Remote Health Monitoring Systems for Elderly People: A Survey
Abstract
1. Introduction
1.1. Data Analysis in the Context of RHMS
1.2. Fog and Cloud Computing
1.3. Human Activity Recognition in RHMS
1.4. Structure of the Paper
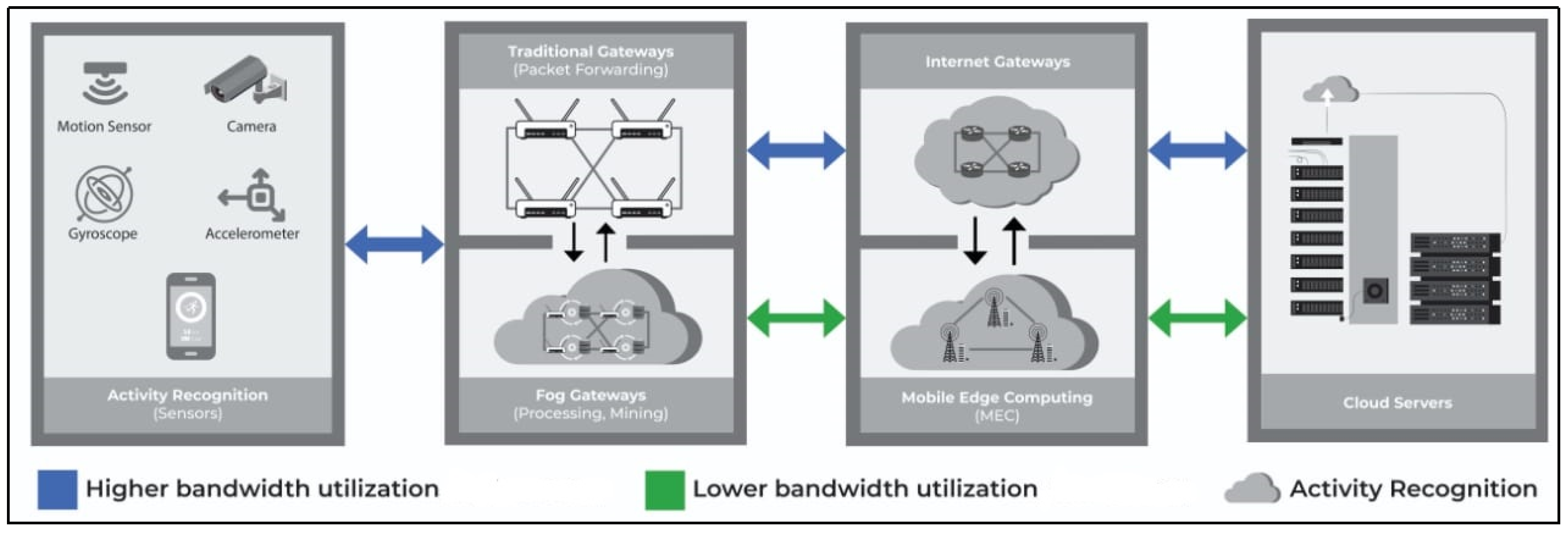
2. GATEWAYS: Data Computation in a Remote Health Monitoring System
2.1. Network Latency
2.2. Internet Bandwidth Utilization
2.3. Power Consumption
2.4. Execution Time
2.5. Context Awareness
2.6. Real-Time Compatibility
3. Human Activity Recognition in RHMS
4. RHMS for Elderly People
5. Major Challenges in RHMS
5.1. Data Accuracy and Availability in Real-Time
5.2. Data Security and Protection
5.3. Selection of Sensors and Devices
5.4. Detection of Concept Drift
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| MDPI | Multidisciplinary Digital Publishing Institute |
| DOAJ | Directory of open access journals |
| TLA | Three letter acronym |
| LD | Linear dichroism |
References
- Rashid, M.M.; Khan, S.U.; Eusufzai, F.; Redwan, M.A.; Sabuj, S.R.; Elsharief, M. A Federated Learning-Based Approach for Improving Intrusion Detection in Industrial Internet of Things Networks. Network 2023, 3, 158–179. [Google Scholar] [CrossRef]
- Blount, M.; Batra, V.M.; Capella, A.N.; Ebling, M.R.; Jerome, W.F.; Martin, S.M.; Nidd, M.; Niemi, M.R.; Wright, S.P. Remote health-care monitoring using Personal Care Connect. IBM Syst. J. 2007, 46, 95–113. [Google Scholar] [CrossRef]
- Kalid, N.; Zaidan, A.; Zaidan, B.; Salman, O.H.; Hashim, M.; Muzammil, H. Based real time remote health monitoring systems: A review on patients prioritization and related" big data" using body sensors information and communication technology. J. Med. Syst. 2018, 42, 30. [Google Scholar]
- Mohammed, K.; Zaidan, A.; Zaidan, B.; Albahri, O.S.; Alsalem, M.; Albahri, A.S.; Hadi, A.; Hashim, M. Real-time remote-health monitoring systems: A review on patients prioritisation for multiple-chronic diseases, taxonomy analysis, concerns and solution procedure. J. Med. Syst. 2019, 43, 223. [Google Scholar] [CrossRef] [PubMed]
- Rahman, H.; Ahmed, M.U.; Begum, S. Vision-based remote heart rate variability monitoring using camera. In Proceedings of the Internet of Things (IoT) Technologies for HealthCare: 4th International Conference, HealthyIoT 2017, Angers, France, 24–25 October 2017; Proceedings 4. Springer: Berlin/Heidelberg, Germany, 2018; pp. 10–18. [Google Scholar]
- Rincon, J.A.; Guerra-Ojeda, S.; Carrascosa, C.; Julian, V. An IoT and fog computing-based monitoring system for cardiovascular patients with automatic ECG classification using deep neural networks. Sensors 2020, 20, 7353. [Google Scholar] [CrossRef]
- Hao, Y.; Helo, P.; Gunasekaran, A. Cloud platforms for remote monitoring system: A comparative case study. Prod. Plan. Control 2020, 31, 186–202. [Google Scholar] [CrossRef]
- Hossain, M.S.; Muhammad, G. Cloud-assisted industrial internet of things (iiot)–enabled framework for health monitoring. Comput. Netw. 2016, 101, 192–202. [Google Scholar] [CrossRef]
- Pramanik, P.K.D.; Pareek, G.; Nayyar, A. Security and privacy in remote healthcare: Issues, solutions, and standards. In Telemedicine Technologies; Elsevier: Cambridge, MA, USA, 2019; pp. 201–225. [Google Scholar]
- Hu, P.; Dhelim, S.; Ning, H.; Qiu, T. Survey on fog computing: Architecture, key technologies, applications and open issues. J. Netw. Comput. Appl. 2017, 98, 27–42. [Google Scholar] [CrossRef]
- Vora, J.; Tanwar, S.; Tyagi, S.; Kumar, N.; Rodrigues, J.J. FAAL: Fog computing-based patient monitoring system for ambient assisted living. In Proceedings of the 2017 IEEE 19th International Conference on e-Health Networking, Applications and Services (Healthcom), Dalian, China, 12–15 October 2017; pp. 1–6. [Google Scholar]
- Vora, J.; Tanwar, S.; Tyagi, S.; Kumar, N.; Rodrigues, J.J. HRIDaaY: Ballistocardiogram-based heart rate monitoring using fog computing. In Proceedings of the 2019 IEEE Global Communications Conference (GLOBECOM), Waikoloa, HI, USA, 9–13 December 2019; pp. 9–13. [Google Scholar]
- Firdhous, M.; Ghazali, O.; Hassan, S. Fog computing: Will it be the future of cloud computing? In Proceedings of the Third International Conference on Informatics and Applications (ICIA2014), Kuala Terengganu, Malaysia, 8–10 October 2014; pp. 8–10. [Google Scholar]
