Combining Blockchains, Smart Contracts, and Complex Sensors Management Platform for Hyper-Connected SmartCities: An IoT Data Marketplace Use Case
Abstract
:1. Introduction
2. Results
3. Discussion
3.1. IoT Platforms and Blockchain Solutions
3.2. IoT Sensor Data Handling and Blockchain
3.3. Identity Management and Blockchains
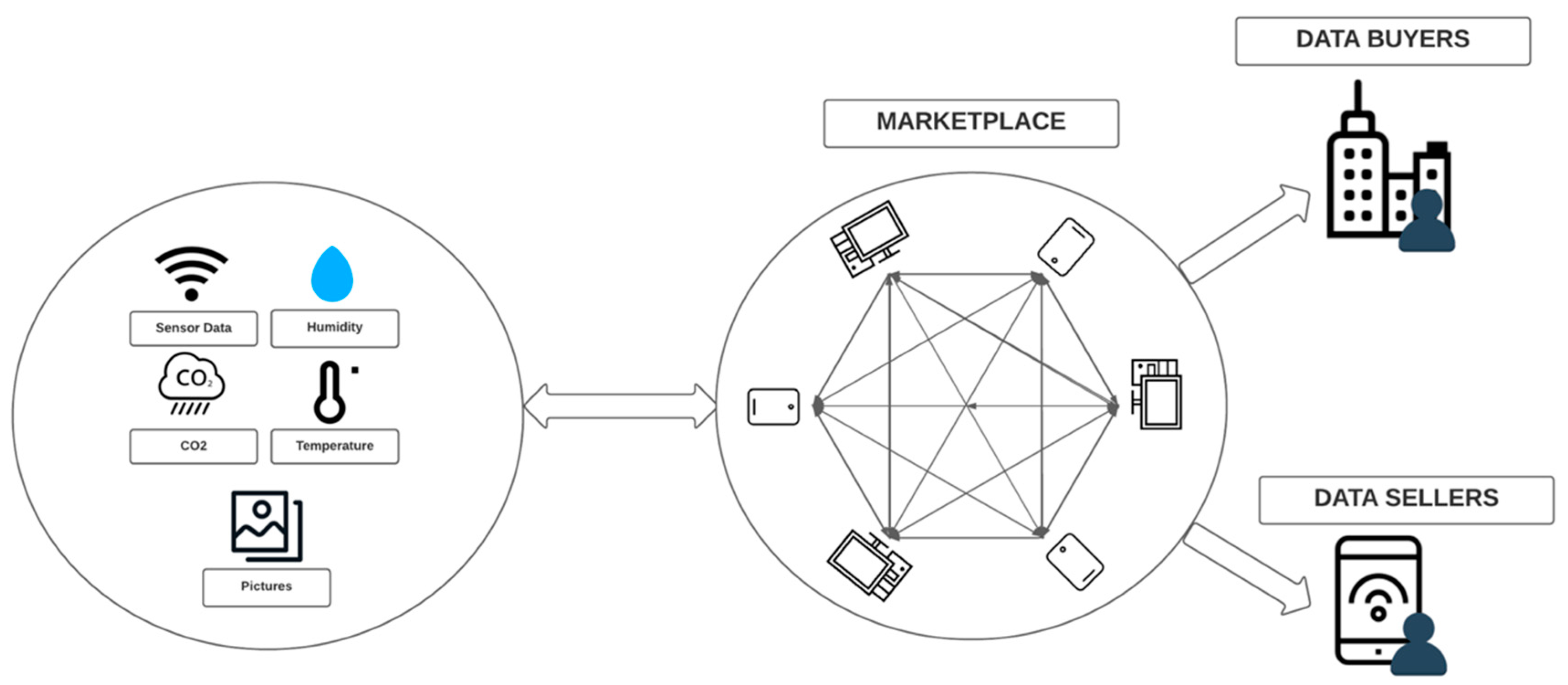
3.4. Hyper-Connected Smart Cities: The Example of M-Sec
4. Materials and Methods
4.1. System Overview and Requirements
4.1.1. Blockchain Marketplace
- Smart Contacts: implemented in Solidity (https://docs.soliditylang.org, accessed on 2 September 2021) programming language, a contract-oriented, high-level language whose syntax is similar to Javascript and supports inheritance, libraries, complex-defined types, and is designed to target the Ethereum Virtual Machine.
