CSCCRA: A Novel Quantitative Risk Assessment Model for SaaS Cloud Service Providers
Abstract
1. Introduction
2. Literature Review
2.1. Cloud Risk Assessment
2.2. Cloud Supply Chain Risks
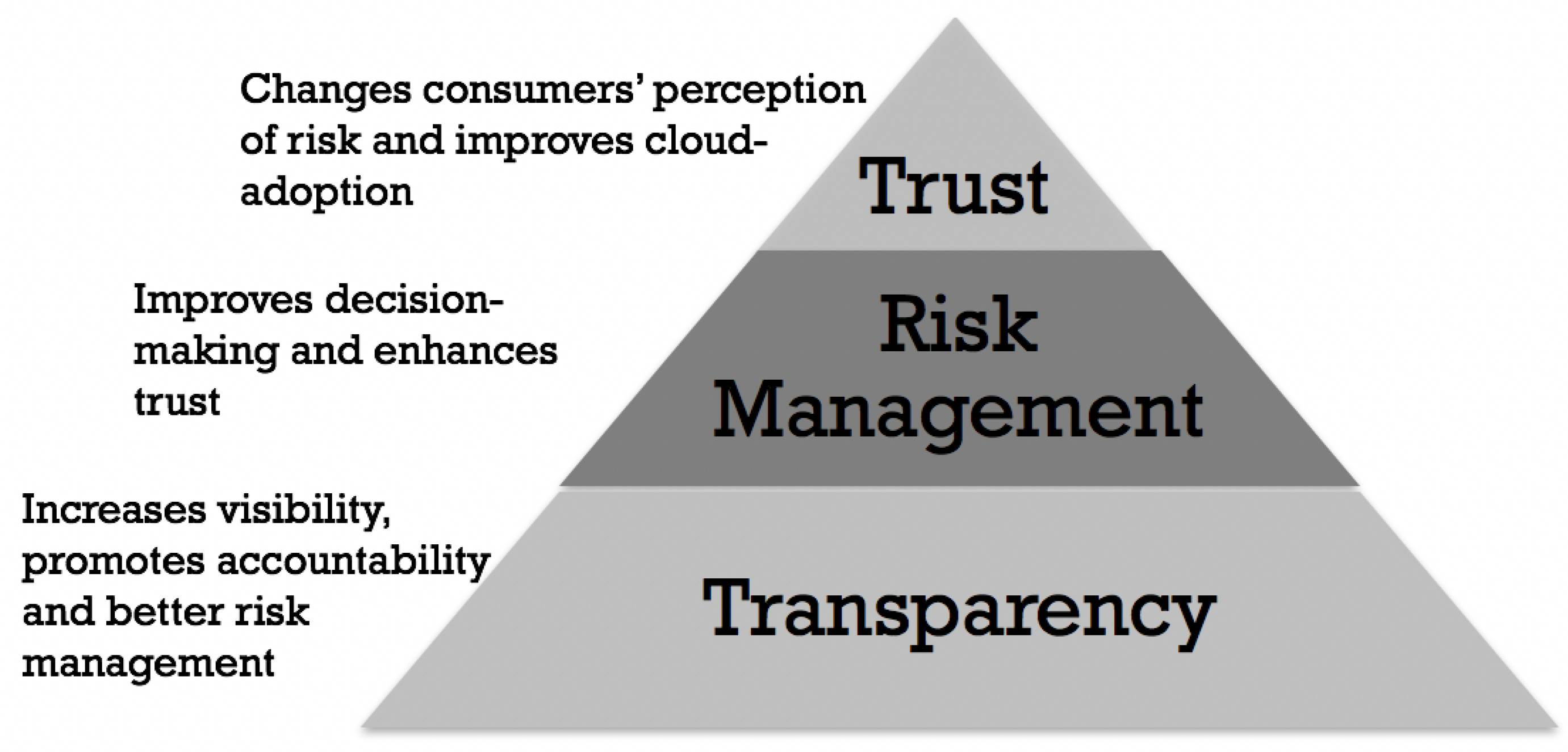
2.3. Transparency, Trust and Risk Assessment
2.4. Research Gap and Proposal
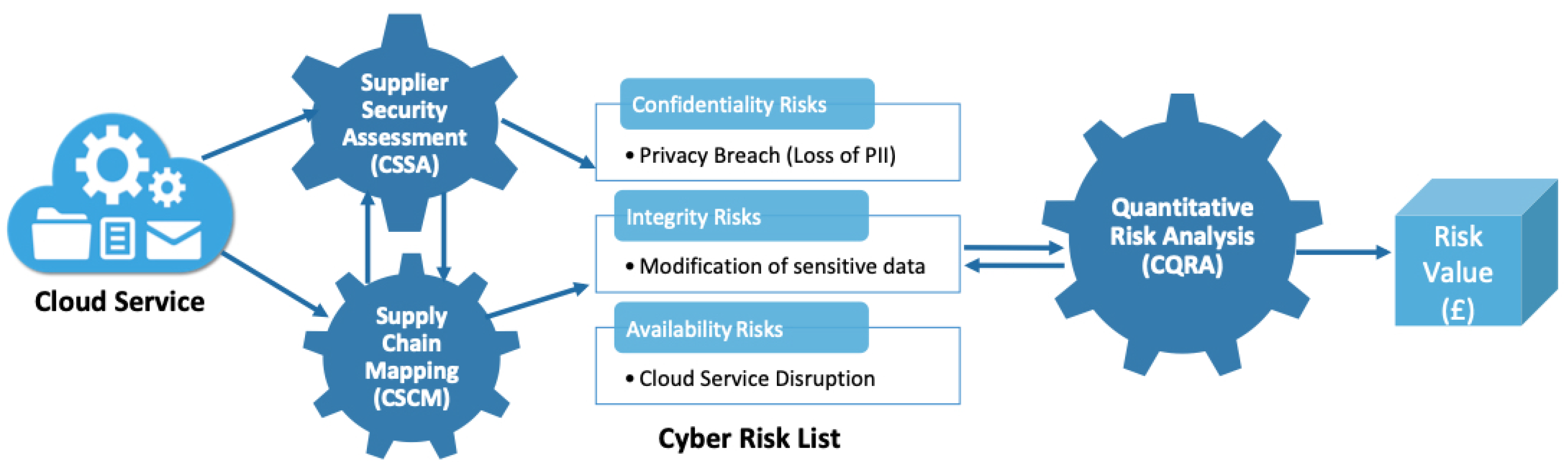
3. The CSCCRA Model
- Decompose the cloud application into its component services and map out the supply chain.
- Assess the security of the supplier of each service component using a multi-criteria decision support system.
- Identify the weak link(s) within the chain and compile a comprehensive list of cloud security risks.
- Enable stakeholders within the CSP to make reasonable estimates of risk values.
- Input risk values to the CSCCRA quantitative simulation tool to arrive at the risk value in monetary terms.
- Cloud Quantitative Risk Analysis (CQRA): The CSCCRA model goes beyond the IT industry norm to apply a quantitative assessment method to cloud risks for at least three reasons. First, the ability to express risk as the combination of the probability of an event and its consequences as per ISO Guide 73:2009 [57]. Second, the rigorous process involved in the identification of supply chain risk factors [23], and third, the use of controlled experimentation [19]. With uncertainty being the primary factor in risk analysis, the CSCCRA model makes use of a probabilistic estimate of risk factors, for example, threat frequency, vulnerability and loss magnitude, representing the forecast as a distribution (e.g., PERT, Poisson). To avoid cloud risk assessment being classed as mere speculation or opinion of risk assessors, and moving it