Securing Fingerprint Template Using Blockchain and Distributed Storage System
Abstract
1. Introduction
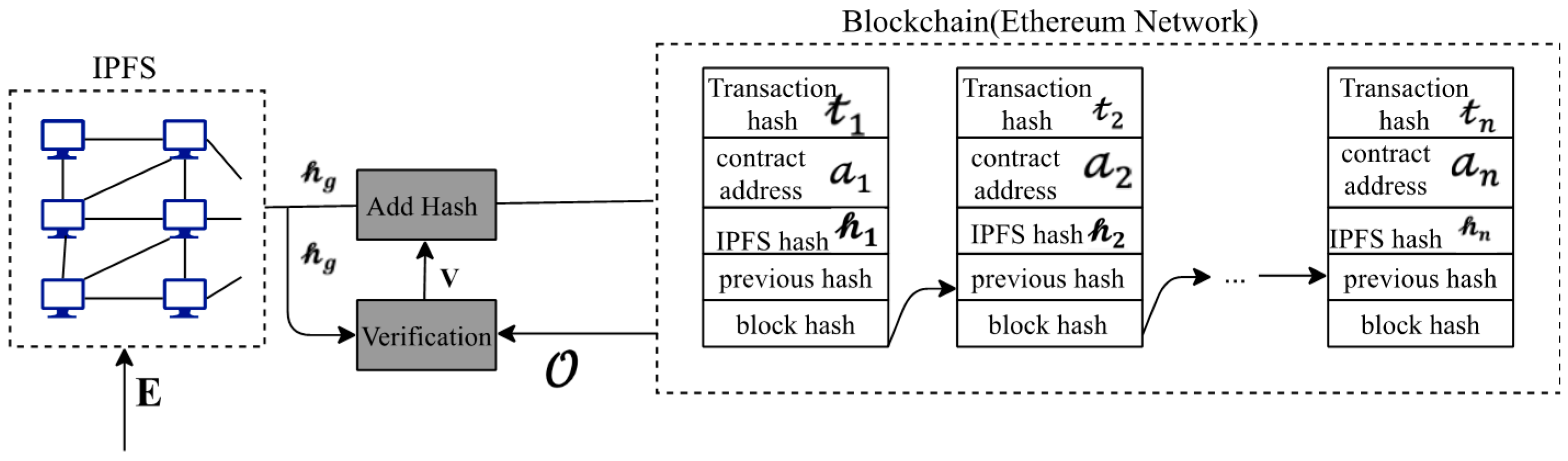
- A merge of Ethereum and IPFS architecture proposal for decentralized fingerprint storage.
- By using data hashing, the system becomes cost-effective and efficient.
- Vulnerabilities from distributing templates on IPFS is tackled by encryption.
2. Background
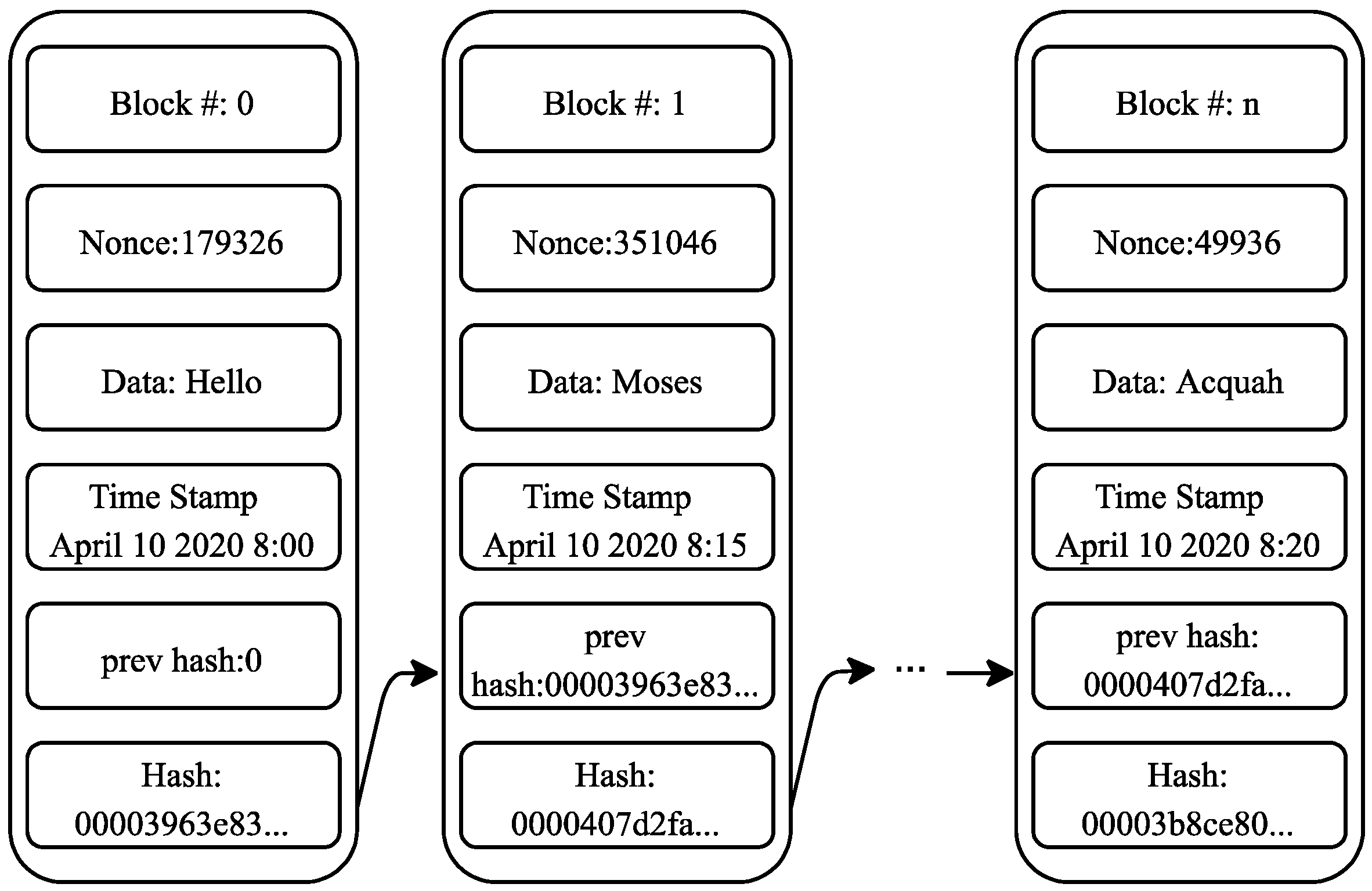
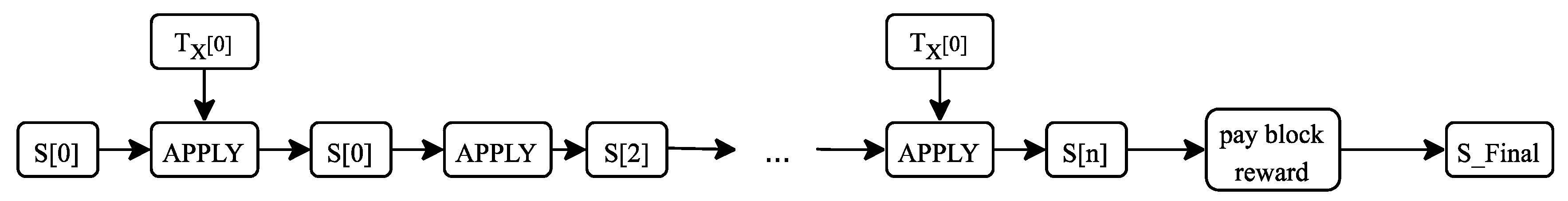
2.1. Blockchain Technology
2.2. The Inter-Planetary File System (IPFS)
3. Related Works
3.1. Blockchain in Biometrics
3.2. Blockchain in Content Protection
- Dipti’s side chain is centralized, and our system is distributed.
- Dipti’s fingerprint and Aadhar number are not encrypted, while the proposed system secures data using the AES algorithm.
- The cost that is involved in implementing the system is high in Dipti’s because the raw fingerprint vector is stored on the blockchain. In contrast, our system is cheaper by using only the IPFS hash.
- Our system is scalable and efficient because of the size of the hash, while Dipti’s system stores extensive data in the form of a fingerprint vector on the blockchain.
4. Proposed Architecture
| Algorithm 1 Generate user data from E. |
| Input: The AES encrypted template E. Output: The returned user data . 1. for uploading E to Ethereum network do 2. Convert E to buffer. 3. Upload buffer to IPFS. 4. The IPFS returns . 5. Write to smart contract assigned a 6. Check for the status of the transaction. 7. if transaction successful = true then 8. return . 9. else. 10. show error. 11. end 12. end |
| Algorithm 2 authenticate user data |
| Input: Generated user data . Hash values in the block chain: Output: Verification decision V. 1. for 2. if 3. set V = 0 4. show already in the system 5. return 6. end 7. end 8. set V = 1 9. add new to the system. |
4.1. Authenticate User Data
4.2. Fingerprint Feature Extraction Methods
- Minutiae-based matching: this is the most popular technique used by most researchers. This method uses minutia extracted from two fingerprints and are compared. Different approaches on how the minutia are extracted and compared. Some by using bifurcation method (BM) [11], enhancing fingerprint image and using crossing number method (MA) [10], and recognition using both local and global structures (MP) [9].
- Texture classification: basic fingerprint patterns are matched with other stored templates. This mostly uses the central point of the fingerprint and aligned with different templates. They use the discrete wavelet method (DWT) in [12] to attain a smaller vector size template. We also acquired the vector template from using the Fingercode approach by the authors in [26]. This vector template has a template vector size of 640 by using eight Gabor filters and 80 sectors. In a recent study conducted by authors in [27], we discovered the vector size of the algorithm to be large because it proposes using Fingercode, phase-only correlation, VeriFinger, and NBIS.
