Double JPEG Compression Detection Based on Noise-Free DCT Coefficients Mixture Histogram Model
Abstract
1. Introduction
2. Preliminaries
2.1. JPEG Compression
- (1)
- DCT transform: an image is first divided into DCT blocks (with size 8 × 8). Each block is subtracted by 128 and transformed to the YCbCr color space. Then, DCT transform is applied to each channel of the DCT block.
- (2)
- Quantization: the DCT coefficients at each frequency are divided by a quantization step and rounded to the nearest integer.
- (3)
- Entropy coding: lossless entropy coding of the quantized DCT coefficients.
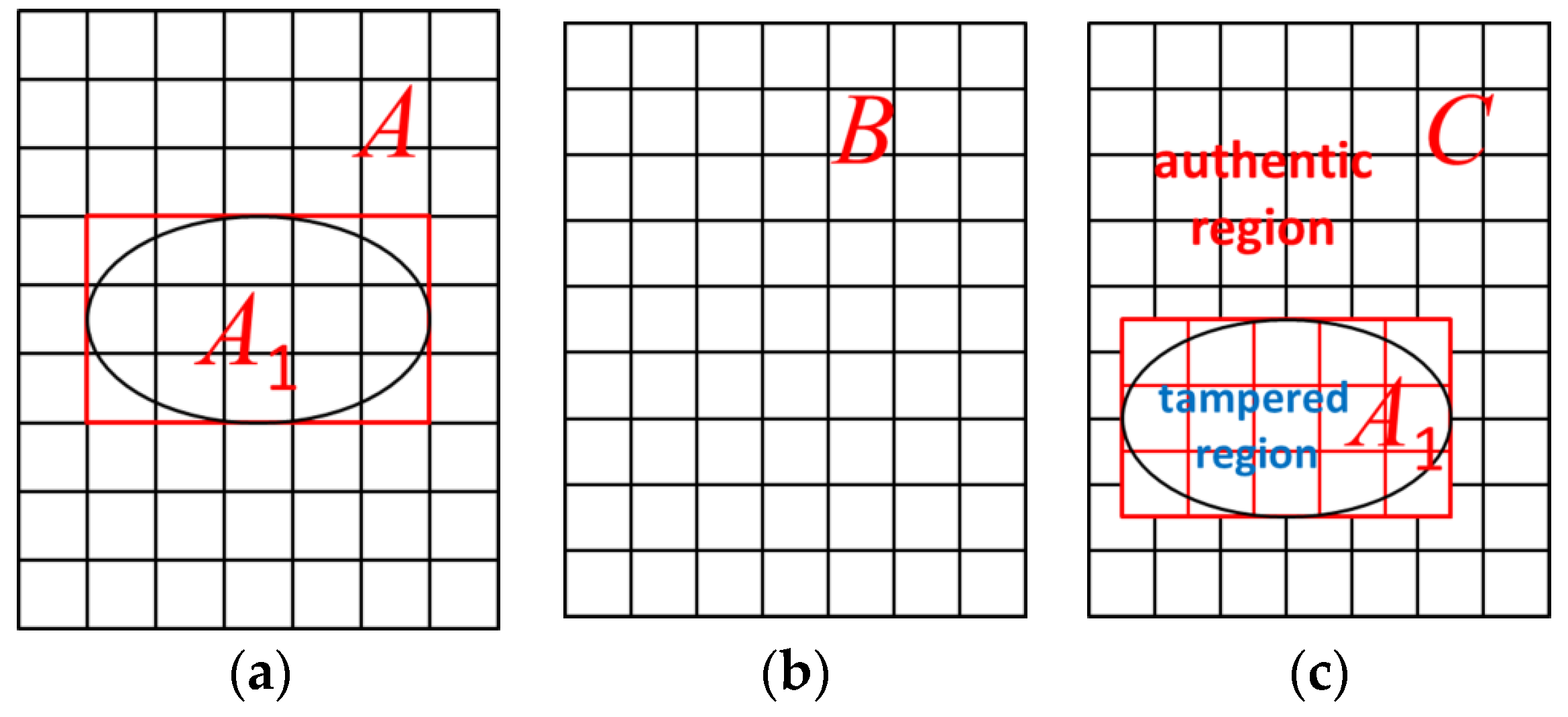
2.2. JPEG Image Tampering Model
- (1)
- Choosing a portion A1 from an image A.
