Symmetric Enhancement of Big Data Utilization and Protection in Healthcare in China from the Perspective of Evolutionary Game Analysis
Abstract
1. Introduction
2. Literature Review
2.1. Data Security Supervision
2.2. Evolutionary Game Theory
2.3. Brief Review
3. Game Model
3.1. Problem Description
3.2. Basic Assumptions
3.3. Model Construction and Analysis
3.4. Model Improvement
3.5. Comparative Analysis
4. Simulation Analysis
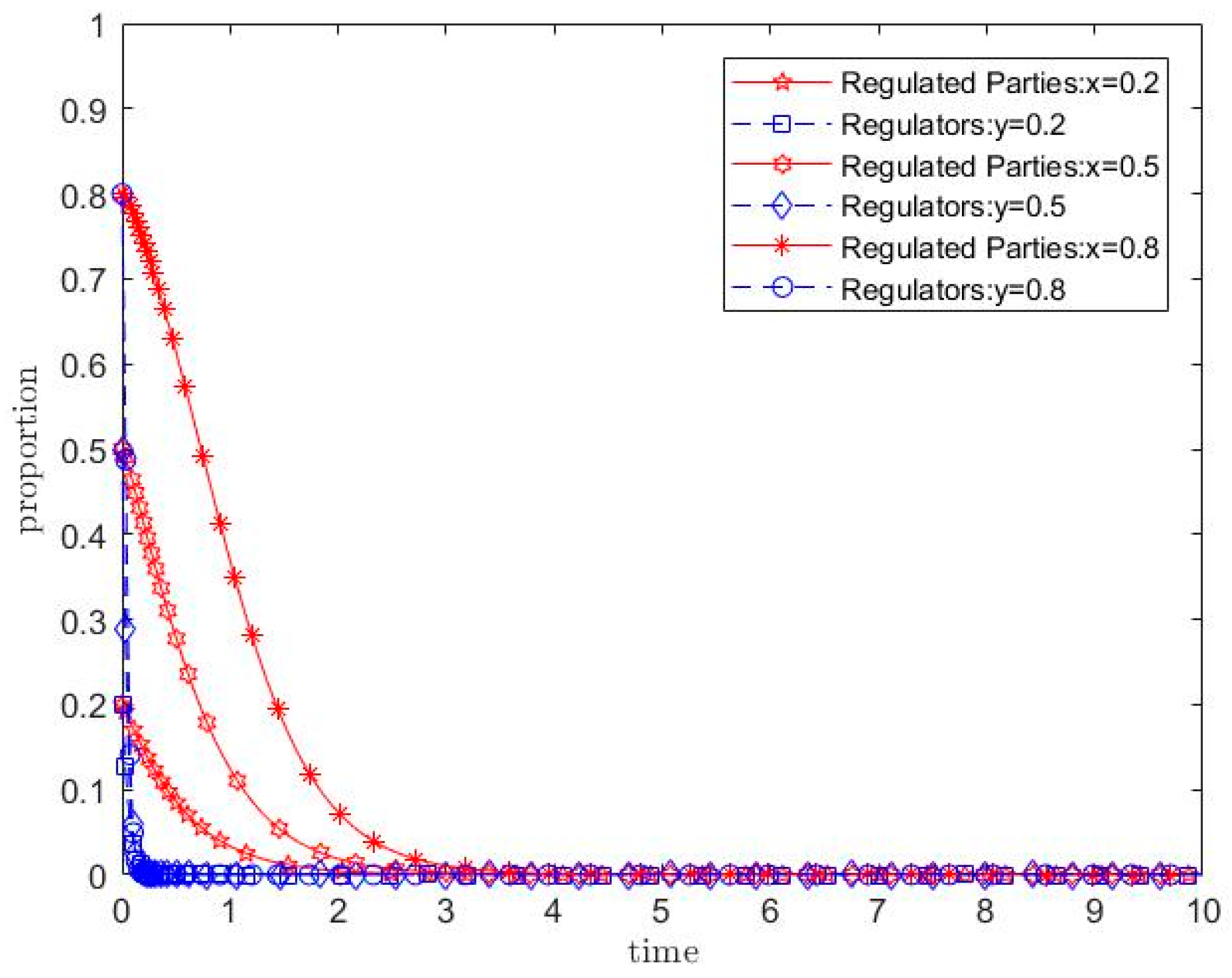
4.1. Initial Values
4.2. Impact of Process Supervision Costs on Evolutionary Results
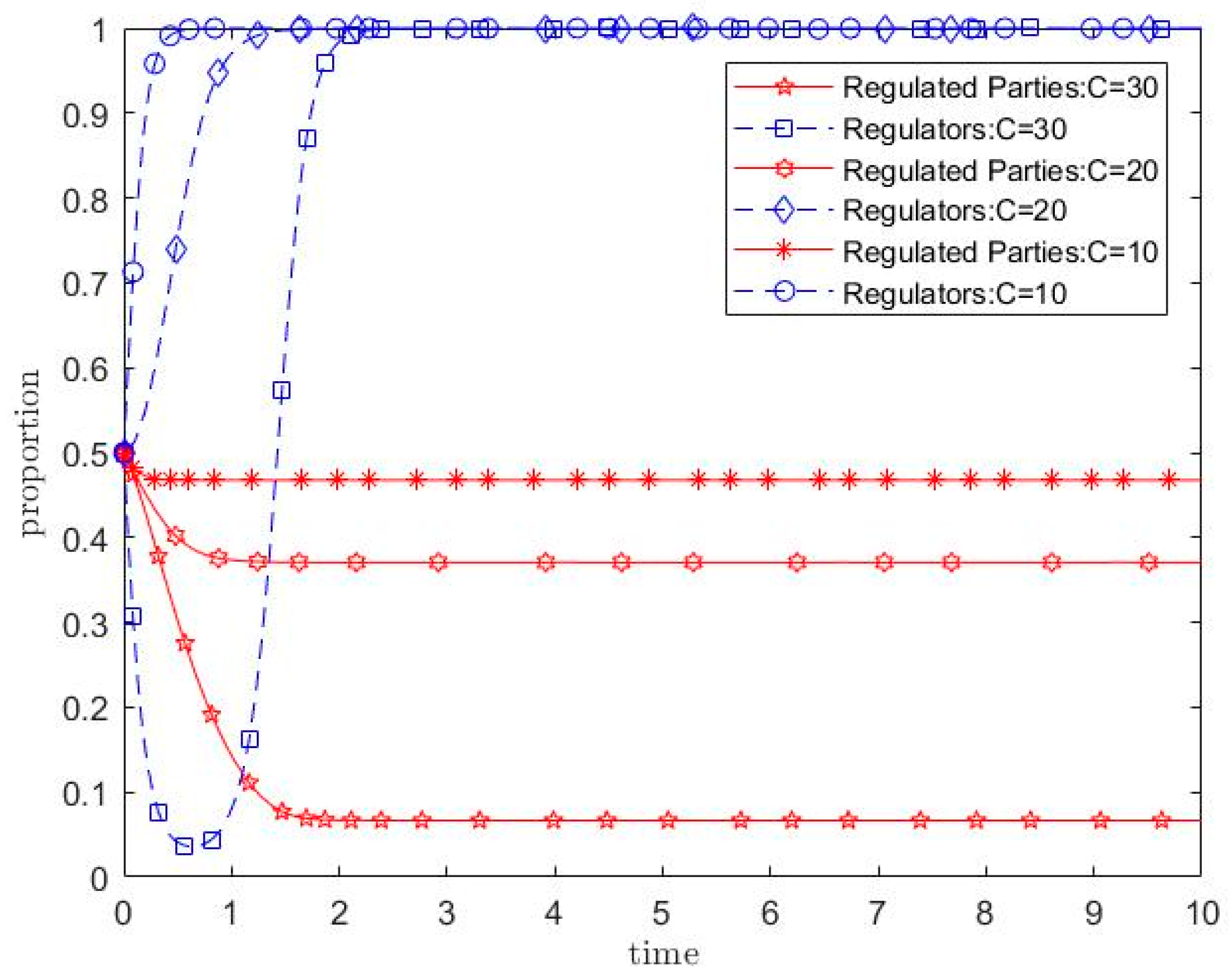
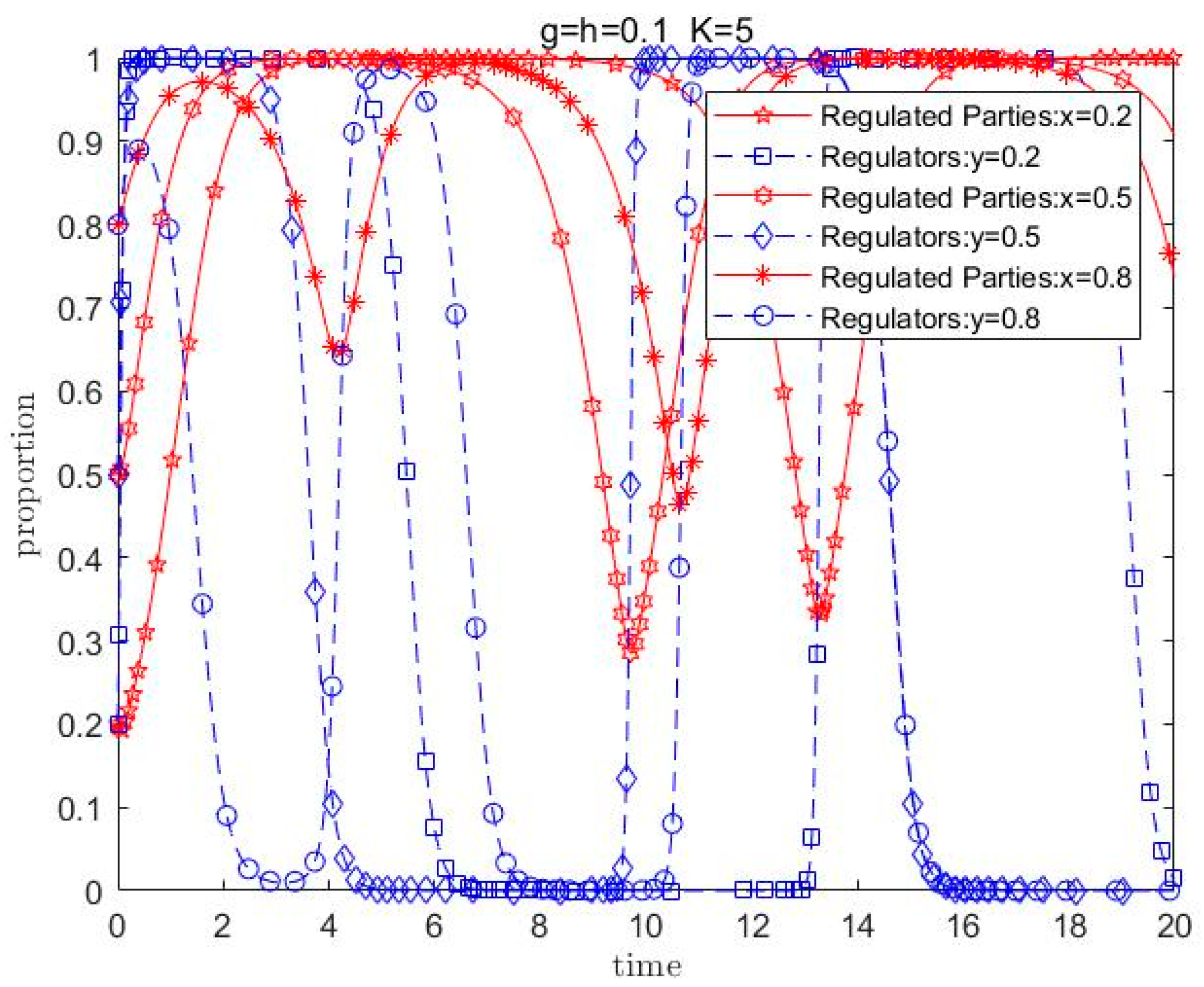
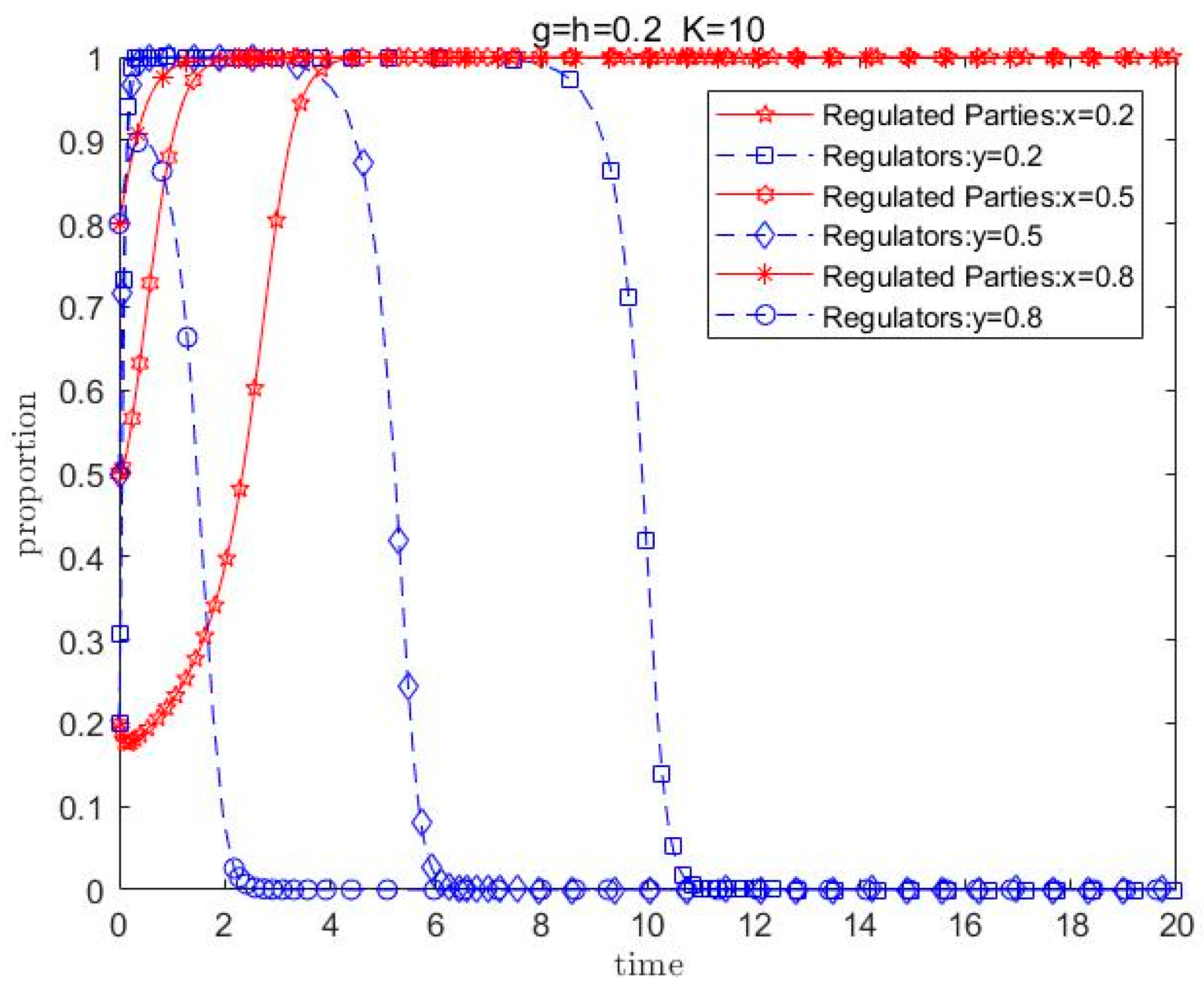
4.3. Impact of Penalty Amount on Evolutionary Results
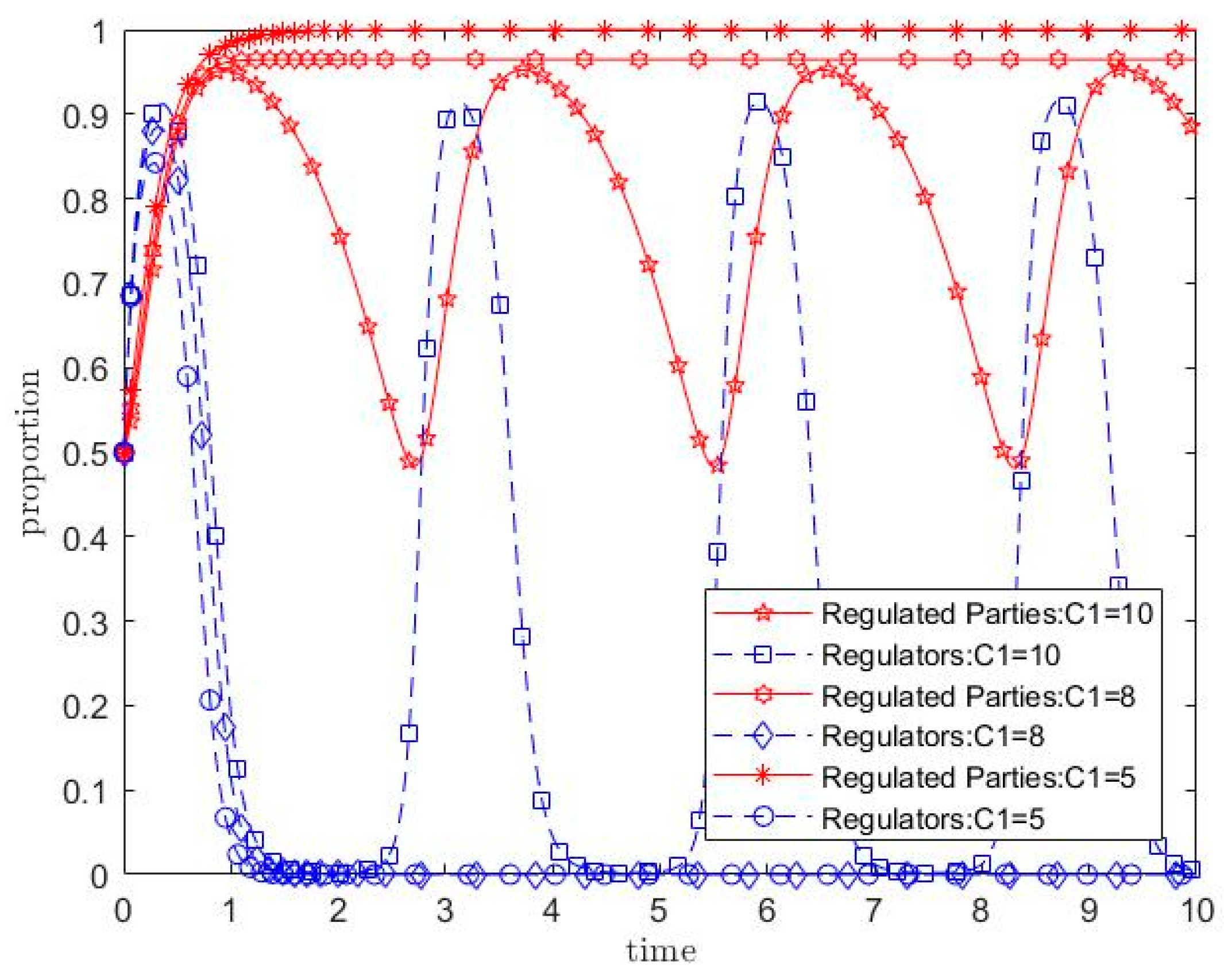
4.4. Impact of Prevention Costs on Evolutionary Results
