1. Introduction
Recent technological advancements in IoT, as well as the emerging new network paradigm as envisioned by 5G [
1,
2], have been the motivation for employing numerous different devices in order to support everyday activities. IoT, firstly introduced in 1999 [
3], has been widely adapted to a variety of fields, such as environmental monitoring, infrastructure management, and home automation [
4], as a concept of making the devices “smarter”—thus less dependent on human intervention.
By the end of 2020, 25 billion IoT devices are expected to have been employed [
5] worldwide. The growth of IoT and the increase in the supported devices lead to the generation of large amounts of data that have to be processed, stored, and transmitted by the different devices. In order for this data to be processed, stored, and transmitted, massive computing resources, storage space, and communication bandwidth are needed. In this sense, many works have focused their attention on tackling the above constraints. For example, computing tasks in IoT devices regarding the generated data can be assigned to cloud servers, since the computing power on the cloud outclasses the capability of the IoT devices [
6]. In addition, in the post-cloud era arriving, many applications will also be deployed at the
edge of a system [
7], so as to bring services closer to the IoT devices by pooling the available computing, storage, and networking resources at the edge of the network [
4].
Regarding the devices composing an IoT system, they have to be of low cost and consume as little energy as possible, in order to support implementation on large-scale and multi-hop environments. In addition, sufficient computational capabilities are required for supporting the emerging applications and techniques, such as acting as edge devices in an edge-computing based system, where many processes occur directly on the IoT devices, rather than on the cloud.
MAC policies, in IoT and networks overall, have a significant impact on the devices’ characteristics described above. For example, MAC policies control the radio transmitter which is the most energy demanding part of an IoT device [
8]; thus, the overall energy consumption and lifetime of the devices are largely determined by the MAC policy implemented. Apart from energy conservation (which is the case in many works in the literature [
9,
10]), the role of MAC policies is to decide how the devices will access the shared medium, ensuring that only one node may access the channel at a time.
Regarding the aforementioned devices’ access to the shared medium, in many systems, specific time constraints have to be satisfied. For example, for safety applications in vehicular networks [
11], it is expected that various and different devices can communicate and transmit their data under certain time bounds. Combining the above with the requirement for low-cost devices, as mentioned earlier, there is a need for more research on time-constrained wireless communication of low-cost devices. This need has initiated a revisit of Time Division Multiple Access (TDMA) MAC policies that are inherently capable of meeting time constraints when compared to the contention-based MAC policies, such as Carrier Sense Multiple Access (CSMA) [
12] policies. Furthermore, in a system under a TDMA policy, there is no need for the nodes to listen to the medium prior to transmitting [
13], while at the same time TDMA’s deterministic approach guarantees a minimum performance level in terms of throughput. On the other hand, specific challenges arise when TDMA policies are applied, such as the need for continuous synchronization among the devices [
14]. The latter drawback’s difficulty to tackle lies both on the aforementioned extensive data generated by IoT devices and on the deviation occurring on the different devices’ clocks as time passes [
15,
16]. It is argued that this problem renders the use of TDMA policies impractical. However, there are network scenarios where the synchronization problem is not present (e.g., the use of the already present GPS receivers in Vehicular Networks) and new ways may be discovered as technology advances. In addition to the synchronization problem,
time-slots assignment to the network nodes within a TDMA
frame is also a prerequisite for a TDMA policy to work properly.
In this paper, the idea known from the literature TDMA-based policy is revisited. Then, this policy’s theoretical expectations are evaluated for their effectiveness on a system consisting of low-cost devices while a decentralized approach is followed regarding synchronization. More specifically, the proposed by Chlamtac and Faragó in [
17] TDMA-based topology independent medium access control (to be referred to as TiMAC in the sequel) policy is adopted. TiMAC policy’s primary goal is to allow for at least one successful transmission per node per frame, independently of the underlying topology. In order to achieve this goal, TiMAC’s time-slot assignment method is based on the properties of Galois polynomials, also presented in [
17]—thus allowing for its implementation on applications of tight delay constraints. The system considered here for implementing TiMAC on consists of devices of low-cost boards (i.e., Arduino [
18]) carrying simple RF modules at 433 MHz [
19,
20]. Note that, in their initial condition, devices are free of any software or coding installed on them (e.g., MAC).
The challenge met in this paper using the previously mentioned low-cost devices is twofold: (i) to implement TiMAC following the rules and properties of Galois polynomials as described in [
17]; and (ii) to synchronize the devices (also referred as nodes in the sequel) in a multi-hop decentralized manner. As it is shown, TiMAC is successfully implemented (i.e., one successful transmission per frame is shown that is guaranteed) on the low-cost system and the decentralized synchronization approach manages to successfully synchronize the nodes in a multi-hop manner.
The above contributions rely on experiments conducted and presented in
Section 5. Note that the experiments mentioned above are limited to only five nodes in a full graph topology configuration, thus allowing for getting a detailed insight of the particulars of the implementation (e.g., the Galois polynomials assigned to nodes). As for the synchronization part of the experiments, it is implemented in a multi-hop manner despite the single-hop topology and time periods dedicated to synchronization are employed between time frames. As it is demonstrated, the nodes are successfully synchronized, showing that this method can be easily implemented in a more realistic and multi-hop topology.
The rest of this paper is organized by including past related work in
Section 2 and a brief description of TiMAC in
Section 3. Details about the low-cost device, the 433 MHz RF modules and the TDMA synchronization approach are given in the system’s description
Section 4. The experimental setup (i.e., the topology and various parameters) along with the experimental results are presented in
Section 5 and the conclusions are drawn in
Section 6.
