Towards a Secure Signature Scheme Based on Multimodal Biometric Technology: Application for IOT Blockchain Network
Abstract
1. Introduction
2. Literature Review
3. Methodology
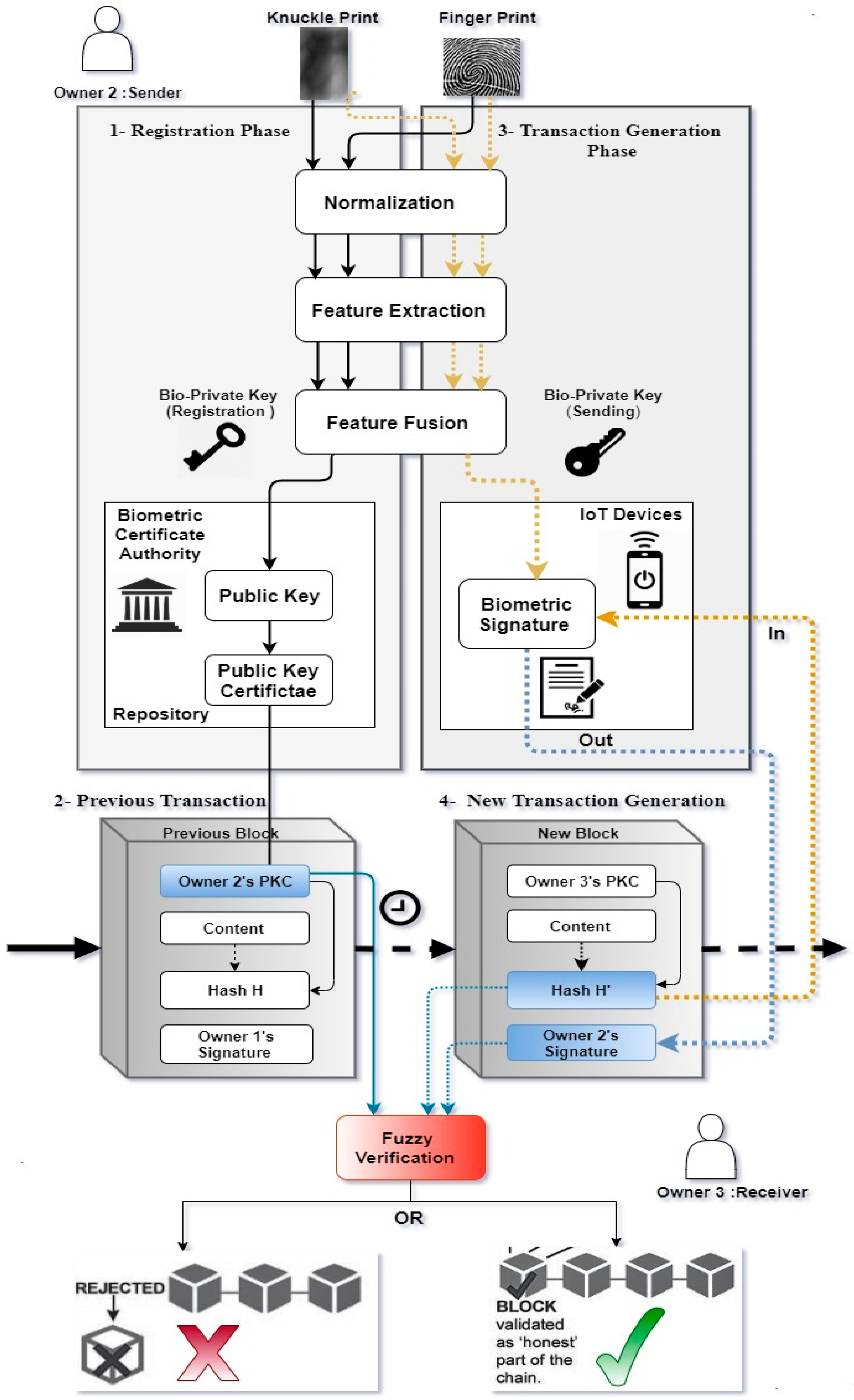
3.1. Signature Scheme Using Fuzzy Identity
- -
- Setup (n, d): The setup algorithm takes a security parameter n and an error tolerance parameter d as input. It generates the master key (MK) and public parameters (PP) (Public Key).
- -
- Extract (PP, MK, ): The private key generation algorithm takes the master key MK and the user biometric fused vector as input. It outputs a private key associated with , denoted by .
- -
- Sign (PP, , M): The signing algorithm takes the public parameters PP, a private key , and a message M as input. It outputs the signature σ.
- -
- Verify (PP, , M, σ): The verification algorithm takes the public parameters PP, a user biometric fused vector such that |∩| ≥ d, the message M and the corresponding signature σ as input. It returns a bit b, where b = 1 means that the signature is valid; otherwise, the signature is not valid.
