1. Introduction
Wireless mobile sensor networks are applied in multiple areas, such as rescue, exploration, visitation and reconnaissance. It has been widely concerned by scholars that intelligent agents, such as networked sensor or robots, can replace human beings to perform tasks in dangerous scenes [
1,
2]. Maintaining connectivity [
3,
4] and covering the field of interest [
5,
6] act as important supports and prerequisites for the multi-agent system (MAS) to perform a task. Therefore, to simultaneously build up a communications network with fault tolerance and a network widely covering the field of interest is an urgent problem in the research on multi-agent collaboration. In particular, networked agent nodes are often equipped with low-cost devices, as well as limited communications and energy resources. How to make these nodes move autonomously to optimize the topological structure of the system and reduce the moving energy consumption as much as possible still remains to be further studied.
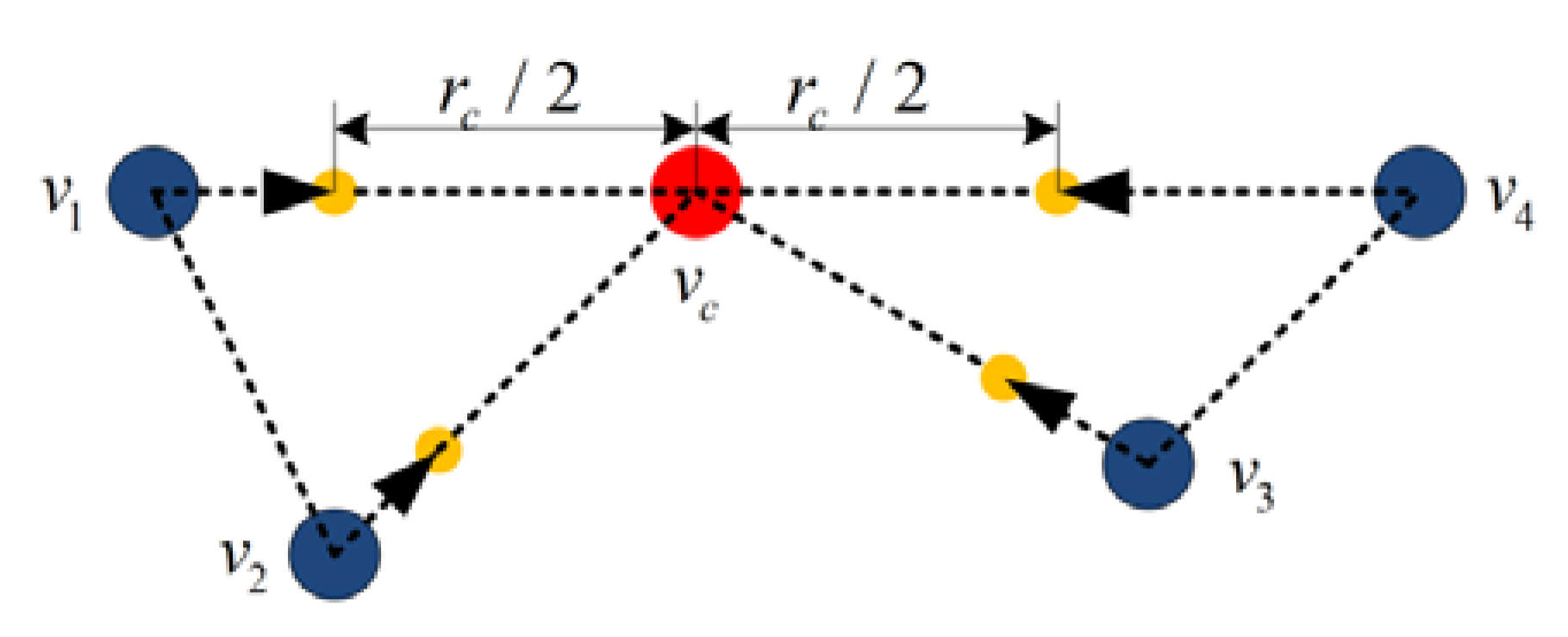
The agent nodes exchange information through one or more hops in wireless networks. Any pair of nodes in the network can communicate with each other if and only if there is at least one communication path/link.
can be defined as the number of disjoint communication paths between any pair of nodes. If the network is simply connected, namely
, the failure of one node will cause the whole network to be divided into two disconnected sub-networks. In the connected network of
, if
, nodes are removed from the network, the network remains connected. However, with the larger
value of the system and the denser nodes, it will impose greater motion constraints on the nodes system [
7], which is not beneficial to enlarge the coverage of the system. Therefore, the objective of this paper is to construct and optimize the biconnected topological structure.
Building up the biconnected topological structure is an efficient approach to establish a communication network with destruction resistance [
8,
9]. The biconnected construction methods described in the existing literatures include the following three types [
10]: 1. The transmitting power of each node in the system should be adjusted to build up the topological structure with destruction resistance [
2,
11,
12,
13], which is applicable for the node-intensive system. As for the node-sparse system, even though the transmitting power of each node reaches the maximum value, the system may not be biconnected. 2. Additional relay nodes should be deployed to improve the destruction resistance of the system [
14,
15], which can help solve the problem of topology control effectively. However, this method is not suitable for some conditions where the nodes cannot be deployed again. 3. It has been widely studied and applied that nodes can be moved to construct a biconnected topological structure [
16,
17,
18]. Prithwish [
16] proposed a centralized movement control method, which required the total information of the system. Then, in the literature [
19], while maintaining the connectivity of the initial topological structure in the system, an iterative optimization algorithm was adopted to gradually move the nodes into the communications radius of the critical node. This method only requires the local information of k-hop neighbor nodes, which expends the application range, but the temporary cluster heads or central nodes are still necessary for calculating and controlling the movement of other nodes. Researchers [
20] proposed a distributed algorithm based on node mobility to construct a biconnected topological structure, whereas, in a sparse topological system, this algorithm would lead to certain disconnections in the original topological structure. Thus, the authors in [
10] put forward a model of motion constraints. The nodes move under the motion constraints, so as to avoid disconnections in the original topological structure. However, because this model was established under the relatively motionless conditions of the neighbor nodes, when the nodes and the neighbor nodes are in relative movements, some connections in the original topological structure will still be disconnected. Overall, further research is required on the optimization of the distributed topological structure based on node mobility.
Covering the field of interest is an important indicator for measuring the service quality of wireless sensor networks [
21]. The coverage ability of a network usually refers to the increased area covered by nodes in an area and the reduced uncovered holes and redundant coverage area. In order to solve the problem of maximum coverage, scholars proposed many centralized methods [
22,
23], while others proposed distributed methods, among which the representative methods include the artificial potential field method [
24], the Voronoi coverage method [
25], and the nearest neighbor rule (NNR) [
26], etc. However, it remains a challenge to minimize the movement distance while maintaining the nodes for effectively covering the field of interest. As the NNR algorithm is simple with the distributed features, this paper will enhance the solutions for the coverage based on the NNR algorithm.
