Sustainable Digital Transformation of Disaster Risk—Integrating New Types of Digital Social Vulnerability and Interdependencies with Critical Infrastructure
Abstract
1. Introduction
- How can the concept of social vulnerability be extended to new semi-digital contexts?
- Which interdependencies with digital and physical critical infrastructure have to be taken into account?
2. Interrelations of Social Vulnerability, CI and Digital Transformation
2.1. Human and Social Vulnerability
2.2. Critical Infrastructure and Cybersecurity
2.3. Digital Transformation and Transhumanism
2.4. Transformation of Crisis and Disaster Management
3. Modifications of Social Vulnerability
3.1. Modifications of Social Vulnerability Indicators of Existing Groups
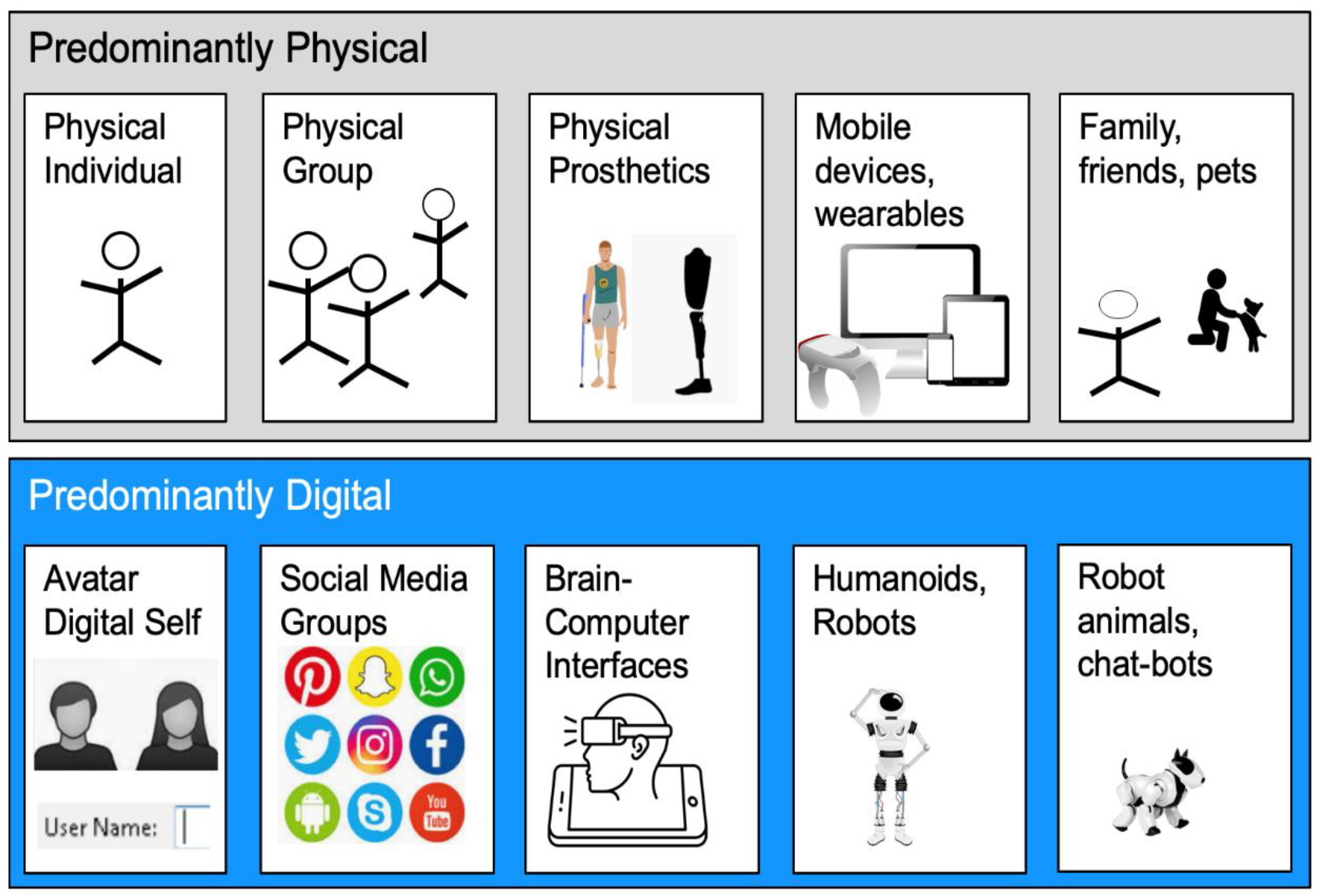
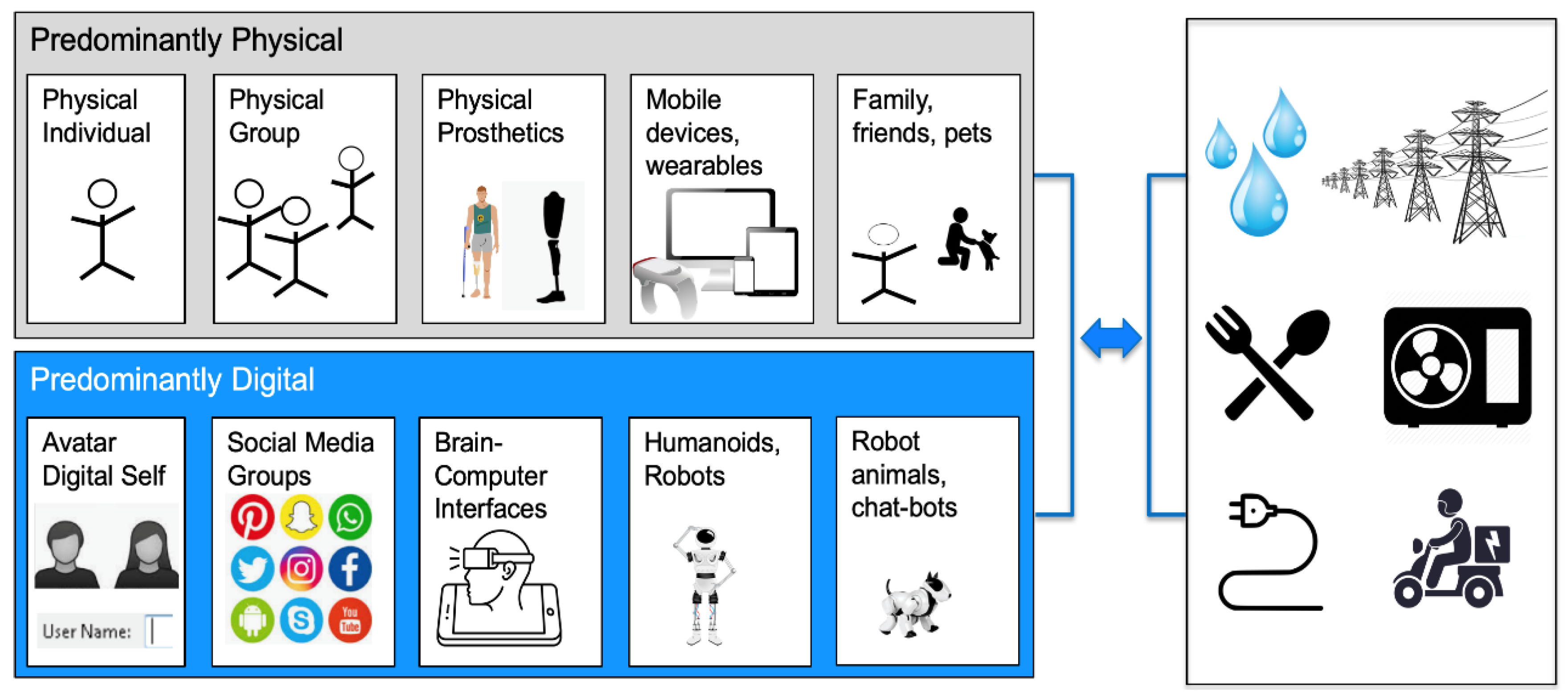
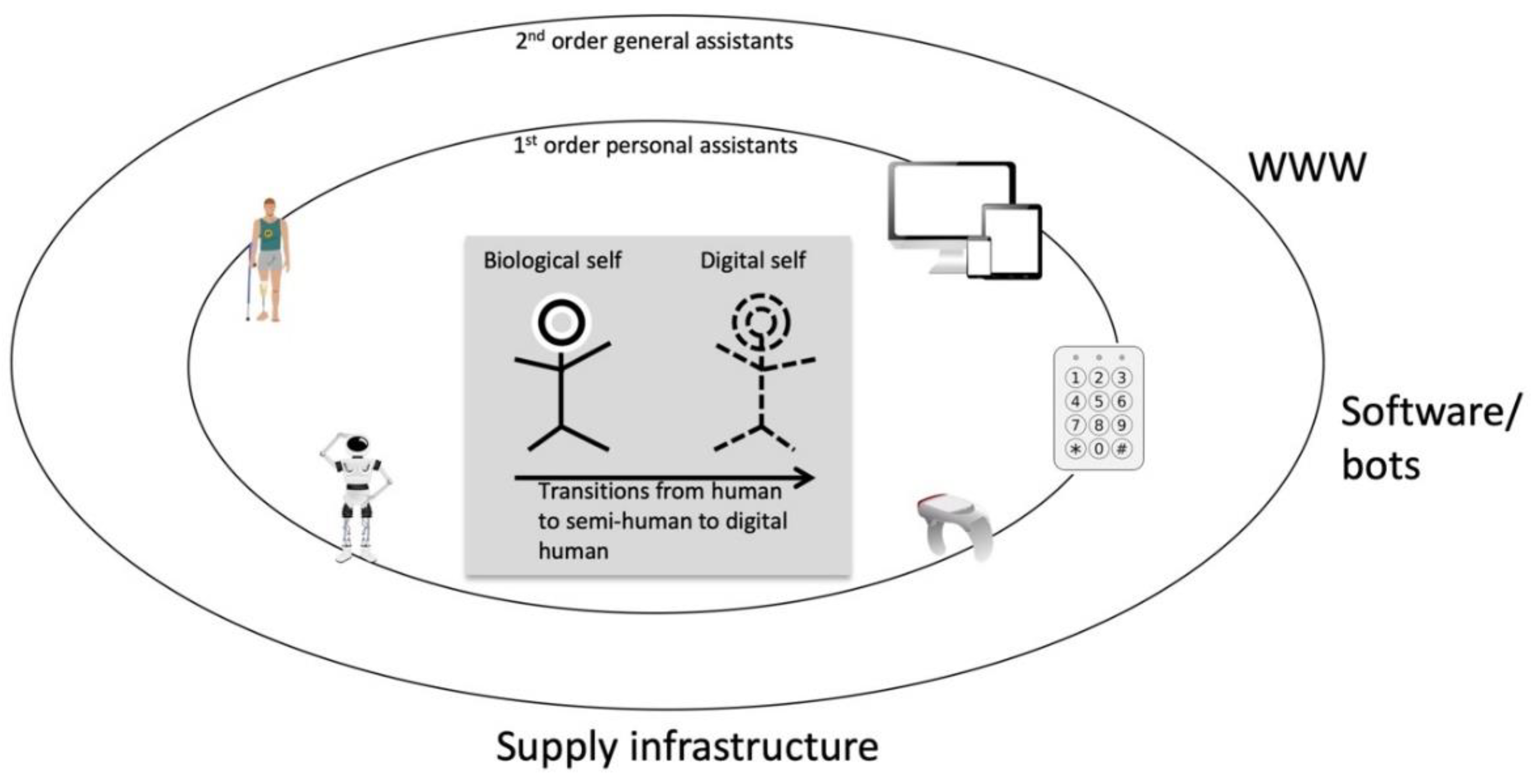
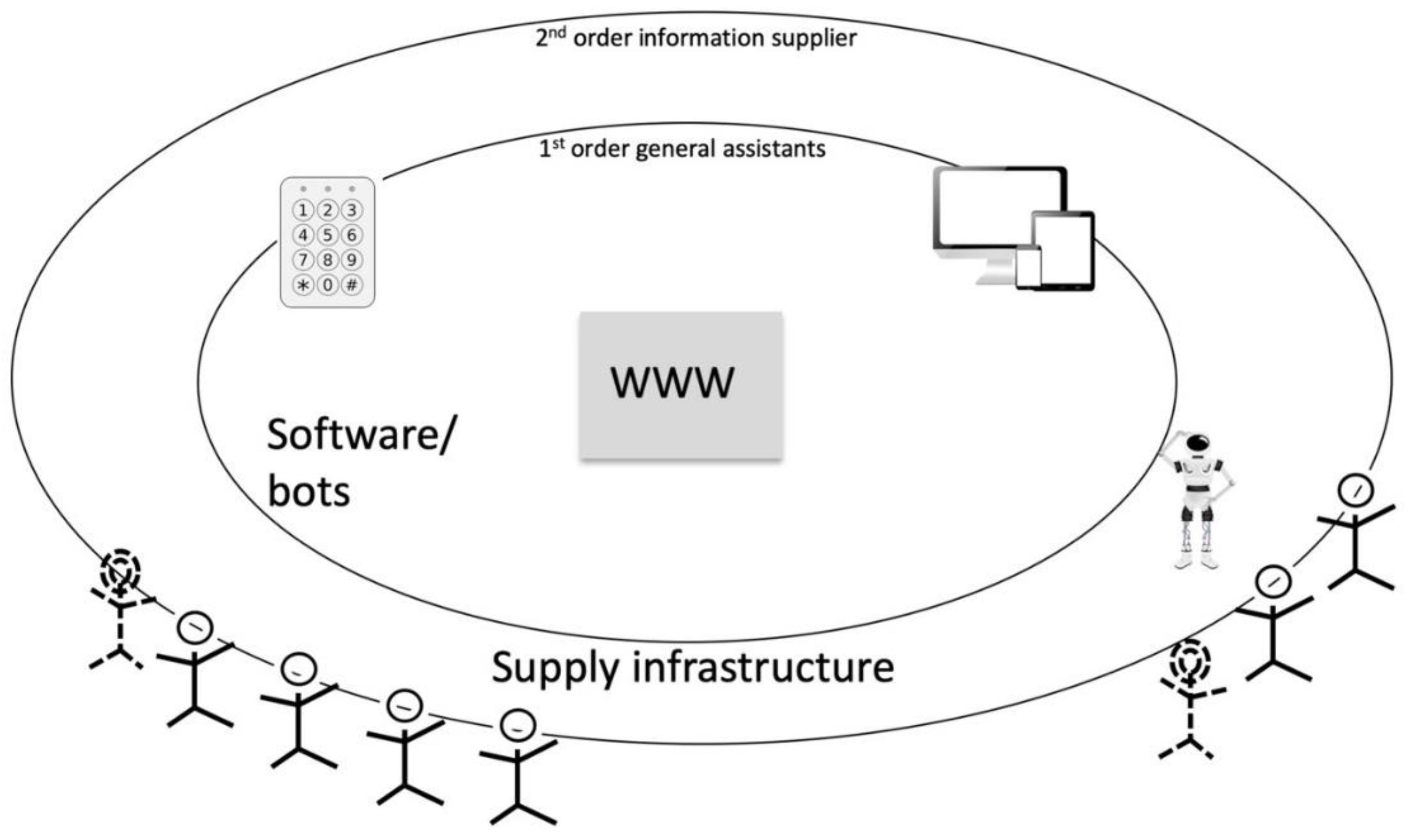
3.2. Adding New Types of Humans and Social Groups to the List of Vulnerabilities
3.3. Adding New Social Vulnerability Indicator Criteria for Semi-Digital or Fully Digital Groups
4. Interdependencies with Critical Infrastructure
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- United Nations. Sendai Framework for Disaster Risk Reduction 2015–2030; United Nations: Geneva, Switzerland, 2015. [Google Scholar]
- United Nations. Transforming Our World: The 2030 Agenda for Sustainable Development. Resolution Adopted by the General Assembly on 25 September 2015; United Nations: Geneva, Switzerland, 2015; p. 35. [Google Scholar]
- IPCC. Managing the Risks of Extreme Events and Disasters to Advance Climate Change Adaptation. A Special Report of Working Groups I and II of the Intergovernmental Panel on Climate Change—IPCC; Barros, T.F., Stocker, D., Qin, D.J., Dokken, K.L., Ebi, M.D., Mastrandrea, K.J., Mach, G.K., Plattner, S.K., Allen, M., Eds.; Cambridge University Press: Cambridge, UK; New York, NY, USA, 2012. [Google Scholar]
- Blaikie, P.; Cannon, T.; Davis, I.; Wisner, B. At Risk—Natural Hazards, People’s Vulnerability and Disasters, 2nd ed.; Routledge: London, UK, 1994. [Google Scholar]
- Bohle, H.G.; Downing, T.E.; Watts, M.J. Climate change and social vulnerability: Toward a sociology and geography of food insecurity. Glob. Environ. Chang. 1994, 4, 37–48. [Google Scholar] [CrossRef]
- Cuny, F.C. Disasters and Development; Oxford University Press: New York, NY, USA, 1983. [Google Scholar]
- Hewitt, K. (Ed.) Interpretations of Calamity. From the Viewpoint of Human Ecology; Allen & Unwin: Boston, MA, USA; London, UK; Sydney, NSW, Australia, 1983; p. 304. [Google Scholar]
- Asghar, S.; Alahakoon, D.; Churilov, L. A comprehensive conceptual model for disaster management. J. Humanit. Assist. 2006, 1360, 1–15. [Google Scholar]
