Ephemeral-Secret-Leakage Secure ID-Based Three-Party Authenticated Key Agreement Protocol for Mobile Distributed Computing Environments
Abstract
:1. Introduction
2. Preliminaries
2.1. Bilinear Pairings
- Bilinearity: Let , we have:
- (1)
- .
- (2)
- .
- (3)
- .
- Non-degeneracy: There exist such that .
- Computable: For , there exists an efficient algorithm to compute .
2.2. Computational Problems
- Discrete Logarithm Problem (DLP): Give ; find an integer such that whenever such integer exists.
- Computational Diffie-Hellman Problem (CDHP): Given for unknown , the CDHP is to compute the value .
2.3. Security Attributes
- Known-Key Security. A unique session key should be constructed in each round of an AKA protocol. An adversary cannot derive other previous session keys if knowledge of the previous session keys has been compromised. The main purpose of known-key security is to ensure that the compromising of one session key will not compromise other or future session keys.
- Forward Secrecy. If the long-term private keys of one or more of the participants are compromised, the secrecy of previously established session keys will not be obtained by an adversary. The main purpose of forward secrecy is to provide complete protection for the previous transferred messages. If all long-term private keys of the participants are compromised without compromising previous established session keys, that means an AKA protocol still provides protection for the previously transferred messages. We say that the AKA protocol offers perfect forward secrecy.
- Key-Compromise Impersonation Resilience. Suppose that ’s private key has been revealed to an adversary. The adversary only can impersonate to cheat and . It is desired that the compromise of ’s private key does not allow the adversary to impersonate or to cheat .
- Unknown Key-Share Resilience. After the session key has been established, believes the session key is shared with and , while and mistakenly believe that the session key is instead shared with an adversary. Therefore, a desirable AKA protocol should be resistant to unknown key-share attacks. None of the participants can force to establish a session key with a participant that he does not know but believes he is sharing the session key with the participants that he knows.
- Key Control Resilience. The session key should be determined jointly by all participants (e.g., , and ). None of the participants can control the session key construction procedure alone. The main purpose of key control resilience is to ensure session key construction fairness and security. It should not be possible for any participants or adversaries to predict or predetermine the session key value.
2.4. Notations
- : an additive cyclic group.
- : a multiplicative cyclic group.
- : a bilinear map, .
- : a generator of the group .
- : the private key of the authentication server, .
- : the public key of the authentication server, .
- : the identity of the authentication server.
- : the identity of the client.
- : the identity of the application server.
- : the private key of /the private key of .
- : six one-way hash functions, , where is a fixed length and .
- : two map-to-point hash functions, .
3. The Proposed Protocol
3.1. System Setup Phase
- Randomly select a system private key .
- Compute the system public key .
- Choose two map-to-point hash functions .
- Choose six one-way hash functions , where is a fixed length and .
- Publish public parameters and functions .
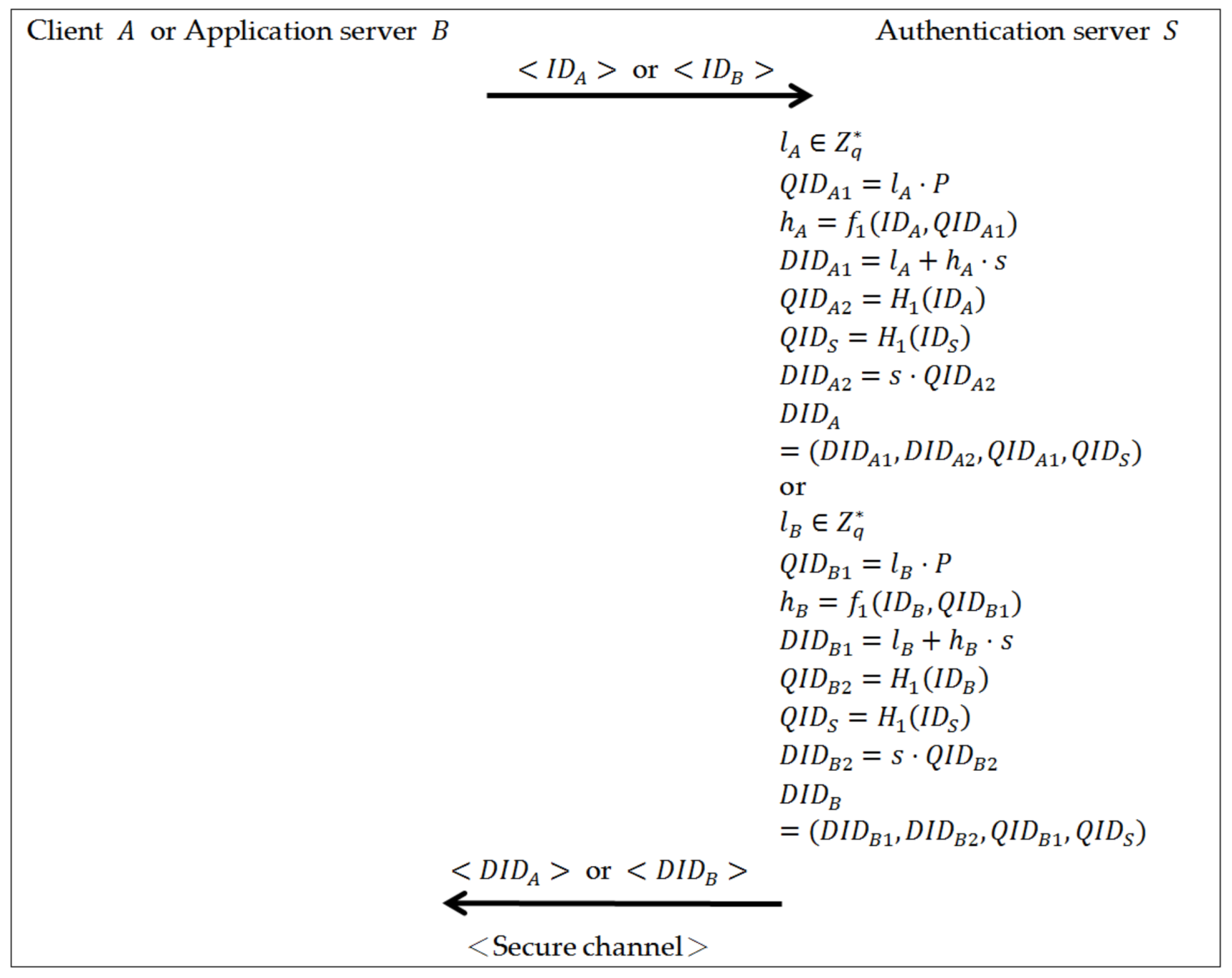
3.2. Key Extract Phase
- The client submits its identity to the authentication server .
- Upon receiving the client with identity , the authentication server chooses an ephemeral secret value , and compute , , , , and .
- Set as the client ’s private key and send it to the client via a secure channel.