- (2)
- Pasting A1 into a JPEG compressed image B or altering a selected region in B with image editing tools directly.
- (3)
- Saving the forgery image as image C in JPEG or any lossless format (in this case, we will re-save the image as JPEG format with a compression quality factor 100 before detection).
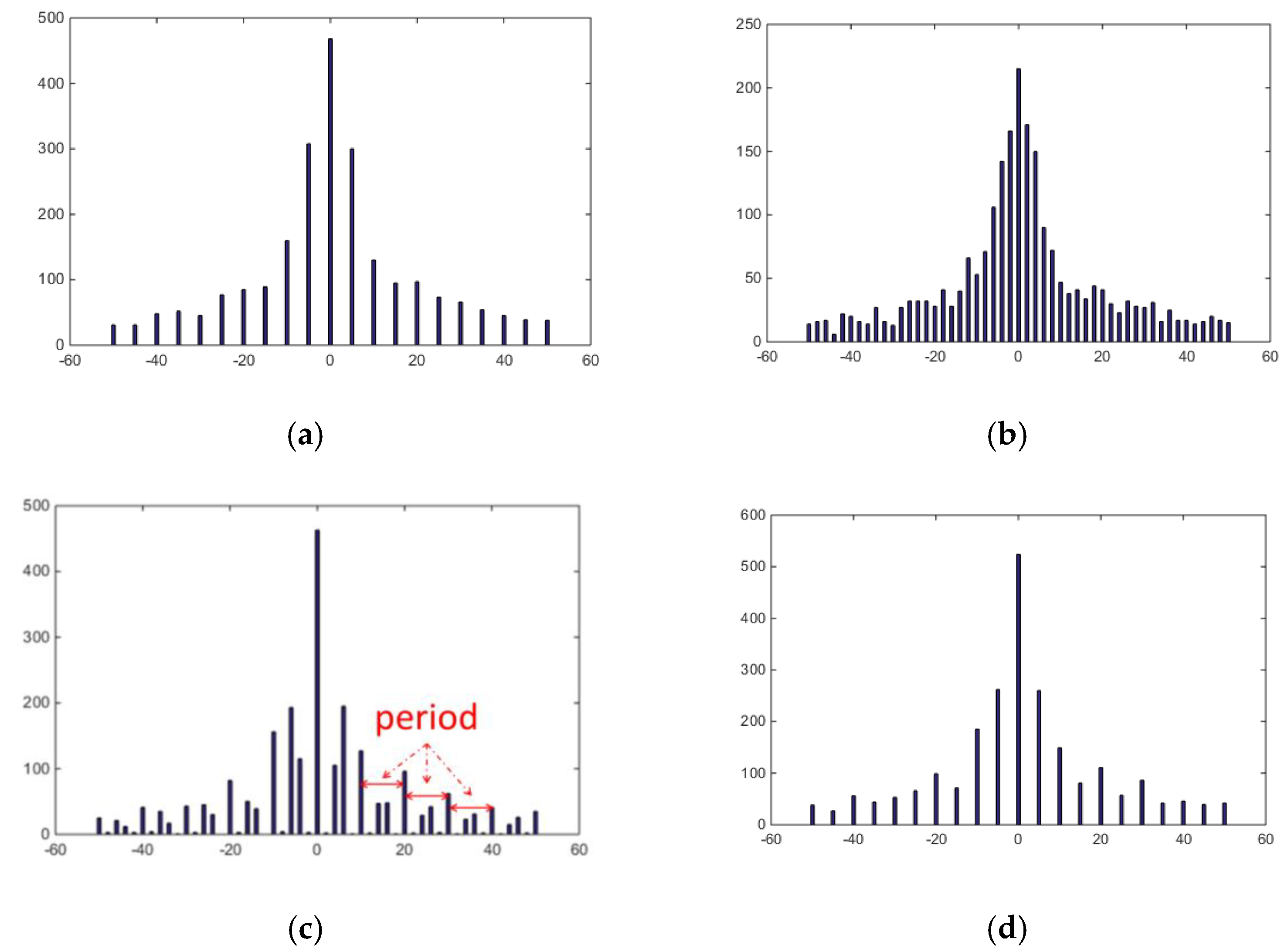
2.3. Double Quantization (DQ) Artifact
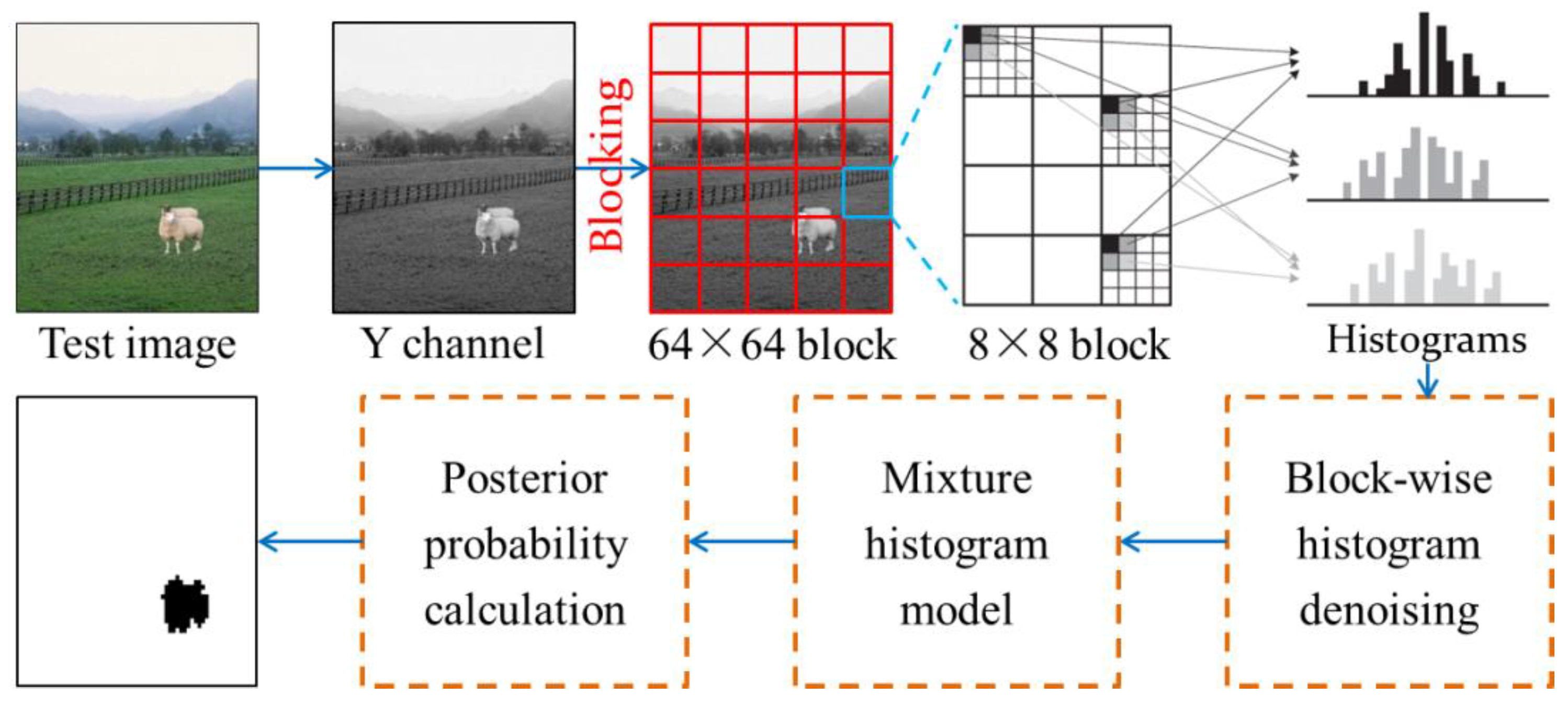
3. Proposed Method
3.1. Quantization Noise Removal
3.2. Tampered Region Localization
4. Experiments and Discussion
4.1. Quantitative Experiments
4.2. Qualitative Experiments
4.3. Computational Complexity
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Birajdar, G.K.; Mankar, V.H. Digital image forgery detection using passive techniques: A survey. Digit. Investig. 2013, 10, 226–245. [Google Scholar] [CrossRef]
- Korus, P. Digital image integrity—A survey of protection and verification techniques. Digit. Signal Process. 2017, 71, 1–26. [Google Scholar] [CrossRef]
- Chang, T.Y.; Tai, S.C.; Lin, G.S. A passive multi-purpose scheme based on periodicity analysis of CFA artifacts for image forensics. J. Vis. Commun. Image Represent. 2014, 25, 1289–1298. [Google Scholar] [CrossRef]
- Chierchia, G.; Poggi, G.; Sansone, C.; Verdoliva, L. A Bayesian-MRF approach for PRNU-based image forgery detection. IEEE Trans. Inf. Forensics Secur. 2014, 9, 554–567. [Google Scholar] [CrossRef]
- Hsu, Y.F.; Chang, S.F. Camera response functions for image forensics: An automatic algorithm for splicing detection. IEEE Trans. Inf. Forensics Secur. 2010, 5, 816–825. [Google Scholar] [CrossRef]
- Cao, G.; Zhao, Y.; Ni, R.R.; Li, X.L. Contrast enhancement-based forensics in digital images. IEEE Trans. Inf. Forensics Secur. 2014, 9, 515–525. [Google Scholar] [CrossRef]
- Bahrami, K.; Kot, A.C.; Li, L.D.; Li, H.L. Blurred image splicing localization by exposing blur type inconsistency. IEEE Trans. Inf. Forensics Secur. 2015, 10, 999–1009. [Google Scholar] [CrossRef]
- Zhu, N.; Deng, C.; Gao, X.B. A learning-to-rank approach for image scaling factor estimation. Neurocomputing 2016, 204, 33–40. [Google Scholar] [CrossRef]
