1. Introduction
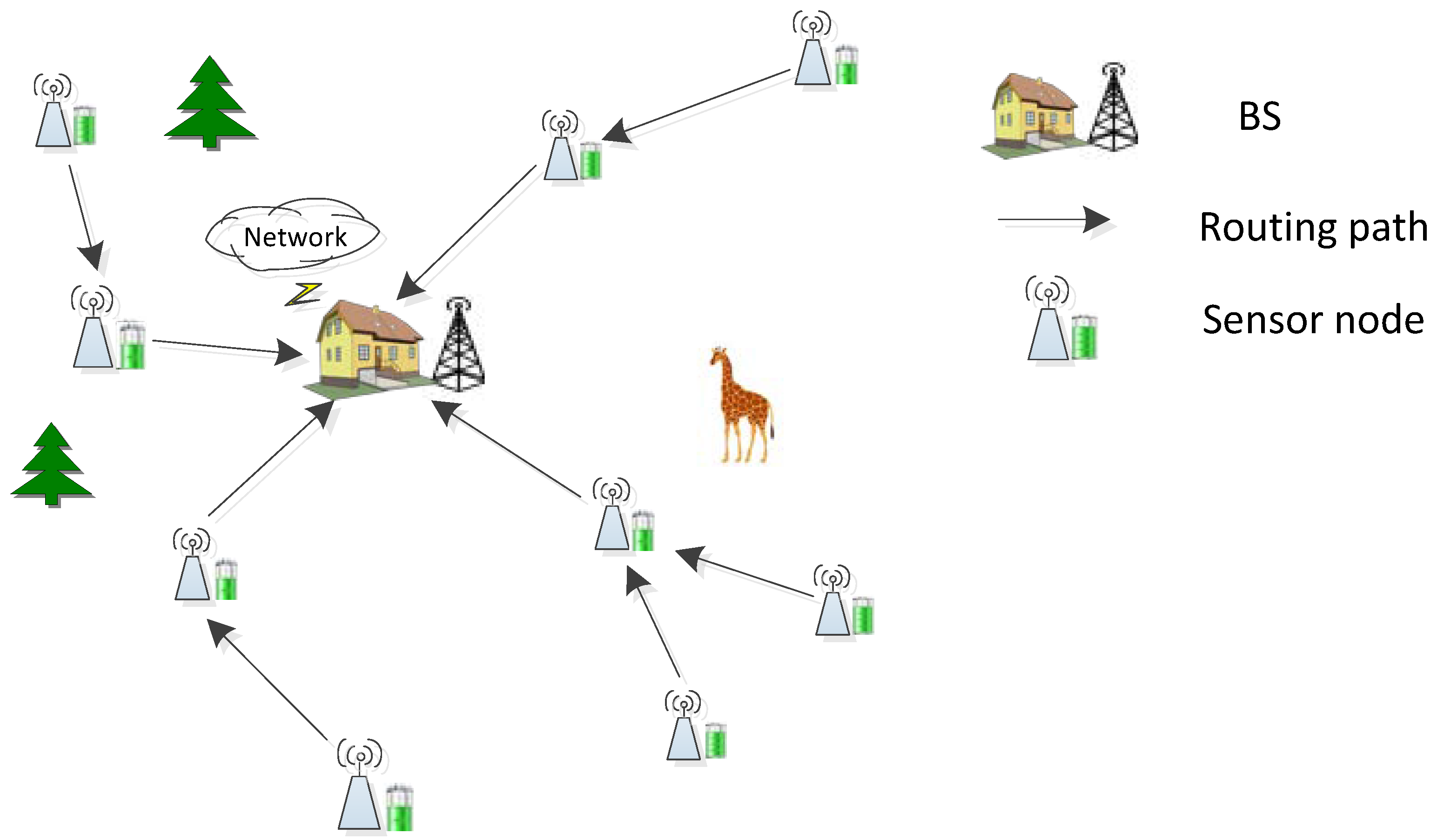
WSN-assisted IOT is used for data collection in the environment and detect the certain events of significance in the physical world. It can bring great convenience to people’s life [
1,
2,
3,
4], such as environmental monitoring, military tracking, and health observations. Sensor nodes send the sensed information to the base station (BS) by single hop or multi-hops. Therefore, the energy consumption and location deployment of the nodes can affect the network lifetime. The sensor nodes are generally powered by battery, which can only maintain a limited lifetime because of the limited energy, and the cost of replacing the battery is relatively expensive and hard to achieve. Numerous researches have shown that the energy consumption of nodes in WSNs is mainly in data transmission during routing [
5]. Therefore, how to design energy balanced and efficient routing algorithms to prolong network lifetime is the key to the development of WSN-assisted IOT.
There are a lot of existing routing protocols to extend the network lifetime, which are mainly divided into three aspects: (1) minimize the path energy consumption. Minimizing the path energy consumption is to save the energy of the entire network by adopting the shortest routing path or reducing path relay hops [
6]. (2) Balance the energy between nodes. This method tries to consume the energy of the nodes in the network as evenly as possible, thereby delaying the death of the first node and extending the network lifetime. (3) Transmission power control. To reduce energy consumption of data transmission, the methods of transmission power control measure and model RSS (received signal strength) to obtain optimal data transmission power, which is used to decrease channel interference among sensor nodes [
7,
8,
9]. However, once the path failure happens, the related nodes need to re-establish the network topology [
10].