- Web Application: The interactions among end-users, the Blockchain Marketplace and deployed smart contracts are handled by the developed web service. It is accessible through its web browser and API endpoints and the data exchanged can be distributed on off-chain and on-chain databases. We used Nodejs and Node-Red (https://nodered.org/, accessed on 2 September 2021) (a flow-based development tool) for the Back End. A relational database management system PostgreSQL (https://www.postgresql.org/, accessed on 2 September 2021) was used for optimizing system’s performance and caching frequent requests.
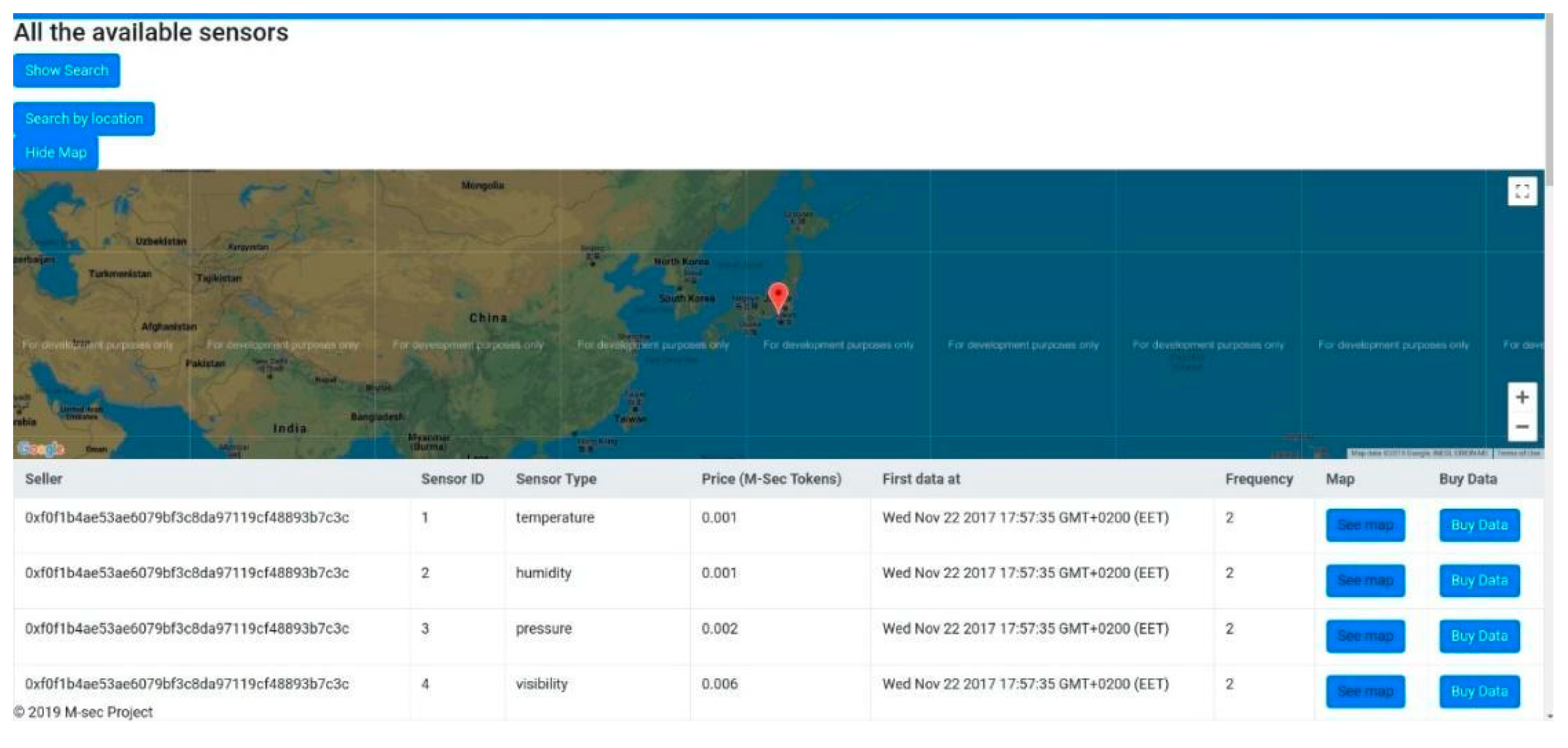
- User Interfaces: Implemented using HTML, Javascript, jQuery, Bootstrap to develop the different Front-End interfaces, Web3 Javascript API to handle the interaction with smart contracts. The Interfaces between the users and the blockchain provide functionalities helping users interact with the smart contracts deployed on blockchain, browse available media items and datasets from smart cities, sensors and other users, and access data they have bought. Owners are able to register their sensors to the marketplace, while a buyer browses sensors, specifies desired time period, and buys data using our dedicated created M-Sec cryptocurrency. Through the Marketplace sending transactions and reading data of transactions and smart contracts is also allowed, while users are “protected” from misreading or mistyping info when sending a transaction. The user searches in all the available sensors registered in the Smart Contracts the sensors of interest specifying details in the corresponding fields such as the location, the type the data (temperature, starting date and time, frequency etc.). Some example GUIs are shown in the following Figure 3 and Figure 4.
