SQDPoS: A Secure and Practical Semi-Quantum Blockchain System for the Post-Quantum Era
Abstract
1. Introduction
- 1.
- A Semi-Quantum Delegated Proof of Stake (SQDPoS) consensus mechanism is proposed. We synergize the high throughput of DPoS with semi-quantum technology. Crucially, to mitigate the risks of node centralization and unfair elections inherent in traditional DPoS, we introduce a malicious behavior penalty model and the Borda count method. This integration not only ensures post-quantum security but also significantly improves the fairness of node elections and the robustness of the consensus committee.
- 2.
- An improved semi-quantum voting protocol adapted for decentralized elections is integrated. Building on the foundational semi-quantum voting principles proposed by Xu et al. [59], we significantly modified and optimized the scheme to meet the specific stringent requirements of a decentralized blockchain environment. By leveraging the entanglement characteristics of GHZ states and Semi-Quantum Secure Direct Communication (SQSDC), this adapted protocol ensures voter privacy and ballot tamper resistance while achieving high architectural compatibility with our newly designed node election mechanism.
- 3.
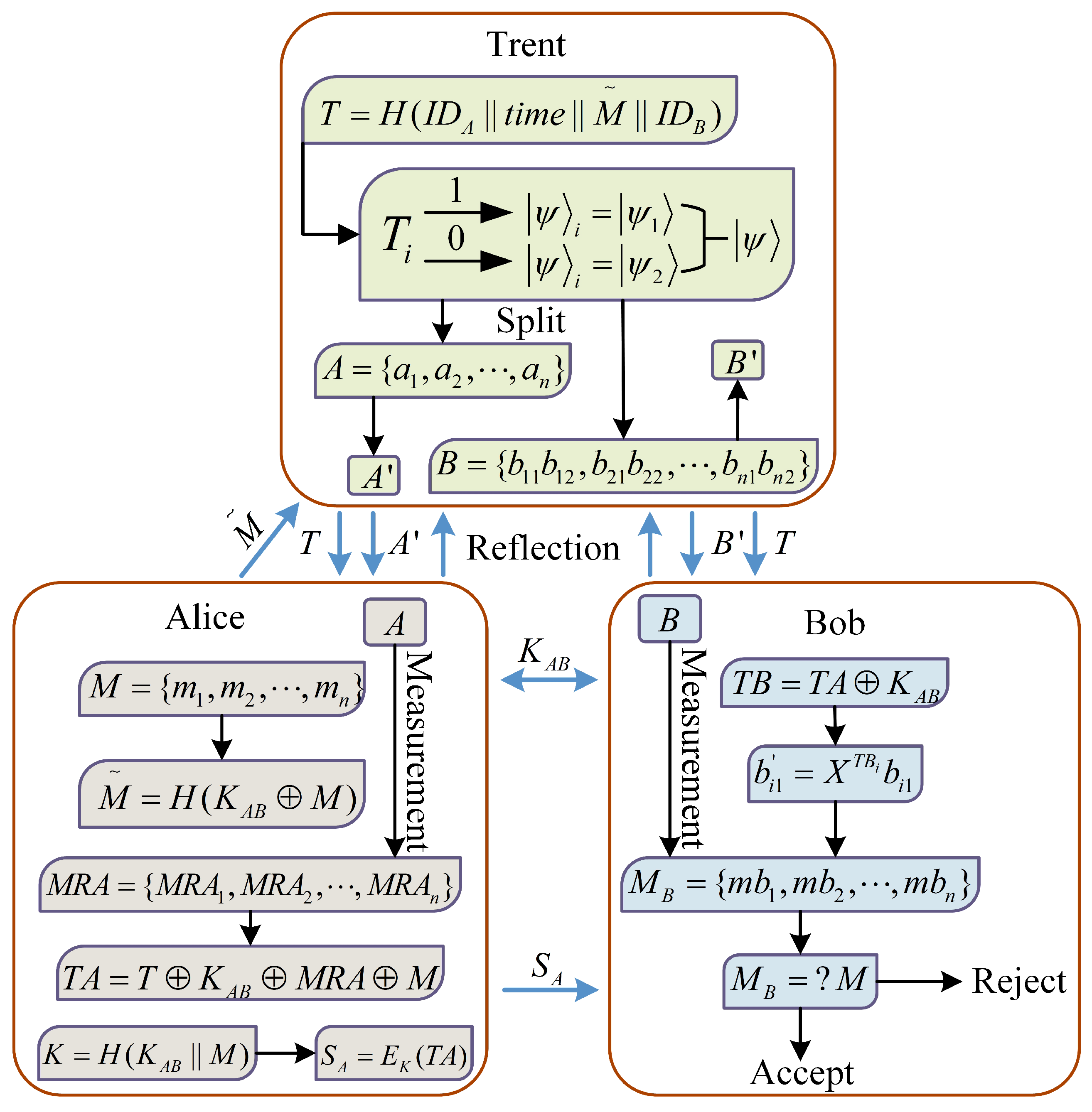
- A practical and lightweight semi-quantum transaction verification framework is designed. Adapted from the theoretical signature scheme of Zhang et al. [60], we built a comprehensive transaction verification process based on Semi-Quantum Key Distribution (SQKD) and One-Time Pad encryption. Our key architectural innovation lies in successfully bridging these cryptographic primitives with distributed ledger scenarios, explicitly allowing classical users with limited quantum capabilities (measure-and-reflect only) to perform unconditionally secure transaction signatures. This drastically reduces the hardware threshold and deployment cost for post-quantum blockchains.