| Algorithm 1 Pseudo Code of our Proposed Scheme |
| 1-Biometric Key Extraction Phase |
| Pre-Processing |
| Feature Extraction |
| Feature Level Fusion |
| Return w |
| 2-Registration Phase |
| Algorithm Setup (n,d) |
| Return PP |
| Algorithm Extract (PP, MK, w) |
| Return Kw |
| 3-Transaction Generation Phase |
| Algorithm Sign (PP, Kw, H) |
| Return σ |
| 4-Verification Phase |
| Algorithm Verify (PP, w’, H, σ) |
| Return True or False |
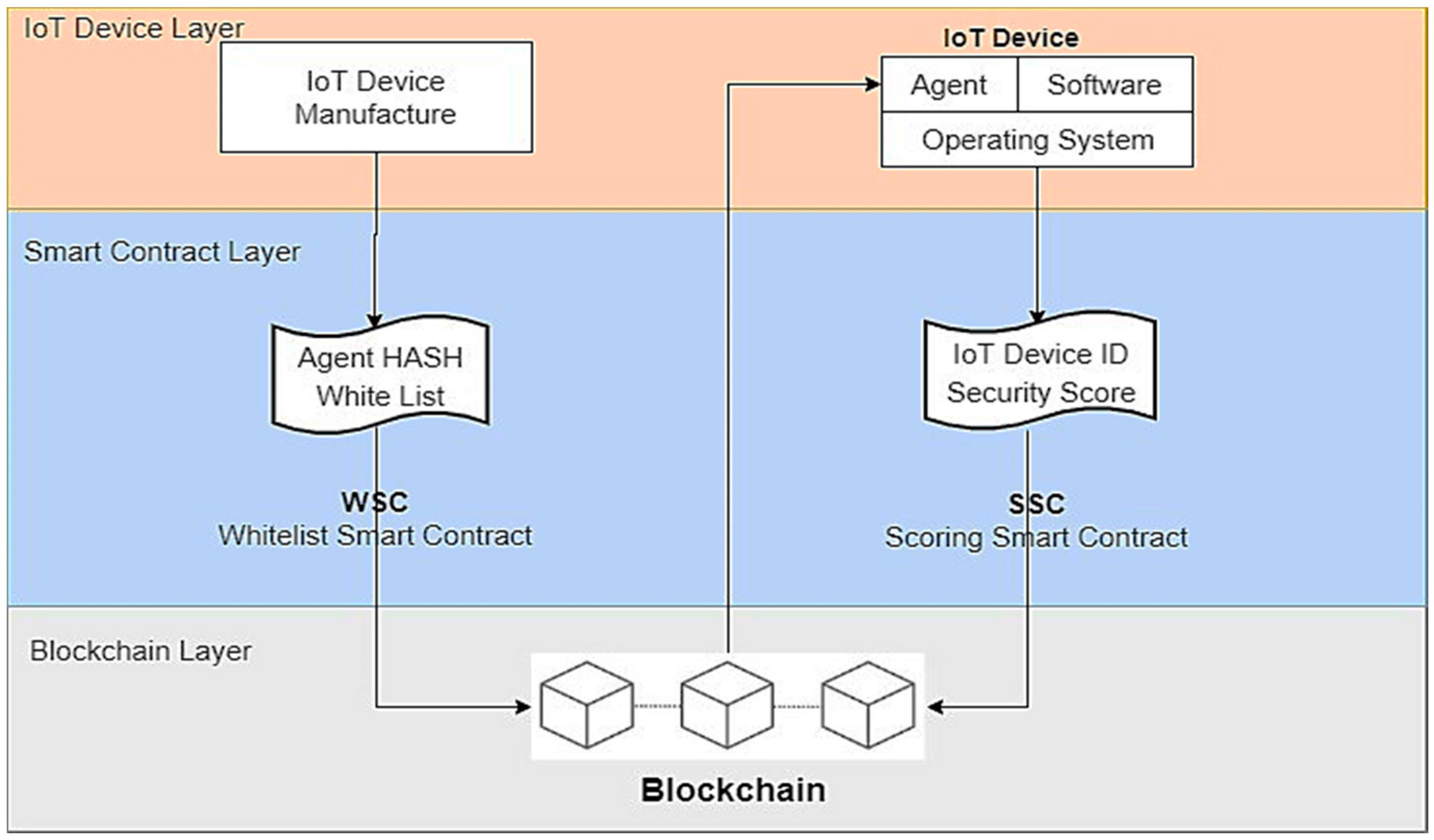
- Step 1:
- IoT device manufacturers compose whitelist software that is installed on IoT devices.
- Step 2:
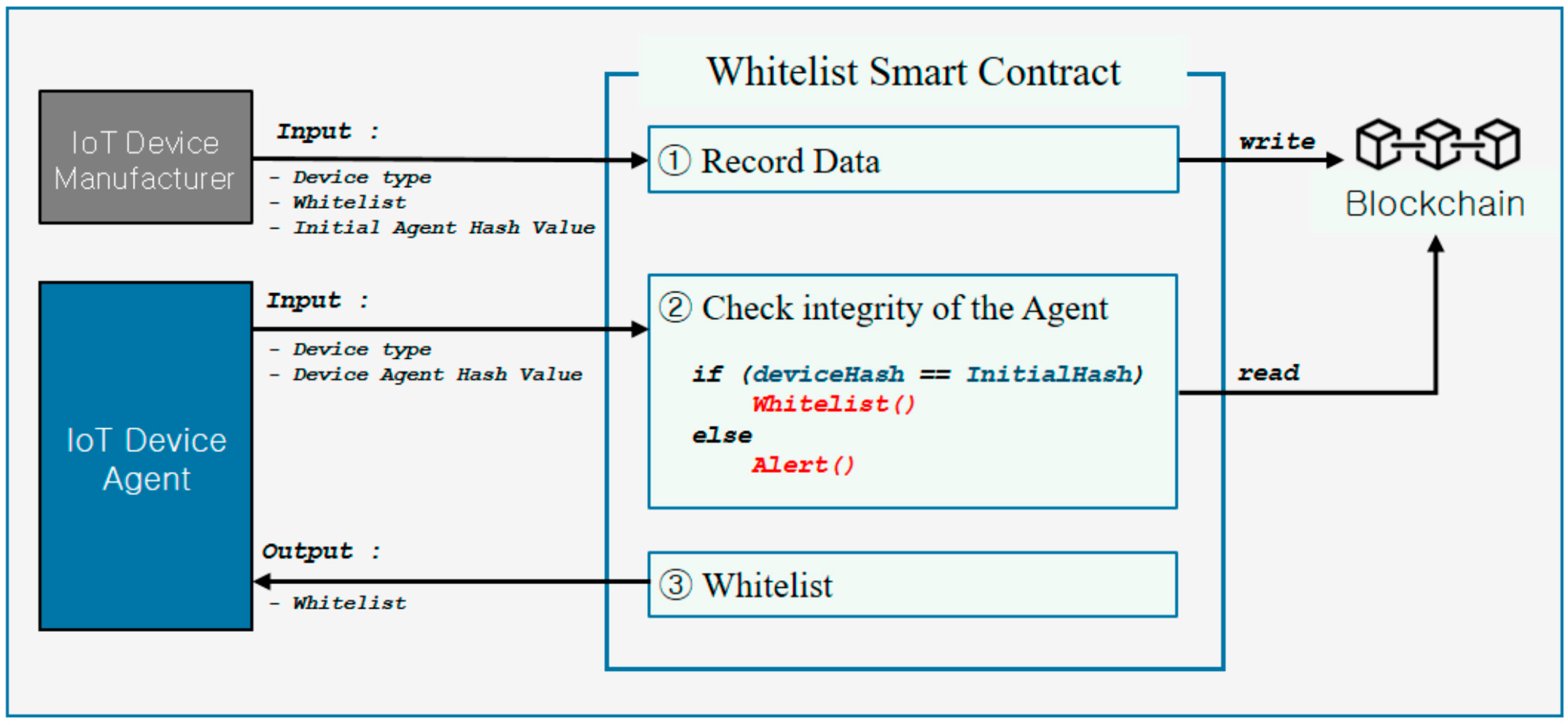
- Device manufacturers build a smart contract comprising manufacturers’ whitelist and the agent’s initial agent hash value (IAHV) that is embedded in an IoT device. The Whitelist Smart Contract (WSC) records this value in the blockchain.