Based on the above observations, in order to balance and efficiently utilize energy to extend the network lifetime, we propose an energy-balanced routing algorithm for network lifetime enhancement (EBRA-NLE) based on DS evidence theory [
11]. DS evidence theory can fuse multiple attributes according to DS fusion rules and make the optimal choice, so it is applied to our routing selection for WSNs. Our main contributions are summarized as follows:
In WSN, many previous researches on DS evidence theory mainly focus on data fusion to enhance the reliability and security of information acquisition, but the application of indexes fusion in sensor nodes as a routing decision-making method is very few. In this paper, we adopt DS fusion rules to fuse three attribute indexes that affecting energy balance and energy efficiency of each node.
First, the node’s forward neighboring nodes are taken as the evaluation object, and three indexes are established as evaluation objects from the perspective of energy balance, minimization of path energy consumption, and buffer proportion. It should be noted that, in order to reflect the importance of each index according to the difference in attributes between nodes, a sine function is adopted to map the belief function corresponding to each index. Then DS fusion rule is utilized to comprehensively evaluate the indexes of each node to obtain the optimal path selection.
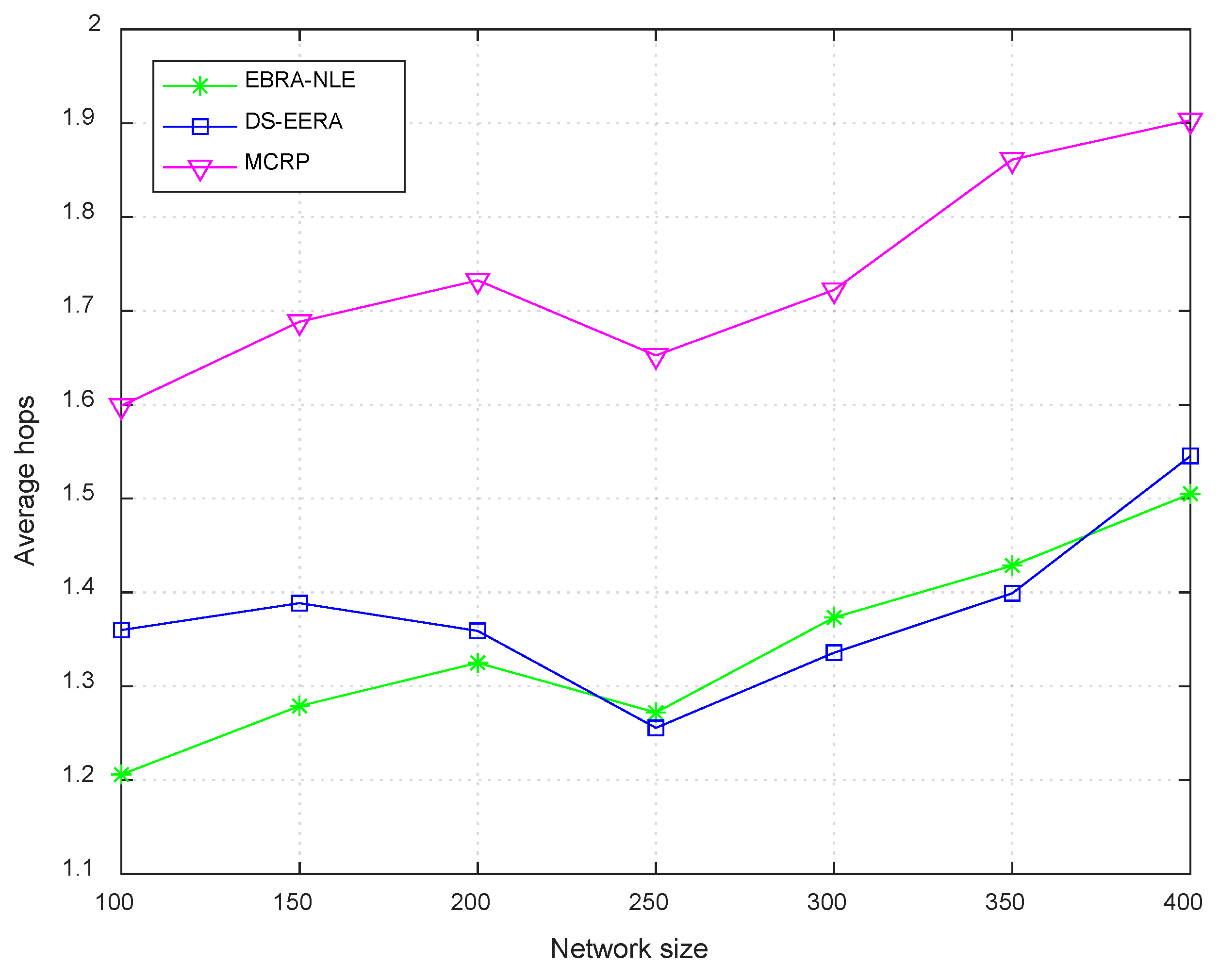
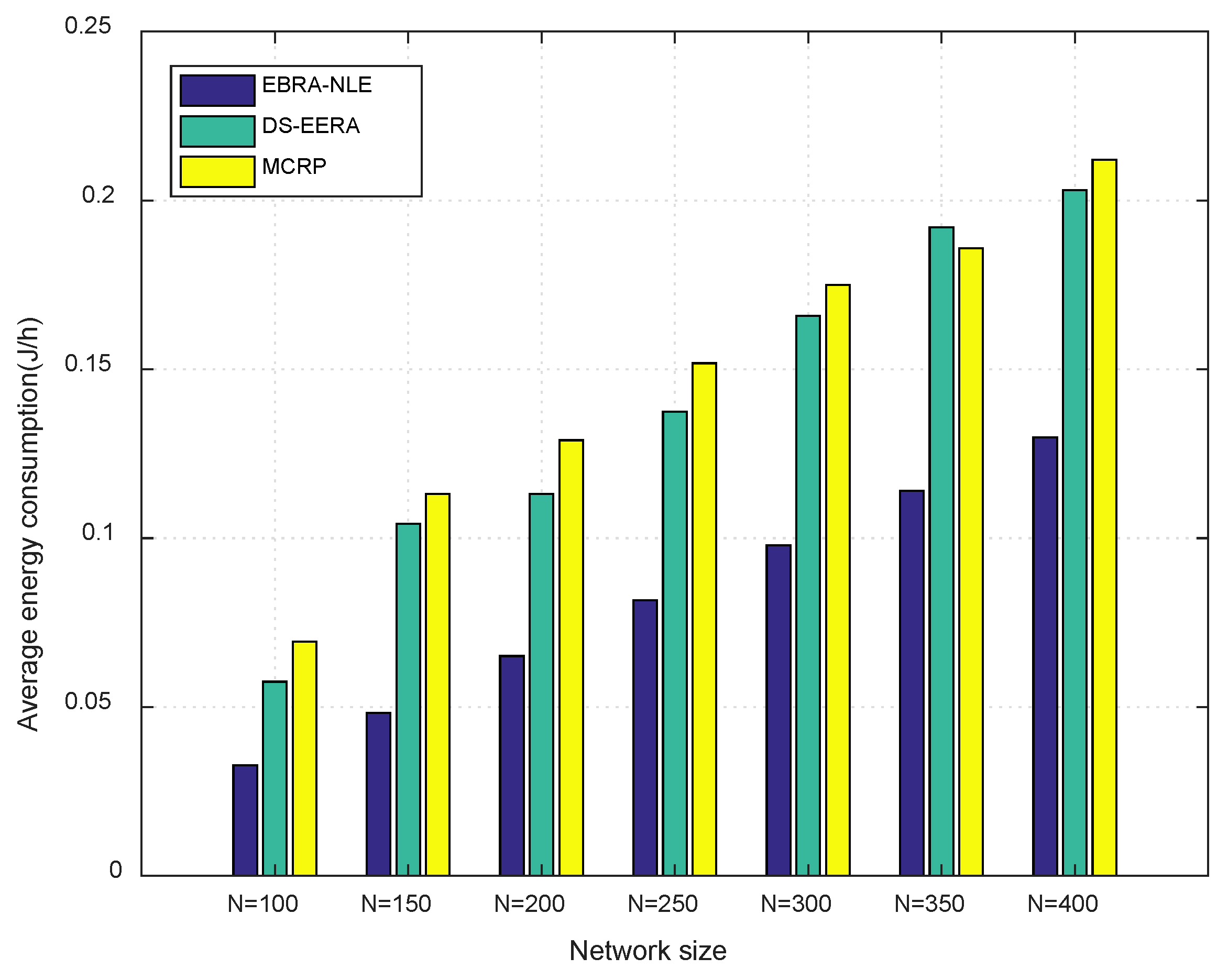
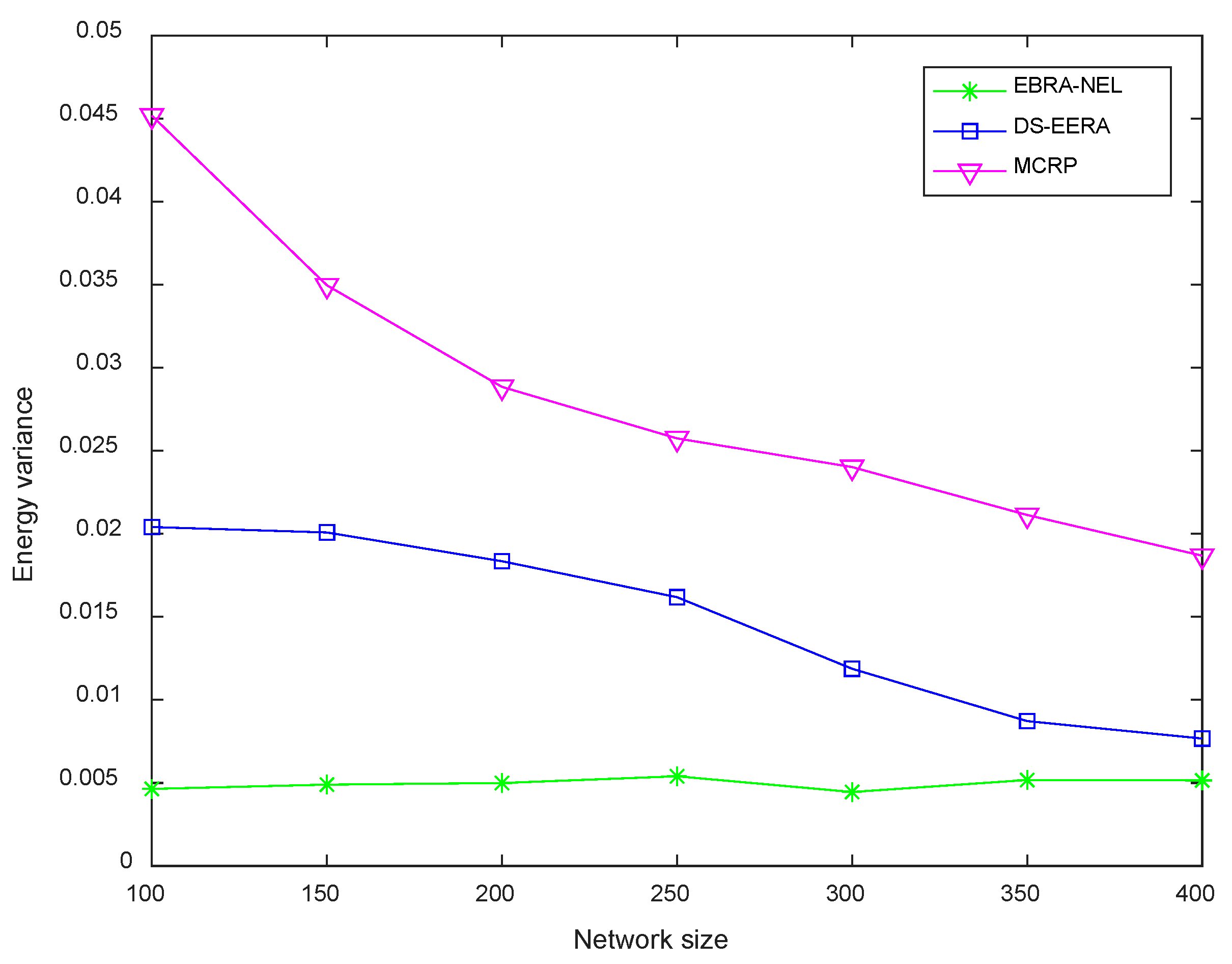
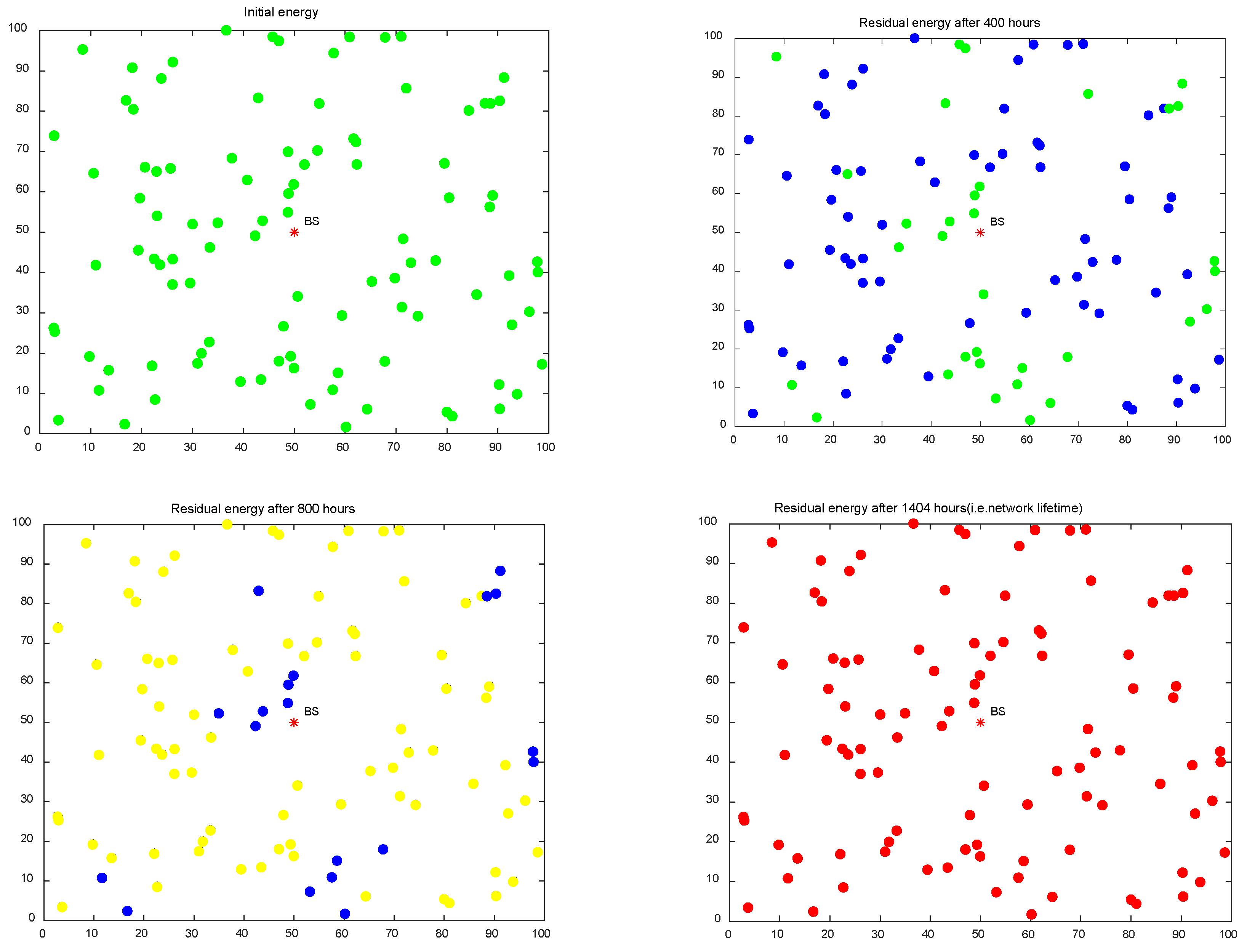
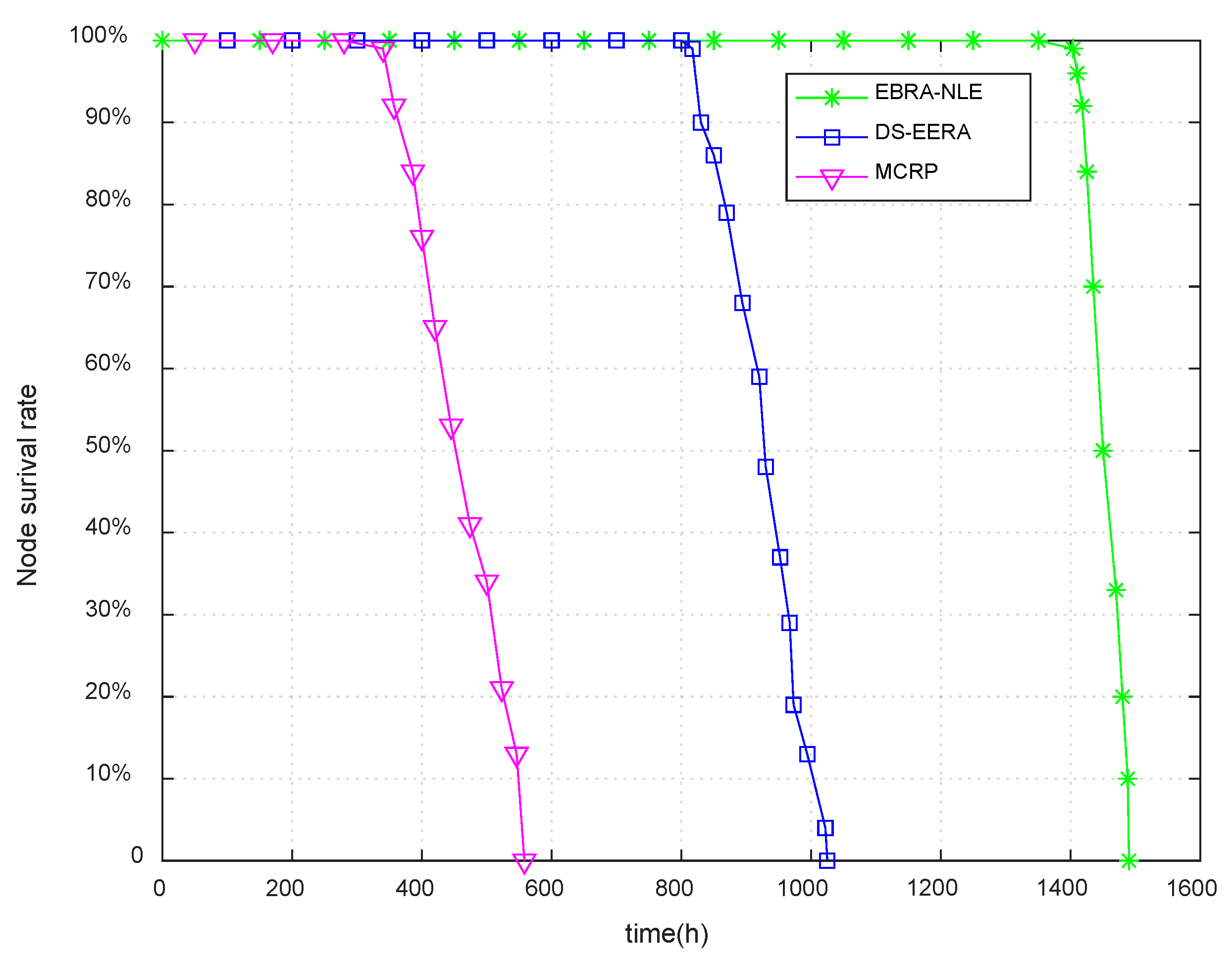
Simulation results show that the proposed EBRA-NLE has certain advantages in prolonging network lifetime and balancing energy between nodes. In addition, the network lifetime obtained by EBRA-NLE is improved about 313% and 72% more than that of MCRP and DS-EERA algorithm respectively.
The rest of the paper is organized as follows:
Section 2 reviews the related research works. The system model is introduced in
Section 3. The EBRA-NLE algorithm is presented in detail in
Section 4. The relevant simulation results are analyzed and discussed in
Section 5. Finally, the conclusion is summarized in
Section 6.
2. Related Works
For these energy saving algorithms of minimizing the energy consumption [
12,
13,