2. Preliminaries
2.1. GHZ States
2.2. DPoS Consensus
- 1.
- Voting Election: Each token-holding node in the network possesses voting power proportional to its stake. Nodes can cast votes for one or more candidate nodes. The system tallies the votes in real-time, and the top N nodes with the highest votes (e.g., 21 in the EOS network) are elected as block producers (witnesses) for the current cycle.
- 2.
- Block Generation Scheduling: The elected witnesses are sorted randomly or in a fixed order and take turns packaging transactions and generating new blocks within strictly defined time slots. This deterministic scheduling mechanism significantly reduces the probability of conflicts among nodes competing for bookkeeping rights.
- 3.
- Verification and Confirmation: The generated blocks are broadcast to the entire network for verification by other witnesses and verification nodes. If a witness fails to produce a block within the stipulated time (e.g., due to being offline or network faults), their time slot is skipped, and such behavior is recorded.
3. Protocol Design
- User Nodes: These constitute the largest scale of basic nodes in the network, required only to possess restricted quantum capabilities such as measurement and reflection. Their primary responsibilities include maintaining local ledger copies, relaying network messages, and participating in voting. Although User Nodes do not possess block production rights, they determine the composition of the consensus committee through the voting mechanism, serving as the cornerstone of the system’s decentralized governance.
- Candidate Nodes: These are high-performance nodes equipped with full quantum computing and communication capabilities. Such nodes must satisfy specific stake (wealth) thresholds and complete identity registration. Once elected via user voting, they form the core consensus set. Subsequent block producer nodes and verification nodes are dynamically selected from this set.
- Block Producer Nodes: These are a minority of nodes elected from the candidate node set. Their core functions include collecting unconfirmed transactions across the network, executing preliminary verification of transaction legitimacy, packaging transactions to generate new blocks, and broadcasting them to the entire network.
- Verification Nodes: These consist of the remaining nodes in the candidate node set, excluding the block producer nodes. Their duties involve validating the effectiveness of new blocks, supervising the behavior of block producer nodes, and broadcasting confirmation signatures. They serve as the critical line of defense for guaranteeing the system’s Byzantine fault tolerance capability.
3.1. Consensus Process
3.1.1. Consensus Operation Workflow
- 1.
- Identity Authentication Phase: Upon a node’s entry into the blockchain network, the system initiates the identity authentication process. All nodes must complete registration via a classical identity authentication mechanism. Successfully registered nodes are categorized as either “User Nodes” or “Quantum Nodes” based on their computational capabilities and participation willingness. Specifically, Quantum Nodes enter a candidate state upon registration completion, awaiting voting support from User Nodes; conversely, nodes that fail to garner sufficient votes or lack quantum capabilities participate in network activities as User Nodes.
- 2.
- User Voting Phase: At the commencement of each consensus cycle, User Nodes cast votes for the system’s Quantum Nodes utilizing a semi-quantum voting mechanism. To mitigate Sybil attacks and increase the cost of malicious behavior, User Nodes are required to lock a certain amount of tokens as a stake before participating in voting. This process elects the set of candidate nodes for the current consensus round. The detailed protocol workflow for this stage is elaborated in Section 3.2.
- 3.
- Block Producer Selection Phase: Assume the system contains N User Nodes and K Quantum Nodes. In this phase, the system first filters out candidate nodes (where ) based on voting results, and subsequently selects the top m nodes from these candidates to serve as block producer nodes for the current round. To address potential malicious nodes hindering block production or manipulating elections, we introduce a malicious behavior penalty mechanism and the Borda count method (Borda Score) in this process to ensure the fairness and robustness of block producer selection.
- 4.
- Block Generation Phase: Block production is executed sequentially by the elected block producer nodes based on their Borda score ranking. Within the allocated time slot t, the current block producer node is responsible for collecting transaction information M occurring during this period, verifying its authenticity, and packaging legitimate transactions to generate a new block. Once the new block is constructed, the block producer broadcasts it to the set of verification nodes to initiate the verification phase. All block producer nodes perform block production tasks in a cyclic sequence until the end of the current consensus round, as shown in Figure 3. If a block producer node fails to complete block generation within the stipulated time window, its production opportunity is skipped, and the event is recorded in the historical malicious behavior log.
- 5.
- Block Verification Phase: Upon receiving a new block, verification nodes first validate whether the block producer possesses legitimate block production qualifications for the current consensus round. Following successful identity validation, verification nodes further scrutinize the integrity and consistency of the transactions within the block. When a new block garners confirmation signatures from no less than of the total verification nodes, the system determines that the block has passed consensus verification and achieved network-wide agreement.
- 6.
- Block Confirmation Phase: Once the new block passes verification, verification nodes broadcast the confirmation message to the entire network. Upon receiving the new block and its corresponding confirmation credentials, User Nodes formally append the block to their local blockchain ledger and subsequently proceed to participate in the next consensus round.