4.1.2. SOXFire and Data Collection
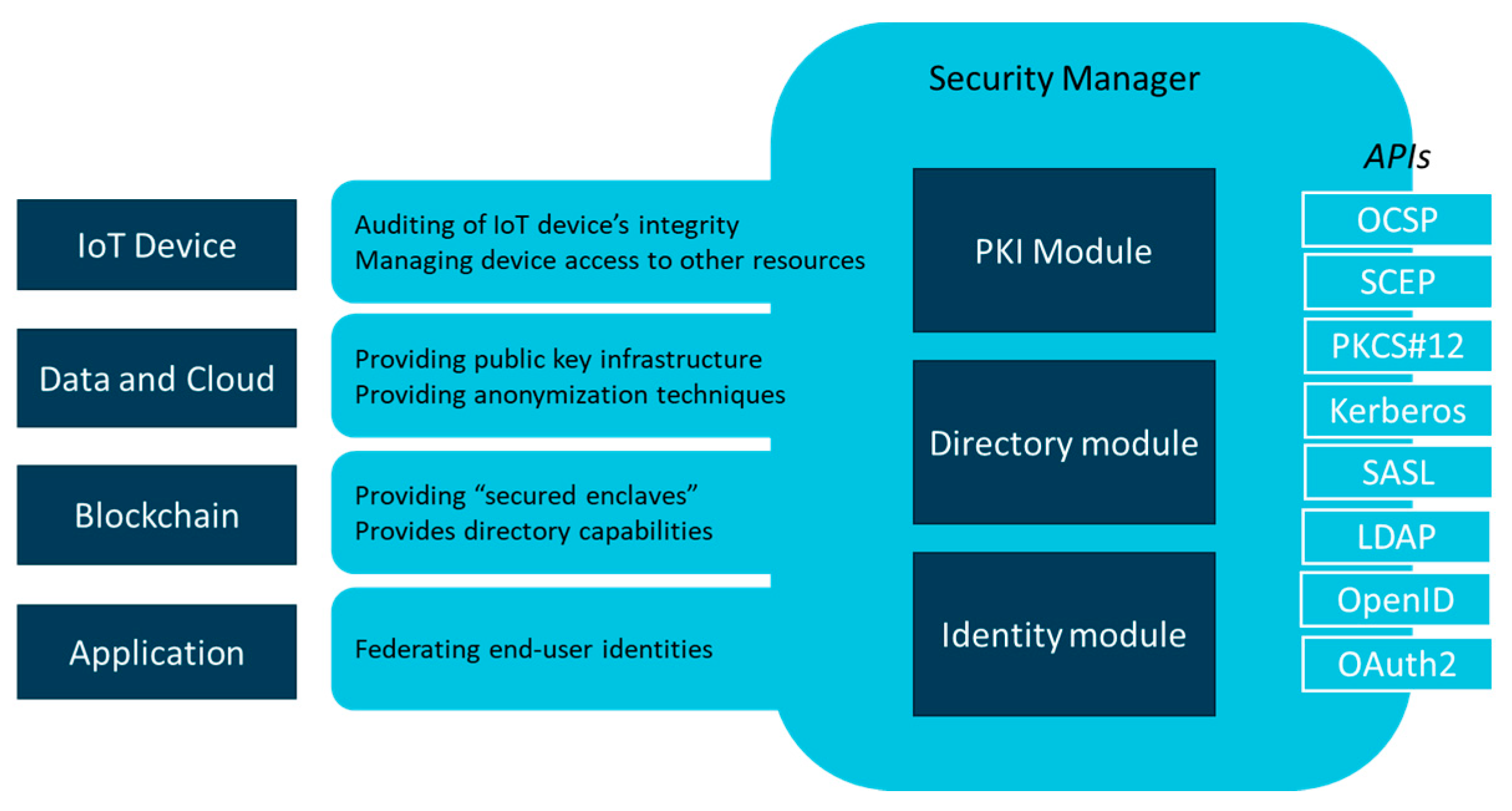
4.1.3. Security Manager
4.1.4. Offchain Data Storage Interacting with IPFS
4.2. Implementation and Integration Details
4.2.1. Blockchain Framework
- Private Ethereum blockchain: During the development process, we used a local private blockchain named Ganache (https://www.trufflesuite.com/ganache, accessed on 2 September 2021), which allowed us extensive testing of the developed smart contracts. It provides a personal Ethereum blockchain which we can use to run tests, execute commands, and inspect the state while controlling how the chain operates. It provides a built-in explorer and allows us to quickly see the current status of all accounts, including their addresses, private keys, transactions, and balances.