4.3. Design and Implementation
- GasPrice: the amount of wei the sender is willing to pay per unit of the gas required to execute the transaction.
- GasLimit: The maximum amount of gas the sender is willing to pay for executing this transaction is set before any computation is done.
- Data: the input data (fingerprint template) of the message call.
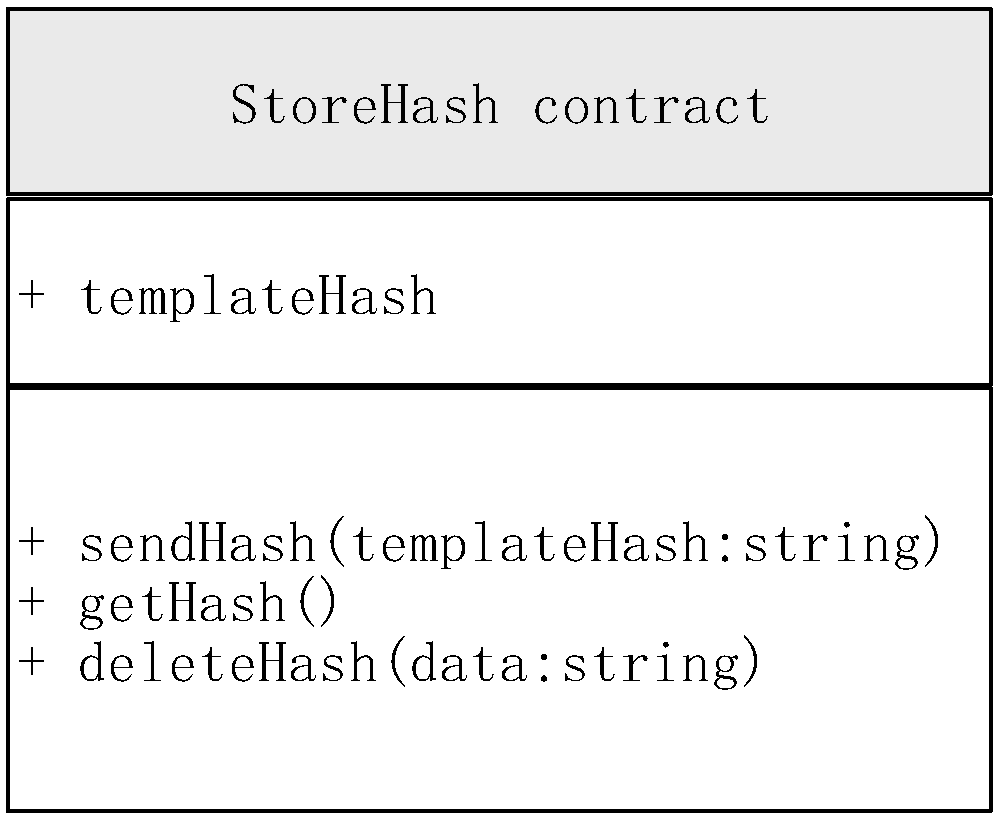
- sendHash: the owner executes this function. An event is triggered to upload the Hash of the template, and it is stored on the smart contract.
- getHash (The cost only applies when called by the storeHash smart contract): returns the template hash stored on the Ethereum contract. This hash begins with “QmY…” depending on the template, so it is identifiable whenever returned.
- deleteHash: this function is executed to delete the stored hash on the Ethereum network.
5. Results and Discussion
5.1. Parameter Setup
- Node.js: Node.js is a JavaScript run-time setting which incorporates everything needed to program in JavaScript
- Ganache: Ganache is a closed personal blockchain with ten accounts loaded with 100ETH each that allows smart contracts to communicate.
- Metamask: Metamask is a browser extension that makes it easier for DApps to run in your browser and interact with the Ethereum network.
- The remix compiler: this is an open-source tool for writing, compiling, debugging, and deploying smart contracts connected to metamask using web3.js.
- Solidity: a programming language for smart contracts.
- Bootstrap and JavaScript: for creating a front-end GUI.
- Local IPFS: setup a local IPFS node on using ipfs daemon on the run-time environment.
