1. Introduction
The Internet of Things (IoT) paradigm has emerged from the proliferation of objects and mobile devices (i.e., “things”) connected, which results in the acquisition of periodic event flows from different devices and sensors that need to be processed [
1]. IoT proposes to expand the current structure of the Internet into a network of interconnected objects that not only collect information from the environment but also interact with the physical world to provide services such as information transfer and analysis, applications, and communications [
2,
3]. Some examples of IoT applications are in Smart Cities, Smart Factories, Smart Buildings, Smart Homes, and Smart Cars [
4]. Understanding these IoT environments and their interactions are becoming an increasingly difficult task [
3]. Thinking in such interactions as event notifications to be processed should improve the analysis and interpretation of information.
Events can be conceived as unique occurrences of interest in time. However, recognizing patterns that comprise a particular composition of these occurrences to obtain meaningful information for systems also makes the processing of these events complex [
5]. In recent years, event-driven communication and processing models have been widely disseminated, studied by the academic community, and accepted by the industry [
6,
7]. Several application domains have benefited from the event processing area involving both event-based processing and communication.
In event processing, the key idea is to explore temporality and causality relationships between events to recognize patterns promptly. This type of processing can reveal opportunities or threats while they arise, so executing decisions in a constrained time. Therefore, systems capable of efficiently processing data to recognize complex situations of interest immediately when they occur define Complex Event Processing (CEP) [
5]. CEP can also be interpreted as a programming paradigm that supports reactions to event data flows in real time through a set of methods and techniques to perform such processing [
8,
9]. Identifying near real-time occurrences of interest in the face of a wide variety of event flows from various sources is one of the essential requirements in many event processing applications [
10].
Event processing has become common in many IoT applications. When considering event processing, such applications assume that event flows are stable, and events are captured while they happen. Furthermore, such applications assume that all communication channels and sensors are reliable, and event processing does not occur on uncertain data [
11,
12]. However, in real-world IoT applications, event producers usually generate event flows that are unreliable. In this case, such applications have to operate in real physical environments, which are intrinsically complex and unpredictable, with data acquired from devices and sensors that can have different levels of precision defined by different manufacturers. In addition, in these applications, the information included in event flows may contain imprecision at the origin of the event [
13]. For example, sensors and devices that emit events may be defective or affected by failures, have poor calibration, and therefore produce inaccurate data, which is then considered uncertainty at the event source [
14].
The common and widely used techniques for analyzing event flows from sensors, devices, and systems present in IoT is CEP [
15]. By providing a structure based on a set of rules, CEP enables to extract information about patterns of relationships between simple events (i.e., primitive event) and derived complex events [
16] (also called “situation” [
17]). Uncertainty in CEP is normally observed in events (e.g., data or sensor readings) or in rules that may propagate unreliable results or conflicting conclusions. Sources that produce events transmitted to the CEP may incorporate inaccuracies [
13,
18] into the event content [
12,
19,
20,
21,
22] or even provide unreliable judgment about a derived event occurrence [
23,
24].
Imprecise data propagated to the event flow processing can result in erroneous information or incorrect system behavior. The event flow in sensor networks may be noisy and may not be assumed to be valid and stable. Several studies have been performed on the processing of noisy event flows [
25,
26,
27] and complex events processing under uncertainty [
6,
12]. According to Akila et al. [
15], uncertainty under primitive events significantly degrades the precision of results in terms of false positives and false negatives. Consequently, CEP does not meet expectations of achieving objectives and decision-making capabilities in mission-critical applications under uncertainty conditions.
The problem of data uncertainty in IoT applications (i.e., by considering limited precision of sensors) causes the second problem of propagating uncertainty from primitive events to the inference of derived events (i.e., complex events). By recognizing these problems, the scope of this paper comprises the treatment of uncertainty on event data from primitive events that directly affect CEP rules by resulting in uncertainty propagation to derived events in IoT applications.
This study proposes an approach to model and treat uncertainties in event flow processing from sensors and devices in IoT applications. We investigate a mathematical theory capable of modeling uncertainties observed in CEP, representing and calculating the propagation of uncertainty inherent in complex events. From this investigation, we take advantage of the Dempster–Shafer Theory (DST) [
28,
29], which is flexible and useful for modeling and treating uncertainties. DST enables the propagation of uncertainty values from sensor and device information and indicates certainty about CEP results. We developed our approach, named
DST-CEP, originally founded in DST elements, specifically designed to model and treat uncertainty in CEP-based IoT applications.
This paper is organized as follows.
Section 2 presents preliminaries to understand the proposed solution.
Section 3 discusses related works, while
Section 4 introduces the
DST-CEP approach for IoT applications.
Section 5 presents a case study conducted with the
DST-CEP approach.
Section 6 presents the experimental evaluation performed with the proposed solution, and discusses results and limitations. In the end, conclusions concerning our study and some directions for future work are drawn in
Section 7.
5. Case Study
This section presents a case study conducted with the DST-CEP approach in an IoT application. The case study is explained to didactically present the use of the proposed approach. Moreover, the same case study is also used in the experimental evaluation. Specifically, we present an application that detects fire outbreak in real time based on sensors.
5.1. Application Scenario
Consider a multi-sensor fire outbreak detection system that can be used in IoT applications such as Smart Buildings, Smart Homes, or Smart Factories. This system consists of sensors and event processing agents. Sensors are automatic components of the fire detection system, which include flame, smoke, and temperature sensors. They are able to quickly detect physical and chemical information generated by a fire, and transmit them to the processing agents to detect fire. These event processing agents are called detectors, since they use sensor-based information to detect fire (or non-fire).
When that system uses a single sensor to collect information, it might become unreliable due to interference caused by dust, electromagnetism, water vapor, air, light, vibration, and other environmental conditions. Eventually, the system cannot effectively distinguish between early fire signals and ambient interference signals. Therefore, it cannot promptly send fire warnings. In this application scenario, the fire detection system use three sensors to improve the reliability of fire and non-fire detections. Therefore, dealing with uncertainty and processing information collected from multiple unreliable (and possibly conflicting) sensors becomes a major issue.