- Public Ethereum blockchain: We deployed smart contracts on Ethereum-based blockchains using browser IDE “Remix” (https://remix.ethereum.org/, accessed on 2 September 2021). Remix is an open-source tool that supports smart contracts development on the browser and facilitates the deployment on local or public Ethereum-based blockchain platforms. We explored the use of public test Ethereum blockchain.
- Quorum blockchain framework: The different smart contracts were deployed on Quorum blockchain framework (https://docs.goquorum.com/en/latest/, accessed on 2 September 2021). Quorum is a permissioned implementation of Ethereum, which allows certified members to build and run decentralized applications that run on blockchain technology. It is an open-source platform and supports smart contract privacy. Both private and public smart contracts are validated by every node within the blockchain network. Additionally, Quorum provides privacy and transparency, both at the transaction-level and network wide. In each Quorum node, consensus is achieved with the Raft or Istanbul BFT consensus algorithms instead of using Proof-of-Work. The P2P layer has been modified to only allow connections to/from permissioned nodes. In Ethereum, the notion of Gas was introduced (the fee or pricing value required to successfully conduct a transaction or execute a contract on Ethereum blockchain platform), while in Quorum the pricing of Gas has been removed, although Gas itself remains. One of the features of Quorum that are of great value for the component is the network and peer-to-peer permission management. This feature enables only the validated and authorized users to have access and be a part of the network. Also, Quorum provides enhanced transaction and smart contract privacy features. The permission-based nature of Quorum enables the constitution of private and public transaction getting the best of both worlds; open transactions are analogous to Ethereum but when it comes to the private transaction then it is confidential, and the data is not exposed to the public. Quorum adds privacy functions that allow for private transactions that are only visible to the transacting parties, while the other parties in the network would only see a hash. Finally, Quorum is considered to be very fast due to its efficient consensus mechanism, which belongs to the family of Byzantine Fault Tolerance (BFT) mechanisms [36]. In order to develop and deploy the smart contracts to Quorum blockchain, we used Truffle suite (https://www.trufflesuite.com/, accessed on 2 September 2021). It is a development environment and testing framework using the Ethereum Virtual Machine (EVM). Before we deploy the smart contracts to the blockchain network, we extensively tested them on the private blockchain previously presented. Additionally, before being deployed on a larger Quorum Network, we used a Quorum test network consisting of seven nodes (https://github.com/jpmorganchase/quorum-examples/tree/master/examples/7nodes, accessed on 2 September 2021).
- ALASTRIA: It is a public-permissioned network, sharing some of the properties of both types of networks public-permissionless and a private consortium, while trying to overcome scalability problems of traditional blockchain platforms related to their consensus mechanisms. There are a lot of efforts being made to solve or alleviate blockchain’s scalability problem, but as of today, the problem still exists and permissioned networks demonstrate significant better performance than public-permissionless. On the other hand, the high transaction cost in public blockchains such as Bitcoin and blockchain and the fact that all nodes store every transaction and smart contract constitute a restriction for certain types of applications. Alastria (https://github.com/alastria/alastria-platform/blob/master/en/Alastria-Core-Technical-Platform.md#alastria-core-technical-platform, accessed on 2 September 2021) is a Public-Permissioned network compatible with regulation, while implementations are based on Quorum. Each participant node has to be identified before it can participate in the network, while there is no cryptocurrency embedded as in the case of Bitcoin or Ethereum.