3.1.2. Block Election Algorithm
- (fp): Transaction packaging failure, with .
- (fv): Block verification failure, with .
- (bn): Node communication failure, with .
- (other): Other malicious behaviors, with .
3.1.3. Block Structure
3.2. Semi-Quantum Voting Process
3.2.1. Phase 1: Initialization
3.2.2. Phase 2: Eavesdropping Detection
3.2.3. Phase 3: Selection of the Ballot
3.2.4. Phase 4: Tallying Votes
3.2.5. Phase 5: Arbitration
3.3. Semi-Quantum Transaction Verification
3.3.1. Phase 1: Transaction Initialization
3.3.2. Phase 2: Eavesdropping Detection
3.3.3. Phase 3: Signature Generation
3.3.4. Phase 4: Signature Verification
4. Protocol Analysis
4.1. Security Analysis
4.1.1. Consensus Security
- 1.
- Fairness and Robustness of Node ElectionTraditional DPoS consensus is susceptible to node centralization issues. This scheme enhances the robustness of the consensus by introducing a multi-dimensional malicious behavior penalty mechanism and the Borda count method. The system defines a set of malicious behaviors, including transaction packaging failure, block verification failure, and communication fault, and assigns different penalty weights . The malicious behavior weight of a node, , is calculated via Equation (5), which in turn is used to dynamically adjust the node’s effective votes according to Equation (6). This mechanism ensures that nodes with a history of malicious behavior are unlikely to obtain high weights, effectively preventing malicious nodes from infiltrating the consensus committee. Distinct from the traditional rule, this scheme employs the Borda count method to construct a preference matrix. By synthesizing the ranking preferences of network-wide nodes for candidates, this method selects block producer nodes that better represent the overall consensus of the system, avoiding the monopoly of consensus rights by minority interest groups and enhancing the representativeness and fairness of the committee.
- 2.
- Cryptographic Security of Voting ProcessThe semi-Quantum voting protocol constitutes the core of the SQDPoS consensus, ensuring the security of votes throughout their lifecycle of generation, transmission, and tallying. This protocol satisfies the following key security properties:
- (1)
- Legitimacy: Only nodes holding the legitimate identity authentication key can participate in the consensus. In the initialization phase, the VMC uses SQKD protocols [67,68] to make the scrutineer Charlie and the voter Alice share the authentication key , which is unconditionally secure and ensures that the authentication key cannot be leaked, thereby only legitimate voters can vote. When voter Alice sends her vote to Charlie, the SQSDC channel is proved to be secure, and ensures that the voting sequence would not be disclosed [54,55,56]. At the time that voting center Bob and scrutineer Charlie communicate with the vote counter David respectively, the QSDC channels are proven to be secure [69,70]. All these quantum cryptographic protocols have been demonstrated to be unconditionally secure with mathematical rigor.
- (2)
- Anonymity: The protocol employs a blinding mechanism. Voter Alice utilizes her unique identity identifier and the quantum measurement result to perform an XOR operation on the ballot content M, generating a blinded ballot . The Counter, David, can only receive the blinded sequence and cannot associate the ballot content with a specific voter without authorization from the VMC for unblinding, thus guaranteeing the anonymity of the voting.
- (3)
- Non-repudiation: The ballot sequence is composed of a unique sequence number and the blinded ballot information P. A voter cannot deny the ballot because each voter’s and are unique. If a voter has an objection to the voting result, they can publish their sequence number for arbitration. If the ballot result is proven correct, the VMC will declare the arbitration failed; consequently, the voter cannot repudiate the voting result.
- (4)
- Unforgeability and Verifiability: The ballot sequence is strongly bound to the unique sequence number , which is generated by hashing . Any tampering with the ballot content (such as a Man-in-the-Middle attack) will lead to a hash verification failure. Furthermore, the arbitration mechanism allows the VMC to recover the original ballot content using the stored and compare it with the publicized result, ensuring the transparency and fairness of the counting process.
- 3.
- Resistance to Entangle–Measure AttackAttacker Eve attempts to intercept the quantum sequence during its transmission from the VMC to Voter Alice. Eve introduces an auxiliary probe state and applies a unitary operation on the traveling qubits in and her probe to steal information. Subsequently, she sends the manipulated sequence to Alice, hoping to deduce Alice’s measurement results () by measuring her probe .Assume that the initial GHZ state prepared by the VMC is . Eve performs a operation in her auxiliary state and the qubit of . According to Alice’s operations on the sequence, there are two cases.
- (1)
- Case 1: For the qubit which Alice chooses to measure.where , , and for .Once Alice measures it with basis, measurement will destroy entangled properties between it and the qubit at the corresponding position of , and it collapses to or . If , , then , . Next, Eve measures auxiliary state in her hand with basis and deduces based on measurement results.
- (2)
- Case 2: For the qubit which Alice dose reflection.After Eve applies , the entangled state evolves into:Alice does not perform any quantum operation on them, so they still retain their original entanglement relation. As long as Eve measures the auxiliary states in her hand with the basis , there will be a certain error rate.