- Bankoff, G. Rendering the World Unsafe: ‘Vulnerability’ as Western Discourse. Disasters 2001, 25, 19–35. [Google Scholar] [CrossRef] [PubMed]
- Pelling, M. Adaptation to Climate Change: From Resilience to Transformation; Routledge: Oxon, UK, 2011. [Google Scholar]
- De Sherbinin, A. Mapping the Unmeasurable? Spatial Analysis of Vulnerability to Climate Change and Climate Variability. Ph.D. Thesis, University of Twente, Enschede, The Netherlands, 2014. [Google Scholar]
- US Government. The President’s Commission on Critical Infrastructure Protection (PCCIP), Executive Order 13010; US Government: Washington, DC, USA, 1996.
- NOTA—Rathenau-Instituut. Stroomloos: Kwetsbaarheid van de Samenleving, Gevolgen van Verstoringen van de Elektriciteitsvoorziening (Blackout. Vulnerability of Society and Impacts of Electricity Supply Failure); Rathenau Instituut Den Haag: The Hague, The Netherlands, 1994; p. 264. [Google Scholar]
- European Commission. Cybersecurity of Smart Grids. Outcomes of the Expert Group on the Security and Resilience of Communications Networks and Information Systems for Smart Grids (2011–2012); European Commission: Brussels, Belgium, 2013. [Google Scholar]
- Radanliev, P.; Montalvo, R.M.; Cannady, S.; Nicolescu, R.; De Roure, D.; Nurse, J.R.; Huth, M. Cyber Security Framework for the Internet-of-Things in Industry 4.0. Preprints 2019, 2019030111. [Google Scholar] [CrossRef]
- Fekete, A. Common Criteria for the Assessment of Critical Infrastructures. Int. J. Disaster Risk Sci. 2011, 2, 15–24. [Google Scholar] [CrossRef]
- UN/ISDR. Developing Early Warning Systems: A Checklist, Third International Conference on Early Warning (EWC III): From Concept to Action: 27–29 March 2006, Bonn, Germany; UN/ISDR—Inter-Agency Secretariat of the International Strategy for Disaster Reduction: Geneva, Switzerland, 2006. [Google Scholar]
- Mirbabaie, M.; Bunker, D.; Stieglitz, S.; Marx, J.; Ehnis, C. Social media in times of crisis: Learning from Hurricane Harvey for the coronavirus disease 2019 pandemic response. J. Inf. Technol. 2020, 35, 195–213. [Google Scholar] [CrossRef]
- Roth, F.; Prior, T. Utility of virtual operation support teams: An international survey. Aust. J. Emerg. Manag. 2019, 34, 53–59. [Google Scholar]
- Turner, B.L.; Kasperson, R.E.; Matson, P.A.; McCarthy, J.J.; Corell, R.W.; Christensen, L.; Eckley, N.; Kasperson, J.X.; Luers, A.; Martello, M.L.; et al. A framework for vulnerability analysis in sustainability science. Proc. Natl. Acad. Sci. USA 2003, 100, 8074–8079. [Google Scholar] [CrossRef]
- Folke, C. Social-Ecological Resilience and Behavioral Responses. In Individual and Structural Determinants of Environmental Practice; Biel, A., Hansson, B., Mårtensson, M., Eds.; Ashgate Publishers: London, UK, 2003; pp. 226–287. [Google Scholar]