into the realm of knowledge, based on informed opinion, making up for the lack of empirical evidence, the CQRA makes use of calibrated assessors, who can make reasonable estimates. The tool is implemented using the @RISK Monte Carlo Simulation Engine by Palisade [58], which is an add-in to Microsoft Excel.
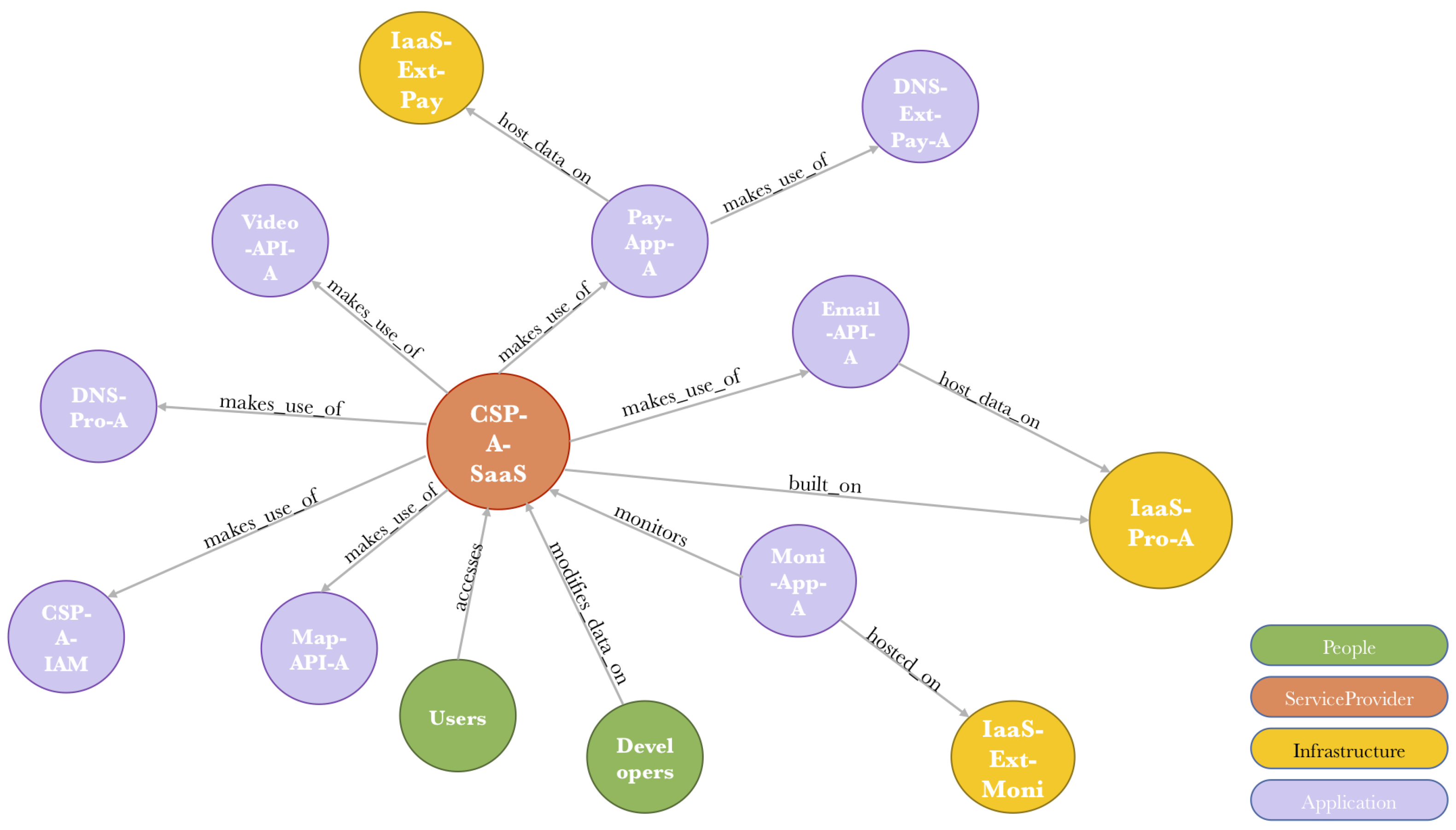
- Cloud Supplier Security Assessment (CSSA): The CSSA module of the CSCCRA, is a novel addition to cloud risk assessment, and functions as a Security Rating Service (SRS) for the suppliers involved in the delivery of the cloud service. The CSCCRA model requires cloud providers to be aware of their supply chain and have sufficient information about the processes and capabilities of their vendors. The CSSA addresses the notion of a distorted and incomplete process involved in cloud supplier selection. Being a Multi-criteria decision making (MCDM) tool, its use in cloud risk assessment ensures that decision made around cloud risks follows a formal and rigorous form. Furthermore, Gartner also encourages organisations to adopt SRS as part of their ongoing program for third-party cyber risk management [59]. The CSSA process involves decomposing the cloud service into its component objects and using an improper linear model, rating all entities based on identified security criteria. This process results in the identification of weak suppliers readily susceptible to a cyber attack or those with a high risk of failure. Ghadge et al. [53] supports this approach, arguing that the identification of potential weak spots in the supply chain through a dynamic model, captures its vulnerability and promote proactive mitigation of risks.
