WDSchain: A Toolbox for Enhancing the Security Using Blockchain Technology in Water Distribution System
Abstract
:1. Introduction
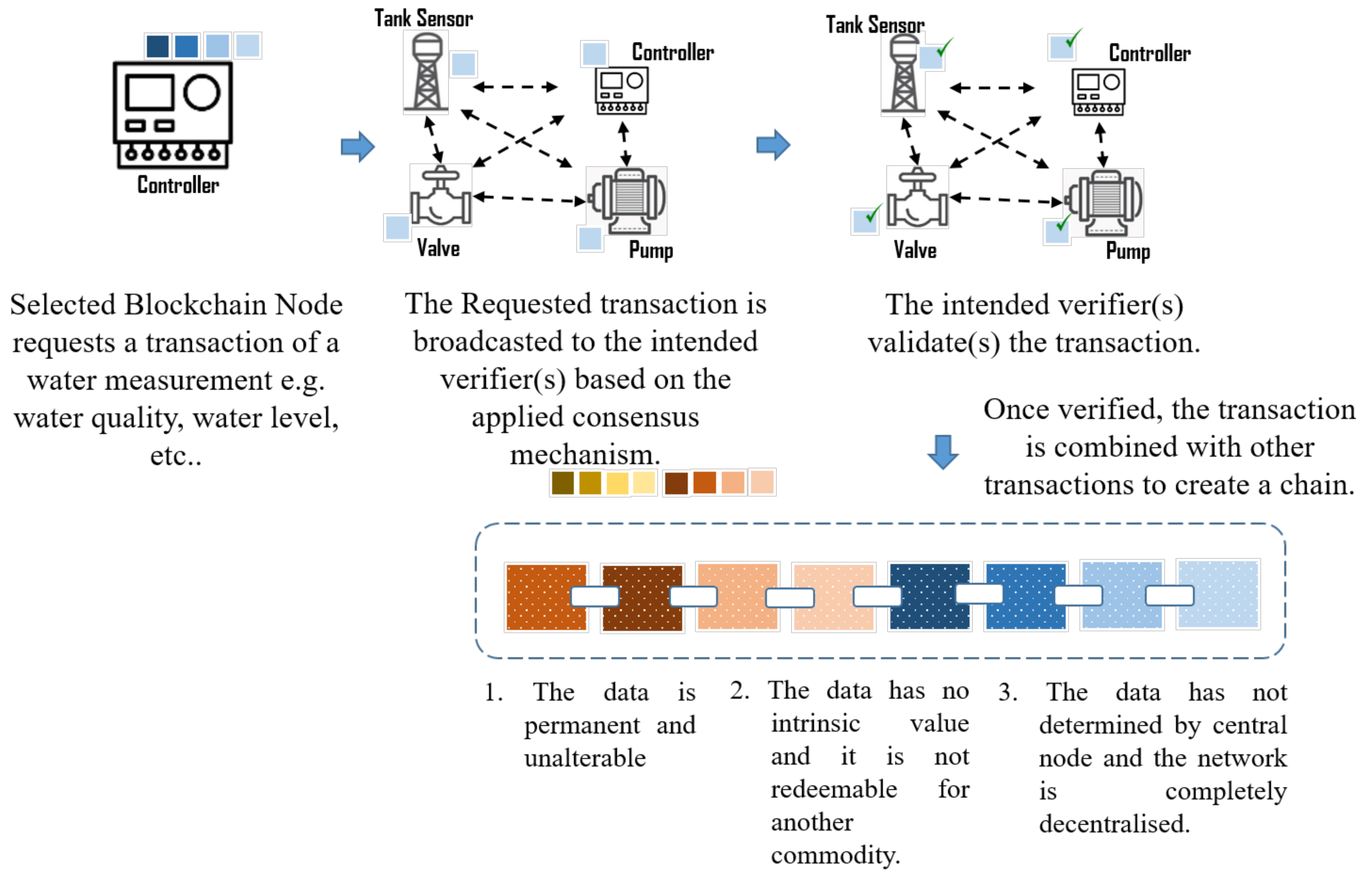
- Availability of service: it is crucial to keep the availability of the OT (physical systems) and to avoid any disruption of the service that can endanger the society and health of human beings. The transferred data are verified by other network peers in a decentralised manner to maintain the continuity of the service and mitigate the Denial of Service (DoS) [9].