14], some routing strategies establish the shortest path from the source node to the destination, so that the path energy consumption in data transmission is the lowest. Among them, a ladder diffusion algorithm based on ACO (ant colony optimization) is proposed to solve the problem of energy consumption in routing [
12], which mainly employed ACO mechanism to effectively reduce path energy consumption. Although the shortest path can reduce the energy consumption of data transmission, it is easy to cause the energy imbalance between nodes because of the lack of consideration of residual energy, which leads to the death of some key nodes because of the premature depletion of energy. In addition, a routing algorithm named dynamic optimal progress routing (DOPR) uses a hybrid routing-mobility strategy to guarantee message delivery [
13], it moves the intermediate nodes on the selected path to proper positions to reduce the energy consumption of nodes. Bouabdallah et al. [
14] put forward SCMR routing algorithm. The SCMR adopts active reporting node selection mechanism of correlation radius, which can inhibit the data transmission of redundant nodes, thus reducing network energy consumption.
In terms of extending the network lifetime by balancing the residual energy between nodes [
15,
16,
17,
18,
19,
20,
21], Behzadan et al. in [
15] proposed a distributed ED balanced based on a theoretic heterogeneous balanced data routing (HBDR) algorithm for routing, while the inter-node interference was not be considered. Petrioli et al. [
16] presented distributed GRP and localized ALBA-R for balancing traffic load of nodes that are located around connectivity holes so that the nodes do not run out of energy too fast. Mehmmood et al. [
17] developed an algorithm that the nodes consume their energy balanced by both region and node level. In this protocol, the evolutionary game theory (EGT) and classical game theory (CGT) are used to balance the traffic load. Gupta and Jha proposed an improved energy balance clustering protocol based on cuckoo search [
18], which adopts an objective function to evenly distribute cluster heads. Then use the cuckoo search algorithm to optimize the data transmission of the cluster head and the destination node, and finally get the purpose of energy saving to improve energy efficiency. However, these algorithms do not fully consider some important attributes of the node when selecting the next hop, such as traffic. As a result, some performance of the nodes is poor.