- Walker, B.; Holling, C.S.; Carpenter, S.; Kinzig, A. Resilience, Adaptability and Transformability in Social-Ecological Systems. Ecol. Soc. 2004, 9, 5. [Google Scholar] [CrossRef]
- Adger, W.N. Vulnerability. Glob. Environ. Chang. 2006, 16, 268–281. [Google Scholar] [CrossRef]
- Cuny, F.C. Refugee camps and camp planning: The state of the art. Disasters 1977, 1, 125–143. [Google Scholar] [CrossRef] [PubMed]
- Taylor, A.J. Assessment of Victim Needs; Intertect: Dallas, TX, USA, 1978. [Google Scholar]
- Tobin, G.A. Sustainability and community resilience: The holy grail of hazards planning? Glob. Environ. Chang. Part B Environ. Hazards 1999, 1, 13–25. [Google Scholar] [CrossRef]
- Onencan, A.M.; Liu, L.E.; Van de Walle, B. Design for Societal Resilience: The Risk Evaluation Diversity-Aiding Approach (RED-A). Sustainability 2020, 12, 5461. [Google Scholar] [CrossRef]
- Birkmann, J. Measuring vulnerability to promote disaster-resilient societies: Conceptual frameworks and definitions. In Measuring Vulnerability to Natural Hazards: Towards Disaster Resilient Societies, 2nd ed.; Birkmann, J., Ed.; United Nations University Press: Tokyo, Japan, 2013; pp. 9–54. [Google Scholar]
- Alves-Foss, J.; Barbosa, S. Assessing computer security vulnerability. ACM SIGOPS Oper. Syst. Rev. 1995, 29, 3–13. [Google Scholar] [CrossRef]
- Koh, D. Occupational risks for COVID-19 infection. Occup. Med. (Oxf. Engl.) 2020, 70, 3. [Google Scholar] [CrossRef]
- Pakpour, A.H.; Griffiths, M.D. The fear of COVID-19 and its role in preventive behaviors. J. Concurr. Disord. 2020. [Google Scholar]
- Peduzzi, P.; Dao, H.; Herold, C.; Mouton, F. Assessing global exposure and vulnerability towards natural hazards: The Disaster Risk Index. Nat. Hazards Earth Syst. Sci. 2009, 9, 1149–1159. [Google Scholar] [CrossRef]
- Heltberg, R.; Siegel, P.B.; Jorgensen, S.L. Addressing human vulnerability to climate change: Toward a ‘no-regrets’ approach. Glob. Environ. Chang. 2009, 19, 89–99. [Google Scholar] [CrossRef]
- Pelling, M.; Uitto, J.I. Small island developing states: Natural disaster vulnerability and global change. Glob. Environ. Chang. Part B Environ. Hazards 2001, 3, 49–62. [Google Scholar] [CrossRef]
- Slovic, P. Perception of Risk. Science 1987, 236, 280–285. [Google Scholar] [CrossRef]
- Werner, E. Vulnerable but invincible: High-risk children from birth to adulthood. Acta Paediatr. 1997, 86, 103–105. [Google Scholar] [CrossRef] [PubMed]
- Werner, E.; Smith, R. Journeys from Childhood to Midlife. Risk, Resilience, and Recovery; Cornell University Press: Ithaca, NY, USA, 2001. [Google Scholar]
- Moteff, J. Risk Management and Critical Infrastructure Protection: Assessing, Integrating, and Managing Threats, Vulnerabilities and Consequences; Congressional Research Service; The Library of Congress: Washington, DC, USA, 2005. [Google Scholar]