- Data Immutability: As in the initial step of integrating blockchain, the transferred data have to be stored in the Cloud. Hence, a hash function can be utilised in the verification process in both blockchain and Cloud to compare the chained data with the meta-data. In this approach, the transferred data cannot be manipulated during the transmission as it is validated again at the Cloud. When all the smart networks get matured enough to handle autonomous decision-making, the data may not be required to be transmitted to the Cloud. Then, the WDS will have the full benefit of data integrity, confidentiality, and immutability.
- Data and Process Transparency: The process does not require a centralised network for verifying the data, and the fact that the network nodes participate in the validation process provides transparency of the whole process in general. However, the centralisation level may change based on the consensus mechanism, but the baseline of the decentralisation network provides a sense of transparency.
2. Related Works
3. WDSchain
3.1. Proposed Architecture
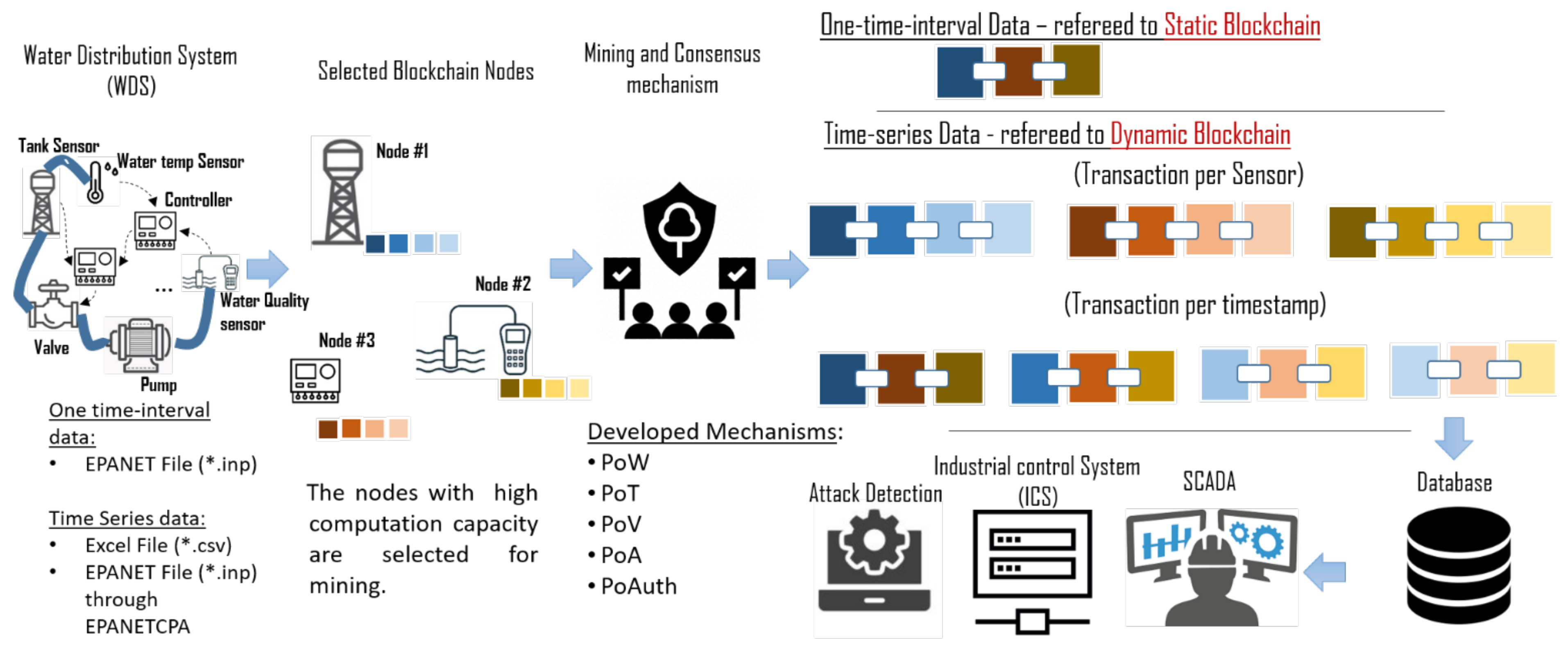
- Importing data into the MATLAB environment: The hydraulic data can be imported either from the CSV file (in dynamic blockchain mode) or from the EPANET modeling file (in static and dynamic blockchain modes) into the MATLAB environment using the EPANET-MATLAB toolkit or EPANETCPA for any one-time interval or time-series data, respectively. The data are imported into MATLAB as tables that represent network configurations (e.g., network nodes, type, their coordinates, and the number of edges). Then, the data are saved in the form of blocks and its self-hash value is generated upon data verification. Only the approved blocks are added to the chain along with other blockchain information, such as node ID, self-hash value, and nonce. A nonce is an abbreviation for "Number Only Used Once" that is used during the hashing of the data.