Currently, many studies focus on minimizing the movement distance of nodes in the system while constructing the topological structure with destruction resistance [
13] or minimizing the movement distance while solving the coverage problem [
27]. On the other hand, few studies optimize multi-objective functions, including the construction of the topological structure with destruction resistance, the maximum coverage of the field of interest and the minimum movement distance [
28]. In the literature [
29], it is applicable for the node-intensive system to conserve the energy consumption while solving the problems of connectivity and coverage by scheduling. Literature [
30] utilizes a centralized algorithm to solve the problems of connectivity, coverage and energy consumption. Literature [
31] proposes a control model, which combines the control law of connectivity maintenance, with the control law of obstacle avoidance. In the literature [
32], based on the above models, a control model introduced will solve the coverage problem, which aims to improve the invulnerability of communication networks, and enhance the coverage performance, and have the ability of obstacle avoidance. The above algorithm enables the multi-agent system to build up the expected topological structure autonomously, achieving the good results. However, it does not involve the minimum movement distance of nodes, and it requires the total information. This paper draws on the method of combining multiple control laws. Based on the local information of k-hop neighbor nodes, the nodes combine the biconnected construction method with the NNR coverage algorithm to construct the biconnected topological structure with the movement distance as short as possible and maximize the coverage under the biconnected condition.
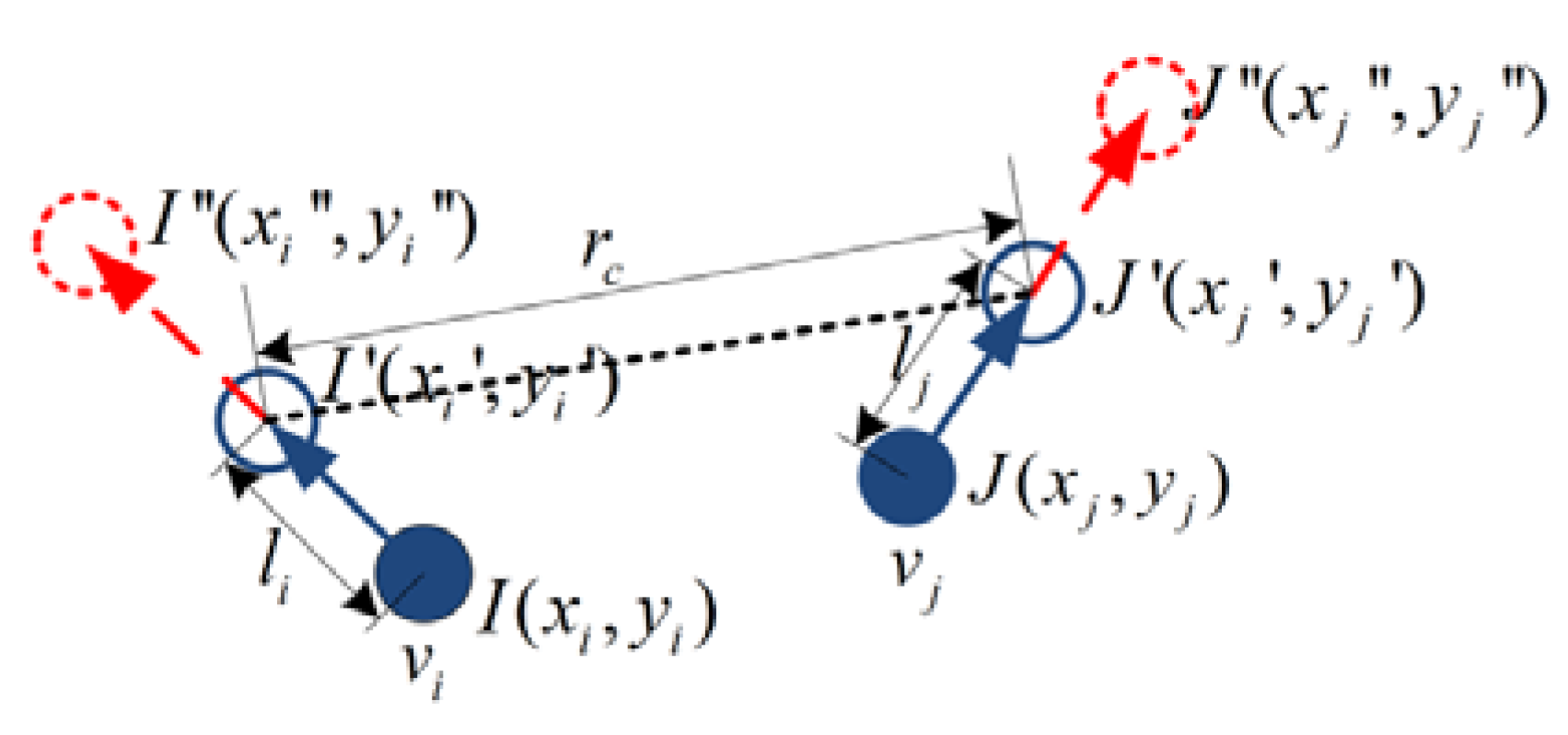
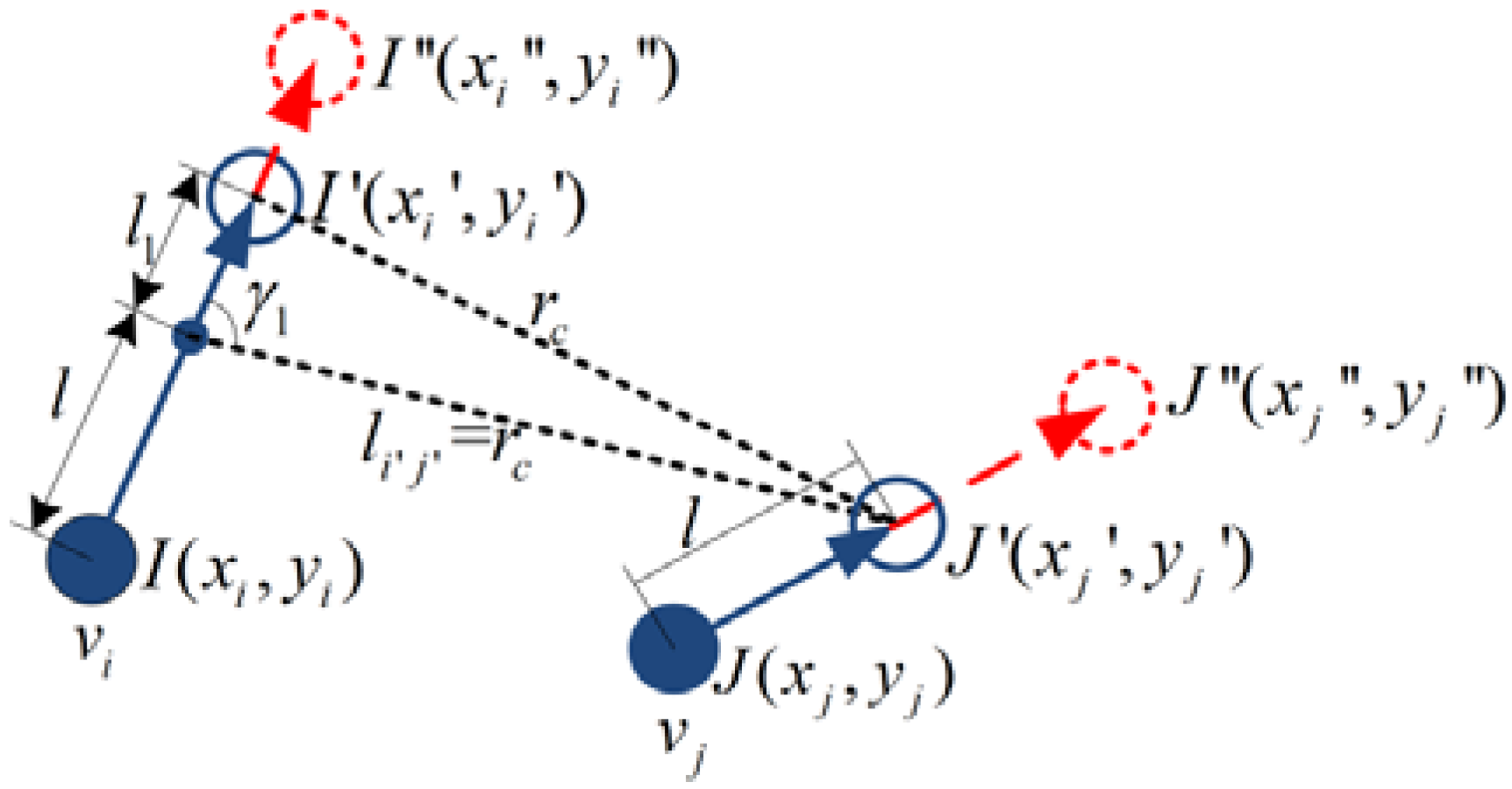
