overview on SDN Architectures with Multiple Controllers. J. Comput. Netw. Commun. 2016, 2016, 9396525. [Google Scholar] [CrossRef]
- Mutlu, O.; Kim, J.S. RowHammer: A Retrospective. IEEE Trans. Comput.-Aided Des. Integr. Circuits Syst. 2020, 39, 1555–1571. [Google Scholar] [CrossRef]
- Jay, J. Two Years after WannaCry, 2300 NHS Computers Are Still Running Windows XP. 2019. Available online: https://www.teiss.co.uk/nhs-computers-windows-xp/ (accessed on 28 October 2020).
- Tawalbeh, L.; Muheidat, F.; Tawalbeh, M.; Quwaider, M. IoT Privacy and Security: Challenges and Solutions. Appl. Sci. 2020, 10, 4102. [Google Scholar] [CrossRef]
- Zhang, K.; Ni, J.; Yang, K.; Liang, X.; Ren, J.; Shen, X.S. Security and Privacy in Smart City Applications: Challenges and Solutions. IEEE Commun. Mag. 2017, 55, 122–129. [Google Scholar] [CrossRef]
- Alhalafi, N.; Veeraraghavan, P. Privacy and Security Challenges and Solutions in IOT: A review. IOP Conf. Ser. Earth Environ. Sci. 2019, 322, 012013. [Google Scholar] [CrossRef]
- Ring, M.; Wunderlich, S.; Scheuring, D.; Landes, D.; Hotho, A. A Survey of Network-based Intrusion Detection Data Sets. CoRR 2019, abs/1903.02460, 147–167. [Google Scholar] [CrossRef]
- Junejo, K.N.; Goh, J. Behaviour-Based Attack Detection and Classification in Cyber Physical Systems Using Machine Learning. In Proceedings of the 2nd ACM International Workshop on Cyber-Physical System Security, Xi’an, China, 30 May 2016; pp. 34–43. [Google Scholar]
- Creech, G.; Hu, J. Generation of a new IDS test dataset: Time to retire the KDD collection. In Proceedings of the 2013 IEEE Wireless Communications and Networking Conference (WCNC), Shanghai, China, 7–10 April 2013; pp. 4487–4492. [Google Scholar]
- Creech, G.; Hu, J. A Semantic Approach to Host-Based Intrusion Detection Systems Using Contiguous and Discontiguous System Call Patterns. IEEE Trans. Comput. 2014, 63, 807–819. [Google Scholar] [CrossRef]
- Creech, G. Developing a High-Accuracy Cross Platform Host-Based Intrusion Detection System Capable of Reliably Detecting Zero-Day Attacks. Ph.D. Thesis, University of New South Wales, Engineering & Information Technology, Sydnay, Australia, 2014. [Google Scholar]
- The ADFA Intrusion Detection Datasets. 2013. Available online: https://www.unsw.adfa.edu.au/unsw-canberra-cyber/cybersecurity/ADFA-IDS-Datasets/ (accessed on 30 November 2020).
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Gritzalis, S. Intrusion Detection in 802.11 Networks: Empirical Evaluation of Threats and a Public Dataset. IEEE Commun. Surv. Tutor. 2016, 18, 184–208. [Google Scholar] [CrossRef]
- AWID Dataset. 2015. Available online: http://icsdweb.aegean.gr/awid/index.html (accessed on 30 November 2020).
- Santanna, J.J.; van Rijswijk-Deij, R.; Hofstede, R.; Sperotto, A.; Wierbosch, M.; Granville, L.Z.; Pras, A. Booters–An analysis of DDoS-as-a-service attacks. In Proceedings of the 2015 IFIP/IEEE International Symposium on Integrated Network Management (IM), Ottawa, ON, Canada, 18–21 May 2015; pp. 243–251. [Google Scholar]
- Koroniotis, N.; Moustafa, N.; Sitnikova, E. andTurnbull, B. Towards the Development of Realistic Botnet Dataset in the Internet of Things for Network Forensic Analytics: Bot-IoT Dataset. CoRR 2018, abs/1811.00701, 779–796. [Google Scholar]
- Bot-IoT Dataset. 2018. Available online: https://research.unsw.edu.au/projects/bot-iot-dataset (accessed on 30 November 2020).
