LoRaWAN Physical Layer-Based Attacks and Countermeasures, A Review
Abstract
:1. Introduction
1.1. Motivation
1.2. LoRaWAN Security
1.3. Related Work
1.4. Novelty and Structure
2. LoRaWAN
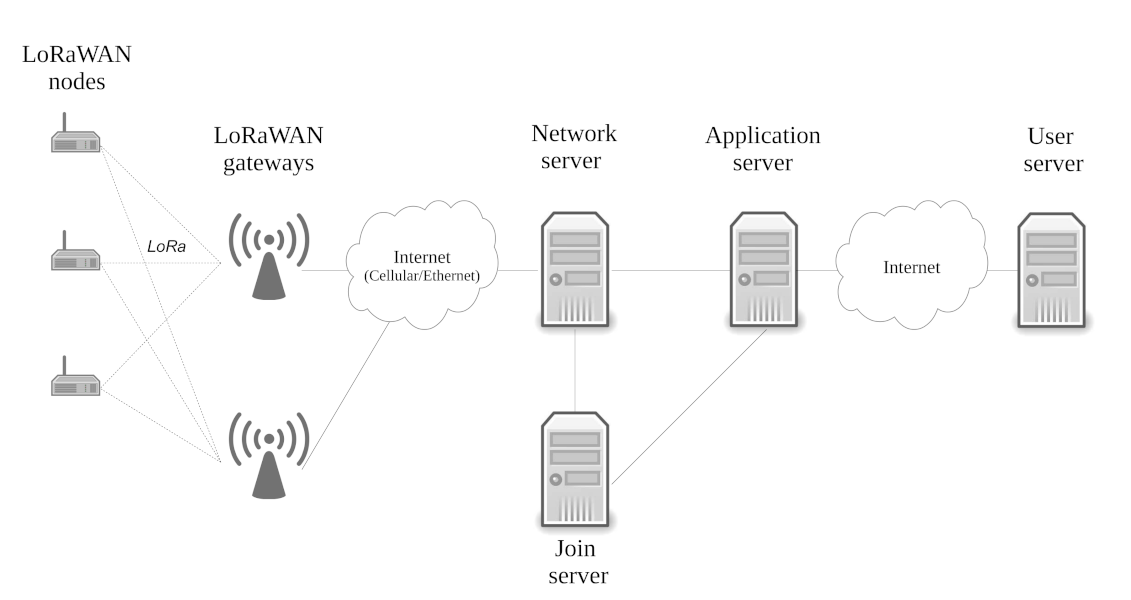
2.1. Network Topology
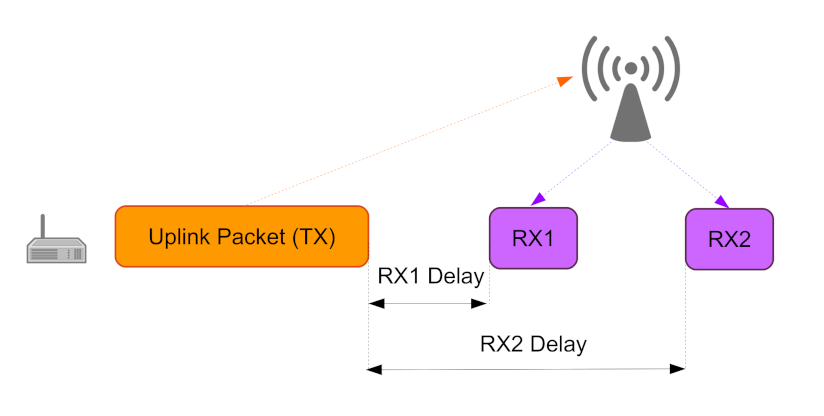
2.2. Medium Access
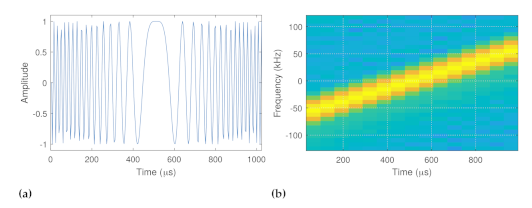
2.3. LoRa Physical Layer
2.4. LoRaWAN Packet Structure
2.5. Adaptive Data Rate
- Collection of RF-link statistics: The algorithm receives the RF link information in SNR values. After a sufficient number of SNR values is collected, a margin to the minimum SNR thresholds of the different spreading-factor settings is calculated. Depending on the margin, the network server can request that a device switch the spreading factor and the transmission power settings accordingly.
- MAC Commands: LoRaWAN defines a few MAC command packets that control the ADR. With the 1-bit ADR uplink packet, a device can request that the network server control its data rate. The 1-bit ADRAckReq uplink packet is periodically sent by devices to request that the network server validate the received uplink messages. Depending on the network servers response to this packet, the end device can optimize its spreading factor and transmission power to find the optimal communication parameters.
- ADR Algorithm: The 4 bytes long LinkADRReq downlink packet contains the parameters determined by the ADR algorithm, which are communicated to the device from the network server. A more comprehensive overview of the algorithm can be found, e.g., from [40].
