A New Lightweight Stream Cipher Based on Chaos
Abstract
1. Introduction
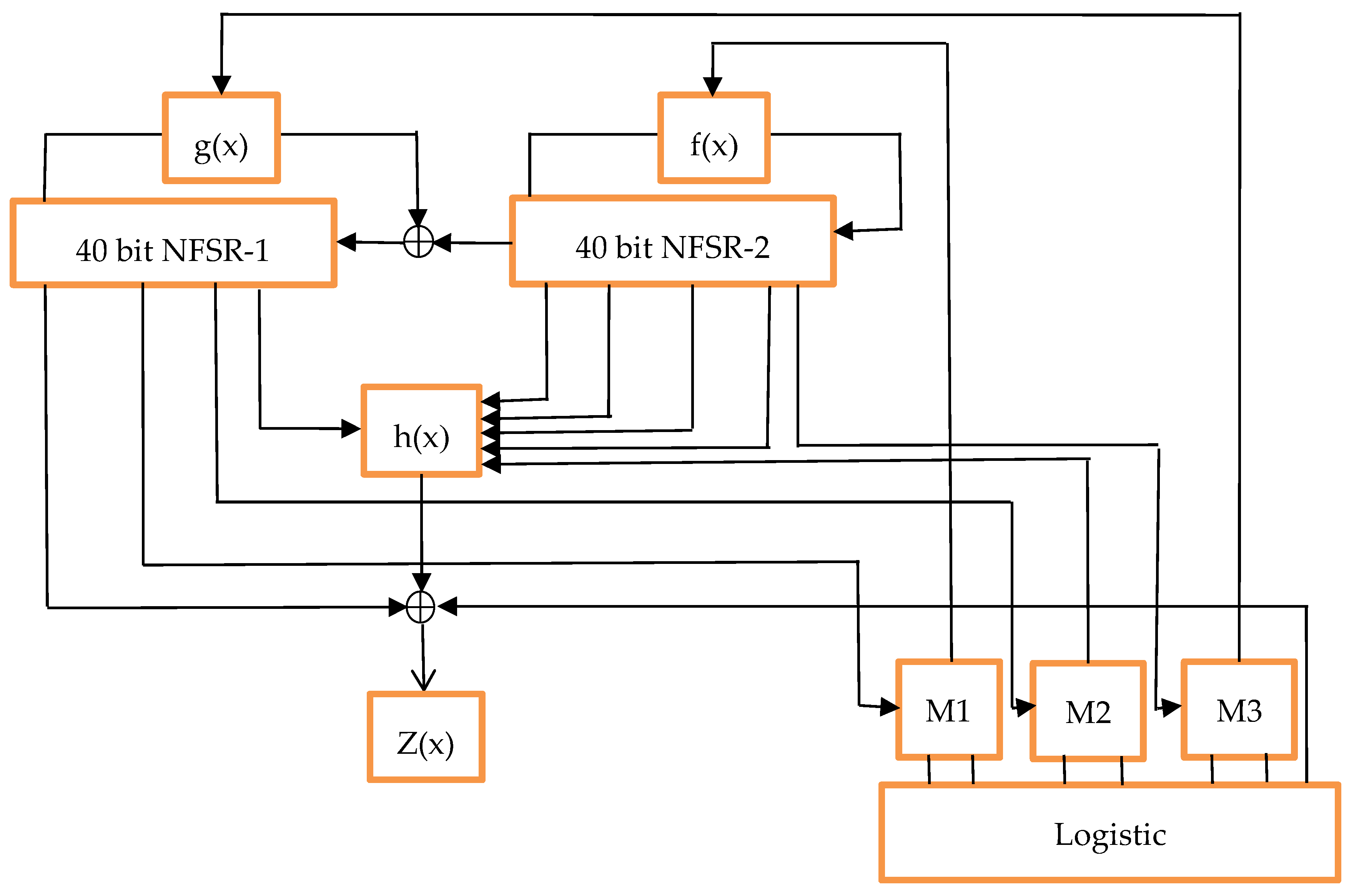
2. Chaotic Sequence and Quantization
3. Logic Lightweight Stream Cipher
4. Design Principles
4.1. Two NFSRs
4.2. Digital Chaotic Module
4.3. Filter Function
4.4. Multiplexer Unit
5. Entropy Analyses
5.1. Permutation Entropy
- There is a discrete time series , , …, with length N, then an embedding dimension and a time delay τ are specified.