2. Past Related Work
MAC policies for IoT have been the case in many works over the past few years. Oliveira et al., in their 2019 work [
21], survey MAC policies used in IoT, providing a detailed description of each one. More specifically, they categorize the reviewed policies in short and long-distance coverage. Under the latter categorization, they survey most of the known policies used by, e.g., Radio Frequency Identification (RFID), Bluetooth Low Energy (BLE), Wireless Highway Addressable Remote Transducer Protocol (Wireless-HART), Long Range Protocol (LoRa), and many more.
Like Oliveira et al., Kumar et al., in their work in [
22], survey MAC policies in IoT. The authors there categorize the considered MAC policies according to the channel access method each one uses. In addition, they give the essential properties of MAC policies for IoT and the common causes of energy consumption. Finally, they address some pros and cons for each surveyed policy.
Other surveys, more dedicated to the applications each IoT system is designed for, can be found in the literature. For example, Sherazi et al., in [
10], provide a detailed analysis of MAC policies exclusively for energy harvesting IoT systems. In contrast, a review and evaluation of MAC policies for satellite IoT systems using nano-satellites are given in [
23] by Ferrer et al.
TDMA policies for IoT, hybrid policies that consider the cooperation of TDMA with other channel access methods, and improvements for TDMA policies have been the case in several works in the literature over the past five years. A distributed and adaptive hybrid medium access control (DAH-MAC) is proposed in [
24] by Ye and Zhuang. In the policy considered there, a distributed TDMA approach is employed for voice packet transmissions to guarantee a voice packet loss rate bound, while truncated CSMA/CA (TCSMA/CA) is used for data nodes to access the channel. The same authors in [
25] propose a token-based adaptive medium access control (TA-MAC) scheme for a two-hop Internet of Things (IoT)-enabled mobile ad hoc network. TA-MAC bases its operation on super-frames created by the devices and these super-frames’ duration, along with the number of token rotation cycles, are optimized and adapted to the network’s traffic load, so as to achieve a consistently minimal average end-to-end packet delay.
Another hybrid approach is given in [
26] by Shahin et al. There, a hybrid slotted-CSMA/CA-TDMA (HSCT) policy is proposed, where a contention-based slotted-CSMA/CA period (SCP) divided into multiple CSMA/CA access windows is assumed, along with a contention-free slotted-TDMA period divided into multiple slots. Both CSMA/CA and slotted-TDMA are cooperating in order to achieve the registration of machine-to-machine (M2M) communications in large scale environments where many devices try to access a single and centralized access point.
An algorithm for fair resource allocation in TDMA-based distributed sensor networks for IoT is proposed in [
27] by Kim et al. The authors of the latter paper implement a multi-hop desynchronization (DESYNC) algorithm for tackling the hidden-node problem in multi-hop TDMA-based networks, by proposing a new frame structure and a procedure dedicated to approaching the problem.
Scheduling in TDMA-based IoT systems is studied in [
28] by Li et al. The authors in this paper propose a distributed TDMA slot scheduling algorithm that takes into account nodes’ energy and the network’s topology. In this approach, the residual energy of nodes and the topology knowledge about the number of nodes’ neighbors play a significant role in the time slot allocation, in providing higher priority in nodes of lower residual energy and more neighbors than the other nodes. In the same spirit, the authors in [
29] introduce a distributed TDMA scheduling algorithm based on exponential backoff rule, the nodes’ residual energy, and the number of neighbors.
All works given above regarding TDMA policies in IoT are some of the newest in the literature (i.e., 2015–2020). Interestingly, in the works referenced above, there are two similarities in all of them: (i) All of the policies and algorithms proposed have been tested on simulators, rather than on real devices; and (ii) synchronization of nodes is not the case in any of them. At the same time, in most, it is either assumed that GPS infrastructure is used by the nodes (thus synchronization is achieved through them), or centralized approaches are assumed. As a result, there is no knowledge on how these approaches would work on low-cost systems, where fewer options are available (e.g., no GPS can be implemented due to its high cost).
The current work is based on deploying a known policy (TiMAC) on a low-cost IoT system. In addition, considering the drawbacks of the low-cost system (further explained later), a decentralized approach for the synchronization of nodes in such systems is given. TiMAC was firstly introduced by Chlamtac and Faragó in [
17] and it has been further extended and implemented in various applications. For example, the authors [
11] consider TiMAC in their paper for vehicular networks, while they also extend TiMAC to one that considers disjoint frames depending on the vehicle’s direction of movement.