- Tran, T.X.; Hajisami, A.; Pandey, P.; Pompili, D. Collaborative mobile edge computing in 5G networks: New paradigms, scenarios, and challenges. IEEE Commun. Mag. 2017, 55, 54–61. [Google Scholar] [CrossRef]
- Moghaddasi, K.; Rajabi, S. Learning at the Edge: Mobile Edge Computing and Reinforcement Learning for Enhanced Web Application Performance. In Proceedings of the 2023 9th International Conference on Web Research (ICWR), Tehran, Iran, 3–4 May 2023; IEEE: PIscataway, NJ, USA, 2023; pp. 300–304. [Google Scholar]
- Dohr, A.; Modre-Opsrian, R.; Drobics, M.; Hayn, D.; Schreier, G. The internet of things for ambient assisted living. In Proceedings of the 2010 Seventh International Conference on Information Technology: New Generations, Las Vegas, NV, USA, 12–14 April 2010; IEEE: Piscatway, NJ, USA, 2010; pp. 804–809. [Google Scholar]
- Costa, R.; Carneiro, D.; Novais, P.; Lima, L.; Machado, J.; Marques, A.; Neves, J. Ambient assisted living. In Proceedings of the 3rd Symposium of Ubiquitous Computing and Ambient Intelligence, 2008; Springer: Berlin/Heidelberg, Germany, 2009; pp. 86–94. [Google Scholar]
- van den Broek, G.; Cavallo, F.; Wehrmann, C. Aaliance Ambient Assisted Living Roadmap; IOS Press: Amsterdam, The Netherlands, 2010; Volume 6. [Google Scholar]
- Wang, L.; Hu, W.; Tan, T. Recent developments in human motion analysis. Pattern Recognit. 2003, 36, 585–601. [Google Scholar] [CrossRef]
- Ramasamy Ramamurthy, S.; Roy, N. Recent trends in machine learning for human activity recognition—A survey. Wiley Interdiscip. Rev. Data Min. Knowl. Discov. 2018, 8, e1254. [Google Scholar] [CrossRef]
- Subasi, A.; Khateeb, K.; Brahimi, T.; Sarirete, A. Human activity recognition using machine learning methods in a smart healthcare environment. In Innovation in Health Informatics; Elsevier: Cambridge, MA, USA, 2020; pp. 123–144. [Google Scholar]
- Gumaei, A.; Hassan, M.M.; Alelaiwi, A.; Alsalman, H. A hybrid deep learning model for human activity recognition using multimodal body sensing data. IEEE Access 2019, 7, 99152–99160. [Google Scholar] [CrossRef]
- Ann, O.C.; Theng, L.B. Human activity recognition: A review. In Proceedings of the 2014 IEEE International Conference on Control System, Computing And Engineering (ICCSCE 2014), Penang, Malaysia, 28–30 November 2014; IEEE: Piscataway, NJ, USA, 2014; pp. 389–393. [Google Scholar]
- Maurya, A.; Yadav, R.K.; Kumar, M.; Saumya. Comparative study of human activity recognition on sensory data using machine learning and deep learning. In Proceedings of the Integrated Intelligence Enable Networks and Computing, Gopeshwar, India, 25–27 May 2020; Springer: Singapore, 2021; pp. 63–71. [Google Scholar]
- Lara, O.D.; Labrador, M.A. A survey on human activity recognition using wearable sensors. IEEE Commun. Surv. Tutorials 2012, 15, 1192–1209. [Google Scholar] [CrossRef]
- Alam, M.A.U.; Roy, N.; Holmes, S.; Gangopadhyay, A.; Galik, E. Automated functional and behavioral health assessment of older adults with dementia. In Proceedings of the 2016 IEEE First International Conference on Connected Health: Applications, Systems and Engineering Technologies (CHASE), Washington, DC, USA, 27–29 June 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 140–149. [Google Scholar]
- Chen, L.; Wei, H.; Ferryman, J. A survey of human motion analysis using depth imagery. Pattern Recognit. Lett. 2013, 34, 1995–2006. [Google Scholar] [CrossRef]
- de Moura Costa, H.J.; da Costa, C.A.; da Rosa Righi, R.; Antunes, R.S. Fog computing in health: A systematic literature review. Health Technol. 2020, 10, 1025–1044. [Google Scholar] [CrossRef]
- Manogaran, G.; Varatharajan, R.; Lopez, D.; Kumar, P.M.; Sundarasekar, R.; Thota, C. A new architecture of Internet of Things and big data ecosystem for secured smart healthcare monitoring and alerting system. Future Gener. Comput. Syst. 2018, 82, 375–387. [Google Scholar] [CrossRef]
- Sood, S.K.; Mahajan, I. Wearable IoT sensor based healthcare system for identifying and controlling chikungunya virus. Comput. Ind. 2017, 91, 33–44. [Google Scholar] [CrossRef] [PubMed]
- Mell, P.; Grance, T. The NIST Definition of Cloud Computing. National Institute of Standards and Technology: Gaithersburg, MD, USA, 2011. [Google Scholar]