- Robert, B. A method for the study of cascading effects within lifeline networks. Int. J. Crit. Infrastruct. 2004, 1, 86–99. [Google Scholar] [CrossRef]
- Collier, S.J.; Lakoff, A. The Vulnerability of Vital Systems: How “Critical Infrastructure” Became a Security Problem. In The Politics of Securing the Homeland: Critical Infrastructure, Risk and Securitisation; Kristensen, M.D.K.S., Ed.; Routledge: Abingdon, UK, 2008. [Google Scholar]
- OECD. Future Global Shocks Improving Risk Governance; Organisation for Economic Co-Operation and Development: Paris, France, 2011; p. 137. [Google Scholar]
- European Commission. COUNCIL DIRECTIVE 2008/114/ EC of 8 December 2008 on the Identification and Designation of European Critical Infrastructures and the Assessment of the Need to Improve their Protection. Off. J. Eur. Union 2008, 345, 75–82. [Google Scholar]
- Bouchon, S. The Vulnerability of Interdependent Critical Infrastructures Systems: Epistemological and Conceptual State-of-the-Art; Institute for the Protection and Security of the Citizen, Joint Research Centre, European Commission: Ispra, Italy, 2006. [Google Scholar]
- Yusta, J.M.; Correa, G.J.; Lacal-Arántegui, R. Methodologies and applications for critical infrastructure protection: State-of-the-art. Energy Policy 2011, 39, 6100–6119. [Google Scholar] [CrossRef]
- Rinaldi, S.M.; Peerenboom, J.P.; Kelly, T.K. Identifying, Understanding, and Analyzing Critical Infrastructure Interdependencies. IEEE Control Syst. Mag. 2001, 21, 11–25. [Google Scholar]
- Labaka, L.; Hernantes, J.; Sarriegi, J.M. A holistic framework for building critical infrastructure resilience. Technol. Forecast. Soc. Chang. 2016, 103, 21–33. [Google Scholar] [CrossRef]
- Murdock, H.; de Bruijn, K.; Gersonius, B. Assessment of Critical Infrastructure Resilience to Flooding Using a Response Curve Approach. Sustainability 2018, 10, 3470. [Google Scholar] [CrossRef]
- Croope, S.V.; McNeil, S. Improving resilience of critical infrastructure systems postdisaster: Recovery and mitigation. Transp. Res. Rec. 2011, 2234, 3–13. [Google Scholar] [CrossRef]
- Giannopoulos, G.; Dorneanu, B.; Jonkeren, O. Risk Assessment Methodology for Critical Infrastructure Protection. In JRC–Scientific and Policy Report; JRC: Ispra, Italy, 2013. [Google Scholar]
- Boin, A.; McConnell, A. Preparing for critical infrastructure breakdowns: The limits of crisis management and the need for resilience. J. contingencies Crisis Manag. 2007, 15, 50–59. [Google Scholar] [CrossRef]
- Golan, M.S.; Jernegan, L.H.; Linkov, I. Trends and applications of resilience analytics in supply chain modeling: Systematic literature review in the context of the COVID-19 pandemic. Environ. Syst. Decis. 2020, 1, 222–243. [Google Scholar] [CrossRef]