2.6. Device Activation
2.6.1. LoRaWAN v1.0
2.6.2. LoRaWAN v1.1
2.7. LoRaWAN Keys
3. Vulnerabilities
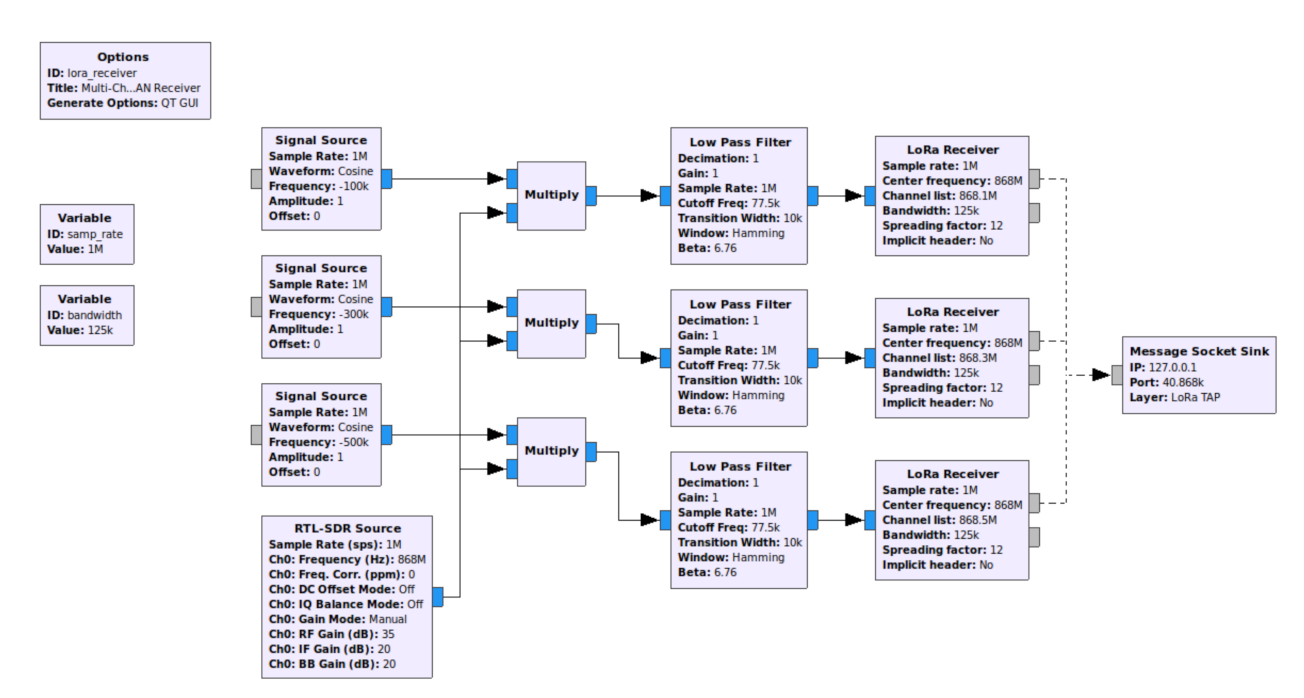
3.1. Sniffers
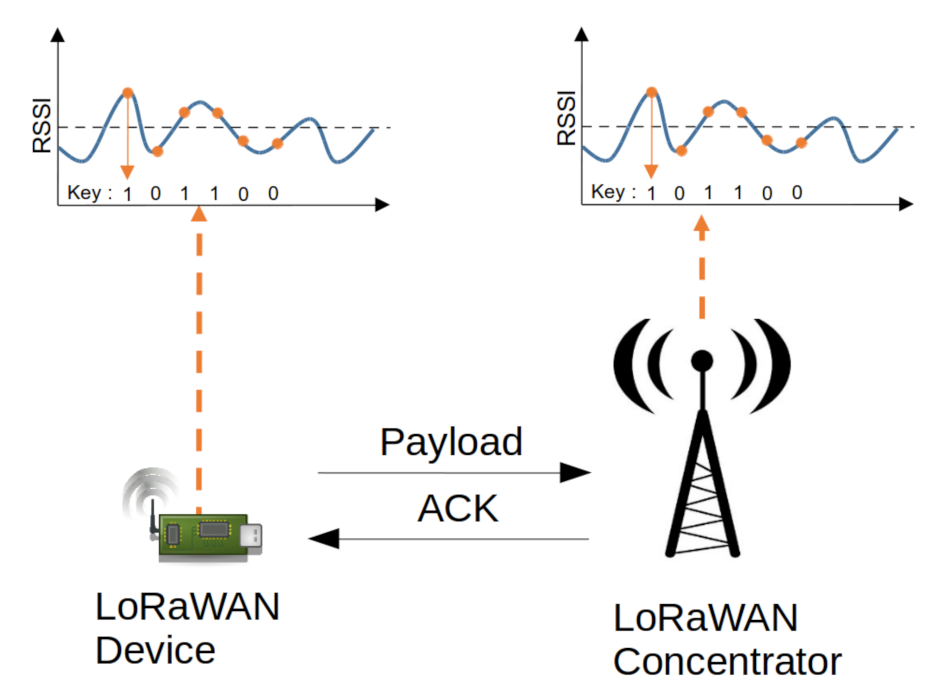
3.2. Covert Channels
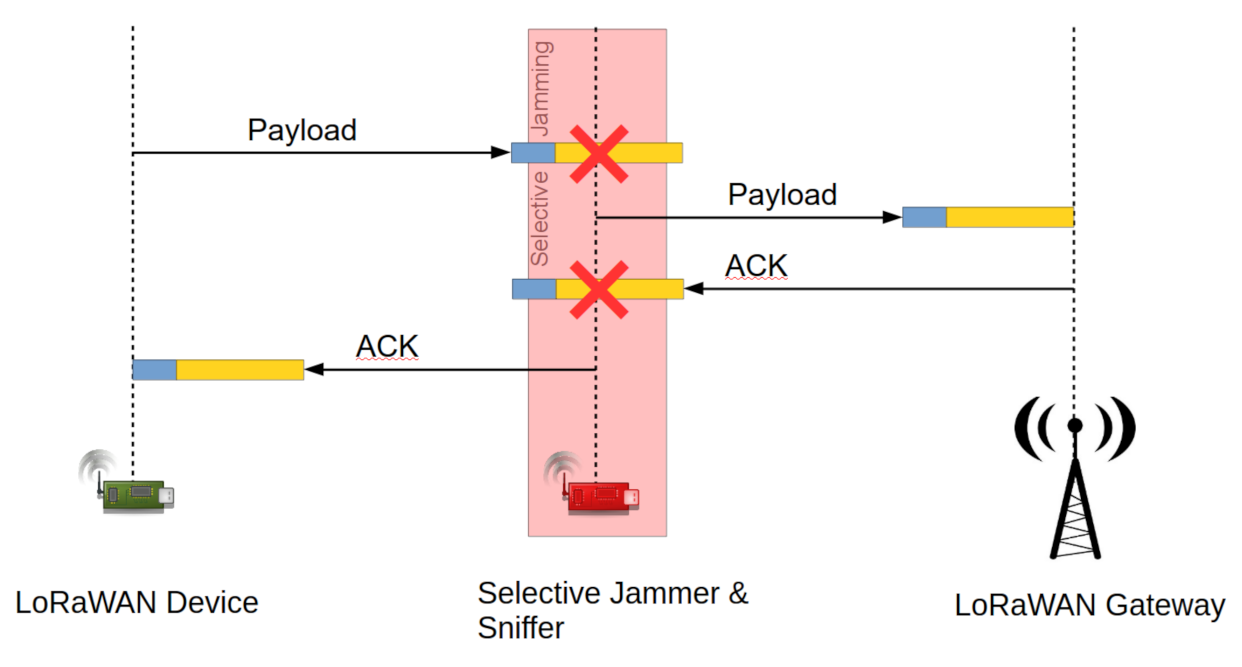
3.3. Jamming Attacks
3.4. Key Extraction Attacks
3.5. Wormhole Attacks
3.6. Energy Attacks
4. Protection Techniques
4.1. Replay Attack Detection
4.2. Wireless Key Generation
4.3. Resilience against Jamming
- Performance evaluations have been conducted to reveal the network system performance under jamming attacks;
- Detection techniques have been developed to distinguish jamming attacks from e.g., faulty gateway/device operation;
- Improved signaling strategies have been presented, which can improve data throughput in the presence of intentional jamming.
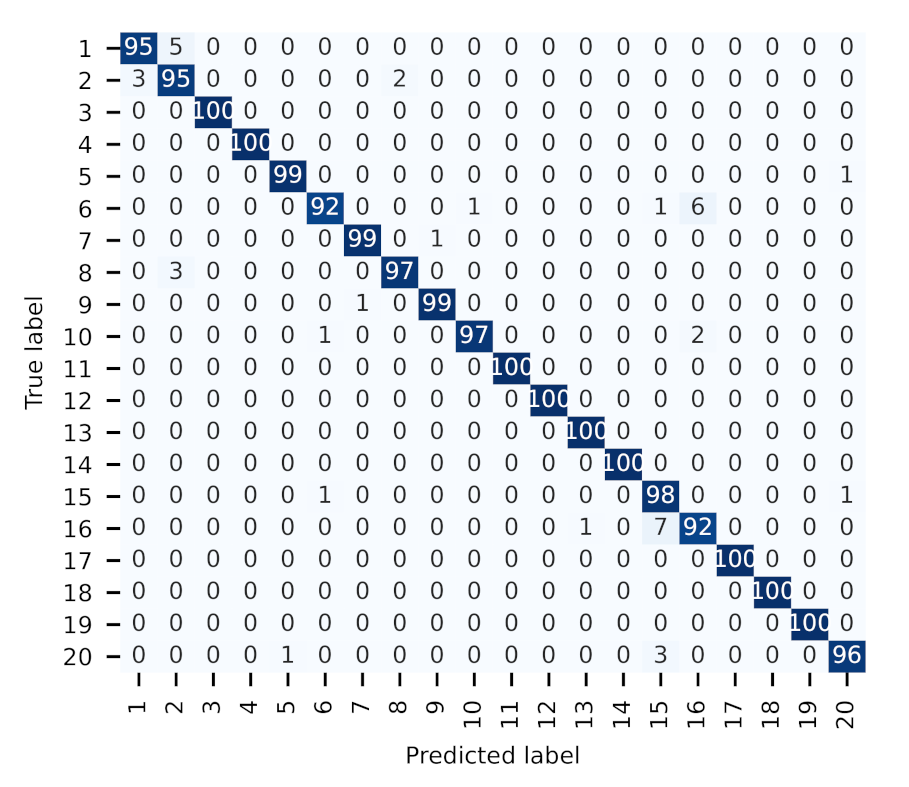
4.4. Device Fingerprinting
4.4.1. Overview
4.4.2. Case Study
5. Discussion
5.1. Lessons Learned—Impact on LoRaWAN Security
5.1.1. Availability
5.1.2. Confidentiality and Integrity
5.2. Research Potential
5.2.1. Resources
5.2.2. Experimental Research
5.2.3. Further Physical Layer Security Concepts
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Peng, Y.; Shangguan, L.; Hu, Y.; Qian, Y.; Lin, X.; Chen, X.; Fang, D.; Jamieson, K. PLoRa: A Passive Long-Range Data Network from Ambient LoRa Transmissions. In Proceedings of the 2018 Conference of the ACM Special Interest Group on Data Communication, SIGCOMM ’18, Budapest, Hungary, 20–25 August 2018; Association for Computing Machinery: New York, NY, USA, 2018; pp. 147–160. [Google Scholar] [CrossRef]
- Chirpstack. Available online: https://www.chirpstack.io/ (accessed on 10 November 2021).