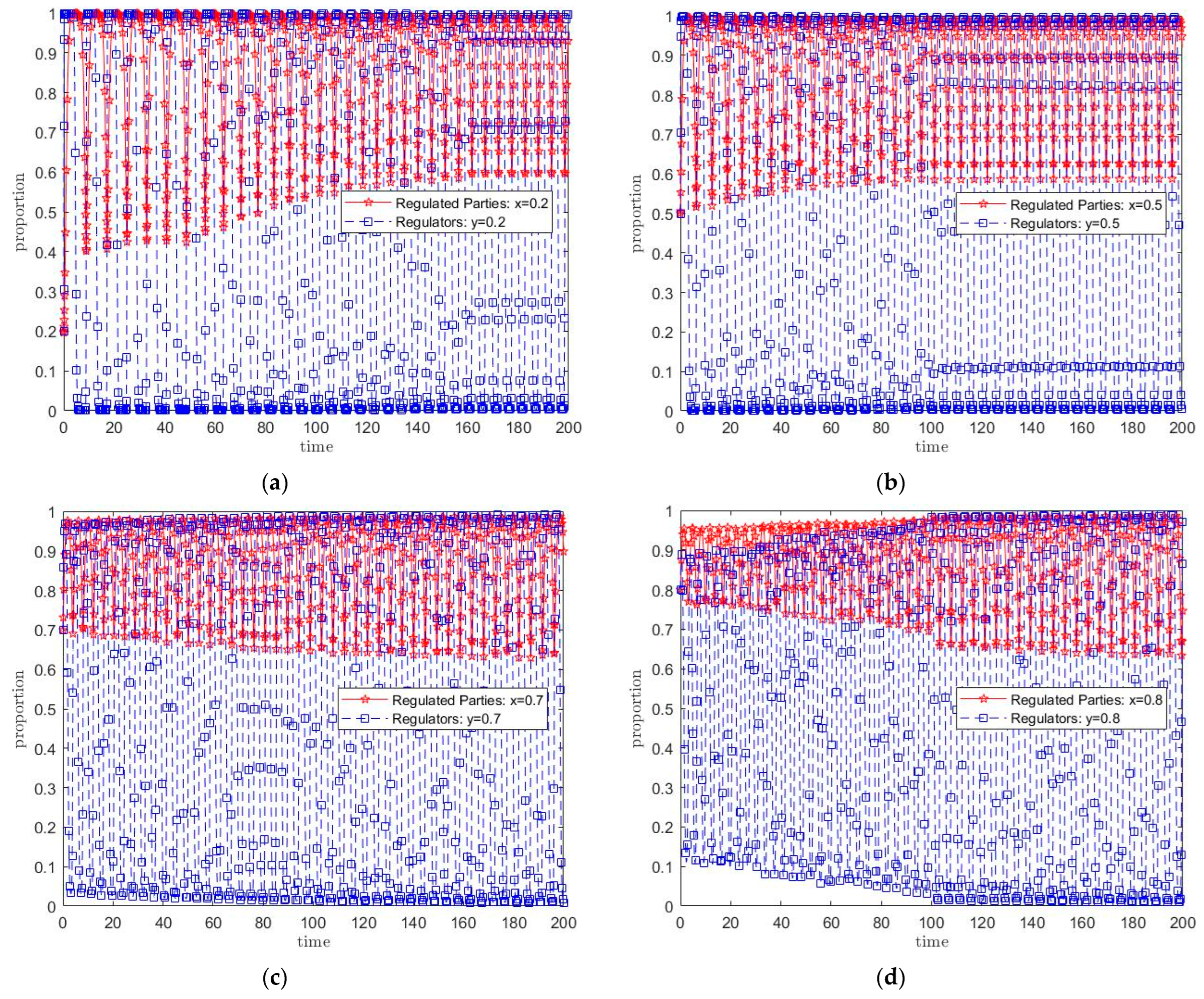
4.5. Impact of Herding Preference Utility on Evolutionary Results
5. Discussion
6. Conclusions and Recommendations
6.1. Summary and Conclusions
- From the perspective of maximizing social welfare, the ideal equilibrium state of the two-party game is (strict prevention, weak supervision). In this state, regulated entities adopt various preventive measures at lower costs, reducing security risks in the circulation and utilization of health data. Regulators only conduct outcome supervision, reducing investment in process supervision and thus yielding the optimal overall social and economic benefits;
- The fine amount imposed on regulated entities during process supervision has a significant impact on their behavior, yet it cannot eliminate unstable fluctuations in the system. The existence of fines