- By reconstructing the original sequence, each sub-sequence is represented as , and , , …, .
- Subsequently, incremental sorting is performed on each interior , i.e., , if the two values are equal, the order is based on the subscripts in . In this way, is mapped to (j1, j2, …, jm), which is just one of permutations. In other words, each subsequence of dimension is mapped to one of permutations.
- Through the above steps, the continuous dimensional subspace is represented by a sequence of such symbols, in which the number of these symbols is . The probabilities of all symbols are expressed by , , …, , where .
- The permutation entropy of the time series , , …, is:
5.2. Approximate Entropy
- Let , , …, be a time series of dimension , which is obtained by sampling at equal intervals.
- The relevant parameters and of the algorithm are defined, in which is an integer that represents the length of comparison vectors and is a real number using the measure of similarity.
- Here, the dimension vectors are reconstructed as , , …, , where .
- For , the number of vectors satisfying the following conditions is counted.
- 5.
- Let us define
- 6.
- The approximate entropy (ApEn) is defined as
5.3. Information Entropy
6. Statistical Tests
7. Hardware Implementation Analysis
7.1. Comparison of Implementation Results
7.2. Throughtput Analysis
8. Security Evaluation
8.1. Algebraic Attack
8.2. TMDTO Attack
8.3. Fault Attack
8.4. Linear Approximation Attack
8.5. Correlation Attack
9. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
References
- eSTREAM—The ECRYPT Stream Cipher Project [EB/OL]. Available online: http://www.ecrypt.eu.org/stream/ (accessed on 26 May 2019).
- Armknecht, F.; Mikhalev, V. On lightweight stream ciphers with shorter internal states. In International Workshop on Fast Software Encryption; Springer: Berlin/Heidelberg, Germany, 2015; pp. 451–470. [Google Scholar]
- Ghafari, V.A.; Hu, H.; Xie, C. Fruit: Ultra-Lightweight Stream Cipher with Shorter Internal State. Available online: http://eprint.iacr.org/2016/355 (accessed on 26 May 2019).
- Hamann, M.; Krause, M.; Meier, W. LIZARD—A lightweight stream cipher for power-constrained devices. IACR Trans. Symmetric Cryptol. 2017, 45–79. [Google Scholar]
- Mikhalev, V.; Armknecht, F.; Müller, C. On ciphers that continuously access the non-volatile key. IACR Trans. Symmetric Cryptol. 2016, 52–79. [Google Scholar]
- Cannière, C.D. Trivium: A Stream Cipher Construction Inspired by Block Cipher Design Principles. Lect. Notes Comput. Sci. 2006, 4176, 171–186. [Google Scholar]
- Babbage, S.; Dodd, M. The Stream Cipher MICKEY 2.0. ECRYPT Stream Cipher. Available online: http://www.ecrypt.eu.org/stream/p3ciphers/mickey/mickey_p3.pdf (accessed on 26 May 2019).