- Wang, X.; Kong, L.; He, L.; Chen, G. mLoRa: A Multi-Packet Reception Protocol in LoRa networks. In Proceedings of the 2019 IEEE 27th International Conference on Network Protocols (ICNP), Chicago, IL, USA, 8–10 October 2019; pp. 1–11. [Google Scholar] [CrossRef]
- Asad Ullah, M.; Mikhaylov, K.; Alves, H. Massive Machine-Type Communication and Satellite Integration for Remote Areas. IEEE Wirel. Commun. 2021, 28, 74–80. [Google Scholar] [CrossRef]
- Oniga, B.; Dadarlat, V.; De Poorter, E.; Munteanu, A. A secure LoRaWAN sensor network architecture. In Proceedings of the 2017 IEEE SENSORS, Glasgow, UK, 29 October–1 November 2017; pp. 1–3. [Google Scholar] [CrossRef] [Green Version]
- LoRa Alliance. LoRaWAN Specification 1.1; LoRa Alliance: Fremont, CA, USA, 2017. [Google Scholar]
- Lee, J.; Hwang, D.; Park, J.; Kim, K.H. Risk analysis and countermeasure for bit-flipping attack in LoRaWAN. In Proceedings of the 2017 International Conference on Information Networking (ICOIN), Da Nang, Vietnam, 11–13 January 2017; pp. 549–551. [Google Scholar] [CrossRef]
- Dönmez, T.C.; Nigussie, E. Security of LoRaWAN v1.1 in Backward Compatibility Scenarios. Procedia Comput. Sci. 2018, 134, 51–58. [Google Scholar] [CrossRef]
- Noura, H.; Hatoum, T.; Salman, O.; Yaacoub, J.P.; Chehab, A. LoRaWAN security survey: Issues, threats and possible mitigation techniques. Internet Things 2020, 12, 100303. [Google Scholar] [CrossRef]
- Brownfield, M.; Gupta, Y.; Davis, N. Wireless sensor network denial of sleep attack. In Proceedings of the Sixth Annual IEEE SMC Information Assurance Workshop, West Point, NY, USA, 15–17 June 2005; pp. 356–364. [Google Scholar] [CrossRef]
- Mikhaylov, K.; Fujdiak, R.; Pouttu, A.; Miroslav, V.; Malina, L.; Mlynek, P. Energy Attack in LoRaWAN: Experimental Validation. In Proceedings of the 14th International Conference on Availability, Reliability and Security, ARES ’19, Canterbury, UK, 26–29 August 2019; Association for Computing Machinery: New York, NY, USA, 2019. [Google Scholar] [CrossRef]
- Aras, E.; Small, N.; Ramachandran, G.S.; Delbruel, S.; Joosen, W.; Hughes, D. Selective jamming of LoRaWAN using commodity hardware. In Proceedings of the 14th EAI International Conference on Mobile and Ubiquitous Systems: Computing, Networking and Services, Melbourne, Australia, 7–10 November 2017; pp. 363–372. [Google Scholar]
- Hessel, F.; Almon, L.; Álvarez, F. ChirpOTLE: A Framework for Practical LoRaWAN Security Evaluation. In Proceedings of the 13th ACM Conference on Security and Privacy in Wireless and Mobile Networks, WiSec ’20, Linz, Austria, 8–10 July 2020; Association for Computing Machinery: New York, NY, USA, 2020; pp. 306–316. [Google Scholar] [CrossRef]
- Robyns, P.; Marin, E.; Lamotte, W.; Quax, P.; Singelée, D.; Preneel, B. Physical-layer fingerprinting of LoRa devices using supervised and zero-shot learning. In Proceedings of the ACM Conference Security Privacy Wireless Mobile Networks (WiSec), Boston, MA, USA, 18–20 July 2017; pp. 58–63. [Google Scholar]
- Shen, G.; Zhang, J.; Marshall, A.; Peng, L.; Wang, X. Radio Frequency Fingerprint Identification for LoRa Using Spectrogram and CNN. In Proceedings of the IEEE International Conference on Computer Communications, Vancouver, BC, Canada, 10–13 May 2021. [Google Scholar]
- Shen, G.; Zhang, J.; Marshall, A.; Peng, L.; Wang, X. Radio Frequency Fingerprint Identification for LoRa Using Deep Learning. IEEE J. Sel. Areas Commun. 2021, 39, 2604–2616. [Google Scholar] [CrossRef]
- Shen, G.; Zhang, J.; Marshall, A.; Cavallaro, J. Towards Scalable and Channel-Robust Radio Frequency Fingerprint Identification for LoRa. IEEE Trans. Inf. Forensics Secur. 2022, 17, 774–787. [Google Scholar] [CrossRef]
- Al-Shawabka, A.; Pietraski, P.; B Pattar, S.; Restuccia, F.; Melodia, T. DeepLoRa: Fingerprinting LoRa Devices at Scale Through Deep Learning and Data Augmentation. In Proceedings of the Twenty-Second International Symposium on Theory, Algorithmic Foundations, and Protocol Design for Mobile Networks and Mobile Computing, MobiHoc ’21, Shanghai, China, 26–29 July 2021. [Google Scholar]
- Zhang, J.; Marshall, A.; Hanzo, L. Channel-Envelope Differencing Eliminates Secret Key Correlation: LoRa-Based Key Generation in Low Power Wide Area Networks. IEEE Trans. Veh. Technol. 2018, 67, 12462–12466. [Google Scholar] [CrossRef] [Green Version]
