Reliable Link Level Routing Algorithm in Pipeline Monitoring Using Implicit Acknowledgements
Abstract
1. Introduction
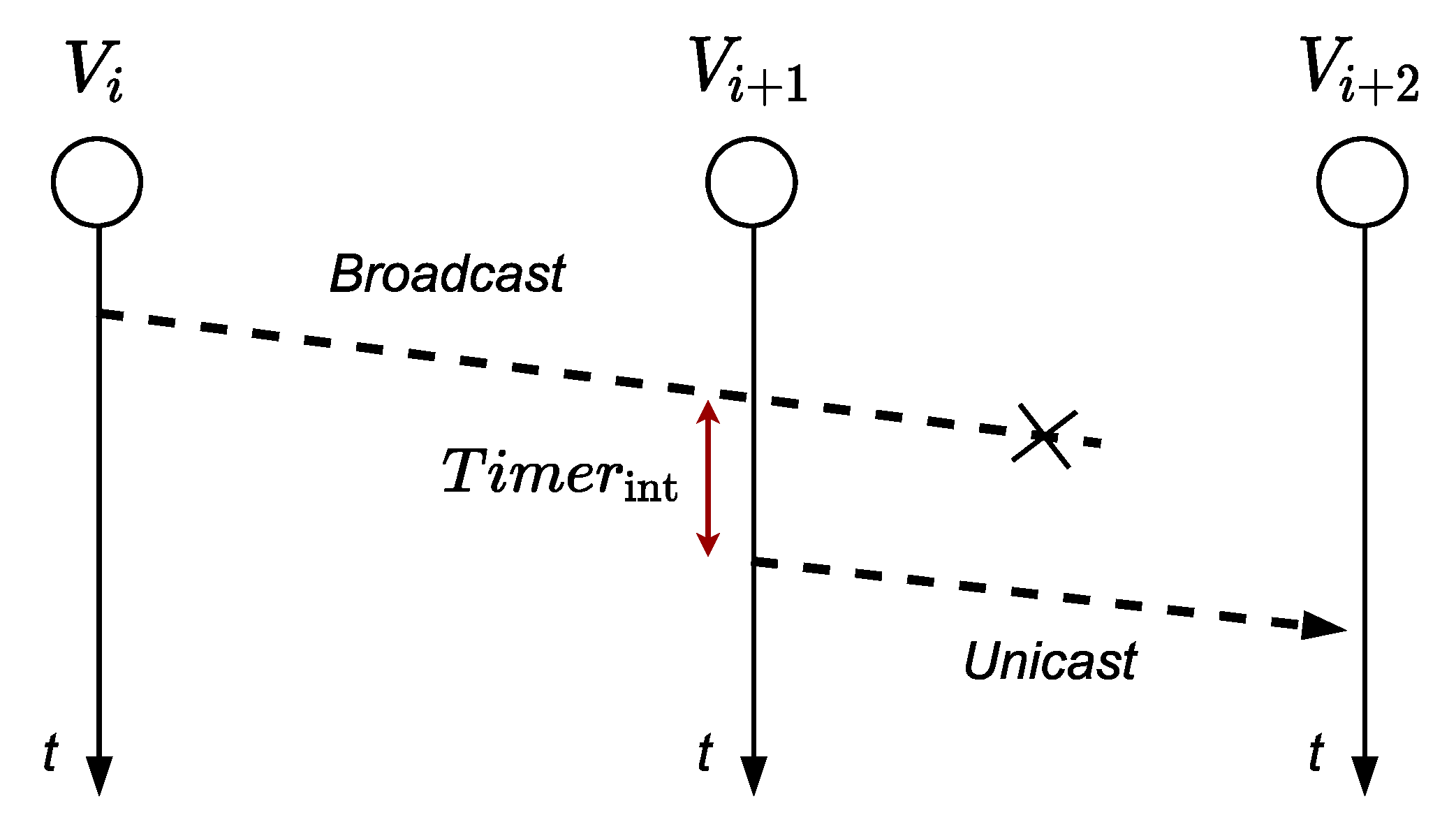
- Reliability of the transmission, using iACK.
- Reduction of the delay time caused by using acknowledgement frames.
- Alternative nodes are selected to transmit when failed nodes or links occurs, without using routing.
- Reduction of computation in the node thanks to the elimination of routing tasks.
- Automatic assignation of addresses to nodes using link level processes.
- Reduction of the energy consumption during the end-to-end reliability transmission process.
