Blockchain-Based Multimedia Content Protection: Review and Open Challenges
Abstract
1. Introduction
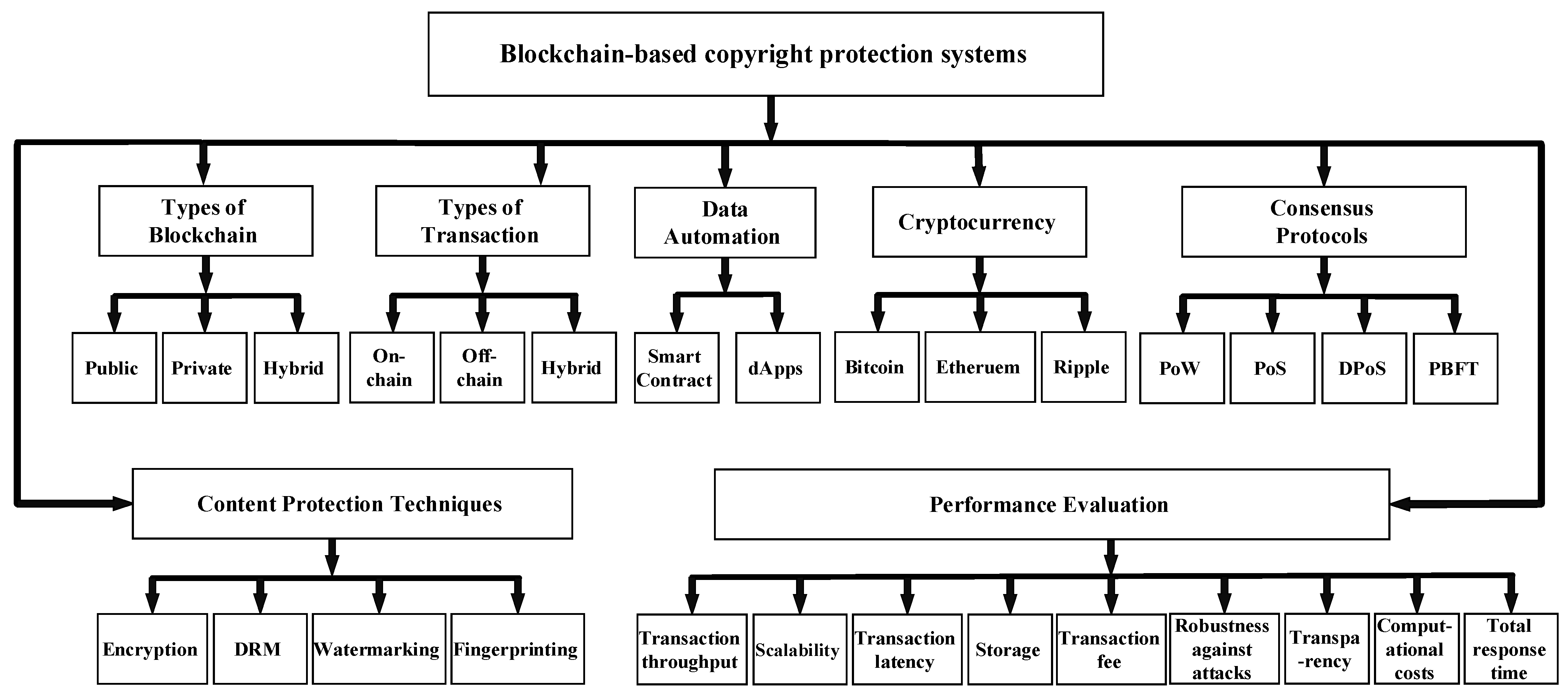
2. Taxonomy of Blockchain-Based Multimedia Content Protection Systems
2.1. Types of Blockchain
- Public (permissionless) blockchain: A decentralized blockchain in which any node can join the network with read and write access permissions. It establishes trust through a consensus mechanism that makes the transaction immutable, once it is stored on the network. Since all nodes need to participate in the consensus process, the transaction speed is anomalously slow. Examples of a public blockchain are Bitcoin and Ethereum.
- Private (permissioned) blockchain: A partially decentralized blockchain in which only permissioned nodes can participate in the consensus, accounting and building blocks. It is managed by a trusted party and the encrypted database is commonly shared among the permissioned nodes. An example of this type is MultiChain.
- Hybrid (consortium) blockchain: A type of blockchain that combines “low-trust" offered by public blockchains and the “single highly-trusted entity" model of private blockchains. It has a multi-party consensus mechanism in which all operations are verified by special pre-approved nodes. A few examples include Quorum, Hyperledger, and Corda.
2.2. Types of Transaction
- On-chain transactions: These are available on the distributed ledger and are visible to all participants on the network. Different details of this transaction are recorded on the block and distributed to the entire blockchain, thus making the transaction irreversible as it cannot be altered. For the transaction to be complete, there has to be an agreed number of confirmations by miners. Moreover, the completion depends on network congestion. Consequently, sometimes transactions are delayed in case of a large volume of transactions waiting to be confirmed.
- Off-chain transactions: These occur outside of a main blockchain and are not published on the network. The involved parties can choose to have an agreement outside of the blockchain. In addition, it may involve a guarantor, who is responsible for confirming the completion of the transaction and certifying that the agreement has been honored. Upon agreement by the involved entities outside the blockchain, the actual transaction is then executed on the blockchain. These transactions can be carried out using different methods, e.g., multi-signature technologies, credit-based solutions, among others. Off-chain transactions are executed instantly as compared to on-chain transactions.
- Hybrid transactions: These transactions combine certain aspects of both on-chain and off-chain transactions. The separation of operations into on- and off-chain is based on different criteria, such as cost, decentralization, storage, privacy, etc.
2.3. Data Automation
2.4. Cryptocurrency
- Bitcoin is the first P2P payment network of electronic cash based on the blockchain technology. The Bitcoin network adopts a hash-based proof-of-work (PoW) distributed consensus protocol. Bitcoin is pseudonymous, i.e., the funds are delivered to the Bitcoin addresses instead of the real-world identities. The average block creation time is 10 min, and the block size is limited to 1 MB [22], which constrains the network throughput. Moreover, the scalability is limited to 3–7 transactions/second [23]. Moreover, it is vulnerable to hacking attacks and theft, while being completely encrypted.
- Ethereum is an open-source, public, blockchain-based distributed computing platform that uses a proof-of-stake (PoS) consensus mechanism and allows programming of various types of smart contracts within the system. The transferable amount in Ethereum is ether. Any action in Ethereum requires gas, which is used as a fee instead of ether for ease of computations. The average block creation time is 17 s [24], and blocks are limited by a 6.7 million gas [25]. A simple Ethereum transaction can cost around 21,000 units of gas. However, a complicated smart contract can cost a lot more. The scalability of Ethereum is limited to 15–20 transactions/second [26]. Moreover, it is susceptible to security violations due to Solidity Language, causing compromise of stored data.