4.2.2. Smarts Contracts Details
M-Sec Token
Item Manager Smart Contract
Sensors Smart Contract
Smart City Data Smart Contract
Value Handler Smart Contract
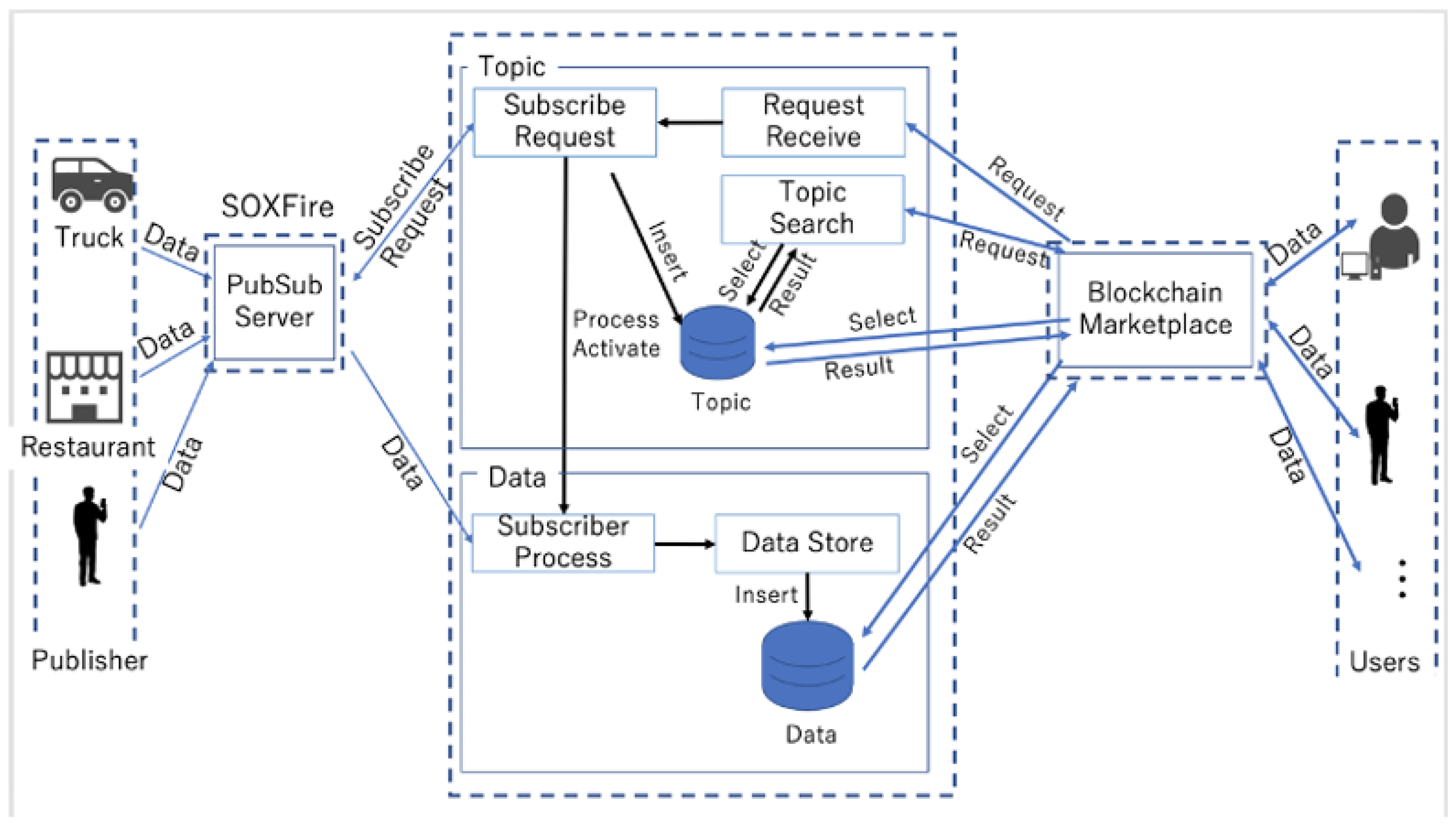
4.2.3. Integrating Pub/Sub Model with Blockchain Marketplace
4.2.4. Integrating Identity Management with Blockchain Marketplace
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef] [Green Version]
- Fernández-Caramés, T.M.; Fraga-Lamas, P. A Review on the Use of Blockchain for the Internet of Things. IEEE Access 2018, 6, 32979–33001. [Google Scholar] [CrossRef]
- Chakrabarty, S.; Engels, D.W. A secure IoT architecture for Smart Cities. In Proceedings of the 2016 13th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 9–12 January 2016; pp. 812–813. [Google Scholar]
- Nofer, M.; Gomber, P.; Hinz, O.; Schiereck, D. Blockchain. Bus. Inf. Syst. Eng. 2017, 59, 183–187. [Google Scholar] [CrossRef]
- Szabo, N. Formalizing and Securing Relationships on Public Networks. First Monday 1997, 2. [Google Scholar] [CrossRef]
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Sensing as a service model for smart cities supported by Internet of Things. Trans. Emerg. Telecommun. Technol. 2014, 25, 81–93. [Google Scholar] [CrossRef] [Green Version]
- Papadodimas, G.; Palaiokrasas, G.; Litke, A.; Varvarigou, T. Implementation of smart contracts for blockchain based IoT applications. In Proceedings of the 2018 9th International Conference on the Network of the Future (NOF), Poznan, Poland, 19–21 November 2018; pp. 60–67. [Google Scholar]
- Lin, C.; He, D.; Zeadally, S.; Huang, X.; Liu, Z. Blockchain-based Data Sharing System for Sensing-as-a-Service in Smart Cities. ACM Trans. Internet Technol. 2021, 21, 40:1–40:21. [Google Scholar] [CrossRef]
- Mohanta, B.K.; Jena, D.; Ramasubbareddy, S.; Daneshmand, M.; Gandomi, A.H. Addressing Security and Privacy Issues of IoT Using Blockchain Technology. IEEE Internet Things J. 2021, 8, 881–888. [Google Scholar] [CrossRef]