5.2. Performance Metric
5.3. Security Analysis of the Improved System
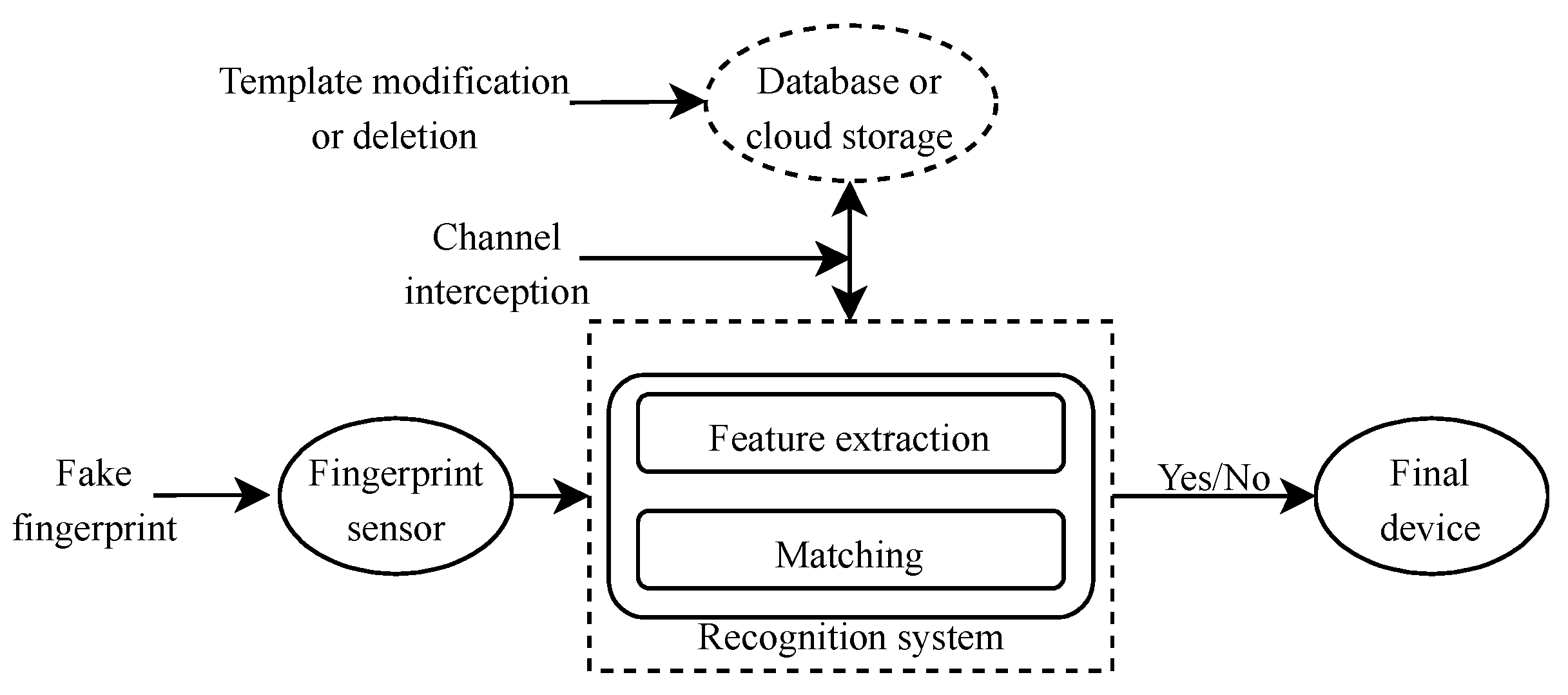
- Template database attack
- Upload of fake template
- Channel interception
5.4. Comparison of with Dipti’s System
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix A
Appendix B
References
- Makhdoom, I.; Abolhasan, M.; Abbas, H.; Ni, W. Blockchain’s adoption in IoT: The challenges, and a way forward. J. Netw. Comput. Appl. 2019, 125, 251–279. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System; 2008; Available online: https://bitcoin.org/bitcoin.pdf (accessed on 1 June 2020).
- Yli-Huumo, J.; Ko, D.; Choi, S.; Park, S.; Smolander, K. Where is current research on blockchain technology?—A systematic review. PLoS ONE 2016, 11, e0163477. [Google Scholar] [CrossRef] [PubMed]
- Roberts, C. Biometric attack vectors and defences. Comput. Secur. 2007, 26, 14–25. [Google Scholar] [CrossRef]
- Páez, R.; Pérez, M.; Ramírez, G.; Montes, J.; Bouvarel, L. An Architecture for Biometric Electronic Identification Document System Based on Blockchain. Future Internet 2020, 12, 10. [Google Scholar] [CrossRef]
- Nimje, R.; Bhalerao, D. Blockchain Based Electronic Voting System Using Biometric. In Proceedings of the International Conference on Sustainable Communication Networks and Application, Erode, India, 30–31 July 2019; pp. 746–754. [Google Scholar]
- Pawade, D.; Sakhapara, A.; Badgujar, A.; Adepu, D.; Andrade, M. Secure Online Voting System Using Biometric and Blockchain. In Data Management, Analytics and Innovation; Springer: Berlin/Heidelberg, Germany, 2020; pp. 93–110. [Google Scholar]
- Odelu, V. IMBUA: Identity Management on Blockchain for Biometrics-Based User Authentication. In Proceedings of the International Congress on Blockchain and Applications, Ávila, Spain, 26–28 June 2019; pp. 1–10. [Google Scholar]
- Jiang, X.; Yau, W.-Y. Fingerprint minutiae matching based on the local and global structures. In Proceedings of the 15th international conference on pattern recognition. ICPR-2000, Barcelona, Spain, 3–7 September 2000; pp. 1038–1041. [Google Scholar]
- Khan, M.A. Fingerprint Image Enhancement and Minutiae Extraction; Cornell University: New York, NY, USA, 2011. [Google Scholar]
- Kumar, L.R.; Kumar, S.S.; Prasad, J.R.; Rao, B.S.; Prakash, P.R. Fingerprint minutia match using bifurcation technique. Int. J. Comput. Sci. Commun. Netw. 2012, 2, 478–486. [Google Scholar]
- Thaiyalnayaki, K.; Karim, S.S.A.; Parmar, P.V. Finger print recognition using discrete wavelet transform. Int. J. Comput. Appl. 2010, 1, 96–100. [Google Scholar]
- Pawade, D.; Sakhapara, A.; Andrade, M.; Badgujar, A.; Adepu, D. Implementation of Fingerprint-Based Authentication System Using Blockchain. In Soft Computing and Signal Processing; Springer: Berlin/Heidelberg, Germany, 2019; pp. 233–242. [Google Scholar]
- Benet, J. IPFS-Content Addressed, Versioned, P2P File System. Whitepaper. 2014. Available online: https://www.researchgate.net/publication/263930348_IPFS_-_Content_Addressed_Versioned_P2P_File_System (accessed on 1 January 2020).
