A Triggering Mechanism for Cyber-Attacks in Naval Sensors and Systems †
Abstract
1. Introduction
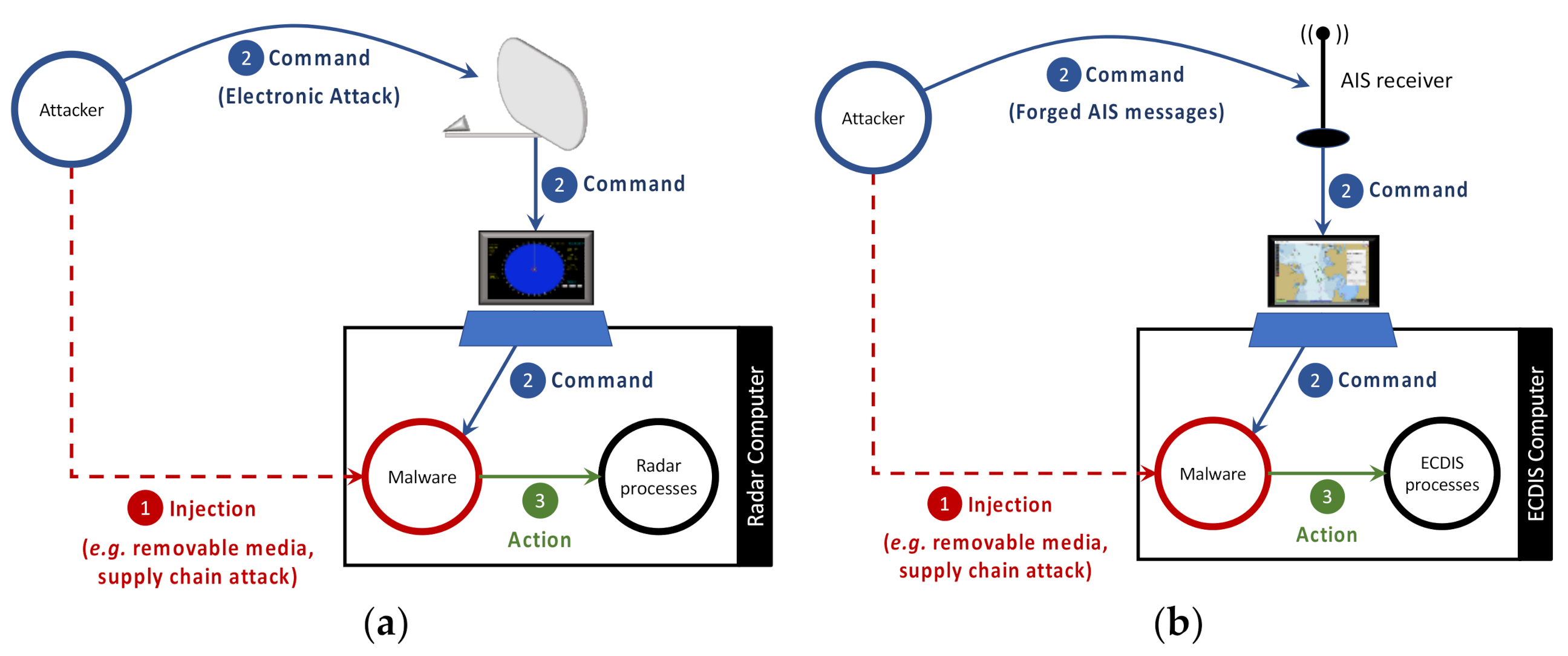
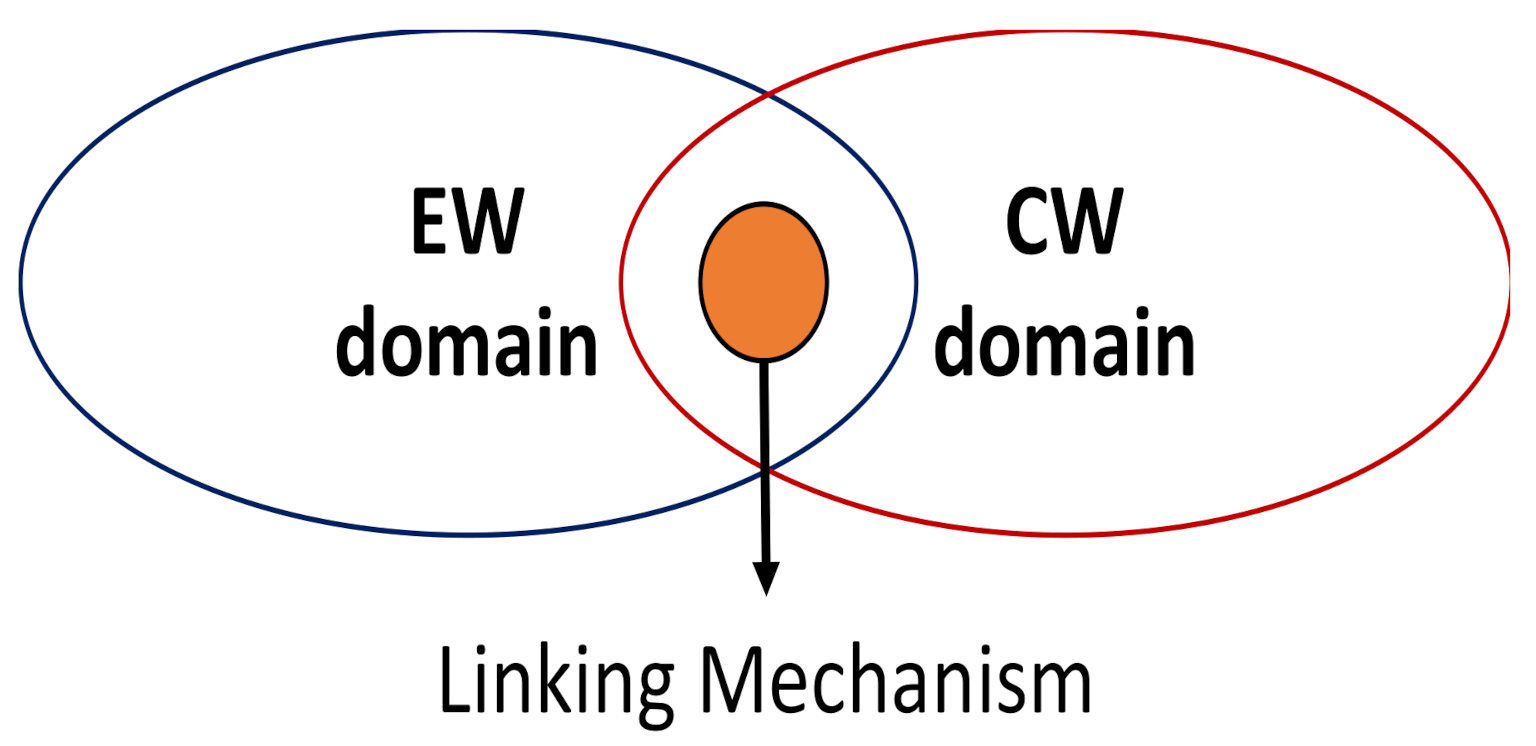
- The proposal of an attack concept where the radar antenna is exploited as open door for receiving malicious commands remotely sent to a cyber threat hosted on the radar computer. In this attack the malicious command is transmitted to the radar through an EA;
- The proposal of an attack concept where the AIS receiver is exploited as open door for receiving malicious commands remotely sent to a cyber threat hosted on an AIS/ECDIS setup (i.e., a navigation system where an AIS is connected to an ECDIS). In this attack the malicious command is transmitted to the AIS/ECDIS setup through forged AIS messages;
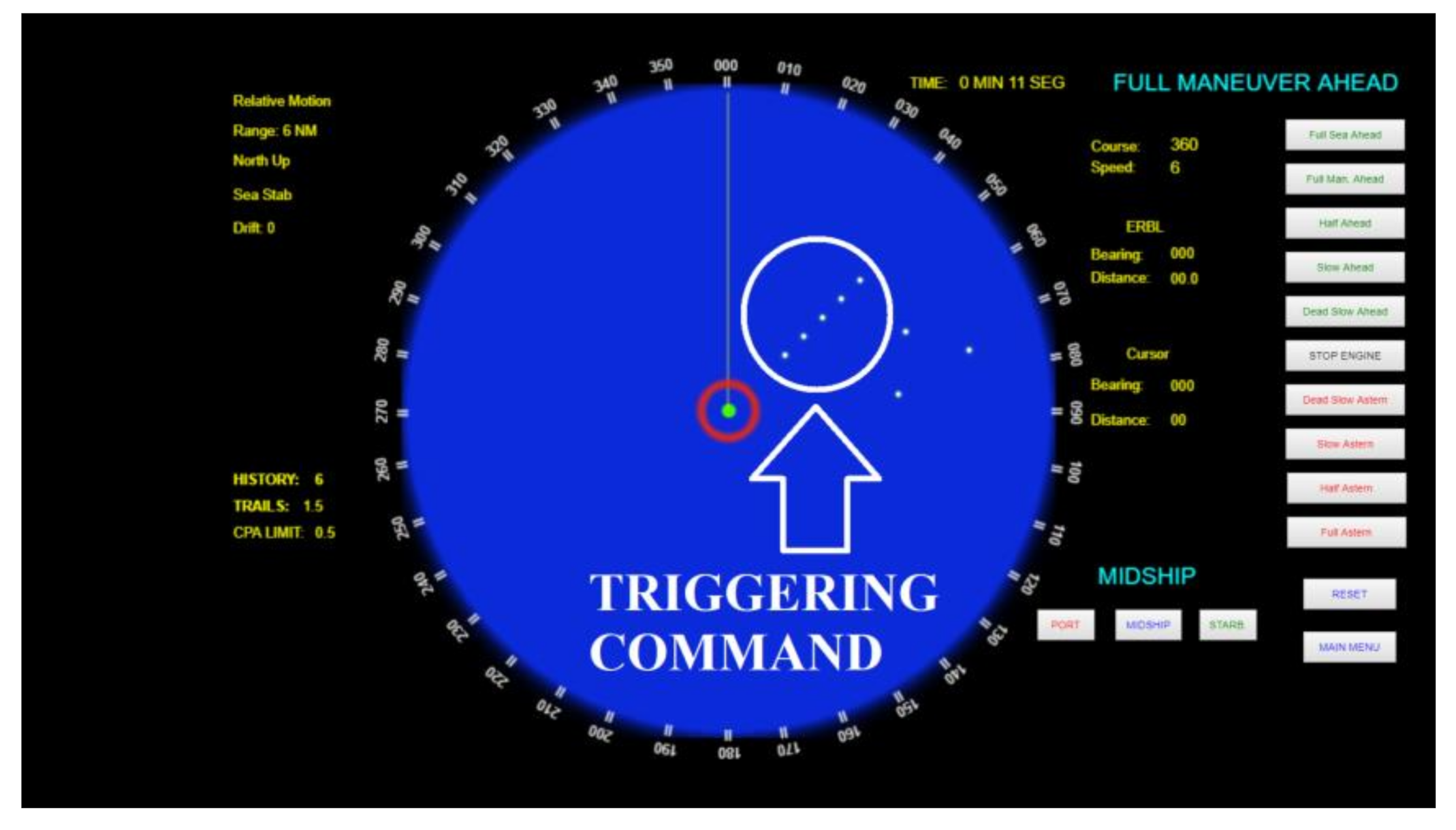
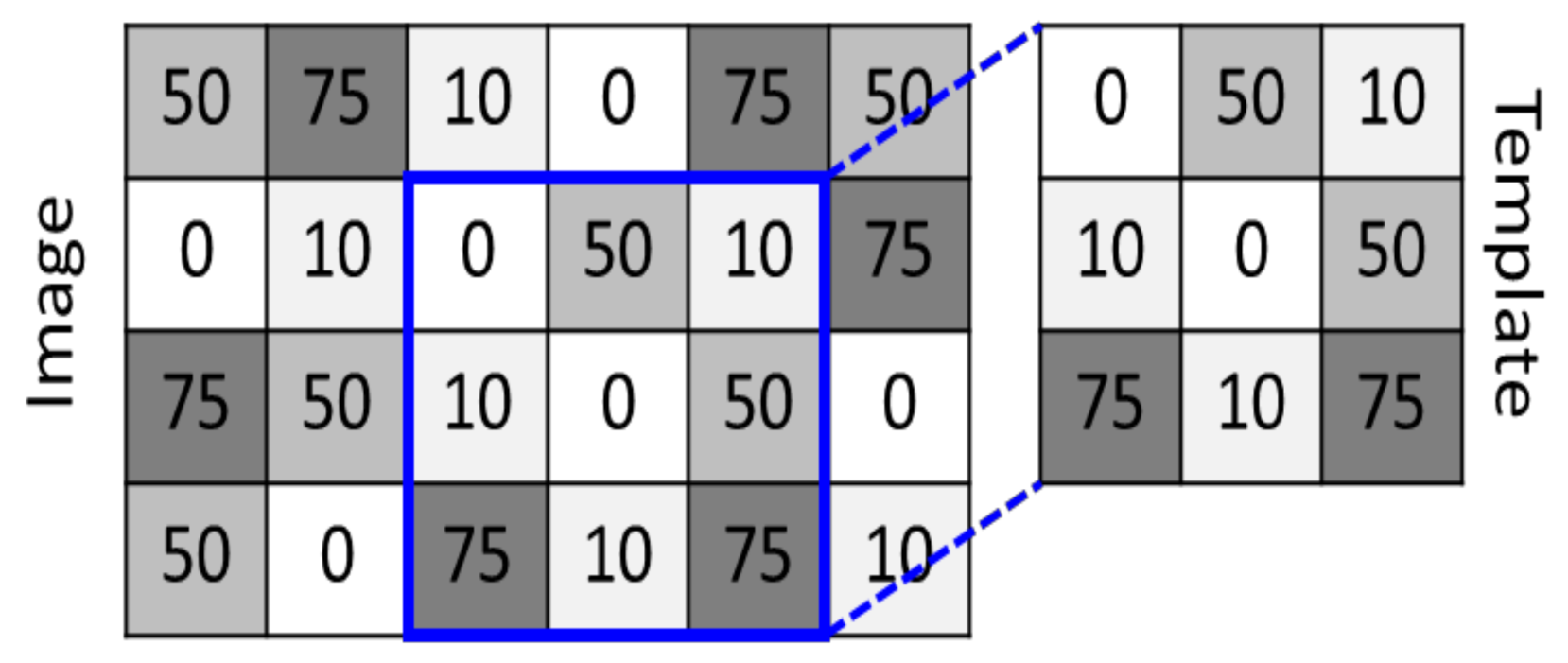
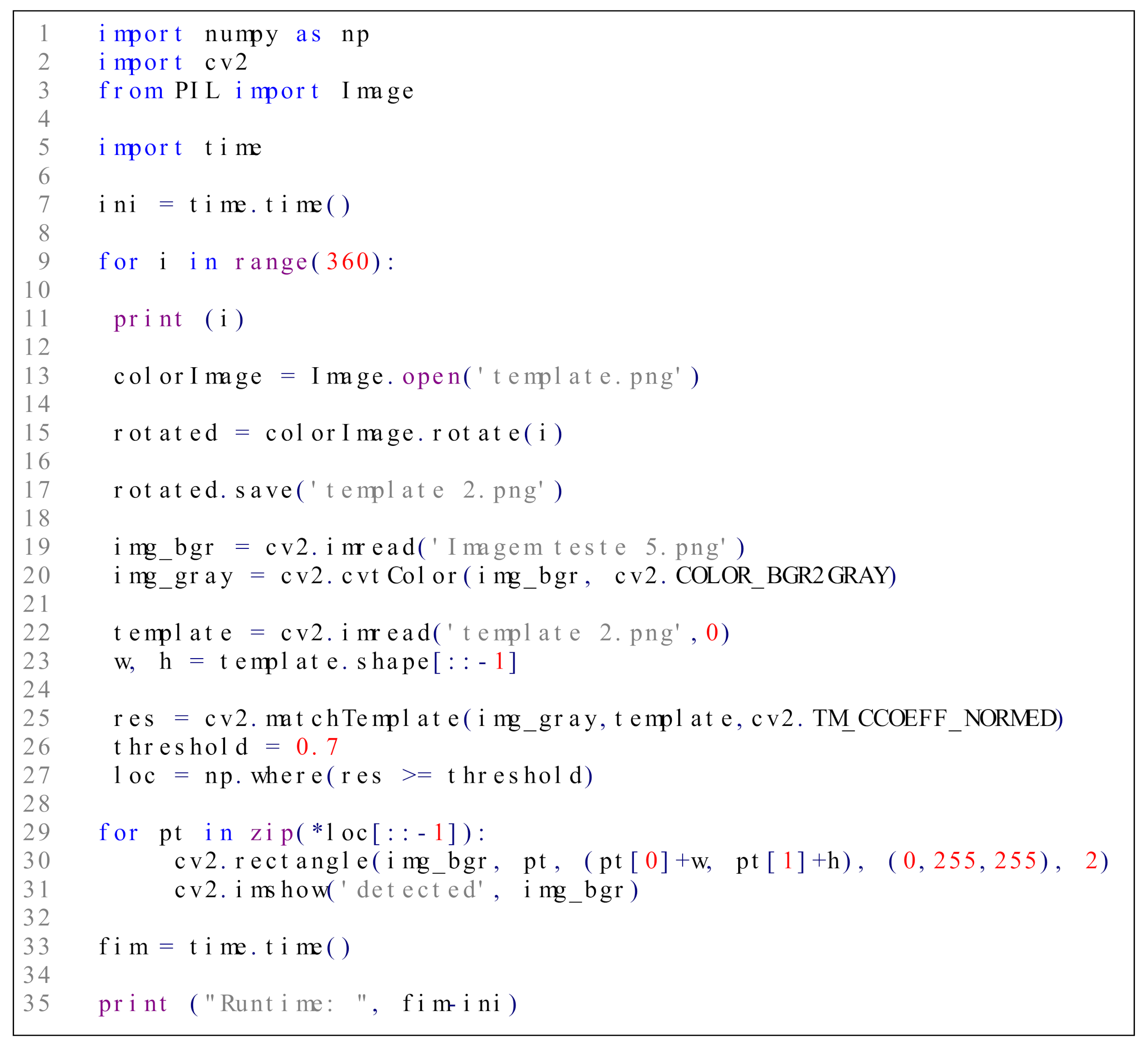
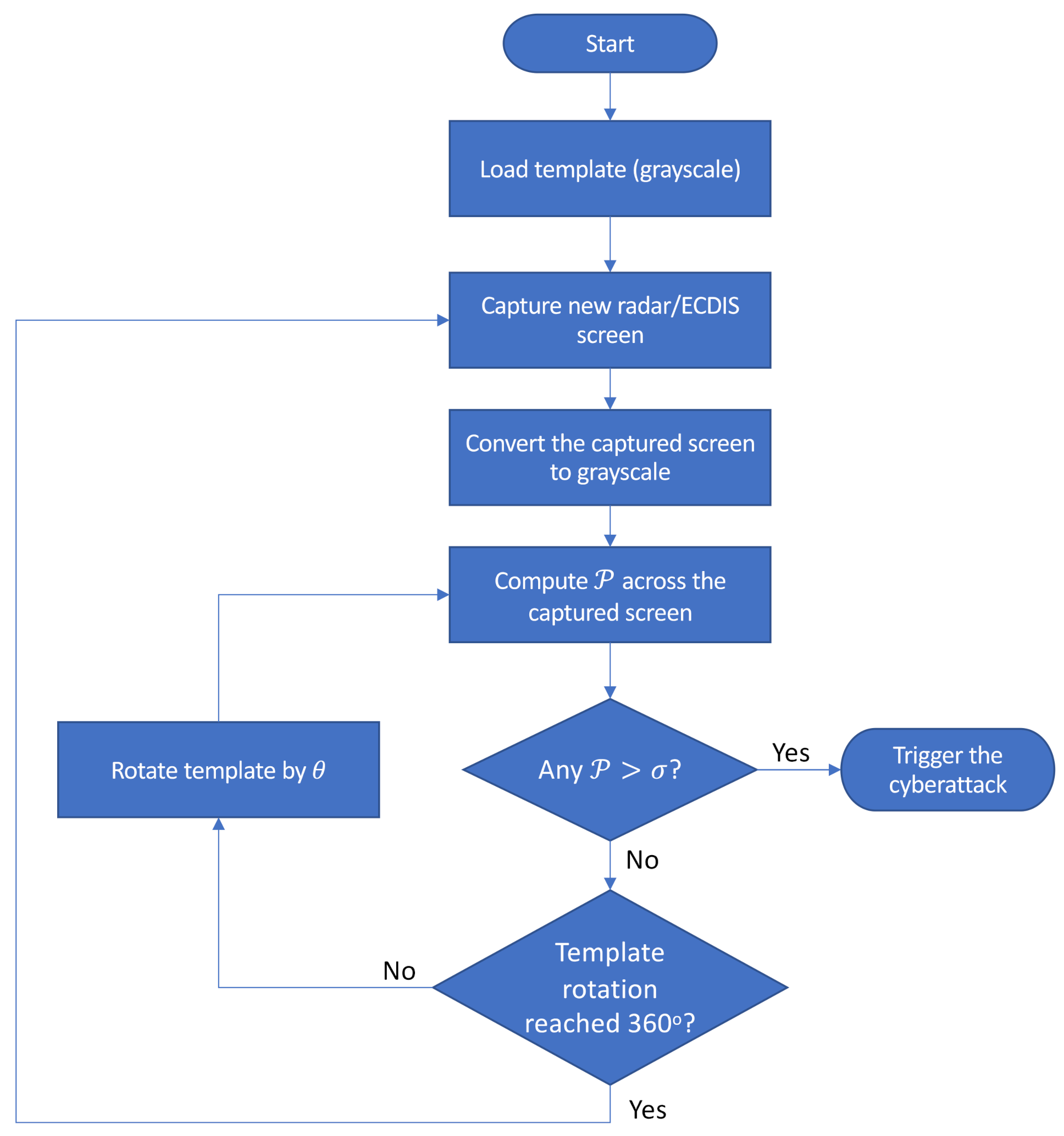
- The demonstration that a template matching technique is suitable to serve as a triggering mechanism capable of accurately acknowledging attack commands received and displayed in both radar PPI and ECDIS screens.
2. Related Works
3. Attack Triggering Mechanism
| Systems | Main Contributions | ||||||
|---|---|---|---|---|---|---|---|
| Ref. | Radar | AIS | ECDIS | INS | GMDSS | Studies on Attacks | Studies on Countermeasures |