5.2. Processing Levels
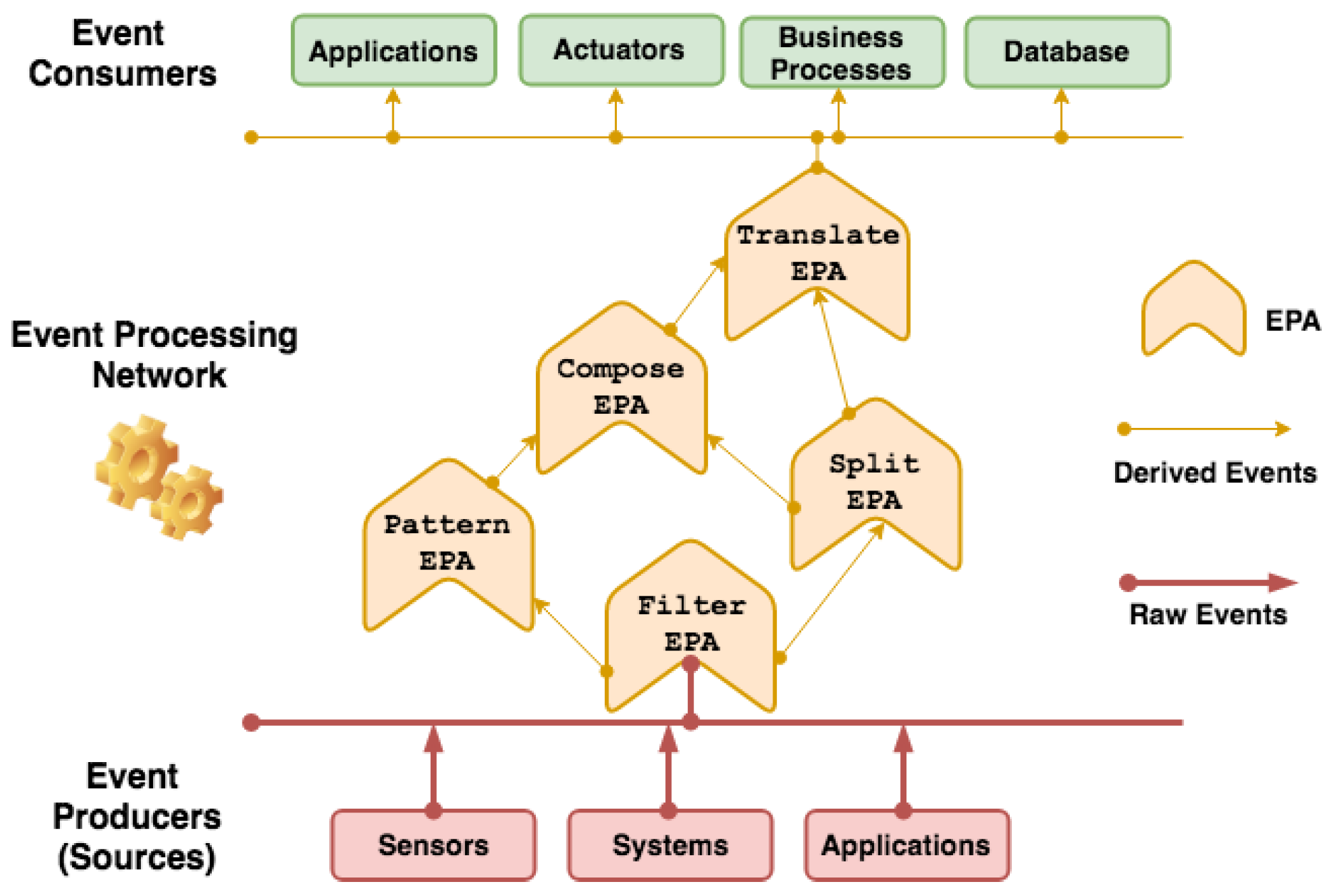
The fire detection system structure follows the
DST-CEP architecture model (
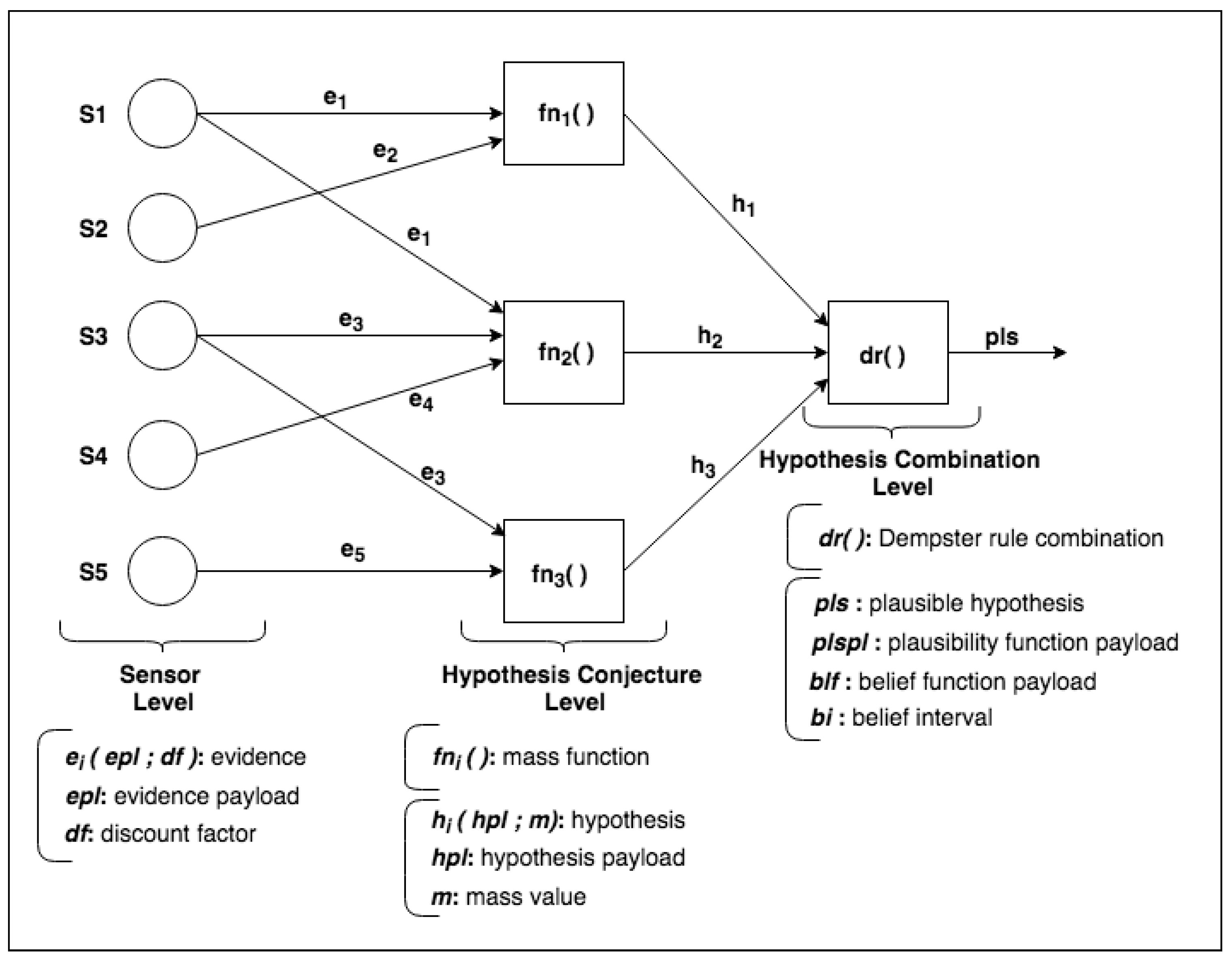
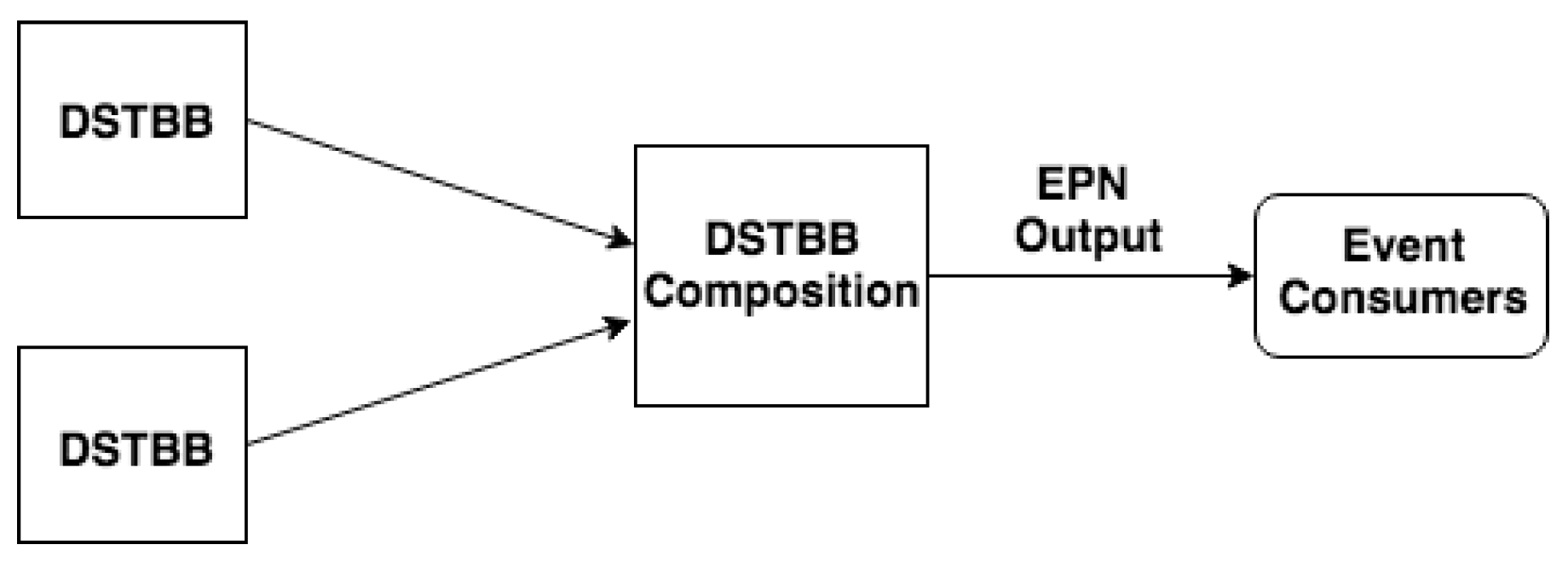
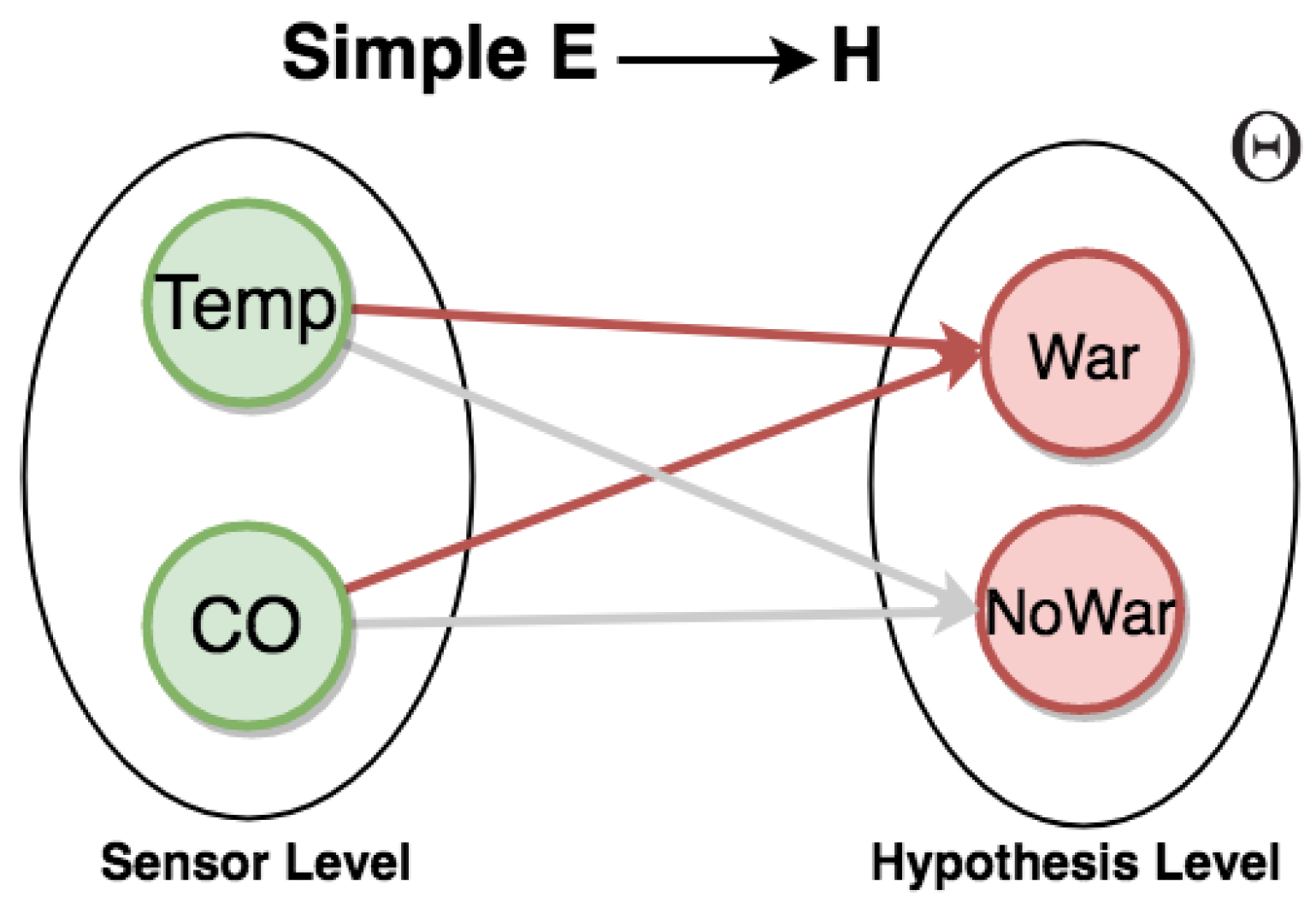
Figure 2) and has three processing levels: sensor, hypothesis conjecture, and hypothesis combination.
Figure 9 shows how IoT application events are processed and calculated in
DST-CEP computing processing levels. Initially, primitive hypotheses defined in the frame of discernment for this fire alarm application is
, where
denotes that a fire is happening,
denotes that no fire is happening. All subsets formed by the disjunction of the primitive hypotheses give rise to all possible hypotheses
, where
denotes uncertainty about whether there is a fire or non-fire. The mass value of the empty set is zero by definition (Equation (
1)).
