An Incremental and Backward-Conflict Guided Method for Unfolding Petri Nets
Abstract
1. Introduction
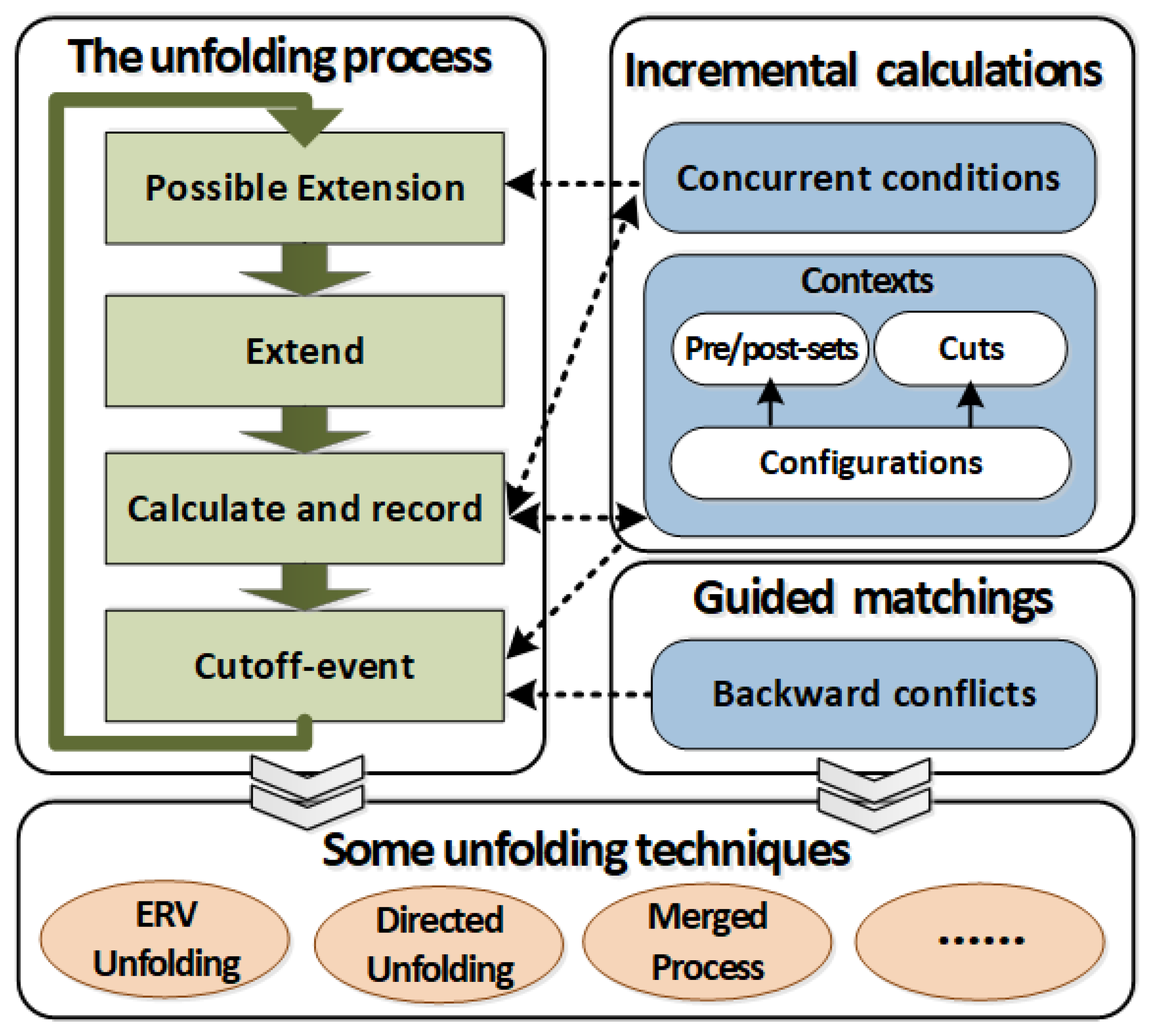
- (1)
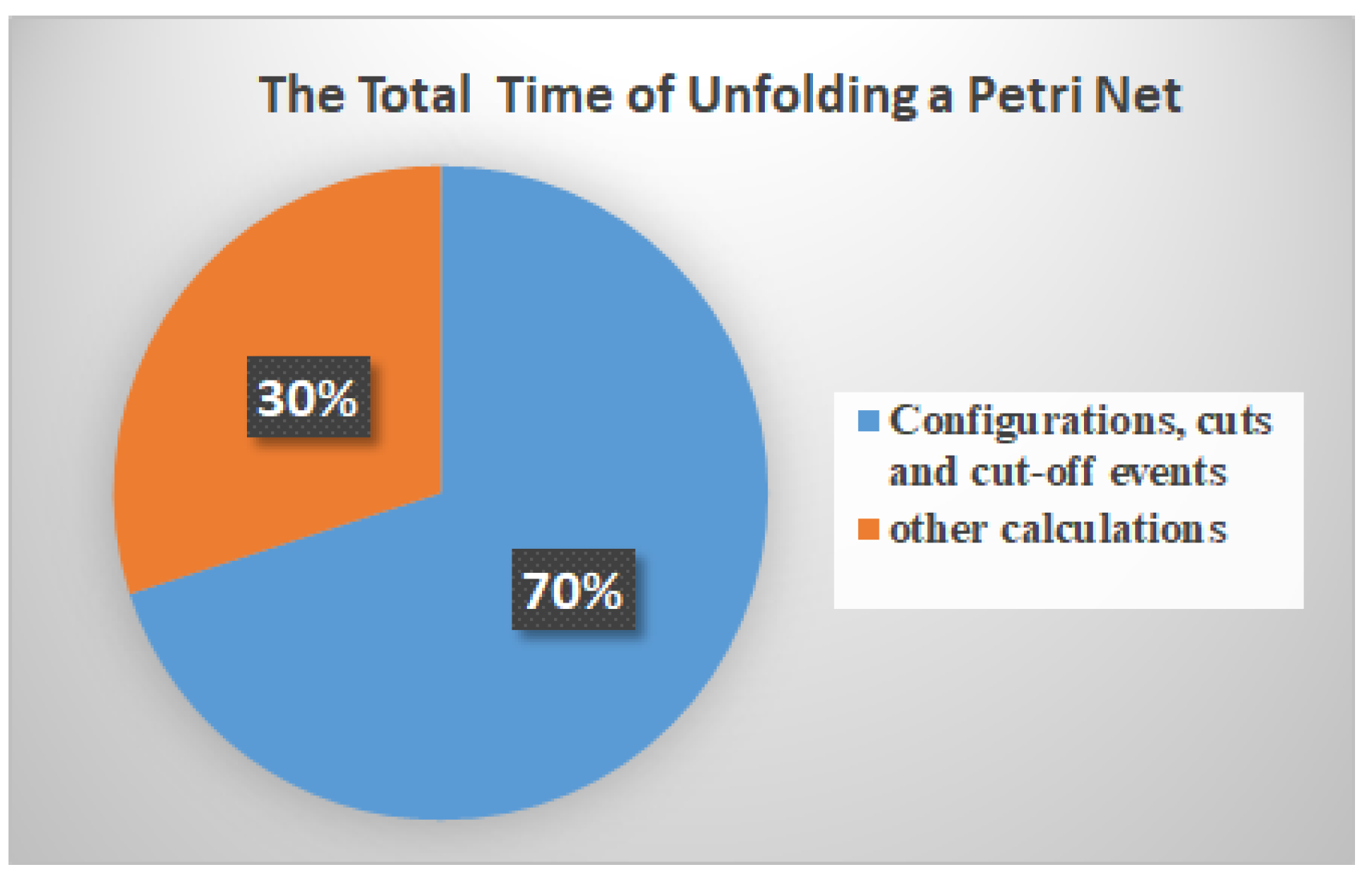
- Incremental methods are proposed to calculate configurations, cuts and concurrent conditions.