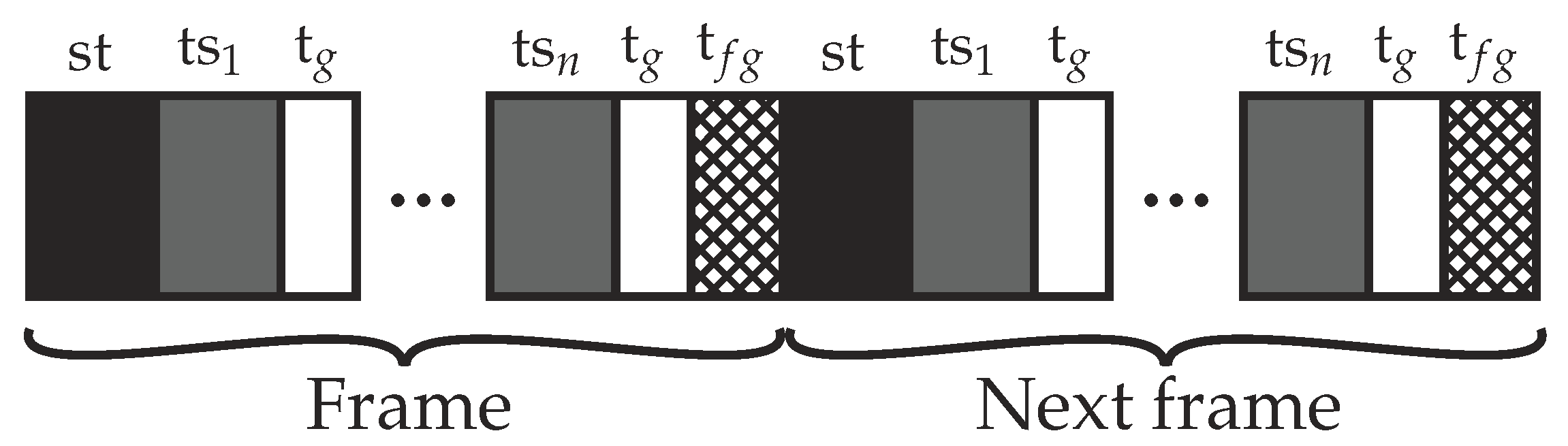
3. The TiMAC Policy
TiMAC is a TDMA-based policy, the latter policies dividing the time into slots and each node is able to access the channel at a given time slot. Note that, in TDMA, all nodes share the same frequency channel; thus, they have to be synchronized for ensuring that interference will not be experienced during transmissions. In this sense, under TiMAC, a fixed-length frame is assigned to all nodes, while the time-slot duration is considered to be long enough for a transmission of a data packet to take place. The next step is to assign to each node a subset of the previously assigned frame’s time-slots, during which a node is allowed to transmit its data packet. The latter time-slot assignment takes place according to arbitrarily assigned Galois polynomials [
30] as described next. The goal here is to ensure a unique subset for all nodes—thus further ensuring that each node will transmit according to a unique repeating pattern. As a result, at least one transmission will be successful for each node during every frame, even if the network load is increased (e.g., each node always has data packets available for transmission) [
17].
As already mentioned, under the TiMAC policy, nodes are assigned time-slots according to arbitrarily assigned Galois polynomials, the latter procedure being derived by the Chlamtac–Faragó algorithm [
17]. In order for the TiMAC policy to exploit the Chlamtac–Faragó algorithm and operate, certain assumptions have to be made regarding the total number of nodes composing the network, as well as the maximum number of neighbors each node can have. Let
N denote the number of network nodes and
D the maximum number of neighbors, respectively.
N and
D are used by the algorithm in order to derive the values of two new (integer) parameters, the first related to the size of the frame and denoted by
q, and the second related to the degree of Galois polynomials of order
q and denoted by
k. More specifically, the frame size consists of
time-slots (i.e., the frame size is
), each one split into
q sub-frames of
q time-slots. Each node is assigned one slot from each one of the
q sub-frames and, therefore, each node is allowed to transmit at
q time-slots within a frame.
Having made the above assumptions, the next step is to derive the particular time-slots during which it is allowed for a certain node
u to transmit its data packet. For deriving the latter time-slot, each node
u is assigned a unique polynomial of degree
k with coefficients from a finite Galois field of order
q (
), to be represented as
where
. In order to find the slot assigned to each node
u inside a subframe
s,
is calculated, where
[
17]. It is reasonable to suppose that, in order to achieve the constraint for unique polynomials assigned to all nodes in the network, it is required that
(
corresponds to all possible polynomials of degree
k when their coefficient belong to the
).
An integral property of this approach is that, in each frame, at least one transmission will be successful for each node even for the case of increased traffic load conditions. For example, even if all nodes always have data packets ready to be transmitted, each node will have at least one collision-free slot during the frame. Taking into account that each node transmits according to its assigned polynomial of degree k, there will be at most k simultaneous transmissions (thus collisions will occur) with any neighbor node since there are at most k common roots between two polynomials of degree k. Considering that the maximum number of neighbor nodes is D, then at most simultaneous transmissions are expected to take place. In addition, given that each node is allowed to transmit at q time-slots, then so as to guarantee at least one successful transmission. Both constraints, and , are exploited by the Chlámtac–Farago algorithm to calculate q and k given N and D.