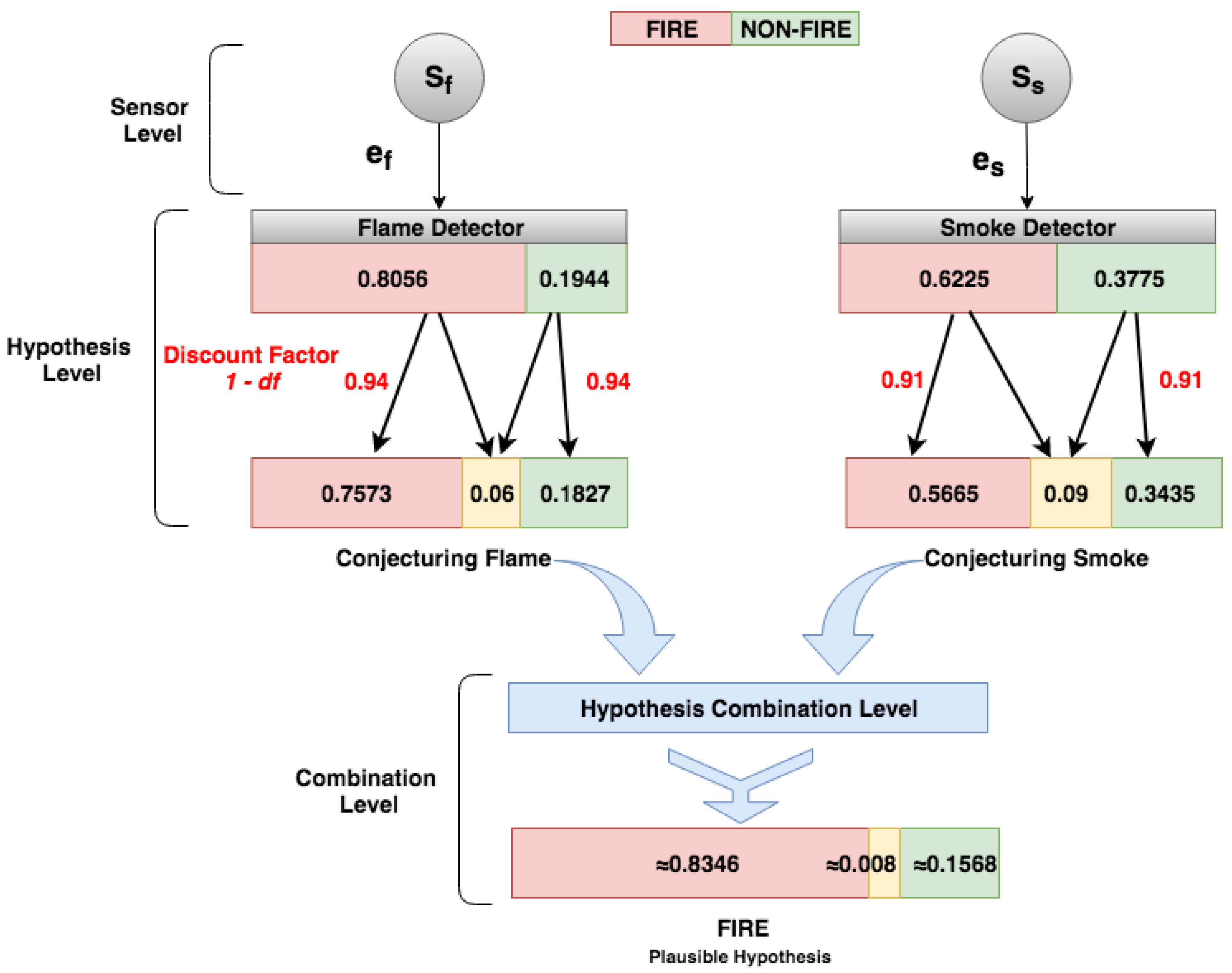
5.2.1. Sensor Level
In the Sensor Level (
Figure 9), two detectors (flame and smoke) send readings (i.e., pieces of evidence) to the
DST-CEP. Given the formal definition of the event (
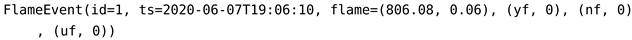
Section 4.1), we show an instance of the flame event, as follows:
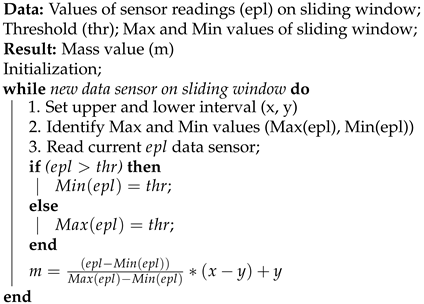
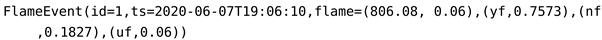
FlameEvent is composed of a sensor identification, ts is the timestamp, flame value is 806.08 nm, discount factor is 0.03, and yf = 0, nf = 0, and uf = 0 are hypotheses “yes fire”, “non-fire” and “uncertain fire” with mass values not calculated at that moment. Consider an example to calculate these values, the flame sensor can detect flames and infrared light sources with wavelengths from 750 nm whose value is the detector threshold. Importantly, we assumed thresholds from sensor manufacturer information related to detection ranges, tests, and sensor sensitivity. Algorithm 1 receives flame data (e.g., 806.08 nm) and checks if the value exceeds the threshold (e.g., 750.0). If yes, then the hypothesis “yes fire” is confirmed (yf), the values of x and y are 0.5 and 1, respectively, and the mass value for this hypothesis should be calculated. The equation of the Algorithm 1 uses the values , and (the highest value of the last 10 sensor readings from the sliding window). From these values, the results of the mass values are: yf = 0.8056, and nf = 0.1944.
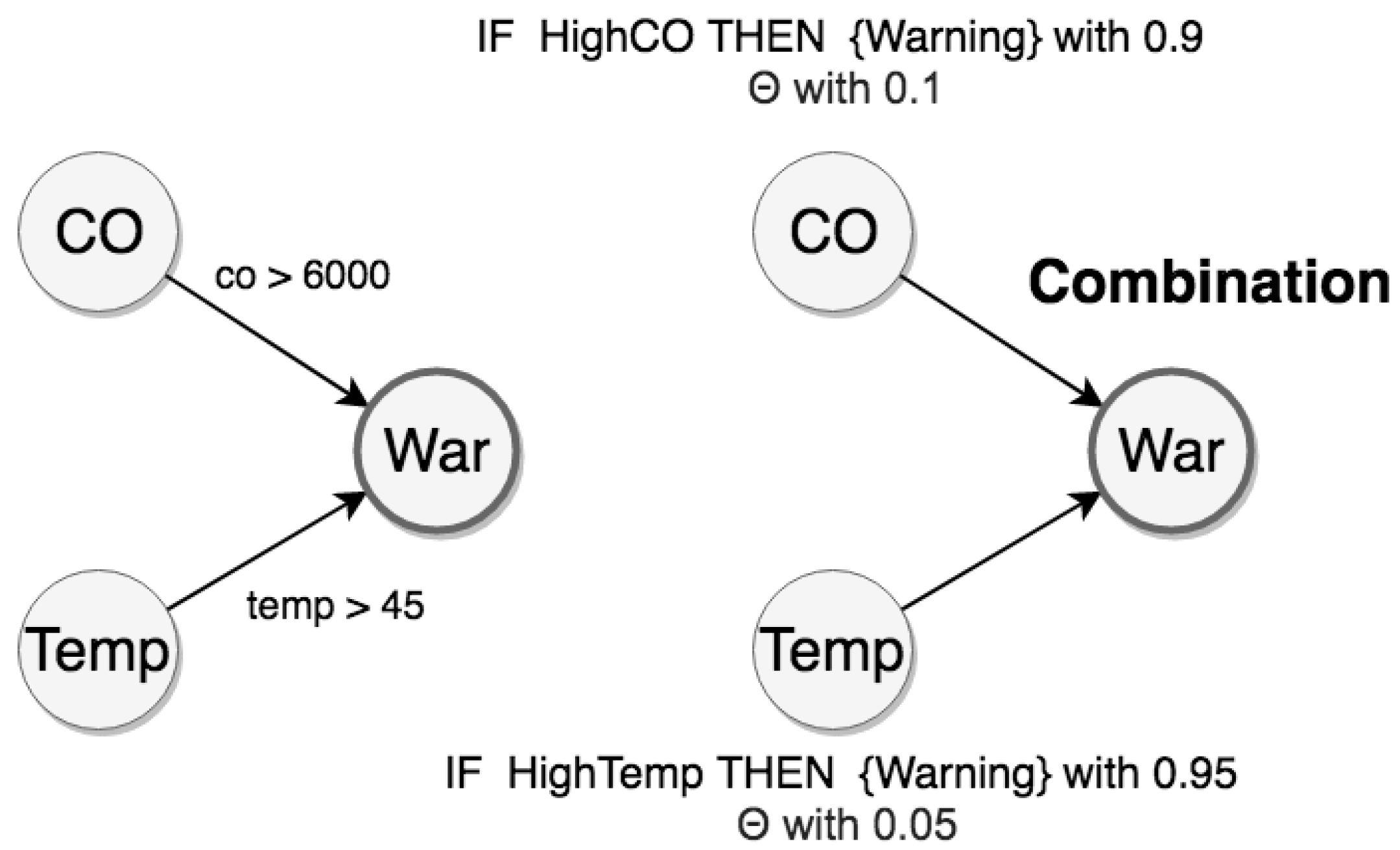
5.2.2. Hypothesis Level
In the Hypothesis Level,
DST-CEP rules perform hypothesis conjectures with the associated mass values. The mass values (
,
, and
) should be calculated. For this purpose, the mass function (see
