Risk Reduction Optimization of Process Systems under Cost Constraint Applying Instrumented Safety Measures †
Abstract
1. Introduction
2. Risk Reduction Approach
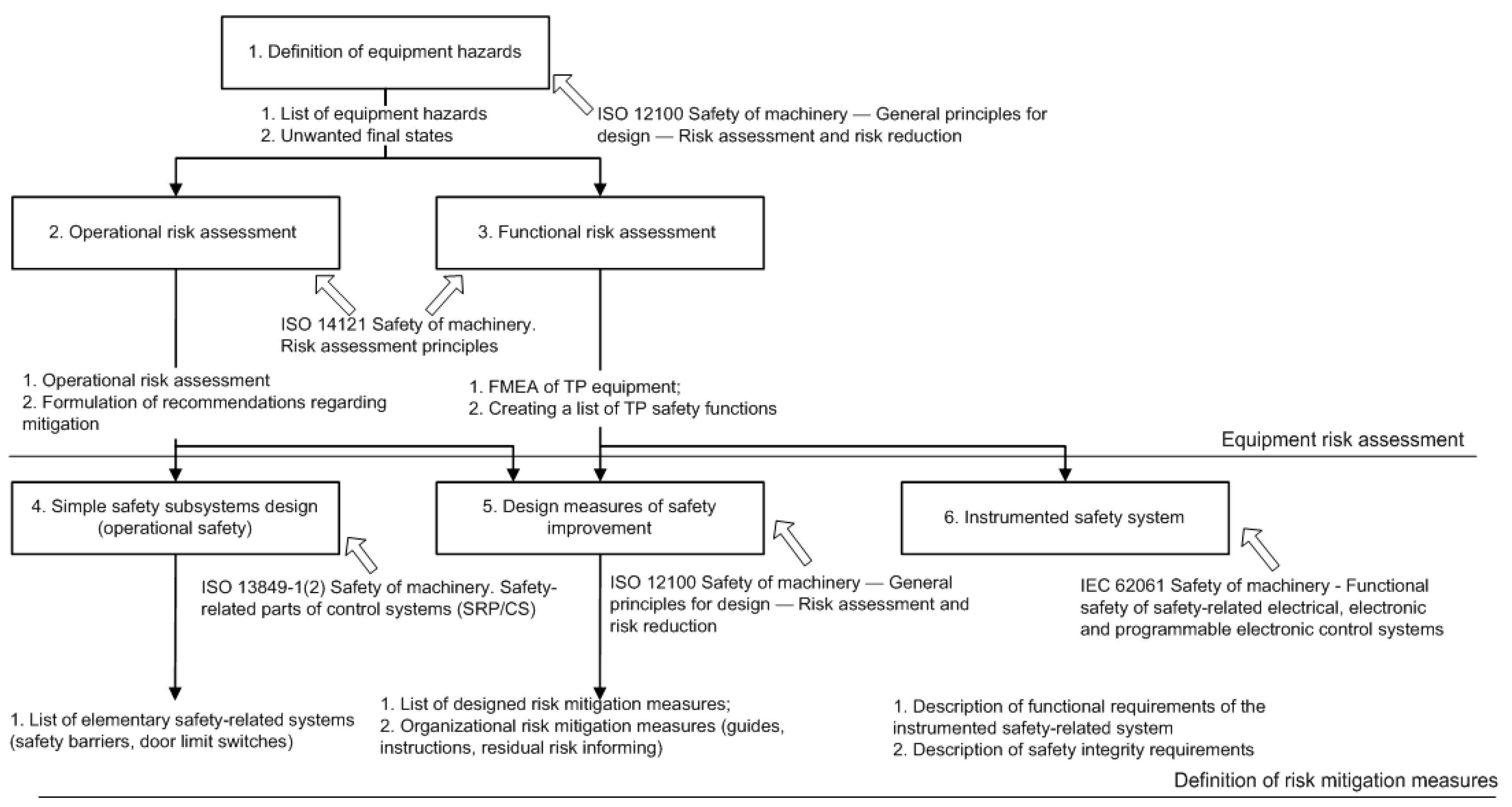
2.1. Relationship of the Safety Analysis and the Design Process
- Safety lifecycle planning: the first and foremost step of the safety analysis is collection of input data, formulation of technological process (TP) safety criteria and objectives. The selection of standards that will be applied to prove the safety level is justified in the frames of safety lifecycle planning.