- Hell, M.; Johansson, T.; Meier, W. Grain: A stream cipher for constrained environments. Int. J. Wirel. Mob. Comput. 2007, 2, 86–93. [Google Scholar] [CrossRef]
- Hell, M.; Johansson, T.; Maximov, A.; Meier, W. A stream cipher proposal: Grain-128. In Proceedings of the IEEE International Symposium on Information Theory (ISIT 2006), Seattle, WA, USA, 9–14 July 2006. [Google Scholar]
- Ågren, M.; Hell, M.; Johansson, T.; Meier, W. Grain-128a: A new version of Grain-128 with optional authentication. Int. J. Wirel. Mob. Comput. 2011, 5, 48–59. [Google Scholar] [CrossRef]
- Lee, Y.; Jeong, K.; Sung, J.; Hong, S. Related-Key Chosen IV Attacks on Grain-v1 and Grain-128. Lect. Notes Comput. Sci. 2008, 5107, 321–335. [Google Scholar]
- Aumasson, J.; Dinur, I.; Henzen, L.; Meier, W.; Shamir, A. Efficient FPGA Implementations of High-Dimensional Cube Testers on the Stream Cipher Grain-128. IACR Cryptol. ePrint Arch. 2009, 2009, 218. [Google Scholar]
- Dinur, I.; Güneysu, T.; Paar, C.; Shamir, A.; Zimmermann, R. An Experimentally Verified Attack on Full Grain-128 Using Dedicated Reconfigurable Hardware. Lect. Notes Comput. Sci. 2011, 7073, 327–343. [Google Scholar]
- Dinur, I.; Shamir, A. Breaking Grain-128 with Dynamic Cube Attacks. Lect. Notes Comput. Sci. 2011, 6733, 167–187. [Google Scholar]
- Knellwolf, S.; Meier, W.; Naya-Plasencia, M. Conditional Differential Cryptanalysis of NLFSR-Based Cryptosystems. Lect. Notes Comput. Sci. 2010, 6477, 130–145. [Google Scholar]
- Mihaljevic, M.J.; Gangopadhyay, S.; Paul, G.; Imai, H. Generic cryptographic weakness of k-normal Boolean functions in certain stream ciphers and cryptanalysis of grain-128. Period. Math. Hung. 2012, 65, 205–227. [Google Scholar] [CrossRef]
- Stankovski, P. Greedy Distinguishers and Nonrandomness Detectors. Lect. Notes Comput. Sci. 2010, 6498, 210–226. [Google Scholar]
- Vaidyanathan, S.; Akgul, A.; Kacar, S.; Cavusoglu, U. A new 4-D chaotic hyperjerk system, its synchronization, circuit design and applications in RNG, image encryption and chaos-based steganography. Eur. Phys. J. Plus 2018, 133, 46. [Google Scholar] [CrossRef]
- Murillo-Escobar, M.A.; Cruz-Hernandez, C.; Abundiz-Perez, F.; Lopez-Gutierrez, R.M.; Del Campo, O.R.A. A RGB image encryption algorithm based on total plain image characteristics and chaos. Signal Process. 2015, 109, 119–131. [Google Scholar] [CrossRef]
- Wang, Y.; Lei, P.; Yang, H.Q.; Cao, H.Y. Security analysis on a color image encryption based on DNA encoding and chaos map. Comput. Electr. Eng. 2015, 46, 433–446. [Google Scholar] [CrossRef]
- Ye, G.; Pan, C.; Huang, X.; Zhao, Z.; He, J. A Chaotic Image Encryption Algorithm Based on Information Entropy. Int. J. Bifurc. Chaos 2018, 28, 1850010. [Google Scholar] [CrossRef]
- Liu, H.J.; Kadir, A.; Sun, X.B. Chaos-based fast colour image encryption scheme with true random number keys from environmental noise. IET Image Process. 2017, 11, 324–332. [Google Scholar] [CrossRef]
- Ping, P.; Xu, F.; Mao, Y.C.; Wang, Z.J. Designing permutation-substitution image encryption networks with Henon map. Neurocomput. 2018, 283, 53–63. [Google Scholar] [CrossRef]
- Helmy, M.; El-Rabaie, E.; Eldokany, I. Chaotic encryption with different modes of operation based on Rubik’s cube for efficient wireless communication. Multimedia Tools Appl. 2018, 77, 27337–27361. [Google Scholar] [CrossRef]