- Xu, W.; Jha, S.; Hu, W. LoRa-key: Secure key generation system for LoRa-based network. IEEE Internet Things J. 2018, 6, 6404–6416. [Google Scholar] [CrossRef]
- Ruotsalainen, H.; Zhang, J.; Grebeniuk, S. Experimental Investigation on Wireless Key Generation for Low-Power Wide-Area Networks. IEEE Internet Things J. 2020, 7, 1745–1755. [Google Scholar] [CrossRef]
- Martinez Bolivar, I.M. Jamming on LoRaWAN Networks: From Modelling to Detection. Ph.D. Thesis, Institut National des Sciences Appliquées de Rennes, Rennes, France, 2021. [Google Scholar]
- Danish, S.M.; Nasir, A.; Qureshi, H.K.; Ashfaq, A.B.; Mumtaz, S.; Rodriguez, J. Network Intrusion Detection System for Jamming Attack in LoRaWAN Join Procedure. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Hou, N.; Xia, X.; Zheng, Y. Jamming of LoRa PHY and Countermeasure. In Proceedings of the IEEE INFOCOM 2021—IEEE Conference on Computer Communications, Vancouver, BC, Canada, 10–13 May 2021; pp. 1–10. [Google Scholar] [CrossRef]
- Zhang, J.; Rajendran, S.; Sun, Z.; Woods, R.; Hanzo, L. Physical layer security for the Internet of Things: Authentication and key generation. IEEE Wirel. Commun. 2019, 26, 92–98. [Google Scholar] [CrossRef]
- Zhang, J.; Li, G.; Marshall, A.; Hu, A.; Hanzo, L. A new frontier for IoT security emerging from three decades of key generation relying on wireless channels. IEEE Access 2020, 8, 138406–138446. [Google Scholar] [CrossRef]
- Zhang, J.; Woods, R.; Duong, T.Q.; Marshall, A.; Ding, Y.; Huang, Y.; Xu, Q. Experimental study on key generation for physical layer security in wireless communications. IEEE Access 2016, 4, 4464–4477. [Google Scholar] [CrossRef] [Green Version]
- Ali, S.T.; Sivaraman, V.; Ostry, D. Eliminating reconciliation cost in secret key generation for body-worn health monitoring devices. IEEE Trans. Mob. Comput. 2013, 13, 2763–2776. [Google Scholar] [CrossRef]
- Premnath, S.N.; Gowda, P.L.; Kasera, S.K.; Patwari, N.; Ricci, R. Secret key extraction using Bluetooth wireless signal strength measurements. In Proceedings of the 2014 Eleventh Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), Singapore, 30 June–3 July 2014; pp. 293–301. [Google Scholar]
- Xu, Q.; Zheng, R.; Saad, W.; Han, Z. Device fingerprinting in wireless networks: Challenges and opportunities. IEEE Commun. Surv. Tutor. 2016, 18, 94–104. [Google Scholar] [CrossRef] [Green Version]
- Vo-Huu, T.D.; Vo-Huu, T.D.; Noubir, G. Fingerprinting Wi-Fi devices using software defined radios. In Proceedings of the 9th ACM Conference on Security & Privacy in Wireless and Mobile Networks, Darmstadt, Germany, 18–20 July 2016; pp. 3–14. [Google Scholar]
- Peng, L.; Hu, A.; Zhang, J.; Jiang, Y.; Yu, J.; Yan, Y. Design of a hybrid RF fingerprint extraction and device classification scheme. IEEE Internet Things J. 2018, 6, 349–360. [Google Scholar] [CrossRef]
- Helluy-Lafont, É.; Boé, A.; Grimaud, G.; Hauspie, M. Bluetooth devices fingerprinting using low cost SDR. In Proceedings of the 2020 Fifth International Conference on Fog and Mobile Edge Computing (FMEC), Paris, France, 20–23 April 2020; pp. 289–294. [Google Scholar]
- Kuntke, F.; Romanenko, V.; Linsner, S.; Steinbrink, E.; Reuter, C. LoRaWAN security issues and mitigation options by the example of agricultural IoT scenarios. Trans. Emerg. Telecommun. Technol. 2022. [Google Scholar] [CrossRef]
- Philip, S.J.; McQuillan, J.M.; Adegbite, O. LoRaWAN v1.1 Security: Are We in the Clear Yet? In Proceedings of the 2020 IEEE 6th International Conference on Dependability in Sensor, Cloud and Big Data Systems and Application (DependSys), Nadi, Fiji, 14–16 December 2020; pp. 112–118. [Google Scholar] [CrossRef]
- Adefemi Alimi, K.O.; Ouahada, K.; Abu-Mahfouz, A.M.; Rimer, S. A Survey on the Security of Low Power Wide Area Networks: Threats, Challenges, and Potential Solutions. Sensors 2020, 20, 5800. [Google Scholar] [CrossRef]
- Butun, I.; Pereira, N.; Gidlund, M. Security Risk Analysis of LoRaWAN and Future Directions. Future Internet 2019, 11, 3. [Google Scholar] [CrossRef] [Green Version]
- Naidu, D.; Ray, N.K. Review on Authentication Schemes for Device Security in LoRaWAN. In Proceedings of the 2021 19th OITS International Conference on Information Technology (OCIT), Bhubaneswar, India, 16–18 December 2021; pp. 387–392. [Google Scholar] [CrossRef]
- What Are LoRa and LoRaWAN. Available online: https://lora-developers.semtech.com/library/tech-papers-and-guides/lora-and-lorawan/ (accessed on 10 November 2021).