incentivizes regulated entities to adopt strict prevention strategies. The larger the fine amount, the more inclined regulated entities are to adopt strict prevention. However, as regulators seek to reduce investment in process supervision, the strategy choices of both parties exhibit continuous fluctuations;
- Reducing the prevention costs of regulated entities is the fundamental approach for the system to achieve the equilibrium state of maximum social welfare. Regulated entities are required to implement prevention measures, entailing certain cost inputs. When their cost inputs are lower than the losses from data security risks mitigated by strict prevention measures, regulated entities will adopt strict prevention strategies regardless of the existence of speculative fines;
- Herding preference utility enhances system stability, and when this utility is sufficiently strong, it may even eliminate unstable fluctuations in the system. When decision-makers base their choices on economic utility, if an equilibrium has already been reached, herding utility will reinforce this equilibrium; if no equilibrium has been reached, the herding utility of both parties in the game can drive the system toward equilibrium once it reaches a certain intensity.
6.2. Policy Recommendations
6.2.1. Enhancing the Feasibility of Protection Measures
6.2.2. Implementing Subsidy Policies When Necessary
6.2.3. Exploring a New Model of Multi-Stakeholder Collaborative Supervision
6.2.4. Enhancing Risk Awareness and Strengthening Publicity and Guidance
Supplementary Materials
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Cyberspace Administration of China. Data Security Management Measures (Draft for Comment). Available online: https://www.gov.cn/xinwen/2019-05/28/content_5395524.htm (accessed on 12 July 2025).
- Central People’s Government of the People’s Republic of China. Decision of the CPC Central Committee on Further Comprehensively Deepening Reform and Advancing Chinese Modernization. Available online: https://www.gov.cn/zhengce/202407/content_6963770.htm (accessed on 12 July 2025).
- The Beijing News. Qi An Xin: Over 900 Million Pieces of Medical Data Leaked in China’s Healthcare Industry in 2023. Available online: https://baijiahao.baidu.com/s?id=1799033114609880080 (accessed on 12 July 2025).
- Verizon Business. Data Breach Investigations Report 2024. Available online: https://www.verizon.com/business/resources/Te1e/reports/2024-dbir-data-breach-investigations-report.pdf (accessed on 12 July 2025).
