1. Introduction
Legacy power systems are transforming into smart grids which are designed to operate in a more reliable and resilient fashion. Existing Supervisory Control and Data Acquisition (SCADA) systems do not have the capability to implement these features [
1]. Substations play a key role in smart grid revolution. IEC 61850 is a de-facto standard for substation automation [
2]. It offers different protocol services such Generic Object-Oriented Substation Event (GOOSE), Sample Value (SV) and Manufacturing Message Service (MMS) [
2]. It enables interoperability among substation devices of different vendors with standard modeling. It also offers many services that include seamless communication, defining data sets, defining logical nodes for substation communication equipment [
3].
IEC 61850 standard was initially developed for substation automation. Due to its widespread popularity and success, it was extended to other components in power grids such as fault current limiters [
4], Distributed Energy Resources (DERs) [
5], Electric Vehicles (EVs) [
6] and smart meters [
7]. In these new implementations, IEC 61850 GOOSE and SV are utilized to exchange different data sets between DERs, EVs and other components. Some researchers have developed open access tools for generating GOOSE and SV messages, which are quite helpful in conducting different studies [
8,
9,
10]. However, the reported tools only use datasets based on IEC 61850-9-2 LE SV format (only include three-phase current and voltages values) or GOOSE formats. Addressing this knowledge gap; in this paper, a C based framework ‘GoSV’ [
11] is developed for generating custom GOOSE and SV messages which can be used to send customized data sets in GOOSE and SV formats.