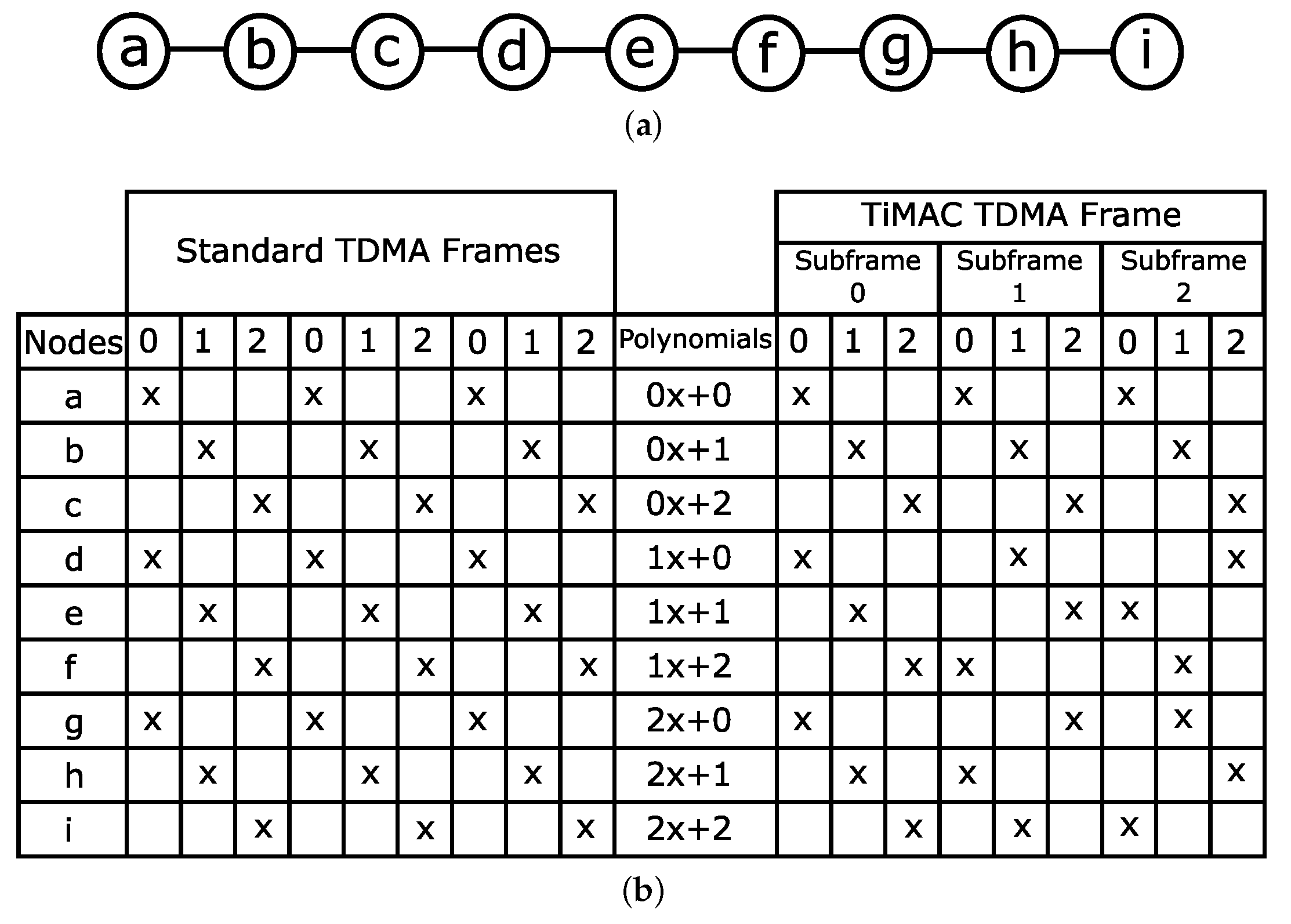
In order to gain more insight into TiMAC, in
Figure 1a, an example chain topology is depicted. Regarding the depicted topology, both the corresponding “traditional” and the TiMAC TDMA frames are presented in
Figure 1b. The traditional TDMA frame is given on the left side of
Figure 1b. It consists of three slots that are repeated three times and each node has been assigned a fixed slot in a way that ensures a collision-free communication among neighbors. On the other hand, a TiMAC frame is depicted on the right side of the figure. It consists of three subframes on which the slot assignment has taken place in accordance with the corresponding arbitrarily assigned polynomials. It is observed here that, when the nodes operate under TiMAC, every node is guaranteed at least one successful transmission per frame, even in the cases where topology changes occur. However, when traditional TDMA is chosen, special care has to be taken after a topology change, as a slot reassignment may be necessary.
The next step is to implement this particular MAC policy in a system that consists of low-cost devices and evaluate its performance. The proposed system’s characteristics are given in the following
Section 4.
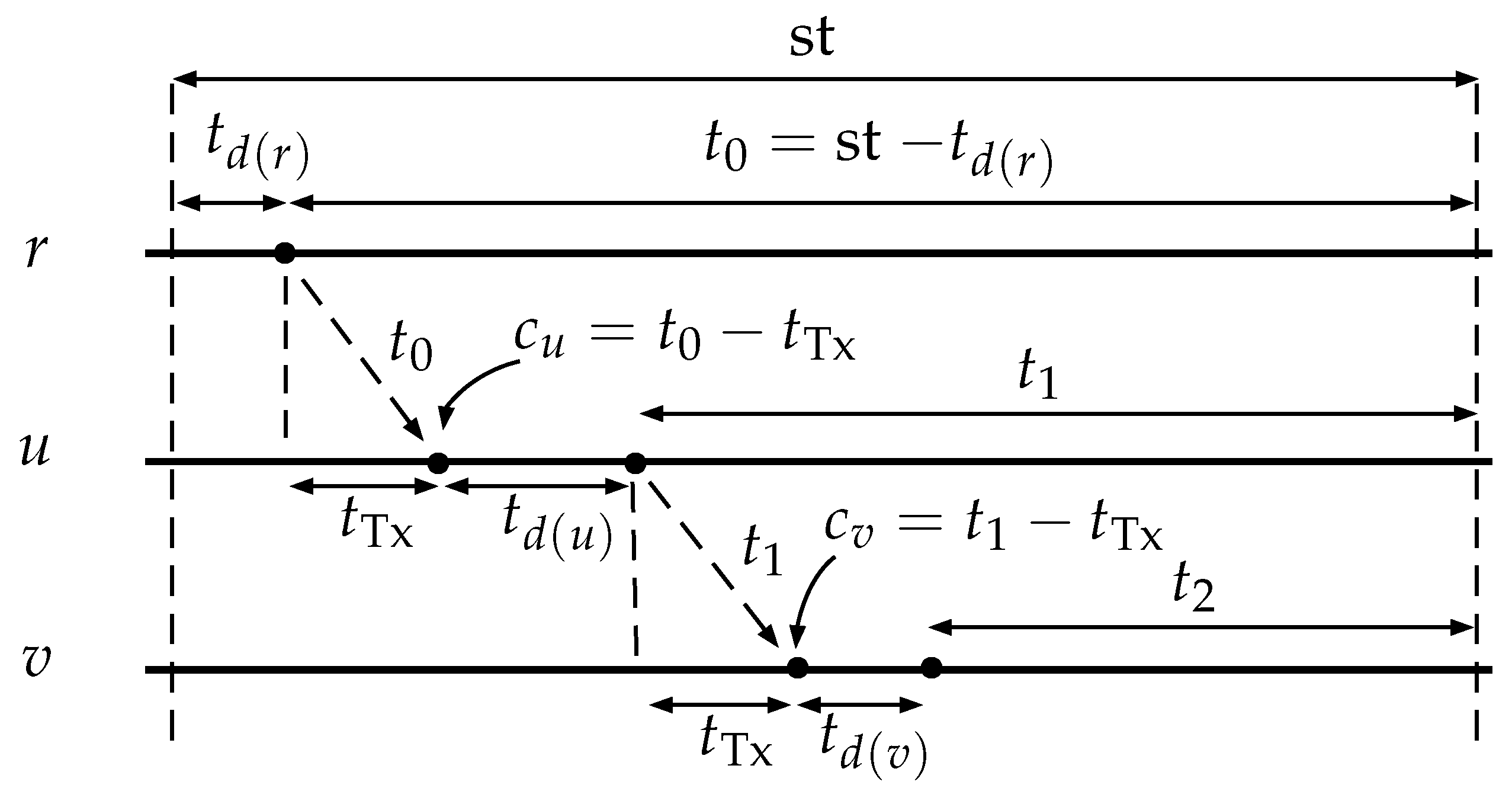
5. Experimental Methodology and Results
A full graph topology is considered here for the experimental setup, consisting of five nodes. The considered network is assumed as part of a larger IoT network of maximum nodes where the maximum number of neighbors is . Taking the above into consideration, the five nodes were set up in a full graph topology so as to simulate the maximum possible neighborhood of the assumed network. As a result, each node has exactly four neighbors, while collisions are expected to occur. The expectation regarding the performance of TiMAC is to accomplish the “at least one transmission per node per frame” goal, i.e., at