- Cloud Supply Chain Mapping (CSCM): Providing end-to-end supply chain visualisation while assessing cloud risk makes it amenable to analyse and explore areas of weakness, strengths and the potential risks to a cloud service while also supporting collaboration and decision-making within the chain [60]. Visualising the information flow of a cloud service through the supply chain assists in identifying critical suppliers and single points of failures (SPOFs) within the chain. The benefit of a graphical representation of the inherent risk in the supply chain helps to counter any documented biases in risk estimation and decision-making and is thought to have an impact in reducing the cognitive load involved in the estimation of risk factors [61]. The CSCCRA model employs supply chain mapping during the pre-assessment stage, to allow for continuous monitoring and visibility of the current state of cloud risk, and enable a data-driven risk identification and estimation; not one based on assessor’s instinct.
4. Sample Risk Assessment with CSCCRA
5. Completeness Comparison of the CSSCRA Model with Established Models and Standards
- Risk Identification: CSCCRA’s risk identification process follows a risk scenario approach, which accounts for the major risk factors that play a part in the risk event. It identifies the asset (cloud service), vulnerability, threat, impact, consequence, and existing controls. Its pre-assessment activity leads to risk identification and risk scenario development. This helps with identifying situations where an asset could be vulnerable without being threatened or threatened without being vulnerable, or where a vulnerable asset is not critical to the organisation.