Section 4.3.1) is applied based on Algorithm 1. The uncertainty (
) of the production source of events needs to be considered in the hypothesis conjecture. Therefore, mass values attributed by the flame detector are hypotheses
and
. By using the mass function with the discount factor 0.06, Equation (
6) generates results for
FlameEvent with mass values for hypotheses
,
, and
(see
Figure 9).
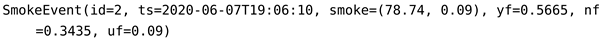
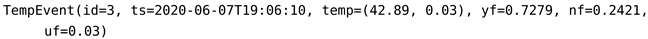
Likewise, all detectors in
DST-CEP generate hypothesis conjecture, therefore the mass functions from smoke and temperature detectors with
and
generate the following event instances:
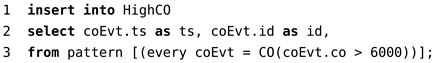
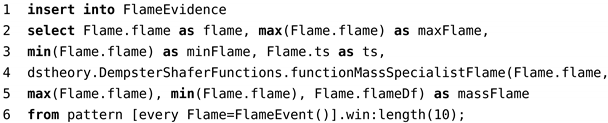
Code 4 shows the CEP rule of the flame detector. Data extracted from the method FlameEvent() (line 6) are processed in the mass function calculation (line 4) and inserted in FlameEvidence (line 1).
| Code 4: CEP rule of flame detector. |
![Sensors 21 01863 i009 Sensors 21 01863 i009]() |
The sliding window (see Code 4, line 6) is continuously formed by the latest ten events. While consuming new events, the sliding window captures flame variations and real-time changes of minimum, maximum, and intervals, which result in different mass values for hypotheses.
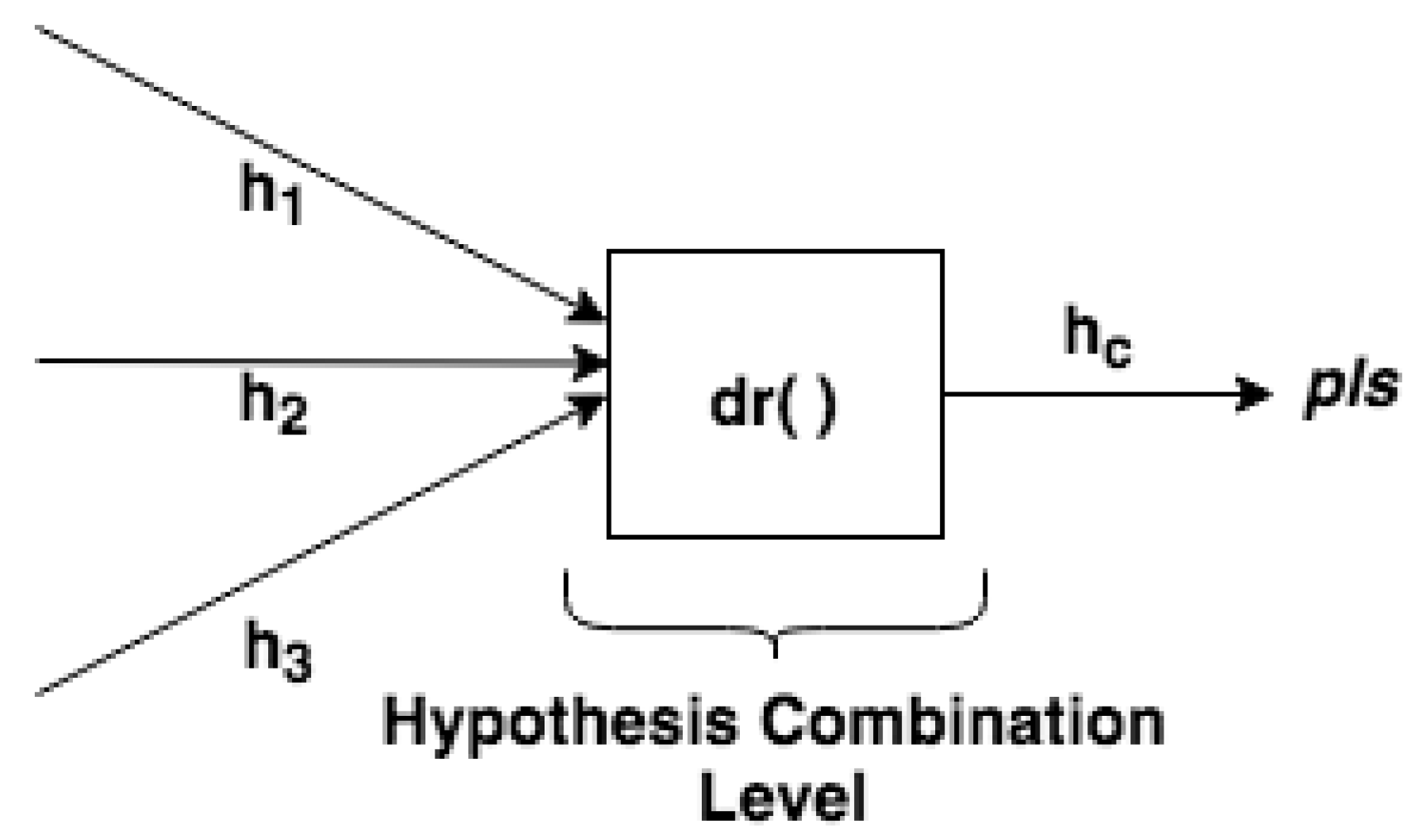
5.2.3. Hypothesis Combination Level
Finally, in the Hypothesis Combination Level, data collected from various information sources are combined to obtain the most accurate fire identification (
Figure 9). In this step, the combination of the hypotheses generated by multiple detectors occurs in the output. There is a result (see
Figure 10) of the combined hypotheses (
), in which the most plausible hypothesis (
pls) can be detected.