| [24] | X | - | Describes a taxonomy to support the creation of adversarial cyber models, risk mitigation, and resiliency plans as applied to the maritime industry. | ||||
| [12,13] | X | - | Proposes an analysis method that covers interviews with the ship’s crew and vulnerability scanning on ECDIS to identify threats and assess cyber risks. | ||||
| [14] | X | X | Summarizes main types of cyberattacks in the shipping industry and their stages. | Discusses general measures for mitigating cyberattacks on ships: physical cybersecurity; recommendations for protecting radio systems; email and browser protection; and use of IDS in networked ship systems. | |||
| [19] | X | X | X | Discusses security threats related to network communication in smart ships. | Proposes a network topology that enables secure communication in smart ships, dividing the ship’s network into multiple zones. | ||
| [25] | X | - | Proposes a certificate-less Identity-Based Cryptography (IBC) along with pseudo-random Maritime Mobile Service Identity (MMSI) to enhance AIS security. | ||||
| [3] | X | X | X | - | Applies the Secure Tropos methodology to systematically draw the security requirements of the three most vulnerable systems onboard a Cyber-Enabled Ship (C-ES), namely the AIS, the ECDIS and the GMDSS. | ||
| [20] | X | - | Presents a methodology that covers interviews with the ship’s crew and vulnerability scanning at the INS to identify threats and assess cyber risks on ships. | ||||
| [21] | X | - | Identification of vulnerabilities in an ECDIS backup arrangement (in its underlying operating system and third-party applications) using the Nessus Professional scanning tool. | ||||
| [22] | X | - | Presents an analysis of the cyber security weaknesses originating from the third-party components of the ECDIS software. | ||||
| [23] | X | - | Assesses critical cyber threat vectors resulting from uncontrolled internetworking of unmaintained ECDIS workstations with identical hardware and software configurations. | ||||
| [26] | X | - | Proposes the Protected AIS (pAIS): an implementation using public-key cryptography methods to address AIS security vulnerabilities. | ||||
| Present study | X | X | X | Describes a method through which cyberattacks targeting naval sensors and systems can be remotely triggered using the ship’s radar or AIS as open door for receiving malicious commands. | - | ||
3.1. Cybersecurity Attack Model
- Command Stage: the attacker remotely sends attack commands to the malware hosted on the target system. When attacking a radar system, the command is transmitted to the malware through an EA. When attacking