- Preliminary safety analysis (PSA): All functions of technological process equipment are assessed to discover potential functional failures, and hazards connected with particular failure states are classified. The preliminary safety analysis systematizes requirements and criteria laid down in the contract (tender documentation) and provides a preliminary proof of that the proposed technological process equipment architecture can ensure fulfillment of these requirements, justifies the necessity of introducing protective measures, additional assemblies and functionality. The PSA is updated throughout the entire duration of the development process.
- Technological process safety analysis: collection, analysis and documenting the results, proving that the design, control system architecture, and selected components meet the safety requirements and objectives.
- Common cause analysis sets requirements for physical and functional separation, isolation, and independence of technological process elements.
2.2. Risks Classification and Safety Barriers Design
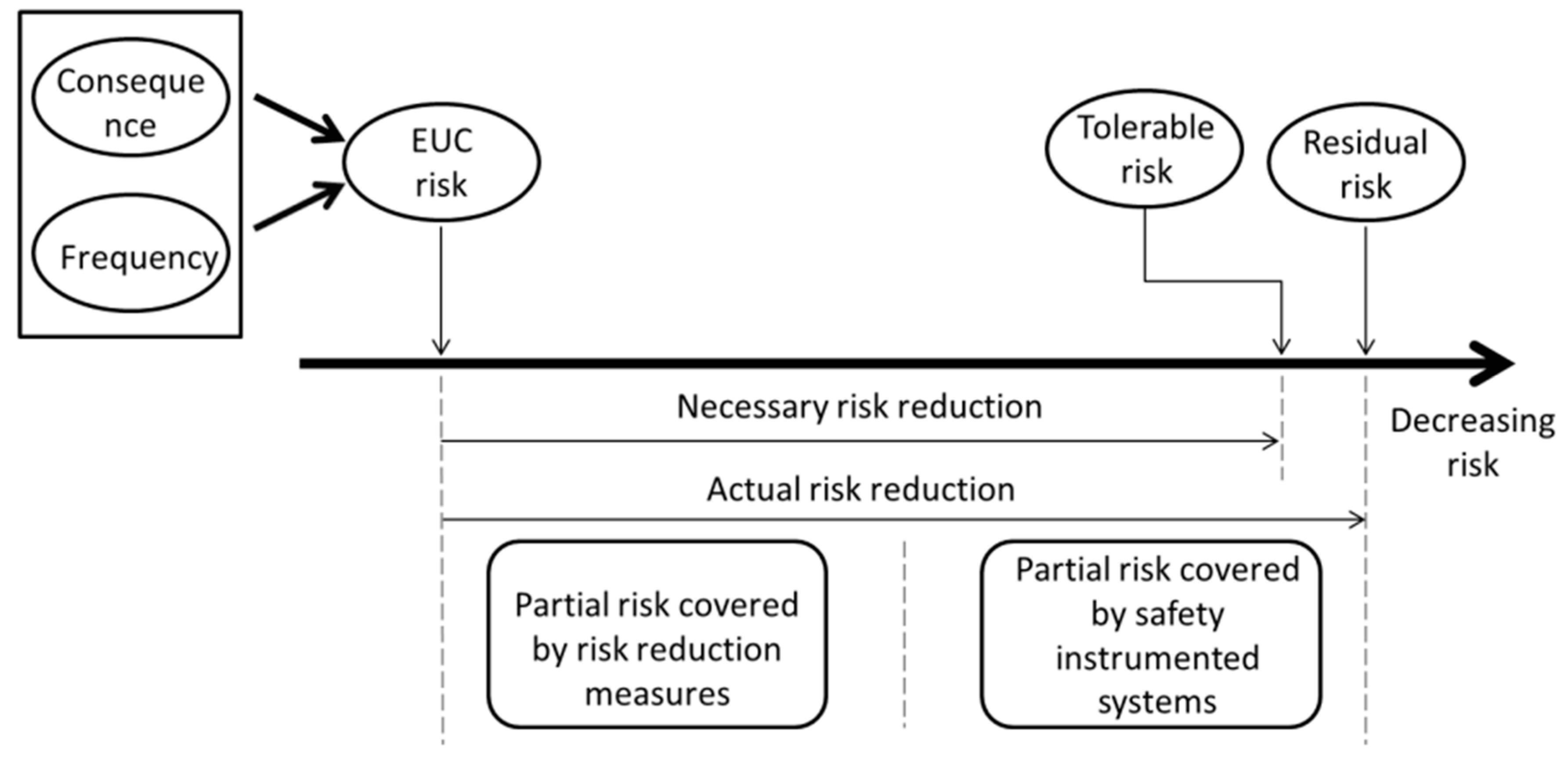
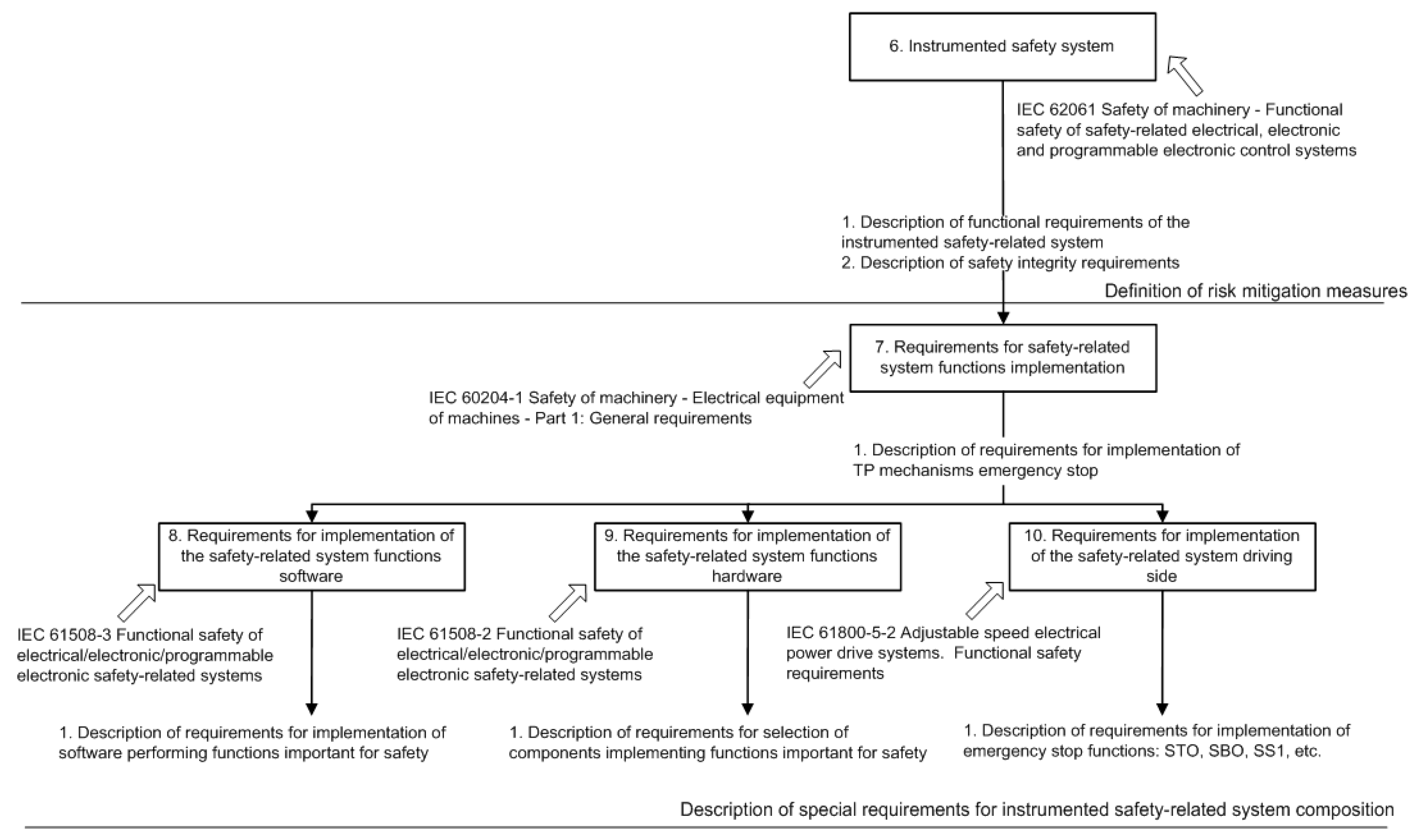