- Delgado-Mohatar, O.; Fierrez, J.; Tolosana, R.; Vera-Rodriguez, R. Biometric Template Storage with Blockchain: A First Look into Cost and Performance Tradeoffs. In Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition Workshops (CVPRW), Long Beach, CA, USA, 16–20 June 2019; pp. 2829–2837. [Google Scholar]
- Christidis, K.; Devetsikiotis, M. Blockchains and smart contracts for the internet of things. IEEE Access 2016, 4, 2292–2303. [Google Scholar] [CrossRef]
- Mohsin, A.; Zaidan, A.; Zaidan, B.; Albahri, O.; Albahri, A.; Alsalem, M.; Mohammed, K. Blockchain authentication of network applications: Taxonomy, classification, capabilities, open challenges, motivations, recommendations and future directions. Comput. Stand. Interfaces 2019, 64, 41–60. [Google Scholar] [CrossRef]
- Buterin, V. Ethereum white paper. Github Repos. 2013, 1, 22–23. [Google Scholar]
- Dannen, C. Introducing Ethereum and Solidity; Springer: Berlin/Heidelberg, Germany, 2017; Volume 1. [Google Scholar]
- Buterin, V.; Griffith, V. Casper the friendly finality gadget. arXiv 2017, arXiv:1710.09437. [Google Scholar]
- Nizamuddin, N.; Salah, K.; Azad, M.A.; Arshad, J.; Rehman, M. Decentralized document version control using ethereum blockchain and IPFS. Comput. Electr. Eng. 2019, 76, 183–197. [Google Scholar] [CrossRef]
- Lee, S.H.; Yang, C.S. Fingernail analysis management system using microscopy sensor and blockchain technology. Int. J. Distrib. Sens. Netw. 2018, 14, 1550147718767044. [Google Scholar] [CrossRef]