- Ripple is a for-profit technology platform that allows banks, payment providers, and digital asset exchanges to provide faster payment settlements and offers lower currency exchange costs. XRP is the cryptocurrency used by the Ripple payment network to make cross-border payments. Unlike blockchain mining, the Ripple network uses a unique distributed consensus protocol to validate transactions. This enables faster transactions without any centralized authority. The transactions in the Ripple network are confirmed instantly by the XRP gateways and take roughly 4 s. The Ripple network can process 1500 transactions/second [27]. Since Ripple is pre-mined, there exist little or no incentive for common nodes to work in the network, which subsequently leaves the corporations to provide the validator nodes.
2.5. Consensus Protocols
- PoW: The nodes (miners) involved in this process compete with each other to solve a complex mathematical puzzle. The first node to find a solution obtains the right to validate the block to create a new block that implements a transaction. Bitcoin and Ethereum 1.0 use the PoW [28]. However, PoW requires a lot of energy and computer power to reach a consensus, and therefore, it is a very expensive option.
- PoS: The miners in this process are required to prove the ownership of a certain amount of currency tokens to establish their stake. Hence, the more tokens a node has, the more likely it will validate the block, and thus, will determine the authenticity of the block. Dash and Neo use PoS [29]. Ethereum 2.0, an upgrade to the Ethereum blockchain, has switched to PoS [28] from PoW, in order to provide increased scalability and throughput. One of the major drawbacks of PoS is that it promotes “crypto-coin saving", rather than spending.
- Delegated proof-of-stake (dPoS): As a variation of the PoS, dPoS requires all token owners to select a group of delegates, who they trust to participate in the validation process. The nodes with the highest votes then authenticate the transactions. Lisk and BitShares use dPoS [30]. Though dPoS does not require much computing power, it is vulnerable to centralization as the number of witnesses is strictly limited.
- Practical Byzantine Fault Tolerance (PBFT): Byzantine fault tolerance (BFT) refers to reaching a consensus between two nodes communicating safely across a distributed network in the presence of malicious nodes. One of the examples of BFT, PBFT, is designed to be a high performance consensus algorithm that can rely on a set of trusted nodes in the network. PBFT can only tolerate faulty or malicious nodes until the number of such nodes is less than one-third of all the nodes. Since greater number of honest nodes will agree on a correct decision than a faulty or malicious nodes agreeing on an incorrect decision, false information will be rejected by the majority. This mechanism is currently being leveraged by Hyperledger Fabric and Zilliqa [31].
2.6. Multimedia Content Protection Techniques
2.6.1. Multimedia Encryption
- Confidentiality: It refers to limiting data access or disclosure to authorized users and preventing access or disclosure to unauthorized ones.
- Integrity: It refers to protecting data against modification, or alteration, whether by accident or deliberately.
- Authenticity: It refers to enabling the receiver of data to ascertain its origin.
2.6.2. Digital Rights Management (DRM)
- Unauthorized copying: It ensures that the digital asset is packaged in a secure manner so as to prevent unauthorized usage. This secure packaging is achieved by encryption.
- Secure distribution: It must securely distribute the digital asset to the authorized user.
- Conditional access: It must obtain the access conditions (licenses) specified by the owners of the protected content. The license consists of rights expression language, metadata or watermark, and a security mechanism to prevent users from circumventing DRM by modifying the access conditions.
- Tampering resistance: It must provide an effective tamper-resistant mechanism to process protected data and enforce content usage rights.
2.6.3. Digital Watermarking
- Imperceptibility: The perceptual similarity between the original and the watermarked versions of the digital content. The embedded watermark must not introduce distortion, which can cause quality degradation.
- Robustness: The ability to detect the watermark after common signal processing operations (such as cropping, compression or additive noise). A watermark must be robust enough to withstand all kinds of signal processing operations (at least below some distortion threshold). Depending on the robustness against attacks, digital watermarking can be categorized as robust, fragile and semi-fragile.
- Capacity: The number of bits a watermark encodes within a unit of time (or space in the case of still images).
- Security: The ability to resist intentional and/or malicious attacks. A watermarking algorithm must be secure in the sense that an attacker must not be able to detect the existence of embedded data or extract/remove it. Watermark information should only be accessible to the authorized parties.
2.6.4. Multimedia Fingerprinting
- Robustness: A fingerprint’s robustness against signal processing operations is determined by the adopted watermark embedding method. Thus, a robust watermarking algorithm must be adopted so that the fingerprinting scheme can trace an illegal re-distributor after the digital content has been manipulated by common signal processing attacks.
- Collusion resistance: While digital fingerprinting may be effective at identifying a single adversary, multiple malicious buyers may collaborate to launch powerful collusion attacks against the fingerprinting system. By comparing their different versions, the colluders can attempt to identify the locations containing the fingerprint signal, remove the information from these locations and thereby create a copy that cannot be traced back to any of them. Thus, a fingerprinting scheme must be designed to withstand such collusion attacks.
- Quality tolerance: Fingerprinted content should have good visual quality and perceptual similarity to the original content.
- Embedding capacity: The capacity determines the length of fingerprint allocated to each user. The fingerprint is a binary string that can be long. Therefore, a digital fingerprint system should have a large enough embedding capacity to accommodate a full fingerprint.
2.7. Performance Requirements
- Transaction throughput: Throughput can be defined as the number of transactions/ second in each block, whereas transaction throughput can be defined as the rate at which valid transactions are committed by the blockchain in a defined time period.
- Scalability: The size and frequency of the blocks along with the number of transactions that the system can process to cope with the increased workload.
- Transaction latency: The amount of time required to add a block of transactions in the blockchain. This includes the propagation time and any settling time due to the consensus mechanism in place.
- Storage: On-chain storage of users’ data (such as personal information, copyright information or keys) or off-chain mechanism (such as InterPlanetary File System (IPFS) or data lake) to store large amount of copyrighted data.
- Transaction fee: In Ethereum, an execution fee is used to compensate miners for the computational resources required to perform different smart contract functions (e.g., content registration or delivery). The gas price is measured in terms of ether. Hence, the total transaction fee is the gas consumed multiplied by the gas price. In Bitcoin, the transaction fee is the cost that a user incurs when he/she sends coins from one bitcoin wallet into another. This fee is based on the size (in bytes) of the transaction and the age of its inputs. The miners responsible for mining the block that includes the transaction are being paid with the transaction fee in BTC.
- Robustness of content protection schemes against different types of attacks: The copyright protection schemes (based on encryption, DRM, watermarking or fingerprinting) must be resistant against all possible threats, such as security, privacy, signal processing, tampering, communication and collusion attacks, among others. These threats are discussed in Section 2.6.