Cyber security is a rising concern for substation communication networks [
12,
13,
14] and phasor measurement units [
15] as reported in the literature recently. Authors in [
12], proposed Anomaly Detection System (ADS) for the substations to protect simultaneous intrusions into multiple substations which may cause severe cascading events that have catastrophic consequences. Authors in [
14] reviewed cyber security challenges and potential threats in IEC 61850-substation network and summarized security measures. They argue that among different IEC 61850 services such as GOOSE, SV and MMS, GOOSE message service is of paramount importance as it carries time critical information related to power system operation. If GOOSE message service is compromised, then it may cause severe loss to power system. To address these concerns, IEC 62351-6 specifies security mechanisms for GOOSE message service [
16]. The security requirements such as authentication and integrity are very important in IEC 61850 substation networks and IEC 62351-6 recommends digital signatures to mitigate cyber-attacks. Furthermore, the said standard specifies RSA digital signature algorithm for signing and verifying the GOOSE messages. The timing performance of the specified digital signature is evaluated and reported in [
17,
18]. Authors in [
19] specify that the actual digital signature algorithm explicitly specified by IEC 62351-6 to secure GOOSE is RSA-Probabilistic Signature Scheme based on Signature Scheme with Appendix (RSASSA-PSS) based on RFC 3447 [
20], which should be also compatible with RFC 2313 [
21].