- Mohsin, A.; Zaidan, A.; Zaidan, B.; Albahri, O.; Albahri, A.; Alsalem, M.; Mohammed, K. Based Blockchain-PSO-AES techniques in finger vein biometrics: A novel verification secure framework for patient authentication. Comput. Stand. Interfaces 2019, 66, 103343. [Google Scholar] [CrossRef]
- Nyaletey, E.; Parizi, R.M.; Zhang, Q.; Choo, K.-K.R. BlockIPFS-Blockchain-enabled Interplanetary File System for Forensic and Trusted Data Traceability. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July; pp. 18–25.
- Hasan, S.S.; Sultan, N.H.; Barbhuiya, F.A. Cloud Data Provenance using IPFS and Blockchain Technology. In Proceedings of the Seventh International Workshop on Security in Cloud Computing, Auckland, New Zealand, 7–12 July 2019; pp. 5–12. [Google Scholar]
- Jain, A.K.; Prabhakar, S.; Hong, L.; Pankanti, S. Filterbank-based fingerprint matching. IEEE Trans. Image Process. 2000, 9, 846–859. [Google Scholar] [CrossRef] [PubMed]
- Kauba, C.; Uhl, A. Fingerprint recognition under the influence of image sensor ageing. IET Biom. 2017, 6, 245–255. [Google Scholar] [CrossRef]
| Blockchain | Traditional Database | |
|---|---|---|
| Architecture | Every node on the network has a copy of transactions, so with every change that occurs, there will be discrepancies. | Records secured on databases are centralized and risk of attacks. |
| Authority | Using smart contracts and consensus algorithms, nodes on the network are made to trust each other. | The use of a database administrator (DBA) eliminates trusts with participating parties because the DBA controls data and can modify or delete data. |
| Security | No single point of failure. | The database is prone to malicious attacks since its centralized. |