For instance, assuming that the initial state is , if Eve measures the auxiliary state in her hand with the basis before Bob makes eavesdropping detection, Eve gets or with the probability of and gets or with the probability of , which cannot accurately judge whether the qubit belongs to the case 2. If Eve measures the auxiliary state after Bob adopts eavesdropping detection, then protocol passes the eavesdropping detection with a correct probability of and cannot pass the eavesdropping detection with an error probability of ; thus, the eavesdropping behavior will be detected. That is to say, there is a probability of to get the correct GHZ state and there is a probability of to get other GHZ states , or , and then Eve’s eavesdropping behavior can be discovered by Bob.In addition, as Eve cannot get the key , she cannot know the position of the quantum bits in case 1 and 2 and cannot distinguish the qubits in case 1 and 2, thus she cannot get the information related to . - 4.
- Resistance to Intercept–Resend AttackAssume attacker Eve intercepts the operated sequence (or ) and resends a forged sequence to the VMC. In the protocol, the legitimate users apply reflection or measurement based on the secret updated authentication key . Because Eve lacks , she cannot distinguish which operation is. Any attempt to measure the intercepted sequence to forge a replacement will inevitably destroy the initial multi-partite GHZ entanglement correlations. During the VMC’s joint GHZ state measurement in the eavesdropping detection phase, this disruption will manifest as a detectable error. If Eve attempts to evade detection by blindly guessing to deduce the exact operational positions, she introduces an expected error rate of , where represents the number of relevant qubits. As the sequence length , this error rate asymptotically approaches 1. Therefore, Eve’s intercept–resend attack will be definitively detected, ensuring the protocol’s robust information-theoretic security.
4.1.2. Transaction Security
- 1.
- Key Confidentiality and Signature SecurityThe security of the transaction system relies primarily on the confidentiality of the secret key and the signature S. At the beginning of the protocol, the signer Alice and the verifier Bob establish a shared private key via the Semi-Quantum Key Distribution (SQKD) protocol. Existing research has proven that the SQKD protocol possesses security equivalent to that of fully quantum QKD protocols, capable of resisting key theft by attackers with infinite computing resources. During the signature generation phase, Alice employs the One-Time Pad algorithm to generate the ciphertext . According to Shannon’s information theory, this encryption is unconditionally secure when the key is random and used only once. The encryption key is generated by a one-way hash function. Since an attacker, Eve, cannot reverse the hash function and does not possess , she cannot crack K to access the signature content. Even if the third party Trent intercepts the intermediate information , due to the lack of , the probability of him successfully guessing the key is only (where n is the key length), which is negligible when n is sufficiently large.
- 2.
- Unforgeability and Non-repudiation of TransactionsUnforgeability is the core for ensuring the safety of blockchain assets. In this scheme, generating a legitimate signature S requires both the shared private key and the quantum measurement result . An external attacker, Eve, possesses neither nor access to Alice’s local quantum measurement values ; thus, she cannot construct a valid signature that satisfies the verification equation . Furthermore, although Trent participates in the preparation of quantum states, he is defined as a semi-trusted party. Since Trent cannot access and cannot predict Alice’s random measurement results for the particle sequence A, he is computationally incapable of forging a legitimate transaction signature, thereby eliminating the risk of malicious behavior by a centralized authority. If a dispute arises between the transacting parties (e.g., Alice denies sending a transaction or Bob denies receiving it), Trent can perform arbitration using the immutable timestamp and hash value .
- 3.
- Resistance to Quantum Channel AttacksAddressing potential eavesdropping threats during quantum communication, this scheme introduces a decoy state detection mechanism in the particle transmission phase (Steps 6–9). Assume that Eve intercepts the quantum sequence and performs measurement attacks on the quantum sequence with the operation and the auxiliary particle . Then Eve’s attack system can be described as:where , which are determined by the normalized vector. If Eve wishes his attacks to be undetected, i.e., the measurement result of is with probability 1, Eve may set . For the measurement of to be , Eve can set . Thus, for , Eve’s attack system can be described as:when , for , Eve’s attack system can be described as:Therefore, Eve’s entanglement measurement attacks will trigger the decoy particles to change their initial states. In the subsequent detection step, Trent announces the positions and preparation bases of the decoy particles, and the communicating parties compare the measurement results to calculate the error rate. Eve’s attack behavior will significantly increase the bit error rate or phase error rate of the channel. Once the error rate exceeds a preset threshold, the protocol is immediately terminated. Therefore, any form of intercept–resend or entangle–measure attack will be detected by the system in real-time, safeguarding the security of the transaction signature.
4.2. Performance Analysis
4.2.1. Consensus Efficiency
4.2.2. Transaction Efficiency
4.3. Comparative Analysis
- User Capacity and Quantum Resource Cost: Categorized strictly by the physical hardware requirements required for a node. Semi-quantum requires only fundamental optical operations, whereas Full Quantum schemes demand expensive, state-of-the-art setups like quantum memory or continuous entanglement maintenance.
- Consensus Mechanism and Chain Structure: Defines the core algorithmic foundation used to achieve network agreement and the architectural nature of the distributed ledger.
- Security: Assesses the protocol’s cryptographic resilience to withstand attacks from quantum computers and its inherent capability to guaranty that a sender cannot deny the authenticity of their submitted transactions.
