PriADA: Management and Adaptation of Information Based on Data Privacy in Public Environments
Abstract
1. Introduction
2. Background
2.1. Comparison with Prior Work
- Address: the work addresses the requirement addressed;
- Not address: the work does not address the requirement;
- Not described: No information was found about the requirement addressed;
- Under Development: The requirement is still under development. It is usually pointed out frequently in tests, validations, results obtained, or future work.
2.2. Comparison with Other Solutions
3. Materials
3.1. Definition of Management Model for Privacy in Public Environments
- Unrestricted Public Environment: Environment without time restrictions or access control;
- Temporarily Unrestricted Public Environment: Time-restricted environment without access control;
- Public Environment of Semi-Restricted Access: Environment without time restriction but with access control;
- Public Restricted Access Environment: Time-restricted environment with access control.
3.2. Definition of Individual Profiles
- Levels 1, 2 or 3: the user only has access to the information given by her/his environment;
- Level 4: the Administrator is a user that can access the information provided by the category of his/her environment. This user can also perform operations on the data as well as the users.
3.3. Definition of Types of Information
- Level 1: information given by the Unrestricted environment.
- Level 2: information provided by the Unrestricted and Temporarily Unrestricted environment.
- Level 3: information provided by the Unrestricted, Temporarily Unrestricted, and Semi-Restricted environment.
- Level 4: information given by the Unrestricted, Temporarily Unrestricted, Semi-Restricted, and Restricted environment.
4. Methods
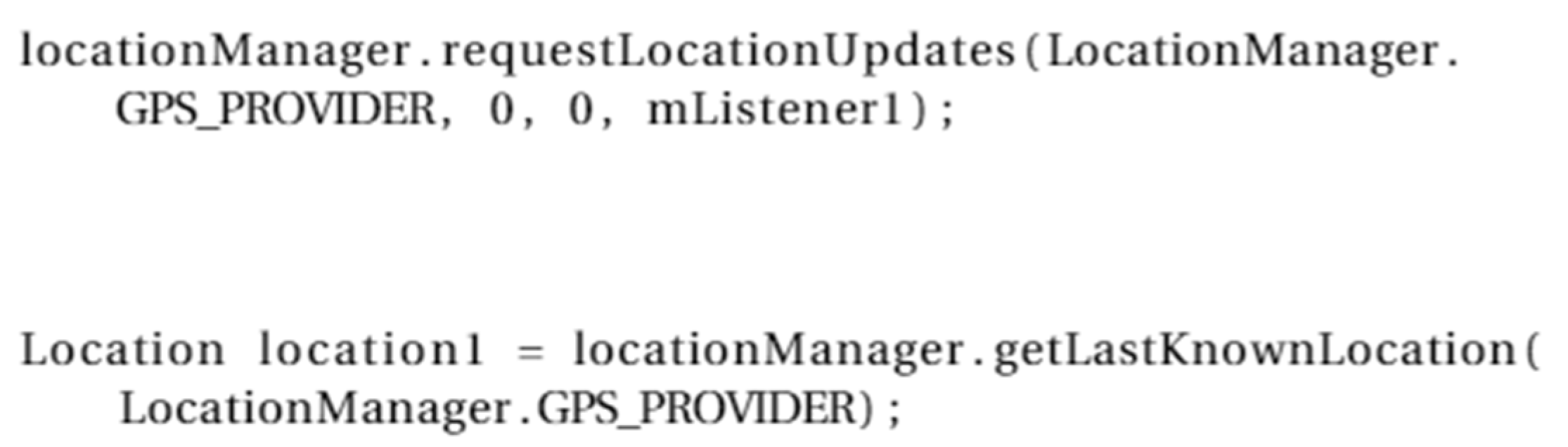
- LocationManager—this class provides access to the system’s location services (see Figure 1). These services allow the application to obtain periodic updates of the device’s location or launch an intent specified by the application when the device enters a given area. This class requires access to the application manifest, which explains the application’s request for internet access and the device’s location. In conclusion, this class uses a service and a content provider for its operation and application operation.
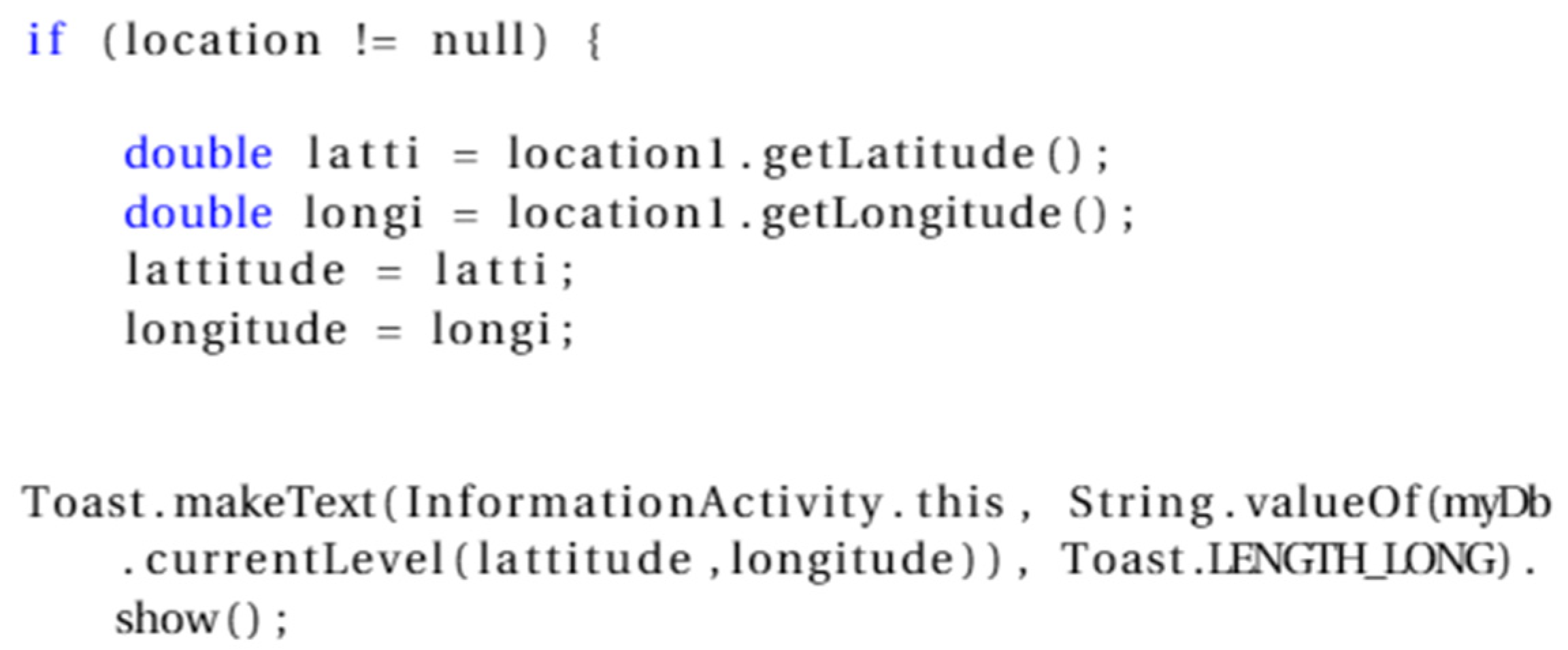
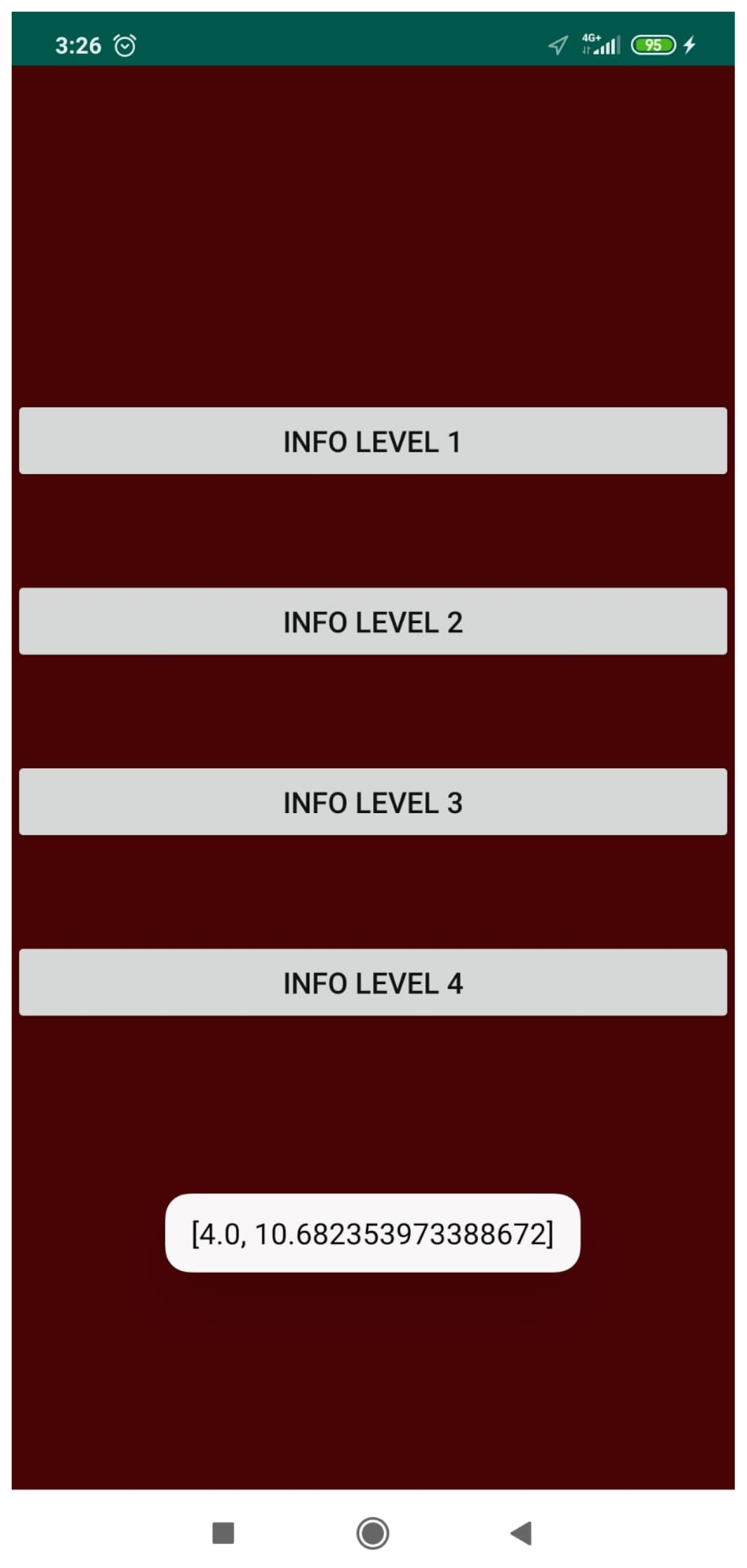
- getLocation—This function allows you first to access the device’s location (see Figure 2) through the coordinates of longitude and latitude obtained using the function currentLevel of the activity DataBaseHelper, the permission level of the location where the user is returned from the comparison with the existing locations in the database.