- Li, S.; Raza, U.; Khan, A. How Agile is the Adaptive Data Rate Mechanism of LoRaWAN? In Proceedings of the 2018 IEEE Global Communications Conference (GLOBECOM), Abu Dhabi, United Arab Emirates, 9–13 December 2018; pp. 206–212. [Google Scholar] [CrossRef] [Green Version]
- Knight, M.; Seeber, B. Decoding LoRa: Realizing a Modern LPWAN with SDR. In Proceedings of the GNU Radio Conference, Boulder, CO, USA, 12–16 September 2016; Volume 1. [Google Scholar]
- Claverie, T.; Esteves, J.L. A LoRaWAN Security Assessment Test Bench. In Proceedings of the GNU Radio Conference, Besançon, France, 17–18 June 2021; Volume 2. [Google Scholar]
- Pospisil, O.; Fujdiak, R.; Mikhaylov, K.; Ruotsalainen, H.; Misurec, J. Testbed for LoRaWAN Security: Design and Validation through Man-in-the-Middle Attacks Study. Appl. Sci. 2021, 11, 7642. [Google Scholar] [CrossRef]
- Monjur, M.M.R.; Heacock, J.; Sun, R.; Yu, Q. An Attack Analysis Framework for LoRaWAN applied Advanced Manufacturing. In Proceedings of the 2021 IEEE International Symposium on Technologies for Homeland Security (HST), Boston, MA, USA, 8–9 November 2021; pp. 1–7. [Google Scholar] [CrossRef]
- Hou, N.; Zheng, Y. CloakLoRa: A Covert Channel over LoRa PHY. In Proceedings of the 2020 IEEE 28th International Conference on Network Protocols (ICNP), Madrid, Spain, 13–16 October 2020; pp. 1–11. [Google Scholar] [CrossRef]
- Huang, C.Y.; Lin, C.W.; Cheng, R.G.; Yang, S.J.; Sheu, S.T. Experimental Evaluation of Jamming Threat in LoRaWAN. In Proceedings of the 2019 IEEE 89th Vehicular Technology Conference (VTC2019-Spring), Kuala Lumpur, Malaysia, 28 April–1 May 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Martinez, I.; Tanguy, P.; Nouvel, F. On the performance evaluation of LoRaWAN under Jamming. In Proceedings of the 2019 12th IFIP Wireless and Mobile Networking Conference (WMNC), Paris, France, 11–13 September 2019; pp. 141–145. [Google Scholar] [CrossRef]
- Danish, S.M.; Qureshi, H.K.; Jangsher, S. Jamming Attack Analysis of Wireless Power Transfer on LoRaWAN Join Procedure. In Proceedings of the 2018 IEEE Globecom Workshops (GC Wkshps), Abu Dhabi, United Arab Emirates, 9–13 December 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Tomasin, S.; Zulian, S.; Vangelista, L. Security Analysis of LoRaWAN Join Procedure for Internet of Things Networks. In Proceedings of the 2017 IEEE Wireless Communications and Networking Conference Workshops (WCNCW), San Francisco, CA, USA, 19–22 March 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Fukushima, K.; Marion, D.; Nakano, Y.; Facon, A.; Kiyomoto, S.; Guilley, S. Experiment on Side-Channel Key-Recovery using a Real LPWA End-device. In Proceedings of the 5th International Conference on Information Systems Security and Privacy—ICISSP, Prague, Czech Republic, 23–25 February 2019; pp. 67–74. [Google Scholar] [CrossRef]
- Xu, J.; Tang, Y.; Wang, Y.; Wang, X. A Practical Side-Channel Attack of a LoRaWAN Module Using Deep Learning. In Proceedings of the 2019 IEEE 13th International Conference on Anti-counterfeiting, Security, and Identification (ASID), Xiamen, China, 25–27 October 2019; pp. 17–21. [Google Scholar] [CrossRef]
- Petajajarvi, J.; Mikhaylov, K.; Roivainen, A.; Hanninen, T.; Pettissalo, M. On the coverage of LPWANs: Range evaluation and channel attenuation model for LoRa technology. In Proceedings of the 2015 14th International Conference on ITS Telecommunications (ITST), Copenhagen, Denmark, 2–4 December 2015; pp. 55–59. [Google Scholar] [CrossRef]
- GNU Radio LoRa Receiver. Available online: https://github.com/rpp0/gr-lora (accessed on 10 November 2021).
- Lampson, B. A Note on the Confinement Problem. Commun. ACM 1973, 16, 613–615. [Google Scholar] [CrossRef]
- Matyunin, N.; Szefer, J.; Biedermann, S.; Katzenbeisser, S. Covert channels using mobile device’s magnetic field sensors. In Proceedings of the 2016 21st Asia and South Pacific Design Automation Conference (ASP-DAC), Macao, China, 25–28 January 2016; pp. 525–532. [Google Scholar] [CrossRef]
- Vadlamani, S.; Eksioglu, B.; Medal, H.; Nandi, A. Jamming attacks on wireless networks: A taxonomic survey. Int. J. Prod. Econ. 2016, 172, 76–94. [Google Scholar] [CrossRef]
- Rahmadhani, A.; Kuipers, F. When LoRaWAN Frames Collide. In Proceedings of the 12th International Workshop on Wireless Network Testbeds, Experimental Evaluation & Characterization, WiNTECH ’18, New Delhi, India, 2 November 2018; Association for Computing Machinery: New York, NY, USA, 2018; pp. 89–97. [Google Scholar] [CrossRef] [Green Version]
- Lauridsen, M.; Vejlgaard, B.; Kovacs, I.Z.; Nguyen, H.; Mogensen, P. Interference Measurements in the European 868 MHz ISM Band with Focus on LoRa and SigFox. In Proceedings of the WiNTECH ’18, 2017 IEEE Wireless Communications and Networking Conference (WCNC), San Francisco, CA, USA, 19–22 March 2017; pp. 1–6. [Google Scholar] [CrossRef] [Green Version]
- Wadatkar, P.V.; Chaudhari, B.S.; Zennaro, M. Impact of Interference on LoRaWAN Link Performance. In Proceedings of the WiNTECH ’18, 2019 5th International Conference On Computing, Communication, Control and Automation (ICCUBEA), Pune, India, 19–21 September 2019; pp. 1–5. [Google Scholar] [CrossRef]
- Perković, T.; Rudeš, H.; Damjanović, S.; Nakić, A. Low-Cost Implementation of Reactive Jammer on LoRaWAN Network. Electronics 2021, 10, 864. [Google Scholar] [CrossRef]
- Semtech LoRaMAC Reference Implementation. Available online: https://github.com/Lora-net/LoRaMac-node (accessed on 10 November 2021).