- Communication Complexity: Defined as the asymptotic number of message exchanges required among participating nodes to reach consensus on a single block, where N denotes the total network size, and m denotes the size of the elected proxy committee.
- Consensus Time Complexity: Evaluated by the asymptotic number of sequential time rounds or communication phases necessary to finalize a block generation process.
- Byzantine Fault Tolerance: Assessed by the architectural capacity of the consensus protocol to maintain ledger consistency and liveness in the presence of malicious or arbitrarily faulty nodes.
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 15 March 2026).
- King, S.; Nadal, S. PPCoin: Peer-to-peer crypto-currency with proof-of-stake. Self-Publ. Pap. 2012, 19, 1–6. [Google Scholar]
- Larimer, D. Delegated Proof-of-Stake (DPoS). Technical Report. Bitshare Whitepaper. Open J. Appl. Sci. 2014, 11. [Google Scholar]
- Sukhwani, H.; Martínez, J.M.; Chang, X.; Trivedi, K.S.; Rindos, A. Performance modeling of PBFT consensus process for permissioned blockchain network (Hyperledger Fabric). In Proceedings of the IEEE 36th Symposium on Reliable Distributed Systems (SRDS); IEEE: New York, NY, USA, 2017; pp. 253–255. [Google Scholar]
- Shor, P.W. Algorithms for quantum computation: Discrete logarithms and factoring. In Proceedings of the 35th Annual Symposium on Foundations of Computer Science (FOCS); IEEE Computer Society: Washington, DC, USA, 1994; pp. 124–134. [Google Scholar]
- Rivest, R.L.; Shamir, A.; Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 1978, 26, 96–99. [Google Scholar] [CrossRef]
- Miller, V.S. Use of elliptic curves in cryptography. In Proceedings of the Advances in Cryptology—CRYPTO ’85 Proceedings, Santa Barbara, CA, USA, 18–22 August 1985; Volume 218, pp. 417–426. [Google Scholar]
- Koblitz, N. Elliptic curve cryptosystems. Math. Comput. 1987, 48, 203–209. [Google Scholar] [CrossRef]
- Grover, L.K. A fast quantum mechanical algorithm for estimating the median. In Proceedings of the 28th Annual ACM Symposium on Theory of Computing (STOC), Philadelphia, PA, USA, 22–24 May 1996; pp. 212–219. [Google Scholar]
- Grover, L.K. Quantum mechanics helps in searching for a needle in a haystack. Phys. Rev. Lett. 1997, 79, 325. [Google Scholar] [CrossRef]
- Fedorov, A.K.; Kiktenko, E.O.; Lvovsky, A.I. Quantum computers put blockchain security at risk. Nature 2018, 563, 465–467. [Google Scholar] [CrossRef]
- Chaudhary, D.; Durgarao, M.S.P.; Mishra, D.; Kumari, S. A module lattice based construction of post quantum secure blockchain architecture. Trans. Emerg. Telecommun. Technol. 2024, 35, e4855. [Google Scholar] [CrossRef]
- Arfaoui, S.; El-Gayar, O. Systematic review of lattice-based cryptography algorithms for securing blockchain networks in the post-quantum era. Issues Inf. Syst. 2025, 26, 443–461. [Google Scholar]
- Cao, B.Y.; Gao, J.; Lian, L. Lattice-Based Regulatory Privacy Protection Scheme on Blockchain. J. Cryptologic Res. 2025, 12, 69–83. [Google Scholar]
- Long, C. Anti-quantum blockchain data encryption method based on lattice signature algorithm. Inf. Technol. Inform. 2024, 74–77. [Google Scholar] [CrossRef]
- Xi, G. Research on Post-Quantum Blockchain Privacy Protection Based on Lattice Cryptography. Ph.D. Thesis, Beijing University of Posts and Telecommunications, Beijing, China, 2025. [Google Scholar]
- Yi, H. A post-quantum blockchain notary scheme for cross-blockchain exchange. Comput. Electr. Eng. 2023, 110, 108832. [Google Scholar] [CrossRef]
- Parameswari, S.; Latha, B. ChainFort: Hybrid Blockchain-Orchestrated Firmware Validation and Secure Update Delivery Using PQC and Federated Trust Consensus. In Proceedings of the 2025 IEEE Pune Section International Conference (PuneCon); IEEE: New York, NY, USA, 2025; pp. 1–6. [Google Scholar] [CrossRef]
- Goh, K.W.; Khan, B.U.I.; Khan, A.R.; Putra, D.S.; Fathimathul Rajeena, P.P.; Bhuyian, A. Eliminating single points of trust: A hybrid quantum and post-quantum blockchain with distributed key generation. Sci. Rep. 2025, 16, 1286. [Google Scholar] [CrossRef] [PubMed]