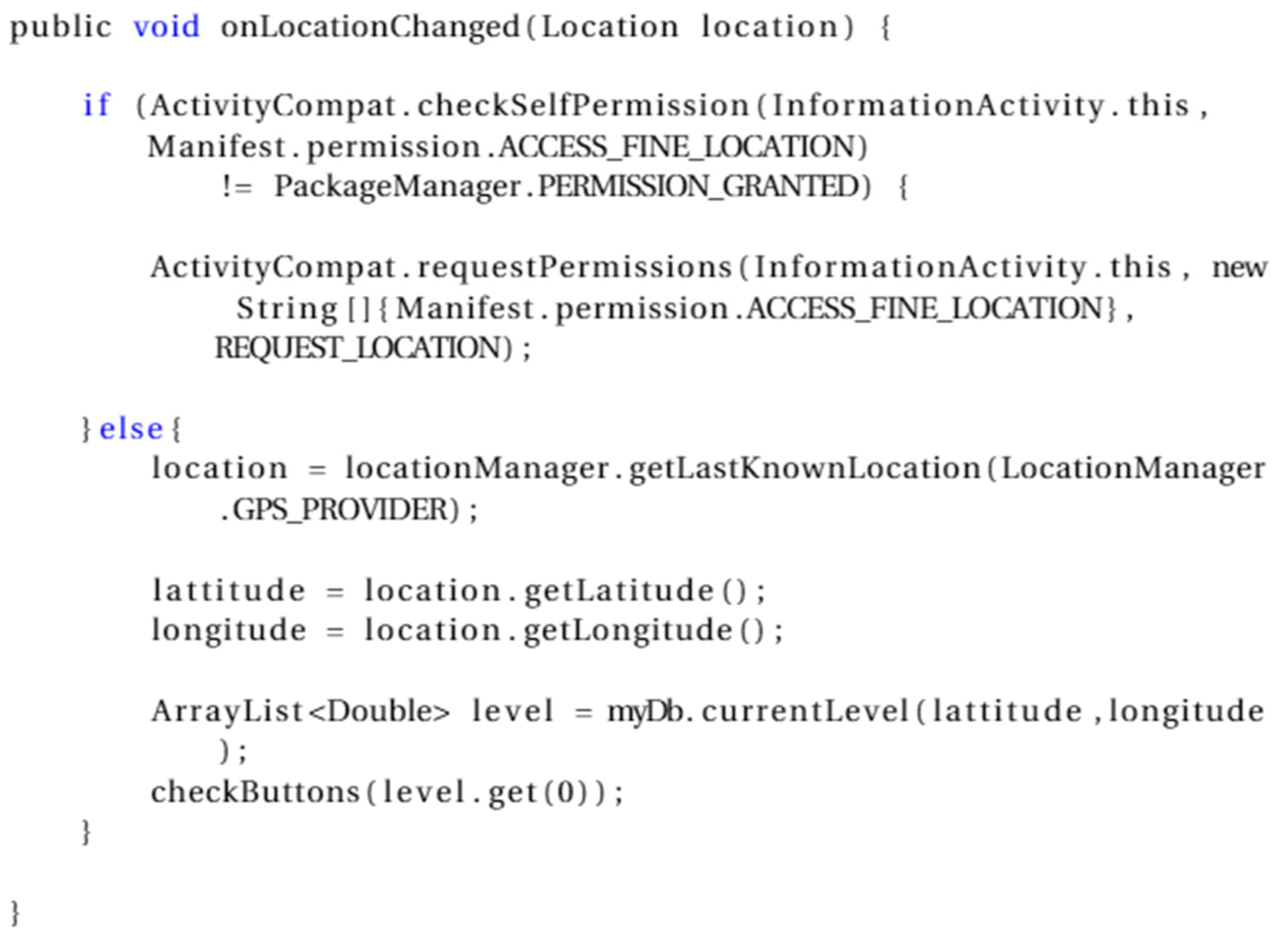
- requestLocationUpdates—This method receives as parameters a minimum distance, in meters, from the required displacement of the device, a minimum time in milliseconds, and the name of the LocationListener to make consecutive calls to the onLocationChanged function (see Figure 3).
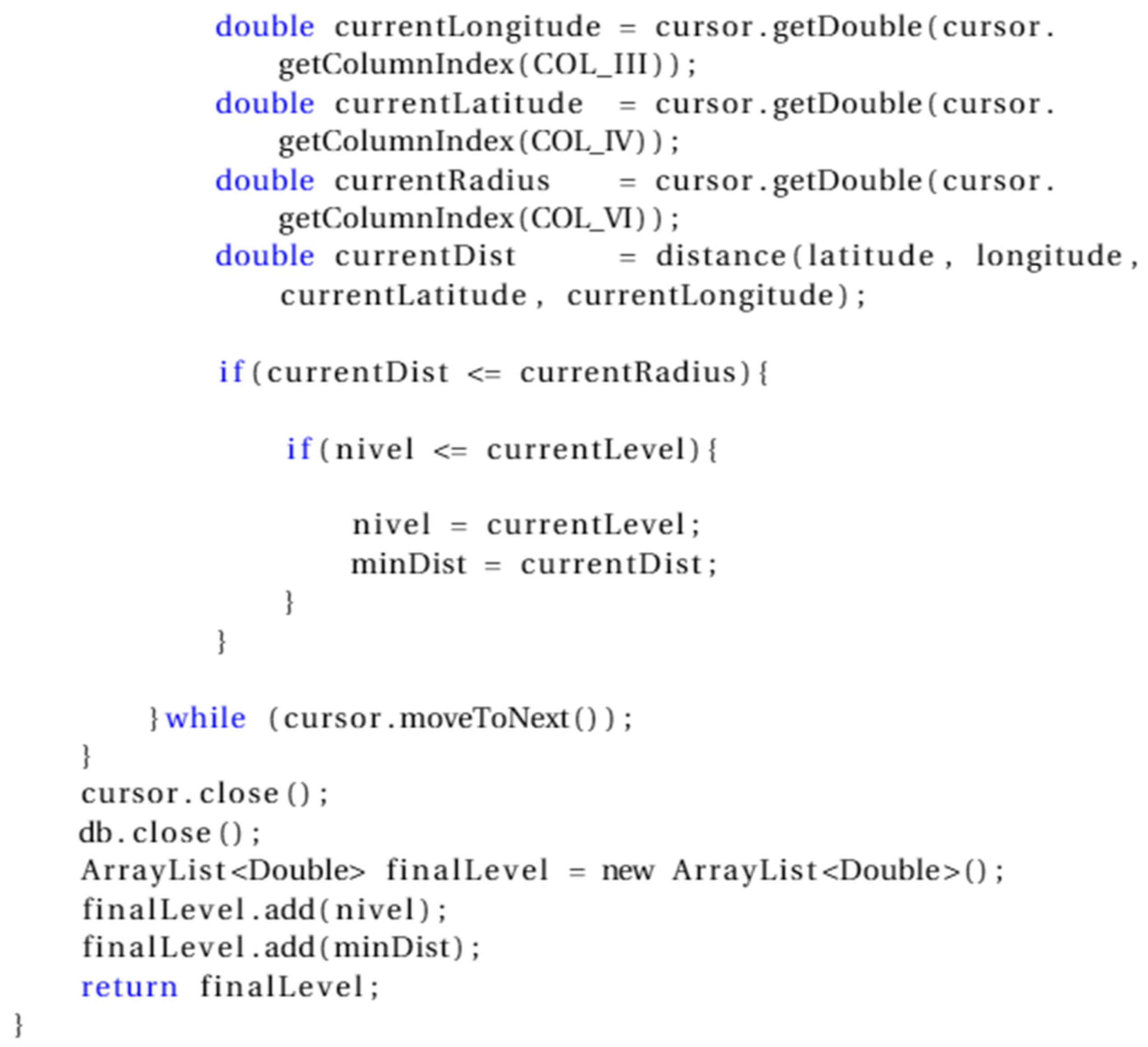
- currentLevel—This function aims to scroll through the table (using the Cursor class) that contains all location points given by longitude and latitude where access to application data is allowed. In turn, each location has an environment category and a maximum radius that delimits the access area. This function will receive the location of the device given by the getLocation function. In the currentLevel function, the distance function is called to calculate the distance. A comparison is made between the calculated distance, the user’s location, and the distance radius belonging to a given site, which is in the database. If this computed distance is less than or equal to the radius belonging to a location, the environment’s category level is returned. This level will be used by the onLocationChanged function, which will call the checkButtons function to determine the application layout change (see Figure 4).