From a set of derived hypothesis conjectures, the Dempster combination rule
is used (Equations (
2)–(
4)) to calculate the combination of hypotheses from temperature, smoke, and flame detectors. When three or more detectors contribute information, the Dempster rule application is repeated using the inner elements calculated from the first application of the rule (e.g., the combination of
with
) with the hypothesis (
) from the next detector. This means that the Dempster combination rule can be generalized from Equation (
2) to more than two hypotheses, as presented in Equation (
7), and the order of several combinations does not affect the result.
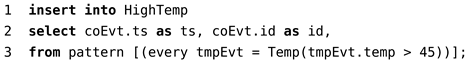
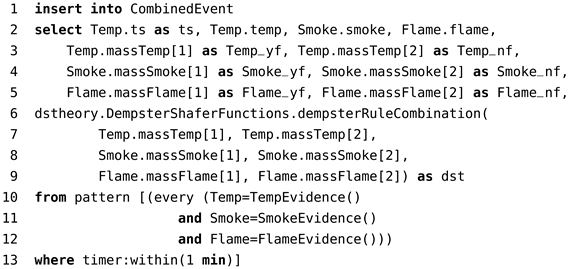
The rule used to process the three events (TempEvent, SmokeEvent, FlameEvent) that occur in one minute is presented in Code 5. In lines 3–5, the mass values of hypotheses are captured from the temperature, smoke, and flame detectors. The Dempster combination rule is called in lines 6–9 using the mass values. Lines 10–13 check if the hypothesis conjectures occurred within 1 min.
| Code 5: CEP rule of Dempster combination rule. |
![Sensors 21 01863 i010 Sensors 21 01863 i010]() |
The Dempster rule is calculated with the following mass values from the three events (TempEvent, SmokeEvent, and FlameEvent). Therefore, the mass values contributed by detectors are:
, and
, and
, and
The hypothesis combination
(see
Figure 10) generated by multiple sensors is given by Equations (
2)–(
4), and the results are
= 0.9342,
= 0.0654, and
= 0.004. From combined hypothesis
, it is possible to detect the most plausible hypothesis, which is
Fire. The final result presented is based on pieces of evidence from all detectors in favor of the fire hypothesis, i.e., the highest mass value from each detector conjecturing fire hypothesis.
However, it is important to observe contradictions between hypotheses in this case study, i.e., the highest mass value from detectors conflicting in favor of fire and non-fire hypotheses.
Table 1 illustrates examples of fire and non-fire conditions and conflicting hypotheses, which are described below.
Conflict 1: it illustrates a real fire condition of slow combustion, i.e., a high amount of smoke at the beginning (smoke detector notifies fire, = 0.7022); but with slow heating and the absence of flames, the other two detectors notify non-fire ( = 0.4910 and = 0.6589). In this situation, the result of the DST-CEP combination ( = 0.5519) concluded the real condition;
Conflict 2: the temperature detector shows that the mass value for fire hypothesis is high ( = 0.8206), while the evidence collected by smoke detector notify non-fire = 0.5519. By using DST-CEP, the final result of the combination concluded the correct condition ( = 0.7967);
Conflict 3: temperature sensors may be close or in contact with heated materials (e.g., electric wires, heated plates); in this case, the temperature detector indicates abnormal, but low, therefore, by mistake, conjecturing the fire hypothesis ( = 0.6649), while the other two detectors indicate the absence of fire = 0.6721 and = 0.5003. DST-CEP correctly concludes non-fire ( = 0.5559);
Conflict 4: it illustrates a real condition of large amount of flame at the beginning (fast combustion). In this case, the flame detector notifies fire ( = 0.5493), while the temperature sensor, in contradiction, indicates non-fire ( = 0.5260). However, pieces of evidence considered together by the DST-CEP conclude fire ( = 0.5720), coinciding with the real condition.
As illustrated, the final results represent synthetic effects of all pieces of evidence of hypothesis conjectures. The DST-CEP solution achieves positive results even when sensors are in abnormal situations and generate conflicting hypotheses.
6. Experimental Evaluation
In this section, we present an investigation on the benefits of uncertainty treatment in IoT applications. In the previous section, we presented a multi-sensor fire outbreak detection system. From that case study, we evaluated the DST-CEP solution with a dataset collected from real sensors. Therefore, the objective of this experiment was to evaluate the performance of the DST-CEP approach compared to individual detectors, rules considering multiple detectors, and probabilistic models.
6.1. Implementation Aspects
Based on the Dempster–Shafer Theory, all formalism presented in our
DST-CEP solution was implemented with TDS functions using CEP and Java technologies. Our fire detection system uses CEP to store continuous queries executed while data flows over the queries. Statements of queries written in EPL allows expressing rich conditions and correlations between events and sliding windows, thus minimizing the development effort required to configure systems that can react to complex situations. The EPL is provided by Esper and implemented in our solution. Esper is an open source engine for CEP, designed for real-time Event-Driven Architecture (EDA) written in Java [
64]. Esper is capable of triggering custom actions written as Plain Old Java Objects (POJO) when event conditions occur between event streams [
64,
68]. Esper enables to import classes and packages, which allows us to declare methods in these classes accessed within CEP rules. The Esper EPL is a rich declarative language for rule specification, continuous queries, including all SQL operators (SQL-like extended), language constructions for interaction and window definitions, and output generation [
68]. Esper EPL statements present expressiveness and concepts that extend capabilities of the SQL.
6.2. Fire Outbreak Dataset and Sensor Models
In this experiment, we used a dataset collected by Umoh at al. [
69]. The authors graciously provided their dataset with 2100 records from three sensors: DHT11 used as temperature sensor, MQ-2 smoke sensor, and LM393 flame sensor. The experiment conducted in [
69] reproduced fire and environment conditions. Therefore, the dataset comprises three features (temperature, smoke, and flame), TS is the timestamp, and a real situation with an output label called “fire outbreak detection” (i.e., the ground truth). The label with value 0 is a negative detection (i.e., “Non-fire”), while 1 is a positive detection (i.e., “Fire”). A sample of this dataset is presented in
Table 2.
6.3. Metrics
We analyzed the following well-known performance metrics [
70]: Accuracy, Precision, Recall, and F-Measure. For this purpose, we represent the results using the matrix confusion as follows:
true positive (TP): when there is a correct conjecture of positive value. The value of fire detection from the dataset is yes fire, and the value of plausible hypothesis from the solution is also yes fire;
true negative (TN): when there is a correct conjecture of negative value. The value of fire detection from the dataset is non-fire, and the value of plausible hypothesis from the solution is also non-fire;
false positive (FP): when there is a wrong conjecture (i.e., contradiction) of negative value. The value of fire detection from the dataset is non-fire, and the value of plausible hypothesis from the solution is yes fire;
false negative (FN): when there is a wrong conjecture of positive value. The value of fire detection from the dataset is yes fire, and the value of plausible hypothesis from the solution is non-fire.