Therefore, some algorithms consider multiple attributes of nodes to make a comprehensive route selection [
19,
20,
21,
22]. Among them, MCRP [
19] sort multiple network attribute matrices to obtain the optimal solution by TOPSIS method. Nevertheless, adopting the TOPSIS can only reflect the relative closeness of each attribute to its own ideal solution, which does not reflect the closeness to the overall ideal solution. Tang et al. [
22] proposed a routing algorithm based on DS evidence theory, which uses DS evidence fusion rules to fuse the attribute indexes of nodes, and selects the best next hop according to the fusion results. Although this method can balance the energy between nodes to a certain extent, the triangular membership function is adopted in the establishment of the belief function, which may lead to too much pursuit of the ideal solution of each index so as to miss the optimal fusion result.
In addition, some methods can solve the energy hole problem by adjusting the data transmission power [
7,
8,
9], so that the energy consumption of the whole network can be minimized and balanced. Fei et al. [
7] proposed a coordinated transmission strategy, which solves the problem of network lifetime maximization and energy minimization through two different simultaneous interpreting strategies. Zeng et al. [
9] presented an algorithm to avoid the “energy hole” problem with adjustable transmit power based on the distribution of network energy consumption, the lifetime of regional nodes, and the real-time data. Thus in order to prolong the network lifetime, the algorithm sends the corresponding proportion of data to the area with low energy consumption in a short communication radius. The energy hole can be alleviated by changing the transmission power to some extent, but it is difficult to determine the value of the adjustable transmission power, so it is difficult to apply it to the actual sensor networks.
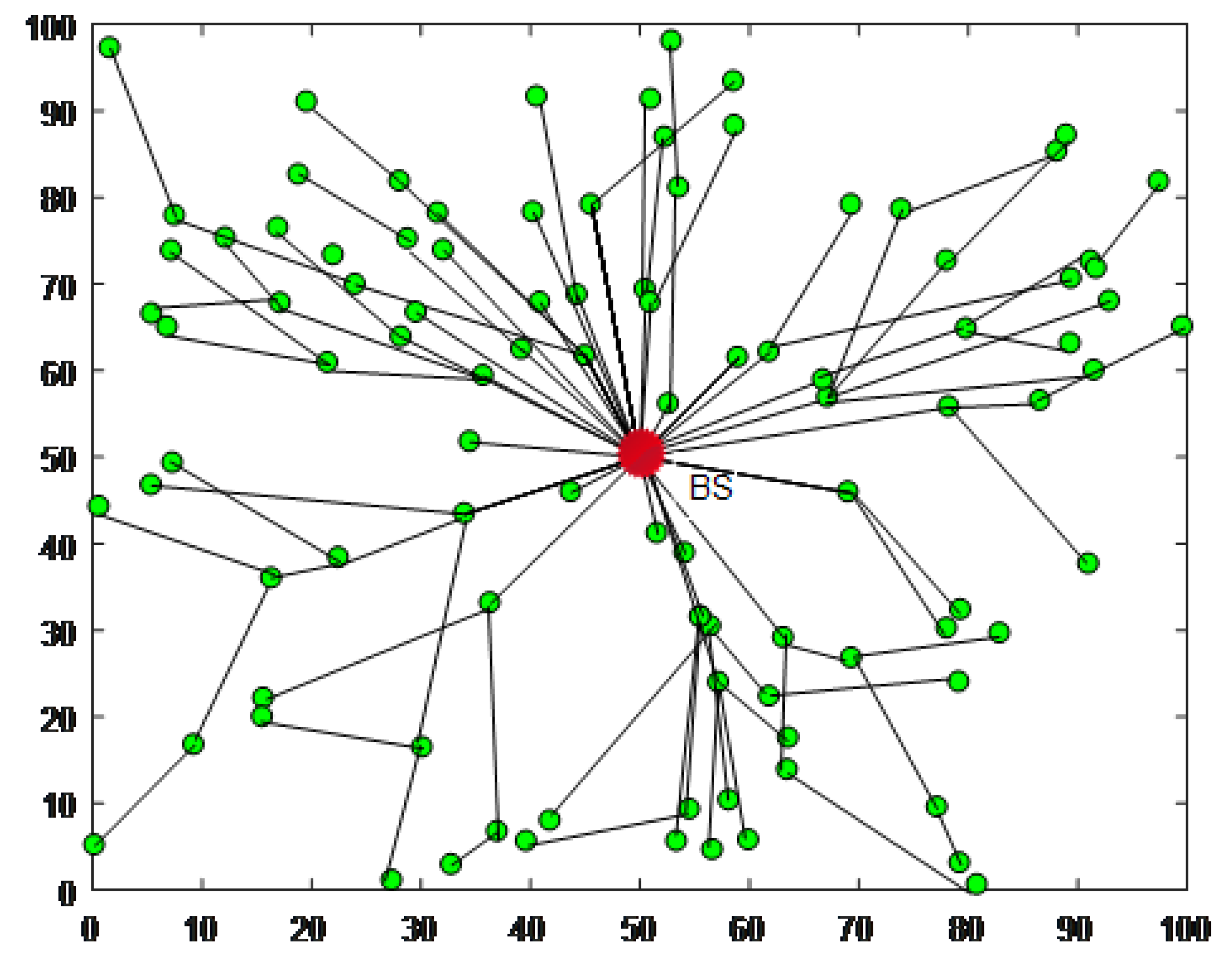
4. EBRA-NLE: DS Evidence Theory-Based Energy Balanced Routing Algorithm for Network Lifetime Enhancement
DS evidence theory was proposed by Dempster Shafer in 1970s [
11], which can fuse multiple information and its fusion results are in line with people’s thinking habits. Therefore, DS evidence theory is widely used in artificial intelligence, detection, and diagnosis etc., [
25]. DS evidence theory establishes a one-to-one correspondence between propositions and sets, which can transform the uncertainty of propositions into the uncertainty of sets. In this paper, we apply DS evidence theory to routing selection in WSNs. First of all, we consider the residual energy of nodes, the shortest data transmission path and the buffer proportion, so as to establish “energy balance factor,” “relay coefficient,” and “buffer idleness” as the evidences of DS fusion rules. Then DS fusion rules are applied to fuse the three indexes of corresponding belief function, thus the results of comprehensive evaluation are obtained. It should be noted that the belief function is obtained by sinusoidal mapping of membership function, so as to reflect the importance of each index in the fusion process and make the optimal routing objectively.