- (2)
- Backward conflicts are used to guide the determination of cut-off events.
- (3)
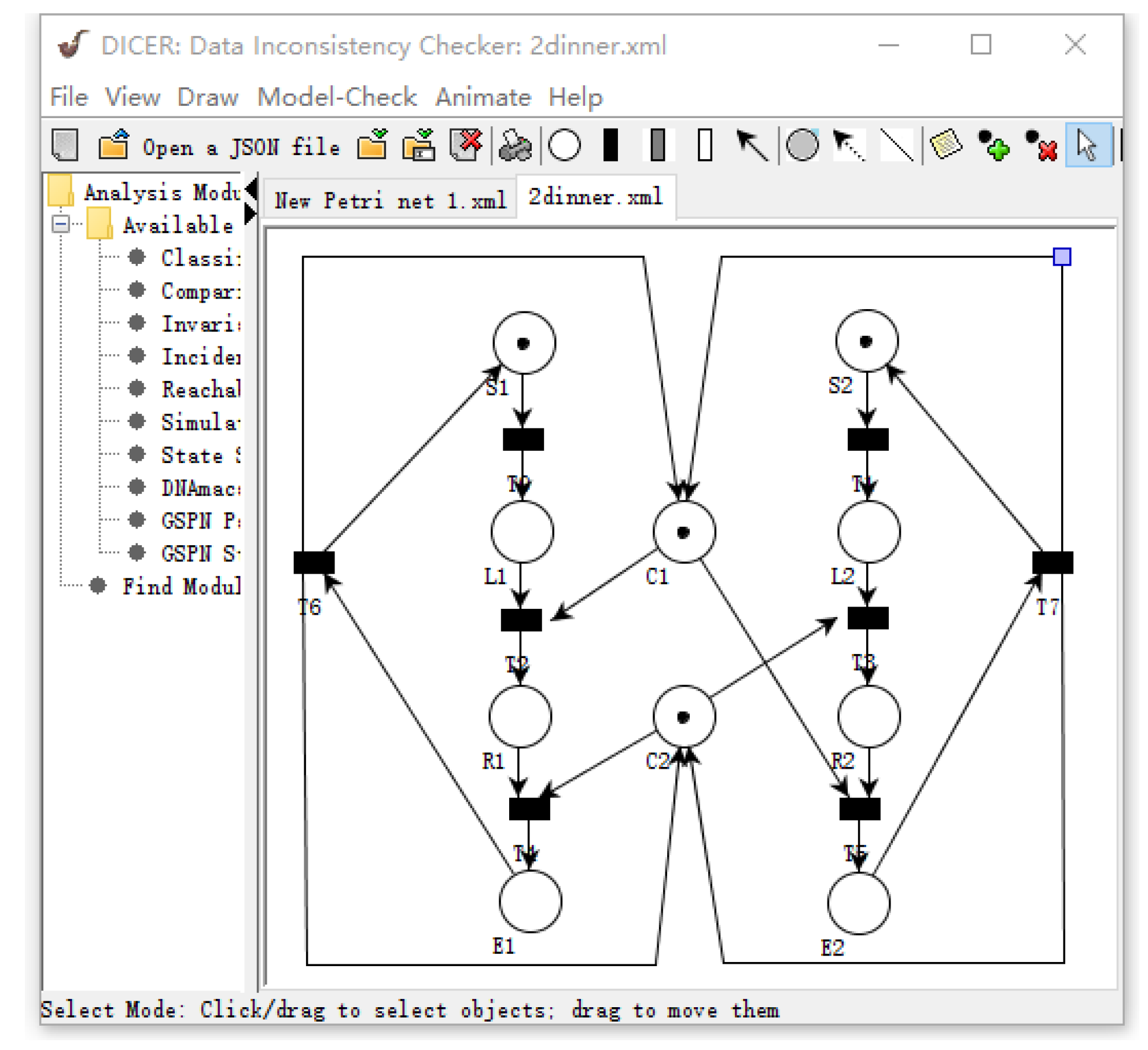
- A tool is developed to implement our improved methods for unfolding a Petri net.
2. Related Work
2.1. The Unfolding Techniques of Petri Nets
2.2. Model Checking Based on Petri Net Unfolding
3. Basic Notations
- (1)
- P and T are two disjoint and finite sets, which are, respectively, called place set and transition set; and,
- (2)
- is a flow relation.
- (1)
- x and y are incausality, which is denoted by x ≤ y, if the net contains a path from x to y. Especially, if , it is denoted as x < y.
- (2)
- x and y are inconflict, which is denoted by , if ∃: ∩≠∅, ≤x, and ≤ y; or,
- (3)
- x and y are inconcurrency, denoted by xcoy, if there is neither , nor , nor .
- (1)
- : ;
- (2)
- : ; and,
- (3)
- no transition is in self-conflict, i.e., :.
- (1)
- and ;
- (2)
- for every , the restriction of h onto (resp., )) is a bijection between and (resp., between and );
- (3)
- the restriction of h onto is a bijection between and ; and,
- (4)
- for every ,, if and , then .