- Blockchain and data-verification algorithms: These two processes are the key parts of any blockchain system. The blockchain algorithm oversees the communication and verification processes based on the selected data-verification algorithm (known as the consensus mechanism). In detail, the blockchain algorithm in this work aims to re-hash the data with the cooperation of the developed consensus mechanisms (see Algorithm 1). In brief, it concatenates the water coefficients to be validated based on the consensus mechanism, as well as the previous hash if previously linked with the block, except for the Genuis block. A consensus mechanism is an algorithm that has a set of rules that all the peers should follow based on the blockchain algorithm and enforce the verification of the block and its transaction. Five consensus mechanisms are developed in this toolbox, which are: Proof-of-Work (PoW), PoT, Proof-of-Assignment (PoA), Proof-of-Vote (PoV), and Proof-of-Authentication (PoAuth). PoA and PoAuth are proposed in the [35] project because the phenomenon of the WDS requires fast-action, voting-based, and real-time verification processes. IoTw is one of the leading blockchain projects that develop blockchain for industries and manufacturers, and it has the highest level of security as well as flexibility of communication with smart devices [35].
- Data-mapping: There are two modes of data-mapping in joining the chain upon verification of data blocks. In dynamic blockchain, either the data (transaction) are chained per timestamp, or sensors. When all sensor data in the one-time interval are kept in one block, this is referred to as the transaction per timestamp. In contrast, it is the transaction per sensor when all data of one sensor are chained in one block or transaction.
| Algorithm 1 Blockchain algorithm |
 |
| Algorithm 2 VerifyNewblock using PoW |
 |
| Algorithm 3 VerifyNewblock using PoT |
 |
| Algorithm 4 VerifyNewblock using PoV |
 |
| Algorithm 5 VerifyNewblock using PoA |
 |
| Algorithm 6 VerifyNewblock using PoAuth |
 |
3.2. Configuring and Running a Simulation
3.2.1. The Input File
3.2.2. The Output File
4. Case Studies and Methodologies for Evaluation
5. Results and Discussion
6. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Hassanzadeh, A.; Rasekh, A.; Galelli, S.; Aghashahi, M.; Taormina, R.; Ostfeld, A.; Banks, M.K. A review of cybersecurity incidents in the water sector. J. Environ. Eng. 2020, 146, 03120003. [Google Scholar] [CrossRef] [Green Version]
- Fekete, B.M.; Revenga, C.; Todd, M. The Global Risks Report 2018, 13th ed.; World Economic Forum: Geneva, Switzerland, 2018. [Google Scholar]
- Mahmoud, H.; Wu, W. Cyber-Physical System Security Open Challenges in Smart Water Networks. Zenodo 2020. [Google Scholar] [CrossRef]
- Dogo, E.M.; Salami, A.F.; Nwulu, N.I.; Aigbavboa, C.O. Blockchain and Internet of things-based technologies for intelligent water management system. In Artificial Intelligence in IoT; Springer: Antalya, Turkey, 2019; pp. 129–150. [Google Scholar]
- Suciu, G.; Nădrag, C.; Istrate, C.; Vulpe, A.; Ditu, M.C.; Subea, O. Comparative analysis of distributed ledger technologies. In Proceedings of the 2018 Global Wireless Summit (GWS), Chiang Rai, Thailand, 25–28 November 2018; pp. 370–373. [Google Scholar]