- Distance—This function is auxiliary to the currentLevel function. Its main objective is to calculate the distance between a longitude and latitude coordinate point at which the user is and a coordinate point existing in the database, referring to a specific location.
- checkTime—This method allows an element of the user interface to be touched to act. In this method, a variable of the Calendar class was created, called currentTime, which will be used to access the current system time. Considering the defined day time, each of the existing buttons may have an access time, depending on the category of the environment. If this access time matches the device’s time, data access will be allowed. A call is made to the database to obtain the data associated with each table.
5. Application
5.1. Functional Requirements
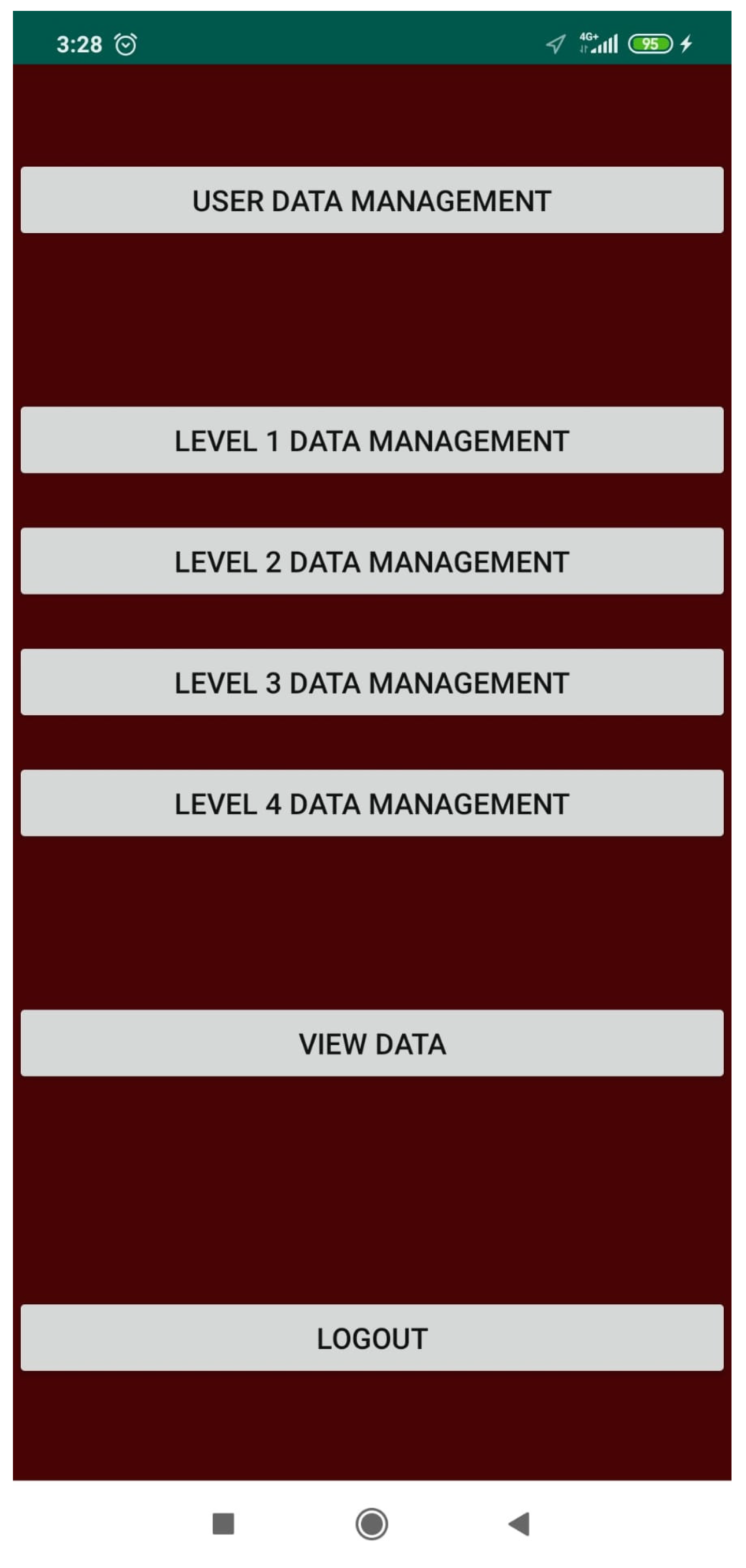
- A user with level 4 or Administrator can manage other users and application data;
- A user from level 1 to 3 can check the application data;
- The data query has access mechanisms by location and time.