- Oh, S.; Seo, Y.; Lee, E.; Kim, Y.G. A comprehensive survey on security and privacy for electronic health data. Int. J. Environ. Res. Public Health 2021, 18, 9668. [Google Scholar] [CrossRef] [PubMed]
- Data Security Governance Committee of Zhongguancun Cyber Security and Informatization Industry Alliance. Data Security Governance White Paper 4.0. Available online: https://13115299.s21i.faiusr.com/61/1/ABUIABA9GAAg7fTSlAYo1PvtBA.pdf (accessed on 12 July 2025).
- Data Security Governance Committee of Zhongguancun Cyber Security and Informatization Industry Alliance. Data Security Governance White Paper 5.0. Available online: http://www.zzife.edu.cn/ewebeditor/uploadfile/file/2023/05/22/20230522111958631.pdf (accessed on 12 July 2025).
- Wei, X.J.; Huang, X.Y.; Xiao, L.Y. Audit-driven Data Security Governance from the Perspective of Developing New Quality Productive Forces. Audit. Res. 2024, 5, 45–52. [Google Scholar]
- Zhang, Q.; Ma, H.Q.; Niu, X.H. Research on Chinese Data Security Policy Evaluation Based on PMC Index Model. J. Mod. Inf. 2024, 44, 13–27+136. [Google Scholar]
- Ma, H.Q.; Cui, W.B.; Zhang, T. Text Topic Mining and Evolution Analysis of Chinese Government Data Security Policy. J. Mod. Inf. 2024, 44, 28–38. [Google Scholar]
- Zhang, T.; Zhang, B.Y.; Ma, H.Q. Research on the Diffusion Characteristics and Topic Transfer of Data Security Policies of China’s Central and Local Governments. Inf. Stud. Theory Appl. 2025, 48, 118–127+137. [Google Scholar]
- Mei, A.; Chen, Z.W. Institutional construction of data security supervision in China from the perspective of holistic national security concept. E-Government 2023, 11, 104–115. [Google Scholar]
- Liao, J.L. On the Normative Configuration of the Right to Data Regulation. Hebei Acad. J. 2025, 45, 216–224. [Google Scholar]
- Zhang, T.; Cui, W.B.; Liu, S.; Cai, Q.P.; Ma, H.Q. UK National Data Security Governance:Systems, Institutions and Implications. J. Inf. Resour. Manag. 2022, 12, 44–57. [Google Scholar]
- Li, H.S. From Static Defense to Dynamic Security: A Paradigm Shift in the Legal Protection of Data Security. Res. Rule Law 2025, 1, 118–131. [Google Scholar]
- Li, H.C.; Ma, J.; Hu, M. Construction of a Medical Blockchain Model for the Security Protection of Healthcare Big Data. Libr. Inf. Serv. 2021, 65, 37–44. [Google Scholar]
- Duan, J.J.; Liu, Y.; Chen, J.H. Secure Electronic Medical Data Sharing Scheme Based On Blockchain. Comput. Appl. Softw. 2024, 41, 116–121+226. [Google Scholar]
- Cai, C.J.; Liu, Y. Blockchain-Based Solution For Secure Sharing of Medical Data. Comput. Appl. Softw. 2024, 41, 360–366. [Google Scholar]
- Wu, Y.; Chen, D.W. Research on Data Security Sharing Technology Based on Blockchain and Proxy Re-encryption. Inf. Secur. Res. 2024, 10, 719–728. [Google Scholar]
- Bao, X.L. Trusted Data Space: A Co-governance Framework of Technology and Legal Rules. Zhejiang Acad. J. 2024, 1, 89–100+239–240. [Google Scholar]
- Zhang, Z.T.; Li, X. Big Data Regulation: Operational Logic, Risk Issues, and Regulatory Approaches. J. Guangdong Univ. Financ. Econ. 2024, 39, 103–111. [Google Scholar]
- Tang, C.L.; Zhang, X.J. Establishing Digital Trust: The Trust Foundations, Intrinsic Logic, and lmplementation Framework for the Trusted Circulation of Data Elements. Available online: http://kns.cnki.net/kcms/detail/44.1306.G2.20241212.1400.002.html (accessed on 12 July 2025).