- Andoni, M.; Robu, V.; Flynn, D.; Abram, S.; Geach, D.; Jenkins, D.; McCallum, P.; Peacock, A. Blockchain technology in the energy sector: A systematic review of challenges and opportunities. Renew. Sustain. Energy Rev. 2019, 100, 143–174. [Google Scholar] [CrossRef]
- Fontein, R. Comparison of static analysis tooling for smart contracts on the evm. In Proceedings of the 28th Twente Student Conference on IT, Twente, The Netherlands, 2 February 2019. [Google Scholar]
- Hill, E. Who’s Snooping on Your Blockchain Transactions? Medium. 2019. Available online: https://medium.com/hackernoon/whos-snooping-on-your-blockchain-transactions-7c4ae1c556d3 (accessed on 12 July 2021).
- Singh, R.; Tanwar, S.; Sharma, T.P. Utilization of blockchain for mitigating the distributed denial of service attacks. Secur. Priv. 2020, 3, e96. [Google Scholar] [CrossRef]
- Astarita, V.; Giofrè, V.P.; Mirabelli, G.; Solina, V. A review of blockchain-based systems in transportation. Information 2020, 11, 21. [Google Scholar] [CrossRef] [Green Version]
- Dwivedi, A.D.; Srivastava, G.; Dhar, S.; Singh, R. A decentralized privacy-preserving healthcare blockchain for IoT. Sensors 2019, 19, 326. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Pincheira, M.; Vecchio, M.; Giaffreda, R.; Kanhere, S.S. Cost-effective IoT devices as trustworthy data sources for a blockchain-based water management system in precision agriculture. Comput. Electron. Agric. 2021, 180, 105889. [Google Scholar] [CrossRef]
- Perboli, G.; Musso, S.; Rosano, M. Blockchain in logistics and supply chain: A lean approach for designing real-world use cases. IEEE Access 2018, 6, 62018–62028. [Google Scholar] [CrossRef]
- Pérez Ortiz, Y. How Blockchain Technology Could Improve the Quality of Drinking Water in Puerto Rico. 2018. Available online: https://ssrn.com/abstract=3266166 (accessed on 12 July 2021).
- Youssef, S.B.H.; Rekhis, S.; Boudriga, N. A blockchain based secure IoT solution for the dam surveillance. In Proceedings of the 2019 IEEE Wireless Communications and Networking Conference, Marrakesh, Morocco, 15–18 April 2019; pp. 1–6. [Google Scholar]
- Predescu, A.; Arsene, D.; Pahonțu, B.; Mocanu, M.; Chiru, C. A Serious Gaming Approach for Crowdsensing in Urban Water Infrastructure with Blockchain Support. Appl. Sci. 2021, 11, 1449. [Google Scholar] [CrossRef]
- Pee, S.J.; Nans, J.H.; Jans, J.W. A simple blockchain-based peer-to-peer water-trading system leveraging smart contracts. In Proceedings of the International Conference on Internet Computing, Philadelphia, PA, USA, 18–20 October 2018; pp. 63–68. [Google Scholar]
- Pincheira, M.; Vecchio, M.; Giaffreda, R.; Kanhere, S.S. Exploiting constrained IoT devices in a trustless blockchain-based water management system. In Proceedings of the 2020 IEEE International Conference on Blockchain and Cryptocurrency, Toronto, ON, Canada, 2–6 May 2020; pp. 1–7. [Google Scholar]
- Kassou, M.; Bourekkadi, S.; Khoulji, S.; Slimani, K.; Chikri, H.; Kerkeb, M. Blockchain-based medical and water waste management conception. In E3S Web of Conferences; EDP Sciences: Paris, France, 2021; Volume 234, p. 00070. [Google Scholar]