least one transmission free of collisions. Note that transmissions may be unsuccessful for various reasons. For example, there might be interference in the 433 Mhz band, since the selected band is an ISM one and several devices placed near the system’s devices may also use it during the experiment. For avoiding as many such cases as possible, special care was taken to conduct the experiments in isolated areas (e.g., the basement of the premises of the University campus).
5.1. Methodology
As already mentioned, TiMAC is based on TDMA and, in this sense, its implementation is also based on TDMA. Considering the values deriving by the experimental system setup (i.e.,
nodes and maximum number of neighbors
), the corresponding values for
k (i.e.,
) and
q (i.e.,
) are extracted [
17]. As a result, first-degree polynomials are going to be used for the slot allocation due to
, and the length of the TDMA frame will be set at
, divided into five subframes of
slots each. Then, each node is randomly assigned a first-degree polynomial with coefficients from
and, according to the latter polynomial, the particular time slot during which each node is allowed to transmit within each sub-frame is derived. Eventually, every node is allowed to transmit in five slots per frame.
Eleven different sets of polynomials are considered here, corresponding to the eleven different scenarios developed for the particular system. Consequently, different time-slots were assigned to each node per scenario and the obtained results are the summation of transmissions of 100 frames. Note that increased traffic conditions are assumed for the experimental setup, and therefore each node has always data ready for transmission during every time slot. As for the receivers of transmitted packets, for each node, one of its neighbors is arbitrarily selected as the destination of the transmitted packets. The latter selection of receivers remains unchanged throughout the experiments.