- Step 3:
- The IoT device access the WSC recorded in the blockchain and verifies if the IAHV of the agent matches the Device Agent Hash Value (DAHV) of the current whitelist installed on the device.
- Step 4:
- In the case of successful verification, the device is not infected nor hacked and the security score is set to be high and vice versa.
- Step 5:
- A Scoring Smart Contract (SSC) is created, which involves the security status of the IoT device, which is evaluated by the agent and the device-unique identifier, and is recorded in the blockchain.
- Step 6:
- The SSC of the device can be inquired when the device is connected to other devices. Based on the recording in the blockchain, the IoT device can be extended safely and quickly when connected to other devices. The WSC collects and records in the blockchain the whitelist of each IoT system and the IAHV from the producer. If the WSC tests by matching the IAHV with the device’s current hash, it may give a warning message to the IoT and the vendor if they do not fit. The whitelist recorded in the blockchain is then forwarded to the IoT device, and the Agent uses the transmitted details and sends the list of the checked and unverified apps to the SSC [35]. Figure 4 illustrates the concept of WSC.
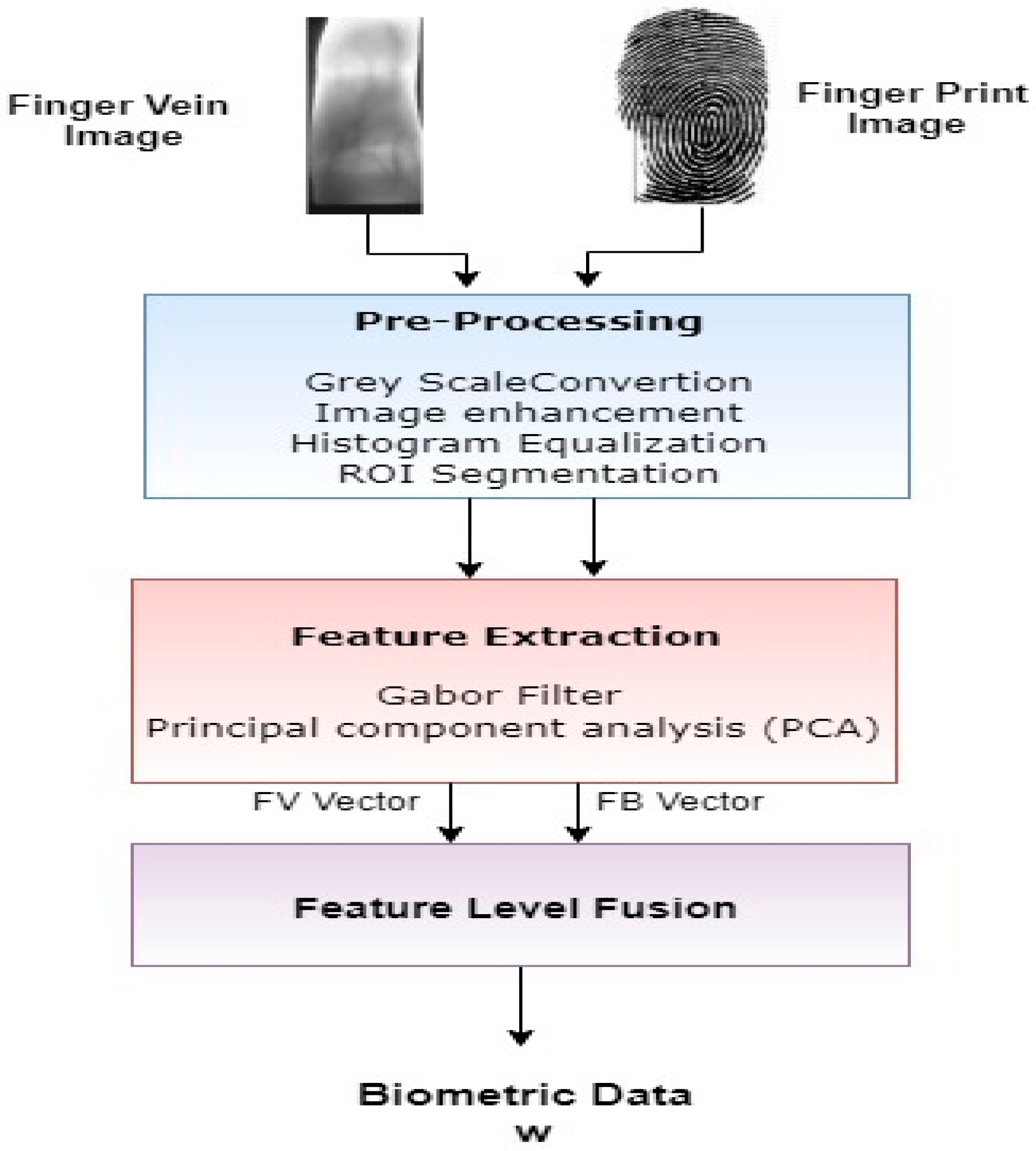
3.2. Biometric Key Extraction Phase
3.2.1. Pre-Processing
3.2.2. Feature Extraction
3.2.3. Feature Level Fusion
3.3. Registration Phase
3.4. Transaction Generation Phase
3.5. Transaction Verification Phase
4. Results and Discussion
4.1. Security Evaluation
4.1.1. Experiment 1: Private key Attack or Leakage
4.1.2. Experiment 2: Forgery of Digital Signatures
4.1.3. Experiment 3: Security Score Evaluation
4.2. Performance Evaluation
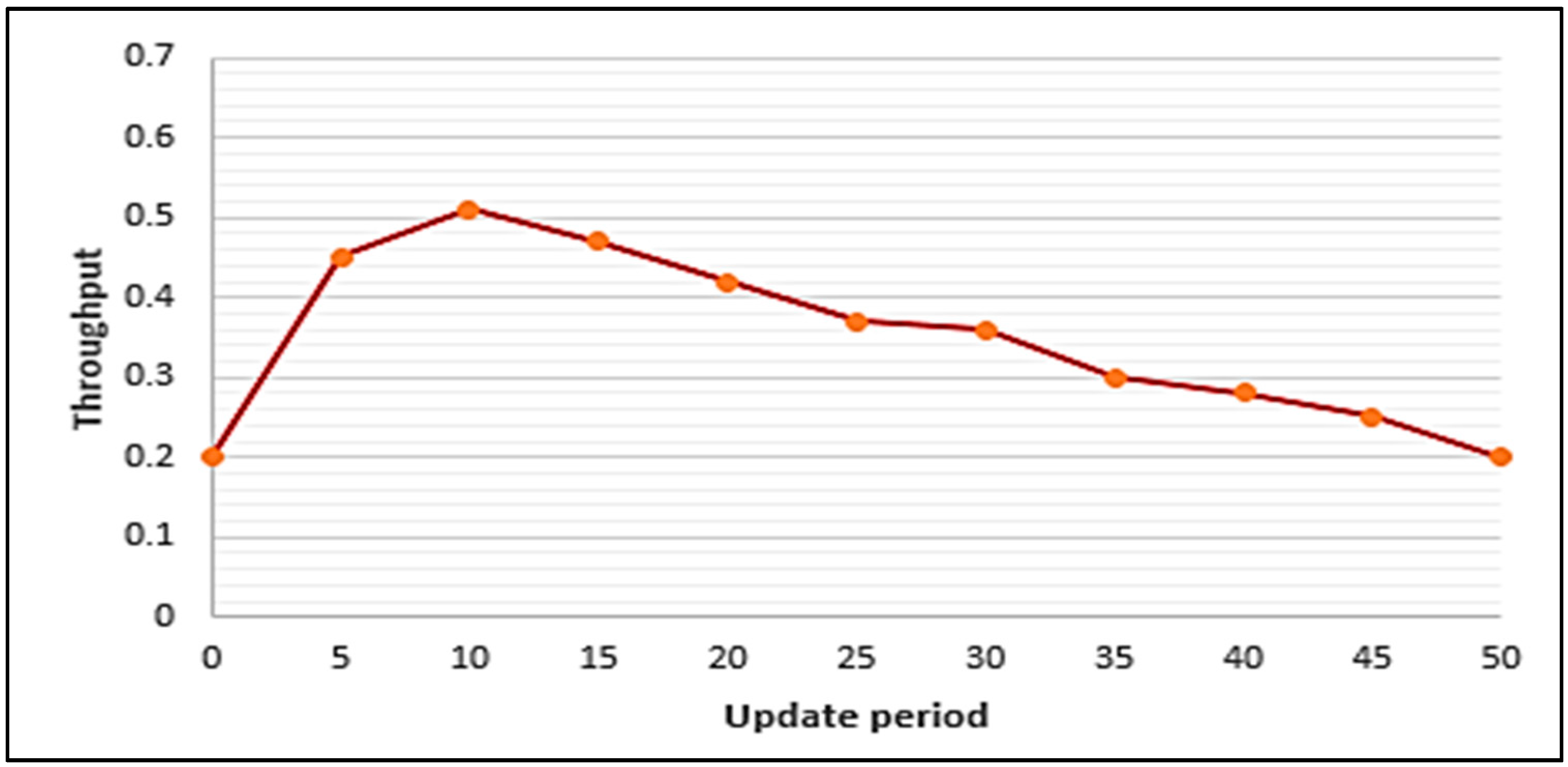
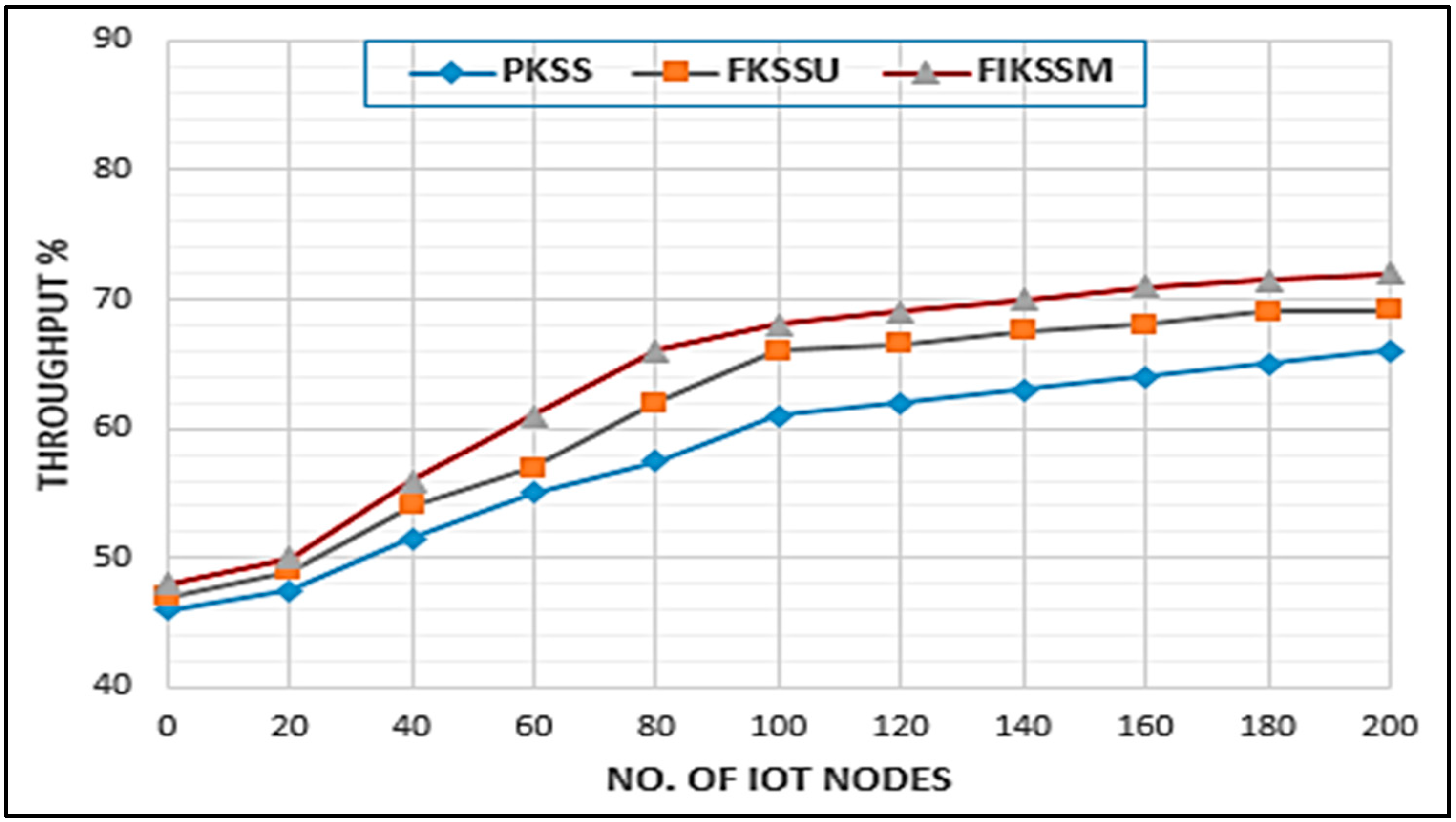
4.2.1. Experiment 4: Throughput
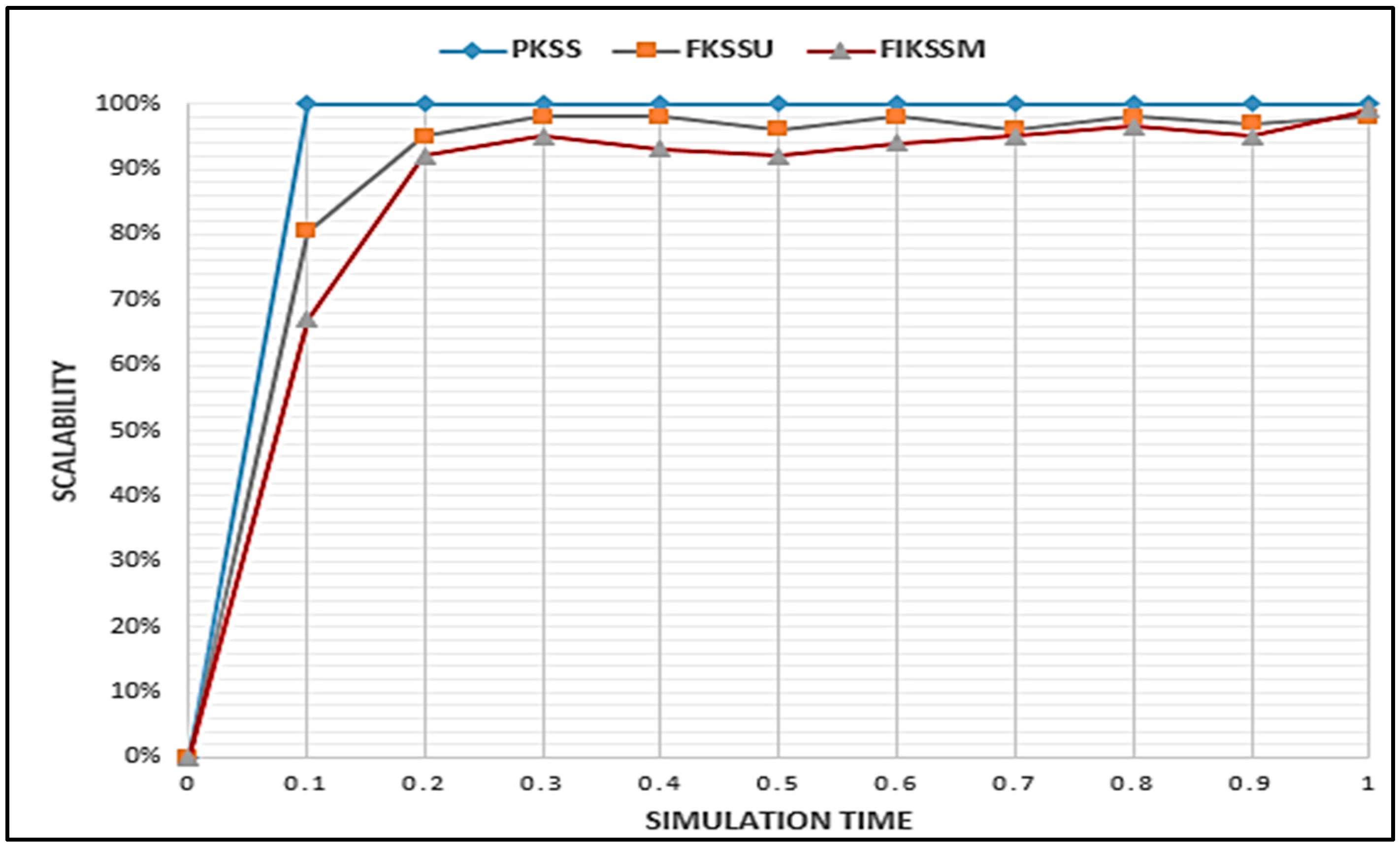
4.2.2. Experiment 5: Scalability
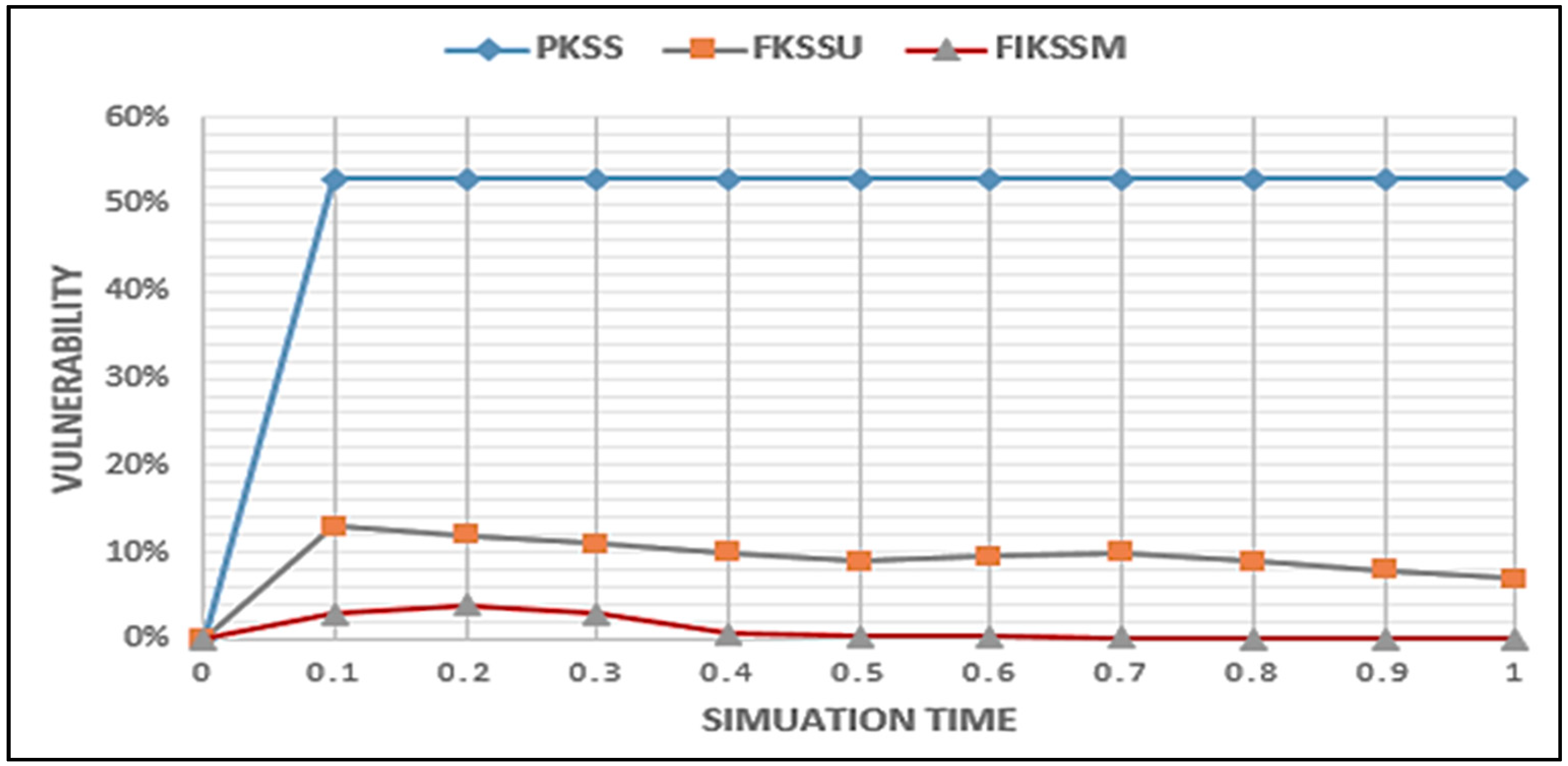
4.2.3. Experiment 6: Vulnerability
4.2.4. Experiment 7: Complexity
5. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Bozic, N.; Pujolle, G.; Secci, S. A Tutorial on Blockchain and Applications to Secure Network Control-Planes. In Proceedings of the 3rd IEEE International on Smart Cloud Networks & Systems (SCNS), Dubai, UAE, 19–21 December 2016; pp. 1–8. [Google Scholar]