- Zhu, N.; Deng, C.; Gao, X.B. Image sharpening detection based on multiresolution overshoot artifact analysis. Multimed. Tools Appl. 2017, 76, 16563–16580. [Google Scholar] [CrossRef]
- Zhu, N.; Li, Z. Blind image splicing detection via noise level function. Signal Process. Image Commun. 2018, 68, 181–192. [Google Scholar] [CrossRef]
- Yao, H.; Wang, S.Z.; Zhao, Y.; Zhang, X.P. Detecting image forgery using perspective constraints. IEEE Signal Process. Lett. 2012, 19, 123–126. [Google Scholar] [CrossRef]
- Luo, W.Q.; Qu, Z.H.; Huang, J.W.; Qiu, G.P. A novel method for detecting cropped and recompressed image block. In Proceedings of the IEEE International Conference on Acoustics, Speech, and Signal Processing (ICASSP), Honolulu, HI, USA, 15–20 April 2007; pp. II-217–II-220. [Google Scholar]
- Qu, Z.H.; Luo, W.Q.; Huang, J.W. A convolutive mixing model for shifted double JPEG compression with application to passive image authentication. In Proceedings of the IEEE International Conference on Acoustics, Speech, and Signal Processing (ICASSP), Las Vegas, NV, USA, 30 March–4 April 2008; pp. 1661–1664. [Google Scholar]
- Bianchi, T.; Piva, A. Detection of nonaligned double JPEG compression based on integer periodicity maps. IEEE Trans. Inf. Forensics Secur. 2012, 7, 842–848. [Google Scholar] [CrossRef]
- Lin, Z.C.; He, J.F.; Tang, X.O.; Tang, C.K. Fast, automatic and fine-grained tampered JPEG image detection via DCT coefficient analysis. Pattern Recogn. 2009, 42, 2492–2501. [Google Scholar] [CrossRef]
- Zhang, R.; Yu, X.G.; Zhao, J.; Liu, J.Y. Symmetric alpha stable distribution model application in detecting double JPEG compression. In Proceedings of the International Conference on Artificial Intelligence and Software Engineering (AISE), Phuket, Thailand, 11–12 January 2014; pp. 462–467. [Google Scholar]
- Bianchi, T.; Piva, A. Image forgery localization via block-grained analysis of JPEG artifacts. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1003–1017. [Google Scholar] [CrossRef]