The first set of polynomials is chosen in order to create a collision-free slot allocation scenario, such that each node transmits packets in different time-slots than that of its neighbors. The rest of the (ten) polynomial sets are created randomly.
The main parameter under investigation is the
throughput value each polynomial set (i.e., scenario) results to. The obtained throughput is derived as the fraction of the average successful transmissions (i.e., total successful transmissions over the number of nodes) over the number of total time-slots i.e.,
During the period of 100 frames, each node is eligible for transmission for up to 500 time-slots, whereas the number of total time-slots equals 2500. Consequently, the maximum network throughput is given by
Throughput as large as capacity is not expected to be achieved due to various reasons like the channel interference, the transmitter’s accuracy, and the receiver’s sensitivity, etc., as already mentioned. On the other hand, TiMAC guarantees that at least one successful transmission per node per frame will take place. Consequently, the minimum network throughput is given by
5.2. Results
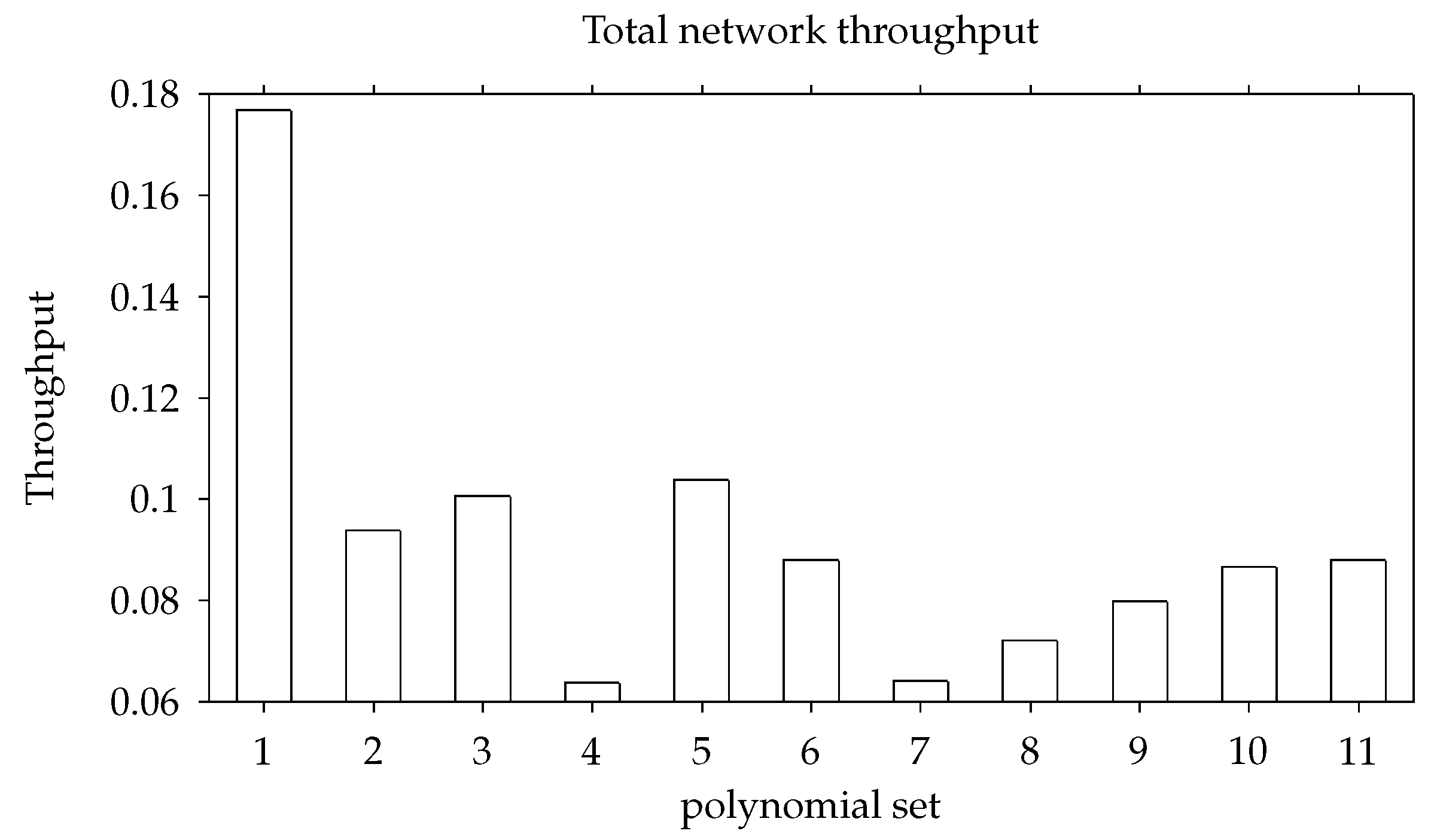
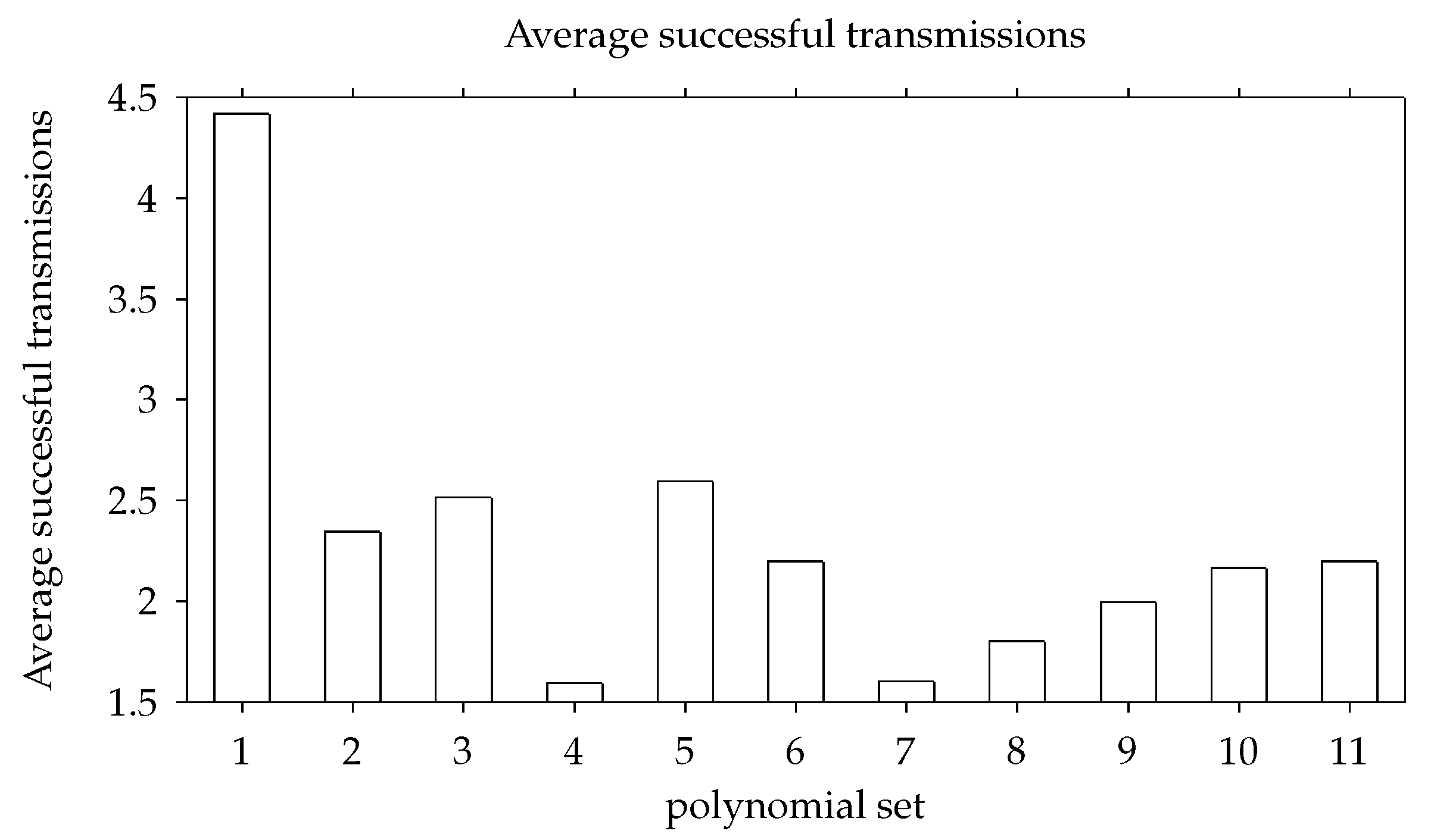
In
Figure 6, the derived values of throughput for the eleven polynomial sets are depicted. It is observed here that, in all cases, throughput is higher than the minimum value guaranteed by the TiMAC policy (i.e., 0.04). In addition, it is clear that the first polynomial set (scenario) results in the highest value of throughput; however, it is smaller than the maximum value (i.e., 0.2). The latter result is expected since, on the one hand, the particular set of polynomials leads to a collision-free slot allocation. On the other hand, the channel interference, transmitter’s accuracy, and receiver’s sensitivity may provoke unsuccessful transmissions.