- Malik, A.; Gautam, S.; Abidin, S.; Bhushan, B. Blockchain Technology-Future of IoT: Including Structure, Limitations and Various Possible Attacks. In Proceedings of the 2019 2nd International Conference on Intelligent Computing, Instrumentation and Control Technologies (ICICICT), Kannur, India, 5–6 July 2019; Volume 1, pp. 1100–1104. [Google Scholar]
- Reyna, A.; Martin, C.; Chen, J.; Soler, E.; Díaz, M. On blockchain and its integration with IoT. Challenges and opportunities. Future Gener. Comput. Syst. 2018, 88, 173–190. [Google Scholar] [CrossRef]
- Hang, L.; Kim, D.-H. Design and Implementation of an Integrated IoT Blockchain Platform for Sensing Data Integrity. Sensors 2019, 19, 2228. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Latif, S.; Idrees, Z.; Ahmad, J.; Zheng, L.; Zou, Z. A blockchain-based architecture for secure and trustworthy operations in the industrial Internet of Things. J. Ind. Inf. Integr. 2021, 21, 100190. [Google Scholar] [CrossRef]
- Yu, B.; Wright, J.; Nepal, S.; Zhu, L.; Liu, J.; Ranjan, R. IoTChain: Establishing Trust in the Internet of Things Ecosystem Using Blockchain. IEEE Cloud Comput. 2018, 5, 12–23. [Google Scholar] [CrossRef]
- Kapsoulis, N.; Psychas, A.; Palaiokrassas, G.; Marinakis, A.; Litke, A.; Varvarigou, T. Know Your Customer (KYC) Implementation with Smart Contracts on a Privacy-Oriented Decentralized Architecture. Future Internet 2020, 12, 41. [Google Scholar] [CrossRef] [Green Version]
- Kumar, R.; Marchang, N.; Tripathi, R. Distributed Off-Chain Storage of Patient Diagnostic Reports in Healthcare System Using IPFS and Blockchain. In Proceedings of the 2020 International Conference on COMmunication Systems NETworkS (COMSNETS), Bengaluru, India, 7–11 January 2020; pp. 1–5. [Google Scholar]
- Cong, R.; Liu, Y.; Tago, K.; Li, R.; Asaeda, H.; Jin, Q. Individual-Initiated Auditable Access Control for Privacy-Preserved IoT Data Sharing with Blockchain. In Proceedings of the 2021 IEEE International Conference on Communications Workshops (ICC Workshops), Montreal, QC, Canada, 14–23 June 2021; pp. 1–6. [Google Scholar]
- Saint-Andre, P. Extensible Messaging and Presence Protocol (XMPP): Core. Available online: https://xmpp.org/rfcs/rfc6120.html (accessed on 2 September 2021).