- Improvement of the scalability with a large number of sensor nodes in LWSN, allowing for the insertion of new nodes automatically.
- Maximization of the entire system’s lifetime due to the energy efficiency in each node.
2. Related Work
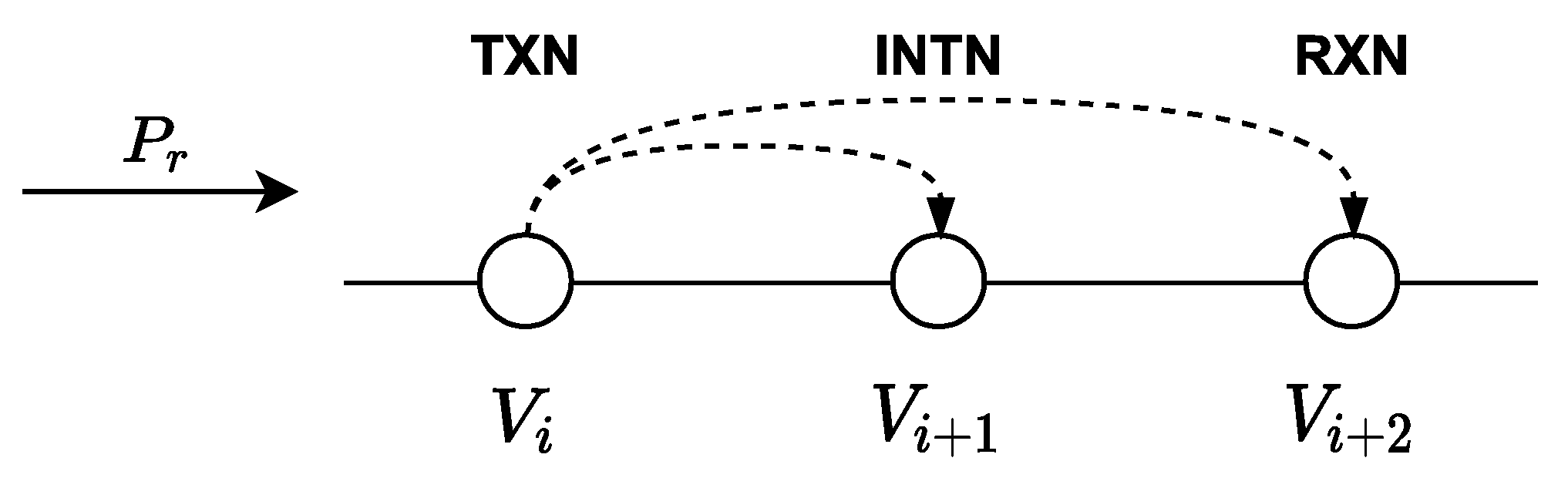
3. Proposed Algorithm
- We consider a linear structure, without branches, with n nodes and two border nodes or base stations, v0 and vn+1, which are responsible for sending information to the central monitoring using long-range communication protocols.
- Each node works with the IEEE 802.15.4 standard in beaconless mode (CSMA/CA).
- Each node has a coverage area of 50 m (a reasonable distance for an IEEE 802.15.4 network in the 2.4 GHz band [43]), without obstacles and transmission conditions in the line of sight, and is associated with four nodes, two on the left and two on the right.
- The nodes are deployed with a separation of 25 m. Therefore, a node has at least 4 nodes in range.
- The participating nodes use a predefined PAN identifier to prevent the connection to other nodes that are not part of the linear infrastructure.
- Each node has an identifier assigned sequentially and automatically using processes at the link level, as indicated in [44].
- The bits of the header identified for future use are used to implement the control messages required by the proposed algorithm.