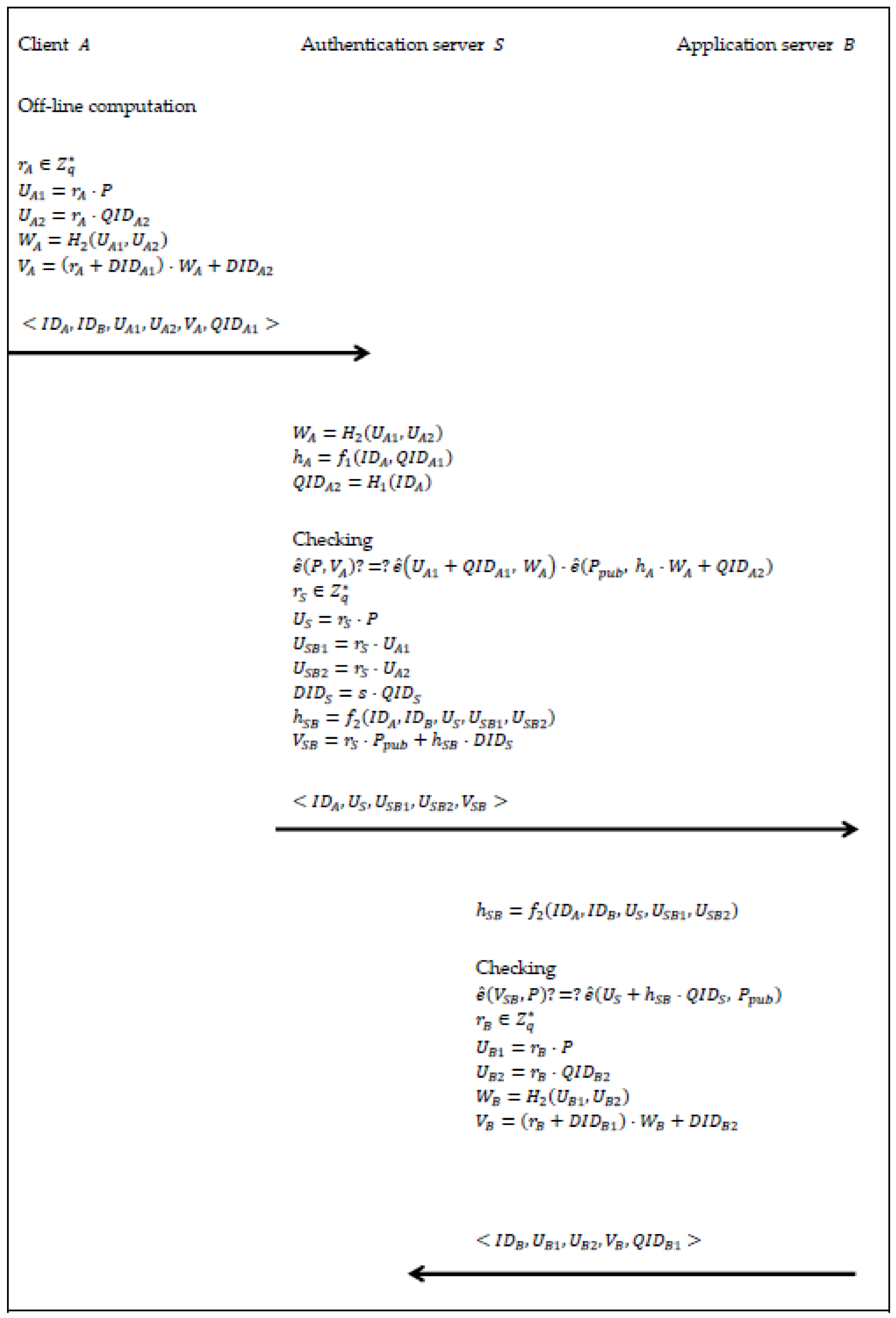
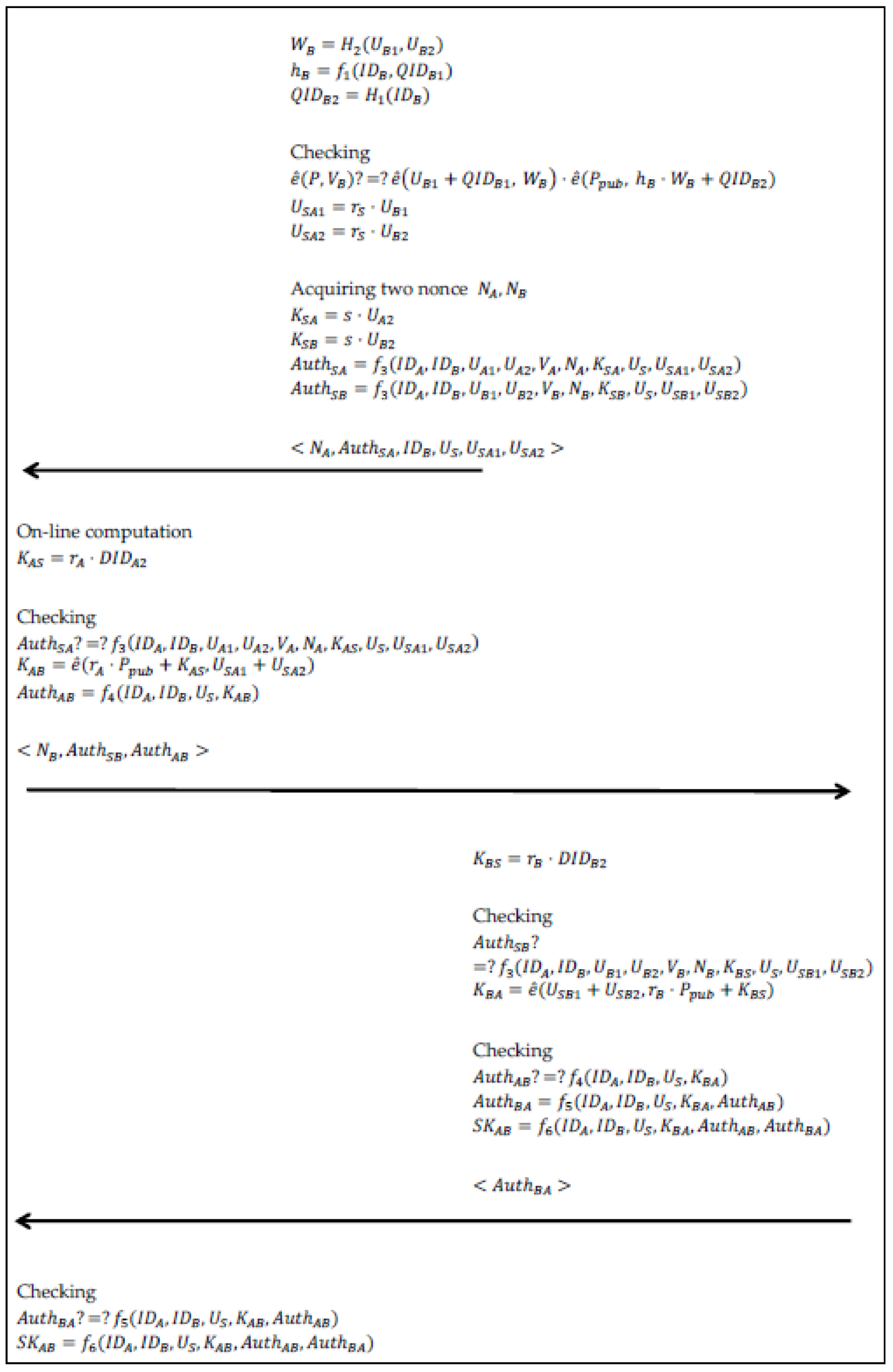
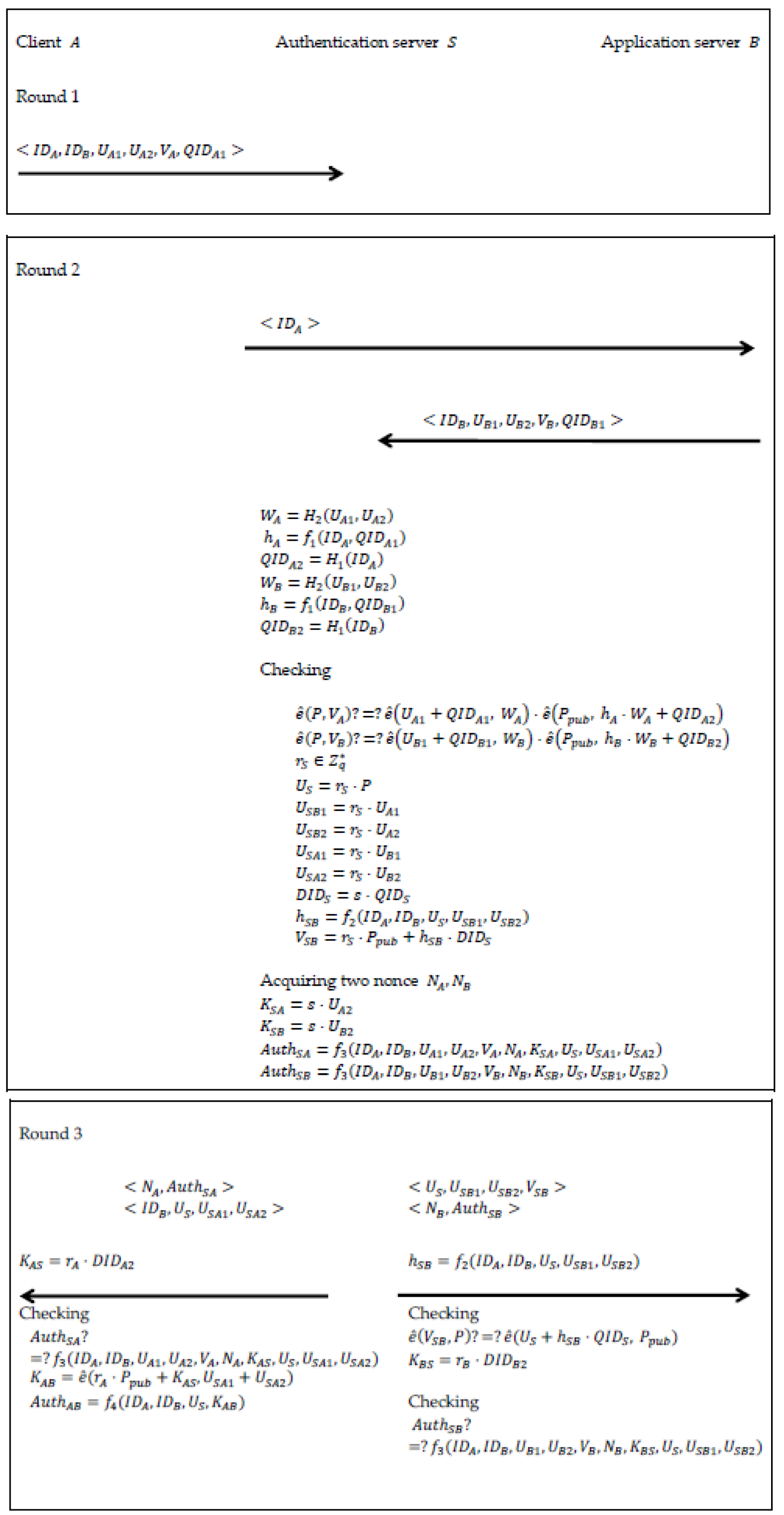
3.3. Mutual Authentication and Key Agreement Phase
- (1)
- Random select an ephemeral secret .
- (2)
- Compute and .
- (3)
- Compute and .
- (4)
- Send to the authentication server .
- (1)
- Compute , and .
- (2)
- Check whether or not. If the equation holds, then the authentication server accepts the request. Otherwise, the authentication server terminates it.
- (3)
- Random select an ephemeral secret .
- (4)
- Compute , and .
- (5)
- Compute , and .
- (6)
- Send to the application server .
- (1)
- Compute .
- (2)
- Check whether or not. If the equation holds, then the application server accepts the request. Otherwise, the application server terminates it.
- (3)
- Random select an ephemeral secret .
- (4)
- Compute and .
- (5)
- Compute and .
- (6)
- Send to the authentication server .
- (1)
- Compute , and .
- (2)
- Check whether or not. If the equation holds, then the authentication server accepts the application server . Otherwise, the authentication server terminates it.
- (3)
- Compute and .
- (4)
- Acquire two nonce , .
- (5)
- Compute and .
- (6)
- Compute and .
- (7)
- Send and to the client .