In order to investigate cybersecurity considerations in power system communication networks, this paper extends the GoSV framework with security implementations as Secure-GoSV (S-GoSV) [
22] using openSSL libraries. In S-GoSV framework RSASSA-PKCS1-v1_5 digital signature algorithm is implemented to secure IEC 61850 GOOSE messages. However, investigations show that performance of RSASSA-PKCS1_v1-5 digital signature algorithm is not suitable for time critical GOOSE messages [
19]. Therefore, authors have proposed the use of fast computing Message Authentication Code (MAC) based digital signature algorithm, Hash based Message Authentication Code- Secure Hash Algorithm (HMAC-SHA-256) [
23]. HMAC-SHA-256 based implementations are also included in the S-GoSV framework for studying their performance.
The rest of the paper is organized as follows,
Section 2 discusses GOOSE and SV message structures according to IEC 61850-8-1 and IEC 61850-9-2 standards, respectively. It also shows implementation details of GoSV software framework that generates custom GOOSE and Sample Values.
Section 3 briefly discusses S-GoSV software that implements RSASSA-PKCS1-v1_5 digital algorithm specified by IEC 62351-6.
Section 4 describes the implementation details of RSASSA-PKCS1-v1_5 digital algorithm and HMAC-SHA256 on GOOSE messages.
Section 5 demonstrates the results with Wireshark captures.
Section 5 draws the conclusions.
2. GoSV Framework
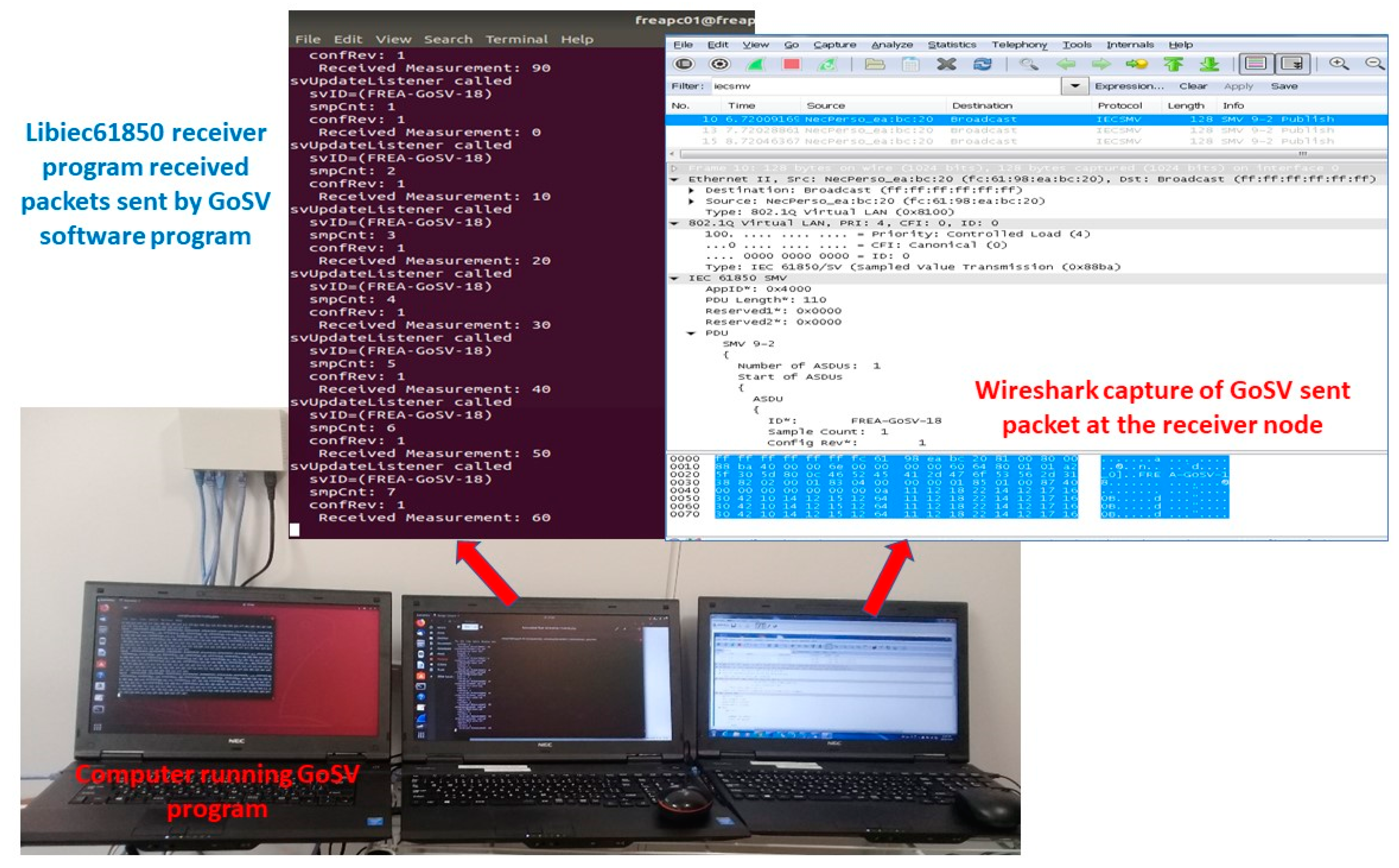
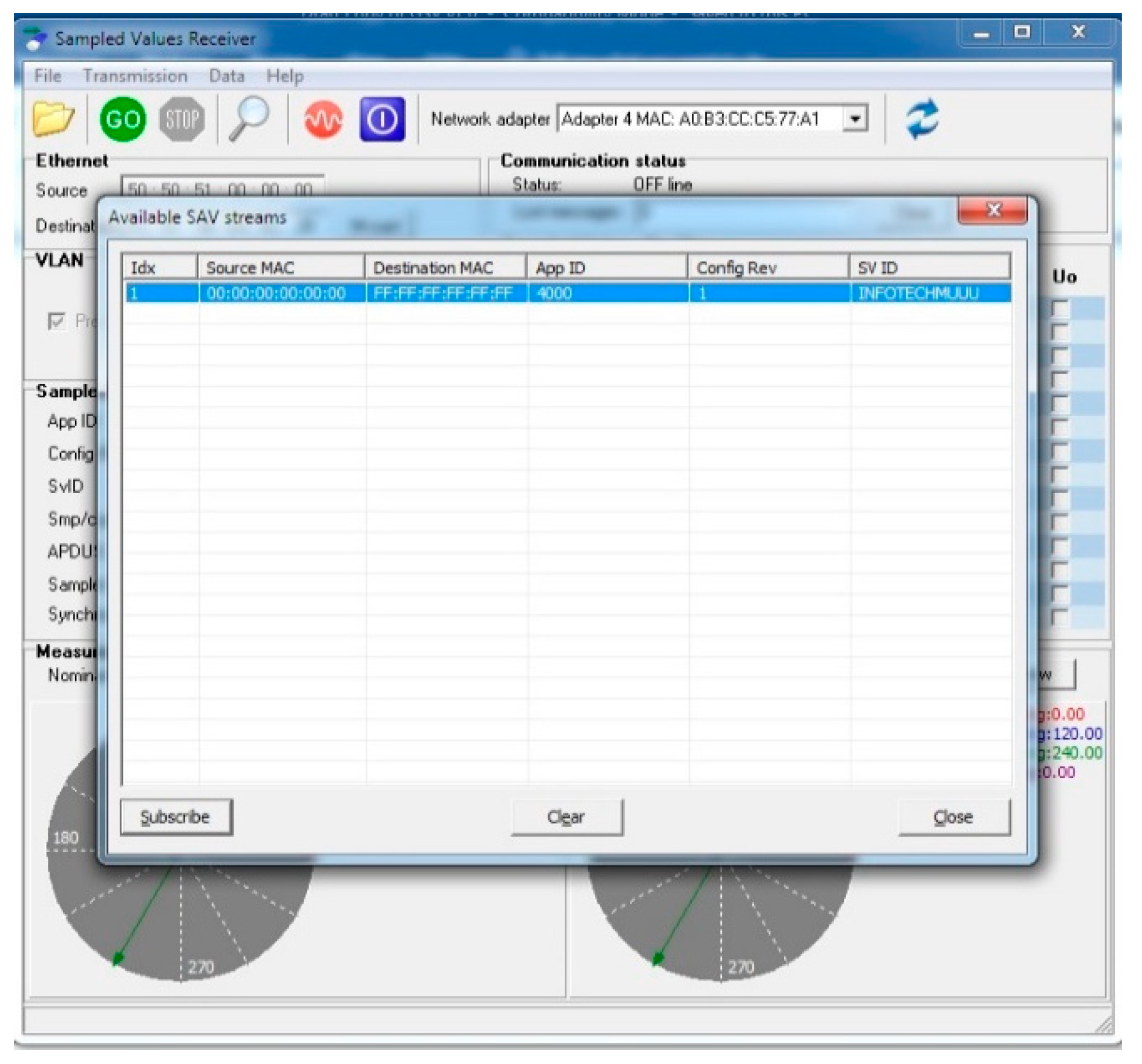
The GoSV framework is developed for generating and publishing customized GOOSE and SV messages. The crucial part of this framework is to accurately construct Ethernet frame according to IEC 61850-9-2 (Sample Values) and IEC 61850-8-1 (GOOSE) formats.
