IoT Security Mechanisms in the Example of BLE
Abstract
:1. Introduction
2. Wireless Network Vulnerabilities
- Eavesdropping. An attacker eavesdrops on a data exchange in order to extract useful information;
- Man In The Middle, MITM. A malicious device secretly establishes a connection between two devices and making them think they are exchanging data with each other;
- Replay Attack. A previously sent valid message captured by an intruder can be used to exploit the system functionality without an authentication procedure [15].
- Relay Attack. A malicious device establishes communication between two nodes and transmits unmodified data between them [14].
3. Bluetooth Mesh Overview
- A relay node is a device designed for data transmission within a mesh network. The message forwarding distance is limited by the TTL value;
- A low-power node is a device that spends most of its time in sleep mode. After waking up, a low-power device receives data from a friendly host;
- A friend node is a device that stores data for the Low-Profile node;
- A proxy node is a device that can work with BLE devices via GATT;
- A provisioner node is a device designed to register nodes in the mesh network and to distribute security keys. It also can be a configurator device.
3.1. Bluetooth Mesh Layers
- The models layer defines model implementation, its behavior, state;
- The foundation models layers defines network configuration and models management;
- The access layers defines application interaction with the upper transport layer to determine data format, data encryption process, and data verification;
- The upper transport layer defines message encryption and verification methods by using the application key generated for each device;
- The lower transport layer performs segmentation of transmitted messages and assembly of incoming messages;
- The network layer defines a message format for transfer data across network elements through a data link layer and message encryption. It also manages messages to be relayed, accepted, or rejected;
- The bearer layer defines packets handling methods such as transmitting data into advertising bearer, which is used in scanning and advertising state. Data transmitting through GATT, which allows communication with regular BLE devices using proxy nodes.