- Cai, Y.; Zhu, D. Fraud detections for online businesses: A perspective from blockchain technology. Financ. Innov. 2016, 2, 20. [Google Scholar] [CrossRef]
- Li, X.; Jiang, P.; Chen, T.; Luo, X.; Wen, Q. A survey on the security of blockchain systems. Future Gener. Comput. Syst. 2020, 107, 841–853. [Google Scholar] [CrossRef]
- Zyskind, G.; Nathan, O.; Pentland, A.S. Decentralizing Privacy: Using Blockchain to Protect Personal Data. In Proceedings of the 2015 IEEE Security and Privacy Workshops, San Jose, CA, USA, 21–22 May 2015; pp. 180–184. [Google Scholar]
- Davenport, A.; Shetty, S. Air Gapped Wallet Schemes and Private Key Leakage in Permissioned Blockchain Platforms. In Proceedings of the 2019 IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019; pp. 541–545. [Google Scholar]
- Min, X.; Li, Q.; Liu, L.; Cui, L. A Permissioned Blockchain Framework for Supporting Instant Transaction and Dynamic Block Size. In Proceedings of the 15th IEEE International Trust. Security and Privacy in Computing and Communications, Tianjin, China, 23–26 August 2016; pp. 90–96. [Google Scholar]
- Sato, M.; Matsuo, S.I. Long-Term Public Blockchain: Resilience against Compromise of Underlying Cryptography. In Proceedings of the 2nd IEEE European Symposium on Security and Privacy Workshops, Vancouver, BC, Canada, 31 July–3 August 2017; pp. 1–8. [Google Scholar]
- Khan, M.A.; Salah, K. IoT security: Review, blockchain solutions, and open challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In Proceedings of the 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar]
- Dmitrienko, A.; Noack, D.; Yung, M. Secure Wallet-Assisted Offline Bitcoin Payments with Double-Spender Revocation. In Proceedings of the 2017 ACM on Conference on Information and Knowledge Management, Abu Dhabi, UAE, 4–6 April 2017; pp. 520–531. [Google Scholar]
- Bonneau, J.; Miller, A.; Clark, J.; Narayanan, A.; Kroll, J.A.; Felten, E.W. SoK: Research Perspectives and Challenges for Bitcoin and Cryptocurrencies. In Proceedings of the 2015 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 17–21 May 2015; pp. 104–121. [Google Scholar]
- Sikorski, J.J.; Haughton, J.; Kraft, M. Blockchain technology in the chemical industry: Machine-to-machine electricity market. Appl. Energy 2017, 195, 234–246. [Google Scholar] [CrossRef]