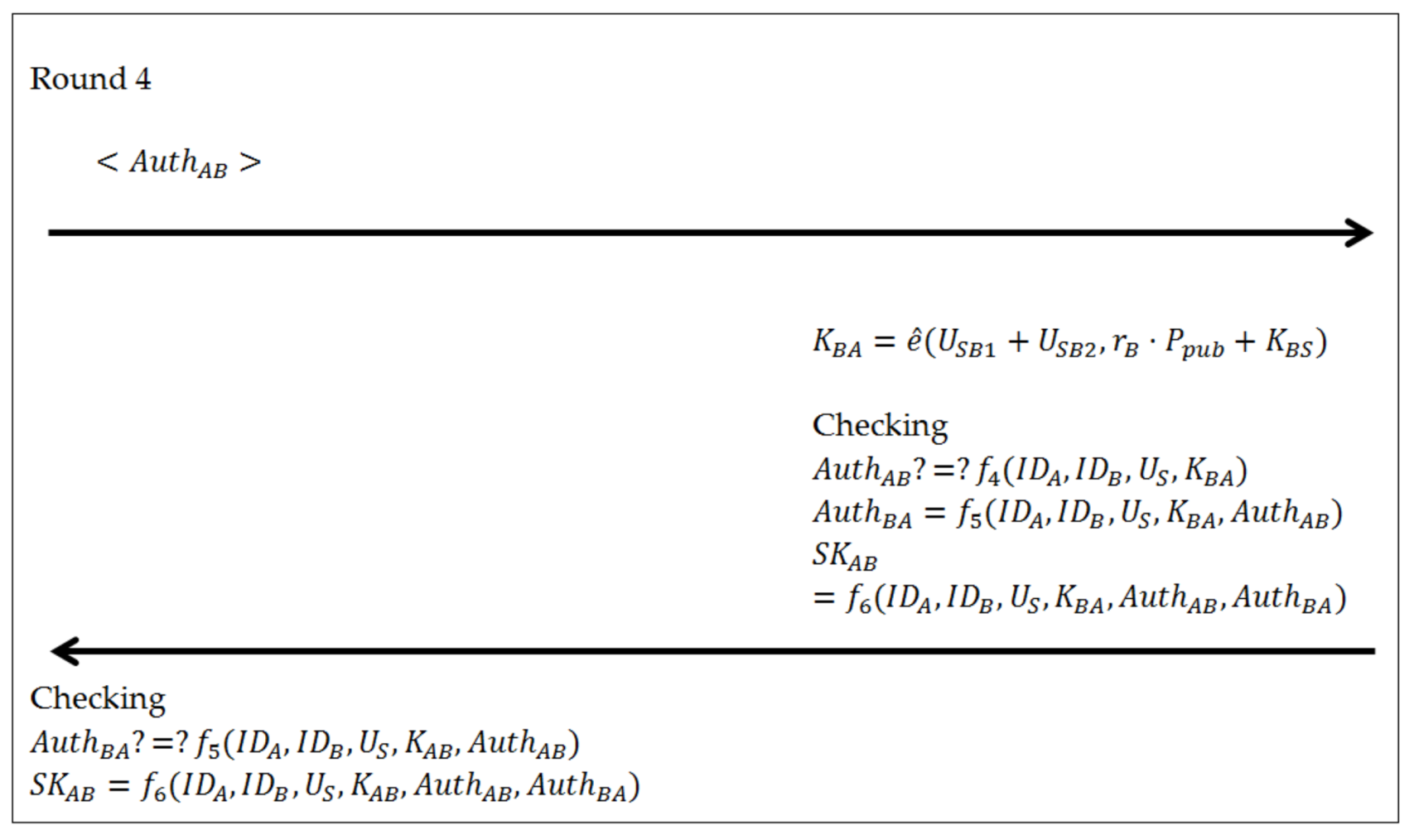
- (1)
- Compute .
- (2)
- Check whether or not. If the equation holds, then the client accepts the authentication server . Otherwise, the client terminates it.
- (3)
- Compute and .
- (4)
- Send to the application server .
- (1)
- Compute .
- (2)
- Check whether or not. If the equation holds, then the application server accepts the authentication server . Otherwise, the application server terminates it.
- (3)
- Compute .
- (4)
- Check whether or not. If the equation holds, then the application server can be sure that the client has the ability to compute the session key. Otherwise, the application server notifies the authentication server that the authentication has been failed and terminates it.
- (5)
- Compute .
- (6)
- Compute the session key .
- (7)
- Send to the client .
3.4. The Parallel Version
3.5. Preventing and Tracing Network Crime
4. Security and Performance Analysis
4.1. Security Analysis
- Mutual authentication and Ephemeral-Secret-Leakage Resistance. The proposed protocol adopted Tseng et al.’s ESL-secure ID-AKE protocol [7] to achieve the client-to-server authentication. The authentication server authenticates the client and the application server by checking whether and or not. To the client as an example, the message , where , and can be viewed as a signature on a message in Tseng et al.’s ESL-secure ID-AKE protocol. According to the security analysis by Tseng et al., if an adversary could have obtained the ephemeral secret using ESL attacks, the adversary still needs to solve the computational Diffie-Hellman problem to violate the client-to-server authentication.The application server authenticates the authentication server by checking whether or not. The message , where , and , can be viewed as a signature on a message . Without knowledge of the authentication server ’s private key , none of the participants or adversaries can forge the message and compute a valid signature. To forge a valid message , an adversary must have obtained the authentication server ’s private key from , where . It is a discrete logarithm problem to the adversary.The proposed protocol provides the server-to-client authentication that is also based on Tseng et al.’s ESL-secure ID-AKE protocol. The client and the application server authenticate the authentication server by checking whether and or not. Even though an adversary could obtain the client ’s ephemeral secret by the ESL attacks. Since and are derived from and respectively. To violate the server-to-client authentication, the adversary has to solve the computational Diffie-Hellman problem to obtain and the discrete logarithm problem to compute the application server ’s ephemeral secret and the computational Diffie-Hellman problem to obtain from the transferred messages. Otherwise, the adversary only can compute the authentication server ’s private key from , in which the adversary needs to solve the discrete logarithm problem.The application server can be sure that the client has obtained the session key by checking whether or not. The client checks whether or not to be sure that the application server also has obtained the session key and both of them with the authentication server can agree upon the common session key . For computing a valid message or , we assume that the client ’s ephemeral secret has been compromised by an adversary. Since the messages and are derived from , where and , the adversary must solve the computational Diffie-Hellman problem to compute or the discrete logarithm problem to compute and the computational Diffie-Hellman problem to compute from transferred messages. Otherwise, the adversary only can compute the authentication server ’s private key from , in which the adversary needs to solve the discrete logarithm problem.Without knowledge of the private key of a participant (e.g., the client ’s private key ). An adversary cannot impersonate the participant since the adversary is unable to forge a valid signature. The proposed protocol employs the signature to authenticate the participants’ identities and one way hash function to protect the integrity of the transferred messages. Even though the ephemeral secret of the client has been compromised, each participant can be sure that none of the adversaries can impersonate other participants to violate the verification procedures and corrupt the participants’ private keys and the session key.
- Known Key Security. Suppose that an adversary can eavesdrop on the transmitted messages to learn the previous session keys. However, the session key of the proposed protocol is unique and dependent of each participant’s ephemeral secrets , and and private keys , and . Therefore, knowledge of the previous session keys does not enable the adversary to derive other session keys and does not give the adversary any information that the adversary could use to derive other session keys. Even though the client ’s ephemeral secret has been compromised. If an adversary would like to compute , where from the transferred messages, the adversary needs to solve the computational Diffie-Hellman problem to compute the client ’s private key or the discrete logarithm problem from , where to obtain the authentication server ’s private key . Otherwise, the adversary only can solve the discrete logarithm problem and the computational Diffie-Hellman problem to compute the application server ’s corresponding ephemeral secret and private key . In the proposed protocol, even if one of the session key has been compromised, the security of the other or future session keys is not endangered.