- Kraemer, F.A.; Braten, A.E.; Tamkittikhun, N.; Palma, D. Fog computing in healthcare—A review and discussion. IEEE Access 2017, 5, 9206–9222. [Google Scholar] [CrossRef]
- Andriopoulou, F.; Dagiuklas, T.; Orphanoudakis, T. Integrating IoT and fog computing for healthcare service delivery. Components and Services for IoT Platforms: Paving the Way for IoT Standards; Springer International Publishing: Cham, Switzerland, 2017; pp. 213–232. [Google Scholar]
- Gia, T.N.; Jiang, M.; Rahmani, A.M.; Westerlund, T.; Liljeberg, P.; Tenhunen, H. Fog computing in healthcare internet of things: A case study on ecg feature extraction. In Proceedings of the 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (CIT/IUCC/DASC/PICOM), Liverpool, UK, 26–28 October 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 356–363. [Google Scholar]
- Mouradian, C.; Naboulsi, D.; Yangui, S.; Glitho, R.H.; Morrow, M.J.; Polakos, P.A. A comprehensive survey on fog computing: State-of-the-art and research challenges. IEEE Commun. Surv. Tutorials 2017, 20, 416–464. [Google Scholar] [CrossRef]
- Mutlag, A.A.; Abd Ghani, M.K.; Arunkumar, N.a.; Mohammed, M.A.; Mohd, O. Enabling technologies for fog computing in healthcare IoT systems. Future Gener. Comput. Syst. 2019, 90, 62–78. [Google Scholar] [CrossRef]
- Mutlag, A.A.; Khanapi Abd Ghani, M.; Mohammed, M.A.; Maashi, M.S.; Mohd, O.; Mostafa, S.A.; Abdulkareem, K.H.; Marques, G.; de la Torre Díez, I. MAFC: Multi-agent fog computing model for healthcare critical tasks management. Sensors 2020, 20, 1853. [Google Scholar] [CrossRef] [PubMed]
- Mach, P.; Becvar, Z. Mobile edge computing: A survey on architecture and computation offloading. IEEE Commun. Surv. Tutorials 2017, 19, 1628–1656. [Google Scholar] [CrossRef]
- Wang, S.; Zhang, X.; Zhang, Y.; Wang, L.; Yang, J.; Wang, W. A survey on mobile edge networks: Convergence of computing, caching and communications. IEEE Access 2017, 5, 6757–6779. [Google Scholar] [CrossRef]
- Rahmani, A.M.; Gia, T.N.; Negash, B.; Anzanpour, A.; Azimi, I.; Jiang, M.; Liljeberg, P. Exploiting smart e-Health gateways at the edge of healthcare Internet-of-Things: A fog computing approach. Future Gener. Comput. Syst. 2018, 78, 641–658. [Google Scholar] [CrossRef]
- Stantchev, V.; Barnawi, A.; Ghulam, S.; Schubert, J.; Tamm, G. Smart items, fog and cloud computing as enablers of servitization in healthcare. Sens. Transducers 2014, 185, 121–128. [Google Scholar]
- Ko, S.W.; Huang, K.; Kim, S.L.; Chae, H. Live prefetching for mobile computation offloading. IEEE Trans. Wirel. Commun. 2017, 16, 3057–3071. [Google Scholar] [CrossRef]
- Saidi, H.; Labraoui, N.; Ari, A.A.A.; Bouida, D. Remote health monitoring system of elderly based on Fog to Cloud (F2C) computing. In Proceedings of the International Conference on Intelligent Systems and Computer Vision (ISCV), Fez, Morocco, 9–11 June 2020; pp. 1–7. [Google Scholar]
- Jamil, B.; Shojafar, M.; Ahmed, I.; Ullah, A.; Munir, K.; Ijaz, H. A job scheduling algorithm for delay and performance optimization in fog computing. Concurr. Comput. Pract. Exp. 2020, 32, e5581. [Google Scholar] [CrossRef]
- Vilela, P.H.; Rodrigues, J.J.; Righi, R.d.R.; Kozlov, S.; Rodrigues, V.F. Looking at fog computing for e-health through the lens of deployment challenges and applications. Sensors 2020, 20, 2553. [Google Scholar] [CrossRef]
- Hartmann, M.; Hashmi, U.S.; Imran, A. Edge computing in smart health care systems: Review, challenges, and research directions. Trans. Emerg. Telecommun. Technol. 2022, 33, e3710. [Google Scholar]
- Nair, G.; Hadresh, G.; Pdinesh, V. A Comparison Analysis of Fog and Cloud Computing. IJRAR 2020, 6, 1386–1390. [Google Scholar]
- Dolui, K.; Datta, S.K. Comparison of edge computing implementations: Fog computing, cloudlet and mobile edge computing. In Proceedings of the 2017 Global Internet of Things Summit (GIoTS), Geneva, Switzerland, 6–9 June 2017; pp. 1–6. [Google Scholar]
- Schilit, B.; Adams, N.; Want, R. Context-aware computing applications. In Proceedings of the 1994 First Workshop on Mobile Computing Systems and Applications—WMCSA 1994, Santa Cruz, CA, USA, 8–9 December 1994; pp. 85–90. [Google Scholar]