- Sangeetha, M.; Bhaskar, V. NR-DCSK based Chaotic Communications in MIMO Multipath Channels. Wirel. Personal Commun. 2018, 103, 1819–1834. [Google Scholar] [CrossRef]
- Guler, H.; Celik, V.; Kaya, T. The Real Time Implementation of a Chaotic System’s Synchronization for Secure Communication. Tehnički vjesnik 2018, 25, 43–48. [Google Scholar]
- Jiang, Y.; Tang, S. An efficient and secure VoIP communication system with chaotic mapping and message digest. Multimedia Syst. 2018, 24, 355–363. [Google Scholar] [CrossRef]
- Zheng, Q.; Wang, X.; Khan, M.K.; Zhang, W.; Gupta, B.B.; Guo, W.A. Lightweight Authenticated Encryption Scheme Based on Chaotic SCML for Railway Cloud Service. IEEE Access 2018, 6, 711–722. [Google Scholar] [CrossRef]
- Janakiraman, S.; Thenmozhi, K.; Rayappan, J.B.B.; Amirtharajan, R. Lightweight chaotic image encryption algorithm for real-time embedded system: Implementation and analysis on 32-bit microcontroller. Microprocessors Microsyst. 2018, 56, 1–12. [Google Scholar] [CrossRef]
- Bandt, C.; Pompe, B. Permutation Entropy: A Natural Complexity Measure for Time Series. Phys. Rev. Lett. 2002, 88, 174102. [Google Scholar] [CrossRef] [PubMed]
- Pincus, S.M. Approximate entropy as a measure of system complexity. Proc. Natl. Acad. Sci. USA 1991, 88, 2297–2301. [Google Scholar] [CrossRef] [PubMed]
- Pincus, S. Approximate entropy (ApEn) as a complexity measure. Chaos Interdiscip. J. Nonlinear Sci. 1995, 5, 110–117. [Google Scholar] [CrossRef] [PubMed]
- Zhang, C.T.; Ma, Q.L.; Peng, H. Chaotic time series prediction based on information entropy optimized parameters of phase space reconstruction. Acta. Phys. Sin. 2010, 59, 7623–7629. [Google Scholar]
- Li, Y.; Li, Y.; Chen, X.; Yu, J.; Yang, H.; Wang, L. A New Underwater Acoustic Signal Denoising Technique Based on CEEMDAN, Mutual Information, Permutation Entropy, and Wavelet Threshold Denosing. Entropy 2018, 20, 563. [Google Scholar] [CrossRef]
- Montesinos, L.; Castaldo, R.; Pecchia, L. On the use of approximate entropy and sample entropy with centre of pressure time-series. J. NeuroEng. Rehabilitation 2018, 15, 116. [Google Scholar] [CrossRef]
- Fan, C.; Xie, Z.; Ding, Q. A Novel Algorithm to Improve Digital Chaotic Sequence Complexity through CCEMD and PE. Entropy 2018, 20, 295. [Google Scholar] [CrossRef]
- Thomas, E.; Christof, P.; Axel, P.; Sandeep, K. A Survey of Lightweight Cryptography Implementations. IEEE Des. Test Comput. 2007, 24, 522–533. [Google Scholar]
- Courtois, N.T.; Meier, W. Algebraic attacks on stream ciphers with linear feedback. In International Conference on the Theory and Applications of Cryptographic Techniques; Springer: Berlin/Heidelberg, Germany, 2003; pp. 345–359. [Google Scholar]
- Lobanov, M.S. Exact relation between onolinearity and algebraic immunity. Discrete Math. Appl. 2006, 16, 453–460. [Google Scholar] [CrossRef]
- Carlet, C. On the higher order nonlinearities of algebraic immune functions. In Annual International Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 2006; pp. 584–601. [Google Scholar]
- Biryukov, A.; Shamir, A. Cryptanalytic time/memory/data tradeoffs for stream ciphers. In International Conference on the Theory and Application of Cryptology and Information Security; Springer: Berlin/Heidelberg, Germany, 2000; pp. 1–13. [Google Scholar]
- Bjostad, T.E. Crypanalysis of Grain using Time/Memory/Data Tradeoffs. Available online: http://www.ecrypt.eu.org/stream (accessed on 26 May 2019).