- Brier, E.; Clavier, C.; Olivier, F. Correlation Power Analysis with a Leakage Model. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2004, Cambridge, MA, USA, 11–13 August 2004; Joye, M., Quisquater, J.J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 16–29. [Google Scholar]
- Hu, Y.C.; Perrig, A.; Johnson, D. Wormhole attacks in wireless networks. IEEE J. Sel. Areas Commun. 2006, 24, 370–380. [Google Scholar] [CrossRef]
- Gu, C.; Jiang, L.; Tan, R.; Li, M.; Huang, J. Attack-Aware Synchronization-Free Data Timestamping in LoRaWAN. ACM Trans. Sen. Netw. 2021, 18, 1–31. [Google Scholar] [CrossRef]
- Ruotsalainen, H.; Grebeniuk, S. Towards Wireless Secret Key Agreement with LoRa Physical Layer. In Proceedings of the 13th International Conference on Availability, Reliability and Security, ARES 2018, Hamburg, Germany, 27–30 August 2018; Association for Computing Machinery: New York, NY, USA, 2018. [Google Scholar] [CrossRef]
- Junejo, A.K.; Benkhelifa, F.; Wong, B.; McCann, J.A. LoRa-LiSK: A Lightweight Shared Secret Key Generation Scheme for LoRa Networks. IEEE Internet Things J. 2021, 9, 4110–4124. [Google Scholar] [CrossRef]
- Andreas, W.; de la Fuente, A.G.; Christoph, L.; Michael, K. Physical Layer Security based Key Management for LoRaWAN. arXiv 2021, arXiv:cs.CR/2101.02975. [Google Scholar]
- da Cruz, P.I.; Suyama, R.; Loiola, M.B. Increasing key randomness in physical layer key generation based on RSSI in LoRaWAN devices. Phys. Commun. 2021, 49, 101480. [Google Scholar] [CrossRef]
- Demeslay, C.; Gautier, R.; Fiche, A.; Burel, G. Band & Tone Jamming Analysis and Detection on LoRa signals. arXiv 2021, arXiv:2107.07782. [Google Scholar]
- Martinez, I.; Nouvel, F.; Lahoud, S.; Tanguy, P.; El Helou, M. On the performance evaluation of LoRaWAN with re-transmissions under jamming. In Proceedings of the IEEE Symposium on Computers and Communications (ISCC), Rennes, France, 7–10 July 2020; pp. 1–7. [Google Scholar]
- Ahmar, A.U.H.; Aras, E.; Nguyen, T.D.; Michiels, S.; Joosen, W.; Hughes, D. CRAM: Robust Medium Access Control for LPWAN using Cryptographic Frequency Hopping. In Proceedings of the 2020 16th International Conference on Distributed Computing in Sensor Systems (DCOSS), Marina del Rey, CA, USA, 25–27 May 2020; pp. 95–102. [Google Scholar] [CrossRef]
- Ahmar, A.U.H.; Aras, E.; Joosen, W.; Hughes, D. Towards More Scalable and Secure LPWAN Networks Using Cryptographic Frequency Hopping. In Proceedings of the 2019 Wireless Days (WD), Manchester, UK, 24–26 April 2019; pp. 1–4. [Google Scholar] [CrossRef]
- Jiang, Y.; Peng, L.; Hu, A.; Wang, S.; Huang, Y.; Zhang, L. Physical layer identification of LoRa devices using constellation trace figure. EURASIP J. Wirel. Commun. Netw. 2019, 2019, 1–11. [Google Scholar] [CrossRef] [Green Version]
- Elmaghbub, A.; Hamdaoui, B. LoRa Device Fingerprinting in the Wild: Disclosing RF Data-Driven Fingerprint Sensitivity to Deployment Variability. IEEE Access 2021, 9, 142893–142909. [Google Scholar] [CrossRef]
- Das, R.; Gadre, A.; Zhang, S.; Kumar, S.; Moura, J.M. A deep learning approach to IoT authentication. In Proceedings of the IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar]
- Drive It Like You Hacked It: New At-Tacks and Tools to Wirelessly Steal Cars. Available online: https://samy.pl/defcon2015/2015-defcon.pdf (accessed on 16 February 2022).
- Maurer, U. Secret key agreement by public discussion from common information. IEEE Trans. Inf. Theory 1993, 39, 733–742. [Google Scholar] [CrossRef] [Green Version]
- Xu, W.; Zhang, J.; Huang, S.; Luo, C.; Li, W. Key Generation for Internet of Things: A Contemporary Survey. ACM Comput. Surv. 2021, 54, 3429740. [Google Scholar] [CrossRef]
- Xia, X.; Zheng, Y.; Gu, T. FTrack: Parallel Decoding for LoRa Transmissions. IEEE/ACM Trans. Netw. 2020, 28, 2573–2586. [Google Scholar] [CrossRef]
- Shen, G.; Zhang, J.; Marshall, A.; Valkama, M.; Cavallaro, J. Radio Frequency Fingerprint Identification for Security in Low-Cost IoT Devices. In Proceedings of the Asilomar, Pacific Grove, CA, USA, 31 October–3 November 2021. [Google Scholar]
- Jeon, Y.; Kang, Y. Implementation of a LoRaWAN protocol processing module on an embedded device using Secure Element. In Proceedings of the 2019 34th International Technical Conference on Circuits/Systems, Computers and Communications (ITC-CSCC), JeJu, Korea, 23–26 June 2019; pp. 1–3. [Google Scholar] [CrossRef]
- Semtech SX127x, Low Power Long Range Transceiver. Available online: https://www.semtech.com/products/wireless-rf/lora-transceivers/sx1276 (accessed on 20 February 2022).
- WARP Project. Available online: http://warpproject.org (accessed on 10 November 2021).
- openwifi. Available online: https://github.com/open-sdr/openwifi (accessed on 6 February 2022).