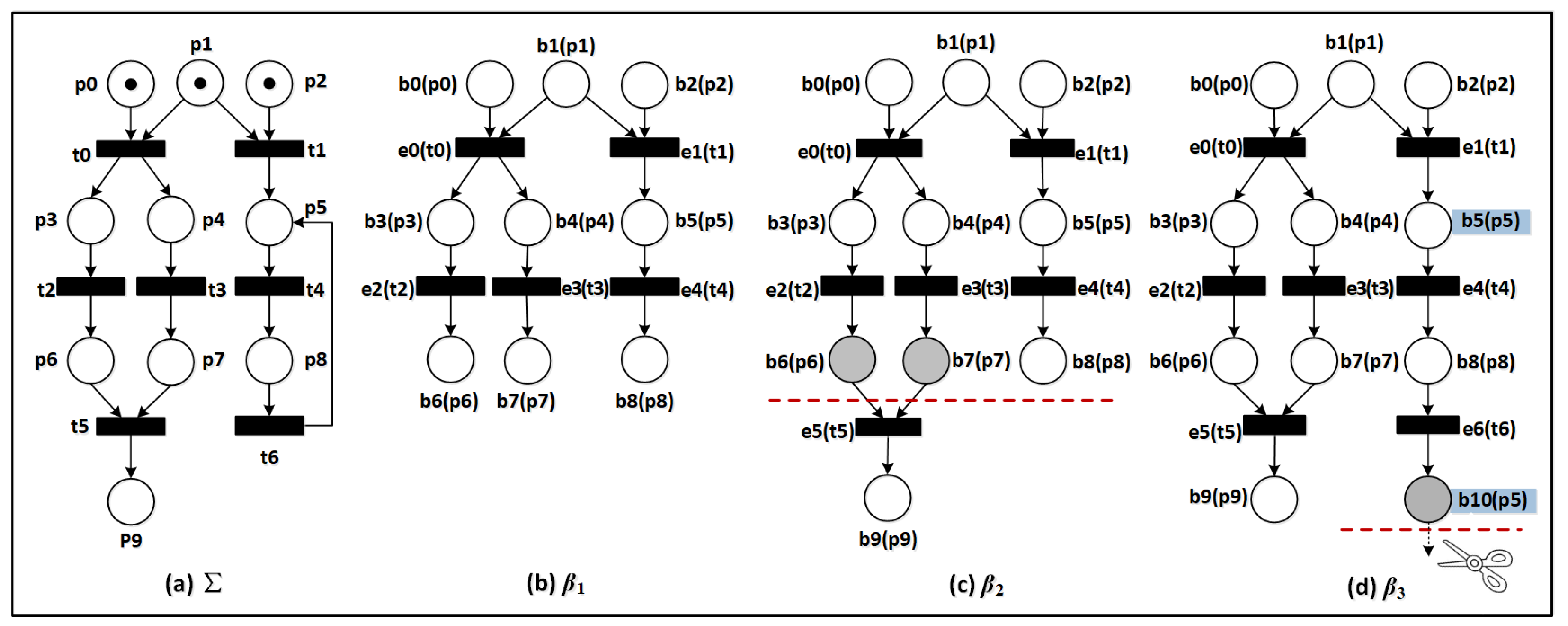
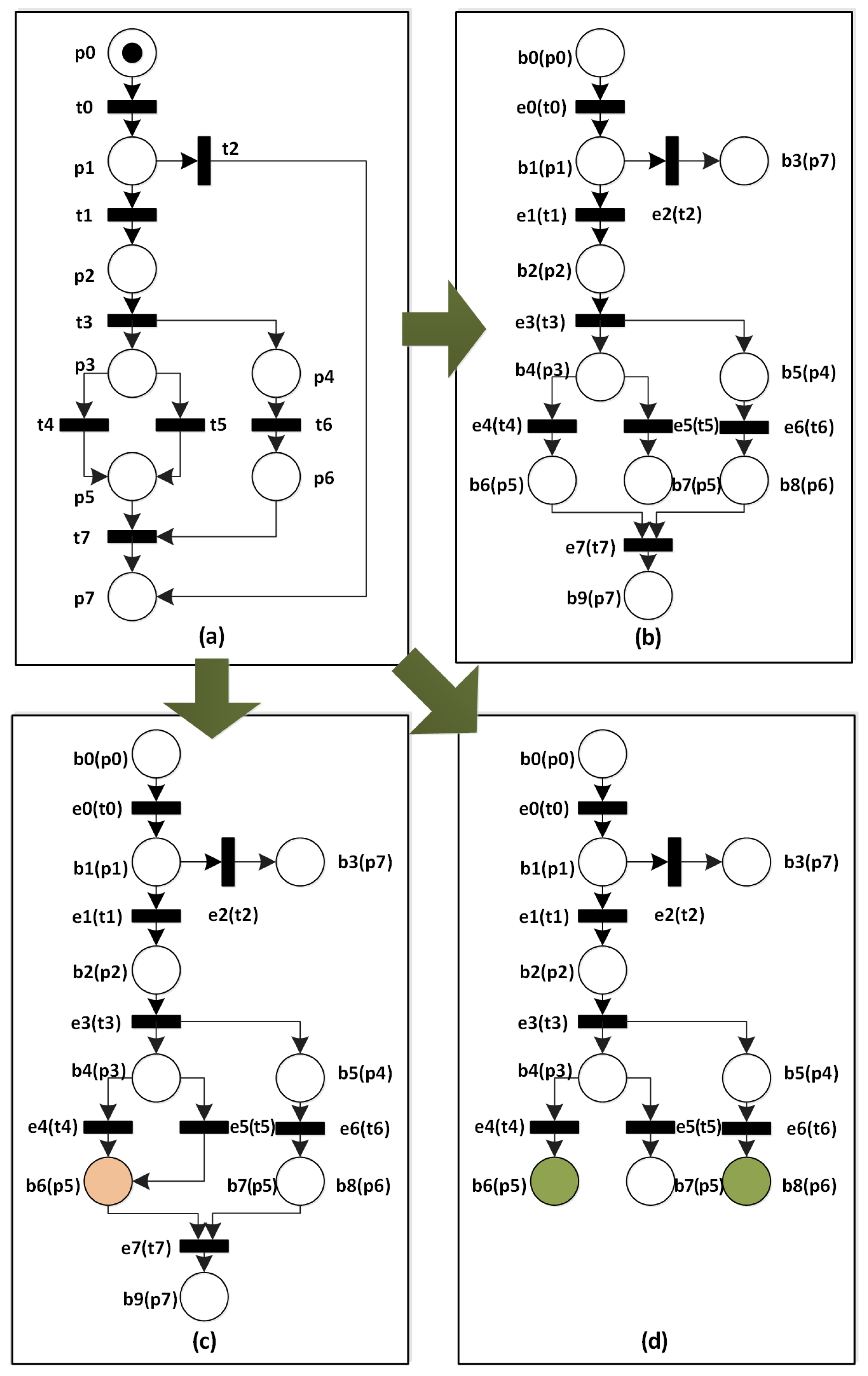
4. The Existing Unfolding Method of Petri Nets
4.1. Finite Complete Prefix
- only contains finitely many events and conditions; and,
- for every reachable marking M there exists a configuration C in such that , and for every transition t enabled by M there exists a configuration such that and e is labeled by t.