- Partial Forward Secrecy. The proposed protocol session key is dependent on each participant’s private key and corresponding ephemeral secret. In the proposed protocol, if the private key of client or the application server has been compromised, an adversary also needs to obtain the corresponding ephemeral secrets to compute the session key. Suppose that the adversary would like to compute the corresponding ephemeral secrets from the transferred messages, the adversary needs to solve the discrete logarithm problem. However, if the adversary corrupts the private key of the authentication server , it is obvious that all of the previous session keys can be recovered from the transferred messages. Since the adversary is indeed able to compute , or , and . The proposed protocol offers partial forward secrecy.
- Key-Compromise Impersonation Resilience. To discuss the key-compromise impersonation resilience property, we assume that client ’s private key is compromised to an adversary who tries to impersonate the application server to cheat the client and the authentication server . When the client requests service from the application server , the adversary only can choose and from the previous sessions and send them to the authentication server and the client , respectively. Since the adversary cannot derive the application server ’s private key and the corresponding ephemeral secret from the transferred messages to compute , where . The adversary only can violate the verification procedures of the authentication server . If the adversary tries to derive the ephemeral secret and the private key from the transferred messages to compute and construct the session key, the adversary needs to solve the discrete logarithm problem and the computational Diffie-Hellman problem.
- Unknown Key-Share Resilience. To implement such an attack, the adversary is required to obtain the private key of client or the application server . In the proposed protocol, both of the client and the application server have to be authenticated by the authentication server . Only the participant that has the private key distributed from the authentication server could compute the valid signature and thus pass the verification procedures and compute the session key. To the client as an example, the client with its private key and the ephemeral secret can compute and to pass the verification procedures of the authentication server and the application server . The ephemeral secret with are able to compute the session key . Hence, the proposed protocol can withstand an unknown key-shared attack.
- Key control Resilience. In the proposed protocol, the session key , where is determined by all participants’ private keys and corresponding ephemeral secrets. None of the participants can force a session key to be predetermined or predict the value and control the outcome of the session key. Hence, the proposed protocol ability to prevent the session key is created only by the authentication server or other two participants.
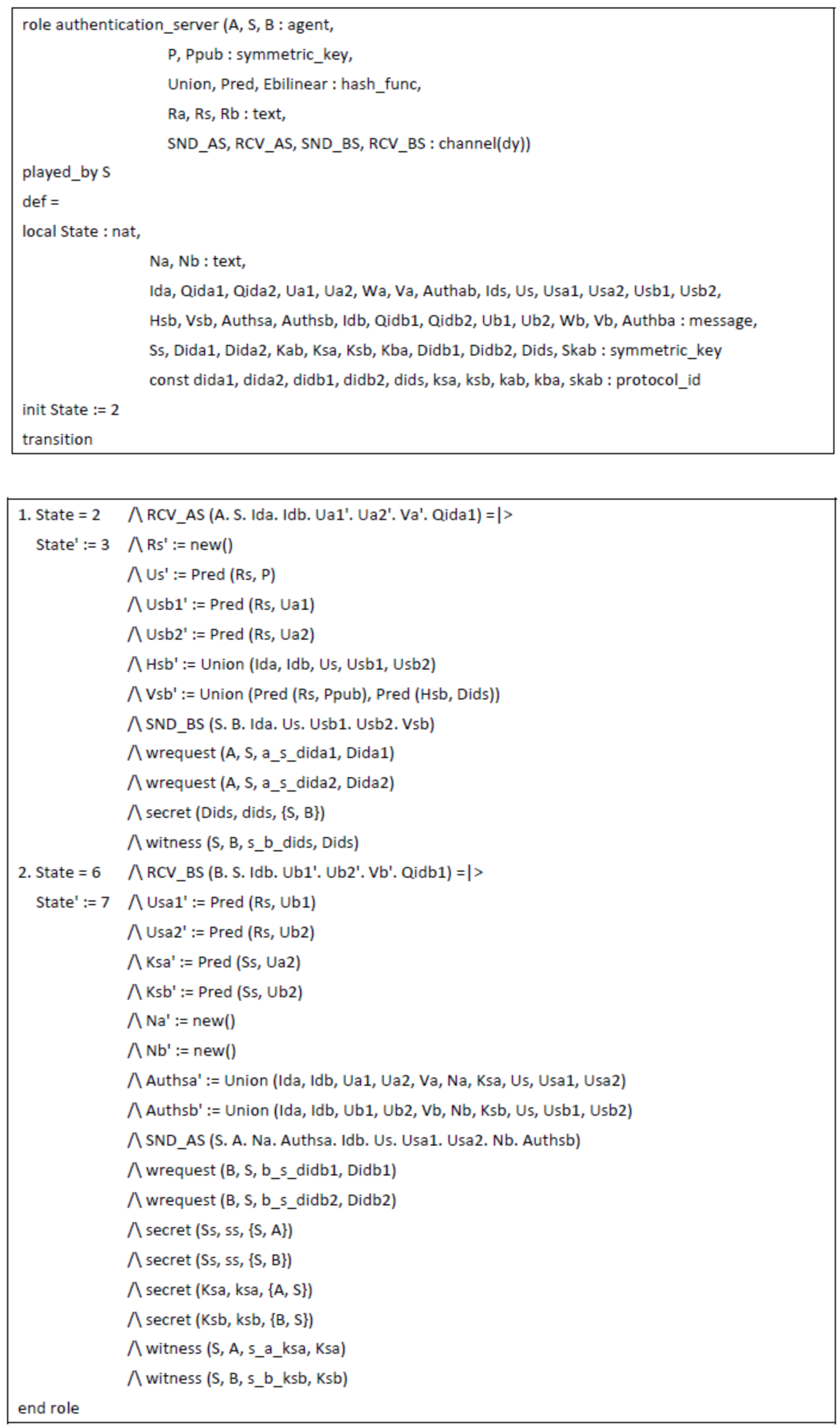
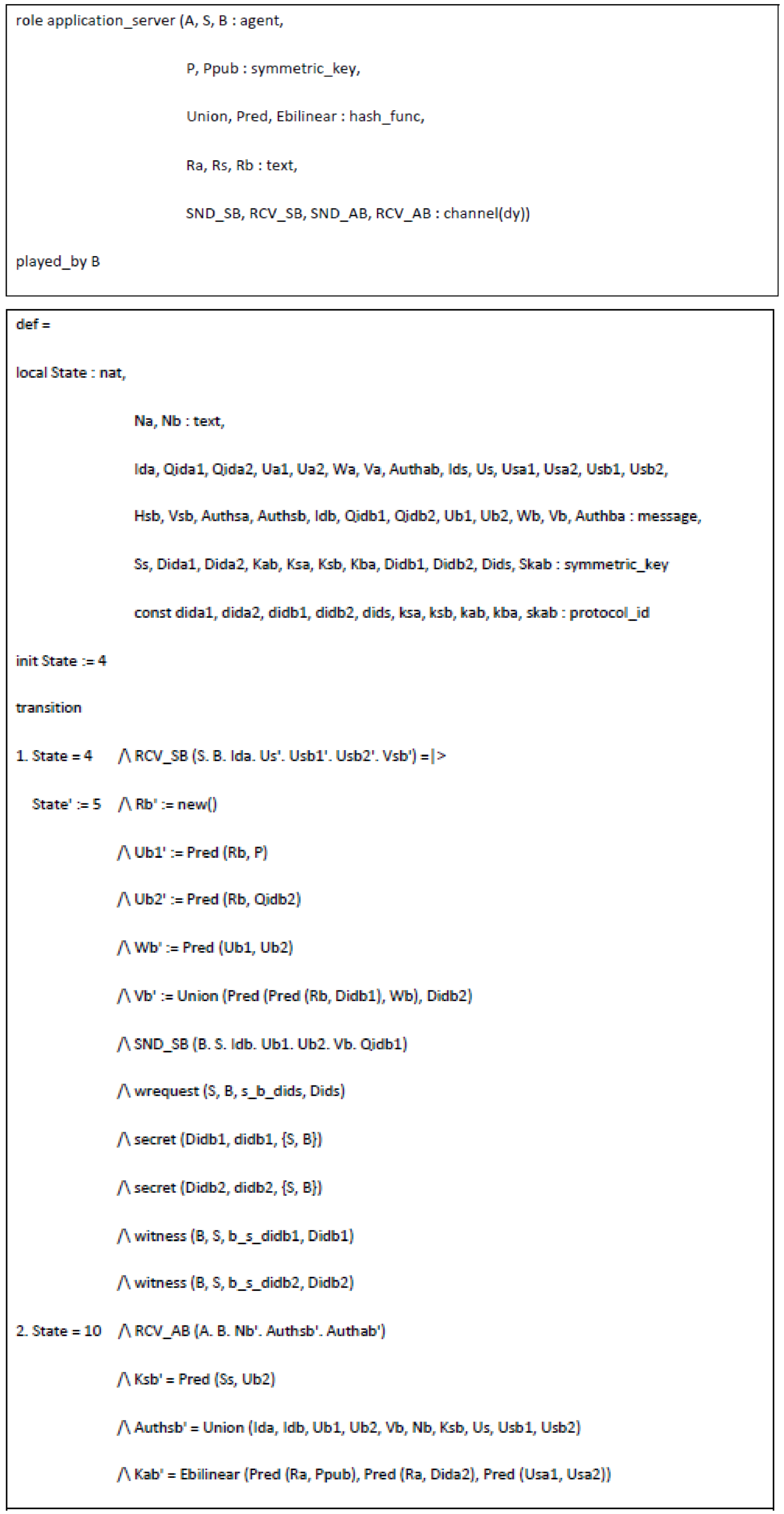