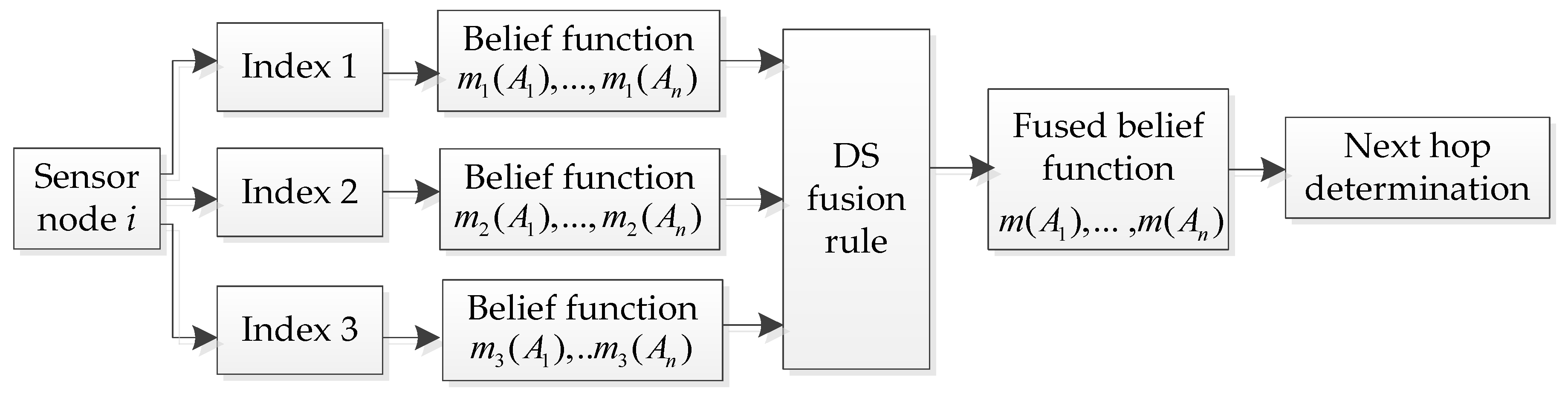
DS evidence theory is an effective method to fuse subjective uncertainty information, and its fusion decision process [
26] is shown in
Figure 2. Where
is the number of forward neighboring nodes of node
, that is
.
is the belief allocation of
forward neighbors under different index
.
is the fused belief allocation of
propositions of node
. When calculating the probability allocation of each neighbor, it is necessary to establish attribute indexes of evaluation nodes, which will be described in the next section.
4.1. The Establishment of Attribute Indexes
4.1.1. Energy Balance Factor
Since the main energy consumption of sensor nodes is used for data transmission, the key to prolong the network lifetime is to balance the energy consumption of each source node
and its next hop. From the perspective of the source node
, when its residual energy
is small, the energy consumption
of single hop transmission is expected to be as small as possible. When the energy of node
is large, it is hoped that node
can transmit a longer distance, that is, the value of
is as large as possible. Therefore, considering the residual energy of the node
and the energy consumption of data transmission, the energy balance factor is defined as follows:
where
denotes the energy consumption of data transmission from node
to node
,
represents the energy consumption of data transmission at the longest transmission distance
.
4.1.2. Relay Coefficient
During data transmission, the closer the forward neighboring node
is to the shortest path from the node
to the BS, the more energy can be saved in the routing path. Meanwhile, the more residual energy of the node
, the more data can be forwarded to it. Thus the relay coefficient is defined as follows:
4.1.3. Buffer Idleness
Because the data transmission in WSNs has the characteristics of “many to one”, it may lead to numerous traffic data converging to some key nodes at the same time. It may run out of energy prematurely because of the overload and reduce the network lifetime. Thus these nodes discard data because of limited buffer, which will affect the reliability of data transmission. Therefore, the buffer idleness is established to measure the ability of nodes to receive data, which is expressed as follows:
where
is the current traffic data of node
,
is the traffic flowing into the node
,
is the traffic flowing out of the node
, and
is the maximum buffer length of each node.
4.2. Acquisition of Belief Function
4.2.1. Sine Mapping Based Membership Function
The acquisition of belief function is based on membership function, so this section first introduces the establishment process of the membership function. For each node , the three attribute indexes of its forward neighbor node are presented as , which correspond to the index . All three are benefit indexes, that is, the larger the index value, the more likely it is to be selected as the next hop. The three indexes value of each forward neighbor node can be calculated, and the maximum value of each index is the optimal solution under this index. That is, , and .
In order to avoid missing the node with the best comprehensive performance due to excessive pursuit of ideal solution, we establish the membership function based on sine function, its expression is as follows:
where
.
The mapping relationship is shown in
Figure 3.