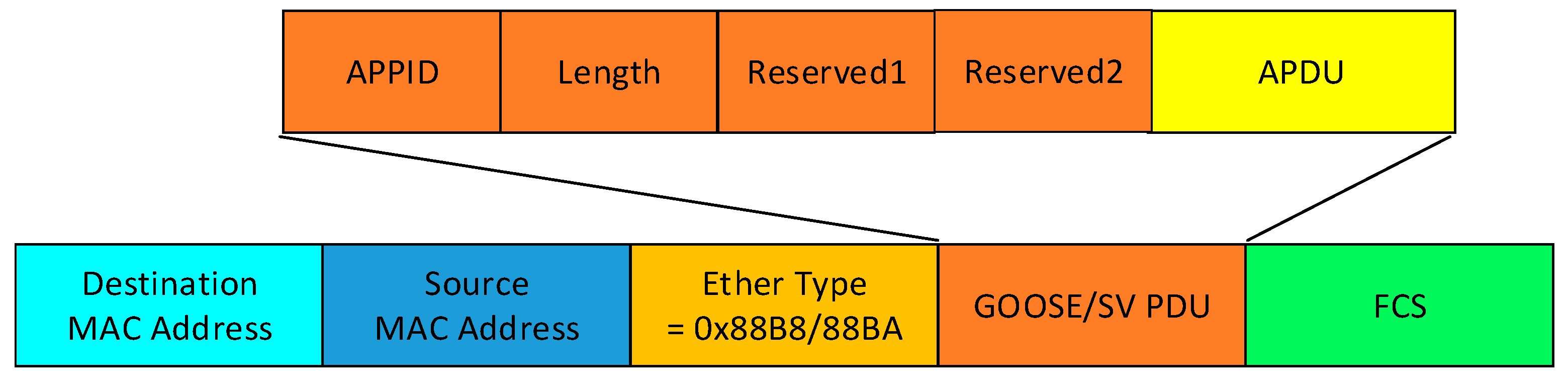
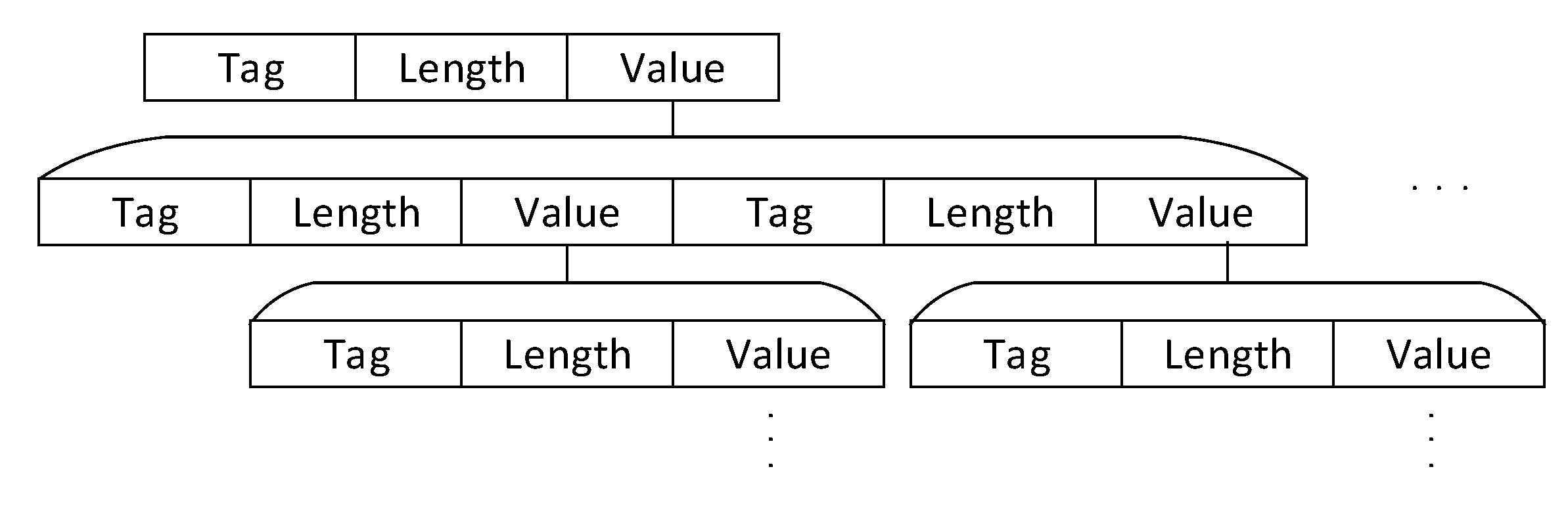
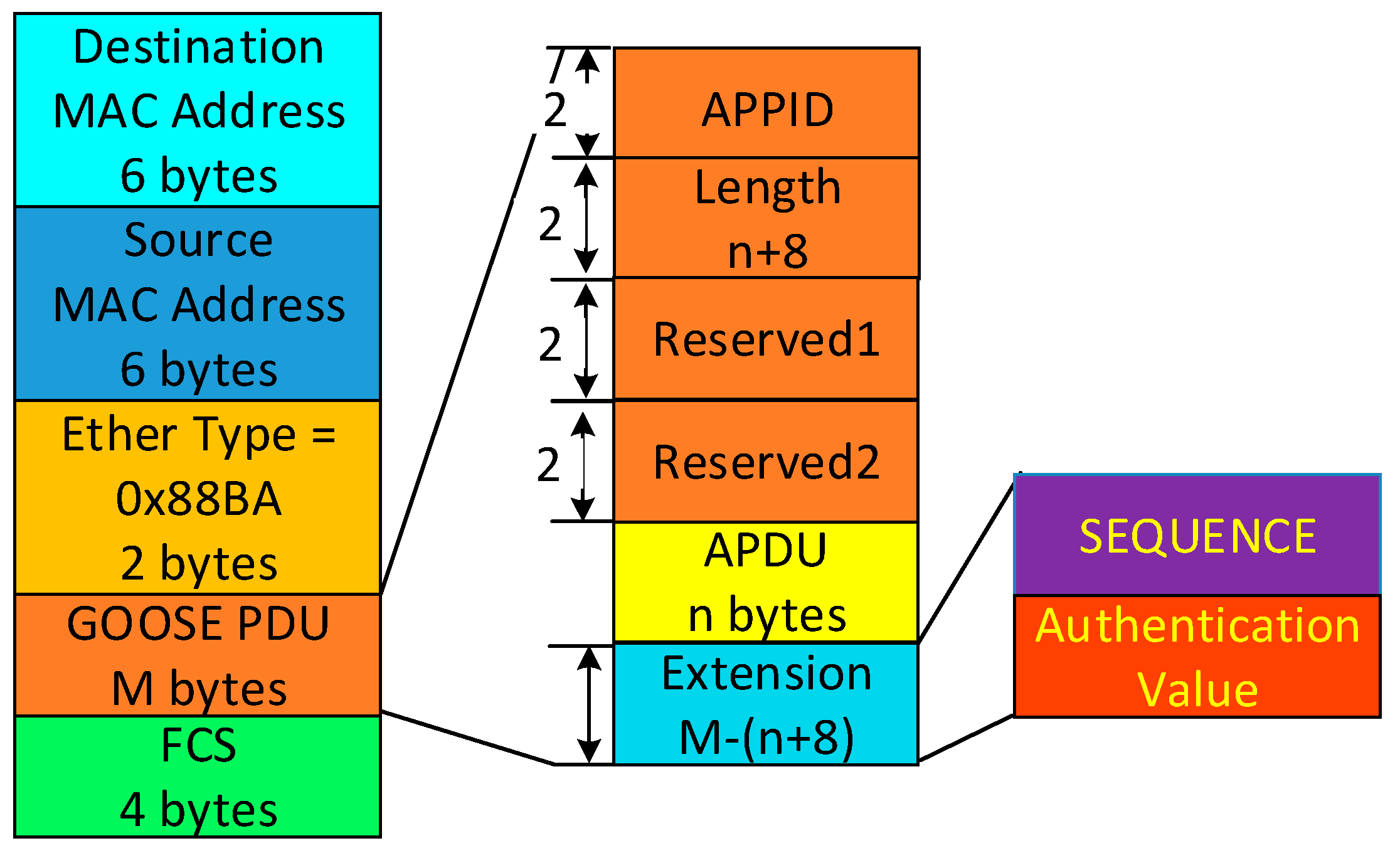
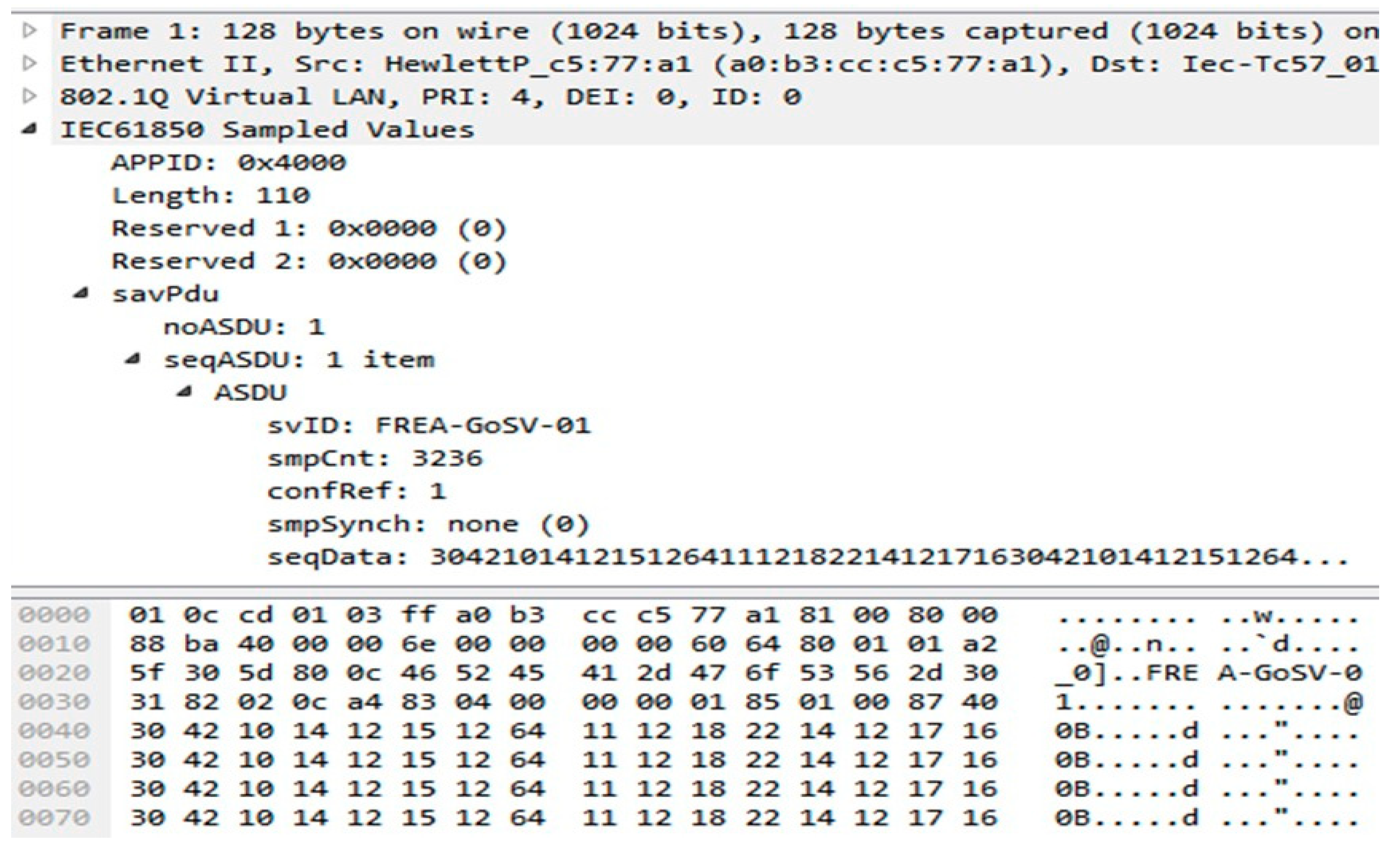
Figure 1 shows the ethernet frame and its fields. The Ethernet frame format starts with destination and source MAC address followed by 802.1q and 802.1p (VLAN and priority tag) optional fields. The next field is ‘ethertype’ which defines the Ethertype Protocol Data unit (PDU) in the frame. The value of the ‘ethertype’ field for GOOSE and SV messages are 0x88-0xB8 and 0x88-0xBA, respectively. All the fields of ‘Ethertype PDU’ are encoded according to ASN.1 BER as specified in ISO/IEC 8825-1. All the fields are in triplet format of Tag, Length and Value (TLV). Again, the value can contain a new set of triplets in itself as shown in
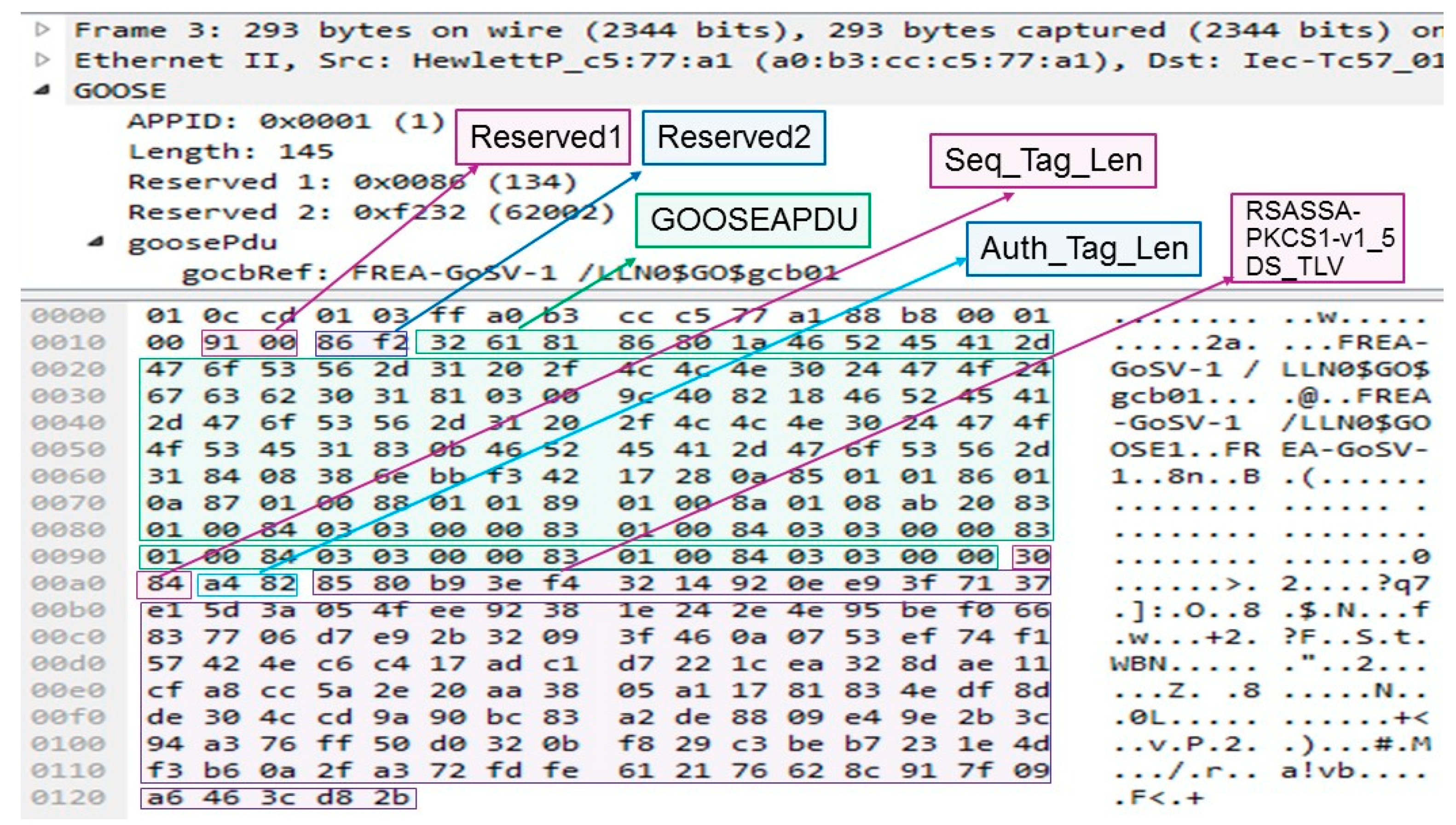
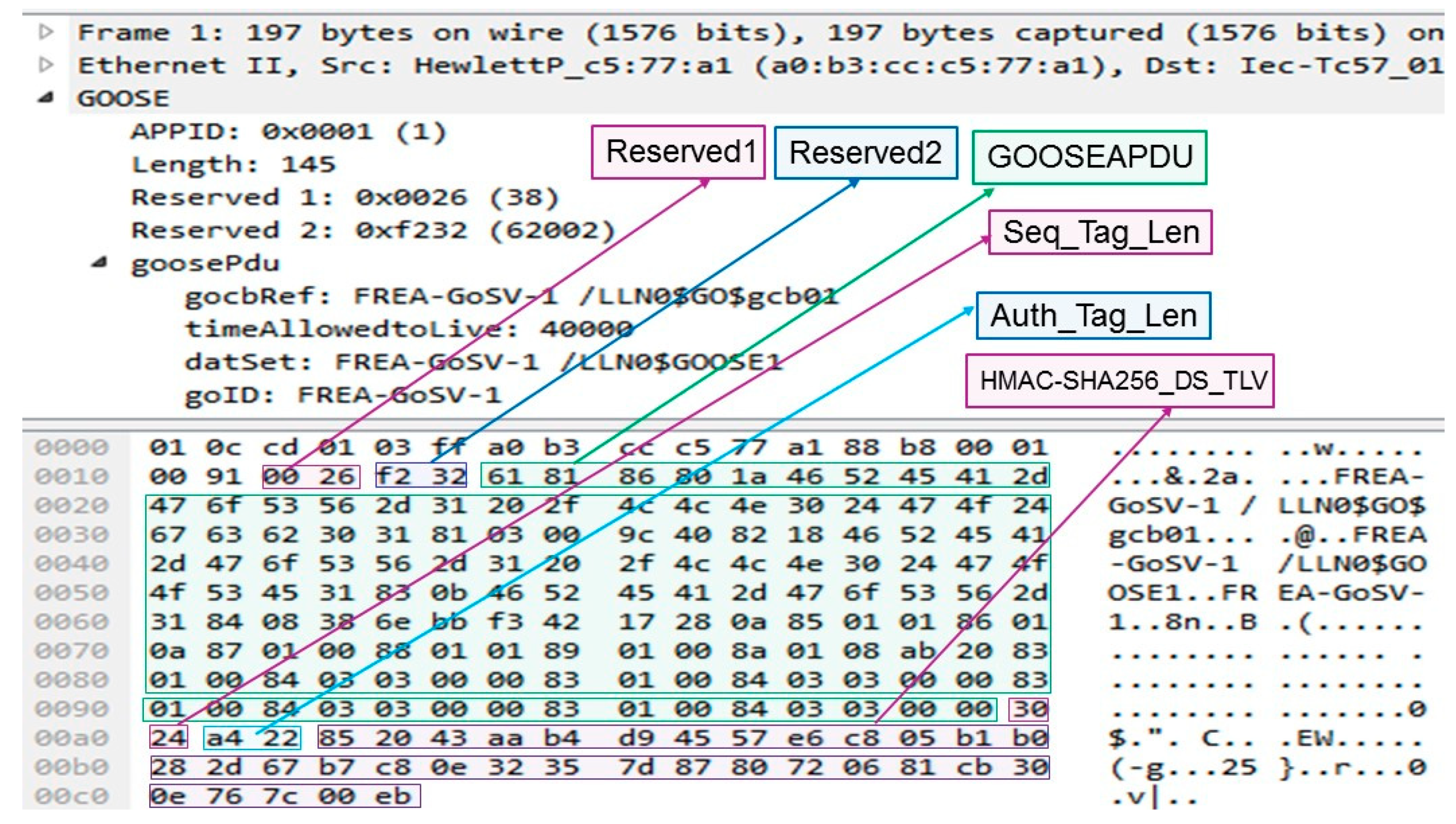
Figure 2. ‘Ethertype PDU’ consists of ‘APPID’, ‘Length’, ‘Reserved1’, ‘Reserved2’ followed by either Sample Values or GOOSE message fields. Ethernet frame ends with Frame Check Sequence (FCS) field. The ‘APPID’ field of 2 bytes contains the tag of ‘Ethertype PDU’. For ‘Ethertype SV PDU’ the ‘APPID’ value can be 0x4000 to 0x7FFF. The length field of 2 bytes contains the value of the total length of the Ethertype SV or GOOSE PDU and it should be less than 1501 bytes. The ‘reserved1’ field of the Ethertype SV or GOOSE PDU are reserved for security related information when the SV or GOOSE is sent with IEC 62351-6 security considerations. The ‘reserved2’ field is of 2 bytes to store 16-bit Cyclic Redundancy Check (CRC) value.
Figure 3 and
Figure 4 gives the description of set of fields that can be interpreted as T-L-V format.