| Environment | Parameters |
|---|---|
| System | Intel Core i5 CPU @2.7 GHz |
| 8 GBRAM | |
| 128 HDD | |
| OSX Catalina | |
| Blockchain | Ganache |
| Metamask | |
| Remix compiler | |
| Solidity 0.6.1 | |
| Node.js 13.5.0 | |
| Web3.js | |
| Bootstrap 3.3.7 | |
| IPFS | Local IPFS |
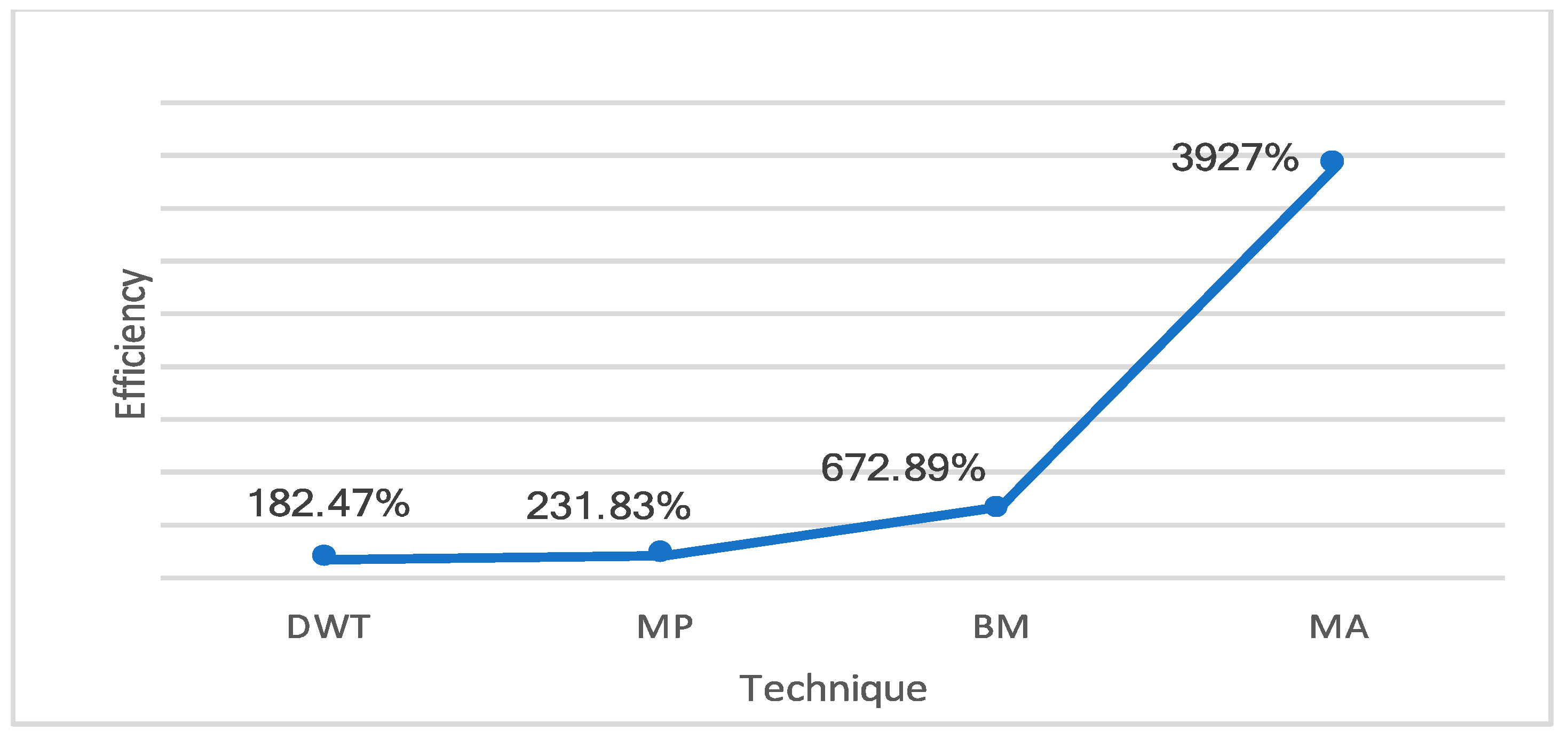
| Technique | Efficiency |
|---|---|
| DWT | 182.47% |
| MP | 231.83% |
| BM | 672.89% |
| MA | 3927% |
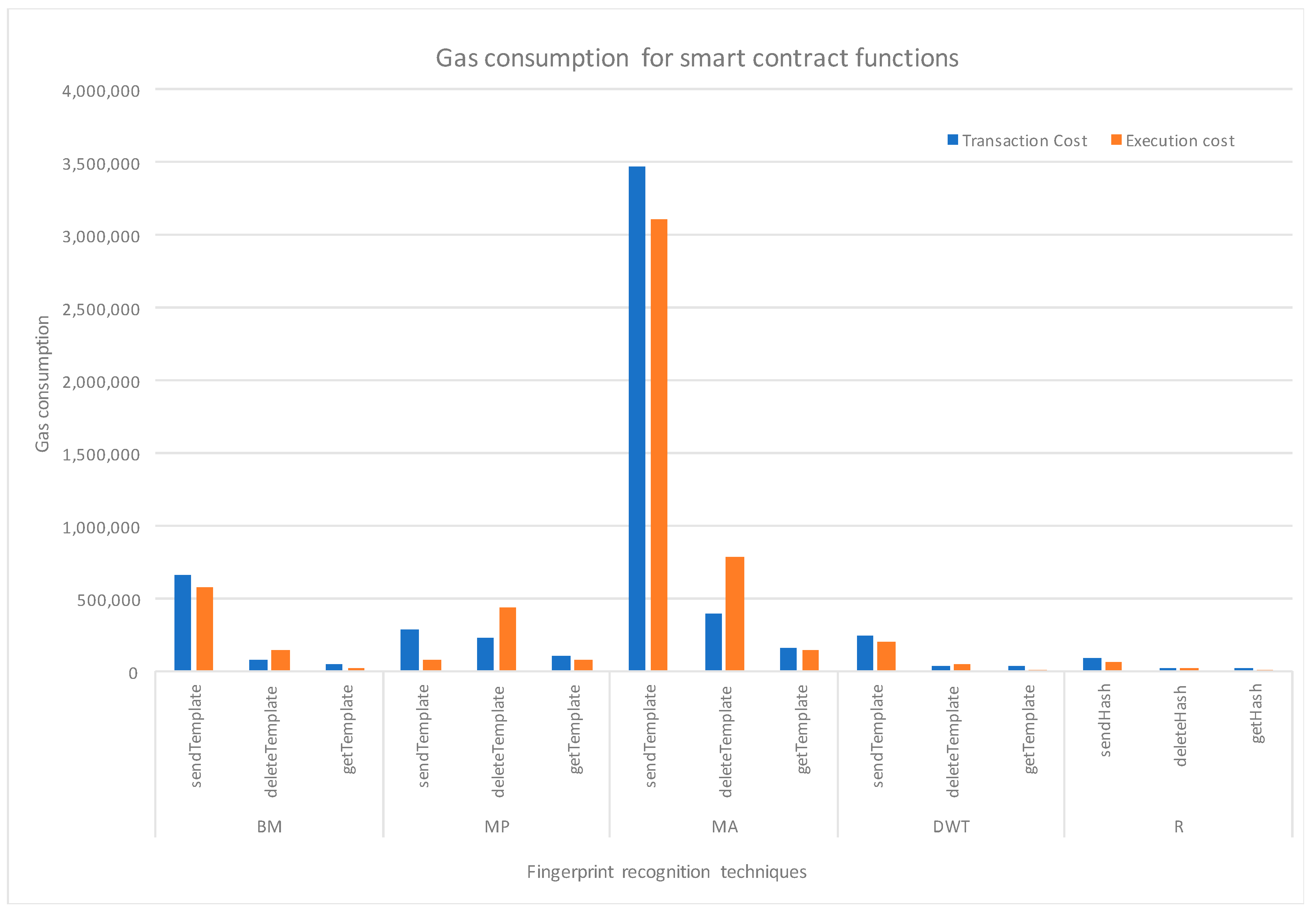
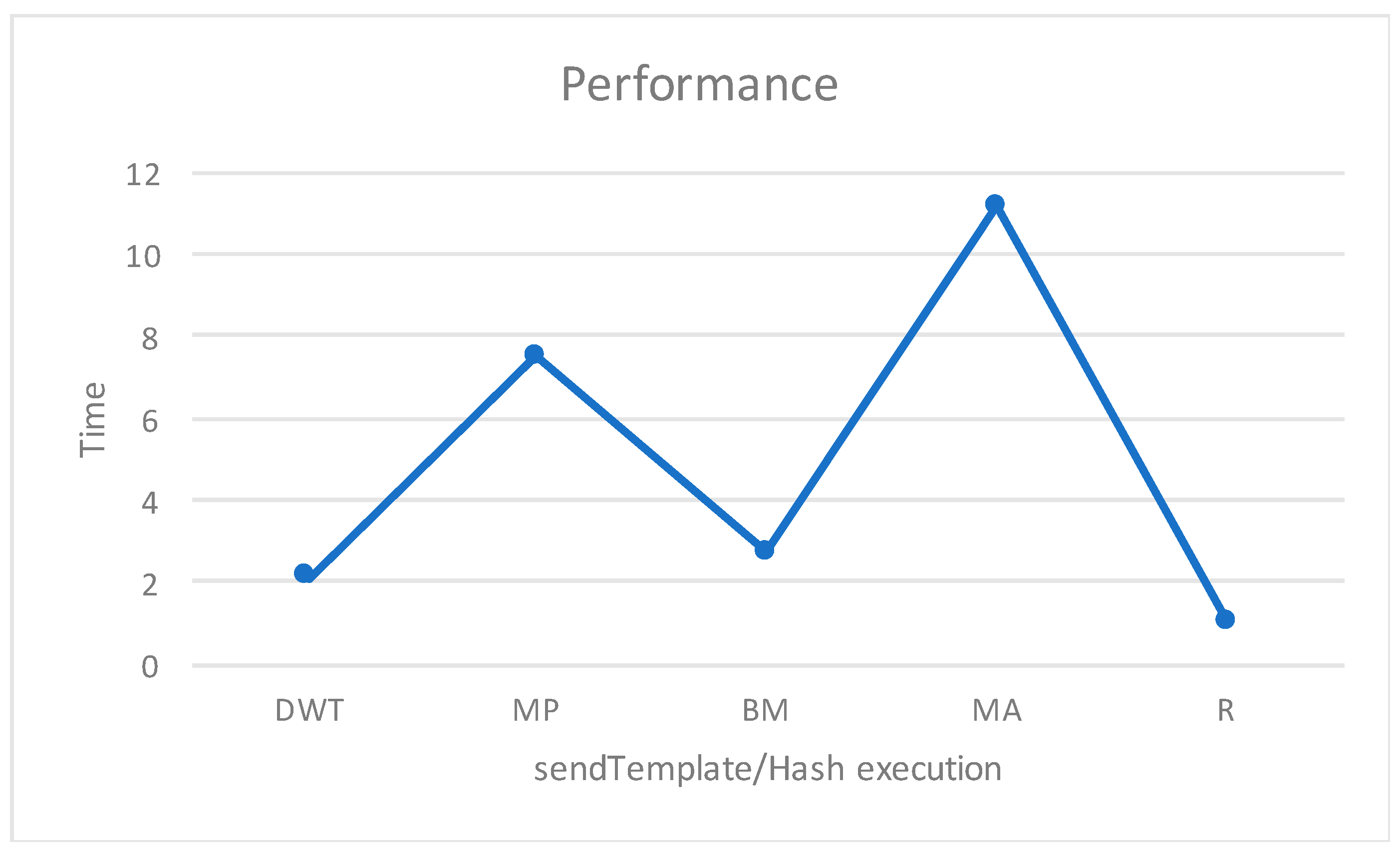
| Fingerprint Templates | Contract Functions | Transaction Cost | Execution Cost | Execution Time (Average) | |
|---|---|---|---|---|---|
| Features | Method of Template Acquisition | ||||
| Minutia based | BM | sendTemplate | 665,608 ($2.63582) | 583,664 ($2.31131) | 2.69 s |
| deleteTemplate | 84,820 ($0.33589) | 148,048 ($0.58628) | 1.98 s | ||
| getTemplate | 49,776 ($0.19711) | 28,504 ($0.11288) | 1.45 s | ||
| MP | sendTemplate | 285,774 ($1.13167) | 77,686 ($0.30763) | 7.5 s | |
| deleteTemplate | 231,473 ($0.91664) | 441,354 ($1.74777) | 5.60 s | ||
| getTemplate | 103,829 ($0.41117) | 82,557 ($0.32692) | 5.33 s | ||
| MA | sendTemplate | 3,468,447 ($13.73504) | 3,113,287 ($12.32861) | 11.13 s | |
| deleteTemplate | 403,411 ($1.5975) | 785,230 ($3.10951) | 9.85 s | ||
| getTemplate | 167,268 ($0.66239) | 145,996 ($0.57814) | 11.38 s | ||
| Texture features | DWT | sendTemplate | 243,266 ($0.96333) | 202,218 ($0.80079) | 2.08 s |
| deleteTemplate | 367,79 ($0.14565) | 51,965 ($0.20578) | 1.45 s | ||
| getTemplate | 32,081 ($0.12704) | 10,809 ($0.04281) | 1.40 s | ||