an AIS/ECDIS setup, the command is transmitted using forged AIS messages. In this stage, the malware keeps monitoring the data received by the radar or AIS, seeking for a pattern corresponding to the attack command. If command is received and acknowledged by the malware, then the third stage (Action Stage) is triggered.
- Action Stage: in this stage the malware manipulates the radar or ECDIS computational processes according to the command transmitted by the attacker. Examples of possible harmful actions performed in the targeted system during this stage are reset the system, record and replay scenarios, freeze the system display, etc.
3.2. Triggering Mechanism in a Radar System
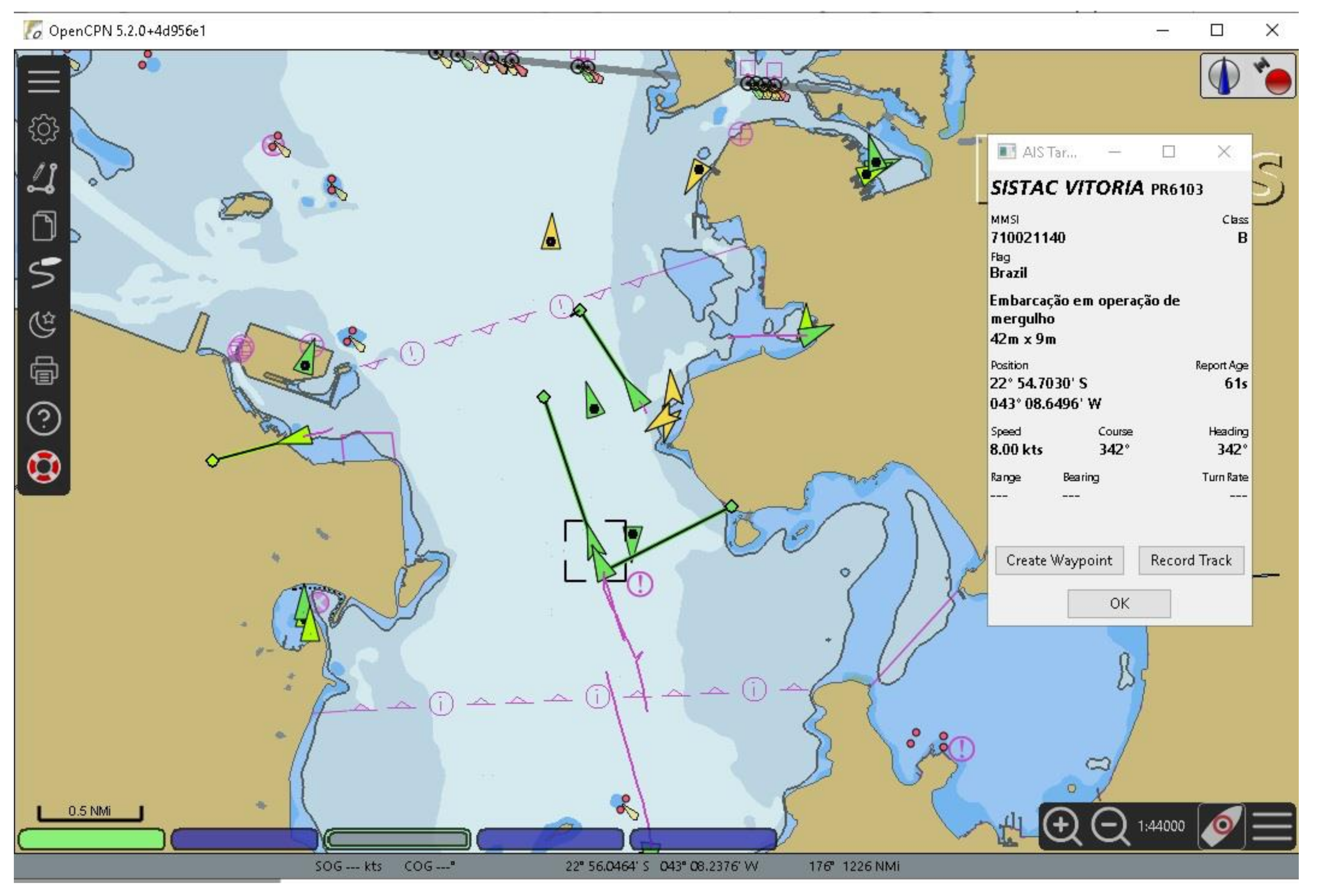
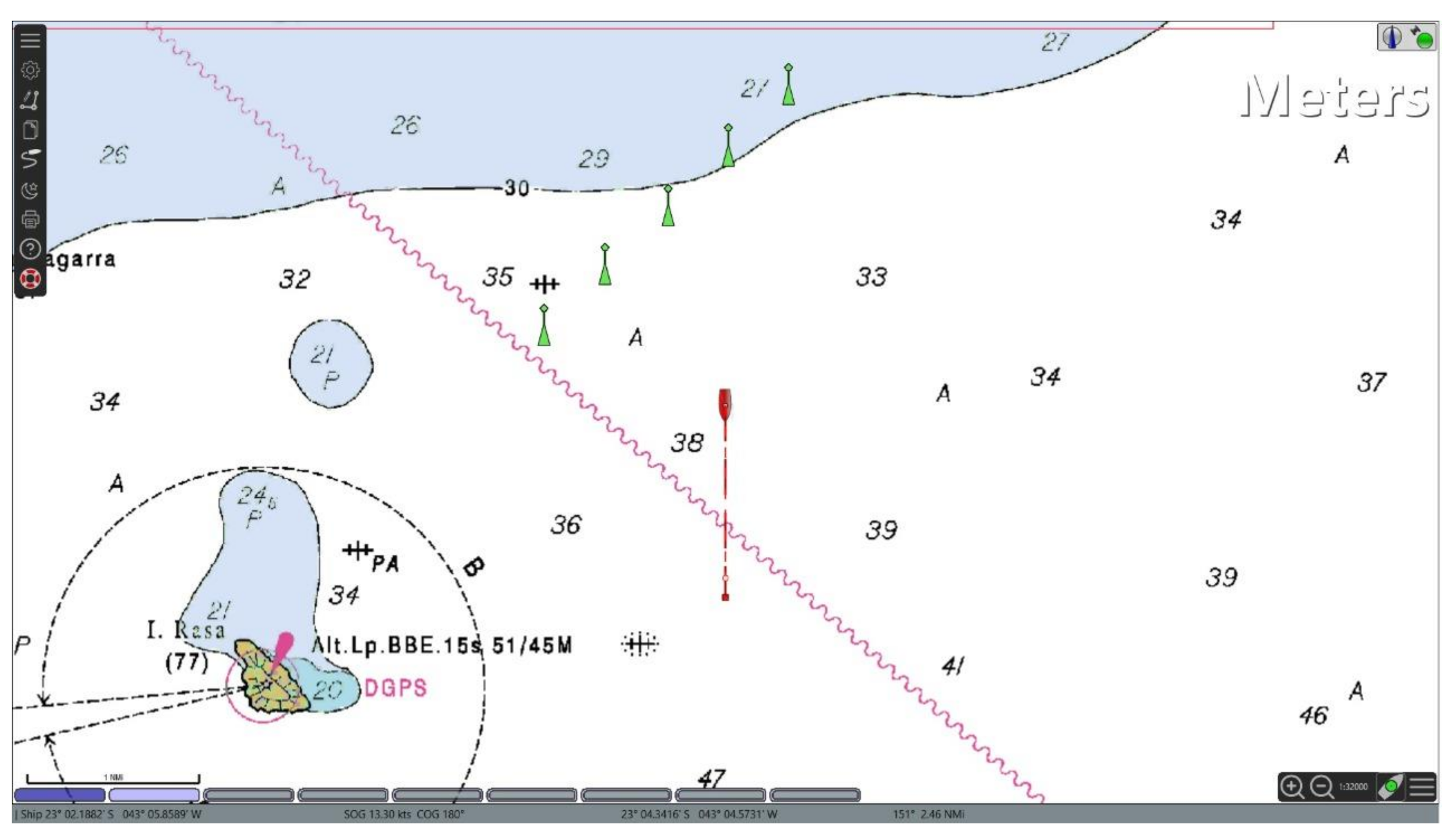
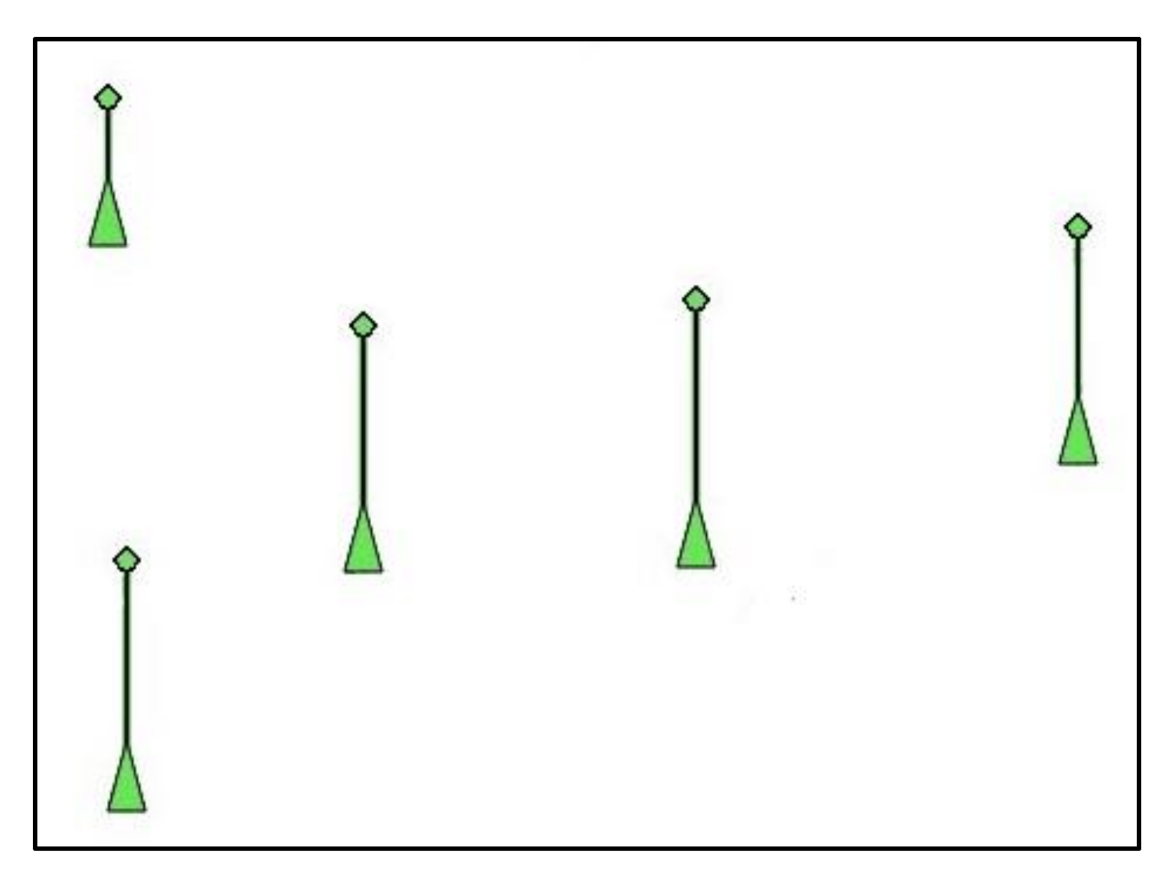
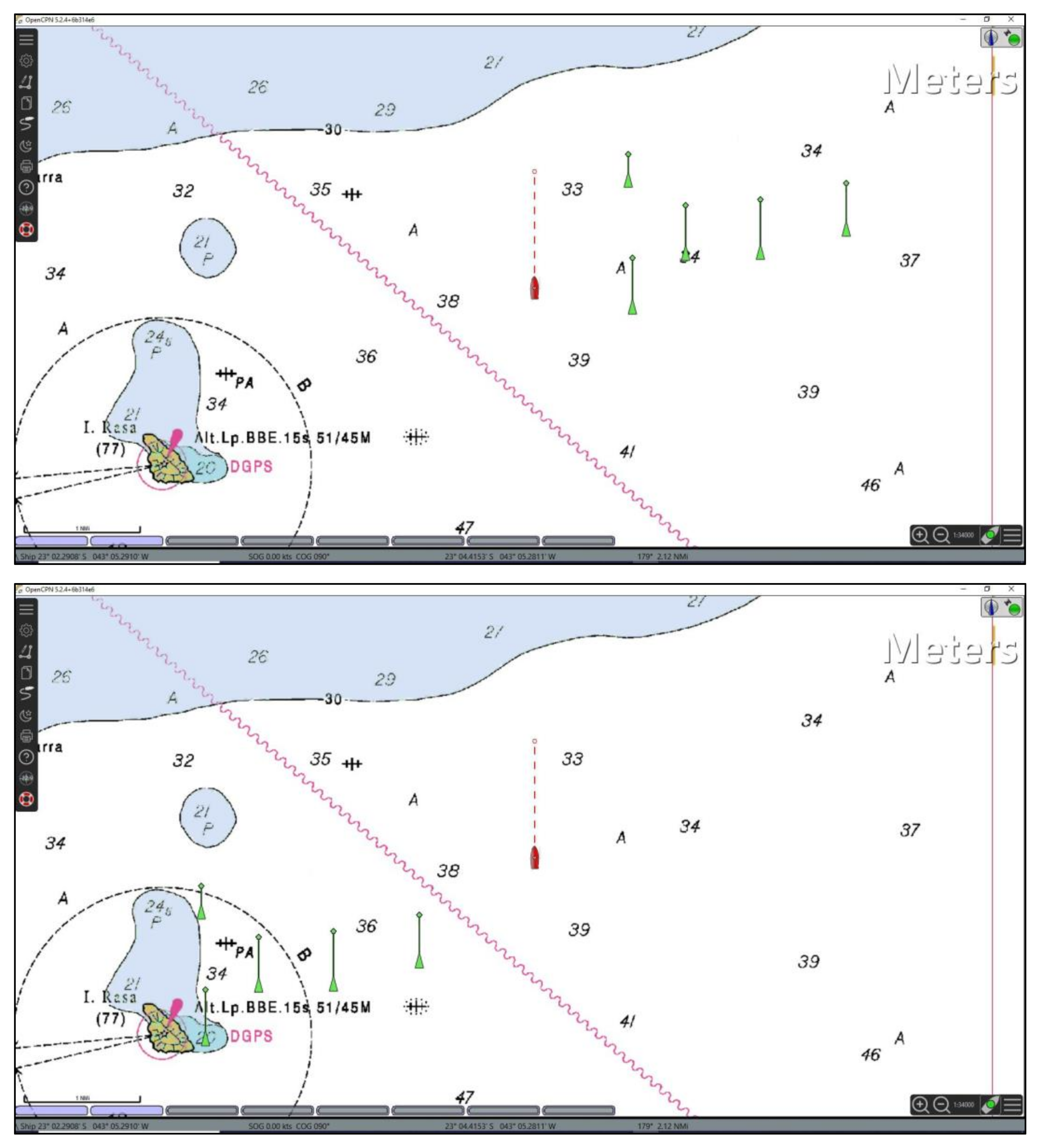
3.3. Triggering Mechanism in a AIS/ECDIS System
3.4. Implementation of the Triggering Mechanism
4. Results
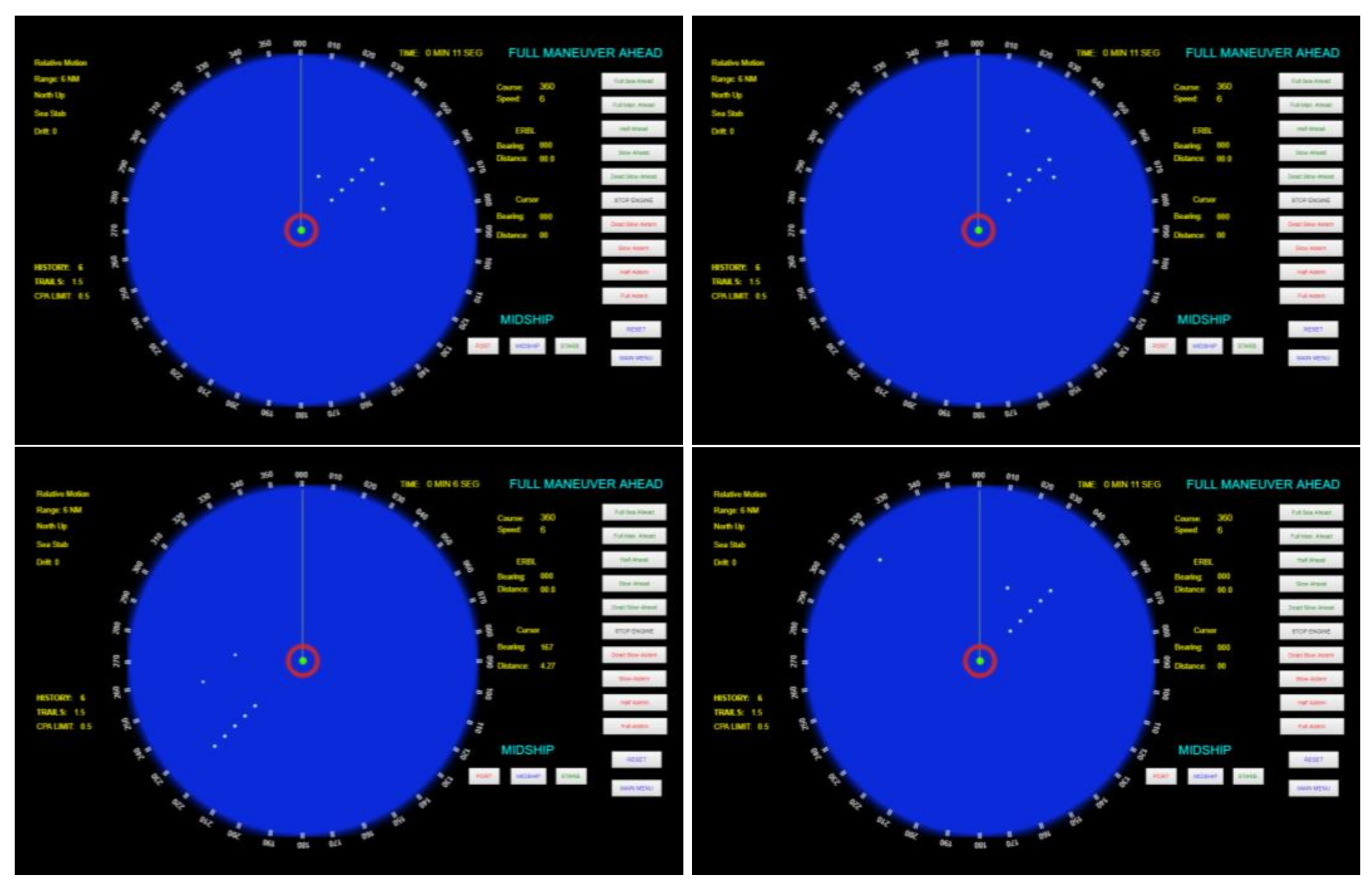
4.1. Simulations of the Radar-Based Attack
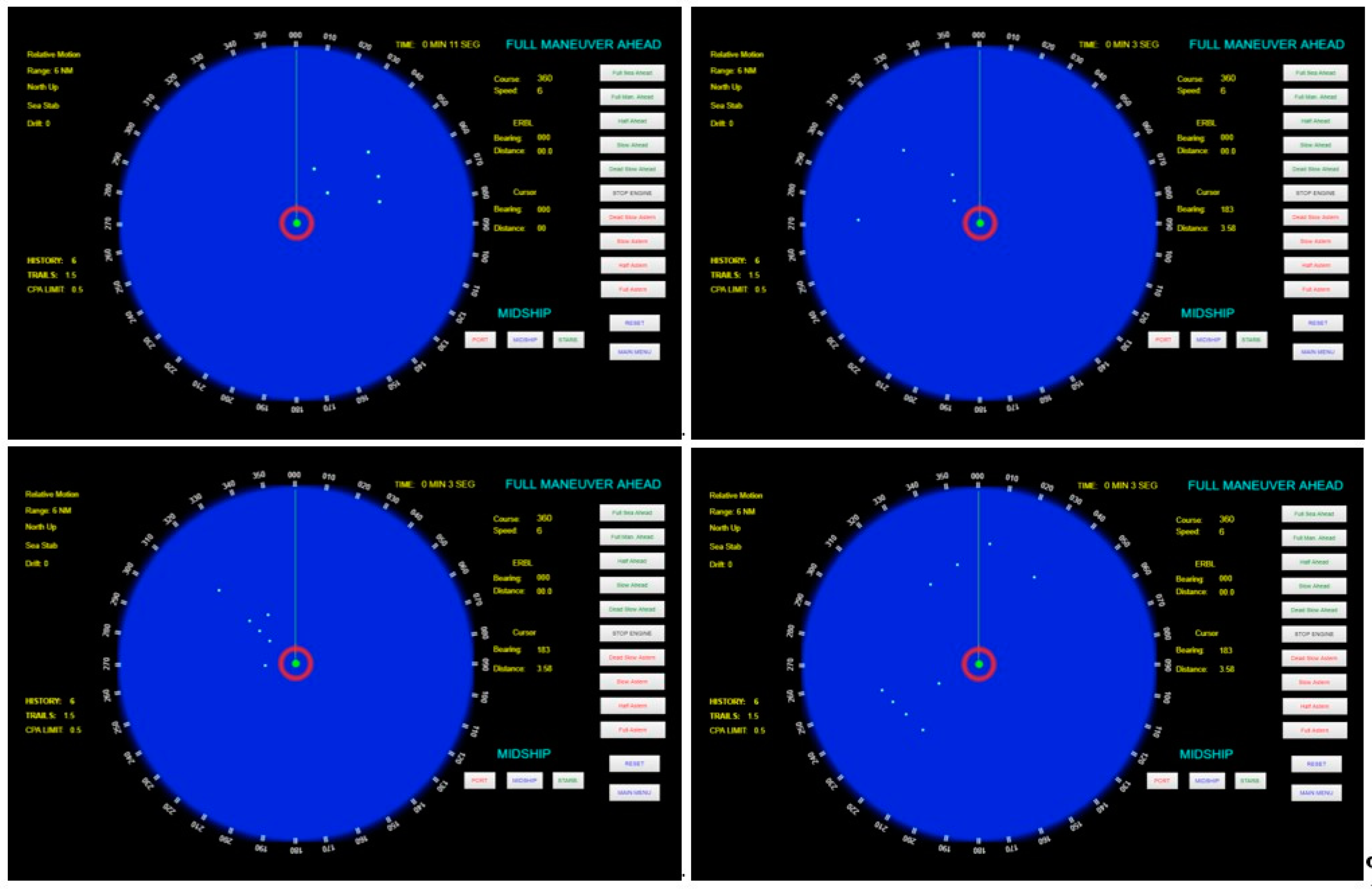
4.2. Simulations of the AIS-Based Attack
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Ruffle, S.; Coburn, A.; Skelton, A.; Evan, T.; Kesaite, V.; Coppack, L.; Maynard, T. Steering the Course—A Different Approach to Modelling Marine Risk; Emerging Risk Report; Society & Security, Centre for Risk Studies (University of Cambridge): Cambridge, UK; Lloyd’s: London, UK, 2018. [Google Scholar]