This paper has made the following contributions to the construction and optimization of topological structure: (1) It proposes a new motion constraint model. If the node moves under the motion constraint condition, the node and the neighbor node (whenever static or dynamic) will always stay connected. (2) It improves the coverage method on the basis of NNR. The nodes in the system can be conducted in iterative optimization for the topological structure. In the end, the nodes will be distributed in the equal space and the node spacing is controllable. Besides, it adds constraints on node movement so that nodes can only move when it is necessary to reduce the movement distance. (3) It proposes a fully distributed approach for nodes moving autonomously to realize the multi objective optimization. Through this method of iterative optimization, the system can build up and maintain a biconnected topological structure while minimizing the movement distance of the nodes and maximizing the coverage of the field of interest.
Through the distributed strategy, this paper constructs the biconnected topological structure with maximum coverage. The sections of this paper are as follows: In
Section 2, it describes the application background and related models. In
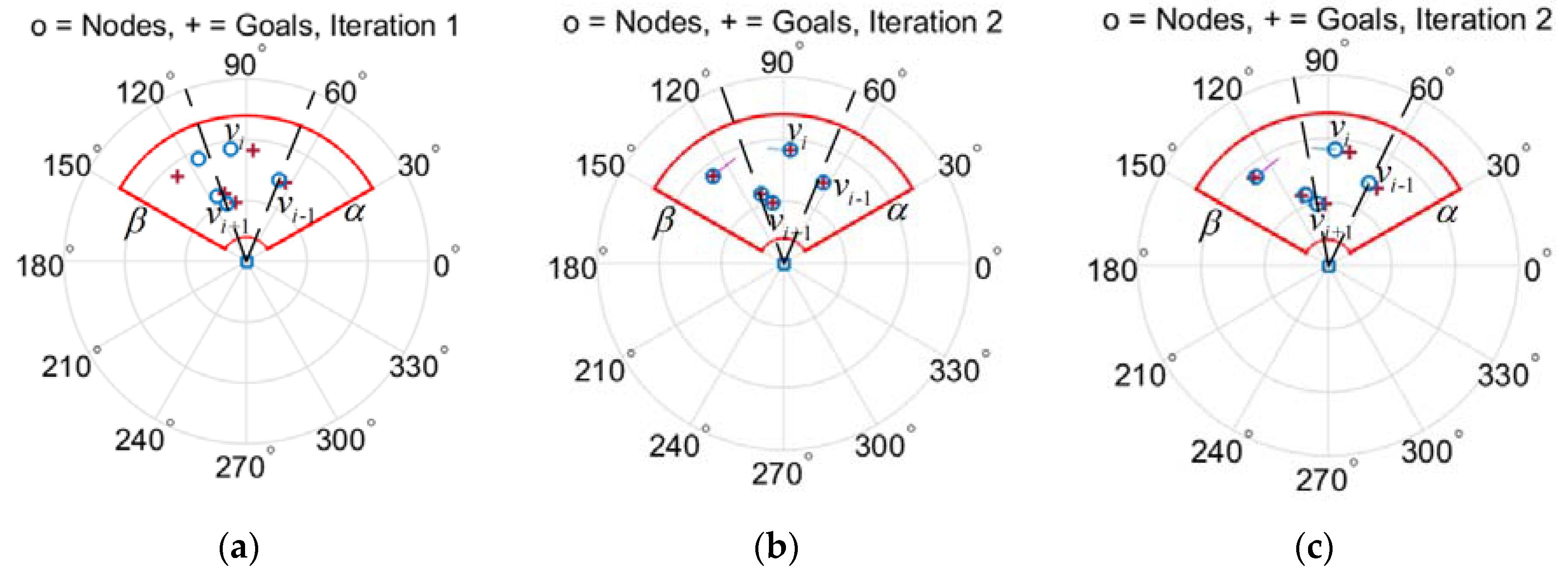
Section 3, it refers to the exchange of location information between nodes and neighbor nodes and conduct the detection for the critical node. It also utilizes the nearest neighbor rule (NNR) to enhance coverage. In
Section 4, in order to optimize the connectivity performance of nodes, nodes should accumulate near the critical node. As for optimizing the coverage performance, the nodes spread along a curve. Then, the nodes gradually optimize the topological structure by moving towards the resultant displacement at each iteration. In
Section 5, it implements the simulation verification for the feasibility of the topological structure optimization algorithm. After optimization, the topological structure represents the features of low movement energy consumption, bi-connectivity and high coverage. In
Section 6, it includes the summary and the expectations of future work.