5.2. Non-Functional Requirements
- The user must be registered to perform authentication;
- Only a user with level 4 can manage other users and application data;
- For any user to consult any application data, they will have to authorize the location permission;
- The mobile application requires access to the device’s location;
- Installing the application on the mobile device requires 4 Megabytes plus the space of data stored by the mobile application;
- The minimum version of the Application Programming Interface (API) for the application was 23, which corresponds to Android version 6.0 (Marshmallow).
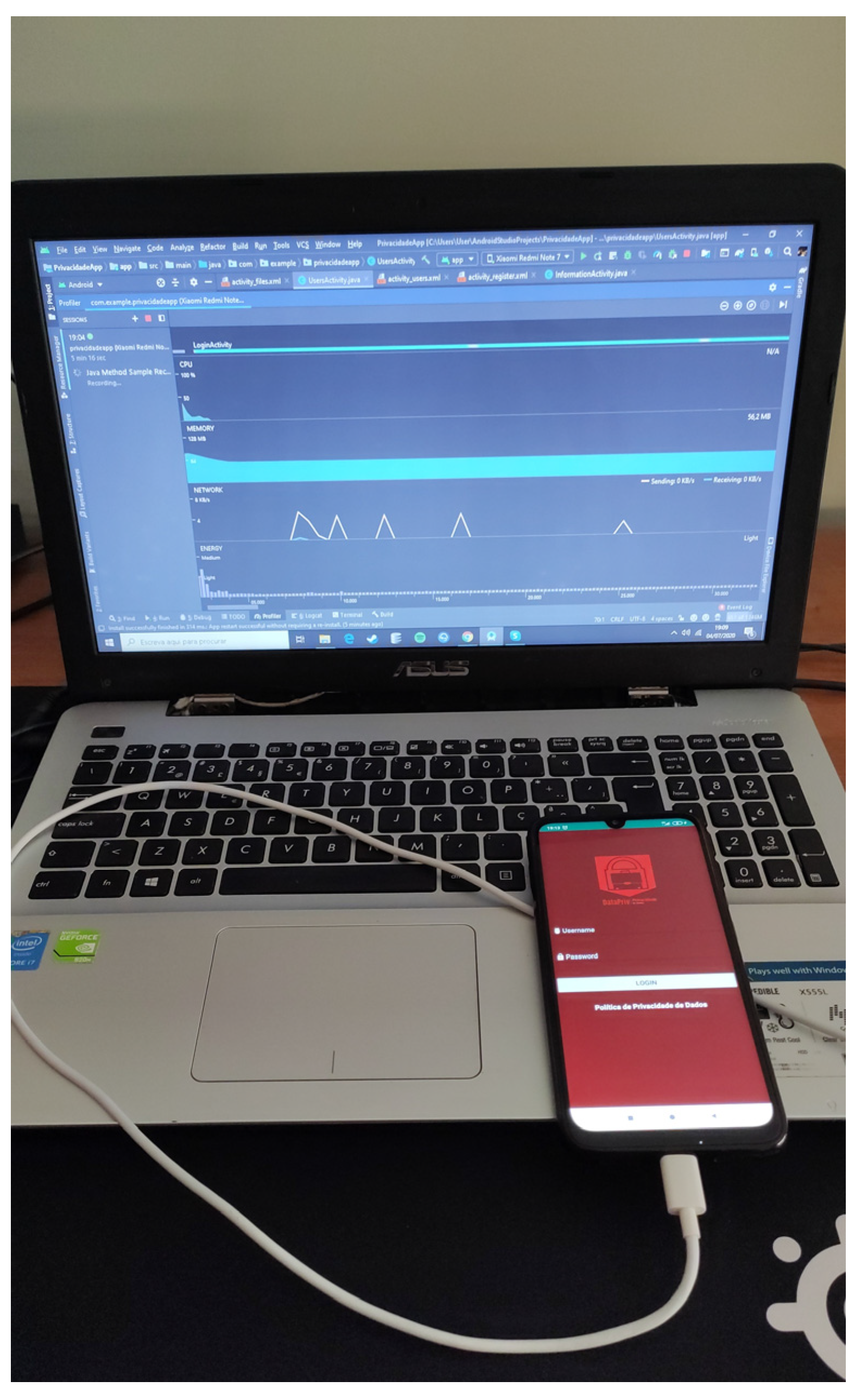
5.3. Implementation
5.3.1. Registration
5.3.2. Authentication
5.3.3. Data Management
- assisted the encrypt and decrypt functions of the data inserted by the different users;
- encrypted any information chosen before being inserted in the database;
- deciphered any existing data in the database when viewing the content or checking the fields in the screens.