Figure 7 depicts the average successful transmissions per frame per node for the eleven polynomial sets. The particular results confirm the TiMAC policy’s lower bound of one successful transmission per frame per node. For the first polynomial set, it is observed that the successful transmissions are significantly more than the successful transmissions in the other ten scenarios. However, they are less than the maximum theoretically expected value of five, which is the number of successful transmissions per node per frame in cases where no packets are lost for the duration of the 100 frames.
The particular polynomials used in each set are listed in
Table 1. Although the network topology remains unchanged throughout the experimental phase, each set leads to different number of successful transmissions.
The successful transmissions per polynomial set are listed in
Table 2. Each set’s sum of successful transmissions was used to derive the aforementioned throughput values.
6. Conclusions
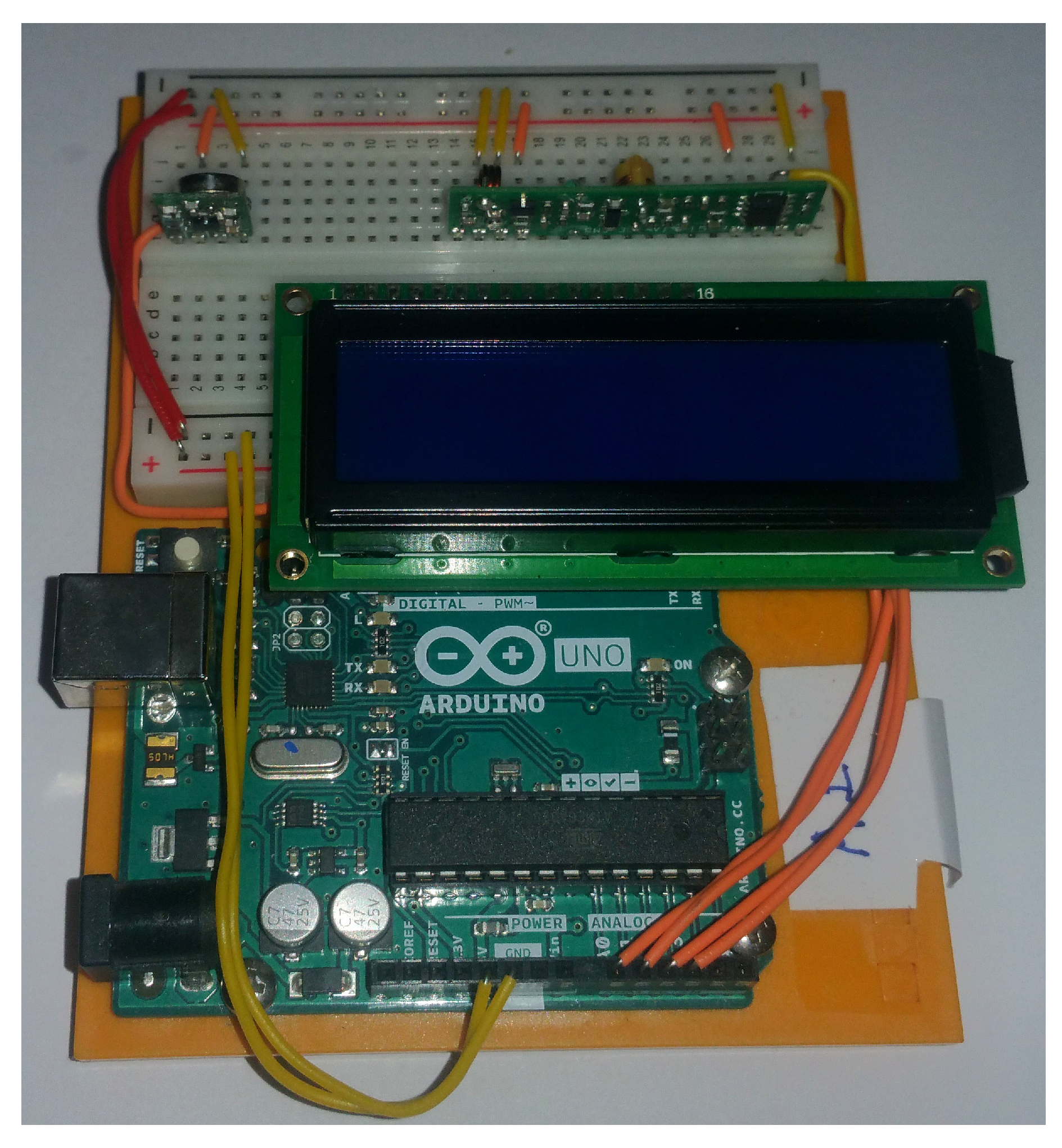
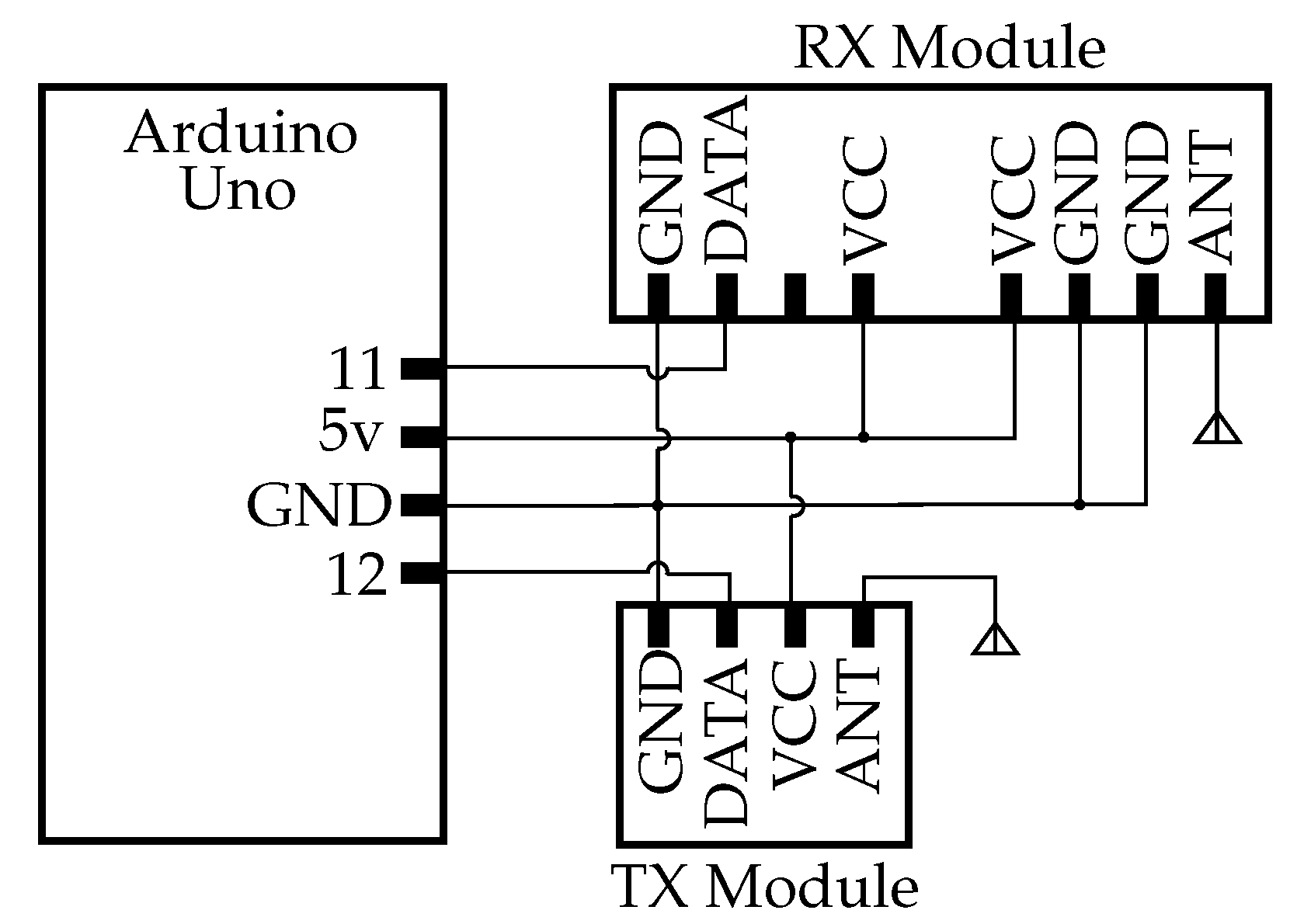
In this work, a MAC policy independent of the underlying topology (TiMAC) was implemented in a small IoT network consisting of low-cost devices based on Arduino and 433 MHz RF modules. A decentralized method was used for synchronizing the nodes’ clocks as required from the underlying TDMA policy. Experiments were conducted in a full graph topology network under increased network traffic load.
The conducted experiments confirm in practice the theoretical expectations from TiMAC as all of the results were within the expected boundaries in terms of throughput and successful transmissions per frame. These results suggest that policies that are independent of the underlying network topology could be considered when designing an IoT system, as they offer a means of node deployment without the usual considerations of traditional TDMA schemes (physical location combined with particular slot assignment), which could prove to be easier due to the nature of this type of networks and still could meet the strict time constraints of various delay-sensitive applications.
The decentralized synchronization method used here also proved to be successful. At the same time, the fact that a particular experimental setup was close to the theoretical maximum expected values suggests that the proposed policy can be improved if unique characteristics of particular polynomial sets are taken into account before assigning them to network nodes.
Future work should experiment with larger sensor networks so that TiMAC may be tested in multi-hop environment. Moreover, cybersecurity and resilience will have to be taken into account, as both of them are crucial parts of IoT, while their performance on low-cost devices is questionable.