- Wang, Y.; Jia, S.; Chen, M.; Dong, Y.; Yang, Y. Post-Quantum Blockchain System Based on Multi-Parent Chain Assisted Proof-of-Work Consensus Mechanism. J. Softw. 2025, 36, 4507–4524. [Google Scholar] [CrossRef]
- Chen, J.; Gan, W.; Hu, M.; Chen, C.M. On the construction of a post-quantum blockchain for smart city. J. Inf. Secur. Appl. 2021, 58, 102780. [Google Scholar] [CrossRef]
- Hu, X.; Xiang, H.; Ding, J.; Liang, B.; Xia, L.; Xiang, T. Public key cryptography security for blockchain under the trend of post-quantum cryptography migration. J. Cryptologic Res. 2023, 10, 219–245. [Google Scholar]
- Bayramova, T.; Mammadov, R. Transition to Post-Quantum Cryptographic Algorithms in Critical Software: Challenges and Strategies. Found. Trends Res. 2026. [Google Scholar]
- Ullah, M.; Ali, A.; Jadoon, A.K. Quantum Computing and Blockchain Security: A Critical Assessment of Cryptographic Vulnerabilities and Post-Quantum Migration Strategies; MPRA Paper 127528; University Library of Munich: Munich, Germany, 2025. [Google Scholar]
- Gisin, N.; Ribordy, G.; Tittel, W.; Zbinden, H. Quantum cryptography. Rev. Mod. Phys. 2001, 74, 145–195. [Google Scholar] [CrossRef]
- Yin, J.; Li, Y.; Liao, S.; Yang, M.; Cao, Y.; Zhang, L.; Ren, J.; Cai, W.; Liu, W.; Li, S.; et al. Entanglement-based secure quantum cryptography over 1120 kilometres. Nature 2020, 582, 501–505. [Google Scholar] [CrossRef]
- Busch, P.; Heinonen, T.; Lahti, P. Heisenberg’s uncertainty principle. Phys. Rep. 2007, 452, 155–176. [Google Scholar] [CrossRef]
- Bennett, C.H.; Brassard, G. An Update on Quantum Cryptography. In Proceedings of the Advances in Cryptology—CRYPTO ’84, Santa Barbara, CA, USA, 19–22 August 1984; pp. 475–480. [Google Scholar]
- Grosshans, F.; Van Assche, G.; Wenger, J.; Brouri, R.; Cerf, N.J.; Grangier, P. Quantum key distribution using gaussian-modulated coherent states. Nature 2003, 421, 238. [Google Scholar] [CrossRef]
- Deng, F.G.; Long, G.L. Bidirectional quantum key distribution protocol with practical faint laser pulses. Phys. Rev. A 2004, 70, 012311. [Google Scholar] [CrossRef]
- Lucamarini, M.; Yuan, Z.L.; Dynes, J.F.; Shields, A.J. Overcoming the rate–distance limit of quantum key distribution without quantum repeaters. Nature 2018, 557, 400. [Google Scholar] [CrossRef]
- Wang, C.; Deng, F.G.; Li, Y.S.; Liu, X.S.; Long, G.L. Quantum secure direct communication with high-dimension quantum superdense coding. Phys. Rev. A 2005, 71, 044305. [Google Scholar] [CrossRef]
- Qin, H.; Tang, W.K.S.; Tso, R. Establishing rational networking using the DL04 quantum secure direct communication protocol. Quantum Inf. Process. 2018, 17, 152. [Google Scholar] [CrossRef]
- Hillery, M.; Bužek, V.; Berthiaume, A. Quantum secret sharing. Phys. Rev. A 1999, 59, 1829. [Google Scholar] [CrossRef]
- Xiao, L.; Long, G.L.; Deng, F.G.; Pan, J.W. Efficient multiparty quantum-secret-sharing schemes. Phys. Rev. A 2004, 69, 052307. [Google Scholar] [CrossRef]
- Liu, F.; Qin, S.J.; Su, Q. An arbitrated quantum signature scheme with fast signing and verifying. Quantum Inf. Process. 2014, 13, 491–502. [Google Scholar] [CrossRef]
- Jogenfors, J. Quantum bitcoin: An anonymous and distributed currency secured by the no-cloning theorem of quantum mechanics. arXiv 2016, arXiv:1604.01383. [Google Scholar] [CrossRef]
- Fedorov, A.K.; Kiktenko, E.O.; Lvovsky, A.I. Quantum-secured blockchain. Quantum Sci. Technol. 2018, 3, 035004. [Google Scholar] [CrossRef]
- Rajan, D.; Visser, M. Quantum blockchain using entanglement in time. Quantum Rep. 2019, 1, 3–11. [Google Scholar] [CrossRef]
- Sun, X.; Sopek, M.; Wang, Q.; Kulicki, P. Towards quantum-secured permissioned blockchain: Signature, consensus, and logic. Entropy 2019, 21, 887. [Google Scholar] [CrossRef]
- Banerjee, S.; Mukherjee, A.; Panigrahi, P.K. Quantum blockchain using weighted hypergraph states. Phys. Rev. Res. 2020, 2, 013322. [Google Scholar] [CrossRef]