- Craciunescu, R.; Mihovska, A.; Mihaylov, M.; Kyriazakos, S.; Prasad, R.; Halunga, S. Implementation of Fog computing for reliable E-health applications. In Proceedings of the 2015 49th Asilomar Conference on Signals, Systems and Computers, Pacific Grove, CA, USA, 8–11 November 2015; pp. 459–463. [Google Scholar]
- Cao, Y.; Chen, S.; Hou, P.; Brown, D. FAST: A fog computing assisted distributed analytics system to monitor fall for stroke mitigation. In Proceedings of the 2015 IEEE International Conference on Networking, Architecture and Storage (NAS), Boston, MA, USA, 6–7 August 2015; pp. 2–11. [Google Scholar]
- Al-Khafajiy, M.; Baker, T.; Chalmers, C.; Asim, M.; Kolivand, H.; Fahim, M.; Waraich, A. Remote health monitoring of elderly through wearable sensors. Multimed. Tools Appl. 2019, 78, 24681–24706. [Google Scholar] [CrossRef]
- Zhang, S.; Wei, Z.; Nie, J.; Huang, L.; Wang, S.; Li, Z. A review on human activity recognition using vision-based method. J. Healthc. Eng. 2017, 2017, 3090343. [Google Scholar] [CrossRef] [PubMed]
- Ishimaru, S.; Hoshika, K.; Kise, K.; Dengel, A.; Kunze, K. Towards reading trackers in the wild: Detecting reading activities by EOG glasses and deep neural networks. In Proceedings of the 2017 ACM International Joint Conference on Pervasive and Ubiquitous Computing and ACM International Symposium on Wearable Computers, UbiComp/ISWC 2017, Hawaii, HI, USA, 11–15 September 2017; Association for Computing Machinery, Inc.: New York, NY, USA, 2017; pp. 704–711. [Google Scholar]
- Tamás, V. Human Behavior Recognition In Video Sequences. Technical University of Cluj-Napoca; Technical University of Cluj-Napoca: Cluj-Napoca, Romania, 2013. [Google Scholar]
- Banos, O.; Damas, M.; Pomares, H.; Prieto, A.; Rojas, I. Daily living activity recognition based on statistical feature quality group selection. Expert Syst. Appl. 2012, 39, 8013–8021. [Google Scholar] [CrossRef]
- Chen, L.; Nugent, C.D.; Wang, H. A knowledge-driven approach to activity recognition in smart homes. IEEE Trans. Knowl. Data Eng. 2011, 24, 961–974. [Google Scholar] [CrossRef]
- Gao, Z.; Xuan, H.Z.; Zhang, H.; Wan, S.; Choo, K.K.R. Adaptive fusion and category-level dictionary learning model for multiview human action recognition. IEEE Internet Things J. 2019, 6, 9280–9293. [Google Scholar] [CrossRef]
- Khan, M.A.A.H.; Hossain, H.S.; Roy, N. Infrastructure-less occupancy detection and semantic localization in smart environments. In Proceedings of the 12th EAI International Conference on Mobile and Ubiquitous Systems: Computing, Networking and Services, Coimbra, Portugal, 22–24 July 2015; pp. 51–60. [Google Scholar]
- Khan, M.A.A.H.; Kukkapalli, R.; Waradpande, P.; Kulandaivel, S.; Banerjee, N.; Roy, N.; Robucci, R. RAM: Radar-based activity monitor. In Proceedings of the IEEE INFOCOM 2016—The 35th Annual IEEE International Conference on Computer Communications, San Francisco, CA, USA, 10–14 April 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–9. [Google Scholar]
- Turaga, P.; Chellappa, R.; Subrahmanian, V.S.; Udrea, O. Machine recognition of human activities: A survey. IEEE Trans. Circuits Syst. Video Technol. 2008, 18, 1473–1488. [Google Scholar] [CrossRef]
- Candamo, J.; Shreve, M.; Goldgof, D.B.; Sapper, D.B.; Kasturi, R. Understanding transit scenes: A survey on human behavior-recognition algorithms. IEEE Trans. Intell. Transp. Syst. 2009, 11, 206–224. [Google Scholar] [CrossRef]
- Joseph, C.; Kokulakumaran, S.; Srijeyanthan, K.; Thusyanthan, A.; Gunasekara, C.; Gamage, C. A framework for whole-body gesture recognition from video feeds. In Proceedings of the 2010 5th International Conference on Industrial and Information Systems, Mangalore, India, 29 July–1 August 2010; IEEE: PIscataway, NJ, USA, 2010; pp. 430–435. [Google Scholar]
- Van Kasteren, T.; Englebienne, G.; Kröse, B.J. An activity monitoring system for elderly care using generative and discriminative models. Pers. Ubiquitous Comput. 2010, 14, 489–498. [Google Scholar] [CrossRef]
- Tolstikov, A.; Hong, X.; Biswas, J.; Nugent, C.; Chen, L.; Parente, G. Comparison of fusion methods based on dst and dbn in human activity recognition. J. Control. Theory Appl. 2011, 9, 18–27. [Google Scholar] [CrossRef]