- Transparency of copyrighted multimedia content: In the copyright protection schemes based on watermarking/fingerprinting, the embedded watermark/fingerprint must be transparent and should not introduce distortion, which can cause quality degradation.
- Computational costs in generation of copyright content: These are on- or off-chain costs associated with the process of generating copyrighted content (encrypted with access control, watermarked or fingerprinted).
- Total response time: It includes the time taken by the content owner in registering the copyrighted content on the blockchain so as to make it available for the clients, and the time taken in delivering the content to the client upon final payment settlement.
3. State-of-The-Art of Blockchain-Based Content Protection Systems
Comparative Analysis
- Most of the selected schemes [36,37,39,42,45,46,49,51] use a permissioned (private) blockchain, which implies a control layer on top of the blockchain that is governed by a trusted authority, who is responsible for permitting actions to be performed by the allowed system entities. Several other schemes [41,43,48] use consortium blockchain as a distributed ledger to retain control and privacy, while cutting down costs and increasing transaction speeds.
- The majority of the schemes [36,37,38,40,42,46,47,48,49,51,52] utilize hybrid transactions, which imply on-chain recording of data in a private or publicly accessible blockchain service, such as the content’s metadata, copyright owners’ or users’ information, watermark or fingerprint of the user (in an encrypted form), DRM license and content obligation, among others, and off-chain mechanisms, such as generation and storage of copyrighted content, extraction of copyright information from the content or traceability protocol. The on-chain transactions are performed to achieve transparency, security, immutability and auditability, and are considered best for cryptocurrency transfers in a completely decentralized manner. The off-chain mechanisms allow the authorities to save on-chain costs as these do not have a transaction fee. In addition, these mechanisms are quite fast since these are not bound by the transactional speed limitations linked to on-chain transactions.
- In many schemes [36,37,40,41,42,43,49,50], multiple smart contracts are bundled together to create a blockchain-enabled dApp to automate the desired functionality between the copyright owner and the buyers. These contracts include a series of functions, such as data processing, value transfer, copyright protection, content distribution, and traceability. In other systems [44,45,46,48,51,53], a single smart contract is proposed to facilitate the purchase of the copyrighted content between the copyright owner and the clients (buyers).
- In the majority of the schemes [36,37,40,42,44,46,48,49,51,53], Ethereum, which is the second largest cryptocurrency platform by market capitalization behind Bitcoin, is used as a cryptocurrency for transactions. The Ethereum crypto token (Ether) transactions tend to be confirmed faster by the blockchain, and are much cheaper than most transactions on Bitcoin. Moreover, Ethereum not only allows Ether transfers between people, but can be used to create all types of other cryptocurrencies, such as in [41].
- Many schemes [38,39,40,41,42] use the most prominent consensus protocol, i.e., PoW, to confirm transactions and produce new blocks in the chain. PoW is the dominant choice in existing digital currencies due to its security features, which use cryptography that deters denial-of-service (DoS) and sybil attacks.
- The majority of the schemes guarantee content protection by using digital watermarking either as a standalone mechanism [44,45,46,47] or in combination with DRM [40,42,48,49] or encryption [37]. Only three schemes [50,51,52,53] used digital fingerprinting to provide copyright protection, while only two schemes, proposed in [39,41], used DRM techniques to ensure conditional access.
- From Table 2, we can make the following observations w.r.t. to the performance of the systems:
- –
- Since the majority of the schemes have utilized either Bitcoin or Ethereum for development or testing purposes, the average transaction throughput (3–7 tps for Bitcoin and 15–20 tps for Ethereum) and latency rates (10 min for Bitcoin and 17 s for Ethereum) have been considered. However, only a few schemes [37,39,41,42,44,46] consider the transaction fees per block per day.
- –
- Only a few schemes [41,42,45] address scalability by using the Schnorr’s multi-signature technology, which also improves the privacy of the system and prevents spam attacks to a higher degree. In [49], a quite small number of miners are pseudo-randomly selected to execute off-chain computationally intensive smart contracts.
- –
- The majority of the schemes use IPFS or data servers for storing and distributing the copyrighted content to the buyers upon a successful purchase.
- –
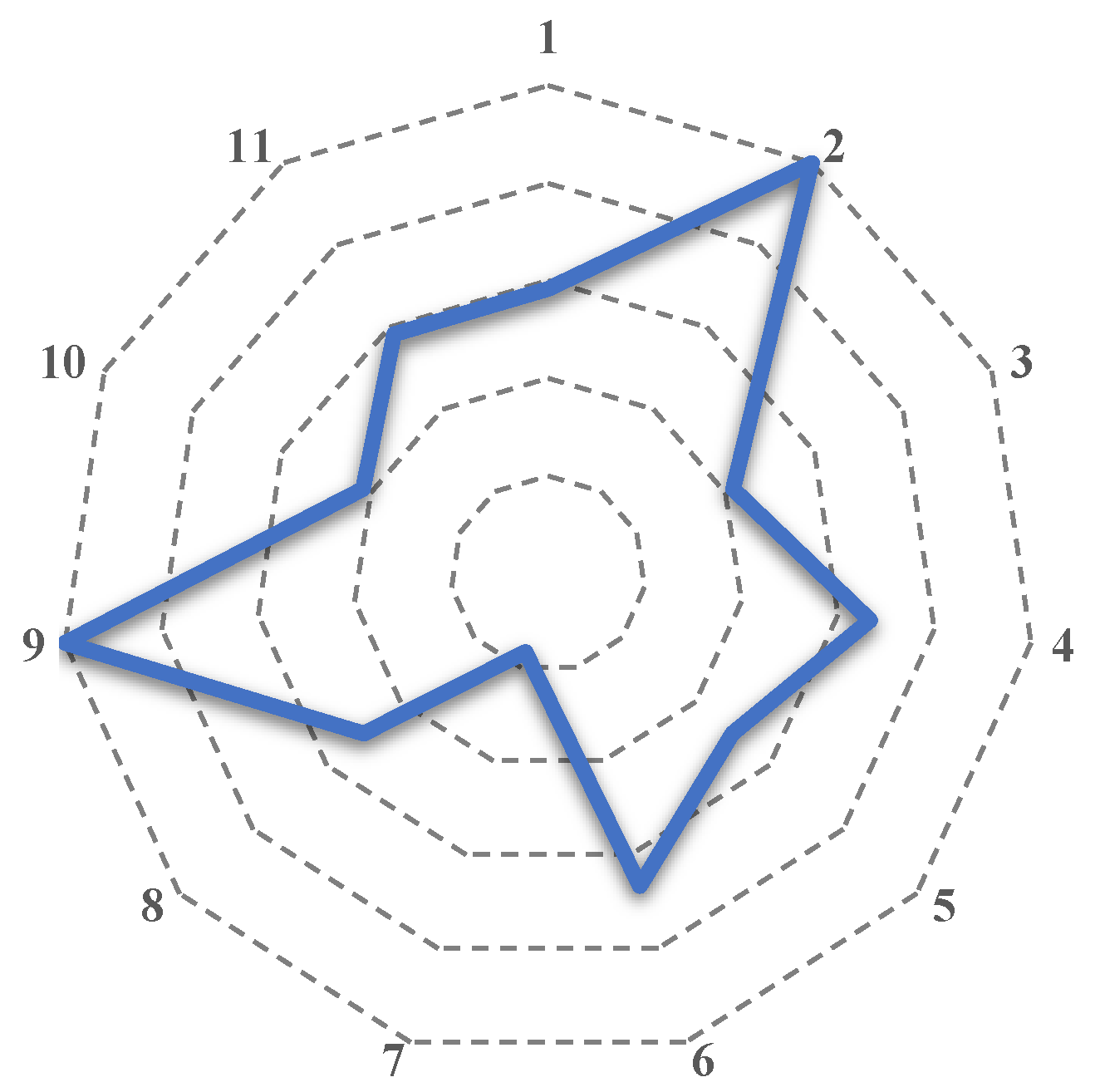
- All schemes are based on different content protection mechanisms and satisfy the basic security requirements described in Section 2.6. Figure 2 illustrates the 11 identified individual security properties (excluding the common security properties) of four multimedia content protection techniques (encryption, DRM, watermarking and fingerprinting), and the analyzed systems (18) that satisfy each of these objectives.It can be observed that the majority of the systems provide data integrity (12 systems) and protection against communication attacks (12 systems). In terms of tamperproofness, we can observe that many systems guarantee tampering resistance (8 systems). This is to be expected since this property is provided by the blockchain technology. It can be observed that fewer schemes address data confidentiality (7 systems), traceability (7 systems), authenticity (6 systems), and conditional access (6 systems). In terms of security against attacks, only a few schemes are robust against common signal processing (7 systems) and collusion/coalition (5 systems) attacks. Considering the quality tolerance objective, we observe that transparency of the copyrighted (watermarked/fingerprinted) content is evaluated by many fewer schemes (2 systems).