- Mettler, M. Blockchain technology in healthcare: The revolution starts here. In Proceedings of the 2016 IEEE 18th International Conference on e-Health Networking, Applications and Services (Healthcom), Munich, Germany, 14–16 September 2016; pp. 1–3. [Google Scholar]
- Murakami, T.; Ohki, T.; Takahashi, K. Optimal sequential fusion for multibiometric cryptosystems. Inf. Fusion 2016, 32, 93–108. [Google Scholar] [CrossRef]
- Yang, P.; Cao, Z.; Dong, X. Fuzzy identity based signature with applications to biometric authentication. Comput. Electr. Eng. 2011, 37, 532–540. [Google Scholar] [CrossRef]
- Novo, O. Blockchain Meets IoT: An Architecture for Scalable Access Management in IoT. IEEE Internet Things J. 2018, 5, 1184–1195. [Google Scholar] [CrossRef]
- Yu, Y.; Li, Y.; Tian, J.; Liu, J. Blockchain-Based Solutions to Security and Privacy Issues in the Internet of Things. IEEE Wirel. Commun. 2018, 25, 12–18. [Google Scholar] [CrossRef]
- Rodriguez-Zurrunero, R.; Utrilla, R.; Rozas, A.; Araujo, A. Process Management in IoT Operating Systems: Cross-Influence between Processing and Communication Tasks in End-Devices. Sensors 2019, 19, 805. [Google Scholar] [CrossRef]
- Fernandez-Carames, T.M.; Fraga-Lamas, P. A Review on the Use of Blockchain for the Internet of Things. IEEE Access 2018, 6, 32979–33001. [Google Scholar] [CrossRef]
- Schuff, D.; Louis, R.S. Centralization vs. decentralization of application software. Commun. ACM 2001, 44, 88–94. [Google Scholar] [CrossRef]
- Dai, W.; Deng, J.; Wang, Q.; Cui, C.; Zou, D.; Jin, H. SBLWT: A Secure Blockchain Lightweight Wallet Based on Trustzone. IEEE Access 2018, 6, 40638–40648. [Google Scholar] [CrossRef]
- Winter, J. Trusted Computing Building Blocks for Embedded Linux-Based ARM Trustzone Platforms. In Proceedings of the 3rd ACM workshop on Security of ad hoc and sensor networks—SASN ’05, Association for Computing Machinery (ACM), Alexandria, VA, USA, 31 October 2008; pp. 21–30. [Google Scholar]
- Da Xu, L.; He, W.; Li, S. Internet of Things in Industries: A Survey. J. IEEE Trans. Ind. Inf. 2014, 10, 2233–2243. [Google Scholar]
- Samaniego, M.; Jamsrandorj, U.; Deters, R. Blockchain as a Service for IoT. In Proceedings of the 2016 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Chengdu, China, 15–18 December 2016; pp. 433–436. [Google Scholar]