2. Background and Nodes Distribution Model
2.1. Background
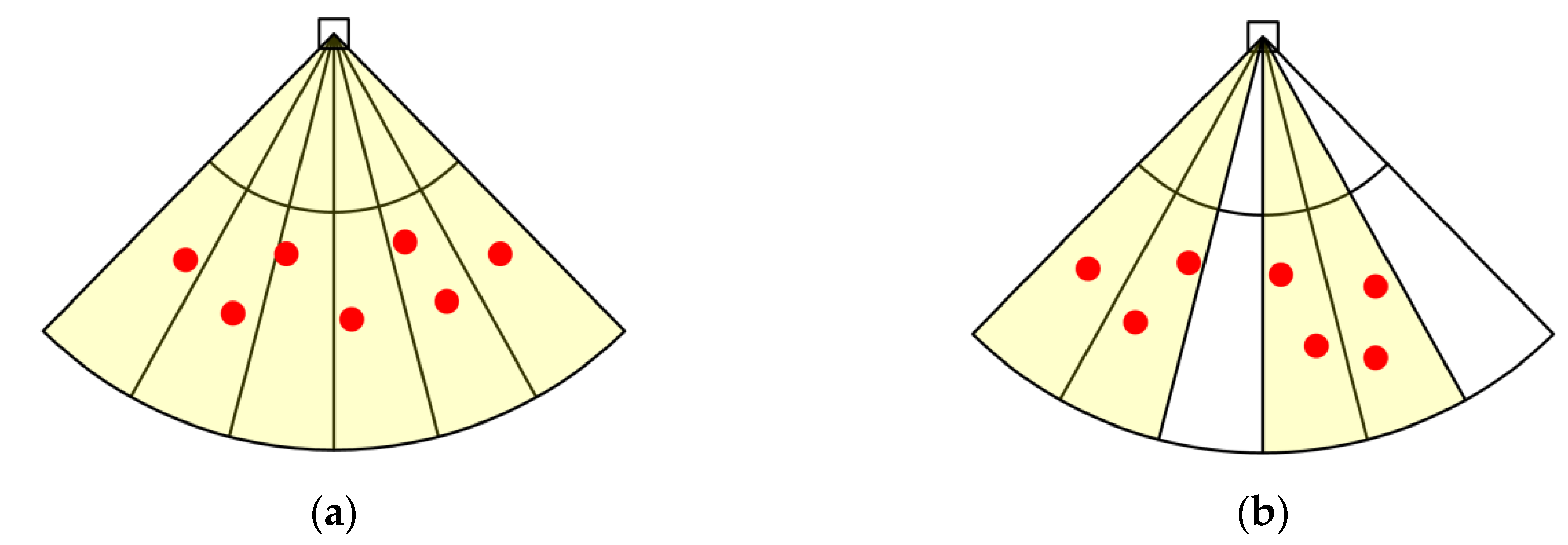
A number of small ground unmanned mobile platforms (hereinafter referred to as jamming nodes or nodes) with jamming equipment are scattered in the area near the enemy radar, as shown in
Figure 1. When the radar is searching or tracing, the radar beam has directivity. Due to the directivity of the radar beam, effective jamming can be only achieved when interference energy enters from the main lobe of the radar beam. If the jamming nodes are deployed reasonably, no matter where the radar beam is directed, the jamming nodes in the main lobe of the radar beam can always be found to interfere with the radar, so that the jamming node group forms the jamming sector for the radar. Multi-jamming nodes can impose many-to-one co-interference on the radar, so that the radar detection performance is suppressed in the sector where the jamming node group is located.
At the initial time, the jamming nodes are randomly deployed in the sector region near the radar. The angle
between the line linking the jamming node with the radar and the X-axis is the random variable uniformly distributed within the range of (
), and the distance from the jamming node to the radar,
, is the variable followed by the distribution function
, as shown in
Figure 1a. In order to optimize the network topology, each node adopts a distributed strategy to move autonomously via iterative optimization, to construct a communications network with destruction resistance and topology with wide coverage, and to achieve the shortest average travelling distance. The distribution of nodes after the topology optimization is shown in
Figure 1b.
2.2. Network Model and Coverage Model
Based on wireless communication theory, the maximum signal transmission distance is proportional to the transmission power. One node can be heard from the other if the transmission power of the other node is great enough. The distance of communication between each other is unique if the value of the transmission power is given. Thus, we use the distance instead of transmission power to represent the communication capability of the node. Besides, the network model is regarded as a Boolean model. That is, draw a circle with the position of node as the center and the communication distance as the radius. The nodes can communicate directly with each other if their corresponding circles are intersecting.
The assumptions are as follows: Nodes are isomorphic. The communication radius
for each node is the same. Each node has the same interference performance, and each node
knows its identification number
and its exact coordinates
. At the same time, according to the previous reconnaissance radar information, the radar coordinates
and the boundary value of the deployment area are available, as shown in
Figure 1 .
For the convenient description, the symbol definitions are as shown in
Table 1:
The network of jamming nodes on the two-dimensional plane constitute graph , among which and are the nodes set and the edges set, respectively. If the distance between the node and the node is less than the communication radius, namely , there will be edge between the two nodes, otherwise there is no edge. Graph in this paper is an undirected graph. For the convenient description, the definitions are introduced as follows.
Definition 1. K-connected. If there are at least K disjoint communication paths between any two nodesand, the Graphis K-connected. Letbe the sets of the disjoint communication paths between nodeand node.
The definition of K-connected is as follows: When K = 1, Graph is simply connected. If there are disjoint paths in Graph , when K-1 paths fail, Graph is still connected, which indicates that this network topology has fault tolerance and invulnerability. The connectivity and invulnerability of Graph will be better with a larger K, but excessive K requires more intensive nodes, causing network congestion or a higher cost. Therefore, this paper constructs a 2-connected network topology.
Definition 2. Neighbor nodes. Letbe the shortest paths linkingwith, and letbe the number of the edges on the shortest path. Defining the set of nodesas 1-hop neighbors of the node, the nodes incan communicate directly with the node. Defining the set of nodesas k-hop neighbors of the node, there are k edges on the shortest path between the nodes inand the node. If there are no special explanations in this paper, the set of neighbors of the noderefers to 1-hop neighbor nodes. Definition 3. Coverage. It is assumed that all nodes located in the sector jamming area can implement the main lobe jamming to the radar, namely, when the radar beam points to the node, the single node has the ability to implement jamming to the radar. The main lobe width of the radar isthe central angle range of the sector area is, and the sector area is divided intosubregions, as shown inFigure 2.
If nodeis located in a subregion, nodewill cover this subregion, and the coverage area of nodeis recorded as.
If there are nodes in each subregion, the sector regionwill be completely covered, as shown inFigure 2a;
otherwise, it will be not completely covered, as shown inFigure 2b.
The mathematical description of the node for being completely covered is as follows:.
The not completely covered mathematical description is as follows:and.
The mathematical description of the coverage is as follows: 2.3. Objective Optimization Model
Each node moves gradually from the initial position to the position after topology optimization. This paper studies the optimization of the multi-objective function, namely minimizing the movement distance of nodes and maximizing the coverage, while building up the biconnected topological structure of the node network. The topology optimization of the node network can be described as shown in Formulas (1)–(3):
In Formula (1), is the average movement distance of all the nodes, and is the distance that the node moves at the iteration. Formula (2) and Formula (3) are the definitions of coverage and bi-connectivity, respectively.