- Zhou, W.J. Evidence-Based Practice for Constructing Trusted Data space: Fundamental Principles, Action Procedure and Application Scenario. Libr. Dev. 2025, 2, 12–20. [Google Scholar]
- Wang, Y.J.; Chen, S.L. Construction of Trusted Data space for Cultural Heritage: Practical Significance, Key Points, and Implementation Pathways. Libr. Dev. 2025, 2, 32–37. [Google Scholar]
- Fan, Z.J.; Liu, T.X. Trusted Data space: Building a New Platform for Cultural Data Circulation and Value Co-Creation. Libr. Dev. 2025, 2, 29–31+48. [Google Scholar]
- Yang, F. Trustworthiness and Feasibility of Data Cross-Border Flow. Libr. Dev. 2025, 2, 9–11+25. [Google Scholar]
- Kong, X.C. The theoretical explanation and practice of the construction of data security supervision system: In accordance with a holistic approach to national security. Qinghai Soc. Sci. 2024, 4, 142–151. [Google Scholar]
- Wang, D.D.; Wu, J.G. Research on Regulatory Strategies of Healthcare Data Open Utilization: Analysis Based on OpenNeuro Platform. Libr. Inf. Serv. 2025, 69, 58–67. [Google Scholar]
- Su, D. A Study on the Supervision of Personal Health Data from the Perspective of Privacy Protection. J. Hangzhou Norm. Univ. (Soc. Sci. Ed.) 2021, 43, 93–103. [Google Scholar]
- Song, D.B.N.; Wu, D.Z. Research on the Regulatory System Optimization of Trans-border Flows of Personal Data under the New Security Pattern. Inf. Stud. Theory Appl. 2024, 47, 54–61. [Google Scholar]
- Huang, Y. Research on the Supervision Model of Cross-border Flow of Non-personal Data in EU. J. Intell. 2022, 41, 111–118. [Google Scholar]
- Chen, Z.Q. Regulatory Sandbox: A New Approach to Data Element Governance. Libr. Trib. 2024, 44, 138–147. [Google Scholar]
- Xu, T.X.; Ma, H.Q. Research on Cooperative Supervision of Open Government Data. Mod. Intell. 2018, 38, 19–23. [Google Scholar]
- Xu, Y.H.; Ji, M.R. “Three Simultaneities” System: Innovation of Risk Supervision of Cross-Border Flow of Personal Data. J. Intell. 2022, 41, 84–90. [Google Scholar]
- He, J.H. Sandbox Regulatory Mechanism for Data Cross-Border Flow from the Perspective of Incomplete Contract. Digit. Libr. Forum 2024, 20, 58–64. [Google Scholar]
- Li, Y.H. Theoretical Traceability, Realistic Contradiction and Regulatory Development of Government Access to Data Between Europe and America in Cross-Border Data Flows. J. Intell. 2023, 42, 86–92. [Google Scholar]
- Pan, D.P.; Hao, Y.J.; Qiao, P.H.; Zhang, Z.Q. Research on Risk Classification Supervision Strategy of Cross-border Data Flow. Manag. Rev. 2024, 36, 43–53. [Google Scholar]
- Chen, C.B.; Cheng, S. On the Responsibility of Government Supervision in Open Data: Practical Dilemma and Optimizing Path. J. Intell. 2019, 38, 184–190. [Google Scholar]
- Chen, C.B.; Cheng, S. International Experience and China’s Path of Open Government Data Supervision. Libr. Inf. Serv. 2020, 64, 49–57. [Google Scholar]
- Di, L.Y. Research on the Curation Model of Government Open Data. Inf. Stud. Theory Appl. 2018, 41, 22–26+10. [Google Scholar]
- Zhang, Z.; Wang, Y.; Ma, H.Q. Research on Public Data Security System from the Perspective of Digital Ecology. Mod. Intell. 2025, 45, 106–115. [Google Scholar]
- Di, L.Y. The Concept, Model and Development Strategy of Circulation Supervision of Authorization Operation for Public Data Factors. Mod. Intell. 2024, 44, 93–104. [Google Scholar]
- Yang, J.; Wang, K.X. Tripartite Evolutionary Game Analysis of Medical Data Sharing Under Blockchain Architecture. Comput. Sci. 2023, 50 (Suppl. 1), 555–561. [Google Scholar]
- Zhao, X.Q.; Li, J.L.; Li, T.E. Research on the Regulation of APP Personal Information Security Based on Tripartite Evolutionary Game. Available online: http://kns.cnki.net/kcms/detail/22.1264.G2.20241015.1520.002.html (accessed on 12 July 2025).
- Bai, Y.; Ding, L.L. Research on the evolution path of carbon financial market considering time preference under reputation incentive mechanism. Available online: http://kns.cnki.net/kcms/detail/11.2267.N.20240515.1305.023.html (accessed on 12 July 2025).
- Bai, Y.; Zhao, X.; Ding, L.L. Research on Chinese Emission Allowances Storage and Lending Mechanism Considering Enterprise Time Preference. Chin. J. Manag. Sci. 2025, 33, 357–368. [Google Scholar]
- Pan, D.P.; Hao, Y.J.; Wang, X.Y.; Zhang, Z.Q. Green development from the perspective of green preference: Government regulation, corporate transformation and investment choice of financial institution. Syst. Eng.-Theory Pract. 2024, 44, 2411–2425. [Google Scholar]
- Ding, L.L.; Guo, Z.M.; Bai, Y.; Wang, P. Impact Analysis of Fairness Preference on Industrial Development of Carbon Capture and Storage(CCS) Projects. Chin. J. Manag. Sci. 2024, 32, 187–197. [Google Scholar]
- Wang, X.N.; Guo, P.; Guo, N. Optimization of Supervision Mechanism for Pollutant Abatement under Limited Supervision Ability and Heterogeneous Risk Preference. Oper. Res. Manag. Sci. 2023, 32, 23–28. [Google Scholar]
- Zhang, D.N.; Guo, P. Speculation in Epidemic Prevention, Long-term Efficient Supervision, and Conformity Preference: Evolutionary Game Modeling and Analysis. Oper. Res. Manag. Sci. 2023, 32, 23–30. [Google Scholar]
- Hyman, H.H. The psychology of status. Arch. Psychol. (Columbia Univ.) 1942, 269, 94. [Google Scholar]
- Burt, R.S. Social contagion and innovation: Cohesion versus structural equivalence. Am. J. Sociol. 1987, 92, 1287–1335. [Google Scholar] [CrossRef]
- Cao, F.F.; Zhang, J.H.; Li, L.; Wang, W.T.; Zhang, K. Research Review of Foreign Herd Behavior from the Perspective of Citing Papers. Inf. Sci. 2022, 40, 183–192. [Google Scholar]
- Abrahamson, E.; Rosenkopf, L. Institutional and competitive bandwagons: Using mathematical modeling as a tool to explore innovation diffusion. Acad. Manag. Rev. 1993, 18, 487–517. [Google Scholar] [CrossRef]
- State Administration For Market Regulation, Standardization Administration of China. Information Security Technology—Health Data Security Guidelines. Available online: https://openstd.samr.gov.cn/bzgk/gb/newGbInfo?hcno=239351905E7B62A7DF537856738247CE&refer=outter (accessed on 12 July 2025).