4.2. The Classical Algorithm for Generating an FCP
| Algorithm 1 A finite complete prefix (FCP) algorithm |
| Require: |
| A Petri net ; |
| Ensure : |
| A finite complete prefix of ; |
|
4.3. Discussion
- (1)
- The repeated calculations of configurations and cuts.
- (2)
- The blindness in determining cut-off events.
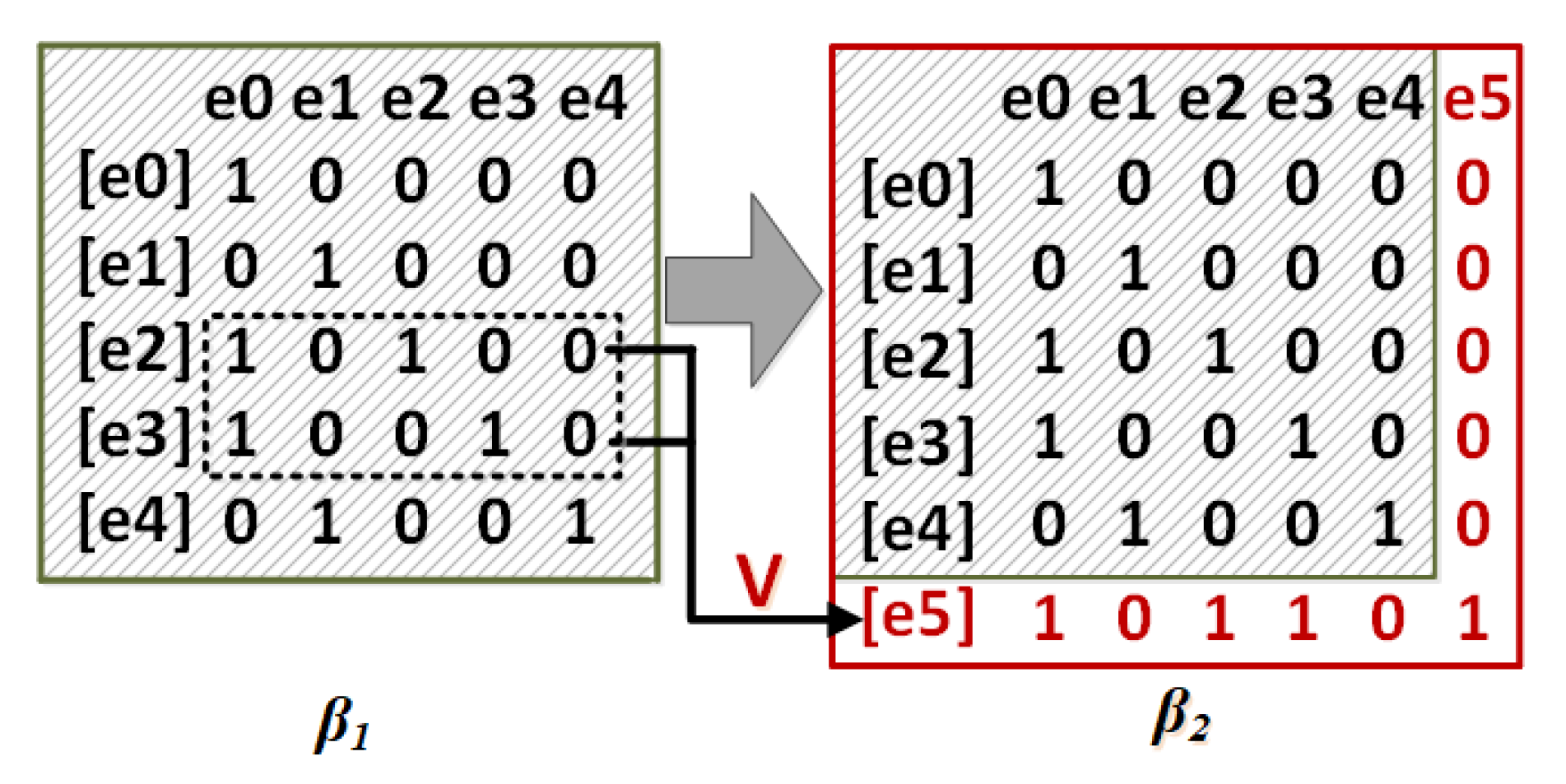
5. An Improved Computing Method for Unfolding Petri Nets
5.1. The Incremental Calculations of Configurations and Cuts
- (1)
- ;
- (2)
- ;
- (3)
- .