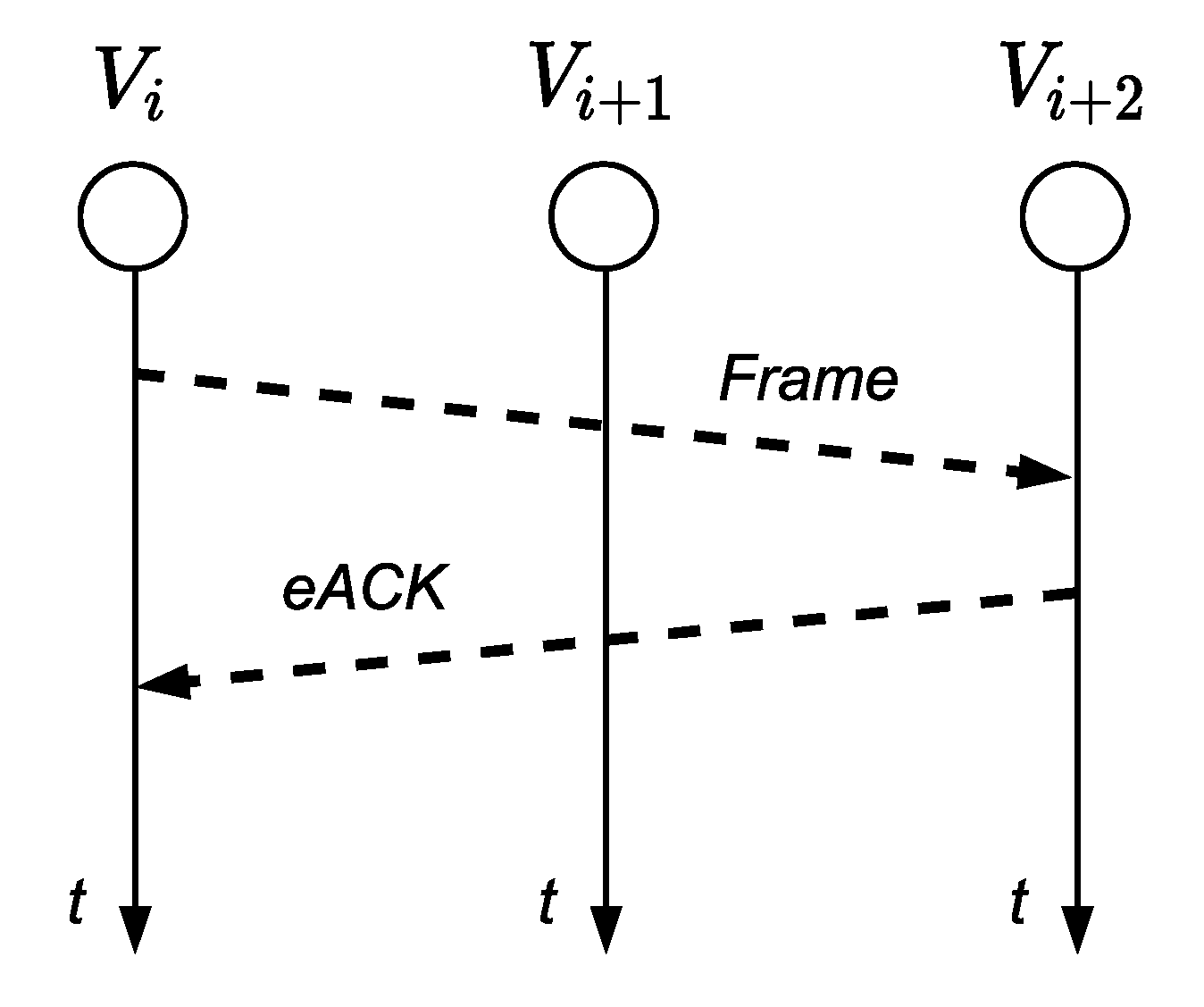