- Biglar Beigi, E.; Hadian Jazi, H.; Stakhanova, N.; Ghorbani, A.A. Towards effective feature selection in machine learning-based botnet detection approaches. In Proceedings of the 2014 IEEE Conference on Communications and Network Security, San Francisco, CA, USA, 29–31 October 2014; pp. 247–255. [Google Scholar]
- Botnet Dataset. 2014. Available online: https://www.unb.ca/cic/datasets/botnet.html (accessed on 30 November 2020).
- The CAIDA “DDoS Attack 2007” Dataset. 2007. Available online: https://www.caida.org/data/passive/ddos-20070804_dataset.xml (accessed on 30 November 2020).
- DDoS Evaluation Dataset (CIC-DDoS2019). 2019. Available online: https://www.unb.ca/cic/datasets/ddos-2019.html (accessed on 25 September 2020).
- Sharafaldin, I.; Lashkari, A.H.; Hakak, S.; Ghorbani, A.A. Developing Realistic Distributed Denial of Service (DDoS) Attack Dataset and Taxonomy. In Proceedings of the 2019 International Carnahan Conference on Security Technology (ICCST), Chennai, India, 1–3 October 2019; pp. 1–8. [Google Scholar]
- Jazi, H.H.; Gonzalez, H.; Stakhanova, N.; Ghorbani, A.A. Detecting HTTP-based application layer DoS attacks on web servers in the presence of sampling. Comput. Netw. 2017, 121, 25–36. [Google Scholar] [CrossRef]
- CIC DoS Dataset. 2017. Available online: https://www.unb.ca/cic/datasets/dos-dataset.html (accessed on 30 November 2020).
- Sharafaldin, I.; Lashkari, A.H.; Ghorbani, A.A. Toward Generating a New Intrusion Detection Dataset and Intrusion Traffic Characterization. In Proceedings of the International Conference on Information Systems Security and Privacy ICISSP, Funchal, Portugal, 24 January 2018; pp. 108–116. [Google Scholar]
- Intrusion Detection Evaluation Dataset (CIC-IDS2017). 2017. Available online: https://www.unb.ca/cic/datasets/ids-2017.html (accessed on 30 November 2020).
- Ring, M.; Wunderlich, S.; Grüdl, D.; Landes, D.; Hotho, A. Flow-based benchmark data sets for intrusion detection. In Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS), ACPI, Dublin, Ireland, 29–30 June 2017; pp. 361–369. [Google Scholar]
- CIDDS-Coburg Intrusion Detection Data Sets. 2017. Available online: https://www.hs-coburg.de/forschung/forschungsprojekte-oeffentlich/informationstechnologie/cidds-coburg-intrusion-detection-data-sets.html (accessed on 30 November 2020).
- Ring, M.; Wunderlich, S.; Grüdl, D.; Landes, D.; Hotho, A. Creation of Flow-Based Data Sets for Intrusion Detection. J. Inf. Warf. 2017, 16, 40–53. [Google Scholar]
- Sangster, B.; O’Connor, T.J.; Cook, T.; Fanelli, R.; Dean, E.; Adams, W.J.; Morrell, C.; Conti, G. Toward Instrumenting Network Warfare Competitions to Generate Labeled Datasets. In Proceedings of the 2nd Conference on Cyber Security Experimentation and Test, Montreal, QC, Canada, 10–14 August 2009; p. 9. [Google Scholar]
- Point, U.S.M.A.W. CDX 2009 Dataset. 2009. Available online: https://www.westpoint.edu/centers-and-research/cyber-research-center/data-sets (accessed on 30 November 2020).
- García, S.; Grill, M.; Stiborek, J.; Zunino, A. An empirical comparison of botnet detection methods. Comput. Secur. 2014, 45, 100–123. [Google Scholar] [CrossRef]
- Lab, S. CTU-13 Dataset. 2009. Available online: https://www.stratosphereips.org/datasets-ctu13 (accessed on 30 November 2020).