- Remko, V.H. Research opportunities for a more resilient post-COVID-19 supply chain-closing the gap between research findings and industry practice. Int. J. Oper. Prod. Manag. 2020, 40, 341–355. [Google Scholar] [CrossRef]
- Müller, S.M.; Mueller, G.F.; Navarini, A.A.; Brandt, O. National Publication Productivity during the COVID-19 Pandemic—A Preliminary Exploratory Analysis of the 30 Countries Most Affected. Biology 2020, 9, 271. [Google Scholar] [CrossRef] [PubMed]
- Ivanov, D. New drivers for supply chain structural dynamics and resilience: Sustainability, industry 4.0, self-adaptation. In Structural Dynamics and Resilience in Supply Chain Risk Management; Springer: Cham, Switzerland, 2018; pp. 293–313. [Google Scholar]
- Magid, E.; Pashkin, A.; Simakov, N.; Abbyasov, B.; Suthakorn, J.; Svinin, M.; Matsuno, F. Artificial intelligence based framework for robotic search and rescue operations conducted jointly by international teams. In Proceedings of 14th International Conference on Electromechanics and Robotics “Zavalishin’s Readings”; Springer: Singapore, 2020; pp. 15–26. [Google Scholar]
- Ogie, R.I.; Rho, J.C.; Clarke, R.J. Artificial intelligence in disaster risk communication: A systematic literature review. In 2018 5th International Conference on Information and Communication Technologies for Disaster Management (ICT-DM); IEEE: Piscataway, NJ, USA, 2018; pp. 1–8. [Google Scholar]
- Aşuroğlu, T.; Açıcı, K.; Erdaş, Ç.B.; Toprak, M.K.; Erdem, H.; Oğul, H. Parkinson’s disease monitoring from gait analysis via foot-worn sensors. Biocybern. Biomed. Eng. 2018, 38, 760–772. [Google Scholar] [CrossRef]
- Fernández-Caramés, T.M.; Fraga-Lamas, P. Towards the Internet of smart clothing: A review on IoT wearables and garments for creating intelligent connected e-textiles. Electronics 2018, 7, 405. [Google Scholar] [CrossRef]
- Bostrom, N. Human Genetic Enhancements: A Transhumanist Perspective. J. Value Inq. 2003, 37, 493–506. [Google Scholar] [CrossRef]
- Moore, M. The Philosophy of Transhumanism. In The Transhumanist Reader: Classical and Contemporary Essays on the Science, Technology, and Philosophy of the Human Future; Moore, M., Vita-More, N., Eds.; John Wiley & Sons, Inc.: Chichester, UK, 2013. [Google Scholar]
- Huxley, J. Transhumanism. J. Humanist. Psychol. 1968, 8, 73–76. [Google Scholar] [CrossRef]
- Kurzweil, R. The Singularity is Near; Penguin: New York, NY, USA, 2005; p. 652. [Google Scholar]
- Benedikter, R.; Giordano, J.; Fitzgerald, K. The future of the self-image of the human being in the Age of Transhumanism, Neurotechnology and Global Transition. Futures 2010, 42, 1102–1109. [Google Scholar] [CrossRef]