- –
4. Limitations, Open Challenges and Future Research Directions
4.1. Limitations and Research Challenges of Content Protection Techniques
- Encrypted content is only as secure as the key used for encrypting it. Thus, cryptographic keys must be carefully managed (e.g., transmission, storage or updating) to ensure data remains protected, yet accessible when needed among multiple users of a system.
- Encryption techniques cannot prevent a user from unauthorized usage and illegal distribution of the content upon decryption of the received content.
- Most of the research work involving DRM is non-interoperable, which does not constitute an efficient option for clients. For this reason, consumers may seek alternative options to obtain the content, such as P2P file-sharing applications. However, to make DRM systems interoperable, the content providers or vendors of multimedia players would need to know the sensitive information related to the DRM protection scheme, thus increasing the risk of leakage. In such a case, a single leakage (or “hack”) has the potential to compromise not only one of several distribution channels, but the distribution of all interoperably DRMed content.
- DRM systems may give rise to a number of legal issues if not used correctly, e.g., the use of monitoring tools, either intentionally or unintentionally, to report and collect data pertaining to their consumers’ habits and preferences (such as the type of content they enjoy, when they enjoy it and even where, by accessing users location details, among others). This may result in serious privacy implications, such as using these data for purposes unrelated to the platform or selling it to third parties.
- At the embedder’s end in a digital watermarking scheme, maintaining an appropriate balance between robustness, capacity and imperceptibility properties is a challenging task, since these properties contradict one another, i.e., if one is increased, the other decreases.
- Security and complexity features have been given less priority in the development of the watermarking schemes. The more complex the watermarking scheme is, the higher the costs associated with the embedding and detection processes. The costs associated with the watermark embedding and detection should be minimal in order to meet the real-time requirements.
- In digital fingerprinting schemes based on collusion-resistant codes, there exists a trade-off among the size of a user base N, the collusion resilience , and the codeword length m. With an increase in N or , the length of m increases and vice versa. This trade-off may make the traceable code impractical because many applications require a large user base and collusion resistance. However, these requirements will result in long traceable codes.
- Most of the research work involving anonymous fingerprinting protocols assume the presence of a trusted third party that is responsible for generating the fingerprint and tracing the copyright violators. This trust implies a belief by the user that the trusted entity will behave in an expected manner in order to ensure security and anonymity. In a few other schemes that have avoided the use of such a party, the computational and communicational overheads are quite high due to the use of at least one of the following highly demanding technologies: homomorphic encryption, bit-commitment or secure multi-party computation.
- All types of attacks—internal and external—should be taken into consideration to evaluate the security and robustness of novel or existing watermarking and fingerprinting schemes.
4.2. Limitations and Research Challenges of the Blockchain Technology
- The blockchain suffers from a scalability problem due to the limited block size, e.g., Bitcoin can reach 7 transactions per second due to the Bitcoin protocol restricting block sizes to 1 MB. A possible solution to this problem is to increase the block size, but it creates a strain on the security due to the fact that an increase in the probability of orphaned blocks would distinctly affect the bandwidth and validation costs. The higher the block size limit, the larger the transaction load, blockchain congestion, and transaction delays. Consequently, a decrease in the transaction fee would result in less security. Thus, a trade-off between security, scalability and decentralization is a challenge in the development of a blockchain.
- Permissionless blockchains establish that the recorded data is accessible, and thus, enable its public access to all participants. However, this may compromise data privacy. Furthermore, in the case that a sensitive or confidential data is uploaded mistakenly to the public blockchain, there is no way to rectify the damage.
- The codes of smart contracts are susceptible to the inclusion of bugs due to human error or incomplete information. Moreover, the self-executing nature of smart contracts implies reduced flexibility to give effect to the actual intentions of the parties.
- A programming language to implement smart contracts is an ongoing research field. Currently, the most used object-oriented and high-level language to implement complex smart contracts in Ethereum is Solidity (Turing-complete language), which is still evolving and has a number of limitations, such as lack of general purpose libraries, type checking and multi-threading support, among others. Other popular programming languages (Python, C++, Java) are also used to code smart contracts. However, making programs readable (human readable code and human readable execution) in each form remains a challenge. In the case of Bitcoin, the scripting language to write a simple code is not Turing complete and does not support all possible programming structures, specifically loops.
- Blockchain could suffer from 51% attacks, where some nodes may attain the majority in a network and abuse it, e.g., they may reverse transactions to perform double spending and prevent other miners from confirming blocks.
- User’s privacy can be breached within the blockchain, e.g., user’s real IP address can be traced, transaction history can be linked to reveal his/her true identity or linkability through his/her connected set of nodes.
- Blockchain lacks interoperability due to the lack of universal standards. Existing blockchain networks have their own parameters, such as consensus models, transaction schemes, cryptocurrency, and smart contract functionality. Moreover, the uncertainty and speculative nature of cryptocurrency still prevent its widespread adoption.