- Lippmann, R.; Haines, J.W.; Fried, D.J.; Korba, J.; Das, K. The 1999 DARPA off-line intrusion detection evaluation. Comput. Netw. 2000, 34, 579–595. [Google Scholar] [CrossRef]
- DARPA. 1999. Available online: https://www.ll.mit.edu/r-d/datasets/1999-darpa-intrusion-detection-evaluation-dataset (accessed on 30 November 2020).
- Perona, I.; Gurrutxaga, I.; Arbelaitz, O.; Martín, J.I.; Muguerza, J.; Pérez, J.M. Service-Independent Payload Analysis to Improve Intrusion Detection in Network Traffic. In Proceedings of the 7th Australasian Data Mining Conference, Glenelg, Australia, 27 November 2008; Volume 87, pp. 171–178. [Google Scholar]
- Sahu, S.K.; Sarangi, S.; Jena, S.K. A detail analysis on intrusion detection datasets. In Proceedings of the 2014 IEEE International Advance Computing Conference (IACC), Gurgaon, Indian, 21–22 February 2014; pp. 1348–1353. [Google Scholar]
- Gure KDD Cup. 2008. Available online: http://www.sc.ehu.es/acwaldap/gureKddcup/ (accessed on 30 November 2020).
- Zuech, R.; Khoshgoftaar, T.; Seliya, N.; Najafabadi, M.M.; Kemp, C. A New Intrusion Detection Benchmarking System. In Proceedings of the FLAIRS Conference, Hollywood, FL, USA, 18–20 May 2015. [Google Scholar]
- Shiravi, A.; Shiravi, H.; Tavallaee, M.; Ghorbani, A.A. Toward developing a systematic approach to generate benchmark datasets for intrusion detection. Comput. Secur. 2012, 31, 357–374. [Google Scholar] [CrossRef]
- Intrusion Detection Evaluation Dataset (ISCXIDS2012). 2012. Available online: https://www.unb.ca/cic/datasets/ids.html (accessed on 30 November 2020).
- Saad, S.; Traore, I.; Ghorbani, A.; Sayed, B.; Zhao, D.; Lu, W.; Felix, J.; Hakimian, P. Detecting P2P botnets through network behavior analysis and machine learning. In Proceedings of the 2011 Ninth Annual International Conference on Privacy, Security and Trust, Montreal, QC, Canada, 26–28 August 2011; pp. 174–180. [Google Scholar]
- Datasets. 2020. Available online: https://www.uvic.ca/engineering/ece/isot/datasets/ (accessed on 25 September 2020).
- Tavallaee, M.; Bagheri, E.; Lu, W.; Ghorbani, A.A. A detailed analysis of the KDD CUP 99 data set. In Proceedings of the 2009 IEEE Symposium on Computational Intelligence for Security and Defense Applications, Ottawa, ON, Canada, 8–10 July 2009; pp. 1–6. [Google Scholar]
- Choudhary, S.; Kesswani, N. Analysis of KDD-Cup9, NSL-KDD and UNSW-NB15 Datasets using Deep Learning in IoT. Procedia Comput. Sci. 2020, 167, 1561–1573. [Google Scholar] [CrossRef]
- KDD Cup 1999 Dataset. 1999. Available online: http://kdd.ics.uci.edu/databases/kddcup99/kddcup99.html (accessed on 30 November 2020).
- Kent, A.D. Cybersecurity Data Sources for Dynamic Network Research. In Dynamic Networks in Cybersecurity; Imperial College Press: London, UK, 2015. [Google Scholar]
- Kent 2016. 2016. Available online: https://csr.lanl.gov/data/cyber1/ (accessed on 30 November 2020).
- Song, J.; Takakura, H.; Okabe, Y.; Eto, M.; Inoue, D.; Nakao, K. Statistical Analysis of Honeypot Data and Building of Kyoto 2006+ Dataset for NIDS Evaluation. In Proceedings of the First Workshop on Building Analysis Datasets and Gathering Experience Returns for Security, Association for Computing Machinery, Vienna, Austria, 17–20 August 2011; pp. 29–36. [Google Scholar]
- Kyoto 2006+. 2016. Available online: https://www.takakura.com/Kyoto_data/ (accessed on 30 November 2020).