- Yu, L.Y.; Han, Q.; Niu, X.M.; Yiu, S.M.; Fang, J.B.; Zhang, Y. An improved parameter estimation scheme for image modification detection based on DCT coefficient analysis. Forensic Sci. Int. 2016, 259, 200–209. [Google Scholar] [CrossRef]
- Wang, W.; Dong, J.; Tan, T.N. Exploring DCT coefficient quantization effects for local tampering detection. IEEE Trans. Inf. Forensics Secur. 2014, 9, 1653–1666. [Google Scholar] [CrossRef]
- Lin, C.S.; Tsay, J.J. Passive forgery detection using discrete cosine transform coefficient analysis in JPEG compressed images. J. Electron. Imaging 2016, 25, 033010-1–033010-6. [Google Scholar] [CrossRef]
- Wang, Q.; Zhang, R. Double JPEG compression forensics based on a convolutional neural network. EURASIP J. Inf. Secur. 2016, 2016, 23. [Google Scholar] [CrossRef]
- Amerini, I.; Becarelli, R.; Caldelli, R.; Mastio, A.D. Splicing forgeries localization through the use of first digit features. In Proceedings of the IEEE International Workshop on Information Forensics and Security, Atlanta, GA, USA, 3–5 December 2014; pp. 143–148. [Google Scholar]
- Taimori, A.; Razzazi, F.; Behrad, A.; Ahmadi, A.; Babaie-Zadeh, M. Quantization-unaware double JPEG compression detection. J. Math. Imaging Vis. 2016, 54, 269–286. [Google Scholar] [CrossRef]
- Galvan, F.; Puglisi, G.; Bruna, A.R.; Battiato, S. First quantization matrix estimation from double compressed JPEG images. IEEE Trans. Inf. Forensics Secur. 2014, 9, 1299–1310. [Google Scholar] [CrossRef]
- Singh, G.; Singh, K. Forensics for partially double compressed doctored JPEG images. Multimed. Tools Appl. 2018, 77, 485–502. [Google Scholar] [CrossRef]
- Image Dataset for Localization of Double JPEG Compression. Available online: Ftp://lesc.dinfo.unifi.it/pub/Public/JPEGloc/ (accessed on 31 July 2019).
- CASIA Tampered Image Detection Evaluation Database. Available online: http://forensics.idealtest.org/ (accessed on 5 May 2019).
- Luo, D.; Yang, R.; Li, B.; Huang, J.W. Detection of double compressed AMR audio using stacked autoencoder. IEEE Trans. Inf. Forensics Secur. 2017, 12, 432–444. [Google Scholar] [CrossRef]
- Bian, S.; Li, H.L.; Gu, T.J.; Kot, A.C. Exposing video compression history by detecting transcoded HEVC videos from AVC coding. Symmetry 2019, 11, 67. [Google Scholar] [CrossRef]