- Balfanz, D. FIDO U2F Implementation Considerations. 2017. Available online: https://fidoalliance.org/what-is-fido/ (accessed on 30 May 2020).
- Shingala, K. An Alternative to the Public Key Infrastructure for the Internet of Things. Master’s Thesis, Norwegian University of Science and Technology (NTNU), Trondheim, Norway, 2019. [Google Scholar]
- Biswas, S. Enhancing the Privacy of Decentralized Identifiers with Ring Signatures. Master’s Thesis, Aalto University, Espoo, Finland, 2020. [Google Scholar]
- Raikwar, M.; Gligoroski, D.; Kralevska, K. SoK of Used Cryptography in Blockchain. IEEE Access 2019, 7, 148550–148575. [Google Scholar] [CrossRef]
- Dery, S. Using Whitelisting to Combat Malware Attacks at Fannie Mae. IEEE Secur. Priv. Mag. 2013, 11, 90–92. [Google Scholar] [CrossRef]
- Lotfy, Y.A.; Darwish, S.M. A Secure Signature Scheme for IoT Blockchain Framework Based on Multimodal Biometrics. In Proceedings of the International Conference on Advanced Intelligent Systems and Informatics; Springer Science and Business Media LLC: Berlin, Germany, 2020; pp. 261–270. [Google Scholar]
- Li, Y.; Yu, Y.; Min, G.; Susilo, W.; Ni, J.; Choo, K.K. Fuzzy identity-based data integrity auditing for reliable cloud storage systems. IEEE Trans. Dependable Secure Comput. 2017, 16, 72–83. [Google Scholar] [CrossRef]
- Waters, B. Efficient Identity-Based Encryption Without Random Oracles; Lecture Notes in Computer Science Book Series; Springer: Berlin, Germany, 2005; Volume 3494, pp. 114–127. [Google Scholar] [CrossRef]
- Boneh, D.; Franklin, M. Identity-Based Encryption from the Weil Pairing. SIAM J. Comput. 2003, 32, 586–615. [Google Scholar] [CrossRef]
- Joux, A. Separating Decision Diffie—Hellman from Computational Diffie—Hellman in Cryptographic. J. Cryptol. 2003, 16, 239–247. [Google Scholar] [CrossRef]
- Choi, Y.-J.; Kang, H.-J.; Lee, I.-G. Scalable and Secure Internet of Things Connectivity. Electronics 2019, 8, 752. [Google Scholar] [CrossRef]
- Ross, A.; Govindarajan, R. Feature Level Fusion Using Hand and Face Biometrics. In Biometric Technology for Human Identification II; International Society for Optics and Photonics: Bellingham, WA, USA, 2005; Volume 5779, pp. 196–204. [Google Scholar]