- Pang, R.; Allman, M.; Bennett, M.; Lee, J.; Paxson, V.; Tierney, B. A First Look at Modern Enterprise Traffic. In Proceedings of the 5th ACM SIGCOMM Conference on Internet Measurement. USENIX Association, Berkeley, CA, USA, 19–21 October 2005; p. 2. [Google Scholar]
- LBNL. 2004. Available online: http://icir.org/enterprise-tracing/Overview.html (accessed on 30 November 2020).
- Beer, F.; Hofer, T.; Karimi, D.; Bühler, U. A new Attack Composition for Network Security. In 10. DFN-Forum Kommunikationstechnologien; Gesellschaft für Informatik e.V.: Bonn, Germany, 2017; pp. 11–20. [Google Scholar]
- NDSec-1. 2016. Available online: https://www2.hs-fulda.de/NDSec/NDSec-1/ (accessed on 30 November 2020).
- Haider, W.; Hu, J.; Slay, J.; Turnbull, B.P.; Xie, Y. Generating realistic intrusion detection system dataset based on fuzzy qualitative modeling. J. Netw. Comput. Appl. 2017, 87, 185–192. [Google Scholar] [CrossRef]
- NSL-KDD Dataset. 2019. Available online: https://www.unb.ca/cic/datasets/nsl.html (accessed on 25 September 2020).
- Singh, R.; Kumar, H.; Singla, R.K. A Reference Dataset for Network Traffic Activity Based Intrusion Detection System. Int. J. Comput. Commun. Control. 2015, 10, 390–402. [Google Scholar] [CrossRef]
- Sharma, R.; Singla, R.K.; Guleria, A. A New Labeled Flow-based DNS Dataset for Anomaly Detection: PUF Dataset. Procedia Comput. Sci. 2018, 132, 1458–1466. [Google Scholar] [CrossRef]
- Wheelus, C.; Khoshgoftaar, T.M.; Zuech, R.; Najafabadi, M.M. A Session Based Approach for Aggregating Network Traffic Data–The SANTA Dataset. In Proceedings of the 2014 IEEE International Conference on Bioinformatics and Bioengineering, Boca Raton, FL, USA, 10–12 November 2014; pp. 369–378. [Google Scholar]
- Vasudevan, A.R.; Harshini, E.; Selvakumar, S. SSENet-2011: A Network Intrusion Detection System dataset and its comparison with KDD CUP 99 dataset. In Proceedings of the 2011 Second Asian Himalayas International Conference on Internet (AH-ICI), Kathmundu, Nepal, 4–6 November 2011; pp. 1–5. [Google Scholar]
- Bhattacharya, S.; Selvakumar, S. SSENet-2014 Dataset: A Dataset for Detection of Multiconnection Attacks. In Proceedings of the 2014 3rd International Conference on Eco-friendly Computing and Communication Systems, Mangalore, India, 18–21 December 2014; pp. 121–126. [Google Scholar]
- Hofstede, R.; Hendriks, L.; Sperotto, A.; Pras, A. SSH Compromise Detection using NetFlow/IPFIX. ACM Sigcomm Comput. Commun. Rev. 2014, 44, 20–26. [Google Scholar] [CrossRef]
- Hofstede, R. SSH Datasets. 2014. Available online: https://www.simpleweb.org/wiki/index.php/SSH_datasets (accessed on 30 October 2020).
- Viegas, E.K.; Santin, A.O.; Oliveira, L.S. Toward a reliable anomaly-based intrusion detection in real-world environments. Comput. Netw. 2017, 127, 200–216. [Google Scholar] [CrossRef]
- Laboratory, S.P. TRAbID-Datasets. 2019. Available online: https://secplab.ppgia.pucpr.br/?q=trabid (accessed on 30 October 2020).