6. Validation
6.1. Test Cases
- Registration/Authentication: Users with varying levels of permission were created to test the functioning of the user registration/authentication. In the first attempt to register a new user, the field “name” was placed equal to that of an existing one in the database, and the application prevented registration. In the second attempt to register a new user, the “name” field was placed differently from an existing one in the database, and the application successfully registered. After the user was introduced, a user verification was performed in the database when the authentication attempt was made. In the first attempt, the user existed in the database, and the application saved the permission level, so the user was redirected to the activity corresponding to his permission level. In the second attempt, as the user’s existence in the database was not verified, he was prevented from entering any activity;
- Location: The coordinates of an “A” location have been inserted away from the device’s position. Next, a maximum distance delimited to the bound and ensured that the user could only consult the data within an area defined by the application. As this distance did not reach the device’s current location, he was not allowed to view any data access button. To test the contrary case, the user walked towards the location “A” defined by the application. As the user walked towards location “A”, the application would automatically update its location and check if its place was within the maximum distance from location “A”. As there was a match, the buttons became visible, and the corresponding data could be viewed depending on the location’s permission. For the tests described above to be possible, first, the application asked for permission to access the device’s location, it was refused, and the user was prevented from proceeding and redirected to the previous activity corresponding to his permission level. The same attempt was made again, and when requesting access to the device’s location, it was accepted, and the GPS was not active, so he was asked for permission to activate it. The user refused and was immediately prevented from proceeding and redirected to the previous activity where he had to repeat the process previously described until all conditions were met. In the last attempt, the conditions were all checked, and the user managed to remain in the information query activity;
- Data consultation time: To ensure that the user could only consult the data at a specific time (day of the week and time), for an information (information buttons), different consultation times were introduced. The test was done for two different kinds of information. In the first, a consultation time was added outside the time the device. The second type of information was within the consultation time imposed by the device. As the first type of information was outside the application’s schedule, it prevented the user from consulting information. Finally, as the second type of data was within the limit imposed by the application, it allowed data to be asked.
6.2. Performance Tests
7. Discussion and Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| AES | Advanced Encryption Standard |
| API | Application Programming Interface |
| BLE | Bluetooth Low Energy |
| CPU | Central Processing Unit |
| DP | Differential Privacy |
| GDPR | General Data Protection Regulation |
| GPS | Global Positioning System |
| GUI | Graphical User Interface |
| IoT | Internet of Things |
| IDE | Integrated Development Environment |
| LDP | Local Differential Privacy |
| PAU | Privacy Assessment with Uncertain Consideration |
| PDT | Private Data Transmission |
| PDU | Private Data Usage |
| POI | Points of Interest |
| XML | Extensible Markup Language |
References
- Leithardt, V.R.Q.; Geyer, C.F.R.; Silva, J.M.S. Controle e Gerenciamento de Privacidade de Dados; Novas Edições Acadêmicas: Lisbon, Portugal, 2019; ISBN 978-3-8417-1533-3. [Google Scholar]
- Leithardt, V.; Santos, D.; Silva, L.; Viel, F.; Zeferino, C.; Silva, J. A Solution for Dynamic Management of User Profiles in IoT Environments. IEEE Latin Am. Trans. 2020, 18, 1193–1199. [Google Scholar] [CrossRef]
- Sousa, P.S.; Sabugueiro, D.; Felizardo, V.; Couto, R.; Pires, I.; Garcia, N.M. mHealth Sensors and Applications for Personal Aid. In Mobile Health; Adibi, S., Ed.; Springer Series in Bio-/Neuroinformatics; Springer International Publishing: Cham, Switzerland, 2015; Volume 5, pp. 265–281. ISBN 978-3-319-12816-0. [Google Scholar]
- Marques, G.; Pires, I.M.; Miranda, N.; Pitarma, R. Air Quality Monitoring using Assistive Robots for Ambient Assisted Living and Enhanced Living Environments through Internet of Things. Electronics 2019, 8, 1375. [Google Scholar] [CrossRef]
- Pires, I.M.; Garcia, N.M.; Pombo, N.; Flórez-Revuelta, F.; Rodríguez, N.D. Validation techniques for sensor data in mobile health applications. J. Sens. 2016, 2016. [Google Scholar] [CrossRef]