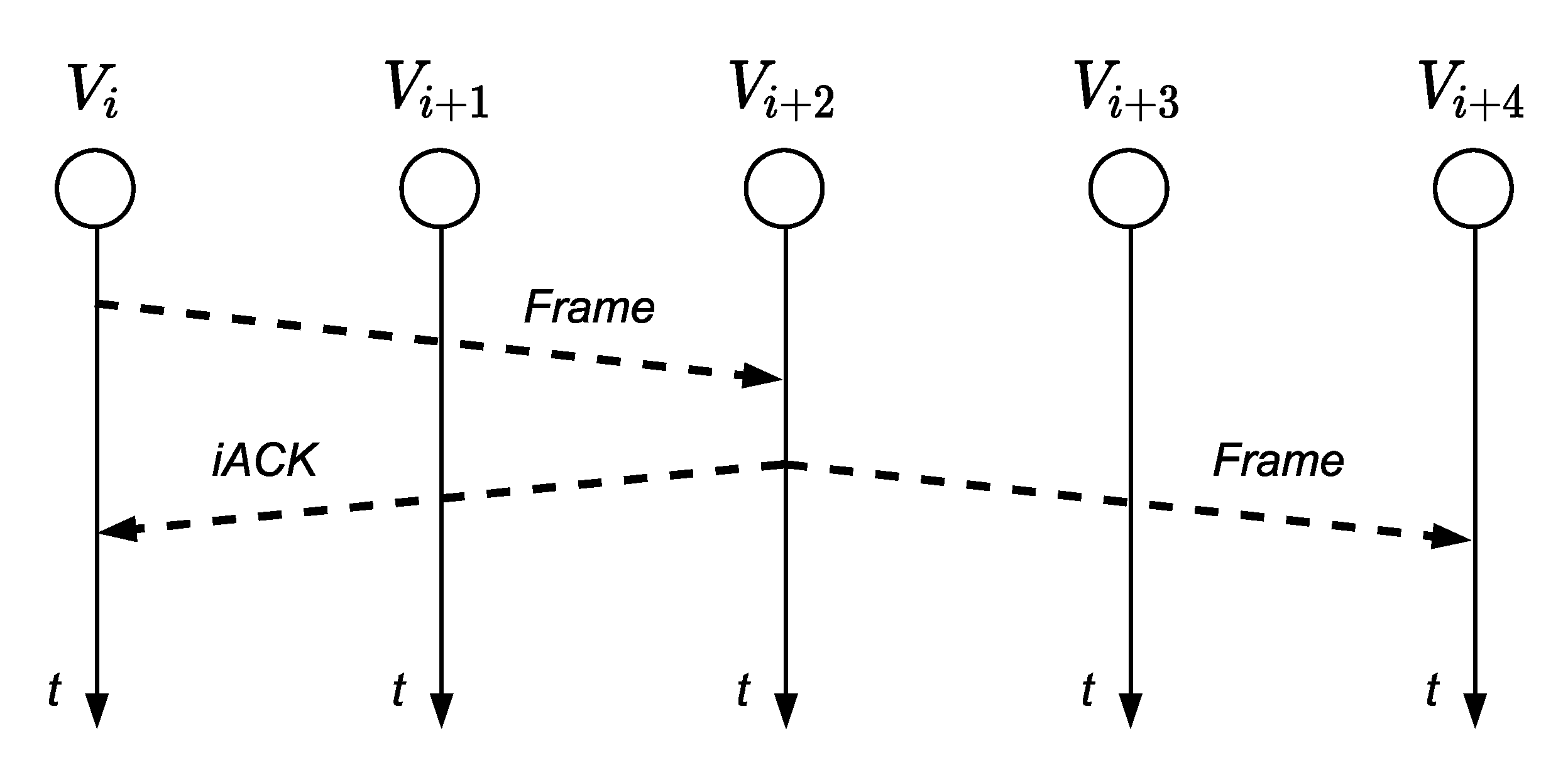
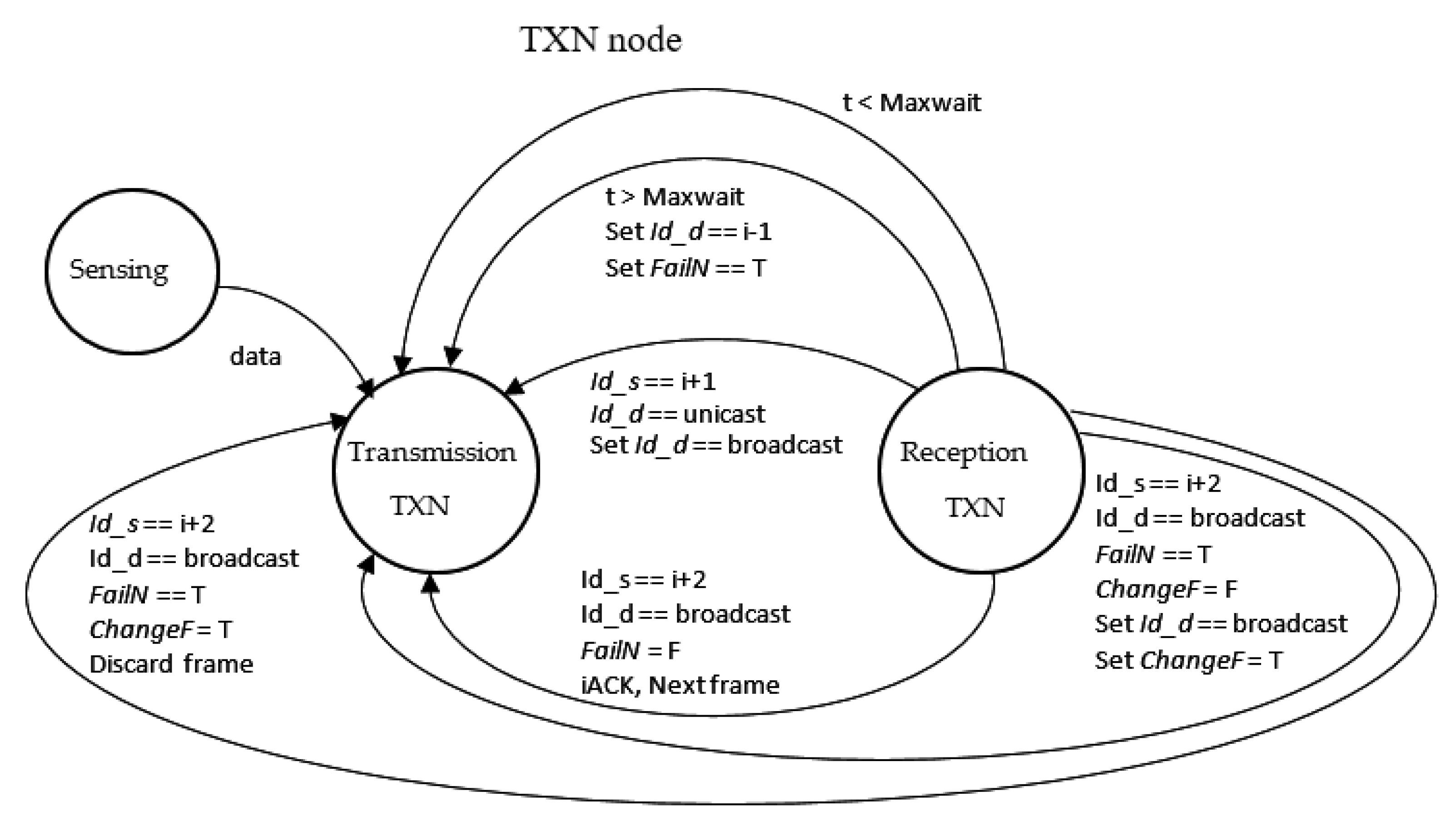