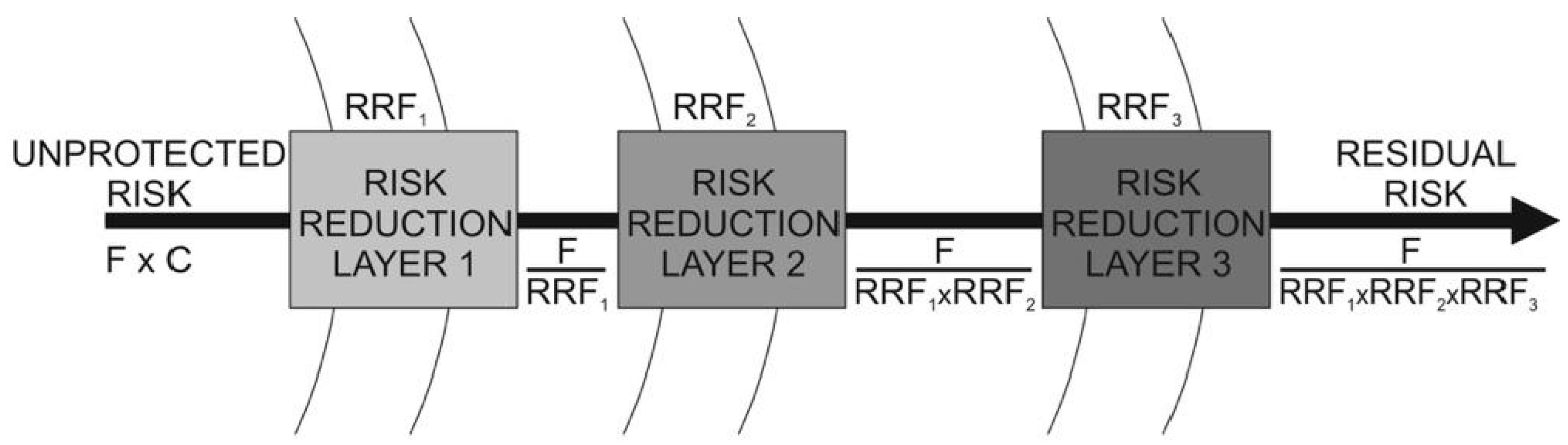
2.3. Risk Reduction and SIS
3. Risk Reduction and Optimization
3.1. Problem Statement
- qi—probability of failure of the i-th component of the process system;
- Sj—the cost of implementing the j-th safety measure;
- qlockj—the probability of failure of the j-th lock;
- qemsj—the probability of failure of j-th emergency stop;
- qdiagj—probability of failure of the j-th diagnosis, revealing pre-emergency conditions; and
- qreq—the probability of occurrence of a dangerous situation, specified in regulations or determined during the analysis.