- Barsocchi, P.; Calabrò, A.; Crivello, A.; Daoudagh, S.; Furfari, F.; Girolami, M.; Marchetti, E. A Privacy-By-Design Architecture for Indoor Localization Systems. In Quality of Information and Communications Technology; Communications in Computer and Information Science; Shepperd, M., Brito e Abreu, F., da Rodrigues Silva, A., Pérez-Castillo, R., Eds.; Springer International Publishing: Cham, Switzerland, 2020; Volume 1266, pp. 358–366. ISBN 978-3-030-58792-5. [Google Scholar]
- Kaaniche, N.; Laurent, M.; Belguith, S. Privacy enhancing technologies for solving the privacy-personalization paradox: Taxonomy and survey. J. Netw. Comput. Appl. 2020, 102807. [Google Scholar] [CrossRef]
- Sollins, K.R. IoT Big Data Security and Privacy Versus Innovation. IEEE Internet Things J. 2019, 6, 1628–1635. [Google Scholar] [CrossRef]
- Katsikas, S.; Gkioulos, V. Security, Privacy, and Trustworthiness of Sensor Networks and Internet of Things. Sensors 2020, 20, 3846. [Google Scholar] [CrossRef]
- Lim, J.-H.; Kim, J.-W. Privacy-Preserving Aggregation of IoT Data with Distributed Differential Privacy. J. Korea Soc. Comput. Inf. 2020, 25, 65–72. [Google Scholar] [CrossRef]
- Affonso Souza, C.; César de Oliveira, C.; Perrone, C.; Carneiro, G. From privacy to data protection: The road ahead for the Inter-American System of human rights. Int. J. Hum. Rights 2020, 1–31. [Google Scholar] [CrossRef]
- Guo, X.; Wang, W.; Huang, H.; Li, Q.; Malekian, R. Location Privacy-Preserving Method Based on Historical Proximity Location. Wirel. Commun. Mobile Comput. 2020, 2020, 1–16. [Google Scholar] [CrossRef]
- Saraiva, D.A.F.; Leithardt, V.R.Q.; de Paula, D.; Sales Mendes, A.; González, G.V.; Crocker, P. PRISEC: Comparison of Symmetric Key Algorithms for IoT Devices. Sensors 2019, 19, 4312. [Google Scholar] [CrossRef]
- Qi, L.; Hu, C.; Zhang, X.; Khosravi, M.R.; Sharma, S.; Pang, S.; Wang, T. Privacy-aware Data Fusion and Prediction with Spatial-Temporal Context for Smart City Industrial Environment. IEEE Trans. Ind. Inf. 2020. [Google Scholar] [CrossRef]
- Sophus Lai, S.; Flensburg, S. A proxy for privacy uncovering the surveillance ecology of mobile apps. Big Data Soc. 2020, 7. [Google Scholar] [CrossRef]
- Lutz, C.; Hoffmann, C.P.; Ranzini, G. Data capitalism and the user: An exploration of privacy cynicism in Germany. New Media Soc. 2020, 22, 1168–1187. [Google Scholar] [CrossRef]
- Ismagilova, E.; Hughes, L.; Rana, N.P.; Dwivedi, Y.K. Security, Privacy and Risks within Smart Cities: Literature Review and Development of a Smart City Interaction Framework. Inf. Syst. Front 2020. [Google Scholar] [CrossRef]
- Yang, P.; Xiong, N.; Ren, J. Data Security and Privacy Protection for Cloud Storage: A Survey. IEEE Access 2020, 8, 131723–131740. [Google Scholar] [CrossRef]
- Anusha Linda Kostka, J.E.; Vinila Jinny, S. Data Security and Privacy Protection in Cloud Computing: A Review. In Intelligence in Big Data Technologies—Beyond the Hype; Advances in Intelligent Systems and Computing; Peter, J.D., Fernandes, S.L., Alavi, A.H., Eds.; Springer: Singapore, 2020; Volume 1167, pp. 253–257. ISBN 9789811552847. [Google Scholar]
- Chanal, P.M.; Kakkasageri, M.S. Security and Privacy in IoT: A Survey. Wirel. Pers. Commun. 2020. [Google Scholar] [CrossRef]
- May, Z.E.; Kaffel Ben Ayed, H.; Machfar, D. State of the art on Privacy Risk Estimation Related to Android Applications. In Proceedings of the 2019 15th International Wireless Communications & Mobile Computing Conference (IWCMC), Tangier, Morocco, 24–28 June 2019; IEEE: Tangier, Morocco, 2019; pp. 889–894. [Google Scholar] [CrossRef]
- Zhang, H.; Latif, S.; Bassily, R.; Rountev, A. Introducing Privacy in Screen Event Frequency Analysis for Android Apps. In Proceedings of the 2019 19th International Working Conference on Source Code Analysis and Manipulation (SCAM), Cleveland, OH, USA, 30 September–1 October 2019; IEEE: Cleveland, OH, USA, 2019; pp. 268–279. [Google Scholar] [CrossRef]
- Liu, X.; Liu, J.; Zhu, S.; Wang, W.; Zhang, X. Privacy Risk Analysis and Mitigation of Analytics Libraries in the Android Ecosystem. IEEE Trans. Mob. Comput. 2020, 19, 1184–1199. [Google Scholar] [CrossRef]
- Kesswani, N.; Lyu, H.; Zhang, Z. Analyzing Android App Privacy with GP-PP Model. IEEE Access 2018, 6, 39541–39546. [Google Scholar] [CrossRef]
- Wang, X.; Qin, X.; Hosseini, M.B.; Slavin, R.; Breaux, T.D.; Niu, J. GUILeak: Tracing privacy policy claims on user input data for Android applications. In Proceedings of the 40th International Conference on Software Engineering, Gothenburg, Sweden, 27 May–3 June 2018; ACM: Gothenburg, Sweden, 2018; pp. 37–47. [Google Scholar] [CrossRef]
- Feng, X.; Wang, L. PAU: Privacy Assessment method with Uncertainty consideration for cloud-based vehicular networks. Future Gener. Comput. Syst. 2019, 96, 368–375. [Google Scholar] [CrossRef]
- Leithardt, V.R.Q. UbiPri: Middleware Para Controle e Gerenciamento de Privacidade em Ambientes Ubíquos. Ph.D. Thesis, Universidade Federal do Rio Grande do Sul, Porto Alegre, Brazil, 2015. Available online: https://lume.ufrgs.br/handle/10183/147774 (accessed on 28 September 2020).