| Algorithm 2 Possible extension algorithm |
| Require: |
| A prefix and its concurrency matrix A of conditions; |
| Ensure : |
| A set of possible extensions ; |
|
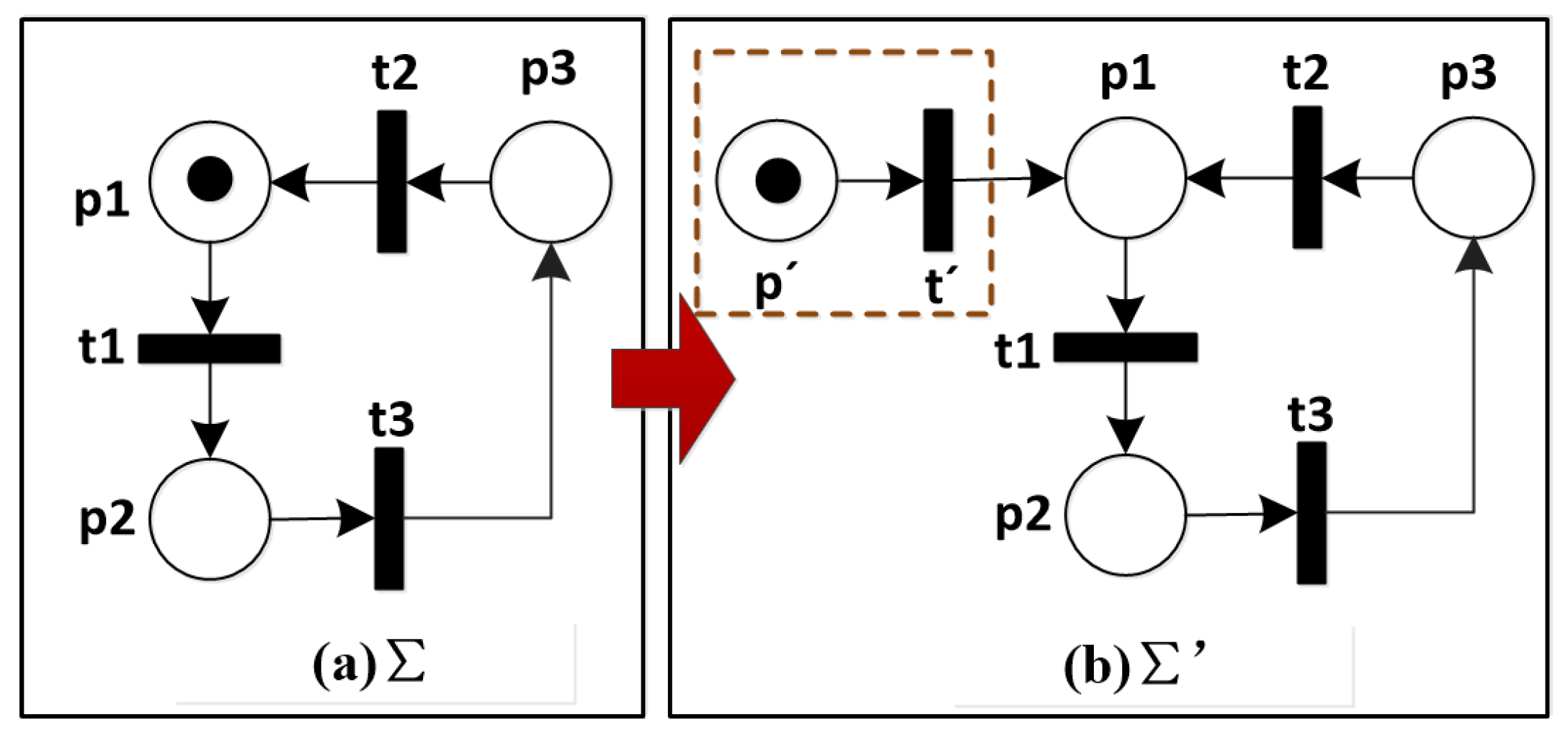
5.2. The Backward-Conflict Guided Calculations of Cut-Off Events
5.3. An Improved Algorithm for Generating an FCP
- The contexts of events are calculated in Lines 10–15 according to Equation (5) and Theorem 2.
- Algorithm 2 is utilized to calculate the possible extensions.
- Cut-off events are determined by Theorem 3, and Lines 19–22 correspond to this point.
| Algorithm 3 An incremental and backward-conflict guided algorithm for generating an FCP |
| Require: |
| A Petri net ; |
| Ensure : |
| A finite complete prefix of ; |
| (1) Initialize |
|
| (2) Unfolding process |
|
5.4. The Validation of Our Improved Unfolding Method
5.5. Model Checkings Based on the Improved Unfolding Method
- (1)
- Embedded into the existing unfolding techniques
- (2)
- Checking reachability, properly completed, and deadlocks
- ReachabilityOn the one hand, we can utilize the directed unfolding technique [15] to verify the reachability of markings or places. On the other hand, some incremental calculations of configurations (e.g., configuration matrix) can be used to check whether a transition is reachable to the other one in the execution of a Petri net. That is, given two transitions and two events , if the configuration matrix A of an FCP satisfies , then we can come to the conclusion that is reachable to . Notice that and are, respectively, the i-th and j-th elements of E.
- Properly completedAs is well known, a WF-net is properly completed if it satisfies , where o is the sink place [44]. In order to verify this property, we can determine whether there exist some conditions that are concurrent with sink conditions (i.e., corresponding to the sink places) in our concurrency matrix. If these conditions exist, they indicate that is not properly completed or sound.
- DeadlocksBecause the context of an event is calculated in our improved unfolding method, we can utilize its cuts and Mark functions to check deadlocks, i.e., a marking M is a deadlock if and no transition is enabled at M.
6. Case Study
- (1)
- There is no deadlock in because there always exist enabled transitions at any local markings (except for the final state).
- (2)
- is properly completed, because no condition is concurrent with the sink condition in the concurrency matrix of Figure 9a.
- (3)
- Because events and are included in the directed unfolding and satisfy ∧∧, the marking is reachable from the initial marking .
- (4)
- According to the configuration matrix of Figure 9b, the transition is reachable to the transition in the execution of , since the events and satisfy ∧∧.