3.2. Authentication and Encryption
3.3. Provisioning Procedure
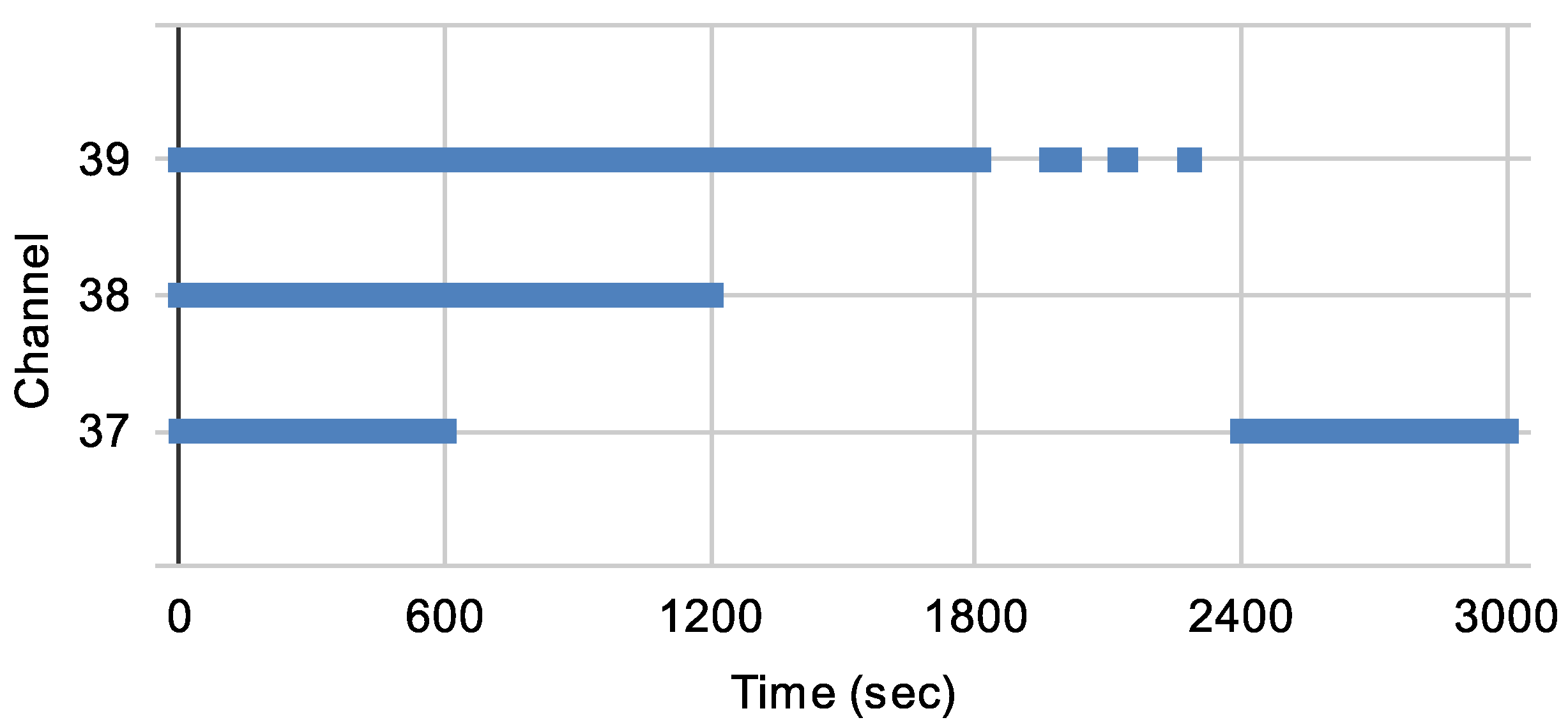
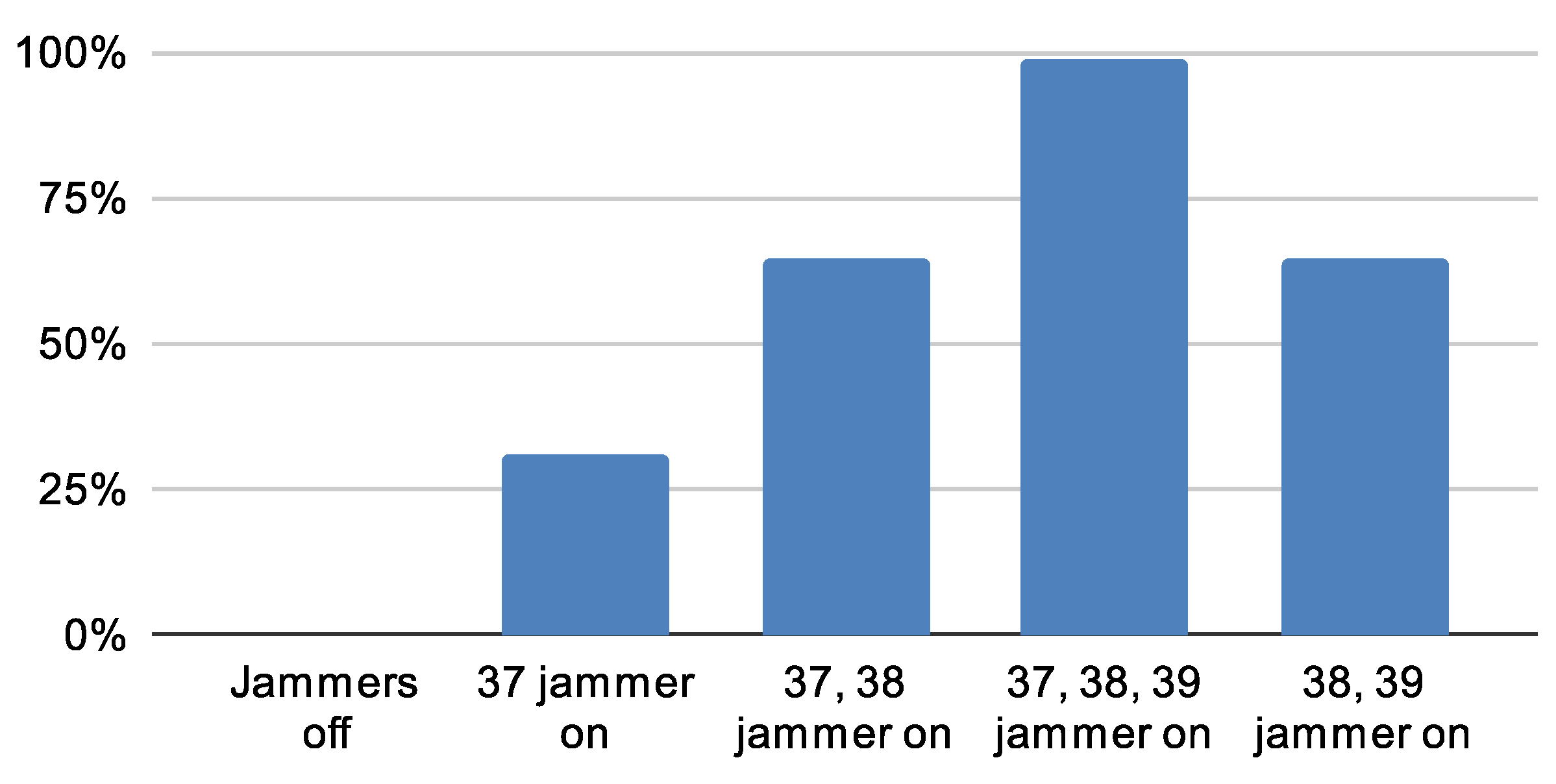
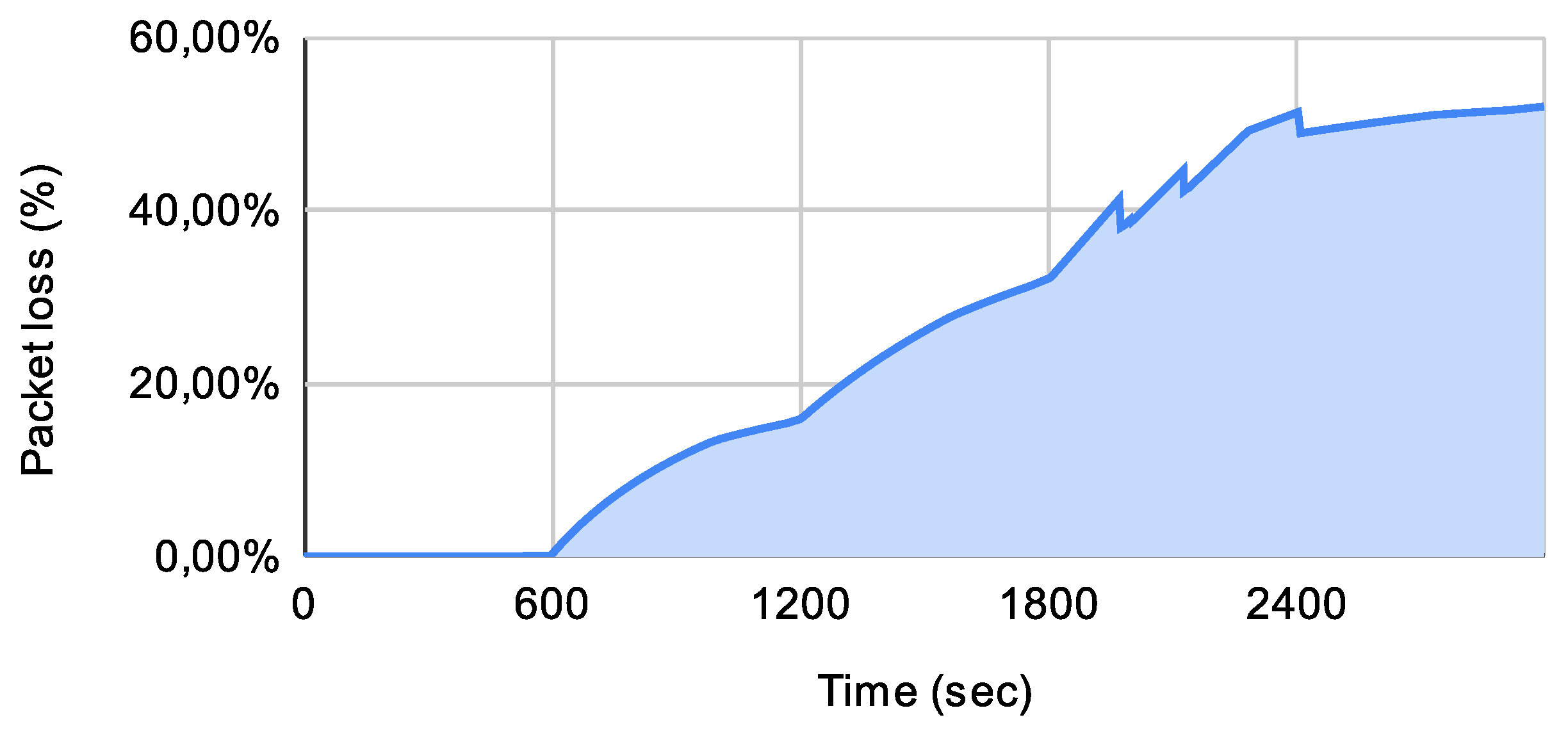
4. Experiment
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Cardullo, P.; Roio, D. Mesh Networks; Wiley Online Library: Hoboken, NJ, USA, 2020; pp. 1–3. [Google Scholar] [CrossRef]
- Cilfone, A.; Davoli, L.; Belli, L.; Ferrari, G. Wireless Mesh Networking: An IoT-Oriented Perspective Survey on Relevant Technologies. Future Internet 2019, 11, 99. [Google Scholar] [CrossRef] [Green Version]
- Zanaj, E.; Caso, G.; De Nardis, L.; Mohammadpour, A.; Alay, O.; Di Benedetto, M.G. Energy Efficiency in Short and Wide-Area IoT Technologies—A Survey. Technologies 2021, 9, 22. [Google Scholar] [CrossRef]
- Basu, S.; Baert, M.; Hoebeke, J. QoS Enabled Heterogeneous BLE Mesh Networks. J. Sens. Actuator Netw. 2021, 10, 24. [Google Scholar] [CrossRef]