4.3. Future Research Directions
4.3.1. Designing an Efficient Blockchain-Based Framework to Satisfy the System Requirements of Copyright Protection Applications
- Scalability: Off-chain mechanisms such as Lightning Network (LN) for Bitcoin [54] and Plasma for Ethereum [55], or on-chain schemes like SegWit for Bitcoin [56] and Sharding [57] for Ethereum, can solve the blockchain’s scalability problem. However, for LN, the main challenges are security and transparency per-transaction basis and centralization (presence of hubs), while in Plasma, long waiting periods (7–14 days) for withdrawal of funds and security risks are the open challenges. Similarly, the main challenges of SegWit are complexity, increased storage space and network bandwidth, while communication and security are the main issues in Sharding. The studies on addressing security, complexity, decentralization, performance, and communication strategies are expected to achieve significant research interest in the future.
- Validation of a framework: Many of the blockchain-based copyright protection applications solely focus on the technology’s benefits, while leaving aside the details of their implementation. Therefore, it is important to design a practical blockchain-based framework that should address both technical and implementation details, e.g., assessing the advantages and disadvantages of permissioned and permissionless systems before opting for one of these solutions, the selection of the appropriate consensus mechanism depending on the requirements (e.g., transaction throughput, latency, minimum transaction fee, centralization/decentralization and security, among others), and the evaluation of the performance by implementing the proof-of-concepts to calculate computational overheads and the total response time.
- Standardization: The recognized technological standards establish specifications and procedures that are beneficial in terms of ensuring efficiency, reliability, and enhanced security. Through our fine-grained analysis, it can be deduced that there is a need of a universal standard that the multimedia content providers, producers and involved companies could follow to share new blockchain-based copyright protection solutions as well as to integrate these with the existing systems. Similarly, this standard should allow automatic conversion between different cryptocurrencies to enhance user experience.
- Privacy-aware design: Future research studies need to investigate possible privacy-aware solutions that could protect the privacy of the entities (content owner, buyer, and so on) involved in the transactions of the blockchain-based content protection applications. The privacy and security requirements should be defined at the initial stage of these schemes due to the fact that the data (e.g., information related to the content owner, the public keys of the participants, pseudonyms and copyright information, among others) is visible to everyone on the network.
- Unlinkability: The privacy leakage issue in the blockchain needs to be addressed in order to prevent linkability and possible identification. Future research works could study the feasibility of incorporating anonymity mechanisms, such as CoinShuffle [58] (shuffle addresses), Zerocash [59] (hides the payment’s origin, destination, and transferred amount) or differential privacy into the applications to meet the anonymity requirements.
- Smart contract security: All possible security and privacy attacks (e.g., eavesdropping, DDoS attack or impersonation) on the smart contract should be analyzed through formal security analysis. Moreover, smart contract transactions must be designed to be technically reversible in order to prove their long-term effectiveness. Furthermore, in order to modify or reverse a smart contract, the triggering event for the modification and its termination/extension should be anticipated by the code. Therefore, the problem of addressing security and privacy attacks on a smart contract needs further investigation.
- Dispute resolution: The immutability property of blockchain can act as a double-edged sword, since it removes the possibility of modifying/updating the content or the copyright information stored on it. Moreover, in the existence of immutability, the problem of resolving disputes over the copyright can be an interesting research topic.
4.3.2. Designing Multimedia Content Protection Systems to Support the Blockchain Technology
- Design improvements: The fine-grained analysis of the evaluated state-of-the-art systems sheds light on the need to improve traditional content protection mechanisms (encryption, DRM, watermarking/fingerprinting) so as to enable amicable integration with the blockchain technology. For example, key management, concurrent key acquisition and protection of keys can be explored in future studies for implementing blockchain-based multimedia encryption systems. Similarly, transfer of access rights to the consumers without a trusted third party, smooth execution of the transaction between the copyright provider and the client, and privacy-aware fine-grained usage control in blockchain-based DRM systems need further investigations. Likewise, in blockchain-based watermarking and fingerprinting schemes, low embedding and computational complexity, high robustness against possible security attacks, and acceptable transparency are a few mentionable open research challenges that the future research should tackle to enable widespread use of the blockchain-based copyright protection applications.
- Trustless systems: Fully decentralized content protection mechanisms had existed before the advent of blockchain. A key advantage that blockchain offers in addition to decentralization is trustlesness. The analyzed blockchain-based content protection systems are based on hybrid trust models that include presence of trusted third party or trusted users. Thus, there is a need to exploit the blockchain technology to its full potential and build truly trustless copyright protection systems.
- Security issues: The integration of the blockchain technology with an access control mechanism for off-chain sources needs to be investigated to ensure that only authorized parties can access the sensitive information. In addition, there is a need to address how to make the off-chain sources fault tolerant and prevent them becoming bottlenecks or single points of failure.
- Promoting adoption of blockchain in copyright applications: Most studies have yet to address the costs and limitations in deploying the content protection mechanisms on blockchain at the commercial level, and it would take considerable time to evolve, and require further technological advancements and security guarantees to be accepted by all the involved parties (such as copyright owners, multimedia producers, buyers, and others).
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Valley, S. Netflix. 2007. Available online: http://www.netflix.com/ (accessed on 21 December 2020).
- Cohen, B. BitTorrent. 2005. Available online: https://www.utorrent.com/ (accessed on 21 December 2020).
- SANDVINE. 2019 Global Internet Phenomena Report. 2019. Available online: https://www.sandvine.com/global-internet-phenomena-report-2019 (accessed on 21 December 2020).
- Amazon.com, Inc. Amazon Prime Video. 2006. Available online: https://www.primevideo.com/ (accessed on 21 December 2020).
- Van Dijk, W. Streamit. 2003. Available online: https://www.streamit.eu/audio-distribution-platform/ (accessed on 21 December 2020).