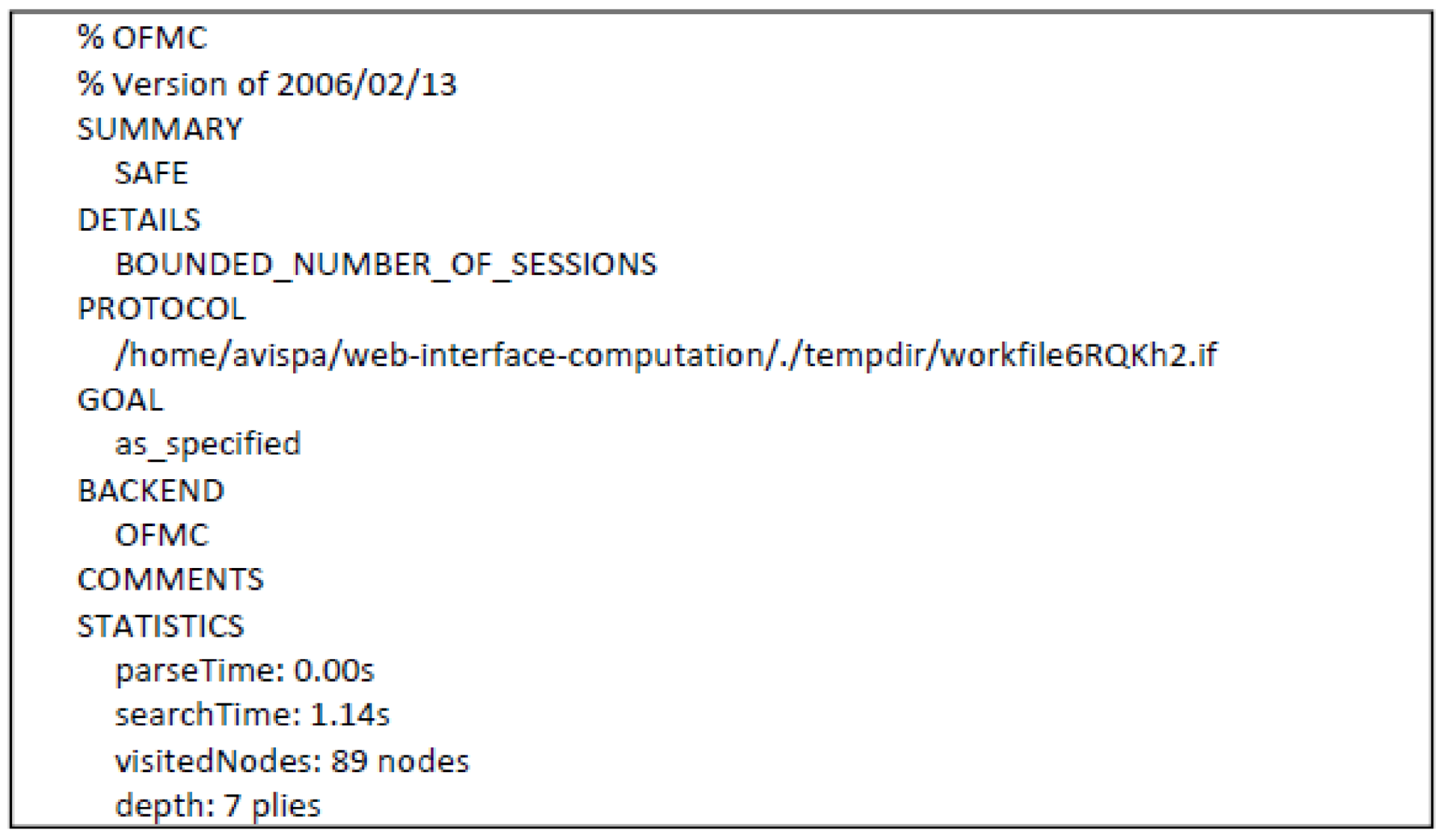
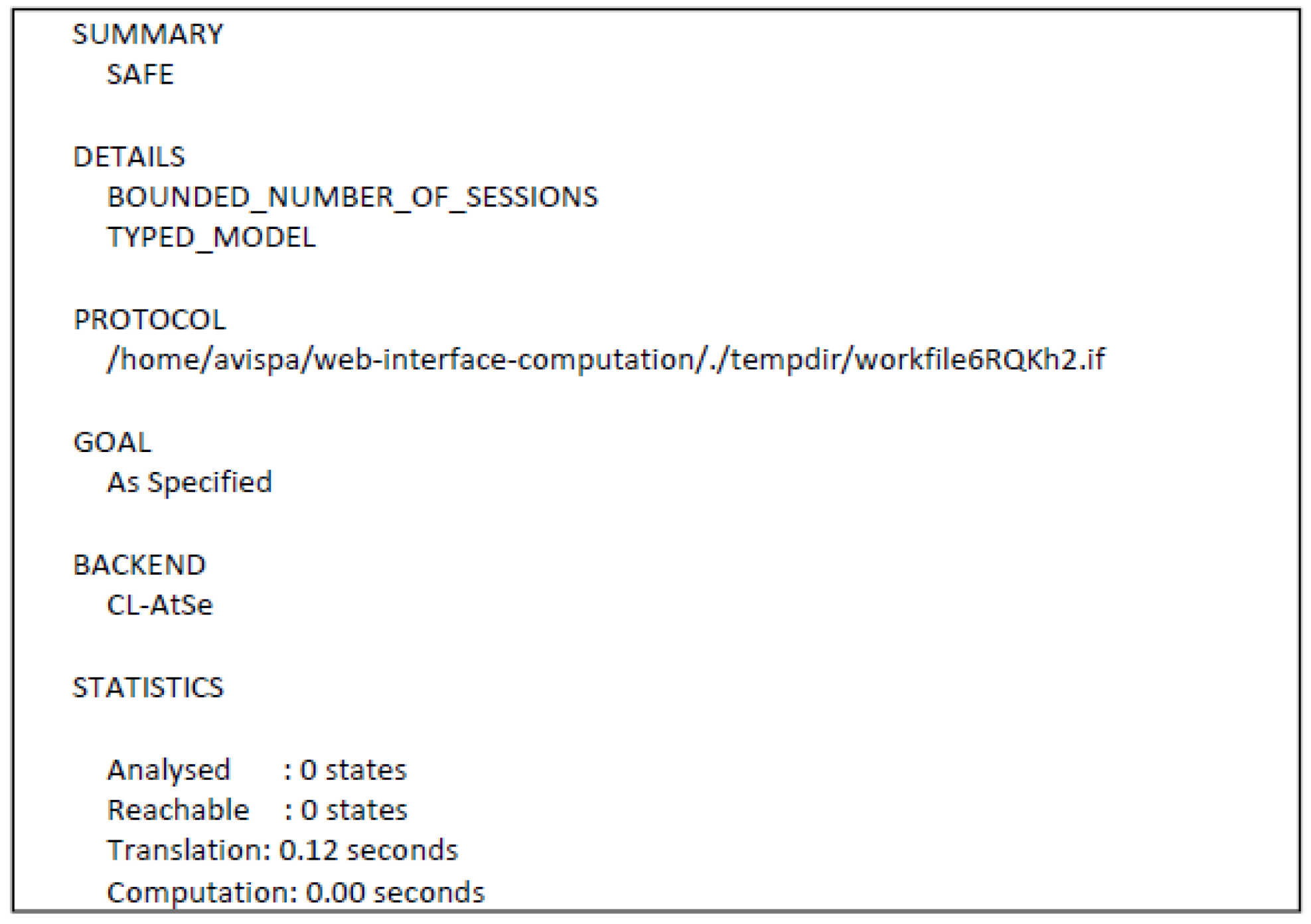
4.2. Formal Analysis Using AVISPA
4.3. Performance Analysis
- : the execution time for a bilinear pairing operation .
- : the execution time for points in multiplication operation.
- : the execution time for a modular exponential operation in .
- : the execution time for a map-to-point hash function in .
- : the execution time for an addition operation of points in or a multiplication operation in .
- : the execution time for a one-way hash function.
4.4. Software Performance
5. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
Appendix A



References
- Wen, H.A.; Lin, C.L.; Hwang, T. Provably secure authenticated key exchange protocols for low power computing clients. Comput. Secur. 2006, 25, 106–113. [Google Scholar] [CrossRef]
- Wong, D.S.; Chan, A.H. Efficient and mutually authenticated key exchange for low power computing devices. In Proceedings of the 14th International Conference on the Theory and Application of Cryptology and Information Security, Melbourne, Australia, 9–13 December 2008; pp. 272–289. [Google Scholar]
- Jakobsson, M.; Pointcheval, D. Mutual Authentication for Low-Power Mobile Devices. Financ. Cryptogr. 2002, 2339, 178–195. [Google Scholar]
- Choi, K.; Hwang, J.; Lee, D.; Seo, I. ID-based Authenticated Key Agreement for Low-Power Mobile Devices. Inf. Sec. Priv. 2005, 3574, 494–505. [Google Scholar]
- Chuang, Y.H.; Tseng, Y.M. Towards generalized ID-based user authentication for mobile multi-server. Int. J. Commun. Syst. 2012, 25, 447–460. [Google Scholar] [CrossRef]
- Wu, T.Y.; Tseng, Y.M. An efficient user authentication and key exchange protocol for mobile client–server environment. Comput. Netw. 2010, 53, 1062–1070. [Google Scholar] [CrossRef]
- Tseng, Y.M.; Tseng, L. Ephemeral-Secret-Leakage Secure ID-Based Authenticated Key Exchange Protocol for Mobile Client-Server Environments. In Proceedings of the 24th Cryptology and Information Security Conference, Putrajaya, Malaysia, 24–26 June 2014. [Google Scholar]
- Diffie, W.; Hellman, M.E. New directions in cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar] [CrossRef]
- Tsai, C.S.; Lee, C.C.; Hwang, M.S. Password Authentication Schemes: Current Status and Key Issues. IJINS 2006, 3, 101–115. [Google Scholar]
- Shamir, A. Identity-Based Cryptosystems and Signature Schemes. Adv. Cryptol. 1985, 5, 47–53. [Google Scholar]
- Boneh, D.; Franklin, M. Identity-Based Encryption from the Weil Pairing. In Proceedings of the 21st Annual International Cryptology Conference, Santa Barbara, CA, USA, 19–23 August 2001; pp. 213–229. [Google Scholar]
- Boneh, D.; Boyen, X. Secure Identity Based Encryption without Random Oracles. In Proceedings of the 24th Annual International Cryptology Conference, Santa Barbara, CA, USA, 15–19 August 2004; pp. 443–459. [Google Scholar]
- Waters, B. Efficient Identity-Based Encryption without Random Oracles. In Proceedings of the 24th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Aarhus, Denmark, 22–26 May 2005; pp. 114–127. [Google Scholar]