- Campbell, R. The Genesis System Wants to Record Cleaned Fracking Water on the Blockchain; Bitcoins Magazine: Nashville, TN, USA, 2017. [Google Scholar]
- Sriyono, E. Digitizing water management: Toward the innovative use of blockchain technologies to address sustainability. Cogent Eng. 2020, 7, 1769366. [Google Scholar] [CrossRef]
- Mahmoud, H.H.M.; Wu, W.; Wang, Y. Secure Data Aggregation Mechanism for Water Distribution System using Blockchain. In Proceedings of the 2019 25th International Conference on Automation and Computing, Lancaster, UK, 5–7 September 2019; pp. 1–6. [Google Scholar]
- Arandia, E.; Eck, B.J. An R package for EPANET simulations. Environ. Model. Softw. 2018, 107, 59–63. [Google Scholar] [CrossRef]
- Demetrios, G.; Eliades, M.; Stelios, V.; Polycarpou, M.M. EPANET-MATLAB Toolkit: An Open-Source Software for Interfacing EPANET with MATLAB. In Proceedings of the IWC—14th International CCWI Conference Computing and Control for the Water Industry Conference, Amsterdam, The Netherlands, 7–9 November 2016; pp. 7–9. [Google Scholar]
- Jonkergouw, P.M. Simulating Chlorine Decay in Water Distribution Systems. Ph.D. Thesis, University of Exeter, Exeter, UK, 2007. [Google Scholar]
- Taormina, R.; Galelli, S.; Douglas, H.; Tippenhauer, N.O.; Salomons, E.; Ostfeld, A. A toolbox for assessing the impacts of cyber-physical attacks on water distribution systems. Environ. Model. Softw. 2019, 112, 46–51. [Google Scholar] [CrossRef]
- Berry, J.; Riesen, L.A.; Hart, W. TEVA-SPOT Toolkit 1.2; Technical Report; Sandia National Laboratories: Albuquerque, NM, USA, 2007. [Google Scholar]
- Klise, K.A.; Nicholson, B.; Laird, C.D. Sensor Placement Optimization Using Chama; Sandia National Laboratories: Albuquerque, NM, USA, 2017. [Google Scholar]
- Shahra, E.Q.; Wu, W. Water contaminants detection using sensor placement approach in smart water networks. J. Ambient. Intell. Humaniz. Comput. 2020, 1–16. [Google Scholar] [CrossRef]
- Eck, B.J. An R package for reading EPANET files. Environ. Model. Softw. 2016, 84, 149–154. [Google Scholar] [CrossRef]
- Hart, D.; Klise, K.A.; Bynum, M.L.; Laird, C.D.; Seth, A. Water Network Tool for Resilience (WNTR) v. 2.0; Technical Report; Sandia National Lab.: Albuquerque, NM, USA, 2019. [Google Scholar]
- Klise, K.A.; Bynum, M.; Moriarty, D.; Murray, R. A software framework for assessing the resilience of drinking water systems to disasters with an example earthquake case study. Environ. Model. Softw. 2017, 95, 420–431. [Google Scholar] [CrossRef]
- Klise, K.; Siirola, J.; Hart, D.; Hart, W.; Phillips, C.; Haxton, T.; Murray, R.; Janke, R.; Taxon, T.; Laird, C.; et al. Water Security Toolkit User Manual Version 1.2; Sandia National Lab.: Albuquerque, NM, USA, 2014. [Google Scholar]
- Zou, J.; Ye, B.; Qu, L.; Wang, Y.; Orgun, M.A.; Li, L. A proof-of-trust consensus protocol for enhancing accountability in crowdsourcing services. IEEE Trans. Serv. Comput. 2018, 12, 429–445. [Google Scholar] [CrossRef]
- Iotw. IOTW Project. Available online: https://iotw.io/ (accessed on 12 July 2021).