- Wang, Z.; Tao, J. A Fast Implementation of Adaptive Histogram Equalization. In Proceedings of the 2006 8th International Conference on Signal Processing, Beijing, China, 16–20 November 2006; Volume 2, pp. 3–6. [Google Scholar]
- Kekre, H.B.; Bharadi, V.A. Fingerprint’s core point detection using orientation field. In Proceedings of the International Conference on Advances in Computing, Control, and Telecommunication Technologies, Trivandrum, Kerala, India, 28–29 December 2009; pp. 150–152. [Google Scholar]
- Yang, J.; Li, X. Efficient Finger Vein Localization and Recognition. In Proceedings of the 2010 20th International Conference on Pattern Recognition, Istanbul, Turkey, 23–26 August 2010; pp. 1148–1151. [Google Scholar]
- Yang, J.; Liu, L.; Jiang, T.; Fan, Y. A modified Gabor filter design method for fingerprint image enhancement. Pattern Recognit. Lett. 2003, 24, 1805–1817. [Google Scholar] [CrossRef]
- Zhu, Z.; Lu, H.; Zhao, Y. Scale multiplication in odd Gabor transform domain for edge detection. J. Vis. Commun. Image Represent. 2007, 18, 68–80. [Google Scholar] [CrossRef]
- Yang, J.; Zhang, X. Feature-level fusion of fingerprint and finger-vein for personal identification. Pattern Recognit. Lett. 2012, 33, 623–628. [Google Scholar] [CrossRef]
- Jain, A.K.; Prabhakar, S.; Hong, L. A multichannel approach to fingerprint classification. IEEE Trans. Pattern Anal. Mach. Intell. 1999, 21, 348–359. [Google Scholar] [CrossRef]
- Srivastava, S. Accurate Human Recognition by Score-Level and Feature-Level Fusion Using Palm—Phalanges Print. J. Sci. Eng. 2017, 2, 543–554. [Google Scholar]
- Cachin, C. Architecture of the Hyperledger Blockchain Fabric. In Proceedings of the 2016 Workshop on Distributed Cryptocurrencies and Consensus Ledgers, Chicago, IL, USA, 25 July 2016. [Google Scholar]
- Wang, C. A provable secure fuzzy identity based signature scheme. Sci. China Inf. Sci. 2012, 55, 2139–2148. [Google Scholar] [CrossRef]
- Yao, Y.; Li, Z. A novel fuzzy identity based signature scheme based on the short integer solution problem. Comput. Electr. Eng. 2014, 40, 1930–1939. [Google Scholar] [CrossRef]
- Shandong University. SDUMLA. Available online: http://mla.sdu.edu.cn/info/1006/1195.htm (accessed on 30 May 2020).