5. Simulation
We verify the feasibility of the Localized Topology Optimized Method (LTOM) proposed in this paper using Matlab software. This paper adopts the LTOM, NNR [
27], Genetic [
35], and Hungarian [
30] algorithms to optimize the topology, then analyzes and compares the average movement distance, coverage and connectivity of two algorithms. When NNR is applied for each node, the azimuth
of the next position is calculated by Formula (4), and the radial distance,
, of the next position is calculated by the following formula:
It is noted that LTOM and NNR are the distributed algorithms, while Genetic and Hungarian are the centralized algorithms. Assume that a central node or base station knows the global information when Genetic and Hungarian algorithms applied, once the optimized topology is obtained, then the central node sends instructions to make all nodes moving directly from their initial positions to the final destinations.
Besides, the pre-defined destinations are needed when the Hungarian algorithm is applied. The topology optimization problem could be transferred to the assignment problem that is to assign exactly one node to one destination in such a way that the moving distance of all nodes is minimized. The pre-defined destinations are calculated by the following formula:
In the simulation for all algorithms, the combat zone is a sector area with an angle range of and the radial range of . Without the loss of generality, the radial distance has no metric unit, and 1 represents a 1-unit distance. The communication radius of each node is 2. As the system nodes are randomly distributed in the sector area, the system may be divided into several disconnected subgroups. For the simplification of analysis, it can be assumed that the initial topology is simply connected. The simulation will not consider the signal attenuation and jam of the communication. It can be assumed that the radar main lobe beam width is , namely the angle coverage range of a single node is . Moreover, it can be assumed that the algorithm’s iteration period is , and the movement speed of the nodes is 0.01.
In order to study the impacts of system scale on results, this paper analyzes the average movement distance, coverage, and connectivity of the four algorithms under scenarios with different number of nodes. Let the number of nodes be . The different scenarios include complete coverage and uncomplete coverage. As the initial deployment of the nodes is random, the results of each calculation are inconsistent. The results in this paper are the mean value calculated for 50 times.
5.1. Feasibility Analysis
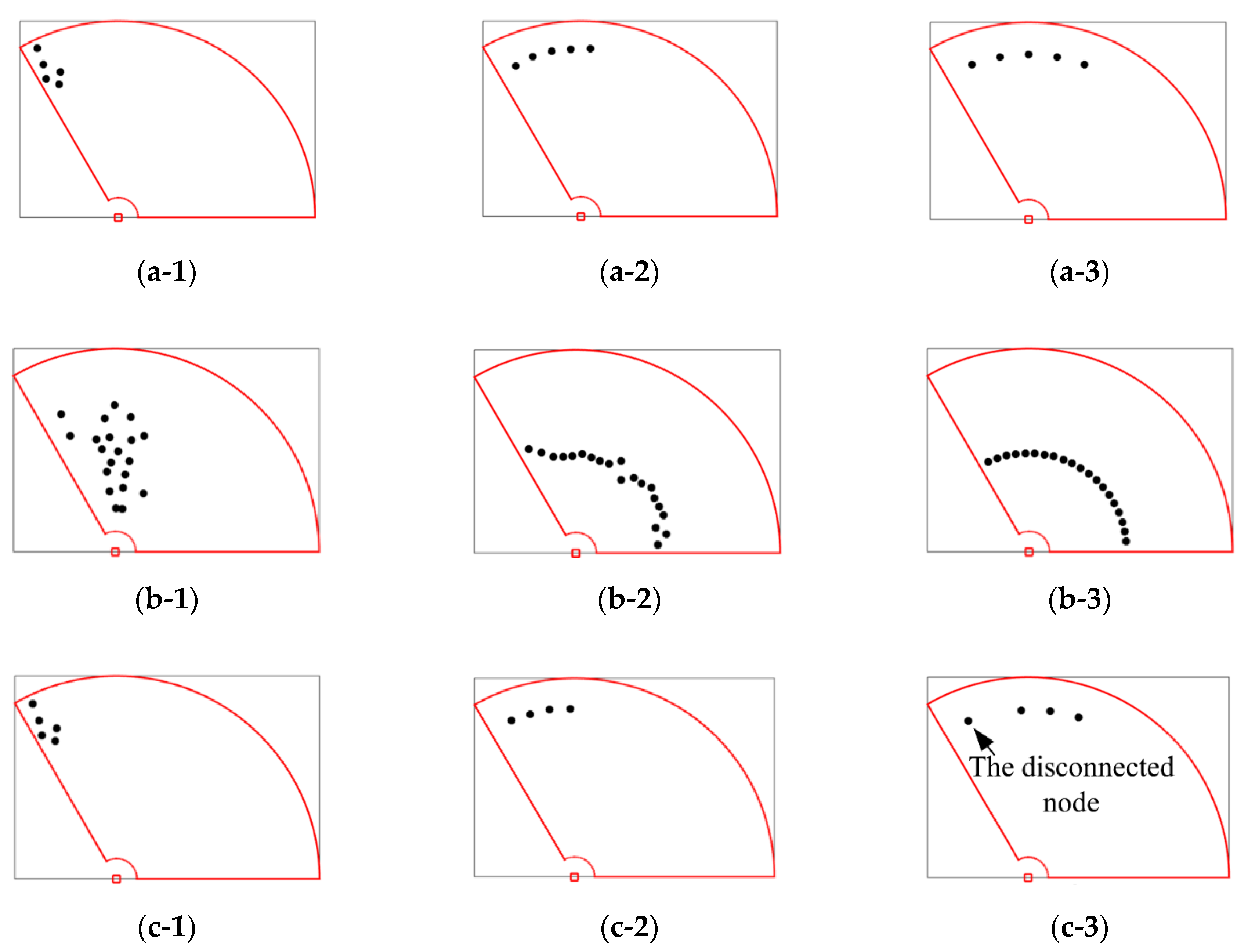
The simulation verifies the feasibility of the LTOM algorithm.
Figure 9 describes the process of the system’s movement according to LTOM and NNR from the initial topology to the final topology under different scenarios. Scene 1 is as shown in
Figure 9a-1–a-3, with the number of nodes at 5. Finally, the system of nodes cannot fully cover the sector area. Scene 2 is as shown in
Figure 9b-1–b-3 with the number of nodes at 20. Finally, the system of nodes can fully cover the sector area. Scene 3 is as shown in
Figure 9c-1–c-3. When one failure node appears, the system can be self-healing.
It can be seen from scene 1 that NNR has good coverage performance and maximizes the coverage without considering the connectivity constraints. LTOM integrates the NNR coverage algorithm and constructs the biconnected algorithm to maximize the coverage under the circumstance of maintaining 2-connectivity. However, it is constrained by the connectivity, and the coverage of LTOM is smaller than that of NNR. It can be seen from Scene 2 that the topology after NNR is an arc line where the nodes are evenly distributed. The nodes after LTOM are evenly distributed along the direction of the azimuth, but they are not at the same distance in the radial direction. The reason is that in order to reduce the movement distance of nodes, the LTOM algorithm adds constraint conditions when calculating the radial movement distance, and the nodes will only move radially if the constraints in Formula (17) are satisfied. Assume that the NNR algorithm also adds the constraint condition of this radial movement. Due to NNR not calculating the limit value of the connectivity constraint, when the condition of radial movement is not met, the nodes spread in the azimuth direction without radial accumulation as compensation, which is easy to disconnect the nodes, resulting in the original connected topology becoming disconnected. It can also be seen from Scene 3 that, for any connected system, LTOM can restore the system to 2-connectivity and maximize the coverage. The topology constructed by LTOM has the self-healing function when a node fails, and it indicates that the system enhances the destruction-resistance ability. For example, if the power of one node is too weak due to energy exhaustion that the node cannot work anymore, the optimized topology will be reconstructed by LTOM.