- Nguyen, G.T.; Kim, K. A survey about consensus algorithms used in blockchain. J. Inf. Process. Syst. 2018, 14, 101–128. [Google Scholar]
| Data | Variable Name |
|---|---|
| Nodes Information | |
| The value of all node emitter coefficients | d.NodeEmitterCoeff |
| The indices of all nodes | d.NodeIndex |
| The value of all node initial quality | d.NodeInitialQuality |
| The ID label of all nodes | d.NodeNameID |
| The demand categories | d.NodeDemandCategoriesNumber |
| The value of all node pattern indices | d.NodePatternIndex |
| The Computed values of all node pressures | getNodePressure |
| The value of the nodes source quality | d.NodeSourceQuality |
| The tank bulk rate coefficient | d.NodeTankBulkReactionCoeff |
| The node code-index for all nodes | d.NodeTypeIndex |
| Pipelines Information | |
| Retrieves the indices of the pipelines | d.getLinkPipeIndex |
| Retrieves all the value of the pipeline lengths | d.LinkLength |
| Retrieves all the value of the pipeline diameter | d. LinkDiameter |
| Bulk chemical reaction coefficient | d. LinkBulkReactionCoeff |
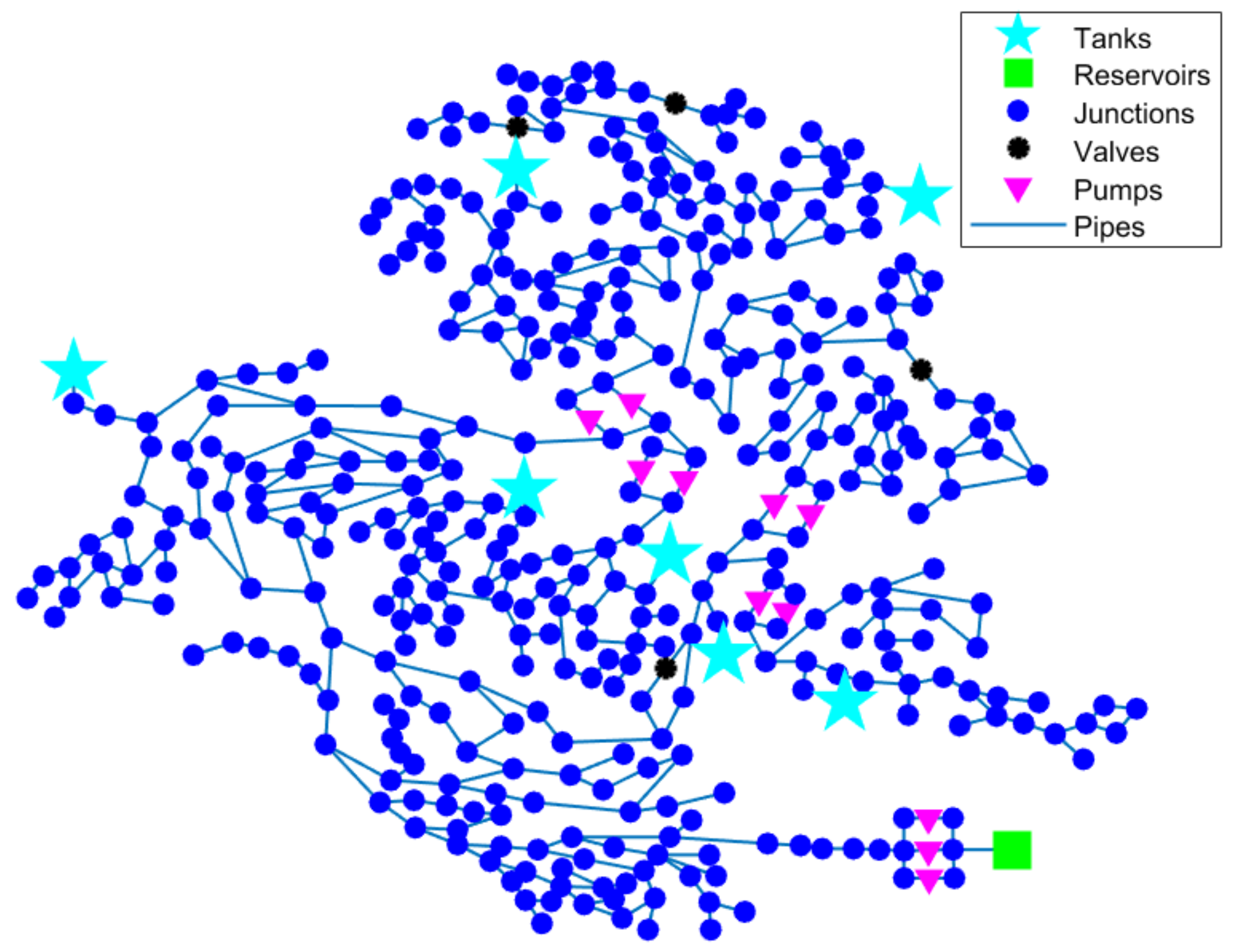
| # | WDS | Description | Specifications |
|---|---|---|---|
| 1 | D-Town | A residential district in the Eastern part of Exeter city. | 407 nodes, 443 pipelines, 11 pumps, 7 tanks, and 1 reservoir. |
| 2 | C-Town | A residential district in the Eastern part of Exeter city. | 396 nodes, 429 pipelines, 11 pumps, 7 tanks, and 1 reservoir. |
| 3 | Net3 | EPANET Example. | 97 nodes, 119 pipelines, 2 pumps, 3 tanks, and 2 reservoirs. |
| 4 | Richmond | A residential district town in the UK. | 872 nodes, 957 pipelines, 7 pumps, 6 tanks, 1 valve, and 1 reservoir. |
| 5 | BWSN | A real WDS are “twisted” to preserve their anonymity. | 129 nodes, 169 pipelines, 2 pumps, 2 tanks, 46 valves, and 1 reservoir. |
| WDS | Consensus Mechanism | (s) | (s) | (s) | (TPS) | ||
|---|---|---|---|---|---|---|---|