- Risk Estimation: The CSCCRA is a quantitative risk assessment model that defines risk as a function of events, consequences, frequency, probability and their associated uncertainties. It uses the Monte Carlo simulation for the calculation of risk value, accounting for the expert’s uncertainty about their estimation and representing risk value as a probability distribution. The model incorporates a control efficiency assessment into the probability of risk event estimations, to provide stakeholders with the strength of their existing controls.
- Risk Evaluation: The final phase of the CSCCRA model is the risk evaluation, where the analysed risks are evaluated and prioritised according to their risk values. Also, during this phase, the risk assessor makes a recommendation to the CSP about the treatment of their top ten risks using security best practices as a guide. This provides the decision-makers with the information they need to prioritise and mitigate their risk according to the available resources.
6. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Ruparelia, N.B.; Ruparelia, N. Cloud Computing; MIT Press: Cambridge, MA, USA, 2016. [Google Scholar]
- Mell, P.; Grance, T. The NIST Definition of Cloud Computing Recommendations of the National Institute of Standards and Technology. Nist Spec. Publ. 2011, 145, 7. [Google Scholar] [CrossRef]
- Jansen, W.; Grance, T. Guidelines on Security and Privacy in Public Cloud Computing. Director 2011, 144. [Google Scholar] [CrossRef]
- Bleikertz, S.; Mastelić, T.; Pieters, W.; Pape, S.; Dimkov, T. Defining the Cloud Battlefield: Supporting Security Assessments by Cloud Customers. In Proceedings of the IEEE International Conference on Cloud Engineering (IC2E 2013), Redwood City, CA, USA, 25–27 March 2013; pp. 78–87. [Google Scholar] [CrossRef]
- Pearson, S. Data Protection in the Cloud. Cloud Secur. Alliance Online 2016, 10–13. [Google Scholar]
- Sherman, M. Risks in the Software Supply Chain. In Proceedings of the Software Solution Symposium, Alexandria, VA, USA, 20–23 March 2017; pp. 1–36. [Google Scholar]
- Cayirci, E.; Garaga, A.; De Oliveira, A.S.; Roudier, Y. A Cloud Adoption Risk Assessment Model. In Proceedings of the 2014 IEEE/ACM 7th International Conference on Utility and Cloud Computing, London, UK, 8–11 December 2014; pp. 908–913. [Google Scholar] [CrossRef]
- Islam, S.; Fenz, S.; Weippl, E.; Mouratidis, H. A Risk Management Framework for Cloud Migration Decision Support. J. Risk Financ. Manag. 2017, 10, 10. [Google Scholar] [CrossRef]
- Sendi, A.S.; Cheriet, M. Cloud Computing: A Risk Assessment Model. In Proceedings of the 2014 IEEE International Conference on Cloud Engineering, London, UK, 8–11 December 2014; pp. 147–152. [Google Scholar] [CrossRef]
- Sivasubramanian, Y.; Ahmed, S.Z.; Mishra, V.P. Risk Assessment for Cloud Computing. Int. Res. J. Electron. Comput. Eng. 2017, 3, 2412–4370. [Google Scholar] [CrossRef]
- SECCRIT. Secure Cloud Computing for Critical Infrastructure IT, “Methodology for Risk Assessment and Management”. 2014. Available online: https://cordis.europa.eu/project/rcn/106660/reporting/en (accessed on 8 September 2019).
- Theoharidou, M.; Tsalis, N.; Gritzalis, D. In Cloud We Trust: Risk-Assessment-as-a-Service. Trust Manag. VII 2013, 401, 100–110. [Google Scholar] [CrossRef]
- Drissi, S.; Benhadou, S.; Medromi, H. Evaluation of Risk Assessment Methods Regarding Cloud Computing. In Proceedings of the 5th Conference on Multidischiplinary Design Optimization and Applicaton, Shenzhen, China, 26–30 June 2016. [Google Scholar]
- Ellison, R.J.; Goodenough, J.B.; Weinstock, C.B.; Woody, C. Evaluating and Mitigating Software Supply Chain Security Risks; Technical Report; Carnegie-mellon University, Pittsburgh PA software Eng, Institute: Pittsburgh, PA, USA, 2010. [Google Scholar]
- Akinrolabu, O.; New, S.; Martin, A. CSCCRA: A Novel Quantitative Risk Assessment Model for Cloud Service Providers. In Proceedings of the European, Mediterranean, and Middle Eastern Conference on Information Systems, Limassol, Cyprus, 4–5 October 2018; pp. 177–184. [Google Scholar]