- Yao, H.; Song, S.H.; Qin, C.; Tang, Z.J.; Liu, X.K. Detection of double-compressed H.264/AVC video incorporating the features of the string of data bits and skip macroblocks. Symmetry 2017, 9, 313. [Google Scholar] [CrossRef]



| QF2 QF1 | 60 | 70 | 80 | 90 | 100 | QF2 QF1 | 60 | 70 | 80 | 90 | 100 | ||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 50 | [19] | 0.7243 | 0.8904 | 0.8399 | 0.8231 | 0.9039 | 50 | [22] | 0.7286 | 0.9560 | 0.9819 | 0.9812 | 0.9849 |
| [18] | 0.7607 | 0.8875 | 0.9498 | 0.9822 | 0.9806 | Our | 0.7662 | 0.9565 | 0.9861 | 0.9883 | 0.9857 | ||
| 60 | [19] | — | 0.6029 | 0.8322 | 0.8462 | 0.9120 | 60 | [22] | — | 0.7322 | 0.9611 | 0.9819 | 0.9853 |
| [18] | — | 0.8032 | 0.9318 | 0.9786 | 0.9806 | Our | — | 0.8024 | 0.9796 | 0.9900 | 0.9926 | ||
| 70 | [19] | — | — | 0.7840 | 0.8615 | 0.8997 | 70 | [22] | — | — | 0.8701 | 0.9842 | 0.9825 |
| [18] | — | — | 0.8546 | 0.9750 | 0.9792 | Our | — | — | 0.8908 | 0.9905 | 0.9903 | ||
| 80 | [19] | — | — | — | 0.8012 | 0.9131 | 80 | [22] | — | — | — | 0.8931 | 0.9830 |
| [18] | — | — | — | 0.9248 | 0.9841 | Our | — | — | — | 0.9317 | 0.9884 | ||
| 90 | [19] | — | — | — | — | 0.8620 | 90 | [22] | — | — | — | — | 0.8899 |
| [18] | — | — | — | — | 0.9534 | Our | — | — | — | — | 0.9408 | ||
| QF2 QF1 | 60 | 70 | 80 | 90 | 100 | QF2 QF1 | 60 | 70 | 80 | 90 | 100 | ||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 50 | [19] | 0.6651 | 0.7865 | 0.8975 | 0.9685 | 0.8668 | 50 | [22] | 0.7324 | 0.8892 | 0.9069 | 0.9146 | 0.9154 |
| [18] | 0.7160 | 0.8896 | 0.8980 | 0.9137 | 0.9053 | Our | 0.8359 | 0.9128 | 0.9217 | 0.9243 | 0.9243 | ||
| 60 | [19] | — | 0.8531 | 0.8851 | 0.9132 | 0.8433 | 60 | [22] | — | 0.6809 | 0.8976 | 0.8938 | 0.8888 |
| [18] | — | 0.7063 | 0.8942 | 0.8942 | 0.8885 | Our | — | 0.7236 | 0.9033 | 0.9010 | 0.8878 | ||
| 70 | [19] | — | — | 0.7176 | 0.8923 | 0.8547 | 70 | [22] | — | — | 0.6503 | 0.8961 | 0.8897 |
| [18] | — | — | 0.7470 | 0.8937 | 0.8902 | Our | — | — | 0.7578 | 0.8972 | 0.8955 | ||
| 80 | [19] | — | — | — | 0.7871 | 0.8351 | 80 | [22] | — | — | — | 0.7278 | 0.8760 |