- Yang, J.; Lee, J.; Choi, J. Activity recognition based on RFID object usage for smart mobile devices. J. Comput. Sci. Technol. 2011, 26, 239–246. [Google Scholar] [CrossRef]
- Sarkar, J.; Vinh, L.T.; Lee, Y.K.; Lee, S. GPARS: A general-purpose activity recognition system. Appl. Intell. 2011, 35, 242–259. [Google Scholar] [CrossRef]
- Hong, J.; Ohtsuki, T. A state classification method based on space-time signal processing using SVM for wireless monitoring systems. In Proceedings of the 2011 IEEE 22nd International Symposium on Personal, Indoor and Mobile Radio Communications, Toronto, ON, Canada, 11–14 September 2011; IEEE: PIscataway, NJ, USA, 2011; pp. 2229–2233. [Google Scholar]
- Kaur, H.; Atif, M.; Chauhan, R. An internet of healthcare things (IoHT)-based healthcare monitoring system. In Proceedings of the Advances in Intelligent Computing and Communication: Proceedings of ICAC 2019, Umea, Sweden, 16–20 June 2019; Springer: Singapore, 2020; pp. 475–482. [Google Scholar]
- Mukherjee, A.; Ghosh, S.; Behere, A.; Ghosh, S.K.; Buyya, R. Internet of Health Things (IoHT) for personalized health care using integrated edge-fog-cloud network. J. Ambient. Intell. Humaniz. Comput. 2021, 12, 943–959. [Google Scholar] [CrossRef]
- Ke, S.R.; Thuc, H.L.U.; Lee, Y.J.; Hwang, J.N.; Yoo, J.H.; Choi, K.H. A review on video-based human activity recognition. Computers 2013, 2, 88–131. [Google Scholar] [CrossRef]
- Damaševičius, R.; Vasiljevas, M.; Šalkevičius, J.; Woźniak, M. Human activity recognition in AAL environments using random projections. Comput. Math. Methods Med. 2016, 2016, 4073584. [Google Scholar] [CrossRef]
- Avci, A.; Bosch, S.; Marin-Perianu, M.; Marin-Perianu, R.; Havinga, P. Activity recognition using inertial sensing for healthcare, wellbeing and sports applications: A survey. In Proceedings of the 23th International Conference on Architecture of Computing Systems, Hannover, Germany, 22–23 February 2010; VDE: Frankfurt, Germany, 2010; pp. 1–10. [Google Scholar]
- Attal, F.; Mohammed, S.; Dedabrishvili, M.; Chamroukhi, F.; Oukhellou, L.; Amirat, Y. Physical human activity recognition using wearable sensors. Sensors 2015, 15, 31314–31338. [Google Scholar] [CrossRef]
- Shahmohammadi, F.; Hosseini, A.; King, C.E.; Sarrafzadeh, M. Smartwatch based activity recognition using active learning. In Proceedings of the 2017 IEEE/ACM International Conference on Connected Health: Applications, Systems and Engineering Technologies (CHASE), Philadelphia, PA, USA, 17–19 July 2017; IEEE: PIscataway, NJ, USA, 2017; pp. 321–329. [Google Scholar]
- Lee, Y.; Song, M. Using a smartwatch to detect stereotyped movements in children with developmental disabilities. IEEE Access 2017, 5, 5506–5514. [Google Scholar] [CrossRef]
- Capela, N.A.; Lemaire, E.D.; Baddour, N. Feature selection for wearable smartphone-based human activity recognition with able bodied, elderly, and stroke patients. PLoS ONE 2015, 10, e0124414. [Google Scholar] [CrossRef]
- Schrader, L.; Vargas Toro, A.; Konietzny, S.; Rüping, S.; Schäpers, B.; Steinböck, M.; Krewer, C.; Müller, F.; Güttler, J.; Bock, T. Advanced sensing and human activity recognition in early intervention and rehabilitation of elderly people. J. Popul. Ageing 2020, 13, 139–165. [Google Scholar] [CrossRef]
- Lentzas, A.; Vrakas, D. Non-intrusive human activity recognition and abnormal behavior detection on elderly people: A review. Artif. Intell. Rev. 2020, 53, 1975–2021. [Google Scholar] [CrossRef]
- Ronao, C.A.; Cho, S.B. Human activity recognition with smartphone sensors using deep learning neural networks. Expert Syst. Appl. 2016, 59, 235–244. [Google Scholar] [CrossRef]
- Bulling, A.; Blanke, U.; Schiele, B. A tutorial on human activity recognition using body-worn inertial sensors. ACM Comput. Surv. (CSUR) 2014, 46, 1–33. [Google Scholar] [CrossRef]
- Deng, L.; Yu, D. Deep learning: Methods and applications. Found. Trends® Signal Process. 2014, 7, 197–387. [Google Scholar] [CrossRef]
- LeCun, Y.; Bengio, Y.; Hinton, G. Deep learning. Nature 2015, 521, 436–444. [Google Scholar] [CrossRef] [PubMed]
- Khan, M.; Jan, B.; Farman, H.; Ahmad, J.; Farman, H.; Jan, Z. Deep learning methods and applications. In Deep Learning: Convergence to Big Data Analytics; Springer: Singapore, 2019; pp. 31–42. [Google Scholar]