The symmetry of the multi-node system is shown in the invariance of the connectivity performance of the system’s topology after some transformations. The corresponding transformation is called a symmetric transformation. Let be the algebraic connectivity of Graph , and it can be calculated by the Laplacian matrix of from the algebraic graph theory. Define as the connected indicator, where implies that is connected, and is the sign function. The scenes show that the connected indicators of topology during implementing LTOM are consistent. Thus, the transformation of topology by LTOM is symmetric.
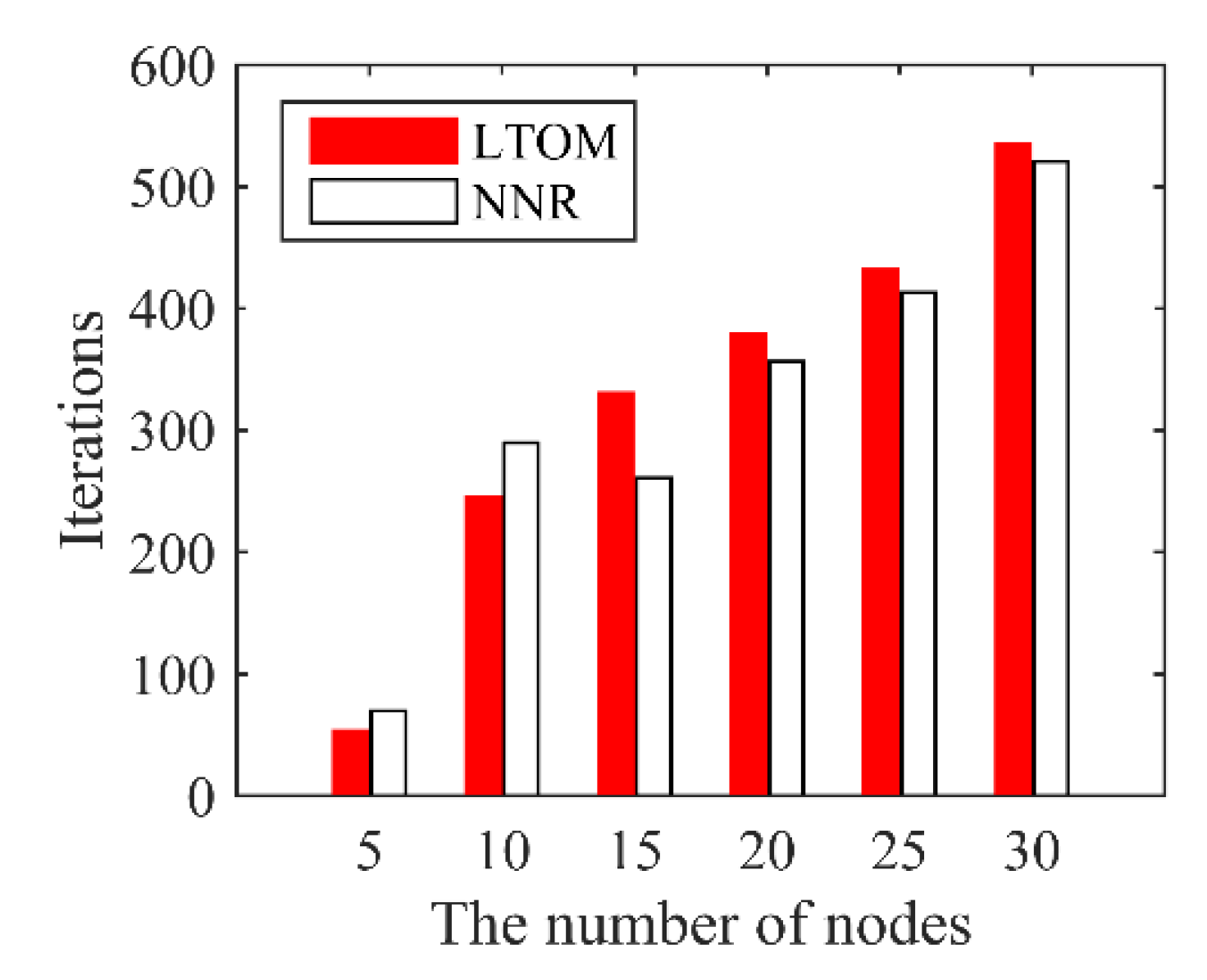
In LTOM and NNR, based on the local information, each node calculates iteratively the coordinates of position at next time and move gradually until the algorithms terminate.
Figure 10 shows the iteration times of both algorithms over the number of nodes. The iteration times of LTOM is slightly higher than that of NNR when the number of nodes is more than 10. The reason is that the nodes move a short distance at each iteration for maintaining connected when LTOM is applied. The results illustrate that LTOM can terminate in the acceptable iteration times.