From the above results, we can calculate Accuracy (
), Precision (
), Recall (
), and F-Measure (
) [
70]. We also analyzed Receiver Operation Characteristic (ROC) curves and Area Under Curve (AUC). Within the simplified version of the ROC approach, we can effortlessly display trade-offs between sensitivity and specificity outcomes. The mathematical expressions are presented below.
In terms of fire detectors, the Sensitivity (Equation (
11)) can be defined as the ability that a detector has to recognize fire (true positive rate). In comparison, the Specificity (Equation (
12)) is defined as the ability that a detector has to recognize non-fire (true negative rate), or the ability to exclude false fire notifications (
).
6.4. Baseline
The first objective of our experiment is to evaluate the gain of using the
DST-CEP over standalone CEP for an IoT application. Thus, we measure the performance rates to detect fire and non-fire with
DST-CEP, when uncertainty is managed, and CEP without considering uncertainty. The second objective of this experiment is to evaluate the performance of the
DST-CEP approach compared to individual and multiple detectors considering contradictions between hypotheses, i.e., the highest mass value from detectors conflicting in favor of fire and non-fire hypotheses. The third objective of this experiment is to compare results achieved by our approach with those by state-of-the-art models. Therefore, we compared the performance of our solution with results from different information sources, which are presented in
Table 3.
The performance of each detector is verified from the mass values and compared with the DST-CEP solution. For this purpose, a single detector is deployed in the EPN, and results are evaluated. For example, the temperature detector is considered individually, and the obtained mass values are verified. The mass values generated by the temperature detector are recorded and evaluated in relation to our solution.
Our experiment also explores the processing of CEP rules without uncertainty to compare results with DST-CEP rules considering uncertainty. We created rules without uncertainty considering the three detectors, i.e., temperature (TD), smoke (SD), and flame (FD). We defined the same thresholds used in the case study, and then combine the results of the detectors using two operators of Propositional Logic (PL): the conjunction using the operator (∧) and the disjunction (∨).
Rule of conjunction (RC) written in PL as uses the conjunction of three results from the detectors TD, SD, and FD.
Rule of disjunction (RD) written in PL as uses the disjunction of three results from the detectors.
The response values of the RC and RD attends 16 possibilities of the truth-values from the detectors TD, SD, and FD.
Our experiment also explores probabilistic models based on [
19], which admit events characterized by a degree of uncertainty using probability theory. Composite events (i.e., derived events) combine primitive events. When sensor readings come from different and independent sources, then the overall probability of the composite event is the product of the probability of primitive events. The Normal Probabilistic Model (NPM) assumes that the probability distribution function (
pdf) of the error is known (i.e., measurement errors of sensors have a normal distribution
). We improved NPM, now called IPM, by specifying the standard deviation
,
, and
for smoke, flame, and temperature detectors, respectively. These values correspond to discount factors that express the inaccuracy of the sensors used in our approach. A lower standard deviation corresponds to a more accurate sensor in order to find better results.
6.5. Results and Analysis
Table 4 shows the results of performance metrics of our experiment when analyzing the detectors working individually. The temperature detector presents the best performance in
Acc,
Rec, and
F1 but low
Prec (77.33%). The smoke detector also presents low
Prec (77.98%), and the other metrics with performance below the temperature detector. This fact is why the temperature detector has the largest number of fire notifications (TP) and has the worst number of false fire notifications (FP). The flame detector presents the worst number of non-notified fire occurrences (FN), so the worst performance with the lowest
Rec (57.30%).
Individual detectors have low overall performance, while the DST-CEP solution achieves the best results on all metrics. We consider FNs more important in this fire scenario because it is critical to neglect a real fire occurrence. In this perspective, the DST-CEP has the number of FNs significantly reduced compared to individual detectors. This fact is why our approach gives a Rec of 97.30%, which shows its ability to detect almost all the fire events correctly. The Recall represents the sensitivity of the DST-CEP, in which the true positive rate is not ignored, and the critical false negatives of real fire occurrences are reduced to a few. To evaluate the DST-CEP overall performance in the fire detection system, we analyze Accuracy and F-Measure. Our solution reaches Acc 95% and F1 91.14%, which shows that it detects fire and non-fire events correctly with even less difficulty. Prec of 85.71% means that our solution increases by approximately 8% of the best precision between detectors.
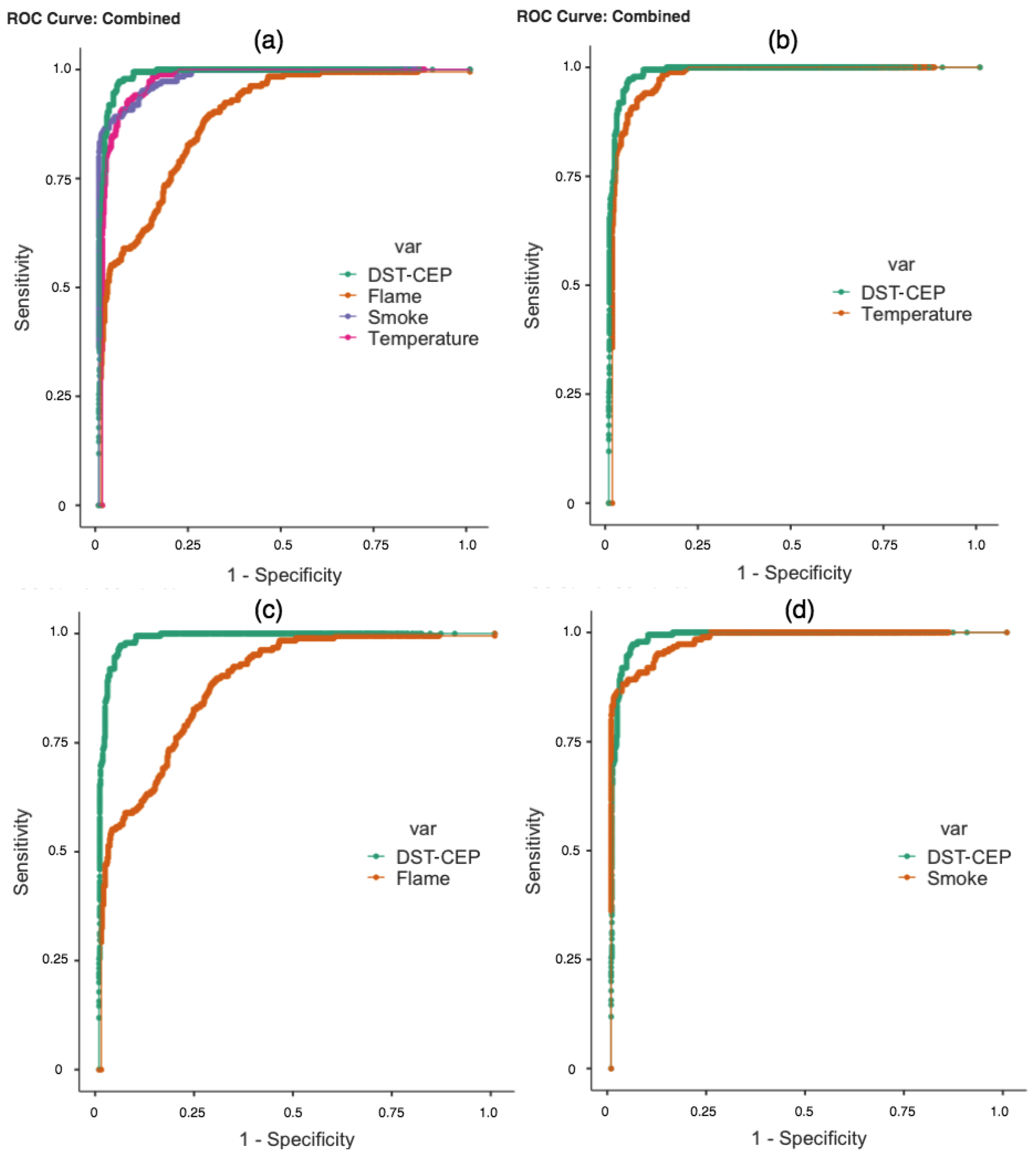
Another point of our analysis concerns the ROC curves and AUC. The results of the fire detectors and
DST-CEP produced answers of mass values for hypotheses. In this case, the relationship in
Figure 11 between sensitivity and specificity of quantitative mass values is represented across “cutoff point” values. Mass values less than or equal to the cutoff point is classified as non-fire, and a response greater than the cutoff point is classified as fire.