- Rodrigues, R.N.; Kamat, N.; Govindaraju, V. Evaluation of biometric spoofing in a multimodal system. In Proceedings of the 2010 Fourth IEEE International Conference on Biometrics: Theory, Applications and Systems (BTAS), Washington, DC, USA, 27–29 September 2010; pp. 1–5. [Google Scholar]

| Signature Approach | Leakage of Private Key | Digital Signature Forgery |
|---|---|---|
| PKSS | Low | Middle |
| FKSSU | Middle | Middle-High |
| FIKSSM | High | High |
| Number of Unverified Software | Security Score | Connection Range of Comparative Signature Scheme | Connection Range of Our Proposed Signature Scheme |
|---|---|---|---|
| 0 | 100–81 | 4 hop | 4 hop |
| 1 | 80–61 | 4 hop | 3 hop |
| 2 | 60–41 | 4 hop | 2 hop |
| 3 | 40–0 | 4 hop | 1 hop |
| Execution Factors | Algorithm | PKSS | FKSSU | FIKSSM |
|---|---|---|---|---|
| File Size | Private Key | 1 Kbyte | 10 Kbyte | 10 Kbyte |
| Public Key | 1 Kbyte | 1 Kbyte | 1 Kbyte | |
| Public key Certificate | 1 Kbyte | 1 Kbyte | 1 Kbyte | |
| Signature in a Blockchain Transaction | 71 byte | 71 byte | 71 byte | |
| Processing Time | Public key Generation | 300 ms | 499 ms | 400 ms |
| Signature Generation | 78 ms | 1306 ms | 74 ms | |
| Signature Verification | 70 ms | 70 ms | 60 ms |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
A. Hassen, O.; A. Abdulhussein, A.; M. Darwish, S.; Othman, Z.A.; Tiun, S.; A. Lotfy, Y. Towards a Secure Signature Scheme Based on Multimodal Biometric Technology: Application for IOT Blockchain Network. Symmetry 2020, 12, 1699. https://doi.org/10.3390/sym12101699
A. Hassen O, A. Abdulhussein A, M. Darwish S, Othman ZA, Tiun S, A. Lotfy Y. Towards a Secure Signature Scheme Based on Multimodal Biometric Technology: Application for IOT Blockchain Network. Symmetry. 2020; 12(10):1699. https://doi.org/10.3390/sym12101699
Chicago/Turabian StyleA. Hassen, Oday, Ansam A. Abdulhussein, Saad M. Darwish, Zulaiha Ali Othman, Sabrina Tiun, and Yasmin A. Lotfy. 2020. "Towards a Secure Signature Scheme Based on Multimodal Biometric Technology: Application for IOT Blockchain Network" Symmetry 12, no. 10: 1699. https://doi.org/10.3390/sym12101699
APA StyleA. Hassen, O., A. Abdulhussein, A., M. Darwish, S., Othman, Z. A., Tiun, S., & A. Lotfy, Y. (2020). Towards a Secure Signature Scheme Based on Multimodal Biometric Technology: Application for IOT Blockchain Network. Symmetry, 12(10), 1699. https://doi.org/10.3390/sym12101699