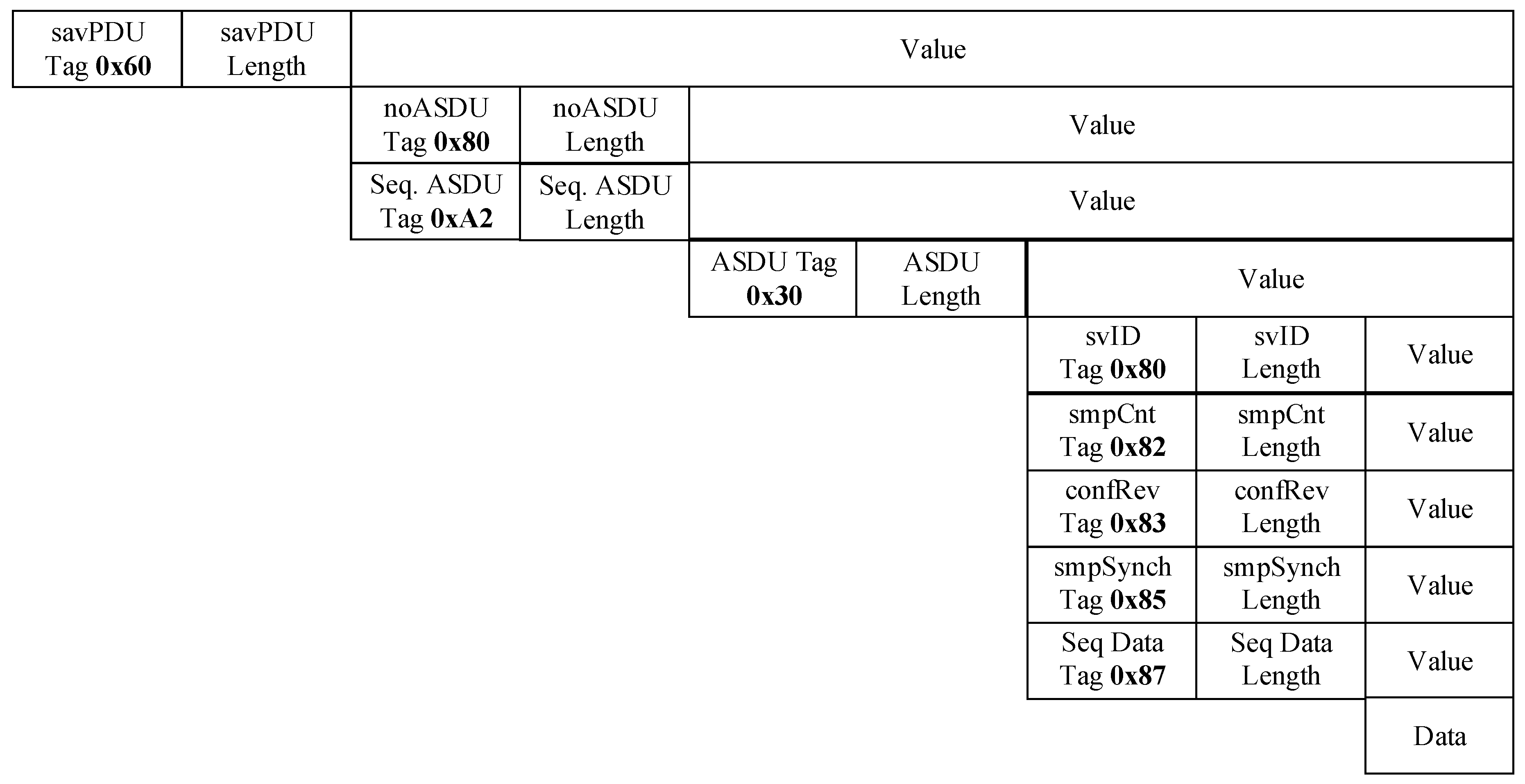
The SV APDU starts with ‘savPdu’ field with a tag of 0x60 followed by its length. The ‘noASDU’ field (number of ASDU) has a tag 0x80 followed by its length and value. The ‘Sequence of ASDU’ field (Sequence of ASDU) begins with a tag 0xA2 followed by its length and value. The ‘ASDU’ field (Application Service Data Unit) has a tag 0x30 followed by its length and value. Each ASDU consists of the following fields: ‘svID’ (sample value ID), ‘smp_Cnt’ (sampling count), ‘confRev’ (count of configuration changes), ‘smpSynch’ (sample synchronization), ‘Sequence of Data’ (sequence of data) and ‘data’ (the actual dataset). The ‘svID’ field begins with a tag 0x80 followed by its length and value. The ‘smp_Cnt’ field has tag 0x82 followed by its length and value. The ‘confRev’ field has a tag 0x83 followed by its length and value. The ‘smpSynch’ field begins with tag of 0x85 followed by its length and value. The ‘Sequence of Data’ field begins with tag of 0x87 followed by its length and value. The final field is the actual data set.
Figure 3 describes the Tag, length, value triplets of every field of SV message.
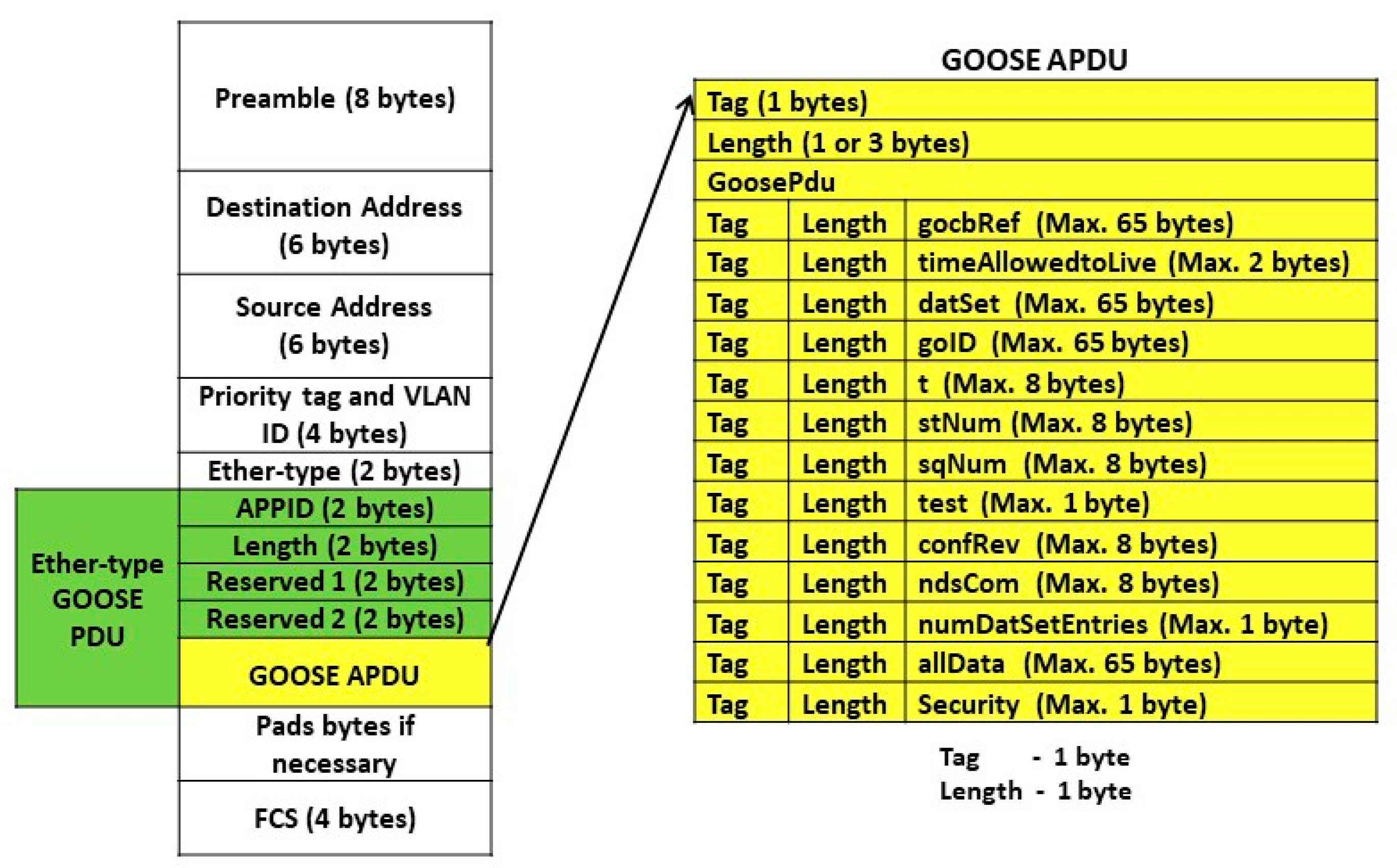
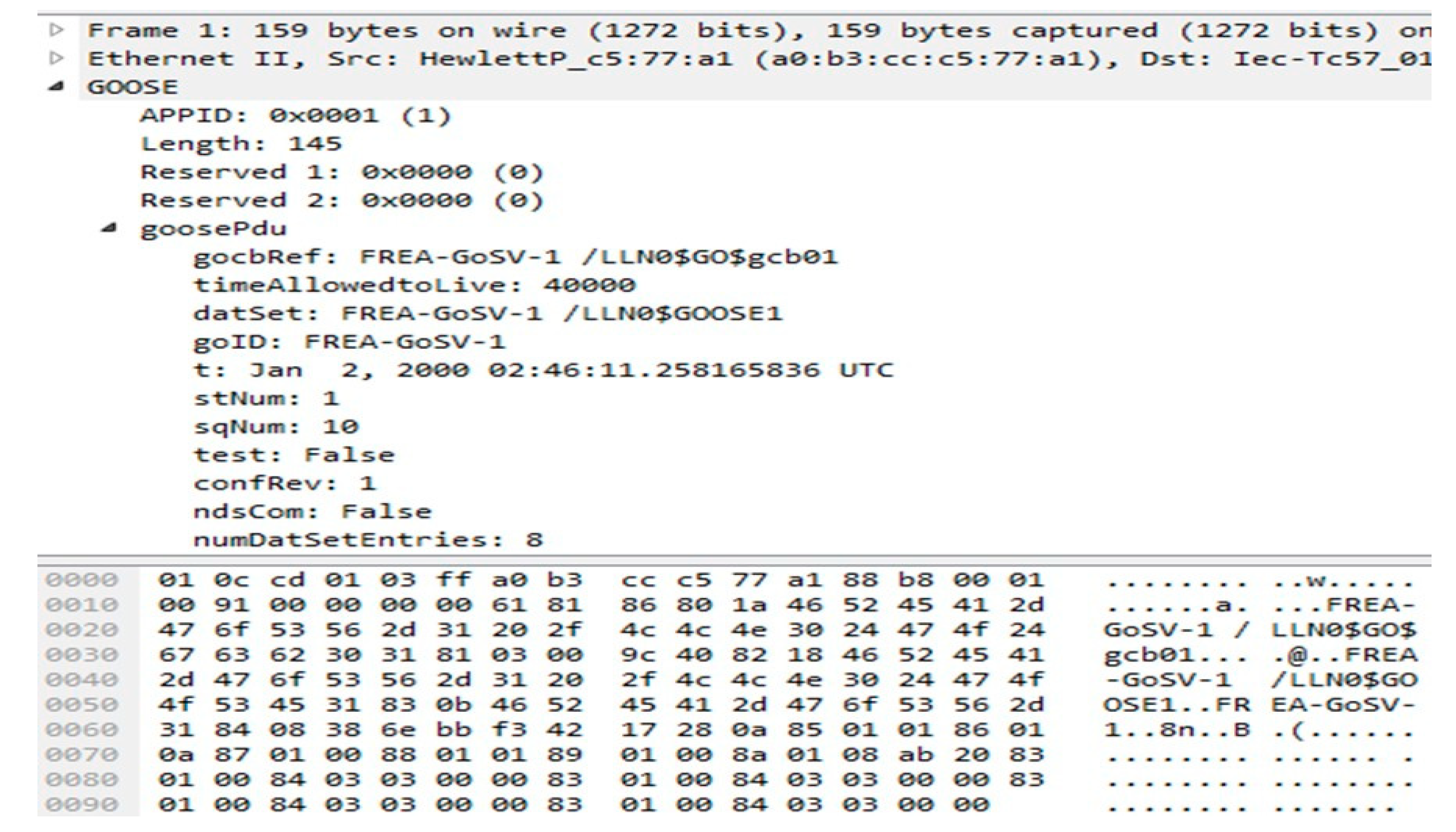
Similarly, PDU of GOOSE consists of following fields as gocbRef, ‘timeAllowedtoLive’, ‘datSet’, ‘goID’, ‘t’, ‘stNum’, ‘sqNum’, ‘test’, ‘confRev’, ‘ndsCom’, ‘numDatSetEntries’, ‘allData’ as shown in