- ISO 27005. BS ISO/IEC 27005: 2011 BSI Standards Publication Information Technology—Security Techniques—Information Security Risk Management; ISO: Geneva, Switzerland, 2011. [Google Scholar]
- International Standards Organisation. ISO 31000—Risk Management; ISO: Geneva, Switzerland, 2009. [Google Scholar] [CrossRef]
- Ross, R.S. Guide for Conducting Risk Assessments; Special Publication (NIST SP)—800-30 Rev 1; NIST: Gaithersburg, MD, USA, 2012; p. 95. [CrossRef]
- Freund, J.; Jones, J. Measuring and Managing Information Risk; Butterworth-Heinemann: Oxford, UK, 2015; pp. 293–333. [Google Scholar] [CrossRef]
- Kaliski, B.S., Jr.; Pauley, W. Toward Risk Assessment as a Service in Cloud Environments. In Proceedings of the 2nd USENIX Conference on Hot Topics in Cloud Computing, Boston, MA, USA, 22–25 June 2010; pp. 1–7. [Google Scholar]
- Groubauer, B.; Walloschek, T.; StÖcker, E. Understanding Cloud Computing Vulnerabilities. Softw. Reuse Emerg. Cloud Comput. Era 2011, 204–227. [Google Scholar] [CrossRef]
- Vohradsky, D. Cloud Risk—10 Principles and a Framework for Assessment. ISACA J. 2012, 5, 1–11. [Google Scholar]
- Hubbard, D. The Failure of Risk Management: Why It’s Broken and How to Fix It; John Wiley & Sons: New York, NY, USA, 2009; pp. 134–143. [Google Scholar]
- Tang, H.; Yang, J.; Wang, X.; Zhou, Q. A Research for Cloud Computing Security Risk Assessment. Open Cybern. Syst. J. 2016, 10, 210–217. [Google Scholar] [CrossRef]
- Samani, R.; Honan, B.; Reavis, J. CSA Guide to Cloud Computing; Number November 1996; Elsevier, Inc.: Philadelphia, PA, USA, 2015; pp. 1–216. [Google Scholar] [CrossRef]
- Alturkistani, F.M.; Emam, A.Z. Alturkistani, F.M.; Emam, A.Z. A Review of Security Risk Assessment Methods in Cloud Computing. In New Perspectives in Information Systems and Technologies, Volume 1; Rocha, Á., Correia, A.M., Tan, F.B., Stroetmann, K.A., Eds.; Springer International Publishing: Cham, Switzerland, 2014; pp. 443–453. [Google Scholar] [CrossRef]
- Albakri, S.H.; Shanmugam, B.; Samy, G.N.; Idris, N.B.; Ahmed, A. Security risk assessment framework for cloud computing environments. Secur. Commun. Netw. 2014, 7, 2114–2124. [Google Scholar] [CrossRef]
- Djemame, K.; Armstrong, D.J.; Kiran, M. A Risk Assessment Framework and Software Toolkit for Cloud Service Ecosystems. In Proceedings of the Second International Conference on Cloud Computing, GRIDs, and Virtualization, Rome, Italy, 25–30 September 2011; pp. 119–126. [Google Scholar]
- Fito, J.; Macias, M.; Guitart, J. Toward Business-Driven Risk Management for Cloud Computing. In Proceedings of the 2010 International Conference on Network and Service Management, Niagara Falls, ON, Canada, 25–29 October 2010; pp. 238–241. [Google Scholar] [CrossRef]
- Liu, P.; Liu, D. The new risk assessment model for information system in Cloud Computing Environment. Procedia Eng. 2011, 15, 3200–3204. [Google Scholar] [CrossRef]
- Saripalli, P.; Walters, B. QUIRC: A Quantitative Impact and Risk Assessment Framework for Cloud Security. In Proceedings of the 2010 IEEE 3rd International Conference on Cloud Computing, Miami, FL, USA, 5–10 July 2010; pp. 280–288. [Google Scholar] [CrossRef]
- Zhang, L.J.; Zhang, J.; Fiaidhi, J.; Chang, J.M. Hot Topics in Cloud Computing. IT Prof. 2010, 12, 17–19. [Google Scholar] [CrossRef]
- Akinrolabu, O.; New, S.; Martin, A. Cyber Supply Chain Risks in Cloud Computing—Bridging the Risk Assessment Gap. Open J. Cloud Comput. 2018, 5, 1–19. [Google Scholar]
- Boyens, J.; Paulsen, C.; Moorthy, R.; Bartol, N. Supply Chain Risk Management Practices for Federal Information Systems and Organizations. NIST Spec. Publ. 2015. [Google Scholar] [CrossRef]
- Lindner, M.; Chapman, C.; Clayman, S.; Henriksson, D.; Elmorth, E. The Cloud Supply Chain: A Framework for Information, Monitoring, Accounting and Billing. In Proceedings of the 2nd International Conference on Cloud Computing, Barcelona, Spain, 25–28 October 2010. [Google Scholar]
- Jenks, M. Critical Infrastructure Protection Supply Chain Risk Management. 2016; pp. 1–6. Available online: https://www.ferc.gov/CalendarFiles/20160127144710-Jenks,%20KCPL.pdf (accessed on 17 July 2017).