- Wen, X.J.; Chen, Y.Z.; Fan, X.C.; Yi, Z.-Z.; Jiang, Z.L.; Fang, J.-B. Quantum blockchain system. Mod. Phys. Lett. B 2021, 35, 2150343. [Google Scholar] [CrossRef]
- Li, Q.; Wu, J.; Quan, J.; Shi, J.; Zhang, S. Efficient quantum blockchain with a consensus mechanism QDPoS. IEEE Trans. Inf. Forensics Secur. 2022, 17, 3264–3276. [Google Scholar] [CrossRef]
- Wang, W.; Yu, Y.; Du, L. Quantum blockchain based on asymmetric quantum encryption and a stake vote consensus algorithm. Sci. Rep. 2022, 12, 8606. [Google Scholar] [CrossRef]
- Weng, C.X.; Gao, R.Q.; Bao, Y.; Li, B.H.; Liu, W.B.; Xie, Y.M.; Lu, Y.S.; Yin, H.L.; Chen, Z.B. Beating the Fault-Tolerance Bound and Security Loopholes for Byzantine Agreement with a Quantum Solution. Research 2023, 6, 0272. [Google Scholar] [CrossRef]
- Liu, A.; Chen, X.B.; Xu, G.; Wang, Z.; Feng, X.; Feng, H. Quantum-enhanced blockchain: A secure and practical blockchain scheme. Comput. Mater. Contin. 2023, 76, 259–277. [Google Scholar] [CrossRef]
- Sun, Z.Z.; Cheng, Y.-B.; Wang, M.; Qian, L.; Ruan, D.; Pan, D.; Long, G.-L. Quantum blockchain relying on quantum secure direct communication network. IEEE Internet Things J. 2025, 12, 1. [Google Scholar] [CrossRef]
- Boyer, M.; Kenigsberg, D.; Mor, T. Quantum key distribution with classical Bob. Phys. Rev. Lett. 2007, 99, 140501. [Google Scholar] [CrossRef]
- Li, Q.; Chan, W.H.; Long, D.Y. Semi-quantum secret sharing using entangled states. Phys. Rev. A 2010, 82, 2422–2427. [Google Scholar] [CrossRef]
- Wang, J.; Zhang, S.; Zhang, Q.; Tang, C.J. Semi-quantum secret sharing using two-particle entangled state. Int. J. Quantum Inf. 2012, 10, 1250050. [Google Scholar] [CrossRef]
- Li, J.; Xiong, J.; Wang, X. Multiparty semi-quantum key agreement protocol without participant measurement. Phys. Scr. 2025, 100, 095122. [Google Scholar] [CrossRef]
- Li, J.; Jiang, S.; Hu, W. Semi-quantum key agreement protocol based on four-particle entangled χ-state and experiment verification on IBM qiskit. Quantum Inf. Process. 2025, 24, 274. [Google Scholar] [CrossRef]
- Hong, W.-L.; Bai, C.-M.; Zhang, S.-J.; Liu, L. Multiparty semi-quantum key agreement protocol based on multiparticle entangled states. Laser Phys. Lett. 2024, 21, 125212. [Google Scholar] [CrossRef]
- Zhang, X.X.; Zhou, R.G.; Xu, W.S. Robust semi-quantum secure direct communication based on multi-particle system. Quantum Inf. Process. 2025, 24, 169. [Google Scholar] [CrossRef]
- Zhang, X.; Zhou, R.; Xu, W. Measurement-Device-Independent Semi-quantum Secure Direct Communication. J. Electron. 2026, 35, 233–242. [Google Scholar]
- Tian, Y.; Zhang, N.; Li, J. Two Novel Semi-Quantum Secure Direct Communication Protocols in IoT. Sensors 2024, 24, 7990. [Google Scholar] [CrossRef]
- Zhou, N.R.; Zhu, K.N.; Bi, W.; Gong, L.-H. Semi-quantum identification. Quantum Inf. Process. 2019, 18, 197. [Google Scholar] [CrossRef]
- Jiang, S.Q.; Zhou, R.G.; Hu, W.W. Semi-quantum mutual identity authentication using Bell states. Int. J. Theor. Phys. 2021, 60, 3353–3362. [Google Scholar] [CrossRef]
- Xu, Y.P.; Gao, D.Z.; Liang, X.Q.; Xu, G.-B. Semi-Quantum Voting Protocol. Int. J. Theor. Phys. 2022, 61, 78. [Google Scholar] [CrossRef]
- Zhang, L.; Zhang, J.H.; Xin, X.J.; Huang, M.; Li, C. Semi-quantum Designated Verifier Signature Scheme. Int. J. Theor. Phys. 2023, 62, 254. [Google Scholar] [CrossRef]
- Greenberger, D.M.; Horne, M.A.; Zeilinger, A. Going beyond Bell’s theorem. In Bell’s Theorem, Quantum Theory and Conceptions of the Universe; Kafatos, M., Ed.; Kluwer Academic: Dordrecht, The Netherlands, 1989; pp. 69–72. [Google Scholar]
- Pan, J.W.; Bouwmeester, D.; Daniell, M.; Weinfurter, H.; Zeilinger, A. Experimental test of quantum nonlocality in three-photon Greenberger–Horne–Zeilinger entanglement. Nature 2000, 403, 515–519. [Google Scholar] [CrossRef] [PubMed]
- Zeng, G.; Keitel, C.H. Arbitrated quantum-signature scheme. Phys. Rev. A 2002, 65, 042312. [Google Scholar] [CrossRef]