- Lin, Y.W.; Lin, C.Y. Beyond Beacons—An Interactive Positioning and Tracking System Solely Based on BLE Mesh Network. 2018, pp. 351–362. Available online: https://link.springer.com/chapter/10.1007/978-3-319-65521-5_30 (accessed on 28 June 2021).
- Dhandapani, K.; Harshavardhan, A.; Kumar, V.; Sunitha, D.; Korra, S. BLE in IoT: Improved link stability and energy conservation using fuzzy approach for smart homes automation. Mater. Today Proc. 2021, in press. [Google Scholar] [CrossRef]
- Darroudi, S.M.; Caldera-Sànchez, R.; Gomez, C. Bluetooth Mesh Energy Consumption: A Model. Sensors 2019, 19, 1238. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Angelov, K.; Sadinov, S.; Kogias, P. Deployment of mesh network in an indoor scenario for application in IoT communications. IOP Conf. Ser. Mater. Sci. Eng. 2021, 1032, 012004. [Google Scholar] [CrossRef]
- SIG, B. Core Specification 5.3. Available online: https://www.bluetooth.com/specifications/specs/core-specification/ (accessed on 1 July 2021).
- SIG, B. Mesh Profile 1.0.1. Available online: https://www.bluetooth.com/specifications/specs/mesh-profile-1-0-1/ (accessed on 1 July 2021).