- Motta, G.; You, L.; Sfondrini, N.; Sacco, D.; Ma, T. Service Level Management ( SLM ) in Cloud Computing Third party SLM framework. In Proceedings of the 2014 IEEE 23rd International WETICE Conference, Parma, Italy, 23–25 June 2014. [Google Scholar]
- Luna, J.; Suri, N.; Iorga, M.; Karmel, A. Leveraging the Potential of Cloud Security Service-Level Agreements through Standards. IEEE Cloud Comput. 2015, 2, 32–40. [Google Scholar] [CrossRef]
- Hofstede, G.J. Supply Chain Management; IGI Global: Hershey, PA, USA, 2007. [Google Scholar] [CrossRef]
- Conley, R. Three Levels of Trust—Where Do Your Relationships Stand? Blanchard LeaderChat on WordPress.com. 2012. Available online: https://leaderchat.org/2012/10/25/three-levels-of-trust-where-do-your-relationships-stand/ (accessed on 26 July 2017).
- Charney, S.; Werner, E.T. Cyber Supply Chain Risk Management: Toward a Global Vision of Transparency and Trust; Microsoft Corporation: Redmond, WA, USA, 2011; p. 19. [Google Scholar]
- New, S.; Brown, D. The Four Challenges of Supply Chain Transparency. Eur. Bus. Rev. 2012, 1–7. Available online: https://www.europeanbusinessreview.com/challenges-supply-chain-transparency/ (accessed on 24 July 2017).
- Pearson, S.; Labs, H.P. Towards Accountability in cloud.pdf. HP Labs Tech. Rep. 2011, 15, 64–69. [Google Scholar]
- Bruce Schneier. Should Companies Do Most of Their Computing in the Cloud? (Part 1)—Schneier on Security. 2015. Available online: https://www.schneier.com/blog/archives/2015/06/should_companie.html (accessed on 21 March 2017).
- Ismail, U.M.; Islam, S.; Ouedraogo, M.; Weippl, E. A framework for security transparency in Cloud Computing. Future Internet 2016, 8, 5. [Google Scholar] [CrossRef]
- Werff, L.V.D.; Lynn, T.; Xiaong, H. Building Trust in the Cloud Environment: Towards a Consumer Cloud Trust Label. In Proceedings of the Eighth International Conference on Digital Society (ICDS 2014), Barcelona, Spain, 23–27 March 2014. [Google Scholar]
- Sako, M. Price, Quality and Trust: Inter-Firm Relations in Britain and JAPAN; Number 18; Cambridge University Press: Cambridge, UK, 1992. [Google Scholar]
- Sung, S.; Kang, S. The Trust Levels, Trust Determinants, and Spatial Dimensions in Inter-Firm Relationships: A Warehousing Firm’s Perspective in the City of Busan, South Korea. iBusiness 2012, 4, 371. [Google Scholar] [CrossRef]
- Grzybowska, K.; Kovács, G.; Lénárt, B. The supply chain in cloud computing. Res. Logist. Prod. 2014, 4, 33–44. [Google Scholar]
- CPNI. Security for Industrial Control Systems—Manage Third Party Risks; CPNI: London, UK, 2015; Volume 1, pp. 1–16. [Google Scholar]
- Power. The risk management of everything. J. Risk Financ. 2004, 5, 58–65. [Google Scholar] [CrossRef]
- Ko, R.; Lee, S.; Rajan, V. Cloud Computing Vulnerability Incidents: A Statistical Overview; Cloud Security Alliance: Palo Alto, CA, USA, 2013; p. 21. [Google Scholar]
- Ghadge, A.; Dani, S.; Chester, M.; Kalawsky, R. A systems approach for modelling supply chain risks. Supply Chain Manag. Int. J. 2013, 18, 523–538. [Google Scholar] [CrossRef]
- Sterman, J.D. Business Dynamics: System Thinking and Modeling for a Complex World; MIT-Engineering Systems Division Working Paper Series; McGraw-Hill Education: Berkshire, UK, 2002; p. 982. [Google Scholar] [CrossRef]
- Hubbard, D.; SEIERSEN, R. How to Measure Anaything in Cybersecurity Risk; John Wiley & Sons: New York, NY, USA, 2016; pp. 1–247. [Google Scholar]
- Akinrolabu, O.; Nurse, J.R.; Martin, A.; New, S. Cyber risk assessment in cloud provider environments: Current models and future needs. Comput. Secur. 2019, 87, 101600. [Google Scholar] [CrossRef]
- Burtescu, E. Decision Assistance in Risk Assessment—Monte Carlo Simulations. Inform. Econ. 2012, 16, 86–93. [Google Scholar]
- Palisade. Monte Carlo Simulation: What Is It and How Does It Work? Palisade: New York, NY, USA, 2017. [Google Scholar]
- Olcott, J. Input to the Commission on Enhancing National Cybersecurity: The Impact of Security Ratings on National Cybersecurity. 2016. Available online: https://www.nist.gov/sites/default/files/documents/2016/09/15/bitsight_rfi_response.pdf (accessed on 20 March 2018).