- Daffron, J.; Ruffle, S.; Andrew, C.; Copic, J.; Quantrill, K. Bashe Attack: Global Infection by Contagious Malware; Centre for Risk Studies (University of Cambridge): Cambridge, UK; Lloyd’s of London: London, UK; Nanyang Technological University: Singapore, 2019. [Google Scholar]
- Kavallieratos, G.; Diamantopoulou, V.; Katsikas, S.K. Shipping 4.0: Security Requirements for the Cyber-Enabled Ship. IEEE Trans. Ind. Inform. 2020, 16, 6617–6625. [Google Scholar] [CrossRef]
- Lund, M.S.; Gulland, J.E.; Hareide, O.S.; Josok, E.; Weum, K.O.C. Integrity of Integrated Navigation Systems. In Proceedings of the 2018 IEEE Conference on Communications and Network Security (CNS), Beijing, China, 30 May–1 June 2018; pp. 1–5. [Google Scholar]
- International Maritime Organization (IMO). Facilitation Committee and Maritime Safety Committee. Guidelines on Mari-Time Cyber Risk Management (MSC-FAL.1/Circ.3, 5.7.2017); International Maritime Organization (IMO): London, UK, 2017. [Google Scholar]
- The President of the United States. National Maritime Cybersecurity Plan; White House Office: Washington, DC, USA, 2020. Available online: https://www.hsdl.org/?view&did=848704 (accessed on 19 March 2021).