5.2. Performance Comparison
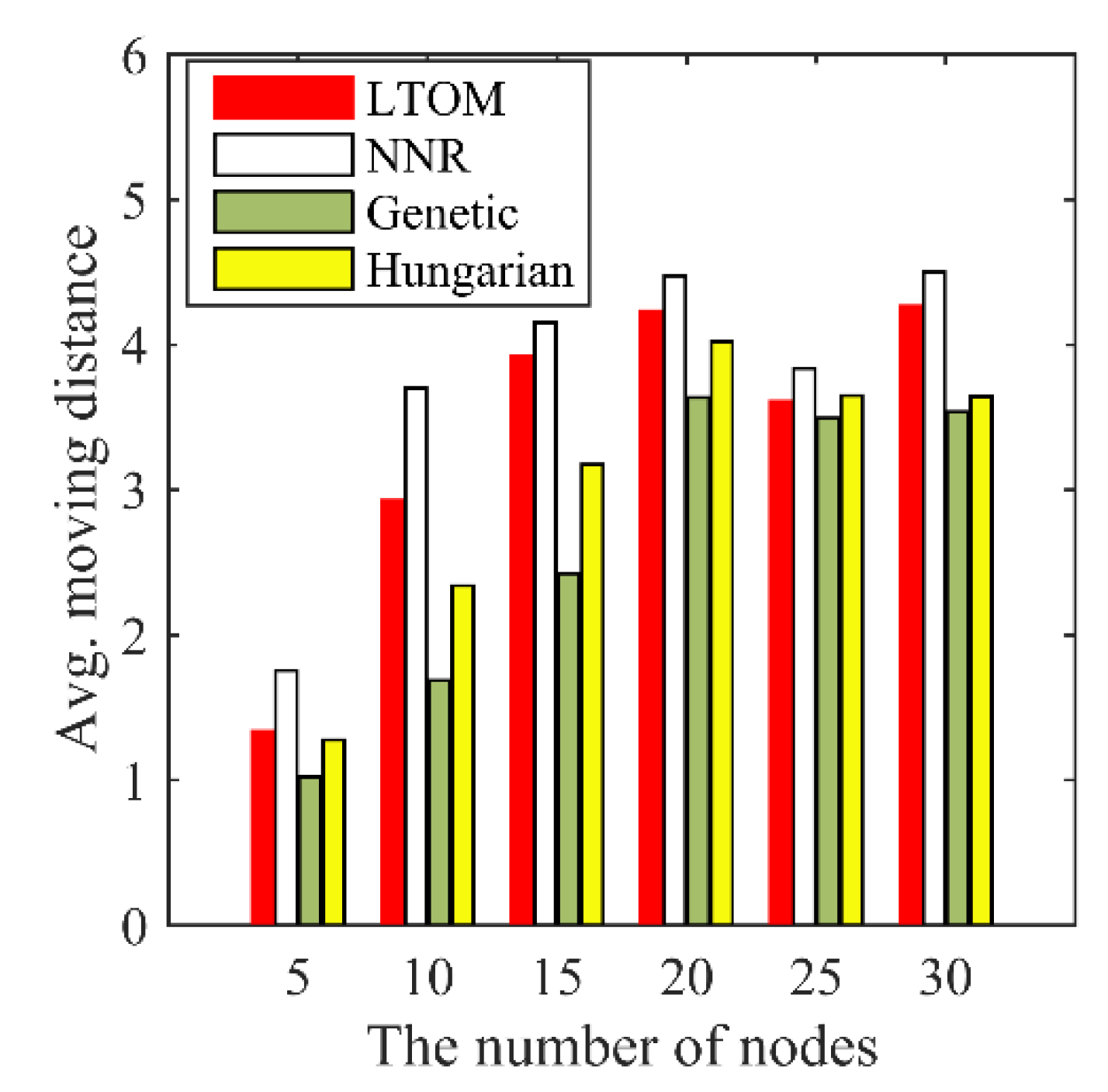
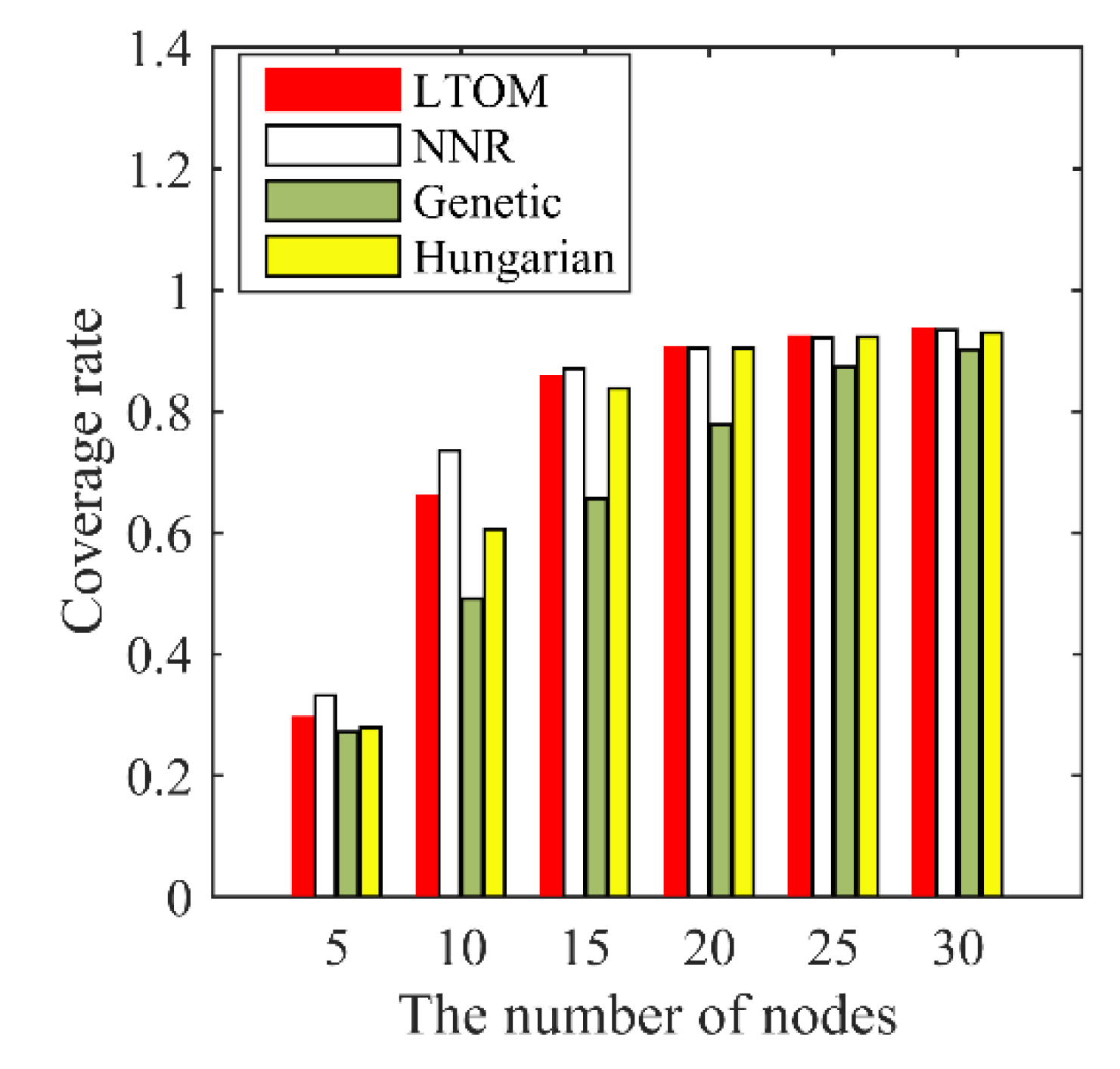
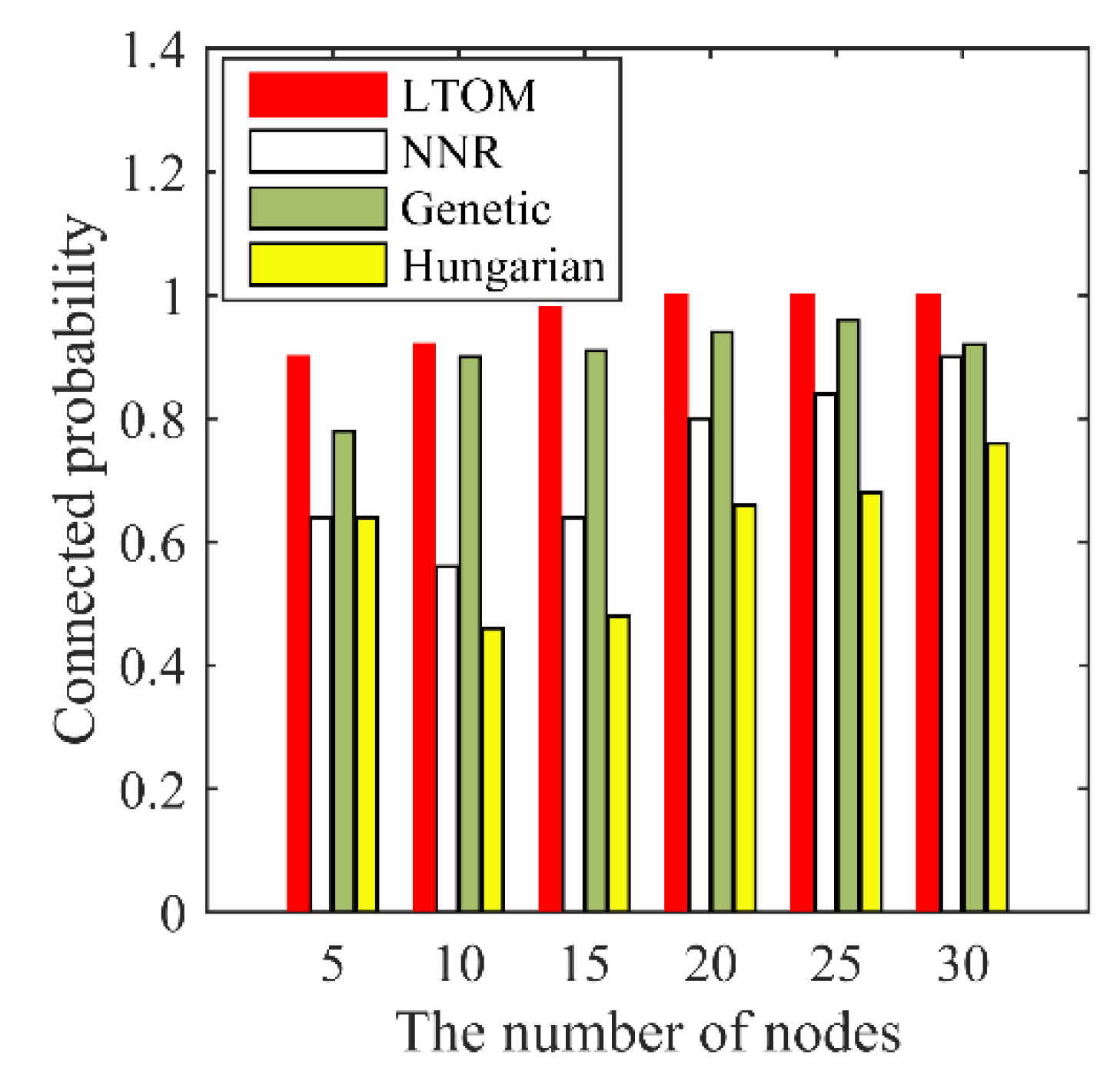
The LTOM, NNR, Genetic and Hungarian algorithms are operated under scenarios with a different number of nodes, and the simulation results are as shown in
Figure 11,
Figure 12 and
Figure 13.
Figure 11 shows that the average movement distances of LTOM and NNR are greater than that of the Genetic and Hungarian algorithms. As mentioned, once the solutions are obtained by the Genetic and Hungarian algorithms, all nodes go straight to their destinations. However, when the distributed algorithms of LTOM and NNR are applied, the nodes adjust their destinations continuously and move step by step until the algorithms terminate. Although the centralized algorithms have better performance in terms of movement cost, they are impractical in some cases. For example, in scenarios where global information is not available in real time, when some nodes fail, the system can neither fill the coverage hole caused by the failure node nor reconstruct the biconnected topology.
Figure 11 shows that the average movement distance of LTOM is less than that of NNR under the scenarios with a different number of nodes. When the number of nodes goes from 5 to 20, the average movement distance of both algorithms is increasing. When the number of nodes goes from 20 to 30, the results of both algorithms vary irregularly and are basically consistent. When the number of nodes is small, the nodes system is not constrained by the area boundaries. The area covered by nodes increases as the number of nodes increases; accordingly, the movement distance of nodes increases. When the number of nodes is large, the nodes are constrained by the area boundaries, the movement distance no longer increases with the number of nodes.
Figure 12 shows that the coverage rate of LTOM is smaller than that of NNR when the number of nodes ranges from 5 to 20, and the coverages of both algorithms are basically consistent when the number of nodes ranges from 20 to 30. Note that the topology after LTOM is biconnected; however, the connectivity after NNR cannot be guaranteed. In conclusion, the LTOM algorithm maximizes the coverage while the 2-connectivity is maintained. Besides,
Figure 12 shows that the distributed algorithms of LTOM and NNR have better performance in terms of coverage than the centralized algorithms of Genetic and Hungarian.
Connectivity is one of the main indicators to evaluate the invulnerability of topology. The connectivity in this paper is measured by the connectivity probability. The connectivity probability refers to the probability that the nodes system stays connected from any initially connected topology to the final topology, even in the presence of some node failures. Define the set of specific times