- MQ Telemetry Transport. Available online: https://mqtt.org/ (accessed on 2 September 2021).
- Caiza, G.; Llamuca, E.S.; Garcia, C.A.; Gallardo-Cardenas, F.; Lanas, D.; Garcia, M.V. Industrial shop-floor integration based on AMQP protocol in an IoT environment. In Proceedings of the 2019 IEEE Fourth Ecuador Technical Chapters Meeting (ETCM), Guayaquil, Ecuador, 11–15 November 2019; pp. 1–6. [Google Scholar]
- Yonezawa, T.; Ito, T.; Nakazawa, J.; Tokuda, H. SOXFire: A Universal Sensor Network System for Sharing Social Big Sensor Data in Smart Cities. In Proceedings of the 2nd International Workshop on Smart, Trento, Italy, 12–16 December 2016; pp. 1–6. [Google Scholar]
- Rowe, A.; Berges, M.E.; Bhatia, G.; Goldman, E.; Rajkumar, R.; Garrett, J.H.; Moura, J.M.F.; Soibelman, L. Sensor Andrew: Large-scale campus-wide sensing and actuation. IBM J. Res. Dev. 2011, 55, 6:1–6:14. [Google Scholar] [CrossRef]
- Bhatia, G.; Rowe, A.; Berges, M.; Spirakis, C. Sensor-Over-XMPP. Available online: https://xmpp.org/extensions/inbox/sensors.html (accessed on 2 September 2021).
- Openfire. Available online: https://www.igniterealtime.org/projects/openfire/ (accessed on 2 September 2021).
- Liu, Y.; He, D.; Obaidat, M.S.; Kumar, N.; Khan, M.K.; Raymond Choo, K.-K. Blockchain-based identity management systems: A review. J. Netw. Comput. Appl. 2020, 166, 102731. [Google Scholar] [CrossRef]
- Ren, Y.; Zhu, F.; Qi, J.; Wang, J.; Sangaiah, A.K. Identity Management and Access Control Based on Blockchain under Edge Computing for the Industrial Internet of Things. Appl. Sci. 2019, 9, 2058. [Google Scholar] [CrossRef] [Green Version]
- Zhao, Z.; Liu, Y. A Blockchain based Identity Management System Considering Reputation. In Proceedings of the 2019 2nd International Conference on Information Systems and Computer Aided Education (ICISCAE), Dalian, China, 28–30 September 2019; pp. 32–36. [Google Scholar]
- Hopwood, D.; Bowe, S.; Hornby, T.; Wilcox, N. Zcash Protocol Specification; GitHub: San Francisco, CA, USA, 2016. [Google Scholar]
- Kosba, A.; Miller, A.; Shi, E.; Wen, Z.; Papamanthou, C. Hawk: The Blockchain Model of Cryptography and Privacy-Preserving Smart Contracts. In Proceedings of the 2016 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–26 May 2016; pp. 839–858. [Google Scholar]
- Garoffolo, A.; Kaidalov, D.; Oliynykov, R. Zendoo: A zk-SNARK verifiable cross-chain transfer protocol enabling decoupled and decentralized sidechains. arXiv 2020, arXiv:2002.01847. [Google Scholar]
- Chen, Y.; Nakazawa, J.; Yonezawa, T.; Tokuda, H. Cruisers: An automotive sensing platform for smart cities using door-to-door garbage collecting trucks. Ad. Hoc. Netw. 2019, 85, 32–45. [Google Scholar] [CrossRef]
- Sasaki, W.; Eigen, Y.; Medela, A.; Litke, A.; Nunez, V.C.; Okoshi, T.; Nakazawa, J. SmileCityReport: Emotion-aware Participatory Sensing for Smart Cities with Double-sided Photo Shooting. In Proceedings of the 2020 IEEE International Conference on Pervasive Computing and Communications Workshops (PerCom Workshops), Austin, TX, USA, 23–27 March 2020; pp. 1–6. [Google Scholar]