- Coşkun, M.; YILDIRIM, Ö.; Ayşegül, U.; Demir, Y. An overview of popular deep learning methods. Eur. J. Tech. (EJT) 2017, 7, 165–176. [Google Scholar] [CrossRef]
- Nguyen, H.; Kieu, L.M.; Wen, T.; Cai, C. Deep learning methods in transportation domain: A review. IET Intell. Transp. Syst. 2018, 12, 998–1004. [Google Scholar] [CrossRef]
- Labrador, M.A.; Yejas, O.D.L. Human Activity Recognition: Using Wearable Sensors and Smartphones; CRC Press: Boca Raton, FL, USA, 2013. [Google Scholar]
- Lai, X.; Liu, Q.; Wei, X.; Wang, W.; Zhou, G.; Han, G. A survey of body sensor networks. Sensors 2013, 13, 5406–5447. [Google Scholar] [CrossRef]
- González-Villanueva, L.; Cagnoni, S.; Ascari, L. Design of a wearable sensing system for human motion monitoring in physical rehabilitation. Sensors 2013, 13, 7735–7755. [Google Scholar] [CrossRef]
- Jobanputra, C.; Bavishi, J.; Doshi, N. Human activity recognition: A survey. Procedia Comput. Sci. 2019, 155, 698–703. [Google Scholar] [CrossRef]
- Cheng, L.; Guan, Y.; Zhu, K.; Li, Y. Recognition of human activities using machine learning methods with wearable sensors. In Proceedings of the 2017 IEEE 7th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 9–11 January 2017; IEEE: PIscataway, NJ, USA, 2017; pp. 1–7. [Google Scholar]
- Ahmed, N.; Rafiq, J.I.; Islam, M.R. Enhanced human activity recognition based on smartphone sensor data using hybrid feature selection model. Sensors 2020, 20, 317. [Google Scholar] [CrossRef]
- Chen, K.; Zhang, D.; Yao, L.; Guo, B.; Yu, Z.; Liu, Y. Deep learning for sensor-based human activity recognition: Overview, challenges, and opportunities. ACM Comput. Surv. (CSUR) 2021, 54, 1–40. [Google Scholar] [CrossRef]
- Li, Y.; Hao, Z.; Lei, H. Survey of convolutional neural network. J. Comput. Appl. 2016, 36, 2508. [Google Scholar]
- Murad, A.; Pyun, J.Y. Deep recurrent neural networks for human activity recognition. Sensors 2017, 17, 2556. [Google Scholar] [CrossRef] [PubMed]
- Zhao, Z.; Chen, W.; Wu, X.; Chen, P.C.; Liu, J. LSTM network: A deep learning approach for short-term traffic forecast. IET Intell. Transp. Syst. 2017, 11, 68–75. [Google Scholar] [CrossRef]
- Gao, H.; Duan, Y.; Miao, H.; Yin, Y. An approach to data consistency checking for the dynamic replacement of service process. IEEE Access 2017, 5, 11700–11711. [Google Scholar] [CrossRef]
- Cao, L.; Wang, Y.; Zhang, B.; Jin, Q.; Vasilakos, A.V. GCHAR: An efficient Group-based Context—Aware human activity recognition on smartphone. J. Parallel Distrib. Comput. 2018, 118, 67–80. [Google Scholar] [CrossRef]
- Zhao, Y.; Li, H.; Wan, S.; Sekuboyina, A.; Hu, X.; Tetteh, G.; Piraud, M.; Menze, B. Knowledge-aided convolutional neural network for small organ segmentation. IEEE J. Biomed. Health Inform. 2019, 23, 1363–1373. [Google Scholar] [CrossRef]
- Li, W.; Liu, X.; Liu, J.; Chen, P.; Wan, S.; Cui, X. On improving the accuracy with auto-encoder on conjunctivitis. Appl. Soft Comput. 2019, 81, 105489. [Google Scholar] [CrossRef]
- Wan, S.; Qi, L.; Xu, X.; Tong, C.; Gu, Z. Deep learning models for real-time human activity recognition with smartphones. Mob. Netw. Appl. 2020, 25, 743–755. [Google Scholar] [CrossRef]
- Wang, J.; Chen, Y.; Hao, S.; Peng, X.; Hu, L. Deep learning for sensor-based activity recognition: A survey. Pattern Recognit. Lett. 2019, 119, 3–11. [Google Scholar] [CrossRef]
- Ignatov, A. Real-time human activity recognition from accelerometer data using Convolutional Neural Networks. Appl. Soft Comput. 2018, 62, 915–922. [Google Scholar] [CrossRef]
- Zhou, X.; Liang, W.; Kevin, I.; Wang, K.; Wang, H.; Yang, L.T.; Jin, Q. Deep-learning-enhanced human activity recognition for Internet of healthcare things. IEEE Internet Things J. 2020, 7, 6429–6438. [Google Scholar] [CrossRef]
- Xu, C.; Chai, D.; He, J.; Zhang, X.; Duan, S. InnoHAR: A deep neural network for complex human activity recognition. IEEE Access 2019, 7, 9893–9902. [Google Scholar] [CrossRef]
- Chen, Z.; Zhang, L.; Jiang, C.; Cao, Z.; Cui, W. WiFi CSI based passive human activity recognition using attention based BLSTM. IEEE Trans. Mob. Comput. 2018, 18, 2714–2724. [Google Scholar] [CrossRef]
- Zhu, Q.; Chen, Z.; Soh, Y.C. A novel semisupervised deep learning method for human activity recognition. IEEE Trans. Ind. Inform. 2018, 15, 3821–3830. [Google Scholar] [CrossRef]