- Gentry, C. Practical Identity-Based Encryption without Random Oracles. In Proceedings of the 24th Annual International Conference on the Theory and Applications of Cryptographic Techniques, St. Petersburg, Russia, 28 May–1 June 2006; pp. 445–464. [Google Scholar]
- Joux, A. A One Round Protocol for Tripartite Diffie–Hellman. Algorithm. Number Theory 2000, 1838, 385–393. [Google Scholar]
- Al-Riyami, S.; Paterson, K. Tripartite Authenticated Key Agreement Protocols from Pairings. In Proceedings of the 9th IMA International Conference, Cirencester, UK, 16–18 December 2003; pp. 332–359. [Google Scholar]
- Lim, M.H.; Lee, S.; Moon, S. Cryptanalysis of Tso et al.’s ID-Based Tripartite Authenticated Key Agreement Protocol. Inf. Syst. Secur. 2007, 4812, 64–76. [Google Scholar]
- Hölbl, M.; Welzer, T.; Brumen, B. Two proposed identity-based three-party authenticated key agreement protocols from pairings. Comput. Secur. 2010, 29, 244–252. [Google Scholar] [CrossRef]
- Xiong, H.; Chen, Z.; Li, F. New identity-based three-party authenticated key agreement protocol with provable security. JNCA 2013, 36, 927–932. [Google Scholar] [CrossRef]
- Yeh, H.T.; Sun, H.M. Password-based user authentication and key distribution protocols for client–server applications. J. Syst. Softw. 2004, 72, 97–103. [Google Scholar] [CrossRef]
- Kohl, J.T.; Neuman, B.C.; Tso, T.Y. The evolution of the Kerberos authentication system. In Distributed Open System; IEEE Computer Society Press: Washington, DC, USA, 1991; pp. 78–94. [Google Scholar]
- Yeh, H.T.; Sun, H.M. Password authenticated key exchange protocols among diverse network domains. Comput. Electr. Eng. 2005, 31, 175–189. [Google Scholar] [CrossRef]
- Li, G. Optimal authentication protocols resistant to password guessing attacks. In Proceedings of the Eighth IEEE Computer Security Foundations Workshop, Kerry, Ireland, 13–15 June 1995; pp. 24–29. [Google Scholar]
- Kwon, T.; Kang, M.; Jung, S.; Song, J. An Improvement of the Password-Based Authentication Protocol (K1P) on Security against Replay Attacks. IEICE Trans. Commun. 1999, 82, 991–997. [Google Scholar]
- Kwon, T.; Song, J. Authenticated key exchange protocols resistant to password guessing attacks. Commun. IEE Proc. 1998, 145, 304–308. [Google Scholar] [CrossRef]
- Chang, T.Y.; Hwang, M.S.; Yang, W.P. A communication-efficient three-party password authenticated key exchange protocol. Inf. Sci. 2011, 181, 217–226. [Google Scholar] [CrossRef]
- Ni, L.; Chen, G.; Li, J. Escrowable identity-based authenticated key agreement protocol with strong security. Comput. Math. Appl. 2013, 65, 1339–1349. [Google Scholar] [CrossRef]
- Chang, T.Y.; Tsai, C.J.; Lin, J.H. A graphical-based password keystroke dynamic authentication system for touch screen handheld mobile devices. J. Syst. Softw. 2012, 85, 1157–1165. [Google Scholar] [CrossRef]
- Blake-Wilson, S.; Menezes, A. Authenticated Diffe-Hellman Key Agreement Protocols. In Proceedings of the Selected Areas in Cryptography, Kingston, Ontario, Canada, 17–18 August 1999; pp. 339–361. [Google Scholar]