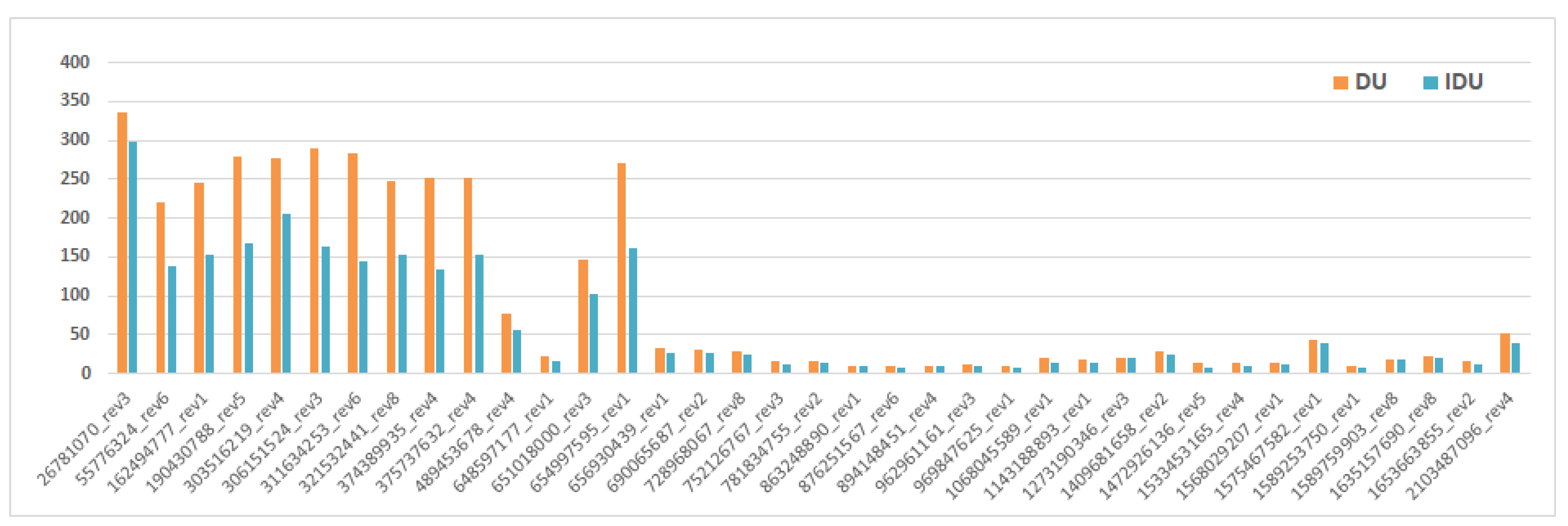
7. Experiments and Results
7.1. Data Collections and Tool
7.2. Implementation and Results
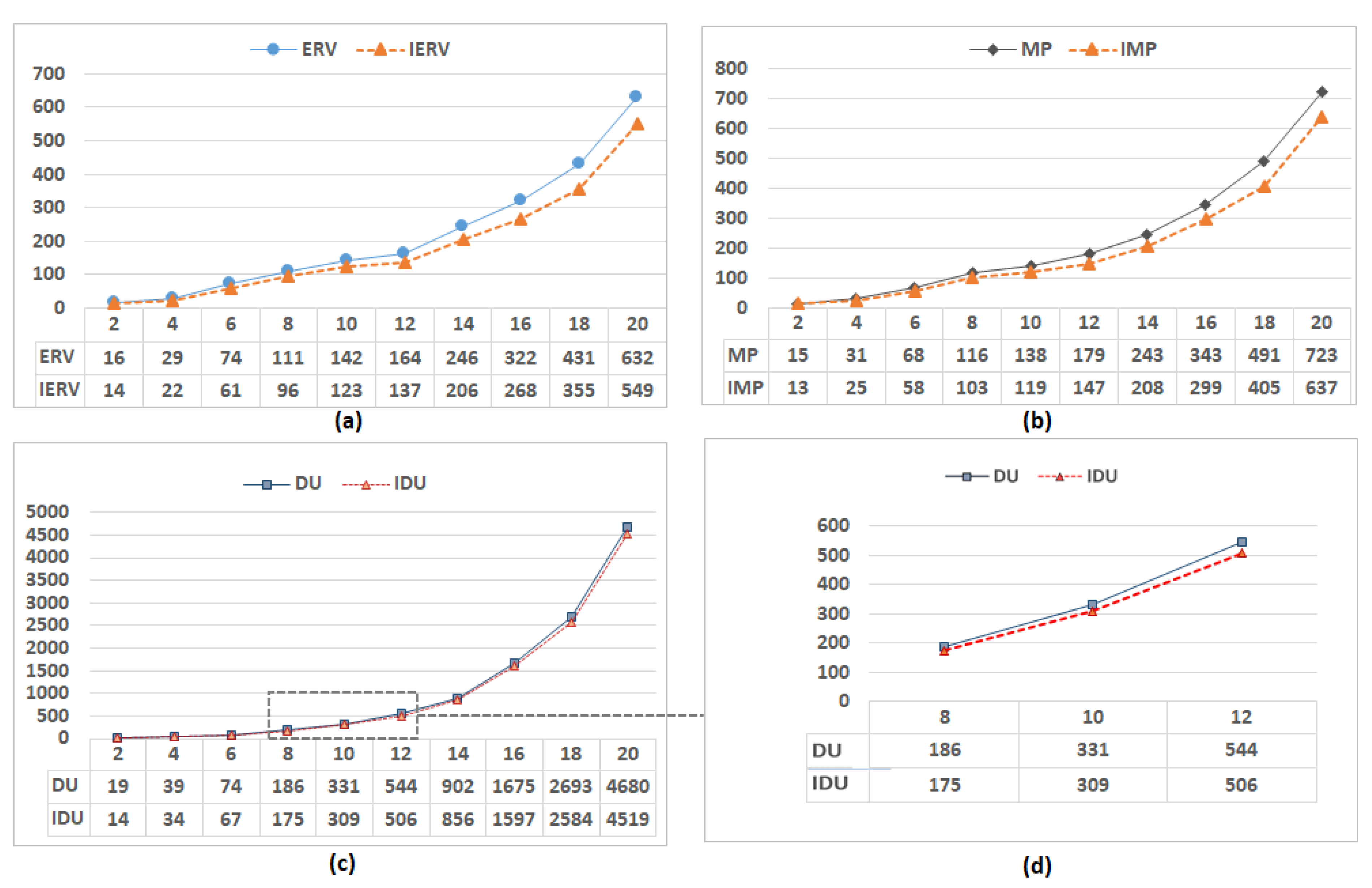
- (1)
- The experiments on BPM_AIM
- (2)
- The experiments on Dining Philosophers
8. Conclusions
- (1)
- we apply our new calculations with heuristic functions into many more model checkings of concurrent systems;
- (2)
- timed concurrent systems are simulated and analyzed based on the unfolding techniques of Petri nets; and,
- (3)
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Moutinho, F.; Gomes, L. Asynchronous-channels within Petri net-based GALS distributed embedded systems modeling. IEEE Trans. Ind. Inform. 2014, 10, 2024–2033. [Google Scholar] [CrossRef]
- Zhou, M.C.; Wu, N. System Modeling and Control with Resource-Oriented Petri Nets; CRC Press, Inc.: Boca Raton, FL, USA, 2009. [Google Scholar]
- Qi, L.; Zhou, M.; Luan, W. A two-level traffic light control strategy for preventing incident-based urban traffic congestion. IEEE Trans. Intell. Transp. Syst. 2016, 19, 13–24. [Google Scholar] [CrossRef]
- Esparza, J.; Schröter, C. Unfolding based algorithms for the reachability problem. Fundam. Inform. 2001, 47, 231–245. [Google Scholar]
- Liu, G.; Reisig, W.; Jiang, C. A Branching-process-based method to check soundness of workflow systems. IEEE Access 2016, 4, 4104–4118. [Google Scholar] [CrossRef]
- Liu, M.; Wang, S.; Zhou, M.; Liu, D.; Al-Ahmari, A.; Qu, T.; Wu, N.; Li, Z. Deadlock and liveness characterization for a class of generalized Petri nets. Inf. Sci. 2017, 420, 403–416. [Google Scholar] [CrossRef]
- Franco, A.; Baldan, P. True Concurrency and Atomicity: A Model Checking Approach with Contextual Petri Nets; LAP LAMBERT Academic Publishing: Saarbrucken, Germany, 2015. [Google Scholar]
- McMillan, K.L. Using unfoldings to avoid the state explosion problem in the verification of asynchronous circuits. In Computer Aided Verification; Springer: Berlin/Heidelberg, Germany, 1992; pp. 164–177. [Google Scholar]
- Buchholz, P.; Kemper, P. Hierarchical Reachability Graph Generation for Petri Nets. Form. Methods Syst. Des. 2002, 21, 281–315. [Google Scholar] [CrossRef]
- Wisniewski, R.; Karatkevich, A.; Adamski, M.; Costa, A.; Gomes, L. Prototyping of Concurrent Control Systems with Application of Petri Nets and Comparability Graphs. IEEE Trans. Control Syst. Technol. 2017, 26, 575–586. [Google Scholar] [CrossRef]
- Wiśniewski, R.; Wiśniewska, M.; Jarnut, M. C-exact hypergraphs in concurrency and sequentiality analyses of cyber-physical systems specified by safe Petri nets. IEEE Access 2019, 7, 13510–13522. [Google Scholar] [CrossRef]
- Bonet, B.; Haslum, P.; Khomenko, V.; Thiébaux, S.; Vogler, W. Recent advances in unfolding technique. Theor. Comput. Sci. 2014, 551, 84–101. [Google Scholar] [CrossRef]
- Esparza, J.; Römer, S.; Vogler, W. An improvement of McMillan’s unfolding algorithm. Form. Methods Syst. Des. 2002, 20, 285–310. [Google Scholar] [CrossRef]
- Khomenko, V.; Kondratyev, A.; Koutny, M.; Vogler, W. Merged processes: A new condensed representation of Petri net behaviour. Acta Inform. 2006, 43, 307–330. [Google Scholar] [CrossRef]
- Bonet, B.; Haslum, P.; Hickmott, S.; Thiébaux, S. Directed unfolding of petri nets. In Transactions on Petri Nets and Other Models of Concurrency I; Springer: Berlin/Heidelberg, Germany, 2008; pp. 172–198. [Google Scholar]
- Haar, S. Types of asynchronous diagnosability and the reveals-relation in occurrence nets. IEEE Trans. Autom. Control 2010, 55, 2310–2320. [Google Scholar] [CrossRef][Green Version]
- Hickmott, S.L.; Rintanen, J.; Thiébaux, S.; White, L.B. Planning via Petri Net Unfolding. In Proceedings of the International Joint Conference on Artificial Intelligence, Hyderabad, India, 6–12 January 2007; Volume 7, pp. 1904–1911. [Google Scholar]
- Leon, H.P.d.; Saarikivi, O.; Kahkonen, K.; Heljanko, K.; Esparza, J. Unfolding Based Minimal Test Suites for Testing Multithreaded Programs. In Proceedings of the 15th International Conference on Application of Concurrency to System Design, Brussels, Belgium, 21–26 June 2015; pp. 40–49. [Google Scholar]