3.2. Approach to the Optimization Problem Solving
3.3. Algorithm of Monte Carlo Simulation
4. Model of Technological Process Subsystem
4.1. Model Description
4.2. Model Initial Data
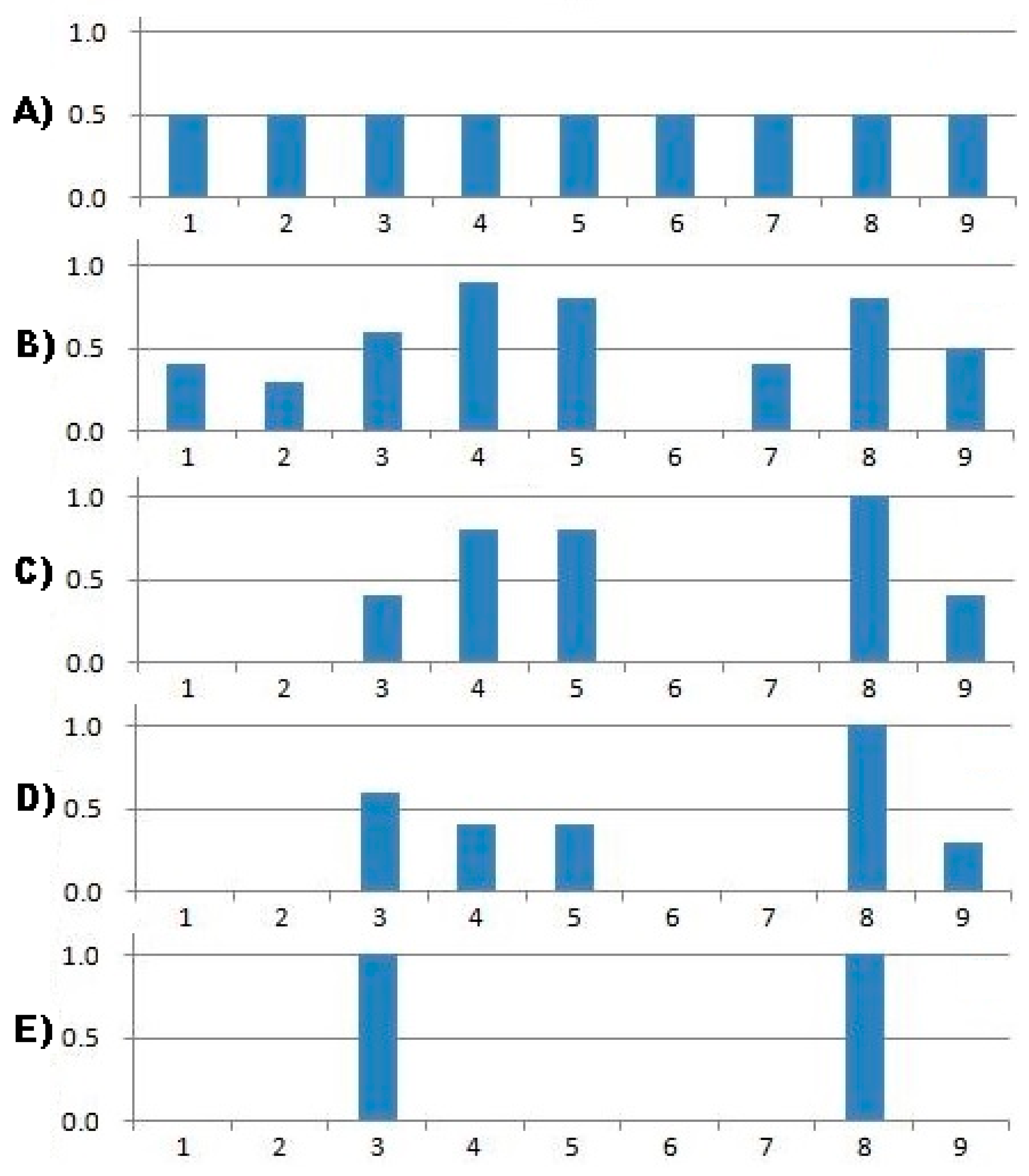
4.3. Optimization Parameters
4.4. Modeling Results
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- IEC. IEC 61511 Functional Safety–Safety Instrumented System for the Process Industry Sector; IEC: Geneva, Switzerland, 2003. [Google Scholar]
- IEC. IEC 61508 Functional Safety of Electronical/Electrical/Programmable Electronic Safety-Related Systems; IEC: Geneva, Switzerland, 2012. [Google Scholar]
- Bogatyrev, V.A. On interconnection control in redundancy of local network buses with limited availability. Eng. Simul. 1999, 16, 463–469. [Google Scholar]
- Habibullah, M.S.; Lumanpauw, E.; Kolowrocki, K.; Soszynska, J.; Ming, N.G. A computational tool for general model of industrial systems. Operation processes. Electron. J. Reliab. Risk Anal. Theory 2009, 2, 181–191. [Google Scholar]
- ISO 12100 Safety of machinery — General principles for design — Risk assessment and risk reduction Safety of Machinery-Basic Concepts, General Principles for Design-Part 1: Basic Terminology, Methodology; ISO: Geneva, Switzerland, 2010.