- Bhuyan, M.H.; Bhattacharyya, D.; Kalita, J. Towards Generating Real-life Datasets for Network Intrusion Detection. Int. J. Netw. Secur. 2015, 17, 683–701. [Google Scholar]
- Sperotto, A.; Sadre, R.; van Vliet, D.F.; Pras, A. A Labeled Data Set For Flow-based Intrusion Detection. In Proceedings of the 9th IEEE International Workshop on IP Operations and Management, IPOM 2009, Venice, Italy, 29–30 October 2009; Springer: Berlin, Germany, 2009; Volume 5843, pp. 39–50. [Google Scholar]
- Laboratory, S.P. Twente-Datasets. 2012. Available online: https://www.simpleweb.org/wiki/index.php/Labeled_Dataset_for_Intrusion_Detection (accessed on 30 October 2020).
- Maciá-Fernández, G.; Camacho, J.; Magán-Carrión, R.; García-Teodoro, P.; Therón, R. UGR’16: A new dataset for the evaluation of cyclostationarity-based network IDSs. Comput. Secur. 2018, 73, 411–424. [Google Scholar] [CrossRef]
- UGR’16-Datasets. 2016. Available online: https://nesg.ugr.es/nesg-ugr16/ (accessed on 30 October 2020).
- Gringoli, F.; Salgarelli, L.; Dusi, M.; Cascarano, N.; Risso, F.; Claffy, K.C. GT: Picking up the Truth from the Ground for Internet Traffic. SIGCOMM Comput. Commun. Rev. 2009, 39, 12–18. [Google Scholar] [CrossRef]
- UNIBS-2009-Datasets. 2016. Available online: http://netweb.ing.unibs.it/~ntw/tools/traces/ (accessed on 30 October 2020).
- Turcotte, M.J.M.; Kent, A.D.; Hash, C. Unified Host and Network Data Set. In Data Science for Cyber-Security; World Scientific: Singapore, 2018; Chapter 1; pp. 1–22. [Google Scholar]
- Unified Host and Network Data Set. 2017. Available online: https://csr.lanl.gov/data/2017/ (accessed on 30 October 2020).
- Moustafa, N.; Slay, J. UNSW-NB15: A comprehensive data set for network intrusion detection systems (UNSW-NB15 network data set). In Proceedings of the 2015 Military Communications and Information Systems Conference (MilCIS), Canberra, Australia, 10–12 November 2015; pp. 1–6. [Google Scholar]
- UNSW-NB15 Dataset. 2015. Available online: https://www.unsw.adfa.edu.au/unsw-canberra-cyber/cybersecurity/ADFA-NB15-Datasets/ (accessed on 30 October 2020).

| Categorisation | Description |
|---|---|
| Attack Severity | Organised dependant on the severity of the attack or the threat level |
| Access Type | Organised dependant upon the type of access used by the attack |
| Attack Type | Organised dependant on the type overall type of attack |
| Attacker Position | Organised dependant on the attackers position relative to the victim |
| Attacker Implication | Organised dependant on the interaction between attacker and victim |
| Objective Oriented | Organised dependant on the overall goal of the specific attack |
| Network Layer Oriented | Organised dependant on the OSI layer where the attack resides |
| Use-Case Specific | Organised dependant on the specific use case |
| Categorisation | Approach | References | |
|---|---|---|---|
| Attack Severity | Six threat levels: Localised, Moderate, Substantial, Significant, Highly Significant and National Cyber Emergency | [15] | |
| Access Type | Physical, Cyber | [16] | |
| Attack Type | DoS, Probing, R2L, U2R | [19,20,21,22,23,24,25] | |
| DoS, MitM, Brute Force | [26,30] | ||
| DoS, Replay, Deception | [35,36] | ||
| Active Eavesdropping, Scanning, Probing | [44] | ||
| Physical, Network, Software, Encryption | [55] | ||
| Attacker Position | Outside, Inside | [13,56,57,58,59] | |