- Hong, J.; Kim, W.H. Tmd-tradeoff and state entropy loss considerations of streamcipher mickey. In International Conference on Cryptology in India; Springer: Berlin/Heidelberg, Germany, 2005; pp. 169–182. [Google Scholar]
- Banik, S.; Maitra, S.; Sarkar, S. A Differential Fault Attack on the Grain Family of Stream Ciphers. Lect. Notes Comput. Sci. 2012, 7428, 122–139. [Google Scholar]
- Berzati, A.; Canovas, C.; Castagons, G.; Debraize, B.; Goubin, L.; Gouget, A.; Paillier, P.; Salgado, S. Fault analysis of GRAIN-128. In Proceedings of the IEEE International Workshop on Hardware-Oriented Secutrity and Trust, Francisco, CA, USA, 27 July 2009; pp. 7–14. [Google Scholar]
- Maximov, A. Cryptanalysis of the “Grain” family of stream ciphers. In Proceedings of the 2006 ACM Symposium on Information, Computer and Communications Security, Taipei, Taiwan, 21–24 March 2006; ACM: New York, NY, USA, 2006; pp. 283–288. [Google Scholar]
| Time Series | PE | ||
|---|---|---|---|
| Logistic | 3 | 1 | 0.3854 |
| Logic | 3 | 1 | 0.5982 |
| Time Series | ApEn | |||
|---|---|---|---|---|
| Logistic | 2 | 0.1013 | 2048 | 0.6655 |
| Logic | 2 | 0.1015 | 2048 | 0.9442 |
| Time Series | InEn |
|---|---|
| Logistic | 0.5951 |
| Logic | 0.9238 |
| Test | Test | |
|---|---|---|
| Frequency Test | 0.400908 | Success |
| Frequency Test within a Block | 0.861626 | Success |
| Runs Test | 0.475849 | Success |
| Test for the Longest Run of Ones in a Block | 0.199175 | Success |
| Binary Matrix Rank Test | 0.949536 | Success |
| Discrete Fourier Transform Test | 0.232884 | Success |
| Non-Overlapping Template Matching Test | 0.815009 | Success |
| Overlapping Template Matching Test | 0.751585 | Success |
| Maurer’s “Universal Statistical” Test | 0.139146 | Success |
| Linear Complexity Test | 0.359316 | Success |
| Serial Test | 0.067079 | Success |
| Approximation Entropy Test | 0.011645 | Success |
| Cumulative Sums Test | 0.557894 | Success |
| Random Excursions Test | 0.459642 | Success |
| Random Excursions Variant Test | 0.254816 | Success |
| Cipher | Key Size (bits) | Area Size (GEs) | Throughput (Kb/s) | Platform |
|---|---|---|---|---|
| Trivium [6] | 80 | 2580 | 100 | 0.13μmCMOS |
| DES [37] | 56 | 2309 | 100 | 0.18μmCMOS |
| Grain-v1 [8] | 80 | 1294 | 100 | 0.13μmCMOS |
| Lizard [4] | 120 | 1161 | 100 | 0.18μmCMOS |
| HIGHT [37] | 128 | 3048 | 100 | 0.25μmCMOS |
| Mickey 2.0 [7] | 80 | 3188 | 100 | 0.13μmCMOS |
| Logic (Our work) | 80 | 2258 | 100 | 0.13μmCMOS |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ding, L.; Liu, C.; Zhang, Y.; Ding, Q. A New Lightweight Stream Cipher Based on Chaos. Symmetry 2019, 11, 853. https://doi.org/10.3390/sym11070853
Ding L, Liu C, Zhang Y, Ding Q. A New Lightweight Stream Cipher Based on Chaos. Symmetry. 2019; 11(7):853. https://doi.org/10.3390/sym11070853
Chicago/Turabian StyleDing, Lina, Chunyuan Liu, Yanpeng Zhang, and Qun Ding. 2019. "A New Lightweight Stream Cipher Based on Chaos" Symmetry 11, no. 7: 853. https://doi.org/10.3390/sym11070853
APA StyleDing, L., Liu, C., Zhang, Y., & Ding, Q. (2019). A New Lightweight Stream Cipher Based on Chaos. Symmetry, 11(7), 853. https://doi.org/10.3390/sym11070853