- Hamidouche, W.; Farajallah, M.; Sidaty, N.; Assad, S.E.; Deforges, O. Real-time selective video encryption based on the chaos system in scalable HEVC extension. Signal Process. Image Commun. 2017, 58, 73–86. [Google Scholar] [CrossRef]
- Chen, Y.Y.; Jan, J.K.; Chi, Y.Y.; Tsai, M.L. A Feasible DRM Mechanism for BT-Like P2P System. In Proceedings of the International Symposium on Information Engineering and Electronic Commerce, Ternopil, Ukraine, 16–17 May 2009; pp. 323–327. [Google Scholar]
- Pizzolante, R.; Castiglione, A.; Carpentieri, B.; Santis, A.D.; Castiglione, A. Reversible Copyright Protection for DNA Microarray Images. In Proceedings of the 10th International Conference on P2P, Parallel, Grid, Cloud and Internet Computing (3PGCIC), Krakow, Poland, 4–6 November 2015; pp. 707–712. [Google Scholar] [CrossRef]
- Qiu, Y.; Gu, H.; Sun, J. Reversible watermarking algorithm of vector maps based on ECC. Multimed. Tools Appl. 2018, 77, 23651–23672. [Google Scholar] [CrossRef]
- Qureshi, A.; Megías, D.; Rifà-Pous, H. Secure and Anonymous Multimedia Content Distribution in Peer-to-Peer Networks. In Proceedings of the 6th International Conference on Advances in Multimedia, Nice, France, 23–27 February 2014; pp. 91–96. [Google Scholar]
- Megías, D. Improved Privacy-Preserving P2P Multimedia Distribution Based on Recombined Fingerprints. IEEE Trans. Dependable Secur. Comput. 2014, 12, 179–189. [Google Scholar] [CrossRef]
- Qureshi, A.; Megías, D.; Rifà-Pous, H. PSUM: Peer-to-Peer Multimedia Content Distribution using Collusion-Resistant Fingerprinting. J. Netw. Comput. Appl. 2016, 66, 180–197. [Google Scholar] [CrossRef]
- Megías, D.; Qureshi, A. Collusion-resistant and privacy-preserving P2P multimedia distribution based on recombined fingerprinting. Expert Syst. Appl. 2017, 71, 147–172. [Google Scholar] [CrossRef]
- Kuribayashi, M.; Funabiki, N. Decentralized tracing protocol for fingerprinting system. APSIPA Trans. Signal Inf. Process. 2019, 8, 1–8. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-To-Peer Electronic Cash System. 2008. Available online: http://www.bitcoin.org/bitcoin.pdf (accessed on 21 December 2020).
- Michalko, M.; Kwan, W. DECENT, 2015. Available online: https://decent.ch/ (accessed on 21 December 2020).
- Spotify USA, Inc. Mediachain, 2016. Available online: http://www.mediachain.io/ (accessed on 21 December 2020).
- Shrestha, B.; Halgamuge, M.N.; Treiblmaier, H. Using Blockchain for Online Multimedia Management: Characteristics of Existing Platforms. In Blockchain and Distributed Ledger Technology Use Cases: Applications and Lessons Learned; Springer: Berlin/Heidelberg, Germany, 2020; pp. 289–303. [Google Scholar] [CrossRef]
- Bambrough, B. Ripple’s XRP Has More Than Doubled In Price This Week, Far Outpacing Bitcoin and Ethereum—Here’s Why. 2020. Available online: https://www.forbes.com/sites/billybambrough/2020/11/24/ripples-xrp-has-more-than-doubled-in-price-this-week-far-outpacing-bitcoin-and-ethereum-heres-why/?sh=71901a8512e5 (accessed on 21 December 2020).
- Statista. Distribution of Leading Cryptocurrencies from 2015 to 2020, by Market Capitalization. 2020. Available online: https://www-statista-com.biblioteca-uoc.idm.oclc.org/statistics/730782/cryptocurrencies-market-capitalization/ (accessed on 21 December 2020).
- Machine, P.W.T. What Are the Most Traded Cryptocurrencies? 2020. Available online: https://www.plus500.com/Trading/CryptoCurrencies/What-are-the-Most-Traded-Cryptocurrencies~2 (accessed on 21 December 2020).
- Kawase, Y.; Kasahara, S. Transaction-Confirmation Time for Bitcoin: A Queueing Analytical Approach to Blockchain Mechanism. In Queueing Theory and Network Applications; Springer: Berlin/Heidelberg, Germany, 2017; pp. 75–88. [Google Scholar]
- Shahriar Hazari, S.; Mahmoud, Q. Improving Transaction Speed and Scalability of Blockchain Systems via Parallel Proof of Work. Future Internet 2020, 12, 125. [Google Scholar] [CrossRef]
- Siriwardena, P. The Mystery Behind Block Time. 2017. Available online: https://medium.facilelogin.com/the-mystery-behind-block-time-63351e35603a (accessed on 21 December 2020).
- Mitra, R. Bitcoin VS Ethereum: [The Ultimate Step-by-Step Comparison Guide]. 2020. Available online: https://blockgeeks.com/guides/bitcoin-vs-ethereum-ultimate-comparison-guide/ (accessed on 21 December 2020).
- Terry, L. What Should We Expect From The Upcoming Release of Ethereum 2.0? 2020. Available online: https://hackernoon.com/what-should-we-expect-from-the-upcoming-release-of-ethereum-20-gc5m38hs (accessed on 21 December 2020).
- Prut, A. Ripple (XRP)—Quick Introduction. 2019. Available online: https://medium.com/the-capital/ripple-xrp-quick-introduction-60b682375609 (accessed on 21 December 2020).
- Won, D. Ethereum Proof of Stake Date: Date + What You Need to Know. 2020. Available online: https://www.exodus.io/blog/ethereum-proof-of-stake-date (accessed on 21 December 2020).
- Won, D. Best Proof of Stake Coins 2020 for Easy Passive Income. 2020. Available online: https://www.exodus.io/blog/best-proof-of-stake-coins (accessed on 21 December 2020).
- Staff, K. List Of DPOS Coins | DPOS Cryptocurrencies. 2018. Available online: https://kryptomoney.com/dpos-coins (accessed on 21 December 2020).