| Attacker Implication | Active, Passive | [13,20,56,60,61,62] | |
| Objective Oriented | Privacy | [16] | |
| Reconnaissance, Access, Malicious, Non-Malicious, Cyber Crime, Cyber Espionage, Cyber Terrorism, Cyber War | [20] | ||
| Disconnection and Goodput Reduction, Side-Channel Exploitation, Covert-Channel Exploitation | [44] | ||
| Hardware, Network, Human Factor | [57] | ||
| Interception, Interruption, Fabrication, Modification | [61] | ||
| Access Control, Authentication, Availability, Confidentiality, Integrity | [70] | ||
| Network Layer Oriented | OSI model, Layers 1–4 and 7 | [56,74] | |
| Use-Case Specific | CPS-NCS | Attacks on Physical Components, Attacks on Communication Network | [80] |
| CPS-Smart Grids | Power and Energy Layer, Computer/IT Layer, Communication Layer | [87] | |
| Wireless Ad-Hoc Networks | Attacks on MANET, Attacks on WSN | [20] | |
| IoT | Low-Level, Intermediate-Level, High-Level Security Issues | [100] | |
| IoT Stack Layers-Perception, Network, Application | [13,108] | ||
| SDN | SDN Architecture-Application Layer, Application-Control Interface, Control Layer, Control-Data Interface, Data Layer | [115] |
| Data Set | Information | Data | Traffic Type | Trace Contents | Data Composition | References | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Year | Public | Size | Duration | Labelled | Normal | Attack | IoT | 0-Day | Network | System | Nb Records | % Normal | % Attack | ||
| ADFA-LD | 2014 | ✔ | 2.3 MB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✔ | ✔ | ✔ | ❋ | ❋ | ❋ | [123,124,125,126] |
| ADFA-WD | 2014 | ✔ | 29.6 MB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✔ | ✔ | ✔ | 1,033,233 | 64% | 36% | [125,126] |
| ADFA-WD:SAA | 2014 | ✔ | 403 MB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✔ | ✔ | ✔ | ❋ | ❋ | ❋ | [125,126] |
| AWID | 2015 | ✔* | ❋ | 108 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | 210,900, 113 | 97% | 3% | [127,128] |
| Booters | 2013 | ✔ | 250 GB. | 2 d. | ✘ | ✘ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | 0% | 100% | [129] |
| Bot-IoT | 2018 | ✔? | 69.3 GB. | ❋ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✘ | 72,000,000 | ❋ | ❋ | [130,131] |
| Botnet | 2014 | ✔* | 13.8 GB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ≈915,944 | 69% | 31% | [132,133] |
| CAIDA | 2007 | ✔* | 21 GB. | 1 h. | ✘ | ✘ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | 0% | 100% | [134,135] |
| CIC-DDoS 2019 | 2019 | ✔* | ❋ | 2 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [135,136] |
| CIC DoS | 2017 | ✔* | 4.6 GB. | 24 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [137,138] |
| CICIDS 2017 | 2017 | ✔* | 51.1 GB. | 5 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [139,140] |
| CIDDS-001 | 2017 | ✔ | 380 MB. | 28 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [141,142] |
| CIDDS-002 | 2017 | ✔ | 200 MB. | 14 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [141,142,143] |
| CDX | 2009 | ✔ | 12 GB. | 4 d. | ✘ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [144,145] |
| CTU-13 | 2013 | ✔ | 697 GB. | 143 h. | ✔ | ✔ | ✔ | ✔ | ✘ | ✔ | ✘ | 20,643,076 | 98% | 2% | [146,147] |
| DARPA | 1999 | ✔ | ❋ | 25 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | ❋ | ❋ | ❋ | [148,149] |
| Gure KDD Cup | 2008 | ✔* | 13.6 GB. | 35 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | 2,759,494 | 41% | 59% | [150,151,152] |
| IRSC | 2015 | ✘ | ❋ | ❋ | ✔ | ✔ | ✔ | ✘ | ❋ | ✔ | ✘ | ❋ | ❋ | ❋ | [153] |