- McNamee, M.; Edwards, S. Transhumanism, medical technology and slippery slopes. J. Med. Ethics 2006, 32, 513–518. [Google Scholar] [CrossRef]
- Ferrando, F. Posthumanism, transhumanism, antihumanism, metahumanism, and new materialisms. Existenz 2013, 8, 26–32. [Google Scholar]
- Grunwald, A. Technikfolgenabschätzung—Eine Einführung, 2nd ed.; Edition Sigma: Berlin, Germany, 2010. [Google Scholar]
- Petrie, K.J.; Wessely, S. Modern worries, new technology, and medicine. BMJ 2002, 324, 690–691. [Google Scholar] [CrossRef]
- Dominici, P. For an inclusive innovation. Healing the fracture between the human and the technological in the hypercomplex society. Eur. J. Futures Res. 2018, 6, 3. [Google Scholar] [CrossRef]
- Papadopoulos, T.; Gunasekaran, A.; Dubey, R.; Altay, N.; Childe, S.J.; Fosso-Wamba, S. The role of Big Data in explaining disaster resilience in supply chains for sustainability. J. Clean. Prod. 2017, 142, 1108–1118. [Google Scholar] [CrossRef]
- Yu, M.; Yang, C.; Li, Y. Big data in natural disaster management: A review. Geosciences 2018, 8, 165. [Google Scholar] [CrossRef]
- Shahid, A.R. The Impact of Crowdmapping on Humanitarian Response: A Structurational Analysis. Ph.D. Thesis, Royal Holloway, University of London, Egham, UK, 2016. [Google Scholar]
- Gulnerman, A.G.; Karaman, H. Spatial Reliability Assessment of Social Media Mining Techniques with Regard to Disaster Domain-Based Filtering. ISPRS Int. J. Geo-Inf. 2020, 9, 245. [Google Scholar] [CrossRef]
- Haworth, B.; Bruce, E. A review of volunteered geographic information for disaster management. Geogr. Compass 2015, 9, 237–250. [Google Scholar] [CrossRef]
- Matsuno, F.; Tadokoro, S. Rescue robots and systems in Japan. In 2004 IEEE International Conference on Robotics and Biomimetics; IEEE: Piscataway, NJ, USA, 2004; pp. 12–20. [Google Scholar]
- Kerle, N.; Nex, F.; Gerke, M.; Duarte, D.; Vetrivel, A. UAV-Based Structural Damage Mapping: A Review. ISPRS Int. J. Geo-Inf. 2020, 9, 14. [Google Scholar] [CrossRef]
- Aziz, N.A.A.; Aziz, K.A. Managing disaster with wireless sensor networks. In Proceedings of the 13th International Conference on Advanced Communication Technology (ICACT2011), Gangwon-Do, Korea, 13–16 February 2011; pp. 202–207. [Google Scholar]
- Twigg, J.; Mosel, I. Emergent groups and spontaneous volunteers in urban disaster response. Environ. Urban. 2017, 29, 443–458. [Google Scholar] [CrossRef]
- Cutter, S.L.; Boruff, B.J.; Shirley, W.L. Social Vulnerability to Environmental Hazards. Soc. Sci. Q. 2003, 84, 242–261. [Google Scholar] [CrossRef]
- Ziervogel, G.; Downing, T.E. Vulnerability Indicators and Mapping. Available online: https://www.sei.org/publications/vulnerability-indicators-mapping/ (accessed on 10 November 2020).