- Fan, C.; Ghaemi, S.; Khazaei, H.; Musilek, P. Performance Evaluation of Blockchain Systems: A Systematic Survey. IEEE Access 2020, 8, 126927–126950. [Google Scholar] [CrossRef]
- Arnold, M.; Schmucker, M.; Wolthusen, S.D. Techniques and Applications of Digital Watermarking and Content Protection, 2nd ed.; Artech House Publishers, Inc.: Norwood, MA, USA, 2003. [Google Scholar]
- Cox, I.; Miller, M.; Bloom, J.; Fridrich, J.; Kalker, T. Digital Watermarking and Steganography, 2nd ed.; Morgan Kaufmann Publishers Inc.: San Francisco, CA, USA, 2007. [Google Scholar]
- Katzenbeisser, S.; Petitcolas, F.A. Information Hiding Techniques for Steganography and Digital Watermarking, 1st ed.; Artech House, Inc.: Norwood, MA, USA, 2000. [Google Scholar]
- Qureshi, A.; Megías, D.; Rifà-Pous, H. Framework for Preserving Security and Privacy in Peer-to-Peer Content Distribution Systems. Expert Syst. Appl. 2015, 42, 1391–1408. [Google Scholar] [CrossRef]
- Vishwa, A.; Hussain, F.K. A Blockchain based approach for multimedia privacy protection and provenance. In Proceedings of the IEEE Symposium Series on Computational Intelligence, Bangalore, India, 18–21 November 2018; pp. 1941–1945. [Google Scholar] [CrossRef]
- Peng, W.; Yi, L.; Fang, L.; XinHua, D.; Ping, C. Secure and Traceable Copyright Management System Based on Blockchain. In Proceedings of the IEEE 5th International Conference on Computer and Communications, Chengdu, China, 6–9 December 2019; pp. 1243–1247. [Google Scholar] [CrossRef]
- Chi, J.; Lee, J.; Kim, N.; Choi, J.; Park, S. Secure and reliable blockchain-based eBook transaction system for self-published eBook trading. PLoS ONE 2020, 15, e0228418. [Google Scholar] [CrossRef] [PubMed]
- Kishigami, J.; Fujimura, S.; Watanabe, H.; Nakadaira, A.; Akutsu, A. The Blockchain-Based Digital Content Distribution System. In Proceedings of the IEEE 5th International Conference on Big Data and Cloud Computing, Dalian, China, 26–28 August 2015; pp. 187–190. [Google Scholar] [CrossRef]
- Zhao, S.; O’Mahony, D. BMCProtector: A Blockchain and Smart Contract Based Application for Music Copyright Protection. In Proceedings of the International Conference on Blockchain Technology and Application, Xi’an, China, 10–12 December 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Ma, Z.; Huang, W.; Gao, H. Secure DRM Scheme Based on Blockchain with High Credibility. Chin. J. Electron. 2018, 27, 1025–1036. [Google Scholar] [CrossRef]
- Ma, Z.; Jiang, M.; Gao, H.; Wang, Z. Blockchain for digital rights management. Future Gener. Comput. Syst. 2018, 89, 746–764. [Google Scholar] [CrossRef]
- Lu, Z.; Shi, Y.; Tao, R.; Zhang, Z. Blockchain for Digital Rights Management of Design Works. In Proceedings of the IEEE 10th International Conference on Software Engineering and Service Science, Beijing, China, 18–20 October 2019; pp. 596–603. [Google Scholar] [CrossRef]
- Bhowmik, D.; Feng, T. The Multimedia Blockchain: A distributed and tamper-proof media transaction framework. In Proceedings of the 22nd International Conference on Digital Signal Processing (DSP), London, UK, 23–25 August 2017; pp. 1–5. [Google Scholar] [CrossRef]
- Mangipudi, E.V.; Rao, K.; Clark, J.; Kate, A. Towards Automatically Penalizing Multimedia Breaches (Extended Abstract). In Proceedings of the IEEE European Symposium on Security and Privacy Workshops (EuroS PW), Stockholm, Sweden, 17–19 June 2019; pp. 340–346. [Google Scholar] [CrossRef]
- Zhao, H.; Liu, Y.; Wang, Y.; Wang, X.; Li, J. A Blockchain-Based Data Hiding Method for Data Protection in Digital Video. In Smart Blockchain; Springer International Publishing: Berlin/Heidelberg, Germany, 2018; pp. 99–110. [Google Scholar] [CrossRef]
- Meng, Z.; Morizumi, T.; Miyata, S.; Kinoshita, H. Design Scheme of Copyright Management System Based on Digital Watermarking and Blockchain. In Proceedings of the IEEE 42nd Annual Computer Software and Applications Conference, Tokyo, Japan, 23–27 July 2018; Volume 2, pp. 359–364. [Google Scholar] [CrossRef]
- Fei, X. BDRM: A Blockchain-based Digital Rights Management Platform with Fine-grained Usage Control. Int. J. Sci. 2019, 6, 54–63. [Google Scholar]
- Zhao, B.; Fang, L.; Zhang, H.; Ge, C.; Meng, W.; Liu, L.; Su, C. Y-DWMS—A digital watermark management system based on smart contracts. Sensors 2019, 19, 3091. [Google Scholar] [CrossRef] [PubMed]
- Wu, Z.; Zheng, H.; Zhang, L.; Li, X. Privacy-friendly Blockchain Based Data Trading and Tracking. In Proceedings of the 5th International Conference on Big Data Computing and Communications, QingDao, China, 9–11 August 2019; pp. 240–244. [Google Scholar] [CrossRef]
- Qureshi, A.; Megías, D. Blockchain-based P2P multimedia content distribution using collusion-resistant fingerprinting. In Proceedings of the 11th Asia-Pacific Signal and Information Processing Association (APSIPA) Annual Summit and Conference, Lanzhou, China, 18–21 November 2019; pp. 1606–1615. [Google Scholar] [CrossRef]
- Li, R. Fingerprint-related chaotic image encryption scheme based on blockchain framework. Multimed. Tools Appl. 2020, 1–21. [Google Scholar] [CrossRef]
- Zhao, J.; Zong, T.; Xiang, Y.; Gao, L.; Beliakov, G. Robust Blockchain-Based Cross-Platform Audio Copyright Protection System Using Content-Based Fingerprint. In Web Information Systems Engineering; Springer: Berlin/Heidelberg, Germany, 2020; pp. 201–212. [Google Scholar] [CrossRef]
- Poon, J.; Dryja, T. The bitcoin lightning network: Scalable off-chain instant payments. Draft Version 0.5 2016, 9, 14. [Google Scholar]
- Poon, J.; Lee, J.H. Plasma: Scalable autonomous smart contracts. Work. Draft 2017, 9, 1–14. [Google Scholar]
- Xie, J.; Tang, H.; Huang, T.; Yu, F.R.; Xie, R.; Liu, J.; Liu, Y. A Survey of Blockchain Technology Applied to Smart Cities: Research Issues and Challenges. IEEE Commun. Surv. Tutor. 2019, 21, 2794–2830. [Google Scholar] [CrossRef]
- Kokoris-Kogias, E.; Jovanovic, P.; Gasser, L.; Gailly, N.; Syta, E.; Ford, B. OmniLedger: A Secure, Scale-Out, Decentralized Ledger via Sharding. In Proceedings of the IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 20–24 May 2018; pp. 583–598. [Google Scholar] [CrossRef]
- Ruffing, T.; Moreno-Sanchez, P.; Kate, A. CoinShuffle: Practical Decentralized Coin Mixing for Bitcoin. In Computer Security—ESORICS 2014; Kutylowski, M., Vaidya, J., Eds.; Springer International Publishing: Berlin/Heidelberg, Germany, 2014; pp. 345–364. [Google Scholar] [CrossRef]