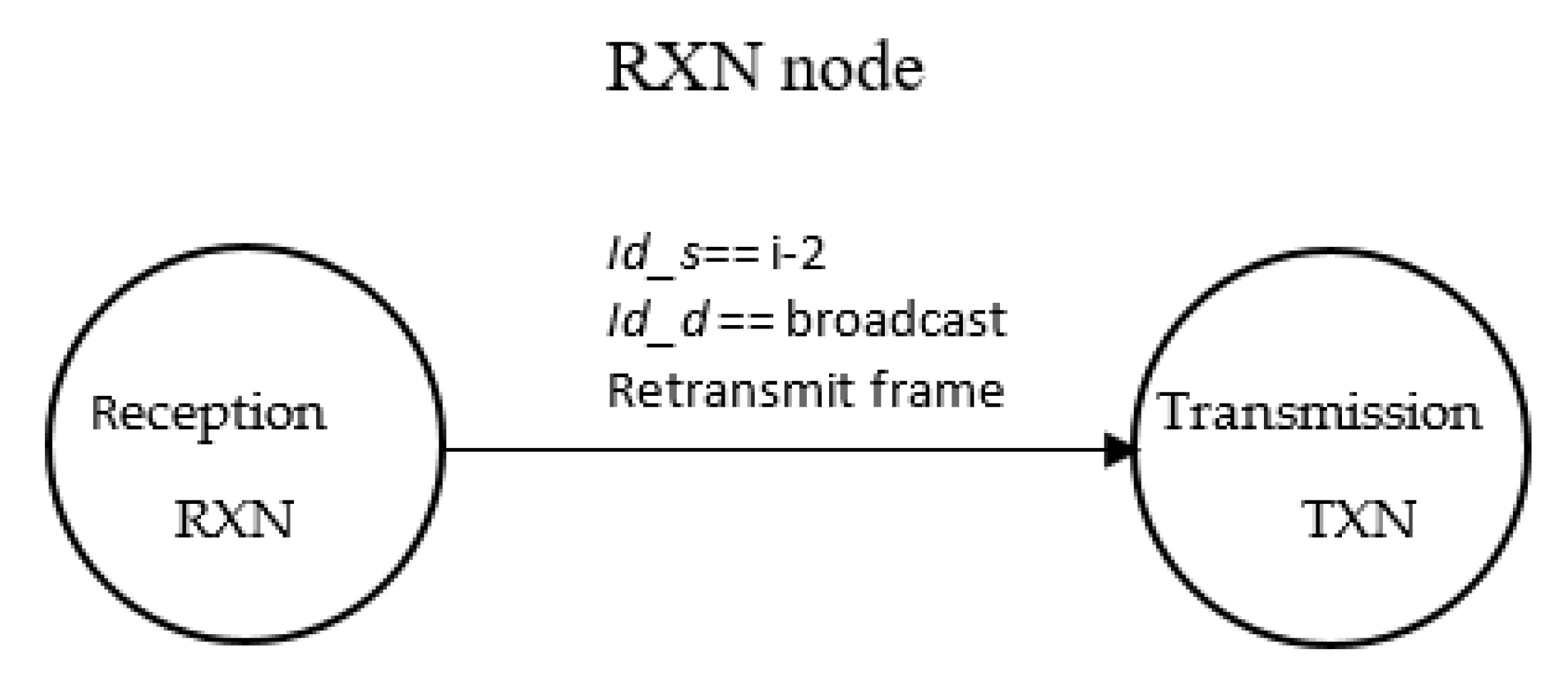