Figure 4. The frame format of GOOSE message along with description of its fields is given in
Table 1.
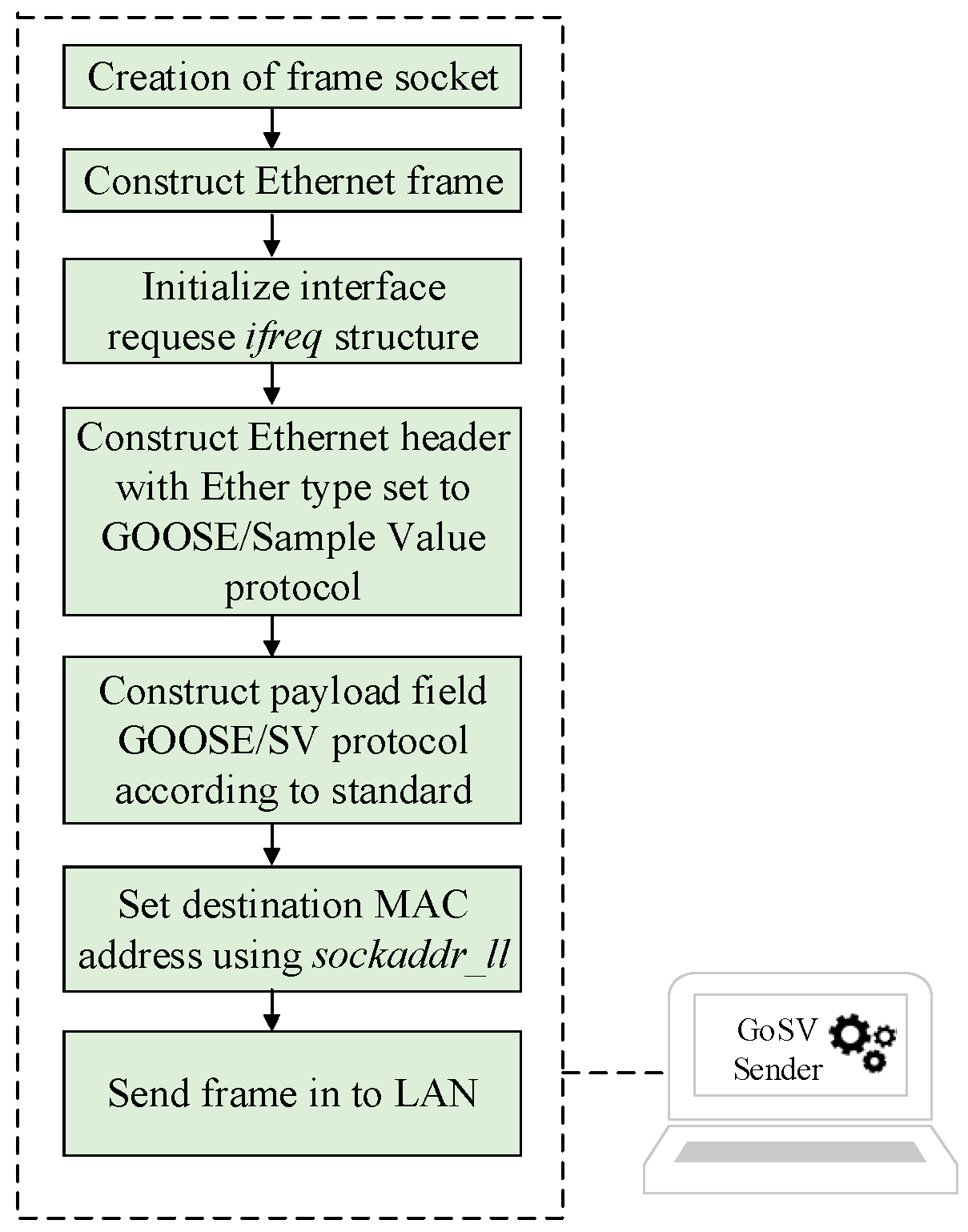
The GoSV software framework is implemented in C programming language using Ethernet libraries available in ether.h, sys/socket.h and sys/ioctl.h header files. The implementation can be accomplished at layer 2 of Open Systems Interconnect (OSI) reference model.
Figure 5 describes the implementation details. First it is needed to configure the network device at the sending end of the GOOSE and Sample Values. It includes the following steps: The packet interface is used to create a raw socket on the device. Linux supports ioctls (input-output controls) to configure network devices. For configuring network device, it is needed to set the structure called ifreq (Interface request) with the name and index of the interface using ioctls. Structure ifreq facilitates low level access to Linux network devices. Device independent physical layer structure called sockaddr_ll is used to set the destination MAC address of the packet. A buffer with the max size of 2048 is taken to construct the ethernet frame. Construction of payload field for GOOSE/SV protocol is considered by taking standard fields in the form of cascading tag, length and value. Authors have uploaded the developed version of GoSV [
11] in the GitHub repository.