- Hale, A. Note on barriers and delivery systems. In Proceedings of the PRISM Conference, Athens, Greece, 15–17 September 2003. [Google Scholar]
- Kecklund, L.J.; Edland, A.; Wedin, P.; Svenson, O. Safety barrier function analysis in a process industry: A nuclear power application. Ind. Ergon. 1996, 17, 275–284. [Google Scholar] [CrossRef]
- Delvosalle, C.; Fievez, C.; Pipart, A. Accidental Risk Assessment Methodology for Industries in the context of the Seveso II directive; Deliverable, D.1C. WP1—Mons; Major Risk Research Centre: Mons, Belgium, 2003. [Google Scholar]
- Svenson, O. The accident evolution and barrier function (AEB) model applied to incident analysis in the processing industries. Risk Anal. 1991, 11, 499–507. [Google Scholar] [CrossRef] [PubMed]
- ISO 14121-2 Safety of Machinery—Risk Assessment—Part 2: Practical Guidance and Examples of Methods; ISO: Geneva, Switzerland, 2012.
- IEC 62061 Safety of Machinery—Functional Safety of Safety Related Electrical, Electronic and Programmable Electronic Control Systems; IEC: Geneva, Switzerland, 2012.
- ISO 13849-1 Safety of Machinery—Safety-Related Parts of Control Systems—Part 1: General Principles for Design; ISO: Geneva, Switzerland, 2015.
- Bogatyrev, V.A.; Bogatyrev, S.V.; Bogatyrev, A.V. Model and Interaction Efficiency of Computer Nodes Based on Transfer Reservation at Multipath Routing. In Wave Electronics and its Application in Information and Telecommunication Systems WECONF; IEEE: Piscataway, NJ, USA, 2019. [Google Scholar] [CrossRef]
- Bogatyrev, A.V.; Bogatyrev, V.A.; Bogatyrev, S.V. Multipath Redundant Transmission with Packet Segmentation. In Wave Electronics and its Application in Information and Telecommunication Systems WECONF; IEEE: Piscataway, NJ, USA, 2019. [Google Scholar] [CrossRef]
- Smith., D.J.; Simpson, K.J.L. Functional Safety: A Straightforward Guide to Applying IEC 61508 and Related Standards, 2nd ed.; Elsevier Butterworth Heinemann: Oxford, UK, 2004. [Google Scholar]
- Rausand, M.; Høyland, A. System Reliability Theory. In Models, Statistical Methods and Applications; Wiley: Hoboken, NJ, USA, 2004. [Google Scholar]
- Hokstad, P.; Utne, I.B.; Vatn, J. Risk and Interdependencies in Critical Infrastructures; Springer: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Andonov, R.; Poirriez, V.; Rajopadhye, S. Unbounded Knapsack Problem: Dynamic programming revisited. Eur. J. Oper. Res. 2000, 123, 168–181. [Google Scholar] [CrossRef]
- Martello, S.; Pisinger, D.; Toth, P. Dynamic programming and strong bounds for the 0-1 knapsack problem. Manag. Sci. 1999, 45, 414–424. [Google Scholar] [CrossRef]
- Martello, S.; Toth, P. Knapsack Problems: Algorithms and Computer Implementations; John Wiley and Sons: Hoboken, NJ, USA, 1990. [Google Scholar]
- Kroese, D.P.; Taimre, T.; Botev, Z.I. Handbook of Monte Carlo Methods. In Wiley Series in Probability and Statistics; John Wiley and Sons: New York, NY, USA, 2011. [Google Scholar]
- Rubinstein, R.Y. Combinatorial optimization, cross-entropy, ants and rare events. In Stochastic Optimization: Algorithms and Applications; Springer: Boston, MA, USA, 2001; pp. 304–358. [Google Scholar]
- Rubinstein, R.Y.; Kroese, D.P. The Cross-Entropy Method: A Unified Approach to Combinatorial Optimization, Monte Carlo Simulation and Machine Learning; Springer: New York, NY, USA, 2004. [Google Scholar]
- IEC 60300-3-9 Dependability Management—Part 3: Application Guide—Section 9: Risk Analysis of Technological Systems; IEC: Geneva, Switzerland, 2003.