| ISCX 2012 | 2012 | ✔* | 84.4 GB. | 7 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [154,155] |
| ISOT | 2010 | ✔* | 420 GB. | 3 mnth. | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | 1,675,424 | 97% | 3% | [156,157] |
| KDD CUP 99 | 1998 | ✔ | 743 MB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | 4,898,431 | 20% | 80% | [151,158,159,160] |
| Kent 2016 | 2016 | ✔* | 12 GB. | 58 d. | ✘ | ✔ | ❋ | ✘ | ✘ | ✔ | ✔ | 1,648,275,307 | ❋ | ❋ | [161,162] |
| Kyoto 2006+ | 2006 to 2015 | ✔ | 19.2 GB. | 10 y. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [163,164] |
| LBNL | 2005 | ✔ | 11 GB. | 4 mnth. | ✘ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [165,166] |
| NDSec-1 | 2016 | ✔ | 869.2 GB. | ❋ | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [167,168] |
| NGIDS-DS | 2016 | ✔ | ❋ | 27 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | 90,054,160 | 99% | 1% | [169] |
| Year | Public | Size | Duration | Labelled | Normal | Attack | IoT | 0-Day | Network | System | Nb Records | % Normal | % Attack | ||
| NSL-KDD | 1998 | ✔ | ❋ | ❋ | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | 5,209,458 | 20% | 80% | [151,158,159,170] |
| PU-IDS | 2015 | ❋ | ❋ | ❋ | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | 198,904 | 47% | 53% | [171] |
| PUF | 2018 | ❋ | ❋ | 3 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | 298,463 | ❋ | ❋ | [172] |
| SANTA | 2014 | ✘ | ❋ | ❋ | ✔ | ✔ | ✔ | ✘ | ✔ | ✔ | ✔ | ❋ | ❋ | ❋ | [173] |
| SSENET-2011 | 2011 | ❋ | ❋ | 4 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [174] |
| SSENET-2014 | 2014 | ❋ | ❋ | 4 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | ❋ | ❋ | [175] |
| SSHCure | 2014 | ✔ | 2.5 GB. | 2 mnth. | ✔ | ✘ | ✔ | ✘ | ✘ | ✔ | ✔ | ❋ | 0% | 100% | [176,177] |
| TRAbID | 2017 | ✔ | 129 GB. | 8 h. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✔ | 469,442,290 | 93% | 7% | [178,179] |
| TUIDS | 2012 | ✔e | 65.2 GB. | 14 d. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | 833,006 | 52% | 48% | [180] |
| Twente | 2008 | ✔ | ❋ | 6 d. | ✔ | ✘ | ✔ | ✘ | ✘ | ✔ | ✘ | ❋ | 0% | 100% | [181,182] |
| UGR’16 | 2016 | ✔ | 236 GB. | 6 mnth. | ✔ | ✔ | ✔ | ✘ | ✘ | ✔ | ✘ | ≈16.9 B. | ❋ | ❋ | [183,184] |
| UNIBS-2009 | 2009 | ✔e | 27 GB. | 3 d. | ✘ | ✔ | ✘ | ✘ | ✘ | ✔ | ✘ | ❋ | 100% | 0% | [185,186] |
| Unified Host and Network | 2017 | ✔* | 150 GB. | 90 d. | ✘ | ✔ | ✘ | ✘ | ✔ | ✔ | ✔ | ❋ | 100% | 0% | [187,188] |
| UNSW-NB15 | 2015 | ✔ | 100 GB. | 31 h. | ✔ | ✔ | ✔ | ✘ | ✔ | ✔ | ✔ | 2,540,044 | 87% | 13% | [159,189,190] |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Staddon, E.; Loscri, V.; Mitton, N. Attack Categorisation for IoT Applications in Critical Infrastructures, a Survey. Appl. Sci. 2021, 11, 7228. https://doi.org/10.3390/app11167228
Staddon E, Loscri V, Mitton N. Attack Categorisation for IoT Applications in Critical Infrastructures, a Survey. Applied Sciences. 2021; 11(16):7228. https://doi.org/10.3390/app11167228
Chicago/Turabian StyleStaddon, Edward, Valeria Loscri, and Nathalie Mitton. 2021. "Attack Categorisation for IoT Applications in Critical Infrastructures, a Survey" Applied Sciences 11, no. 16: 7228. https://doi.org/10.3390/app11167228
APA StyleStaddon, E., Loscri, V., & Mitton, N. (2021). Attack Categorisation for IoT Applications in Critical Infrastructures, a Survey. Applied Sciences, 11(16), 7228. https://doi.org/10.3390/app11167228