3. Secure GoSV Framework
Security is a growing concern in power system communication networks. Compromising it may lead to plethora of security attacks such as Data integrity attack, replay attack, Man in The Middle (MITM) attack, Denial of Service (DoS) attack etc. These attacks may cause catastrophic damages to power grid. IEC 62351-6 specifies authentication and integrity as the security requirements and recommends using of digital signatures to protect IEC 61850 GOOSE or SV messages from cyber-attacks. Further, the IEC 62351-6 standard recommends RSASSA-PKCS1-v1_5 to Secure GOOSE and SV. However, the RSA based digital signature algorithms exhibit higher computational delays and do not meet the strict timing requirement of 3 ms for GOOSE messages [
19]. The computational times required for generating digital signatures using RSASSA-PKCS1-v1_5 are given in the
Table 2. Accordingly, Keyed Hash based Message Authentication Code (HMAC) based digital are proposed in literature for securing GOOSE messages [
23].
In this paper, authors developed S-GoSV software framework that implements both RSASSA-PKCS1-v1_5 digital signature and HMAC algorithms. Authors considered securing Sample Value messages as a future work.
3.1. RSASSA-PKCS1-v1_5 Digital Signature Algorithm
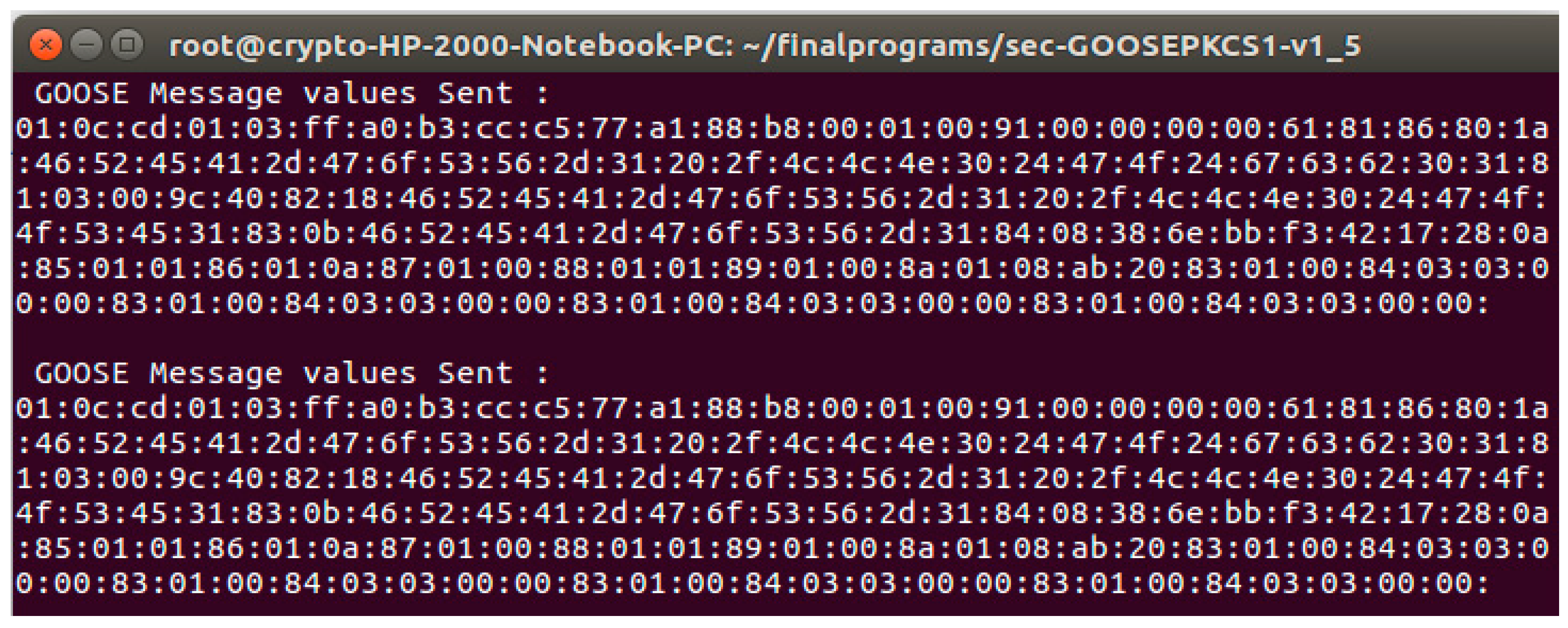
Development of secure S-GoSV software framework for RSASSA-PKCS1-v1_5 digital signature is done in two steps. In the first step, the digital signature is generated using RSASSA-PKCS1-v1_5 digital signature algorithm. The first step is implemented using python Crypto.PKCS1_v1_5 libraries. In the second step, the generated digital signature is transmitted using GoSV software which is developed using C language by adding extension fields.
Digital signatures for GOOSE message are generated in two major steps. First, an EMSA encoded message (EAPDU) generated for the GOOSE message. The EMSA encoding involves generation of hash value using SHA256 and addition of paddings [
19]. Second, the generated encoded message is converted to octet string format and then signed by digital signature algorithm RSASSA-PKCS1-v1_5. The complete process of digital signature generation and verification for RSASSA-PKCS1-v1_5 is described in [
19].
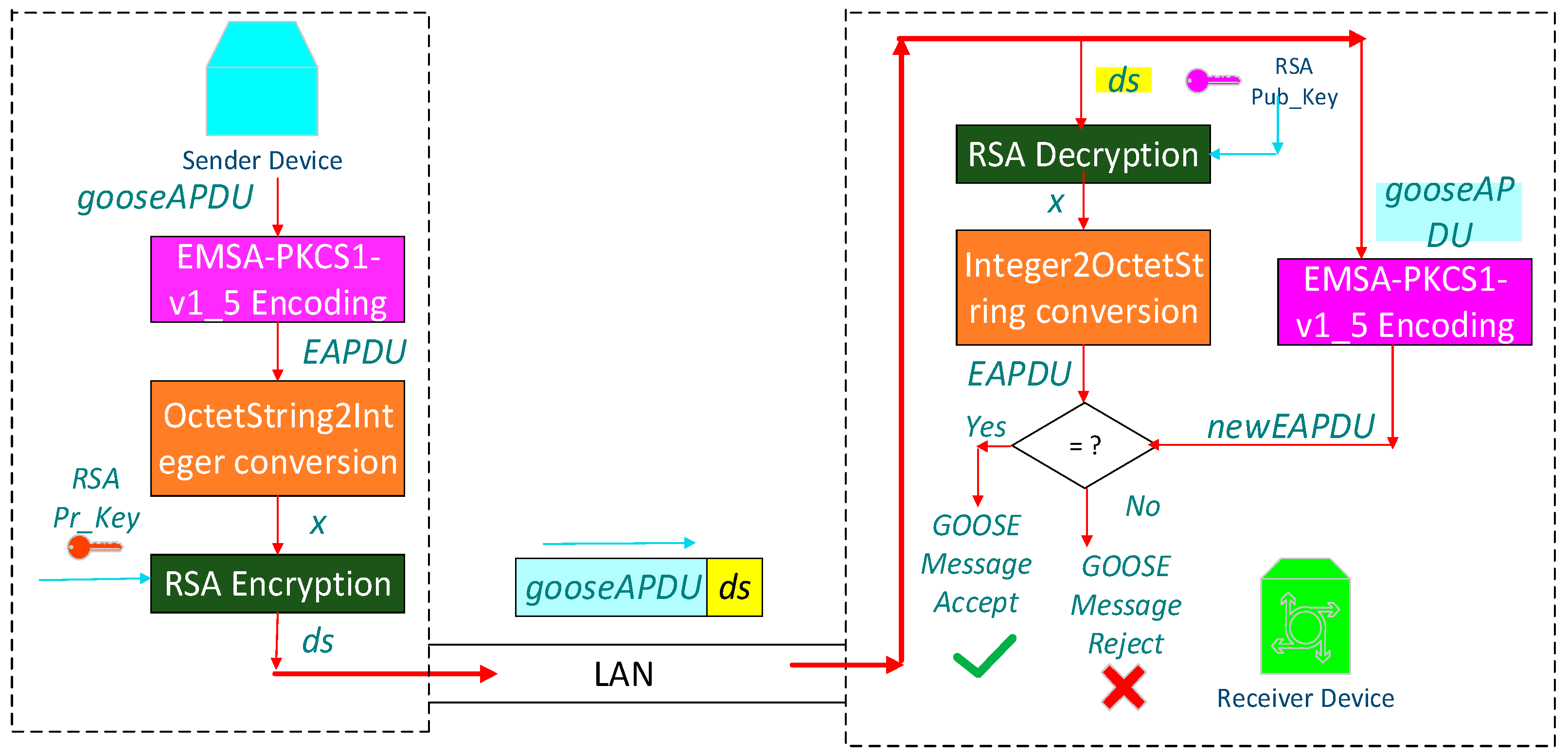
Figure 6 outlines the generation and verification of digital signature using RSASSA-PKCS1-v1_5 algorithm. GOOSE message along with appended DS is sent to subscriber in the network. At subscriber, a new EMSA encoded message (newEAPDU) is generated with the received GOOSE message and the received DS is decrypted by using the public key of the publisher. This decrypted digital signature value (EAPDU) is compared with the a new EMSA encoded value (newEAPDU) generated at the subscriber. If both are the same, then GOOSE message is valid otherwise it will not be accepted as a legitimate message.