- Ali, M.S.; Dolui, K.; Antonelli, F. IoT data privacy via blockchains and IPFS. In Proceedings of the Seventh International Conference on the Internet of Things, Linz, Austria, 22–25 October 2017; pp. 1–7. [Google Scholar]
- Zou, S.; Xi, J.; Wang, S.; Lu, Y.; Xu, G. Reportcoin: A Novel Blockchain-Based Incentive Anonymous Reporting System. IEEE Access 2019, 7, 65544–65559. [Google Scholar] [CrossRef]
- Chen, Y.; Li, H.; Li, K.; Zhang, J. An improved P2P file system scheme based on IPFS and Blockchain. In Proceedings of the 2017 IEEE International Conference on Big Data (Big Data), Boston, MA, USA, 11–14 December 2017; pp. 2652–2657. [Google Scholar]
- Vukolić, M. The Quest for Scalable Blockchain Fabric: Proof-of-Work vs. BFT Replication. In Open Problems in Network Security; Camenisch, J., Kesdoğan, D., Eds.; Springer International Publishing: Cham, Switzerland, 2016; Volume 9591, pp. 112–125. ISBN1 9783319390277. ISBN2 9783319390284. [Google Scholar]

| Serial Number | Type of Sensor | Proposed Unit of Measurement |
|---|---|---|
| 1 | Temperature | °C |
| 2 | Relative humidity | % |
| 3 | Pressure Hectopascal | hPa |
| 4 | Visibility | Km |
| 5 | Wind speed and direction | m/s |
| 6 | Sky cloud coverage | % |
| 7 | Dew point | °C |
| 8 | Solar Radiation | watt/m² |
| 9 | UV index | 0 to 11 |
| 10 | Columnar density of total atmospheric ozone layer Dobson | DU |
| 11 | Smart Plug | Volts |
| 12 | Smoke Bool | on/off |
| 13 | Mattress Bool | on/off |
| Name | Proposed Unit of Measurement |
|---|---|
| Topic_ID | Unique topic name |
| Transducer_ID | Each transducer’s name |
| Value | Value |
| Pub_Timestamp | Timestamp when published from publisher |
| Timestamp | Timestamp of arrival in the Bridge |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Palaiokrassas, G.; Skoufis, P.; Voutyras, O.; Kawasaki, T.; Gallissot, M.; Azzabi, R.; Tsuge, A.; Litke, A.; Okoshi, T.; Nakazawa, J.; et al. Combining Blockchains, Smart Contracts, and Complex Sensors Management Platform for Hyper-Connected SmartCities: An IoT Data Marketplace Use Case. Computers 2021, 10, 133. https://doi.org/10.3390/computers10100133
Palaiokrassas G, Skoufis P, Voutyras O, Kawasaki T, Gallissot M, Azzabi R, Tsuge A, Litke A, Okoshi T, Nakazawa J, et al. Combining Blockchains, Smart Contracts, and Complex Sensors Management Platform for Hyper-Connected SmartCities: An IoT Data Marketplace Use Case. Computers. 2021; 10(10):133. https://doi.org/10.3390/computers10100133
Chicago/Turabian StylePalaiokrassas, Georgios, Petros Skoufis, Orfefs Voutyras, Takafumi Kawasaki, Mathieu Gallissot, Radhouene Azzabi, Akira Tsuge, Antonios Litke, Tadashi Okoshi, Jin Nakazawa, and et al. 2021. "Combining Blockchains, Smart Contracts, and Complex Sensors Management Platform for Hyper-Connected SmartCities: An IoT Data Marketplace Use Case" Computers 10, no. 10: 133. https://doi.org/10.3390/computers10100133
APA StylePalaiokrassas, G., Skoufis, P., Voutyras, O., Kawasaki, T., Gallissot, M., Azzabi, R., Tsuge, A., Litke, A., Okoshi, T., Nakazawa, J., & Varvarigou, T. (2021). Combining Blockchains, Smart Contracts, and Complex Sensors Management Platform for Hyper-Connected SmartCities: An IoT Data Marketplace Use Case. Computers, 10(10), 133. https://doi.org/10.3390/computers10100133