- King, D. Uses and Limitations of Socioeconomic Indicators of Community Vulnerability to Natural Hazards: Data and Disasters in Northern Australia. Nat. Hazards 2001, 24, 147–156. [Google Scholar] [CrossRef]
- Goss, K.C. Guide for All-Hazard Emergency Operations Planning; FEMA: Washington DC, USA, 1996. [Google Scholar]
- Cannon, T. A hazard need not a disaster make: Vulnerability and the causes of ‘natural’ disasters. In Natural Disasters: Protecting Vulnerable Communities: Proceedings of the Conference Held in London, UK, 13–15 October 1993; Thomas Telford Publishing: London, UK, 1993; pp. 92–105. [Google Scholar]
- Luhmann, N. Risk: A Sociological Theory; de Gruyter: Berlin, Germany, 1993. [Google Scholar]
- Fischer, H.W.; Stine, G.F.; Stoker, B.L.; Trowbridge, M.L.; Drain, E.M. Evacuation behaviour: Why do some evacuate, while others do not? A case study of the Ephrata, Pennsylvania (USA) evacuation. Disaster Prev. Manag. Int. J. 1995, 4, 30–36. [Google Scholar] [CrossRef]
- Heath, S.E.; Kass, P.H.; Beck, A.M.; Glickman, L.T. Human and pet-related risk factors for household evacuation failure during a natural disaster. Am. J. Epidemiol. 2001, 153, 659–665. [Google Scholar] [CrossRef] [PubMed]
- Zhao, S. The digital self: Through the looking glass of telecopresent others. Symb. Interact. 2005, 28, 387–405. [Google Scholar] [CrossRef]
- The Broadband Commission. The State of Broadband: Broadband Catalyzing Sustainable Development; ITU, UNESCO: Geneva, Switzerland, 2018; p. 90. [Google Scholar]
- Donner, W.; Rodríguez, H. Population composition, migration and inequality: The influence of demographic changes on disaster risk and vulnerability. Soc. Forces 2008, 87, 1089–1114. [Google Scholar] [CrossRef]
- Beasley, R.A. Medical robots: Current systems and research directions. J. Robot. 2012, 2012, 401613. [Google Scholar] [CrossRef]
- Broadbent, E.; Stafford, R.; MacDonald, B. Acceptance of healthcare robots for the older population: Review and future directions. Int. J. Soc. Robot. 2009, 1, 319. [Google Scholar] [CrossRef]
- Pisarchik, A.N.; Maksimenko, V.A.; Hramov, A.E. From novel technology to novel applications: Comment on “An integrated brain-machine interface platform with thousands of channels” by Elon Musk and Neuralink. J. Med Internet Res. 2019, 21, e16356. [Google Scholar] [CrossRef]
- Gilbert, F.; Pham, C.; Viaña, J.; Gillam, W. Increasing brain-computer interface media depictions: Pressing ethical concerns. Brain-Comput. Interfaces 2019, 6, 49–70. [Google Scholar] [CrossRef]
- Anupama, H.; Cauvery, N.; Lingaraju, G. Brain computer interface and its types-a study. Int. J. Adv. Eng. Technol. 2012, 3, 739. [Google Scholar]
- Barfield, W.; Williams, A. Cyborgs and enhancement technology. Philosophies 2017, 2, 4. [Google Scholar] [CrossRef]
- Ajiboye, A.B.; Willett, F.R.; Young, D.R.; Memberg, W.D.; Murphy, B.A.; Miller, J.P.; Walter, B.L.; Sweet, J.A.; Hoyen, H.A.; Keith, M.W. Restoration of reaching and grasping movements through brain-controlled muscle stimulation in a person with tetraplegia: A proof-of-concept demonstration. Lancet 2017, 389, 1821–1830. [Google Scholar] [CrossRef]
- Byrom, B.; McCarthy, M.; Schueler, P.; Muehlhausen, W. Brain monitoring devices in neuroscience clinical research: The potential of remote monitoring using sensors, wearables, and mobile devices. Clin. Pharmacol. Ther. 2018, 104, 59–71. [Google Scholar] [CrossRef] [PubMed]
- Picard, R.W.; Healey, J. Affective wearables. Pers. Technol. 1997, 1, 231–240. [Google Scholar] [CrossRef]
- Neža, P.; Maja, T.; Dejan, G.; Dušan, F. Lightning may pose a danger to patients receiving deep brain stimulation: Case report. J. Neurosurg. JNS 2018, 1–3. [Google Scholar] [CrossRef]
- Cooper, C.; Sovacool, B.K. Not your father’s Y2K: Preparing the north american power grid for the perfect solar storm. Electr. J. 2011, 24, 47–61. [Google Scholar]
- Bruneau, M.; Chang, S.E.; Eguchi, R.T.; Lee, G.C.; O’Rourke, T.D.; Reinhorn, A.M.; Shinozuka, M.; Tierney, K.; Wallace, W.A.; von Winterfeld, D. A Framework to Quantitatively Assess and Enhance the Seismic Resilience of Communities. Earthq. Spectra 2003, 19, 733–752. [Google Scholar] [CrossRef]
- Robinson, L.; Schulz, J.; Khilnani, A.; Ono, H.; Cotten, S.R.; Mcclain, N.; Levine, L.; Chen, W.; Huang, G.; Casilli, A.A. Digital inequalities in time of pandemic: COVID-19 exposure risk profiles and new forms of vulnerability. First Monday 2020, 25. [Google Scholar] [CrossRef]
- Gilbert, D.T.; Gill, M.J.; Wilson, T.D. The future is now: Temporal correction in affective forecasting. Organ. Behav. Hum. Decis. Process. 2002, 88, 430–444. [Google Scholar] [CrossRef]