- Mahfoudi, M.; Sivadoss, G.; Bensouda Korachi, O.; Turletti, T.; Dabbous, W. Joint range extension and localization for LPWAN. Internet Technol. Lett. 2019, 2, e120. [Google Scholar] [CrossRef]
- Zeng, H.; Cao, C.; Li, H.; Yan, Q. Enabling jamming-resistant communications in wireless MIMO networks. In Proceedings of the 2017 IEEE Conference on Communications and Network Security (CNS), Las Vegas, NV, USA, 9–11 October 2017; pp. 1–9. [Google Scholar] [CrossRef]
- Huang, P.; Wang, X. Fast secret key generation in static wireless networks: A virtual channel approach. In Proceedings of the 2013 Proceedings IEEE INFOCOM, Turin, Italy, 14–19 April 2013; pp. 2292–2300. [Google Scholar] [CrossRef]



| Reference | Year | Physical Layer Attacks | Physical Layer Countermeasures |
|---|---|---|---|
| [9] | 2020 | moderate | moderate |
| [34] | 2021 | moderate | moderate |
| [35] | 2020 | superficial | - |
| [37] | 2019 | moderate | moderate |
| [36] | 2020 | moderate | superficial |
| [38] | 2021 | - | - |
| This work | 2022 | comprehensive | comprehensive |
| Reference | Attack Category | Affects * | Technology | Experimental Results |
|---|---|---|---|---|
| [41] | Sniffers | C | LoRaWAN 1.0x | yes |
| [42] | Sniffers | C | LoRaWAN 1.0x | no |
| [43] | Sniffers | C | LoRaWAN 1.0x | yes |
| [44] | Sniffers | C | LoRaWAN 1.0x | yes |
| [45] | Covert Channels | C,I | LoRaWAN 1.0x | yes |
| [46] | Jamming | A | LoRaWAN 1.0x | yes |
| [47] | Jamming | A | LoRaWAN 1.0x | no |
| [12] | Jamming | A | LoRaWAN 1.0x | yes |
| [13] | Jamming | A | LoRaWAN 1.1/1.0x | yes |
| [48] | Jamming | A | LoRaWAN 1.0x | no |
| [49] | Jamming | A | LoRaWAN 1.0x | yes |
| [50] | Key Extraction | C,I | LoRaWAN 1.0x | yes |
| [51] | Key Extraction | C,I | LoRaWAN 1.03 | yes |
| [37] | Key Extraction | C,I | LoRaWAN 1.0x | no |
| [12] | Worm-Hole | A | LoRaWAN 1.0x | yes |
| [13] | Worm-Hole | A | LoRaWAN 1.1/1.0x | yes |
| [11] | Energy attack | A | LoRaWAN 1.1/1.0x | yes |
| Ref. | Technique | Enhances * | Advantages | Disadvantages |
|---|---|---|---|---|
| [64] | Replay detection | C | Comprehensive experimental validation | - |
| [65] | Secret key agreement | C,I | Experimental validation | No experiments with LoRaWAN |
| [19] | Secret key agreement | C,I | Quantization for high key randomness | No experiments with LoRaWAN |
| [21] | Secret key agreement | C,I | Effective over long communication distances | Requires reconfigurable antennas |
| [66] | Secret key agreement | C,I | Suitable for mobile and stationary nodes | - |
| [67] | Secret key agreement | C,I | Low algorithmic complexity | Bit disagreement rate |
| [68] | Secret key agreement | C,I | High secret key entropy | Increased algorithmic complexity |
| [22] | Jamming detection | A | Versatile modeling tools for performance evaluation | No large scale validation |
| [23] | Jamming detection | A | High detection accuracy | Only small scale validation |
| [69] | Jamming resilience | A | - | No experimental validation |
| [70] | Jamming resilience | A | - | No experimental validation |
| [24] | Jamming resilience | A | Effective against synchronized jammers | - |
| [71] | Jamming resilience | A | High performance improvement with low overhead | Acknowledged transmissions not supported |
| [72] | Jamming resilience | A | High performance improvement | - |
| [16] | Wireless fingerprinting | U | Investigation on various neural networks | Channel effect is not considered |
| [73] | Wireless fingerprinting | U | Algorithm for manual extraction of RF fingerprints | Experiments on channel robustness are missing |
| [74] | Wireless fingerprinting | U | Both indoor and outdoor experiments. Receiver and channel effects are studied. | Solutions to channel and receiver effects are not provided |
| [75] | Wireless fingerprinting | U | Experiments at various distances are conducted | Solutions to channel effects are not provided |
| [14] | Wireless fingerprinting | U | Consideration on openset/zero-shot classification | Solutions to channel effects are not provided |
| [18] | Wireless fingerprinting | U | Large-scale dataset of 100 LoRa devices. Both outdoor and indoor environments | - |
| [17] | Wireless fingerprinting | U | Design of channel independent spectrogram to mitigate channel effects. | Low SNR outdoor experiments are missing |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ruotsalainen, H.; Shen, G.; Zhang, J.; Fujdiak, R. LoRaWAN Physical Layer-Based Attacks and Countermeasures, A Review. Sensors 2022, 22, 3127. https://doi.org/10.3390/s22093127
Ruotsalainen H, Shen G, Zhang J, Fujdiak R. LoRaWAN Physical Layer-Based Attacks and Countermeasures, A Review. Sensors. 2022; 22(9):3127. https://doi.org/10.3390/s22093127
Chicago/Turabian StyleRuotsalainen, Henri, Guanxiong Shen, Junqing Zhang, and Radek Fujdiak. 2022. "LoRaWAN Physical Layer-Based Attacks and Countermeasures, A Review" Sensors 22, no. 9: 3127. https://doi.org/10.3390/s22093127
APA StyleRuotsalainen, H., Shen, G., Zhang, J., & Fujdiak, R. (2022). LoRaWAN Physical Layer-Based Attacks and Countermeasures, A Review. Sensors, 22(9), 3127. https://doi.org/10.3390/s22093127