- Wang, H.; Zhao, J.; Li, J.; Tian, L.; Tu, P.; Cao, T.; An, Y.; Wang, K.; Li, S. Wearable sensor-based human activity recognition using hybrid deep learning techniques. Secur. Commun. Netw. 2020, 2020, 2132138. [Google Scholar] [CrossRef]
- Lu, J.; Zheng, X.; Sheng, M.; Jin, J.; Yu, S. Efficient human activity recognition using a single wearable sensor. IEEE Internet Things J. 2020, 7, 11137–11146. [Google Scholar] [CrossRef]
- Qi, J.; Yang, P.; Waraich, A.; Deng, Z.; Zhao, Y.; Yang, Y. Examining sensor-based physical activity recognition and monitoring for healthcare using Internet of Things: A systematic review. J. Biomed. Inform. 2018, 87, 138–153. [Google Scholar] [CrossRef]
- Hong, Y.J.; Kim, I.J.; Ahn, S.C.; Kim, H.G. Mobile health monitoring system based on activity recognition using accelerometer. Simul. Model. Pract. Theory 2010, 18, 446–455. [Google Scholar] [CrossRef]
- Tao, M.; Li, X.; Wei, W.; Yuan, H. Jointly optimization for activity recognition in secure IoT-enabled elderly care applications. Appl. Soft Comput. 2021, 99, 106788. [Google Scholar] [CrossRef]
- Dritsas, E.; Trigka, M. Stroke risk prediction with machine learning techniques. Sensors 2022, 22, 4670. [Google Scholar] [CrossRef]
- Luna-Perejón, F.; Muñoz-Saavedra, L.; Civit-Masot, J.; Civit, A.; Domínguez-Morales, M. AnkFall—Falls, falling risks and daily-life activities dataset with an ankle-placed accelerometer and training using recurrent neural networks. Sensors 2021, 21, 1889. [Google Scholar] [CrossRef] [PubMed]
- Ahsan, M.M.; Siddique, Z. Machine learning-based heart disease diagnosis: A systematic literature review. Artif. Intell. Med. 2022, 128, 102289. [Google Scholar] [CrossRef]
- MS, A.R.; Nirmala, C.; Aljohani, M.; Sreenivasa, B. A novel technique for detecting sudden concept drift in healthcare data using multi-linear artificial intelligence techniques. Front. Artif. Intell. 2022, 5, 950659. [Google Scholar]
- Gama, J.; Medas, P.; Castillo, G.; Rodrigues, P. Learning with drift detection. In Proceedings of the Advances in Artificial Intelligence—SBIA 2004: 17th Brazilian Symposium on Artificial Intelligence, Sao Luis, Maranhao, Brazil, 29 September–1 October 2004; Proceedings 17. Springer: Berlin, Germany, 2004; pp. 286–295. [Google Scholar]
- Wang, L.; Chen, S.; He, Q. Concept drift-based runtime reliability anomaly detection for edge services adaptation. IEEE Trans. Knowl. Data Eng. 2021. [Google Scholar] [CrossRef]
- Gulcan, E.B.; Can, F. Unsupervised concept drift detection for multi-label data streams. Artif. Intell. Rev. 2023, 56, 2401–2434. [Google Scholar] [CrossRef]
- Casado, F.E.; Lema, D.; Iglesias, R.; Regueiro, C.V.; Barro, S. Ensemble and continual federated learning for classification tasks. Mach. Learn. 2023, 1–41. [Google Scholar] [CrossRef]
- Jothimurugesan, E.; Hsieh, K.; Wang, J.; Joshi, G.; Gibbons, P.B. Federated learning under distributed concept drift. In Proceedings of the International Conference on Artificial Intelligence and Statistics, Valencia, Spain, 25–27 April 2023; PMLR; pp. 5834–5853. [Google Scholar]
| Cloud Computing | Mobile Edge Computing | Fog Computing | |
|---|---|---|---|
| Network Latency | High | Medium | Low |
| Internet Bandwidth Utilization | High | Medium | Low |
| Power Consumption | High | High | Low |
| Access Mechanisms | Wi-Fi, Mobile Networks | Mobile Networks | Bluetooth, Wi-Fi |
| Execution Time | Low | Medium | High |
| Resources Availability | High | Medium | Low |
| Context Awareness | Low | High | Medium |
| Real Time Compatibility | Low | Medium | High |
| Technology Devices | Centralized Servers, Data Centers | Servers running in base stations | Gateways (Routers, Switches) |
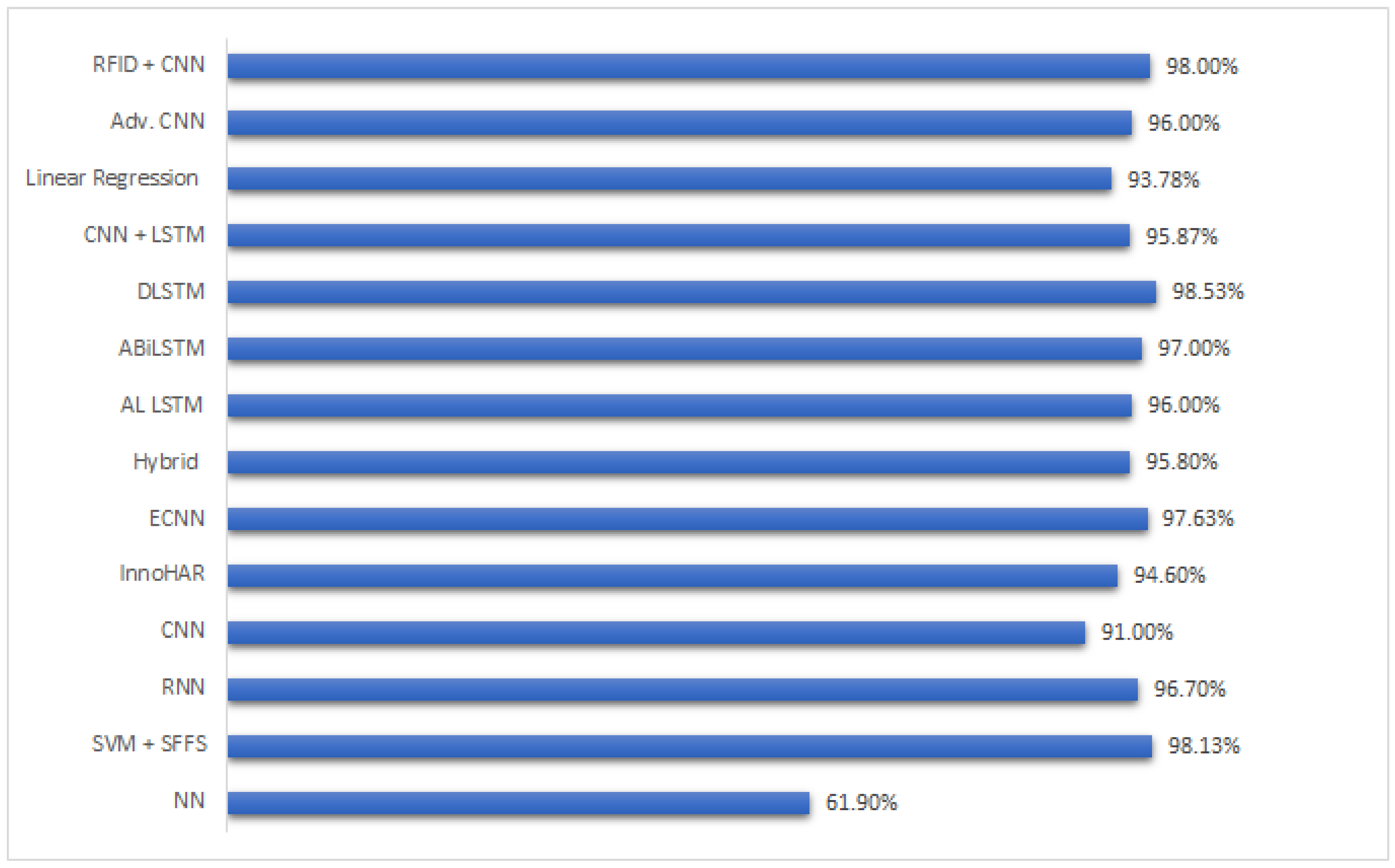
| Ref. | Model (M.L/D.L/Hybrid) | Strength | Weakness |
|---|---|---|---|
| [91] | M.L (SVM+ANN) | A unique architecture fused basic SVM with conventional ANN. Can be very useful for shallow feature extraction. | Average accuracy, slow network. |
| [92] | M.L (SVM+ SFFS) | A very efficient lightweight feature filtration technique employing SFFS module. | Shows good results on smaller datasets only. |