- Clarke, R.A.; Knake, R.K. Cyber War; Tantor Media, Incorporated: Old Saybrook, CT, USA, 2014. [Google Scholar]
- Adee, S. The Hunt for the Kill Switch. IEEE Spectrum 2008, 45, 34–39. [Google Scholar] [CrossRef]
- Dipert, R.R. Other-than-Internet (OTI) cyberwarfare: Challenges for ethics, law, and policy. J. Mil. Ethics 2013, 12, 34–53. [Google Scholar] [CrossRef]
- Yang, C.; Feng, L.; Zhang, H.; He, S.; Shi, Z. A novel data fusion algorithm to combat false data injection attacks in net-worked radar systems. IEEE Trans. Signal Inf. Process. Netw. 2018, 4, 125–136. [Google Scholar]
- ITU Radiocommunication Sector. ITU-R M.1371-5 (02/2014). Technical Characteristics for an Automatic Identification System Using Time-Division Multi-ple Access in the VHF Maritime Mobile Band. Geneva. 2014. Available online: https://www.itu.int/rec/R-REC-M.1371-5-201402-I/en (accessed on 30 April 2021).
- Svilicic, B.; Kamahara, J.; Rooks, M.; Yano, Y. Maritime Cyber Risk Management: An Experimental Ship Assessment. J. Navig. 2019, 72, 1108–1120. [Google Scholar] [CrossRef]
- Svilicic, B.; Kamahara, J.; Celic, J.; Bolmsten, J. Assessing ship cyber risks: A framework and case study of ECDIS security. WMU J. Marit. Aff. 2019, 18, 509–520. [Google Scholar] [CrossRef]
- Mednikarov, B.; Tsonev, Y.; Lazarov, A. Analysis of Cybersecurity Issues in the Maritime Industry. Inf. Secur. Int. J. 2020, 47, 27–43. [Google Scholar] [CrossRef]
- Liagkou, V.; Kavvadas, V.; Chronopoulos, S.K.; Tafiadis, D.; Christofilakis, V.; Peppas, K.P. Attack detection for healthcare monitoring systems using mechanical learning in virtual private networks over optical transport layer architecture. Computation 2019, 7, 24. [Google Scholar] [CrossRef]
- Khan, M.A.; Kim, Y. Deep Learning-Based Hybrid Intelligent Intrusion Detection System. Comput. Mater. Contin. 2021, 68, 671–687. [Google Scholar] [CrossRef]
- Daniya, T.; Kumar, K.S.; Kumar, B.S.; Kolli, C.S. A survey on anomaly based intrusion detection system. Mater. Today Proc. 2021. [Google Scholar] [CrossRef]
- Quincozes, S.E.; Albuquerque, C.; Passos, D.; Mossé, D. A survey on intrusion detection and prevention systems in digital substations. Comput. Netw. 2021, 184, 107679. [Google Scholar] [CrossRef]
- Furumoto, K.; Kolehmainen, A.; Silverajan, B.; Takahashi, T.; Inoue, D.; Nakao, K. Toward Automated Smart Ships: De-signing Effective Cyber Risk Management. In Proceedings of the 2020 International Conferences on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData) and IEEE Congress on Cybermatics (Cybermatics), Rhodes, Greece, 2–6 November 2020; pp. 100–105. [Google Scholar]
- Svilicic, B.; Rudan, I.; Jugović, A.; Zec, D. A Study on Cyber Security Threats in a Shipboard Integrated Navigational System. J. Mar. Sci. Eng. 2019, 7, 364. [Google Scholar] [CrossRef]
- Svilicic, B.; Brčic, D.; Žułkin, S.; Kalebic, D. Raising Awareness on Cyber Security of ECDIS. TransNav Int. J. Mar. Navig. Saf. Sea Transp. 2019, 13, 231–236. [Google Scholar] [CrossRef]
- Svilicic, B.; Rudan, I.; Frančić, V.; Doričić, M. Shipboard ECDIS cyber security: Third-party component threats. Pomorstvo 2019, 33, 176–180. [Google Scholar] [CrossRef]
- Svilicic, B.; Kristić, M.; Žuškin, S.; Brčić, D. Paperless ship navigation: Cyber security weaknesses. J. Transp. Secur. 2020, 13, 203–214. [Google Scholar] [CrossRef]
- Kessler, G.C.; Craiger, J.P.; Haass, J.C. A Taxonomy Framework for Maritime Cybersecurity: A Demonstration Using the Automatic Identification System. TransNav Int. J. Mar. Navig. Saf. Sea Transp. 2018, 12, 429–437. [Google Scholar] [CrossRef]
- Goudossis, A.; Katsikas, S.K. Towards a secure automatic identification system (AIS). J. Mar. Sci. Technol. 2019, 24, 410–423. [Google Scholar] [CrossRef]
- Kessler, G.C. Protected AIS: A Demonstration of Capability Scheme to Provide Authentication and Message Integrity. TransNav Int. J. Mar. Navig. Saf. Sea Transp. 2020, 14, 279–286. [Google Scholar] [CrossRef]
- Geer, D. Malicious bots threaten network security. Computer 2005, 38, 18–20. [Google Scholar] [CrossRef]
- Hachem, N.; Ben Mustapha, Y.; Granadillo, G.D.G.; DeBar, H. Botnets: Lifecycle and Taxonomy. In Proceedings of the 2011 Conference on Network and Information Systems Security, La Rochelle, France, 18–21 May 2011; pp. 1–8. [Google Scholar]
- Hayes, C.R. Maritime Cybersecurity: The Future of National Security. Master’s Thesis, Naval Postgraduate School, Monterey, CA, USA, June 2016. [Google Scholar]
- Reed, M.; Miller, J.F.; Popick, P. Supply Chain Attack Patterns: Framework and Catalog; Office of the Deputy Assistant Secretary of Defense for Systems Engineering: Washington, DC, USA, 2014.
- Barabanov, A.; Markov, A.; Tsirlov, V. On Systematics of the Information Security of Software Supply Chains. In Proceedings of the Computational Methods in Systems and Software, Vsetin, Czech Republic, 14–16 October 2020; Springer: Cham, Switzerland, 2020; pp. 115–129. [Google Scholar]
- Sá, A.O.; Machado, R.C.S.; Almeida, N.N. The Convergence of Cyber, Electronic and Kinetic Warfare within the Scope of Sea Power. J. Braz. Nav. War Coll. 2018, 25, 89–128. [Google Scholar] [CrossRef]
- Bhatti, J.; Humphreys, T.E. Hostile Control of Ships via False GPS Signals: Demonstration and Detection. Navigation 2017, 64, 51–66. [Google Scholar] [CrossRef]
- Almslmany, A.; Wang, C.; Cao, Q. Advanced Deceptive Jamming Model Based on DRFM Sub-Nyquist Sampling. In Proceedings of the 2016 13th International Bhurban Conference on Applied Sciences and Technology (IBCAST), Islamabad, Pakistan, 12–16 January 2016; pp. 727–730. [Google Scholar]
- McLaughlin, S.; Konstantinou, C.; Wang, X.; Davi, L.; Sadeghi, A.-R.; Maniatakos, M.; Karri, R. The Cybersecurity Landscape in Industrial Control Systems. Proc. IEEE 2016, 104, 1039–1057. [Google Scholar] [CrossRef]
- Langner, R. Stuxnet: Dissecting a Cyberwarfare Weapon. IEEE Secur. Priv. Mag. 2011, 9, 49–51. [Google Scholar] [CrossRef]
- Zetter, K. Countdown to Zero Day: Stuxnet and the Launch of the World’s First Digital Weapon; Broadway Books: Portland, OR, USA, 2014. [Google Scholar]
- Falliere, N.; Murchu, L.O.; Chien, E. W32. Stuxnet Dossier; Symantec: Sunnyvale, CA, USA, 2010. [Google Scholar]
- Robertson, J.; Riley, M. The Big Hack: How China Used a Tiny Chip to Infiltrate US Companies. Bloomberg Businessweek. 4 October 2018. Available online: https://www.bloomberg.com/news/features/2018-10-04/the-big-hack-how-china-used-a-tiny-chip-to-infiltrate-america-s-top-companies (accessed on 30 April 2021).