- Jing, J.; Zhang, S.; Wang, P. Threshold Cryptography and Its Standardization Progress. J. Cryptologic Res. 2024, 11, 227–254. [Google Scholar] [CrossRef]
- Sun, Z.; Chen, H.; Cai, X. Quantum deterministic key distribution protocol based on GHZ states entanglement swapping. Chin. J. Quantum Electron. 2015, 32, 83–89. [Google Scholar]
- Xu, Y.; Li, Z.; Liu, T.; Zhu, H. Multi-Party Quantum Secret Sharing Protocol Based on GHZ States Entanglement Swapping. Int. J. Theor. Phys. 2022, 61, 76. [Google Scholar] [CrossRef]
- Hajji, H.; El Baz, M.; Krawec, W.O. Optimal eavesdropping in semi-quantum key distribution. Phys. Lett. A 2026, 567, 131174. [Google Scholar] [CrossRef]
- Chen, C.T.; Lee, C.C. A secure authenticated semi-quantum key distribution scheme for semi-quantum environments. Quantum Inf. Process. 2024, 23, 409. [Google Scholar] [CrossRef]
- Ying, J.; Wang, J.; Xiao, Y.; Gu, S.-P.; Wang, X.-F.; Zhong, W.; Du, M.-M.; Li, X.-Y.; Shen, S.-T.; Zhang, A.-L.; et al. Passive-state preparation for quantum secure direct communication. Sci. China Phys. Mech. Astron. 2025, 68, 240312. [Google Scholar] [CrossRef]
- Cao, Z.; Lu, Y.; Chai, G.; Yu, H.; Liang, K.; Wang, L. Realization of Quantum Secure Direct Communication with Continuous Variable. Research 2024, 6, 159–170. [Google Scholar] [CrossRef]
- Zhao, X.; Chen, T. A Novel Semi-Quantum Co-Signature Scheme Based on GHZ States and Four-Particle Cluster States. Int. J. Theor. Phys. 2023, 62, 78. [Google Scholar] [CrossRef]
- Chen, L.Y.; Liao, Q.; Tan, R.C.; Gong, L.H.; Chen, H.Y. Offline arbitrated semi-quantum signature scheme with four-particle cluster state. Int. J. Theor. Phys. 2020, 59, 3685–3695. [Google Scholar] [CrossRef]
- Zheng, T.; Chang, Y.; Yan, L.; Zhang, S.B. Semi-quantum proxy signature scheme with quantum walk-based teleportation. Int. J. Theor. Phys. 2020, 59, 3145–3155. [Google Scholar] [CrossRef]
- Xia, C.; Li, H.; Hu, J. Semi-quantum digital signature protocol based on Einstein–Podolsky–Rosen steering. J. Phys. A Math. Theor. 2022, 55, 325302. [Google Scholar] [CrossRef]
- Gao, Y.L.; Chen, X.B.; Xu, G.; Yuan, K.; Liu, W.; Yang, Y. A novel quantum blockchain scheme base on quantum entanglement and DPoS. Quantum Inf. Process. 2020, 19, 420. [Google Scholar] [CrossRef]







| Bob’ Operation | |||||
|---|---|---|---|---|---|
| 0 | 0 | 0 | |||
| 1 | X | ||||
| 0 | 1 | 0 | X | ||
| 1 | |||||
| 1 | 0 | 0 | X | ||
| 1 | |||||
| 1 | 1 | 0 | |||
| 1 | X |
| Comparison Metric | Ours | Kiktenko et al. [38] | Gao et al. [75] | Li et al. [43] |
|---|---|---|---|---|
| User Capability | Semi-Quantum | Full Quantum | Full Quantum | Full Quantum |
| Consensus Mechanism | SQDPoS | BFT | Quantum DPoS | QDPoS |
| Chain Structure | Classical Chain | QKD Encrypted Comm | GHZ Entanglement | Quantum State Entanglement |
| Non-repudiation | Yes | No | Yes | Yes |
| Comm Complexity | ||||
| Byzantine Fault Tolerance | Yes | Yes | Yes | Yes |
| Resist Computing Attacks | Yes | No | Yes | Yes |
| Quantum Resource Cost | Semi-quantum | QKD | Quantum Memory | Entanglement Maintenance |
| Consensus Time Complexity |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Liu, A.; An, Q.; Xie, S.; Yan, Y. SQDPoS: A Secure and Practical Semi-Quantum Blockchain System for the Post-Quantum Era. Computers 2026, 15, 210. https://doi.org/10.3390/computers15040210
Liu A, An Q, Xie S, Yan Y. SQDPoS: A Secure and Practical Semi-Quantum Blockchain System for the Post-Quantum Era. Computers. 2026; 15(4):210. https://doi.org/10.3390/computers15040210
Chicago/Turabian StyleLiu, Ang, Qi An, Sijiang Xie, and Yalong Yan. 2026. "SQDPoS: A Secure and Practical Semi-Quantum Blockchain System for the Post-Quantum Era" Computers 15, no. 4: 210. https://doi.org/10.3390/computers15040210
APA StyleLiu, A., An, Q., Xie, S., & Yan, Y. (2026). SQDPoS: A Secure and Practical Semi-Quantum Blockchain System for the Post-Quantum Era. Computers, 15(4), 210. https://doi.org/10.3390/computers15040210