- Sourcemap. Sub-Supplier Mapping: Tracing Products to the Source with a Supply Chain Social Network; Sourcemap: Lower Manhattan, NY, USA, 2011; p. 5. [Google Scholar]
- Gresh, D.; Deleris, L.A.; Gasparini, L.; Evans, D. Visualizing Risk. In Proceedings of the IEEE Information Visualization Conference, Las Vegas, NV, USA, 26–28 September 2011. [Google Scholar]
- Akinrolabu, O.; New, S.; Martin, A. Cloud Service Supplier Assessment: A Delphi Study. In Proceedings of the Eighth International Conference on Innovative Computing Technology (INTECH), Luton, UK, 15–17 August 2018; pp. 142–150. [Google Scholar]
- Hogan, R. Introduction to Statistics for Uncertainty Analysis. 2016. Available online: http://www.isobudgets.com/introduction-statistics-uncertainty-analysis/ (accessed on 26 September 2018).
- Miles, S.B. Participatory model assessment of earthquake-induced landslide hazard models. Nat. Hazards 2011, 56, 749–766. [Google Scholar] [CrossRef]
- Wangen, G.; Hallstensen, C.; Snekkenes, E. A framework for estimating information security risk assessment method completeness. Int. J. Inf. Secur. 2018, 17, 681–699. [Google Scholar] [CrossRef]
| Author/Year | Cloud Risk Assessment Description | Method | Implementation | Risk Value | Use of Experts | Supply Chain |
|---|---|---|---|---|---|---|
| (Albakri et al., 2014) [27] | They proposed a model that considers both the cloud customer and the CSP during its risk assessment process. | Qualitative | Yes | Risk Matrix | No | Yes |
| (Busby et al., 2014) [11] | SECCRIT is a risk assessment model developed to assist organisations in determining the risk associated with cloud adoption. | Qualitative | No | Risk Score | No | Yes |
| (Djemame et al., 2011) [28] | Risk assessment framework with methodologies for the identification, evaluation, mitigation & monitoring of cloud risks during the various stages of cloud provision. | Semi-quantitative | No | Risk Score | No | Yes |
| (Fito et al., 2010) [29] | A cloud risk assessment model for analysing the data security risks of confidential data. It prioritises cloud risks according to their impact on Business Level Objectives(BLO). | Semi-quantitative | Yes | Risk Score | No | No |
| (Liu & Liu, 2011) [30] | The model assesses cloud risks based on eight kinds of threats to security principles, and their corresponding factors. | Qualitative | No | Risk Score | Yes | No |
| (Saripalli & Walters, 2010) [31] | A quantitative risk and impact assessment of cloud risk events based on six key security objectives. | Semi-quantitative | No | Risk Score | Yes | No |
| (Sendi & Cheriet, 2014) [9] | The model uses fuzzy multi-criteria decision-making technique to assess cloud risks. Linguistic variables are used to obtain expert opinions for weighting security risk criteria. | Quantitative | Yes | Risk Score | No | No |
| (Sivasubramanian et al., 2017) [10] | The model measures cloud risks in terms of impact, occurrence and disclosure, to arrive at a Risk Priority Number (RPN). | Semi-quantitative | No | Risk Score | No | No |
| (Zhang et al., 2010) [32] | The framework was developed for a better understanding of critical areas in cloud computing environ- ments and the identification and mitigation of cloud risks. | Quali-tative | No | Risk Score | No | No |
| Anonymised Supplier | AoS | DSH | DSC | MSA | MOS | SGC | IAM | EKM | AS | Combined Z-Score Value |
|---|---|---|---|---|---|---|---|---|---|---|
| IaaS-Pr-A | 8 | 10 | 10 | 10 | 10 | 10 | 10 | 9 | 9 | −0.20 |
| CSP-A | 7 | 9 | 9 | 8 | 8 | 8 | 9 | 9 | 9 | 1.28 |
| Email-API-A | 10 | 9 | 10 | 10 | 9 | 9 | 10 | 10 | 9 | −0.17 |
| Video-API-A | 9 | 10 | 10 | 9 | 7 | 7 | 9 | 9 | 9 | 0.65 |
| Map-API-A | 9 | 10 | 9 | 10 | 8 | 10 | 10 | 10 | 9 | −0.07 |
| DNS-Pr-A | 10 | 10 | 10 | 10 | 10 | 10 | 9 | 10 | 10 | −0.71 |