to be the failure times. The connectivity probability is the ratio of the counting of surviving connected network to the total simulations in the presence of failures.
Figure 13 shows that the connectivity probability of LTOM is the highest among all algorithms. The results show that the LTOM algorithm improves the performance of the connectivity by constructing a biconnected topology.
6. Conclusions
This paper proposes a new topology optimization method (LTOM), combining the biconnected construction algorithm and NNR coverage algorithm. The multi-objective optimization problem is solved, that is, to minimize the moving distance, to maximize the coverage, and to construct and maintain the biconnected topology. Applying LTOM only needs information from finite neighbors, which has the advantage of distributed computing. It is noticed that LTOM is not only applied to the scenario of radar countermeasure, but is also applied to other scenarios such as border surveillance or intrusion detection.
In terms of building up the biconnected topology, the limit value for moving is calculated. The topology stays connected whenever the nodes are moving or stationary according to LTOM. Meanwhile, the handshake mechanism is adopted to remove redundant connections. This mechanism reduces the impact of movement restrictions, and it maximizes the coverage without weakening the connectivity performance. In terms of improving the coverage, LTOM further optimizes the coverage strategy based on NNR. This paper discovers the rule of nodes spreading in an unbounded scenario. Let be the distance between the outermost node and the virtual node. The nodes after LTOM are distributed evenly, and the spacing of the adjacent nodes is . Besides, the judgment is added to determine whether a node requires to move in the radial direction. The improved coverage strategy conduces to reduce the moving distance and energy consumption of the nodes system.
The feasibility and effectiveness of LTOM are demonstrated through simulation. For any initially connected topology, LTOM has the ability to construct a biconnected topology while the coverage is maximized. Compared with the other existing algorithms, LTOM in a decentralized way reduces the moving distance of each node, improves the performance of connectivity, and maximizes the coverage on the premise of bi-connection.
The LTOM algorithm optimizes the topology where the nodes are isomorphic. In future work, we will study how to optimize the topology while minimizing the cost in the case of inconsistent communication distances or different agents’ capabilities.