- Alexander, D. Resilience and disaster risk reduction. an etymological journey. Nat. Hazards Earth Syst. Sci. 2013, 13, 2707–2716. [Google Scholar] [CrossRef]
- Waldrop, M.M. Complexity: The Emerging Science at the Edge of Order and Chaos; Edition of 1994; Penguin Books: London, UK, 1992. [Google Scholar]
| Demographic Characteristics | Indication Hypothesis Today | Indication Change Hypothesis for the Year 2100 1 |
|---|---|---|
| (Old) Age | Old age means higher vulnerability due to increasing health issues and dependency on other persons and services | Vulnerability decreases due to better health care system, technical monitoring, and support systems, but vulnerability in terms of technical dependency increases |
| (Very young—baby) age | Same as cell above, but dependency on parents greater (on average) | Same as cell above |
| Functional needs (water, food, etc.) | Vulnerability is similar to most people, but access (distance, time, income) makes a difference | Vulnerability decreases: more automated food delivery, smart water systems |
| Language proficiency | Higher vulnerability when warning messages cannot be understood | Vulnerability decreases: automated language translation on the fly |
| Diversity: race and ethnicity, family structure, gender | Different human group attributions render them vulnerable or resilient. Social media groups have emerged with new options of sharing knowledge or even disaster help thus reducing vulnerability | Diversification of human groups expands (degrees of semi-humanisms and robots), while certain digital devices connect traditional groups and create novel (digital) social groups |
| Humans without Digital Access to Information | Humans with Some (Removable) Access to Digital Services and Machines | Humans with Digital Implants | Hardware, with a Digital Interface | Software |
|---|---|---|---|---|
| Certain Tribal indigenous groups Elderly citizens Sick or disabled people Homeless Temporarily without access Voluntarily without access Prisoners Children | Social web-based networks Job-related access Private access (Brain) wearables Other mobile devices (phones, etc.) | Medical enhancement (hearing, heart, prostheses) Brain implants for information enhancement or access | Computers Mobile devices (from Nano to Macro) Robots Androids | Software Uploads of humans (bots with voice and memory of deceased, etc.) |
| Vulnerable Individuals and Groups | Specific Hazard-Exposure | Susceptibilities | Capacities or Resilience |
|---|---|---|---|
| Avatar, Digital Self | Electromagnetic storm or impulse, identity theft, deepfakes | Backup, data coherence, and updating Accessibility to a person | Stored and processed information and algorithms |
| Social Media Groups | Electromagnetic storm or impulse | Fake news, data coherence, and updating Access by everyone | Shared information and storage |
| Chat-bots | Electromagnetic storm or impulse | Information coherence and updating Access by everyone | Stored and processed information and algorithms |
| Brain-Computer Interface individuals | Lightning, hacking, day and night exposure | Biological and electronic susceptibility, access restriction, updating | Embedded availability |
| Humanoids, Robots | Roads, transport, charging points | Physical susceptibility, climatic conditions, maintenance, updates | Mobility |
| Robot animals | Roads, transport, charging points | Physical susceptibility, climatic conditions, maintenance, updates | Mobility |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fekete, A.; Rhyner, J. Sustainable Digital Transformation of Disaster Risk—Integrating New Types of Digital Social Vulnerability and Interdependencies with Critical Infrastructure. Sustainability 2020, 12, 9324. https://doi.org/10.3390/su12229324
Fekete A, Rhyner J. Sustainable Digital Transformation of Disaster Risk—Integrating New Types of Digital Social Vulnerability and Interdependencies with Critical Infrastructure. Sustainability. 2020; 12(22):9324. https://doi.org/10.3390/su12229324
Chicago/Turabian StyleFekete, Alexander, and Jakob Rhyner. 2020. "Sustainable Digital Transformation of Disaster Risk—Integrating New Types of Digital Social Vulnerability and Interdependencies with Critical Infrastructure" Sustainability 12, no. 22: 9324. https://doi.org/10.3390/su12229324
APA StyleFekete, A., & Rhyner, J. (2020). Sustainable Digital Transformation of Disaster Risk—Integrating New Types of Digital Social Vulnerability and Interdependencies with Critical Infrastructure. Sustainability, 12(22), 9324. https://doi.org/10.3390/su12229324