- China Academy of Information and Communications Technology. Research Report on Data Governance: Legal and Regulatory System for Network Data Security Management (2024). Available online: https://www.caict.ac.cn/kxyj/qwfb/ztbg/202501/P020250124606084575821.pdf (accessed on 12 July 2025).
- Ritzberger, K.; Weibull, J.W. Evolutionary selection in normal-form games. Econometrica 1995, 63, 1371–1399. [Google Scholar] [CrossRef]
- Friedman, D. Evolutionary games in economics. Econometrica 1991, 59, 637–666. [Google Scholar] [CrossRef]
- Zhu, L.L.; Rong, J.M.; Zhang, S.Y. Three-party Evolutionary Game and Simulation Analysis of Drug Quality Supervision under the Government Reward and Punishment Mechanism. Chin. J. Manag. Sci. 2021, 29, 55–67. [Google Scholar]
- Lv, F. The impact of conformity on adult learning: Motivation and behavior. Hum. Resour. Dev. China 2010, 4, 98–100. [Google Scholar]
- Banerjee, A.V. A simple model of herd behavior. Q. J. Econ. 1992, 107, 797–817. [Google Scholar] [CrossRef]
- Latané, B. The psychology of social impact. Am. Psychol. 1981, 36, 343. [Google Scholar] [CrossRef]
- Bikhchandani, S.; Hirshleifer, D.; Welch, I. A theory of fads, fashion, custom, and cultural change as informational cascades. J. Political Econ. 1992, 100, 992–1026. [Google Scholar] [CrossRef]
- Dal, B.E. Regulatory capture: A review. Oxf. Rev. Econ. Policy 2006, 22, 203–225. [Google Scholar] [CrossRef]
- Yoon, A.; Kim, J.; Donaldson, D.R. Big data curation framework: Curation actions and challenges. J. Inf. Sci. 2025, 51, 205–223. [Google Scholar] [CrossRef]
- Li, M. A Research on Ftc’S Administrative Enforcement Settlement of Privacy and Data Security. Master’s Thesis, Shanghai Jiao Tong University, Shanghai, China, 30 May 2022. [Google Scholar]
- The European Parliament and the Council of the European Union. Regulation (EU) 2025/327 on the European Health Data Space and Amending Directive 2011/24/EU and Regulation (EU). Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32025R0327&qid=1742006688936 (accessed on 12 August 2025).
- NHS ENGLAND. Data Access Request Service (DARS). Available online: https://digital.nhs.uk/services/data-access-request-service-dars (accessed on 12 August 2025).
- The Uk Caldicott Guardian Council. Origins of the Role. Available online: https://caldicottguardian.squarespace.com/origins-of-the-role (accessed on 12 August 2025).


| Regulated Parties/Regulators | Regulators | ||
|---|---|---|---|
| Strong Supervision | Weak Supervision | ||
| Regulated Parties | Strict prevention | , | , |
| Opportunistic non-compliance | , | , | |
| Equilibrium Point | Stability Conclusion | Corresponding States | ||
|---|---|---|---|---|
| Saddle OR ESS | (Opportunistic non-compliance, weak supervision) | |||
| Unstable | (Opportunistic non-compliance, strong supervision) | |||
| Saddle OR ESS | (strict prevention, weak supervision) | |||
| Unstable | (strict prevention, strong supervision) |
| Equilibrium Point | Stability Conclusion | Corresponding States | ||
|---|---|---|---|---|
| Saddle OR ESS | (Opportunistic non-compliance, weak supervision) | |||
| Saddle OR ESS | (Opportunistic non-compliance, strong supervision) | |||
| Saddle OR ESS | (strict prevention, weak supervision) | |||
| Saddle OR ESS | (strict prevention, strong supervision) |
| Initial Values | |||||||||||
| 10 | 5 | 50 | 100 | 500 | 0.02 | 0.1 | 0 | 0 | 0 | 0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wang, D.; Xie, S. Symmetric Enhancement of Big Data Utilization and Protection in Healthcare in China from the Perspective of Evolutionary Game Analysis. Symmetry 2025, 17, 1405. https://doi.org/10.3390/sym17091405
Wang D, Xie S. Symmetric Enhancement of Big Data Utilization and Protection in Healthcare in China from the Perspective of Evolutionary Game Analysis. Symmetry. 2025; 17(9):1405. https://doi.org/10.3390/sym17091405
Chicago/Turabian StyleWang, Dandan, and Shicheng Xie. 2025. "Symmetric Enhancement of Big Data Utilization and Protection in Healthcare in China from the Perspective of Evolutionary Game Analysis" Symmetry 17, no. 9: 1405. https://doi.org/10.3390/sym17091405
APA StyleWang, D., & Xie, S. (2025). Symmetric Enhancement of Big Data Utilization and Protection in Healthcare in China from the Perspective of Evolutionary Game Analysis. Symmetry, 17(9), 1405. https://doi.org/10.3390/sym17091405