| Hashing of features | Hashing of DWT | sendHash | 86,119 ($0.34104) | 61,863 ($0.24499) | 1 s |
| deleteHash | 18,468 ($0.07314) | 16,743 ($0.06631) | 1 s | ||
| getHash | 25,552 ($0.10118) | 4280 ($0.01695) | 1 s | ||
| smart-contract creation | 338,033 ($1.33862) | 1 s | |||
| Dipti’s System | ||
|---|---|---|
| Setup | Side-chain | Distributed with IPFS |
| Encryption | No encryption of user data | User template is encrypted with AES E |
| Cost | Expensive from storing fingerprint features directly on the main chain | Cheaper by just storing |
| Scalability & efficiency | Large files in the form fingerprint vector and user data increase the size of the system and become less efficient | Only using makes the system efficient |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Acquah, M.A.; Chen, N.; Pan, J.-S.; Yang, H.-M.; Yan, B. Securing Fingerprint Template Using Blockchain and Distributed Storage System. Symmetry 2020, 12, 951. https://doi.org/10.3390/sym12060951
Acquah MA, Chen N, Pan J-S, Yang H-M, Yan B. Securing Fingerprint Template Using Blockchain and Distributed Storage System. Symmetry. 2020; 12(6):951. https://doi.org/10.3390/sym12060951
Chicago/Turabian StyleAcquah, Moses Arhinful, Na Chen, Jeng-Shyang Pan, Hong-Mei Yang, and Bin Yan. 2020. "Securing Fingerprint Template Using Blockchain and Distributed Storage System" Symmetry 12, no. 6: 951. https://doi.org/10.3390/sym12060951
APA StyleAcquah, M. A., Chen, N., Pan, J.-S., Yang, H.-M., & Yan, B. (2020). Securing Fingerprint Template Using Blockchain and Distributed Storage System. Symmetry, 12(6), 951. https://doi.org/10.3390/sym12060951