| D-Town | PoW | 7 | 0.07 | 0.8707 | 0.9407 | 7.44 | 24 |
| PoT | 0.4634 | 0.5334 | 13.1 | 5 | |||
| PoA | 0.4372 | 0.5072 | 13.8 | 5 | |||
| PoV | 0.4447 | 0.5147 | 13.6 | 23 | |||
| PoAuth | 3.35 + Auth | 3.42 + Auth | - | 9 | |||
| C-Town | PoW | 7 | 0.07 | 0.6919 | 0.76 | 9.18 | 24 |
| PoT | 0.4500 | 0.52 | 13.4 | 5 | |||
| PoA | 0.4380 | 0.508 | 13.7 | 5 | |||
| PoV | 0.4272 | 0.49 | 14.2 | 23 | |||
| PoAuth | 3.35 + Auth | 3.42 + Auth | - | 9 | |||
| Net3 | PoW | 3 | 0.03 | 0.2061 | 0.2361 | 12.7 | 12 |
| PoT | 0.1176 | 0.1476 | 20.3 | 5 | |||
| PoA | 0.1321 | 0.1621 | 18.5 | 5 | |||
| PoV | 0.0988 | 0.1288 | 23.2 | 11 | |||
| PoAuth | 0.15 + Auth | 0.18 + Auth | - | 5 | |||
| Richmond | PoW | 6 | 0.06 | 1.3622 | 1.4222 | 4.21 | 21 |
| PoT | 0.6168 | 0.6768 | 8.86 | 5 | |||
| PoA | 0.6606 | 0.7206 | 8.32 | 5 | |||
| PoV | 0.5611 | 0.6211 | 9.66 | 20 | |||
| PoAuth | 0.3 + Auth | 0.36 + Auth | - | 8 | |||
| BWSN | PoW | 2 | 0.02 | 0.5741 | 0.5941 | 3.36 | 9 |
| PoT | 0.1774 | 0.1974 | 10.1 | 5 | |||
| PoA | 0.1810 | 0.201 | 9.95 | 5 | |||
| PoV | 0.1688 | 0.1888 | 10.5 | 8 | |||
| PoAuth | 0.1 + Auth | 0.12 + Auth | - | 4 |
| WDS | Data Mapping | Consensus Mechanism | (s) | (s) | (s) | (TPS) | ||
|---|---|---|---|---|---|---|---|---|
| D-Town | Per timestamp | PoW | 381 | 3.81 | 277.87 | 281.68 | 1.352 | 1143 |
| PoT | 54.6 | 58.41 | 6.522 | 5 | ||||
| PoA | 59.7 | 63.51 | 6.00 | 5 | ||||
| PoV | 111.8 | 115.61 | 3.29 | 1146 | ||||
| PoAuth | 19.2 + Auth | 23.01 + Auth | - | 383 | ||||
| Per sensor | PoW | 2668 | 26.6 | 4079.9 | 4106.5 | 0.649 | 8004 | |
| PoT | 260.71 | 287.31 | 9.286 | 5 | ||||
| PoA | 265.09 | 291.69 | 9.146 | 5 | ||||
| PoV | 640.14 | 666.74 | 4.001 | 8007 | ||||
| PoAuth | 133.4 + Auth | 160 + Auth | - | 2670 | ||||
| C-Town | Per timestamp | PoW | 953 | 9.53 | 872.6 | 882.13 | 1.080 | 2859 |
| PoT | 109.2 | 118.73 | 8.02 | 5 | ||||
| PoA | 116.4 | 125.93 | 7.567 | 5 | ||||