| [94] | D.L (CNN) | Detailed Survey on CNN & its state-of-the-art applications. | CNN cause overfitting, and typical models fail to adapt to certain configurations. |
| [95] | D.L (RNN) | Can outperform CNN’s in extracting long term dependencies. | Can cause extreme exploding gradients. |
| [96] | D.L (LSTM) | The memory cell enables the network to perform back propagation and remember long term dependencies, which better correlates data; hence, they outperform conventional RNN’s. | Training time increases exponentially on larger datasets. |
| [101] | D.L (CNN) | Context-aware classification handled some errors in conventional CNN, which increased the overall accuracy. | Compared with vanilla models with no parameter adjustments or fine tuning. |
| [102] | M.L/D.L/Hybrid | A detailed survey on conventional vs. advance activity recognition approaches in both M.L and D.L. Portrayed the advanced in D.L. | None. |
| [103] | D.L (Enhanced CNN) | Showed superior results compared to state-of-the-art works. | Results are based on strongly labelled data only. Performance may vary on weakly labelled data. |
| [104] | D.L (LSTM+ALM) | Auto labelling module showed significant improvement in accuracy. | The auto labelling module required a large pool of unlabelled data, which made the system costly. |
| [105] | Hybrid (InnoHAR) | A fusion of RNN with Inception neural networks showed good performance on smaller and larger datasets. | Not implemented in real-time scenarios. Moreover, the configuration of INN is very complicated if a change or update is required. |
| [106] | D.L (ABiLSTM) | Attention-based BLSTM implemented on Wi-Fi data. Attention module filtered the features-f-interest and dropped low level features, thus making the proposed approach time efficient. | A single channelled Wi-Fi was used without any real-time data collection, which is not a viable source of activity recognition data. |
| [107] | D.L (DLSTM) | A DLSTM based on labelled and unlabelled data, which extracts high level features and retrains low-level features and labels the unlabelled data. Superior accuracy compared to state-of-the-art LSTM works. | Results generated in a controlled environment; performance may vary in real-time scenarios. Moreover, DLSTM structure makes the network too slow and time complexity increases. |
| [108] | Hybrid (CNN+LSTM) | A state-of-the-artwork employing postural transition with static activities. Showed superior performance compared to several approaches employing transition activities. | Complex structure only considers basic static and transition activities while the experiments were based on a pre-processed dataset with abundant features. Performance may vary for datasets where number of features is far less. |
| Approach | Type | Strength |
|---|---|---|
| [52] | Wearable sensors | Able to detect abnormalities in elderly people and capable of employment in real-time scenarios |
| [111] | RFID + wearable sensors | By the tracking of hand motion, RFID tagged objects are able to be detected which provides additional pattern data for efficient human activity recognition |
| [112] | CNN + vision devices | Introduced an authentication-based access network to avoid any unwanted access or breach in the network |
| [66] | RFID + CNN | A dense CNN with RFID unit brought forward a novel RSS based approach. However no solid strengths were presented in the research work |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ahmed, S.; Irfan, S.; Kiran, N.; Masood, N.; Anjum, N.; Ramzan, N. Remote Health Monitoring Systems for Elderly People: A Survey. Sensors 2023, 23, 7095. https://doi.org/10.3390/s23167095
Ahmed S, Irfan S, Kiran N, Masood N, Anjum N, Ramzan N. Remote Health Monitoring Systems for Elderly People: A Survey. Sensors. 2023; 23(16):7095. https://doi.org/10.3390/s23167095
Chicago/Turabian StyleAhmed, Salman, Saad Irfan, Nasira Kiran, Nayyer Masood, Nadeem Anjum, and Naeem Ramzan. 2023. "Remote Health Monitoring Systems for Elderly People: A Survey" Sensors 23, no. 16: 7095. https://doi.org/10.3390/s23167095
APA StyleAhmed, S., Irfan, S., Kiran, N., Masood, N., Anjum, N., & Ramzan, N. (2023). Remote Health Monitoring Systems for Elderly People: A Survey. Sensors, 23(16), 7095. https://doi.org/10.3390/s23167095