- Heljanko, K.; Khomenko, V.; Koutny, M. Parallelisation of the Petri net unfolding algorithm. In Proceedings of the 8th International Conference on Tools and Algorithms for Construction and Analysis of Systems (TACAS), LNCS, Grenoble, France, 8–12 April 2002; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2280, pp. 371–385. [Google Scholar]
- Khomenko, V.; Mokhov, A. An algorithm for direct construction of complete merged processes. In Proceedings of the International Conference on Application and Theory of Petri Nets and Concurrency, Paris, France, 24–25 June 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 89–108. [Google Scholar]
- Couvreur, J.M.; Poitrenaud, D.; Weil, P. Branching processes of general Petri nets. Fundam. Inform. 2013, 122, 31–58. [Google Scholar] [CrossRef]
- Rodríguez, C.; Sousa, M.; Sharma, S.; Kroening, D. Unfolding-based Partial Order Reduction. In Proceedings of the 26th International Conference on Concurrency Theory (CONCUR 2015), Schloss Dagstuhl-Leibniz-Zentrum fuer Informatik, Madrid, Spain, 1–4 September 2015. [Google Scholar]
- Chatain, T.; Paulevé, L. Goal-Driven Unfolding of Petri Nets. In Proceedings of the 28th International Conference on Concurrency Theory (CONCUR 2017), Berlin, Germany, 5–8 September 2017. [Google Scholar]
- Lu, F.; Tao, R.; Du, Y.; Zeng, Q.; Bao, Y. Deadlock detection-oriented unfolding of unbounded Petri nets. Inf. Sci. 2019, 497, 1–22. [Google Scholar] [CrossRef]
- Jiroveanu, G.; Boel, R.K.; Schutter, B.D. Fault Diagnosis for Time Petri Nets. In Proceedings of the International Workshop on Discrete Event Systems, Ann Arbor, MI, USA, 10–12 July 2006. [Google Scholar]
- Chatain, T.; Fabre, E. Factorization Properties of Symbolic Unfoldings of Colored Petri Nets. In Proceedings of the International Conference on Applications & Theory of Petri Nets, Braga, Portugal, 21–25 June 2010. [Google Scholar]
- Rodriguez, C.; Schwoon, S.; Baldan, P. Efficient Contextual Unfolding. In Proceedings of the International Conference on Concurrency Theory, Aachen, Germany, 6–9 September 2011. [Google Scholar]
- Lomazova, I.A.; Ermakova, V.O. Verication of Nested Petri Nets Using an Unfolding Approach. In Proceedings of the International Workshop on Petri Nets & Software Engineering, Torun, Poland, 20–21 June 2016. [Google Scholar]
- Khomenko, V.; Koutny, M. LP deadlock checking using partial order dependencies. In Proceedings of the International Conference on Concurrency Theory, State College, PA, USA, 22–25 August 2000; Springer: Berlin/Heidelberg, Germany, 2000; pp. 410–425. [Google Scholar]
- Rodriguez, C.; Schwoon, S. Verification of Petri nets with read arcs. In Proceedings of the International Conference on Concurrency Theory, Newcastle, UK, 4–7 September 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 471–485. [Google Scholar]
- De León, H.P.; Haar, S.; Longuet, D. Model-based testing for concurrent systems: Unfolding-based test selection. Int. J. Softw. Tools Technol. Transf. 2016, 18, 305–318. [Google Scholar] [CrossRef]
- Jezequel, L.; Madalinski, A.; Schwoon, S. Distributed computation of vector clocks in Petri nets unfolding for test selection. In Proceedings of the Workshop on Discrete Event Systems (WODES), Sorrento Coast, Italy, 30 May–1 June 2018. [Google Scholar]
- Kähkönen, K.; Saarikivi, O.; Heljanko, K. Using unfoldings in automated testing of multithreaded programs. In Proceedings of the 27th IEEE/ACM International Conference on Automated Software Engineering, Essen, Germany, 3–7 September 2012; pp. 150–159. [Google Scholar]
- Saarikivi, O.; Ponce-De-León, H.; Kähkönen, K.; Heljanko, K.; Esparza, J. Minimizing test suites with unfoldings of multithreaded programs. ACM Trans. Embed. Comput. Syst. (TECS) 2017, 16, 45. [Google Scholar] [CrossRef]
- Lutz-Ley, A.; López-Mellado, E. Stability Analysis of Discrete Event Systems Modeled by Petri Nets Using Unfoldings. IEEE Trans. Autom. Sci. Eng. 2018, 15, 1964–1971. [Google Scholar] [CrossRef]
- Meyer, R.; Khomenko, V.; Strazny, T. A practical approach to verification of mobile systems using net unfoldings. Fundam. Inform. 2009, 94, 439–471. [Google Scholar] [CrossRef]