| [18] | — | — | — | 0.7574 | 0.8780 | Our | — | — | — | 0.7628 | 0.8896 | ||
| 90 | [19] | — | — | — | — | 0.7987 | 90 | [22] | — | — | — | — | 0.7444 |
| [18] | — | — | — | — | 0.7996 | Our | — | — | — | — | 0.8048 | ||
| QF2 QF1 | 60 | 70 | 80 | 90 | 100 | QF2 QF1 | 60 | 70 | 80 | 90 | 100 | ||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 50 | [19] | 0.6934 | 0.8352 | 0.8677 | 0.8899 | 0.8850 | 50 | [22] | 0.7305 | 0.9214 | 0.9429 | 0.9467 | 0.9489 |
| [18] | 0.7377 | 0.8885 | 0.9231 | 0.9467 | 0.9415 | Our | 0.7995 | 0.9341 | 0.9528 | 0.9552 | 0.9540 | ||
| 60 | [19] | — | 0.7065 | 0.8579 | 0.8784 | 0.8763 | 60 | [22] | — | 0.7056 | 0.9283 | 0.9358 | 0.9346 |
| [18] | — | 0.7516 | 0.9126 | 0.9345 | 0.9323 | Our | — | 0.7610 | 0.9399 | 0.9434 | 0.9373 | ||
| 70 | [19] | — | — | 0.7494 | 0.8766 | 0.8766 | 70 | [22] | — | — | 0.7443 | 0.9381 | 0.9338 |
| [18] | — | — | 0.7972 | 0.9326 | 0.9326 | Our | — | — | 0.8189 | 0.9415 | 0.9405 | ||
| 80 | [19] | — | — | — | 0.7941 | 0.8724 | 80 | [22] | — | — | — | 0.8020 | 0.9264 |
| [18] | — | — | — | 0.8328 | 0.9281 | Our | — | — | — | 0.8388 | 0.9364 | ||
| 90 | [19] | — | — | — | — | 0.8291 | 90 | [22] | — | — | — | — | 0.8107 |
| [18] | — | — | — | — | 0.8698 | Our | — | — | — | — | 0.8675 | ||
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhu, N.; Shen, J.; Niu, X. Double JPEG Compression Detection Based on Noise-Free DCT Coefficients Mixture Histogram Model. Symmetry 2019, 11, 1119. https://doi.org/10.3390/sym11091119
Zhu N, Shen J, Niu X. Double JPEG Compression Detection Based on Noise-Free DCT Coefficients Mixture Histogram Model. Symmetry. 2019; 11(9):1119. https://doi.org/10.3390/sym11091119
Chicago/Turabian StyleZhu, Nan, Junge Shen, and Xiaotong Niu. 2019. "Double JPEG Compression Detection Based on Noise-Free DCT Coefficients Mixture Histogram Model" Symmetry 11, no. 9: 1119. https://doi.org/10.3390/sym11091119
APA StyleZhu, N., Shen, J., & Niu, X. (2019). Double JPEG Compression Detection Based on Noise-Free DCT Coefficients Mixture Histogram Model. Symmetry, 11(9), 1119. https://doi.org/10.3390/sym11091119