In practice, it is desirable to have a result that is both sensitive and specific. In
Figure 11a, we present the ROC curves that refer to fire detectors and
DST-CEP. We can identify that the
DST-CEP curve is the most sensitive and specific. In
Figure 11b,c, the result of the
DST-CEP curve (green line) demonstrates greater discriminating power of sensitivity and specificity, and the flame curve is the worst one. When the
DST-CEP curve crosses the smoke curve (
Figure 11d), more attention is required because there is no dominant relationship between them. AUC is presented as a summary of the ROC curves, and can deal with overlapping curves [
71]. As observed in
Table 5, the AUC of the
DST-CEP shows a better performance overcoming all results of individual detectors. A high AUC means that the fire detection has low false positive rates (high specificity) when the sensitivity is high, which is the desired behavior for our
DST-CEP solution.
It is worth noting that RC, RD, NPM, and IPM do not generate results with continuous values mostly, consequently not enabling a curve projection for ROC analysis.
Table 6 shows the results of our experiment when analyzing performance metrics of rules without uncertainty from RC and RD. The fire notification by RC is precise because it requires fire confirmation in all three detectors. For this reason, RC is capable of recognizing fire occurrences without any false positive, so reaching 100% precision. However, the Recall metric is low (55.68%), and Accuracy and F-Measure values are below our solution. Fire notification by the RD is more sensible to fire notifications because this rule requires fire confirmation from only one detector. For this reason, RD detects fire notifications without any false negative (Recall of 100%). However, RD generates many false positive notifications (i.e., low Precision). Our
DST-CEP solution overcomes RD in Precision, Accuracy, and F-Measure metrics.
Table 7 shows the results of our experiment when analyzing performance metrics of the probabilistic models. Our approach outperforms the results of these models. The better result of the NPM is accuracy with 81.14%. It is worth noting that all results of NPM do not outperform the rules without uncertainty. This phenomenon is repeated in [
19], where rules without considering uncertainty do not have accuracy overcome. We find better results in IPM compared to the NMP. Even with the improvement,
DST-CEP outperforms the IPM in all performance metrics.
6.6. Discussion
6.6.1. What Went Well
We performed an experimental evaluation that allowed us to analyze the performance of the DST-CEP solution considering state-of-art metrics in a real-time fire detection application. Results confirmed the gains of our approach. When analyzing the detectors, the DST-CEP presented the best performance in Accuracy, Precision, Recall, and F-Measure. We achieved the best ROC curve even when combining information from detectors with low performance causing conflicting fire notifications, and the DST-CEP curve had better sensitivity and specificity in this situation. The case study demonstrated that the most plausible hypothesis from the combination of data provided by unreliable sensors was obtained. The AUC values confirmed the promising result of the DST-CEP.
Additionally, the DST-CEP demonstrated significant improvements in performance results over standalone CEP without considering uncertainty (i.e., the rules RC and RD), which attends the exhaustive 16 possibilities of combining the results from detectors. RC had the best Precision, but it had Recall, Accuracy, and F-Measure results below our solution. RD was more sensible to fire notifications and had the best Recall. However, RD generated many false positive notifications, thus our solution gained in Precision, Accuracy, and F-Measure results.
Eventually, an acceptance threshold for events can be used in our approach. This situation is useful in IoT applications where resulting events are sufficiently critical to accept only notifications with high reliability. For example, when accepting non-fire notifications only with values above 0.9, thus decreasing false non-fire notifications, then avoiding false negatives, which is critical in this scenario. This is a feature that DST-CEP can provide, and standalone CEP without considering uncertainty cannot.
DST-CEP demonstrated to be suitable and flexible to deal with the uncertainty issues described in this study. Several related works are based on the probability theory [
6,
7,
13,
19,
37,
42]. In those approaches, the role of sample space (
), which is the set of all possible outcomes, resembles the frame of discernment (
) in
DST-CEP. However, the difference is the number of possible hypotheses, which is
in our approach. This fact implies, for example, that a sample space would typically hold either yes fire (
) or non-fire (
). However, the uncertain fire (
) is not modeled in a sample space, i.e., uncertain observations cannot be modeled. In our study, we aimed at supporting multiple interpretations of one data from a frame of discernment, attending uncertainty about all possibles hypotheses and any combination of them. Therefore,
DST-CEP offers an alternative to probabilistic approaches for representing and reasoning over uncertain information.
We performed experiments with probabilistic models based on [
19]. In such models, parameters are manually estimated or calculated by domain specialists. These users are expected to extend BNs (i.e., BN enrichment) to capture a-priori knowledge about aspects of the environment that cannot be observed by information sources. During the enrichment, the BN can be edited by changing the a-priori distribution of probability values. In
DST-CEP, we dealt with uncertainty in events by explicitly assigning them with uncertain information from real sensors in a formal representation. This permits associating a level of uncertainty related to the event source (e.g., sensor readings) in a natural way without requiring any user computation. We also dealt with propagation of uncertainty to rules using the Dempster combination rule, which presents positive synthetic effects of all pieces of evidence of hypothesis conjectures even when sensors are in abnormal situations. Unlike probabilistic approaches, which use simulated datasets, we used a dataset composed of data from real sensors, and
DST-CEP obtained significant performance results in relation to the studied probabilistic models.
6.6.2. Identified Limitations
From the development of our proposed solution and experimental evaluation, we were able to identify some limitations. A difficulty with the DST-CEP approach is to model mass functions. It is worth noting that the Dempster–Shafer Theory does not focus on the judgment, calculation, or mechanism by which the mass value is determined. This theory focuses on combining distinct mass values based on pieces of evidence from multiple sources. Therefore, modeling mass functions may be complex depending on the problem domain or application scenario.
Another difficulty is the absence of consensus on selecting the optimal threshold for a detector rule to generate a notification. There is scant guidance on the selection of thresholds at which detectors are required to alarm. Specifically in the case study presented, in fire detection systems, the nature of fire is a science apart. For example, many variables such as fuel type, detector design, burn mode, and smoke aging, can affect the fire detector response [
72]. We have assumed thresholds from the sensor manufacturer information.