4.2.2. Belief Function
The domain of evidence theory is called recognition framework
, which includes a limited number of propositions and are recorded as
. It corresponds to the basic event in probability theory, which is called focal element. In this paper, it corresponds to the forward neighboring nodes of each node. The propositions in
are mutually exclusive. The calculation of belief function is referred to [
26,
27], and this paper also makes the following relevant definitions as follows:
Definition 1. Supposeis the recognition framework. If the set function:(is the power set of) satisfy:whereis called the belief function allocation on recognition framework.
is the empty set. For,is called the belief function value of. When,is called the focal element on the allocation of belief function, that is, the reliability of a node selected as the next hop. Definition 2. whereis the three indexes (),is the number of forward neighbors of node.
andare fixed values for the sensor network.is the weighted coefficient of the index. In this paper, .
is the correlation coefficient of the attribute indexto each forward neighboring node.,,are denote the maximum correlation coefficient, the correlation allocation value and the reliability coefficient of the index. In this paper, the membership function
in fuzzy theory is used to replace the correlation coefficient
[
26], both of which can be used to evaluate the trust degree belonging to the next hop based on the value of the indexes of the forward neighboring nodes. Thus, the correlation coefficient of the index
is
. Bringing
into above equations, thus
,
,
of the forward neighboring node
at the index
can be obtained.
Then, the belief function
of the index
to the proposition
corresponding to the forward neighbor node
can be obtained as follows:
The function of uncertainty reliability
under index
is:
It can be seen from Equations (14) and (15) that weighted coefficient and the correction coefficient have certain subjectivity, which is determined by field experience and sensor characteristics.
4.3. The DS Fusion Rules of Indexes and the Routing Path Section
4.3.1. DS Fusion Rules
According to the fusion rule [
26] of DS evidence theory, all forward neighboring nodes
in
are regarded as the propositions
. First, take two indexes (that is
) as an example, let
respectively correspond to the belief function assignment of two different indexes. Then, the allocation of the combined belief function is defined as follows:
where
is the sum of all belief products including complete conflict hypothesis,
is the belief products of non-conflict hypothesis. Conflict hypothesis means that
and
cannot exist at the same time, that is, they are mutually exclusive in the
. The belief function value
refers to the sum of all the reliability products of
and
, which contain the non-conflict hypothesis.
The uncertainty function values of fusion results are calculated as follows:
After the fusion of index 1 and index 2 is assigned to the belief function value of each forward neighboring node, the fusion result is taken as the belief function of the new index. Then the fusion result is obtained by the fusion with index 3 according to the Equations (16) and (18).
4.3.2. Path Selection Principle
In order to avoid the counter-intuitive and conflict results in the next hop selection, the routing decisions generally follow the following principles:
The next hop selected should have the largest belief function value and be greater than a certain threshold.
The difference of the belief function between the next hop and other forward neighbors is greater than a certain threshold value.
The belief function value of the selected next hop is greater than its uncertainty function value.
The determination of the corresponding threshold is adjusted according to specific experimental scenarios. Then find with that satisfy the path selection principle and regard the node (denoted by proposition ) as the optimal next hop of node . Finally, according to this routing selection rules, all nodes in the network can get an energy balanced data transmission path from the source nodes to BS.
In order to facilitate the reader’s understanding, the routing process is formed into Algorithm 1.
| Algorithm 1. The routing path selection. |
| Input: Node |
| Output: The next hope J |
| 1. for i = 1:N do |
| 2.
|
| 3. for j = 1:n do |
| 4. Calculate by Equations (5)–(7) |
| 5. end for |
| 6. , Calculate by Equation (8) |
| 7.
, Calculate by Equation (8) |
| 8.
, Calculate by Equation (8) |
| 9.
|
| 10. Obtain by Equation (14),(15) |
| 11. by Equation (16) and calculate by Equation (18) |
| 12. by Equation (16) and calculate by Equation (18) |
| 13. Find J with that satisfy the path aelection principle |
| 14. Regard J as next hop of node i |
| 15. end for |
| 16. Return J |
4.4. The Time Complexity of EBRA-NLE
In our proposed EBRA-NLE, is the number of sensor nodes in the network, is the set of forward neighboring node of node . is the number of , that is, . In addition, the number of forward neighbors of each node is different, so is usually an indefinite value much less than . In order to avoid confusion between and , here set .
At first, calculate the three indexes values of nodes’ forward neighbors and convert them into corresponding membership function through the sine mapping function, which generally requires calculation complexity of (). Therefore, the time complexity required to calculate the belief function of three indexes by the membership function is also . In the stage of data fusion by adopting DS rules, three attribute indexes need to be fused twice. For proposition in each fusion, the complexity of conflict hypothesis is () and the complexity of the allocation for the fused belief function is (). For example, the belief function of in one fusion process is:. Therefore, the time complexity of DS data fusion is .
To sum up, the time complexity of our proposed algorithm is usually . In the worst case, the number of forward neighbors of each node is nearly , and then the worst time complexity is .
6. Conclusions
In this paper, in order to efficiently manage the energy of WSN-assisted IoT by considering energy balance and energy consumption minimization, a routing algorithm called energy balanced routing algorithm for network lifetime enhancement (EBRA-NLE) is proposed. Three attribute indexes are established as criterion to evaluate the forward neighboring nodes. Then we innovatively introduced a DS evidence theory-based routing algorithm to select the optimal routing path for each node. Simulation results assert the effectiveness of the proposed EBRA-NLE on enhancing the energy balance and network lifetime. The network lifetime obtained by EBRA-NLE is improved about 313% and 72% more than that of MCRP and DS-EERA algorithm respectively.
In future works, we aim to evaluate our proposed approach in the rechargeable sensor networks and combined with some energy harvest methods to further extend the network lifetime of WSN-assisted IOT.