- Ponce-de León, H.; Rodríguez, C.; Carmona, J.; Heljanko, K.; Haar, S. Unfolding-based process discovery. In Proceedings of the International Symposium on Automated Technology for Verification and Analysis, Shanghai, China, 12–15 October 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 31–47. [Google Scholar]
- Weidlich, M.; Elliger, F.; Weske, M. Generalised computation of behavioural profiles based on petri-net unfoldings. In Proceedings of the International Workshop on Web Services and Formal Methods, Hoboken, NJ, USA, 16–17 September 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 101–115. [Google Scholar]
- Xiang, D.; Liu, G.; Yan, C.; Jiang, C. Detecting data inconsistency based on the unfolding technique of petri nets. IEEE Trans. Ind. Inform. 2017, 13, 2995–3005. [Google Scholar] [CrossRef]
- Römer, S. Theorie und Praxis der Netzentfaltungen als Grundlage Für die Verifikation Nebenläufiger Systeme. Ph.D. Thesis, Technical University, Munich, Germany, 2000. [Google Scholar]
- Dong, L.; Liu, G.; Xiang, D. Verifying CTL with Unfoldings of Petri Nets. In Proceedings of the International Conference on Algorithms and Architectures for Parallel Processing, Melbourne, Australia, 9–11 September 2018; Springer: Berlin/Heidelberg, Germany, 2018; pp. 47–61. [Google Scholar]
- Liu, C.; Zeng, Q.; Duan, H.; Wang, L.; Tan, J.; Ren, C.; Yu, W. Petri net based data-flow error detection and correction strategy for business processes. IEEE Access 2020, 8, 43265–43276. [Google Scholar] [CrossRef]
- Liu, G.; Jiang, C.; Zhou, M. Process nets with channels. IEEE Trans. Syst. Man Cybern. Part A Syst. Hum. 2012, 42, 213–225. [Google Scholar] [CrossRef]
- Wynn, M.T. Soundness of workflow nets: Classification, decidability, and analysis. Form. Asp. Comput. 2011, 23, 333–363. [Google Scholar]
- Guo, X.; Wang, S.; You, D.; Li, Z.; Jiang, X. A siphon-based deadlock prevention strategy for S 3 PR. IEEE Access 2019, 7, 86863–86873. [Google Scholar] [CrossRef]
- Zhou, M.C.; Fanti, M.P. Deadlock Resolution in Computer-Integrated Systems; CRC Press, Inc.: Boca Raton, FL, USA, 2004. [Google Scholar]
- Hillah, L.M.; Kordon, F.; Petrucci, L.; Treves, N. PNML Framework: An extendable reference implementation of the Petri Net Markup Language. In Proceedings of the International Conference on Applications and Theory of Petri Nets, Braga, Portugal, 21–25 June 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 318–327. [Google Scholar]
- Xiang, D.; Liu, G.; Yan, C.G.; Jiang, C. A Guard-driven Analysis Approach of Workflow Net With Data. IEEE Trans. Serv. Comput. 2019, 1. [Google Scholar] [CrossRef]
- Kim, K.H.; Yavuz-Kahveci, T.; Sanders, B.A. JRF-E: Using model checking to give advice on eliminating memory model-related bugs. Autom. Softw. Eng. 2012, 19, 491–530. [Google Scholar] [CrossRef]
- Xiang, D.; Liu, G.; Yan, C.; Jiang, C. Detecting data-flow errors based on Petri nets with data operations. IEEE/CAA J. Autom. Sin. 2017, 5, 251–260. [Google Scholar] [CrossRef]
- Zhang, M.; Wu, Y.; Shan, L.U.; Qi, S.; Ren, J.; Zheng, W. A Lightweight System for Detecting and Tolerating Concurrency Bugs. IEEE Trans. Softw. Eng. 2016, 42, 899–917. [Google Scholar] [CrossRef]





| Transition | Activity | Transition | Activity |
|---|---|---|---|
| Verify reservations | Receive baggages and print receipts | ||
| Choose/change seats | – | ||
| Handle incorrect reservations | Print boarding cards | ||
| – | Give travel documents to passengers |
| Events | Contexts | |||
|---|---|---|---|---|
| Local Configurations () | Pre-Sets () | Post-Sets () | Cuts () | |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Xiang, D.; Tao, X.; Liu, Y. An Incremental and Backward-Conflict Guided Method for Unfolding Petri Nets. Symmetry 2021, 13, 392. https://doi.org/10.3390/sym13030392
Xiang D, Tao X, Liu Y. An Incremental and Backward-Conflict Guided Method for Unfolding Petri Nets. Symmetry. 2021; 13(3):392. https://doi.org/10.3390/sym13030392
Chicago/Turabian StyleXiang, Dongming, Xiaoyan Tao, and Yaping Liu. 2021. "An Incremental and Backward-Conflict Guided Method for Unfolding Petri Nets" Symmetry 13, no. 3: 392. https://doi.org/10.3390/sym13030392
APA StyleXiang, D., Tao, X., & Liu, Y. (2021). An Incremental and Backward-Conflict Guided Method for Unfolding Petri Nets. Symmetry, 13(3), 392. https://doi.org/10.3390/sym13030392