| Moni-App-A | 10 | 10 | 10 | 9 | 10 | 10 | 10 | 10 | 9 | −0.46 |
| Pay-App-A | 8 | 10 | 10 | 10 | 9 | 10 | 10 | 10 | 9 | −0.31 |
| Parameter of Distribution | ||||
|---|---|---|---|---|
| Uncertain Inputs | Distri- bution | Lower Bound | Most Likely | Upper Bound |
| Probability of risk (without controls) (PWC) | PERT | 5% | 7% | 10% |
| Control Efficiency (CE) | PERT | 2% | 3% | 4% |
| Impact cost (IC) | PERT | £50,000 | £250,000 | £700,000 |
| Average Rate | ||||
| Frequency of occurrence per year (Fr) | Poisson | 1 | ||
| Estimated Risk Value (ERV) | Without Controls (ERV_WC) | With Controls (ERV_C) | ||
| 5% Percentile | £0 | £0 | ||
| Mean | £20,768.90 | £12,067.60 | ||
| 95% Percentile | £68,667.13 | £40,746.61 | ||
| Risk Identification | Score | Risk Estimation | Score | Risk Evaluation | Score |
|---|---|---|---|---|---|
| Preliminary assessment | XX | Asset identification and evaluation | XX | Risk criteria assessment /revision (RCA) | X |
| Risk criteria determination | XX | Threat willingness/ Motivation | X | Risk prioritisation/ Evaluation (RPE) | XX |
| Cloud-specific risk considerations | XX | Threat capability (know how) | X | Risk treatment recommendation (RTR) | XX |
| Business objective Identification | XX | Threat capacity (Resources) | - | ||
| Key risk indicators | XX | Threat attack duration | - | ||
| Stakeholder identification | XX | Vulnerability assessment | XX | ||
| Stakeholder analysis | XX | Control efficiency assessment | XX | ||
| Asset identification | XX | Subjective Probability Estimate for event | - | ||
| Mapping of personal data | X | Quantitative Probability Estimate for event | XX | ||
| Asset evaluation | XX | Subjective impact estimation | - | ||
| Asset owner and custodian | X | Quantitative impact estimation | XX | ||
| Asset container | XX | Privacy risk estimation | X | ||
| Business process identification | X | Utility and incentive calculation | XX | ||
| Vulnerability identification | XX | Cloud vendor assessment | - | ||
| Vulnerability assessment | X | Opportunity cost | XX | ||
| Threat identification | XX | Level of risk determination | X | ||
| Threat assessment | X | Risk aggregation | XX | ||
| Control identification | XX | Event, | XX | ||
| Control assessment | X | Consequence, | XX | ||
| Outcome identification | XX | Uncertainty, | XX | ||
| Outcome assessment | X | Probability, | XX | ||
| Asset, | XX | Model sensitivity, | XX | ||
| Vulnerability, | XX | Knowledge about risk | X | ||
| Threat, | XX | ||||
| Outcome | XX | ||||
| Completeness (Total) | 43/50 | 31/46 | 5/6 |
| CSCCRA | CRAMM | FAIR | OCTAVE Allegro | ISO 27005 | NIST 800-30 | RISK IT | Max Score | |
|---|---|---|---|---|---|---|---|---|
| Risk Identification | 43 | 29 | 26 | 32 | 38 | 24 | 29 | 50 |
| Risk Estimation | 31 | 10 | 30 | 14 | 27 | 26 | 22 | 46 |
| Risk Evaluation | 5 | 4 | 2 | 5 | 3 | 2 | 4 | 6 |
| Completeness Total | 79 | 43 | 58 | 51 | 68 | 52 | 55 | 102 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Akinrolabu, O.; New, S.; Martin, A. CSCCRA: A Novel Quantitative Risk Assessment Model for SaaS Cloud Service Providers. Computers 2019, 8, 66. https://doi.org/10.3390/computers8030066
Akinrolabu O, New S, Martin A. CSCCRA: A Novel Quantitative Risk Assessment Model for SaaS Cloud Service Providers. Computers. 2019; 8(3):66. https://doi.org/10.3390/computers8030066
Chicago/Turabian StyleAkinrolabu, Olusola, Steve New, and Andrew Martin. 2019. "CSCCRA: A Novel Quantitative Risk Assessment Model for SaaS Cloud Service Providers" Computers 8, no. 3: 66. https://doi.org/10.3390/computers8030066
APA StyleAkinrolabu, O., New, S., & Martin, A. (2019). CSCCRA: A Novel Quantitative Risk Assessment Model for SaaS Cloud Service Providers. Computers, 8(3), 66. https://doi.org/10.3390/computers8030066