- Yan, Y.; Gai, K.; Jiang, P.; Xu, L.; Zhu, L. Location-based Privacy-Preserving Techniques in Connected Environment: A Survey. In Proceedings of the 2019 IEEE International Conference on Smart Cloud (SmartCloud), Tokyo, Japan, 10–12 December 2019; IEEE: Tokyo, Japan, 2019; pp. 156–162. [Google Scholar] [CrossRef]
- Zhuo, G.; Yang, H. Privacy-preserving context-aware friend discovery based on mobile sensing. In Proceedings of the 2018 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 12–14 January 2018; IEEE: Las Vegas, NV, USA, 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Hao, G.; Ya-Bin, X. Research on privacy preserving method based on T-closeness model. In Proceedings of the 2017 3rd IEEE International Conference on Computer and Communications (ICCC), Chengdu, China, 13–16 December 2017; IEEE: Chengdu, China, 2017; pp. 1455–1459. [Google Scholar] [CrossRef]
- Sales Mendes, A.; Jiménez-Bravo, D.M.; Navarro-Cáceres, M.; Reis Quietinho Leithardt, V.; Villarrubia González, G. Multi-Agent Approach Using LoRaWAN Devices: An Airport Case Study. Electronics 2020, 9, 1430. [Google Scholar] [CrossRef]
- Zhao, M.; Ding, Y.; Wu, Q.; Wang, Y.; Qin, B.; Fan, K. Privacy-Preserving Lightweight Data Monitoring in Internet of Things Environments. Wirel. Pers. Commun. 2020. [Google Scholar] [CrossRef]
- Kang, J.; Steiert, D.; Lin, D.; Fu, Y. MoveWithMe: Location Privacy Preservation for Smartphone Users. IEEE Trans. Inf. Forensic Secur. 2020, 15, 711–724. [Google Scholar] [CrossRef]
- Silva, L.A.; Valderi, R.Q.L.; Rudimar, S.D.; Silva, J.S. Priser—Utilização De Ble Para Localização E Notificação Com Base Na Privacidade De Dados. Rev. Eletrônica Argent-Bras. Tecnol. Inf. Comun. 2018. [Google Scholar] [CrossRef]
- Zhang, P.; Hu, C.; Chen, D.; Li, H.; Li, Q. ShiftRoute: Achieving Location Privacy for Map Services on Smartphones. IEEE Trans. Veh. Technol. 2018, 67, 4527–4538. [Google Scholar] [CrossRef]
- Huang, J.; Xiong, Y.; Huang, W.; Xu, C.; Miao, F. SieveDroid: Intercepting Undesirable Private-Data Transmissions in Android Applications. IEEE Syst. J. 2020, 14, 375–386. [Google Scholar] [CrossRef]
- Toresson, L.; Shaker, M.; Olars, S.; Fritsch, L. PISA: A Privacy Impact Self-assessment App Using Personas to Relate App Behavior to Risks to Smartphone Users. In HCI International 2020—Posters; Communications in Computer and Information Science; Stephanidis, C., Antona, M., Eds.; Springer International Publishing: Cham, Switzerland, 2020; Volume 1226, pp. 613–621. ISBN 978-3-030-50731-2. [Google Scholar]
- Measure App Performance with Android Profiler. Available online: https://developer.android.com/studio/profile/android-profiler (accessed on 11 July 2020).
- Android. The Platform Pushing what’s Possible. Available online: https://www.android.com/ (accessed on 10 July 2020).
- Inspect Energy Usage with the Energy Profiler. Available online: https://developer.android.com/studio/profile/energy-profiler (accessed on 10 July 2020).
- View Java Heap and Memory Allocations with Memory Profiler. Available online: https://developer.android.com/studio/profile/memory-profiler (accessed on 10 July 2020).
- Inspect CPU Activities with the CPU Profiler. Available online: https://developer.android.com/studio/profile/cpu-profiler (accessed on 11 July 2020).


| Study | Data Privacy Approaches | |||
|---|---|---|---|---|
| User | Application | Generalized Environment | Public Environments | |
| May et al. [19] | Address | Address | Not described | Not described |
| Zhang et al. [20] | Address | Address | Not described | Not described |
| Liu et al. [21] | Address | Address | Not described | Not described |
| Kesswani et al. [22] | Address | Address | Not described | Not described |
| Wang et al. [23] | Address | Not address | Not described | Not described |
| Sollins et al. [6] | Address | Not address | Address | Not described |
| Feng et al. [24] | Not described | Address | Not described | Not described |
| Leithardt et al. [25] | Address | Address | Address | Not address |
| Yan et al. [28] | Address | Address | Not described | Not described |
| Zhuo et al. [29] | Address | Address | Not described | Not described |
| Hao et al. [30] | Address | Address | Not described | Not described |
| Sales Mendes et al. [31] | Address | Address | Address | Not address |
| Zhao et al. [32] | Address | Address | Not described | Not described |
| This study | Address | Address | Address | Address |
| Applications | Approaches | ||
|---|---|---|---|
| Local Privacy | Mobile Devices | Geolocation | |
| MoveWithMe [33] | Yes | Yes | Yes |
| Priser [34] | Yes | Yes | Yes |
| ShiftRoute [35] | Yes | Yes | Yes |
| SieveDroid [36] | No | Yes | No |
| UbiPri [27] | Yes | Yes | Yes |
| PISA [37] | Yes | Yes | No |
| This study | Yes | Yes | Yes |
| Categories | Public Environments | |||
|---|---|---|---|---|
| Unrestricted Public Environment | Temporarily Unrestricted Public Environment | Public Environment of Semi-Restricted Access | Public Restricted Access Environment | |
| Garden | Yes | No | No | No |
| Public highway | Yes | No | No | No |
| Square | Yes | No | No | No |
| Shopping center | No | Yes | No | No |
| Gallery | No | Yes | No | No |
| Parking | No | Yes | No | No |
| Trade point | No | No | No | Yes |
| Service | No | No | Yes | No |
| Institution | No | No | No | Yes |
| Categories | Public Environments | |||
|---|---|---|---|---|
| Level 1 | Level 2 | Level 3 | Level 4 | |
| Unrestricted | Yes | No | No | No |
| Temporarily Unrestricted | Yes | Yes | No | No |
| Semi-Restricted | Yes | Yes | Yes | No |
| Restricted | Yes | Yes | Yes | Yes |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lopes, H.; Pires, I.M.; Sánchez San Blas, H.; García-Ovejero, R.; Leithardt, V. PriADA: Management and Adaptation of Information Based on Data Privacy in Public Environments. Computers 2020, 9, 77. https://doi.org/10.3390/computers9040077
Lopes H, Pires IM, Sánchez San Blas H, García-Ovejero R, Leithardt V. PriADA: Management and Adaptation of Information Based on Data Privacy in Public Environments. Computers. 2020; 9(4):77. https://doi.org/10.3390/computers9040077
Chicago/Turabian StyleLopes, Hugo, Ivan Miguel Pires, Hector Sánchez San Blas, Raúl García-Ovejero, and Valderi Leithardt. 2020. "PriADA: Management and Adaptation of Information Based on Data Privacy in Public Environments" Computers 9, no. 4: 77. https://doi.org/10.3390/computers9040077
APA StyleLopes, H., Pires, I. M., Sánchez San Blas, H., García-Ovejero, R., & Leithardt, V. (2020). PriADA: Management and Adaptation of Information Based on Data Privacy in Public Environments. Computers, 9(4), 77. https://doi.org/10.3390/computers9040077