- Redutskiy, Y. Optimization of safety instrumented system design and maintenance frequency for oil and gas industry processes. Manag. Prod. Eng. Rev. 2017, 8, 46–59. [Google Scholar] [CrossRef]
- Ramírez-Marengo, C.; de Lira-Flores, J.; López-Molina, A.; Vázquez-Román, R.; Carreto-Vázquez, V.; Mannan, M.S. A Formulation to Optimize the Risk Reduction Process Based on LOPA. J. Loss Prev. Ind. 2013, 26, 489–494. [Google Scholar] [CrossRef]



| Element | Failure Type | Consequences | Safety Measures |
|---|---|---|---|
| Tank | Destruction of the hull | Fire | D1-control of the hull by ultrasonic control device D2-magneto resistive monitoring device H1-switching on the fire pump and water supply H3-emergency opening of the emergency drain |
| Level sensor | False values | Exceeding the limit | D5-monitoring of the sensor Z2-emergency stop of process equipment (pump) H3-emergency opening of drain valve |
| Level sensor | The absence of values | Shutdown | not required |
| Feed pump | Feed loss | Shutdown | not required |
| Feed pump | Overheat | Fire | D3-monitoring the state of the windings D4-housing temperature control H1-switching on the fire pump and water supply |
| Feed pump | False start | Exceeding the limit | Z2-emergency stop of process equipment (pump) H3-emergency opening of drain valve |
| Transfer valve | Failure to respond | Shutdown | not required |
| Transfer valve | False opening | Shutdown | not required |
| Control system | Loss of control signal | Shutdown | not required |
| Control system | Erroneous command | Exceeding the limit | Z2-emergency stop of process equipment (pump) L1-pump control limitation when 70% of the tank volume H3-emergency opening of drain valve |
| Event | Code | FR, h−1 | α * | Probability Per Year ** |
|---|---|---|---|---|
| Tank. Destruction | qtank | 1 × 10−7 | 80% | 7.01 × 10−4 |
| Feed pump. Overheating | qPD.H | 1 × 10−5 | 50% | 4.29 × 10−2 |
| Level sensor. False signal | qLV.F | 1 × 10−6 | 30% | 2.62 × 10−3 |
| Feed pump. False start | qPD.F | 1 × 10−5 | 5% | 4.37 × 10−3 |
| Control system. Erroneous response | qCU.F | 1 × 10−6 | 5% | 4.38 × 10−4 |
| # | Safety Measures | Cost, c.u. | Probability Per Year * |
|---|---|---|---|
| qD1 | Control of the body condition by ultrasonic method | 100 | 1.00 × 10−3 |
| qD2 | Magneto resistive monitoring device | 200 | 1.00 × 10−3 |
| qD3 | Control condition of winding | 10 | 1.00 × 10−5 |
| qD4 | Housing temperature control | 25 | 1.00 × 10−4 |
| qD5 | Monitoring of the sensor status by initial test | 10 | 1.00 × 10−5 |
| qZ1 | The inclusion of the fire pump and water flow | 400 | 1.00 × 10−3 |
| qZ2 | Emergency stop of process equipment (pump) | 200 | 1.00 × 10−3 |
| qZ3 | Emergency opening of the discharge valve | 200 | 1.00 × 10−4 |
| qL1 | Pump control limitation at 70% of tank volume | 5 | 1.00 × 10−4 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Moshnikov, A.; Bogatyrev, V. Risk Reduction Optimization of Process Systems under Cost Constraint Applying Instrumented Safety Measures. Computers 2020, 9, 50. https://doi.org/10.3390/computers9020050
Moshnikov A, Bogatyrev V. Risk Reduction Optimization of Process Systems under Cost Constraint Applying Instrumented Safety Measures. Computers. 2020; 9(2):50. https://doi.org/10.3390/computers9020050
Chicago/Turabian StyleMoshnikov, Aleksandr, and Vladimir Bogatyrev. 2020. "Risk Reduction Optimization of Process Systems under Cost Constraint Applying Instrumented Safety Measures" Computers 9, no. 2: 50. https://doi.org/10.3390/computers9020050
APA StyleMoshnikov, A., & Bogatyrev, V. (2020). Risk Reduction Optimization of Process Systems under Cost Constraint Applying Instrumented Safety Measures. Computers, 9(2), 50. https://doi.org/10.3390/computers9020050