- AVISPA v1.1 User Manual. 2006. Available online: http://www.avispa-project.org/ (accessed on 24 January 2018).
- Chen, T.H.; Lee, W.B.; Chen, H.B. A round- and computation-efficient three-party authenticated key exchange protocol. J. Syst. Softw. 2008, 81, 1581–1590. [Google Scholar] [CrossRef]
- Metz, C. AAA protocols: Authentication, authorization, and accounting for the Internet. IEEE Int. Comput. 1999, 3, 75–79. [Google Scholar] [CrossRef]
- Rensing, C.; Karsten, M.; Stiller, B. AAA: A survey and a policy-based architecture and framework. IEEE Netw. 2002, 16, 22–27. [Google Scholar] [CrossRef]
- Decugis, S. Towards a Global AAA Framework for Internet. In Proceedings of the 2009 Ninth Annual International Symposium on Applications and the Internet, Bellevue, WA, USA, 20–24 July 2009; pp. 227–230. [Google Scholar]
- Dolev, D.; Yao, A.Y. On the Security of Public Key Protocols. IEEE Inf. Theory Soc. 1983, 29, 198–208. [Google Scholar] [CrossRef]
- AVISPA Web tool. Automated Validation of Internet Security Protocols and Applications. Available online: http://www.avispa-project.org/web-interface (accessed on 24 January 2018).
- Scott, M.; Costigan, N.; Abdulwahab, W. Implementing Cryptographic Pairings on Smartcards. In Proceedings of the 8th International Workshop, Yokohama, Japan, 10–13 October 2006; pp. 134–147. [Google Scholar]
- Oliveira, L.B.; Aranha, D.F.; Gouvêa, C.P.L.; Scott, M.; Câmara, D.F.; López, J. TinyPBC: Pairings for authenticated identity-based non-interactive key distribution in sensor networks. Comput. Commun. 2011, 34, 485–493. [Google Scholar] [CrossRef]
- Hu, L.; Dong, J.W.; Pei, D.Y. Implementation of Cryptosystem Based on Tate Pairing. J. Comput. Sci. Technol. 2005, 20, 264–269. [Google Scholar] [CrossRef]
| Android 5.0 and 2.3 Intel Atom with 4 GB of RAM | 0.251 s | 0.148 s | 0.076 s | 0.002 s | 0.001 s | 0.001 s |
| Computational Cost (Total) | Computational Cost (Online) | Execution Time (Total) | Execution Time (Online) | |
|---|---|---|---|---|
| Client Side | s | s |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, C.-L.; Tsai, W.-J.; Chang, T.-Y.; Liu, T.-M. Ephemeral-Secret-Leakage Secure ID-Based Three-Party Authenticated Key Agreement Protocol for Mobile Distributed Computing Environments. Symmetry 2018, 10, 84. https://doi.org/10.3390/sym10040084
Liu C-L, Tsai W-J, Chang T-Y, Liu T-M. Ephemeral-Secret-Leakage Secure ID-Based Three-Party Authenticated Key Agreement Protocol for Mobile Distributed Computing Environments. Symmetry. 2018; 10(4):84. https://doi.org/10.3390/sym10040084
Chicago/Turabian StyleLiu, Chao-Liang, Wang-Jui Tsai, Ting-Yi Chang, and Ta-Ming Liu. 2018. "Ephemeral-Secret-Leakage Secure ID-Based Three-Party Authenticated Key Agreement Protocol for Mobile Distributed Computing Environments" Symmetry 10, no. 4: 84. https://doi.org/10.3390/sym10040084
APA StyleLiu, C.-L., Tsai, W.-J., Chang, T.-Y., & Liu, T.-M. (2018). Ephemeral-Secret-Leakage Secure ID-Based Three-Party Authenticated Key Agreement Protocol for Mobile Distributed Computing Environments. Symmetry, 10(4), 84. https://doi.org/10.3390/sym10040084