In order to carry this additional Digital Signature (DS) value in the ethernet frame, IEC 62351-6 standard specifies extension to be added at the end of ethernet frame as shown in the
Figure 7. Extension field consists of SEQUENCE field and authentication value. SEQUENCE field is reserved for future security considerations other than encryption and message authentication. Authentication value contains digital signature value generated by RSASSA-PKCS1-v1_5.
RSASSA-PKCS1-v1_5 (Public Key Cryptography Standard #1 version 1.5) digital signature algorithm generates digital signature in three steps, as shown in Algorithm 1 below. In the first step, it takes GOOSE APDU as input and performs encoding using EMSA_PKCS1-v1_5 encoding scheme. The output of the encoding scheme is Encoded APDU (EAPDU). In the second step, EAPDU is converted into integer representation. In the final step, integer representation is encrypted with private key of RSA algorithm that gives digital signature (ds).
| Algorithm 1. RSASSA_PKCS1-v1_5_Gen_Signature (gooseAPDU) |
|
|
|
|
|
| Algorithm 2. RSASSA_PKCS1-v1_5_Signature_Verify (gooseAPDU, ds) |
|
|
|
|
|
|
|
|
|
|
At the publisher device, Algorithm 2 takes input a GOOSE APDU (
gooseAPDU) and gives encoded code (
EAPDU) using EMSA_PKCS1-v1_5 encoding algorithm. The output of encoding scheme is converted into integer representation (
x) which is further signed with RSA private key (
Pr_Key) that generates digital signature (ds). At the subscriber device, RSASSA_PKCS1-v1_5_Signature_verify algorithm verifies the generated signature (
ds). The received digital signature (
ds) is decrypted with RSA public key (
Pub_Key) that gives integer representation
x. Further, integer representation (
x) value is converted into octet string that gives Encoded APDU (
EAPDU). A new Encoded APDU (
newEAPDU) is generated by taking received GOOSE APDU (
gooseAPDU) as input to EMSA Encoding scheme. Newly generated EAPDU and received EAPDU is compared, if both are same then received GOOSE APDU (
gooseAPDU) is valid otherwise it is invalid.
Figure 6 illustrates the signature generation and verification process based on RSASSA_PKCS1-v1_5 digital signature algorithm.
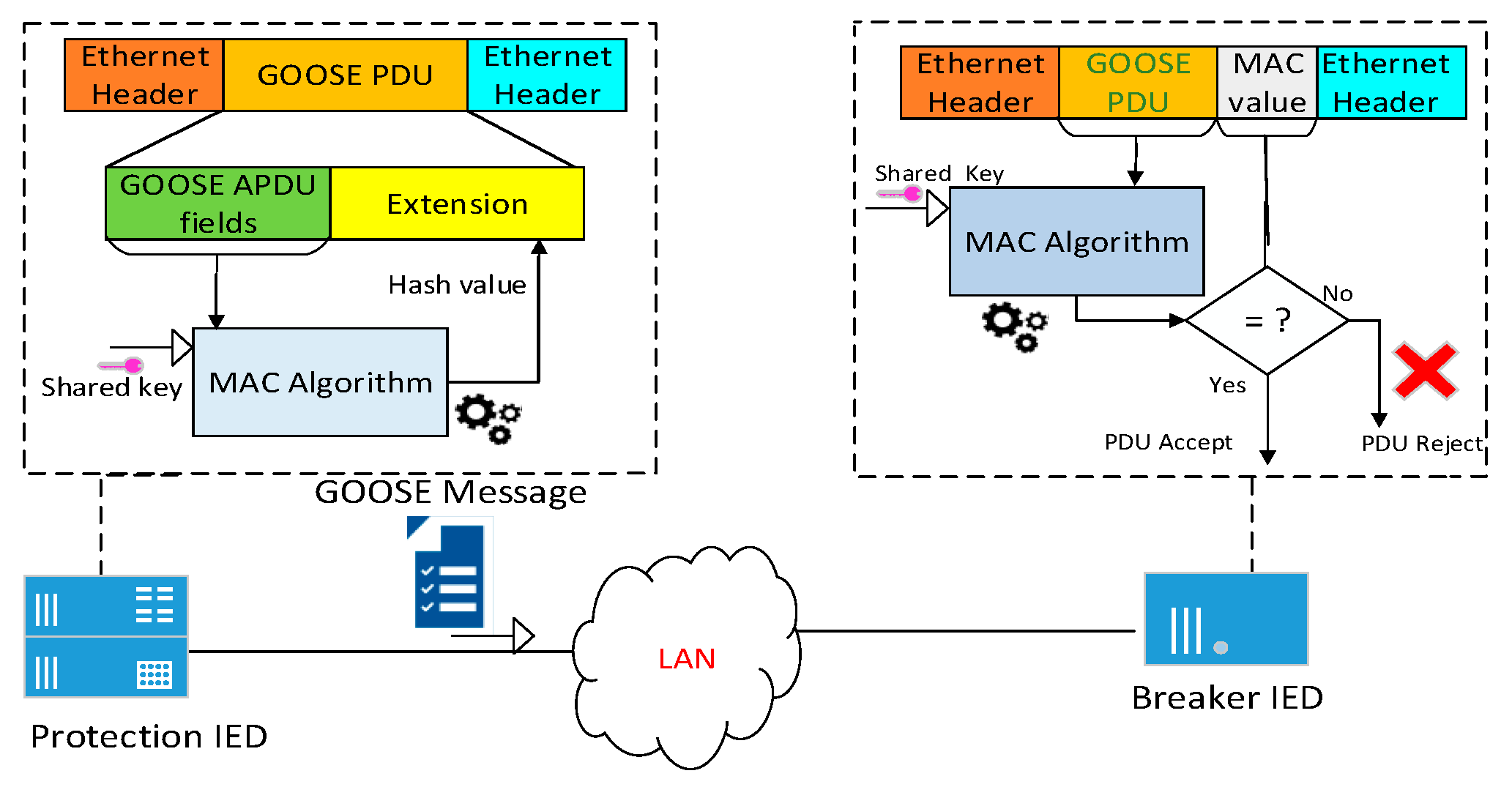
3.2. HMAC
Keyed Hash based Message Authentication Code (HMAC) is used for data origin authentication and integrity verification mechanisms in the network communications. It can be combined with either of the three different Secure Hash Algorithms: SHA256, SHA384 and SHA512. Secure Hash algorithms are cryptographic hash functions that generate hash values. HMAC combined with either of the above Secure Hash algorithms can be employed to generate digital signature instead of asymmetric RSASSA-PKCS1-v1_5 specified by IEC 62351-6. In this paper, among the above variants we have chosen HMAC with SHA256 algorithm for digital signature calculation. The main goal of these variants is to ensure the authenticity of data and it is not modified during its transmission in the network. HMAC implementation requires a pre-shared key shared by both publisher and subscriber. The security of the HMAC is ensured by the secure distribution and unpredictability of the associated secret symmetric key. The size of input data is arbitrary and produces a fixed size output. For HMAC-SHA256 where key size is 256 bits, it produces 32 bytes of digital signature.
In S-GoSV framework the HMAC algorithm is implemented using openSSL/hmac C libraries. The openSSL/hmac libraries are used to generate the MAC value (i.e., digital signature), using the pre-shared key, which is appended to GOOSE message and sent to subscriber. At the subscriber, again the MAC value is calculated for the received GOOSE message using the pre-shared key. The newly generated MAC value at the subscriber is compared with the received MAC value. If they do not match the GOOSE message is rejected.
Figure 8 shows the process of securing GOOSE messages with HMAC algorithm.