- Tavares, Y.M.; Nedjah, N.; Mourelle, L.M. Embedded implementation of template matching using correlation and particle swarm optimization. Int. J. Bio-Inspired Comput. 2018, 11, 102–109. [Google Scholar] [CrossRef]
- International Maritime Organization (IMO). Resolution A.1106(29) Revised Guidelines for the Onboard Operational Use of Shipborne Automatic Identification Sysetm (AIS); International Maritime Organization (IMO): London, UK, 2015. [Google Scholar]
- National Marine Electronics Association (NMEA). NMEA 0183. Standard for Interfacing Marine Electronic Devices; Revision 4.11; National Marine Electronics Association (NMEA): Severna Park, MD, USA, 2018. [Google Scholar]
- International Association of Marine Aids to Navigation and Lighthouse Authorities (IALA). IALA 1082. An Overview of AIS, 2nd ed.; IALA: Saint Germain en Laye, France, 2016. [Google Scholar]
- International Electrotechnical Commision (IEC). IEC 62288. Maritime Navigation and Radiocommunication Equipment and Systems—Presentation of Navigation-Related Information on Shipborne Navigational Displays—General Requirements, Methods of Testing and Required Test Results; International Electrotechnical Commision (IEC): Geneva, Switzerland, 2008. [Google Scholar]
- Balduzzi, M.; Pasta, A.; Wilhoit, K. A security evaluation of AIS automated identification system. In Proceedings of the 30th Annual Computer Security Applica-tions Conference on—ACSAC’14, New Orleans, LA, USA, 8–12 December 2014. [Google Scholar] [CrossRef]
- Centro de Hidrografia da Marinha, Baía de Guanabara. Available online: https://www.marinha.mil.br/chm/dados-do-segnav-cartas-raster/baia-de-guanabara (accessed on 7 February 2021).
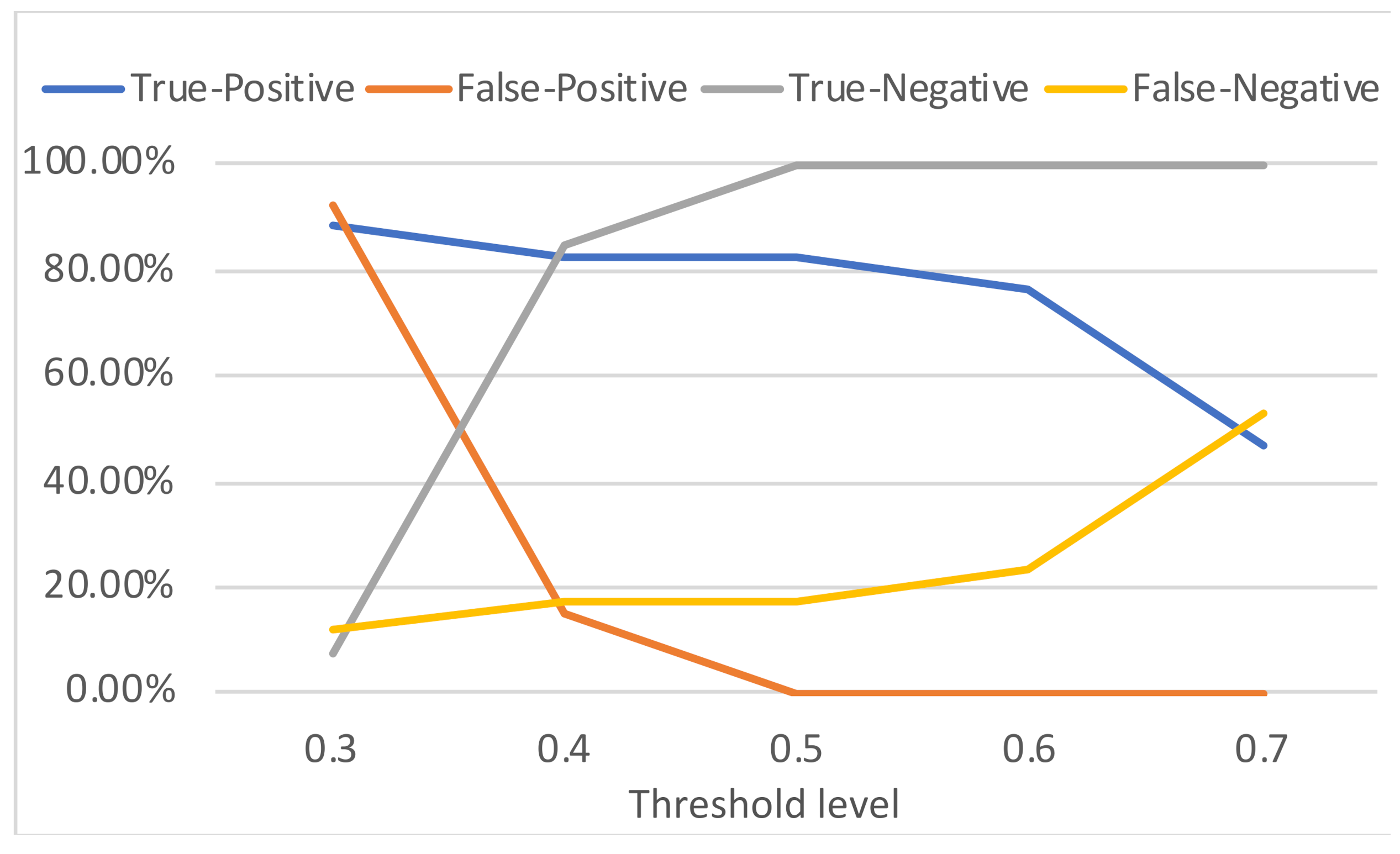
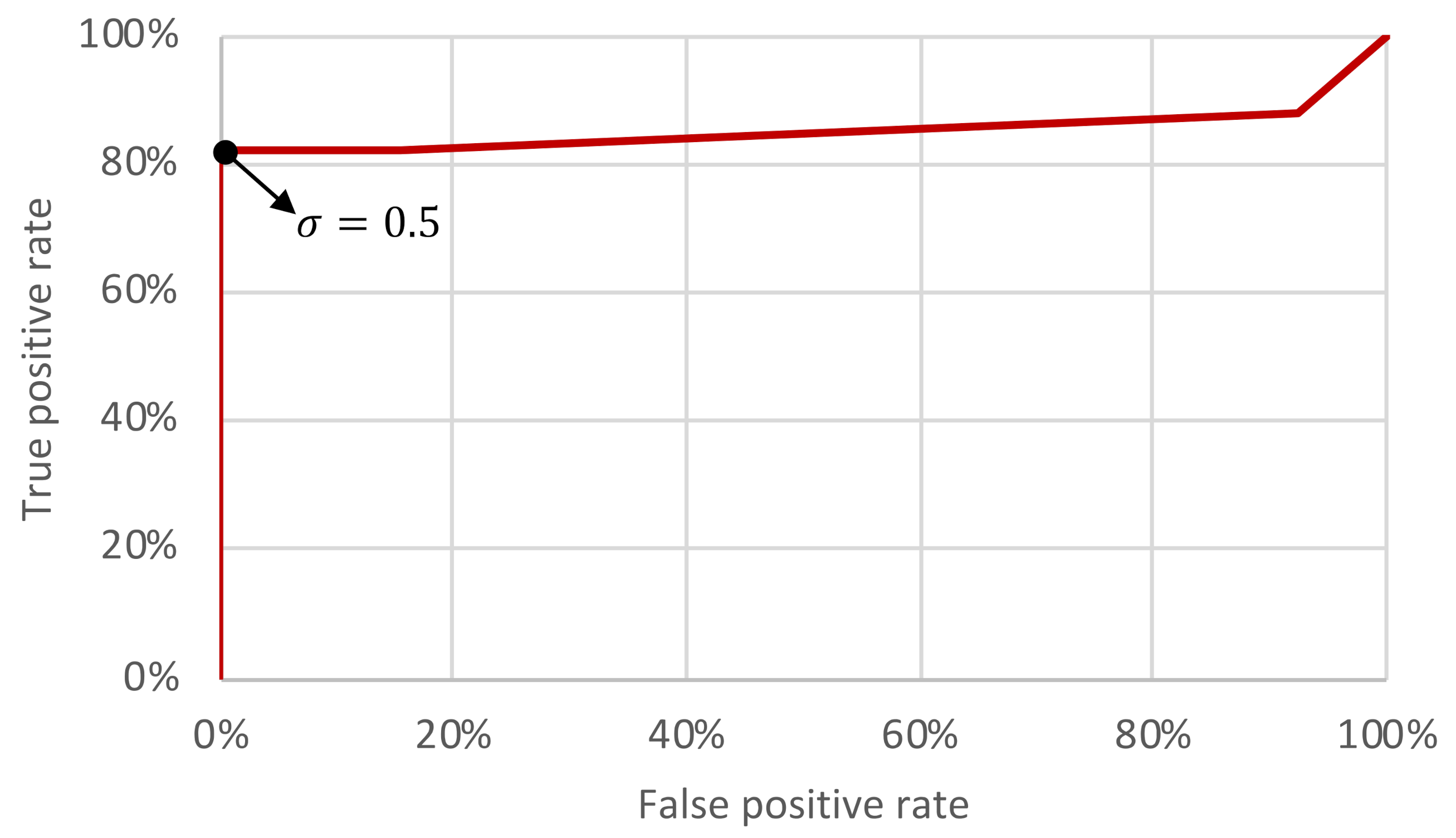

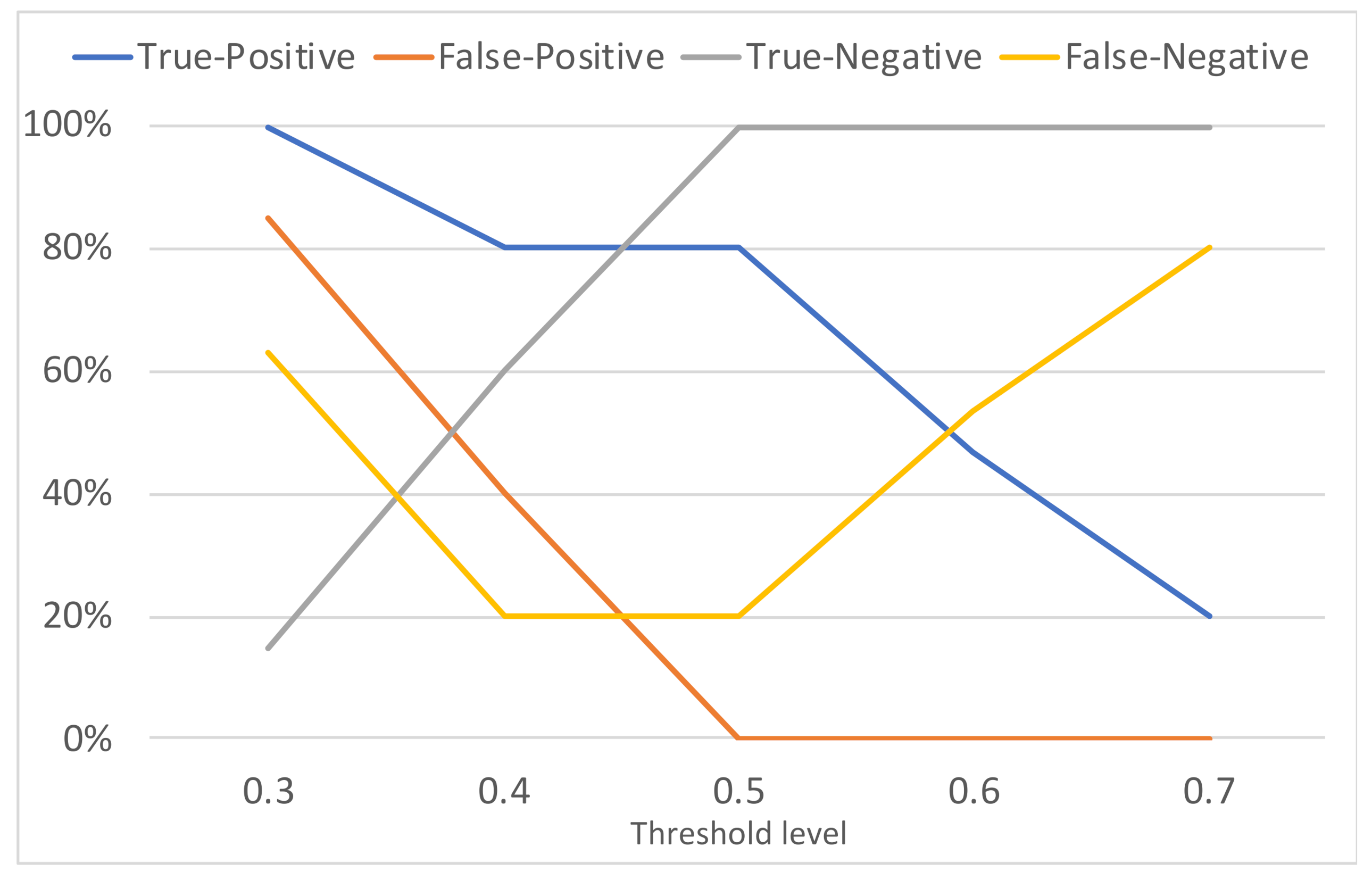
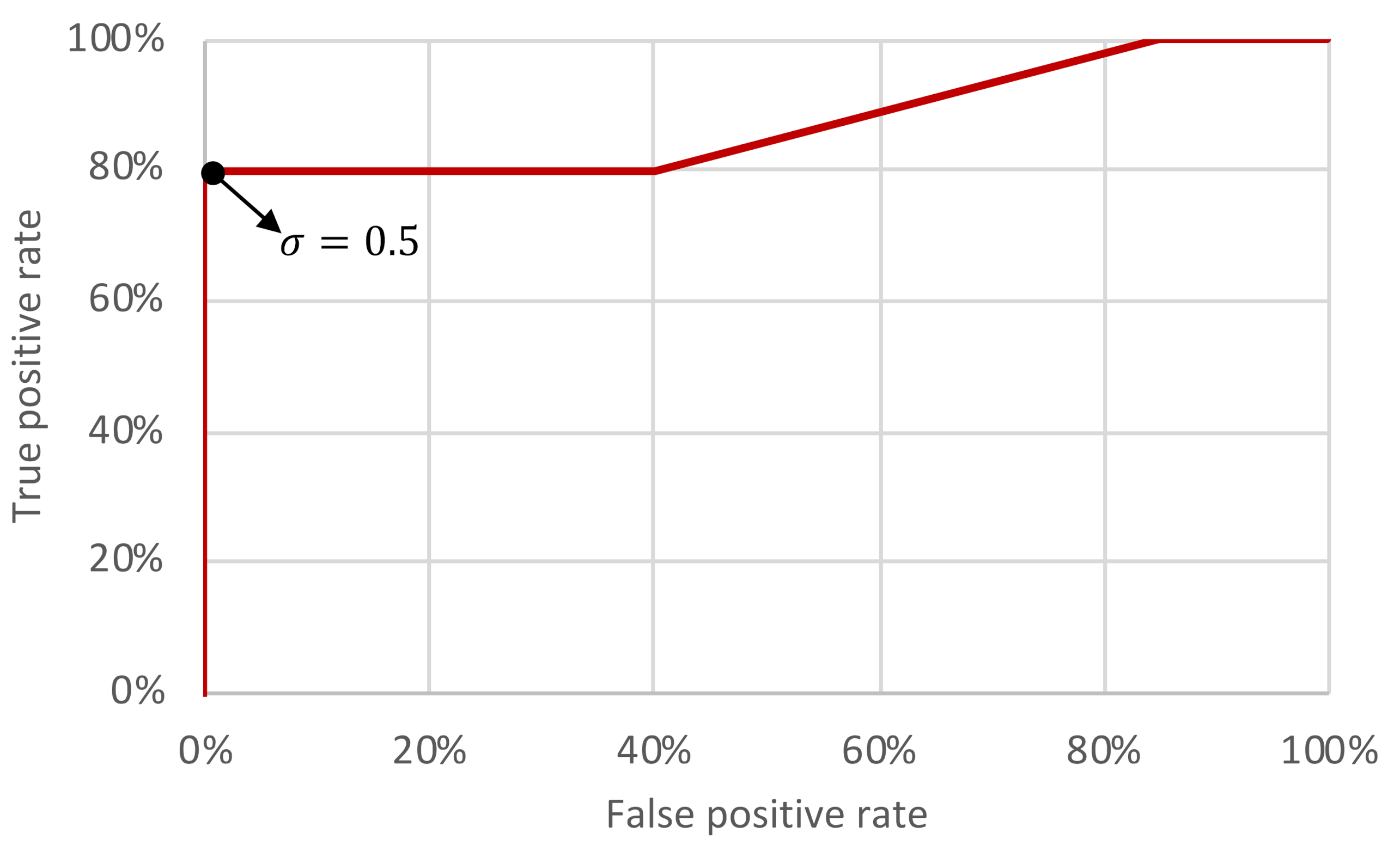
| Actual Condition | ||||
|---|---|---|---|---|
| Positive | Negative | Accuracy | ||
| Predicted positive | 15 | 12 | 0.53 | |