- Sasson, E.B.; Chiesa, A.; Garman, C.; Green, M.; Miers, I.; Tromer, E.; Virza, M. Zerocash: Decentralized Anonymous Payments from Bitcoin. In Proceedings of the IEEE Symposium on Security and Privacy, San Jose, CA, USA, 18–21 May 2014; pp. 459–474. [Google Scholar] [CrossRef]
| References | Types of Content | Types of Blockchain | Types of Transaction | Data Automation | Crypto- currency | Consensus Protocols | Content Protection Techniques |
|---|---|---|---|---|---|---|---|
| Kishigami et al. (2015) [39] | HD video | Permissioned | On-chain | – | Bitcoin | PoW | DRM |
| Bhowmik & Feng (2017) [44] | Image | – | On-chain | Smart contract | Ethereum | – | Watermarking |
| Vishwa & Hussain (2018) [36] | – | Permissioned | Hybrid | dApp | Ethereum | – | Encryption |
| Zhao & Mahony (2018) [40] | Audio | Permissionless | Hybrid | dApp | Ethereum | PoW | Watermarking- based DRM |
| Ma et al. (2018) [41] | Video | Consortium | On-chain | dApp | Ethereum Token | PoW/PoS/ PBFT | DRM |
| Ma et al. (2018) [42] | Video | Permissioned | Hybrid | dApp | Ethereum | PoW/PoS/ PBFT | Watermarking- based DRM |
| Zhao et al. (2018) [46] | Video | Permissioned | Hybrid | Smart contract | Bitcoin | – | Watermarking |
| Meng et al. (2018) [47] | Image | Permissionless | Hybrid | – | – | – | Watermarking |
| Peng et al. (2019) [37] | Image | Permissioned | Hybrid | dApp | Ethereum | – | Encryption+ Watermarking |
| Lu et al. (2019) [43] | Image | Consortium | On-chain | dApp | – | – | DRM |
| Mangipudi et al. (2019) [45] | Document | – | Hybrid | Smart contract | Bitcoin | – | Watermarking |
| Fei (2019) [48] | – | Consortium | Hybrid | Smart contract | Ethereum | Proof-of- Authority | Watermarking- based DRM |
| Zhao et al. (2019) [49] | – | Permissioned | On-chain | dApp | Ethereum | PBFT | Watermarking- based DRM |
| Wu et al. (2019) [50] | Image | – | Hybrid | dApp | – | – | Fingerprinting |
| Qureshi & Megías (2019) [51] | Image, Audio, Video | Permissioned | Hybrid | Smart contract | Ethereum | – | Fingerprinting |
| Chi et al. (2020) [38] | Document | Self- developed | Hybrid | – | Customized coin | PoW | ECC- based encryption |
| Li (2020) [52] | Image | – | On-chain | – | – | – | Encryption+ Fingerprinting |
| Zhao (2020) [53] | Audio | Permissionless | On-chain | Smart contract | – | – | Content- based Fingerprinting |
| References | Performance Evaluation | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Transaction Throughput | Scalability | Transaction Latency | Storage | Transaction Fee | Robustness against Attacks | Transparency | Computational Costs | Total Response Time | ||||
| Signal Processing | Communication | Collusion | Security | |||||||||
| Kishigami et al. (2015) [39] | 3–7 tps | – | 10 min | On-chain | BTC | – | – | – | Tampering resistance + Conditional access | – | – | – |
| Bhowmik & Feng (2017) [44] | 15–20 tps | – | 17 s | On-chain | Ether | – | – | – | Tampering resistance | – | – | – |
| Vishwa & Hussain (2018) [36] | 15–20 tps | – | 17 s | On-chain+ Data lake | – | – | – | – | Data confidentiality | – | – | – |
| Zhao & Mahony (2018) [40] | 123k tps per day | – | 17 s | On-chain+ IPFS | – | Yes | Yes | – | Conditional access + Data confidentiality | – | – | – |
| Ma et al. (2018) [41] | – (HyperLedger fabric) 15–20 tps (Ethereum) | Yes (multi-sig) | – (HyperLedger fabric) 17 s (Ethereum) | On-chain | Ether | – | Yes | – | Tampering resistance + Conditional access | – | 1074 ms | 987 ms |
| Ma et al. (2018) [42] | 15–20 tps | Yes (multi-sig) | 17 s | On-chain+ IPFS | Ether | Yes | Yes | – | Tampering resistance + Conditional access + Traceability | dB | 12,000 ms | 45,000 ms |
| Zhao et al. (2018) [46] | 3–7 tps | – | 10 min | On-chain + Server | BTC | Yes | Yes | – | Data integrity Tampering resistance | db | – | – |
| Meng et al. (2018) [47] | – | – | – | On-chain+ IPFS | – | – | – | – | Data integrity Tampering resistance | – | – | – |
| Peng et al. (2019) [37] | 15–20 tps | – | 17 s | On-chain + IPFS | Ether | – | Yes | – | Data integrity Access control | – | – | – |
| Lu et al. (2019) [43] | – | – | – | On-chain + Personal equipment | – | – | Yes | – | Data confidentiality Proof-of-delivery Traceability | – | – | – |
| Mangipudi et al. (2019) [45] | 3–7 tps | Yes (multi-sig) | 10 min | On-chain + Server | – | Yes | Yes | Yes | Data integrity Fairness | – | – | – |
| Fei (2019) [48] | – | – | – | On-chain + IPFS | – | – | – | Yes | Conditional access Fine-grained usage control | – | – | ms |
| Zhao et al. (2019) [49] | – | Computationally intensive contract | – | On-chain | – | – | Yes | Yes | Traceability Rewards & Punishments Screen Record Prevention | – | – | – |
| Wu et al. (2019) [50] | – | – | – | On-chain + Server | – | Yes | Yes | – | Tamper proofness Traceability Frameproofness Non repudiation | – | – | – |
| Qureshi & Megías (2019) [51] | 15–20 tps | – | 17 s | On-chain+ IPFS | – | Yes | Yes | Yes | Proof-of-delivery Traceability Frameproofness Unlinkability | – | – | – |
| Chi et al. (2020) [38] | – | – | s | On-chain+ Server | – | – | Yes | – | Data confidentiality Non forgeability Verifiability | – | ms (10 MB file) | 11,386 ms (10 MB file) |
| Li (2020) [52] | – | – | – | On-chain | – | – | Yes | Yes | Data integrity Traceability | – | – | – |
| Zhao (2020) [52] | 15–20 tps | – | 17 s | On-chain | – | Yes | No | No | Authenticity | – | – | – |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Qureshi, A.; Megías Jiménez, D. Blockchain-Based Multimedia Content Protection: Review and Open Challenges. Appl. Sci. 2021, 11, 1. https://doi.org/10.3390/app11010001
Qureshi A, Megías Jiménez D. Blockchain-Based Multimedia Content Protection: Review and Open Challenges. Applied Sciences. 2021; 11(1):1. https://doi.org/10.3390/app11010001
Chicago/Turabian StyleQureshi, Amna, and David Megías Jiménez. 2021. "Blockchain-Based Multimedia Content Protection: Review and Open Challenges" Applied Sciences 11, no. 1: 1. https://doi.org/10.3390/app11010001
APA StyleQureshi, A., & Megías Jiménez, D. (2021). Blockchain-Based Multimedia Content Protection: Review and Open Challenges. Applied Sciences, 11(1), 1. https://doi.org/10.3390/app11010001