| PoV | 491.3 | 500.83 | 1.902 | 2861 | ||||
| PoAuth | 48.2 + Auth | 489.53 + Auth | - | 955 | ||||
| Per sensor | PoW | 6672 | 66.7 | 12,288.8 | 12,355.5 | 0.54 | 20,016 | |
| PoT | 810.9 | 877.6 | 7.602 | 5 | ||||
| PoA | 794.4 | 861.1 | 7.748 | 5 | ||||
| PoV | 3314.5 | 3381.2 | 1.97 | 20,019 | ||||
| PoAuth | 333.6 + Auth | 400.3 + Auth | - | 6674 |
| Mining Metric (s) | Complexity Metric (TPS) | Throughput Metric | Cons | No. of Verifiers | Verification Based on | |
|---|---|---|---|---|---|---|
| PoW | 0.1–0.3 | 3–20 | 0.73–6.84 | Extremely High Energy consumption | All peers | The Computational capacity |
| PoT | 0.09–0.19 | 0.005–0.5 | 0.9–9.7 | Initially random generation of reputation matrix | One peer | Peers Reputation |
| PoA | 0.09–0.17 | 0.09–0.68 | 5.48–10 | A random selection of a verifier | One peer | Random-selection |
| PoV | 0.09–0.68 | 0.034–0.065 | 1.4–18.3 | High Energy consuming | All nodes | Vote of peers |
| PoAuth | 0.03–0.06 + Auth | - | - | Assumes all peers are genuine | One peer | Authentication |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mahmoud, H.H.; Wu, W.; Wang, Y. WDSchain: A Toolbox for Enhancing the Security Using Blockchain Technology in Water Distribution System. Water 2021, 13, 1944. https://doi.org/10.3390/w13141944
Mahmoud HH, Wu W, Wang Y. WDSchain: A Toolbox for Enhancing the Security Using Blockchain Technology in Water Distribution System. Water. 2021; 13(14):1944. https://doi.org/10.3390/w13141944
Chicago/Turabian StyleMahmoud, Haitham H., Wenyan Wu, and Yonghao Wang. 2021. "WDSchain: A Toolbox for Enhancing the Security Using Blockchain Technology in Water Distribution System" Water 13, no. 14: 1944. https://doi.org/10.3390/w13141944
APA StyleMahmoud, H. H., Wu, W., & Wang, Y. (2021). WDSchain: A Toolbox for Enhancing the Security Using Blockchain Technology in Water Distribution System. Water, 13(14), 1944. https://doi.org/10.3390/w13141944