| Predicted negative | 2 | 1 | ||
| Predicted positive | 14 | 2 | 0.83 | |
| Predicted negative | 3 | 11 | ||
| Predicted positive | 14 | 0 | 0.90 | |
| Predicted negative | 3 | 13 | ||
| Predicted positive | 13 | 0 | 0.86 | |
| Predicted negative | 4 | 13 | ||
| Predicted positive | 8 | 0 | 0.70 | |
| Predicted negative | 9 | 13 | ||
| Actual Condition | ||||
|---|---|---|---|---|
| Positive | Negative | Accuracy | ||
| Predicted positive | 10 | 17 | 0.43 | |
| Predicted negative | 0 | 3 | ||
| Predicted positive | 8 | 8 | 0.66 | |
| Predicted negative | 2 | 12 | ||
| Predicted positive | 8 | 0 | 0.93 | |
| Predicted negative | 2 | 20 | ||
| Predicted positive | 7 | 0 | 0.90 | |
| Predicted negative | 3 | 20 | ||
| Predicted positive | 3 | 0 | 0.76 | |
| Predicted negative | 7 | 20 | ||
| Actual Condition | ||||
|---|---|---|---|---|
| Positive | Negative | Accuracy | ||
| Predicted positive | 13 | 2 | 0.93 | |
| Predicted negative | 0 | 15 | ||
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Leite Junior, W.C.; de Moraes, C.C.; de Albuquerque, C.E.P.; Machado, R.C.S.; de Sá, A.O. A Triggering Mechanism for Cyber-Attacks in Naval Sensors and Systems. Sensors 2021, 21, 3195. https://doi.org/10.3390/s21093195
Leite Junior WC, de Moraes CC, de Albuquerque CEP, Machado RCS, de Sá AO. A Triggering Mechanism for Cyber-Attacks in Naval Sensors and Systems. Sensors. 2021; 21(9):3195. https://doi.org/10.3390/s21093195
Chicago/Turabian StyleLeite Junior, Walmor Cristino, Claudio Coreixas de Moraes, Carlos E. P. de Albuquerque, Raphael Carlos Santos Machado, and Alan Oliveira de Sá. 2021. "A Triggering Mechanism for Cyber-Attacks in Naval Sensors and Systems" Sensors 21, no. 9: 3195. https://doi.org/10.3390/s21093195
APA StyleLeite Junior, W. C., de Moraes, C. C., de Albuquerque, C. E. P., Machado, R. C. S., & de Sá, A. O. (2021). A Triggering Mechanism for Cyber-Attacks in Naval Sensors and Systems. Sensors, 21(9), 3195. https://doi.org/10.3390/s21093195