- Sen, J. Security and Privacy Issues in Wireless Mesh Networks: A Survey; Springer: Berlin/Heidelberg, Germany, 2013; pp. 189–272. [Google Scholar] [CrossRef] [Green Version]
- Ghori, M.; Wan, T.C.; Anbar, M.; Sodhy, G.; Rizwan, A. Review on security in bluetooth low energy mesh network in correlation with wireless mesh network security. In Proceedings of the 2019 IEEE Student Conference on Research and Development (SCOReD), Bandar Seri Iskandar, Malaysia, 15–17 October 2019; pp. 219–224. [Google Scholar] [CrossRef]
- Toçilla, A. Overview of Security in Wireless Mesh Networks (WMNs). 2020. Available online: https://www.researchgate.net/publication/341043358_Overview_of_Security_in_Wireless_Mesh_Networks_WMNs (accessed on 28 June 2021).
- Sevier, S.; Tekeoglu, A. Analyzing the Security of Bluetooth Low Energy. In Proceedings of the 2019 International Conference on Electronics, Information, and Communication (ICEIC), Auckland, New Zealand, 22–25 June 2019; pp. 1–5. [Google Scholar] [CrossRef]
- Gupta, D.S.; Wani, A.; Kumar, S.; Srivastava, A.; Sharma, D. Wireless Mesh Network Security, Architecture, and Protocols; IGI Global: Hershey, PA, USA, 2019; pp. 1–27. [Google Scholar] [CrossRef]
- Adomnicai, A.; Fournier, J.; Masson, L. Hardware Security Threats Against Bluetooth Mesh Networks. In Proceedings of the 2018 IEEE Conference on Communications and Network Security (CNS), Beijing, China, 30 May–1 June 2018; pp. 1–9. [Google Scholar] [CrossRef]
- Hortelano, D.; Olivares, T.; Ruiz, M.C. Providing interoperability in Bluetooth mesh with an improved provisioning protocol. Wirel. Netw. 2021, 27, 1–23. [Google Scholar] [CrossRef]
- Ghori, M.; Wan, T.C.; Sodhy, G. Bluetooth Low Energy Mesh Networks: Survey of Communication and Security Protocols. Sensors 2020, 20, 3590. [Google Scholar] [CrossRef] [PubMed]
- SIG, B. Mesh Model 1.0.1. Available online: https://www.bluetooth.com/specifications/specs/mesh-model-1-0-1/ (accessed on 1 July 2021).
- Suthar, F.A.; Patel, R.K.; Prajapati, J.B. Overview of Wireless Mesh Network’s in Bluetooth Mesh. 2019. Available online: https://ssrn.com/abstract=3817363 (accessed on 1 July 2021).
- Baert, M.; Rossey, J.; Shahid, A.; Hoebeke, J. The Bluetooth Mesh Standard: An Overview and Experimental Evaluation. Sensors 2018, 18, 2409. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Wan, Q.; Liu, J. Smart-Home Architecture Based on Bluetooth mesh Technology. IOP Conf. Ser. Mater. Sci. Eng. 2018, 322, 072004. [Google Scholar] [CrossRef] [Green Version]
- Brandao, A.; Lima, M.; Abbas, C.; García Villalba, L. An Energy Balanced Flooding Algorithm for a BLE Mesh Network. IEEE Access 2020, 8, 97946–97958. [Google Scholar] [CrossRef]
- Darroudi, S.M.; Gomez, C. Bluetooth Low Energy Mesh Networks: A Survey. Sensors 2017, 17, 1467. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Sirur, S.; Juturu, P.; Gupta, H.P.; Serikar, P.R.; Reddy, Y.K.; Barak, S.; Kim, B. A mesh network for mobile devices using Bluetooth low energy. In Proceedings of the 2015 IEEE SENSORS, Busan, Korea, 1–4 November 2015; pp. 1–4. [Google Scholar] [CrossRef]
- Murillo, Y.; Reynders, B.; Chiumento, A.; Malik, S.; Crombez, P.; Pollin, S. Bluetooth now or low energy: Should BLE mesh become a flooding or onnection oriented network? In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Zhang, Y.; Weng, J.; Dey, R.; Fu, X. Bluetooth Low Energy (BLE) Security and Privacy. 2019. Available online: http://www.cs.ucf.edu/~rajib/BLE-Encyclopedia2019.pdf (accessed on 28 June 2021).
- Darroudi, S.M.; Gomez, C.; Crowcroft, J. Bluetooth Low Energy Mesh Networks: A Standards Perspective. IEEE Commun. Mag. 2020, 58, 95–101. [Google Scholar] [CrossRef]
- Hernandez-Solana, A.; Pérez Díaz de Cerio, D.; Garcia-Lozano, M.; Valdovinos, A.; Valenzuela, J.L. Bluetooth Mesh Analysis, Issues and Challenges. IEEE Access 2020, 8, 53784–53800. [Google Scholar] [CrossRef]
- Veiga, A.; Abbas, C. Proposal and Application of Bluetooth Mesh Profile for Smart Cities’ Services. Smart Cities 2018, 2, 1–19. [Google Scholar] [CrossRef] [Green Version]
- Padgette, J.; Bahr, J.; Batra, M.; Holtmann, M.; Smithbey, R.; Chen, L.; Scarfone, K. NIST Special Publication 800-121 Revision 2, Guide to Bluetooth Security; Technical Report; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2017. [CrossRef]
- Diffie, W.; Hellman, M. New directions in cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar] [CrossRef] [Green Version]
- Ren, K. Provisioning a Bluetooth Mesh Network Part 2. 2017. Available online: https://www.bluetooth.com/blog/provisioning-a-bluetooth-mesh-network-part-2/ (accessed on 1 July 2021).
- Nordic. nRF52840 DK. Available online: https://www.nordicsemi.com/Products/Development-hardware/nRF52840-DK (accessed on 1 July 2021).
- Murillo, Y.; Reynders, B.; Chiumento, A.; Pollin, S. A Multiprotocol Low-Cost Automated Testbed for BLE Mesh. IEEE Commun. Mag. 2019, 57, 76–83. [Google Scholar] [CrossRef]
- PlutoSDR. ADALM-PLUTO Overview. Available online: https://plutosdr.org/adalm-pluto-overview/ (accessed on 1 July 2021).
- Dhivyasri, K. Wireless Sensor Network Jammer Attack: A Detailed Review. Int. J. Res. Appl. Sci. Eng. Technol. 2020, 8, 233–238. [Google Scholar] [CrossRef]
- Di Marco, P.; Park, P.; Pratesi, M.; Santucci, F. A Bluetooth-Based Architecture for Contact Tracing in Healthcare Facilities. J. Sens. Actuator Networks 2020, 10, 2. [Google Scholar] [CrossRef]



| Attack Type | Protection Methods |
|---|---|
| Denial of Service | - |
| Eavesdropping | Message encryption and message header obfuscation |
| Man In The Middle | Authentication during node provisioning process by using OOB |
| Replay Attack | Use of the sequential number (SEQ) and IV Index |
| Relay Attack | Authentication during node provisioning process by using OOB and using two-level key separation |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kalinin, E.; Belyakov, D.; Bragin, D.; Konev, A. IoT Security Mechanisms in the Example of BLE. Computers 2021, 10, 162. https://doi.org/10.3390/computers10120162
Kalinin E, Belyakov D, Bragin D, Konev A. IoT Security Mechanisms in the Example of BLE. Computers. 2021; 10(12):162. https://doi.org/10.3390/computers10120162
Chicago/Turabian StyleKalinin, Evgeny, Danila Belyakov, Dmitry Bragin, and Anton Konev. 2021. "IoT Security Mechanisms in the Example of BLE" Computers 10, no. 12: 162. https://doi.org/10.3390/computers10120162
APA StyleKalinin, E., Belyakov, D., Bragin, D., & Konev, A. (2021). IoT Security Mechanisms in the Example of BLE. Computers, 10(12), 162. https://doi.org/10.3390/computers10120162