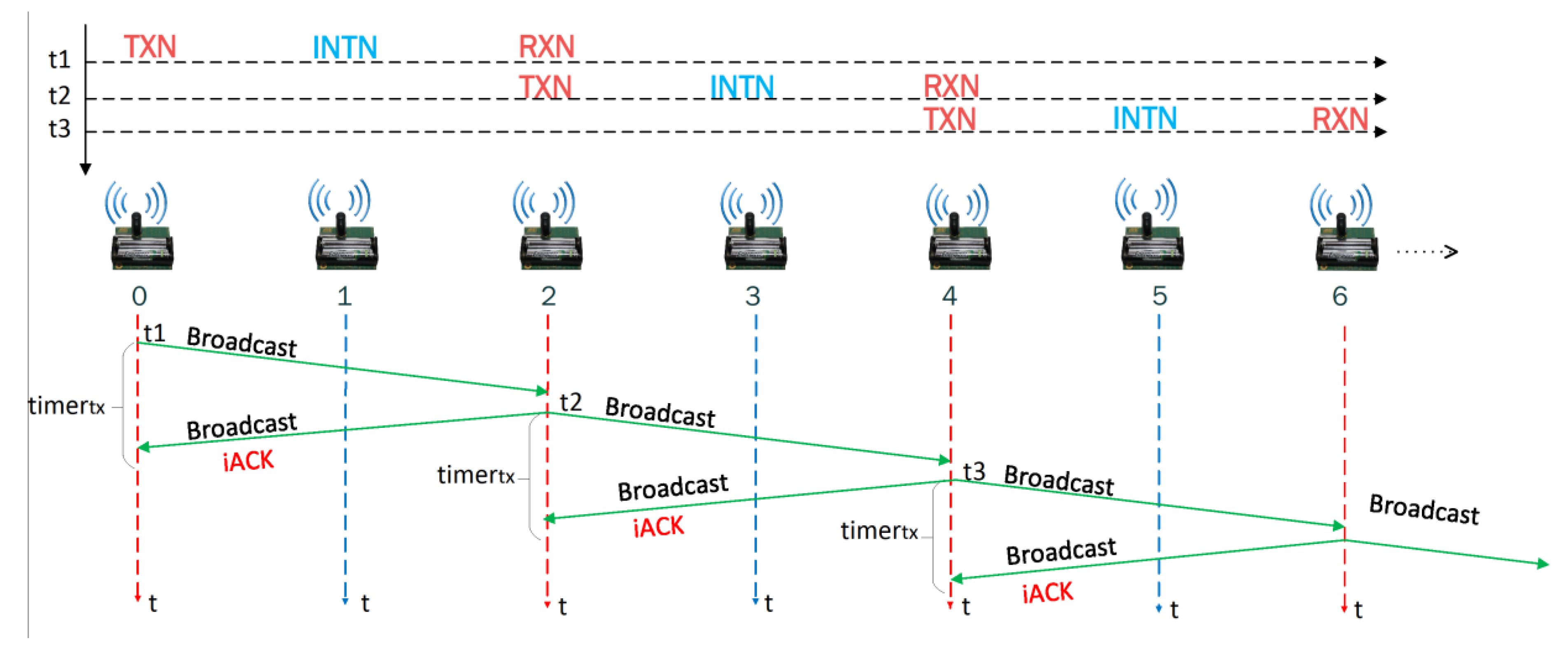
3.1. Algorithm Implementation
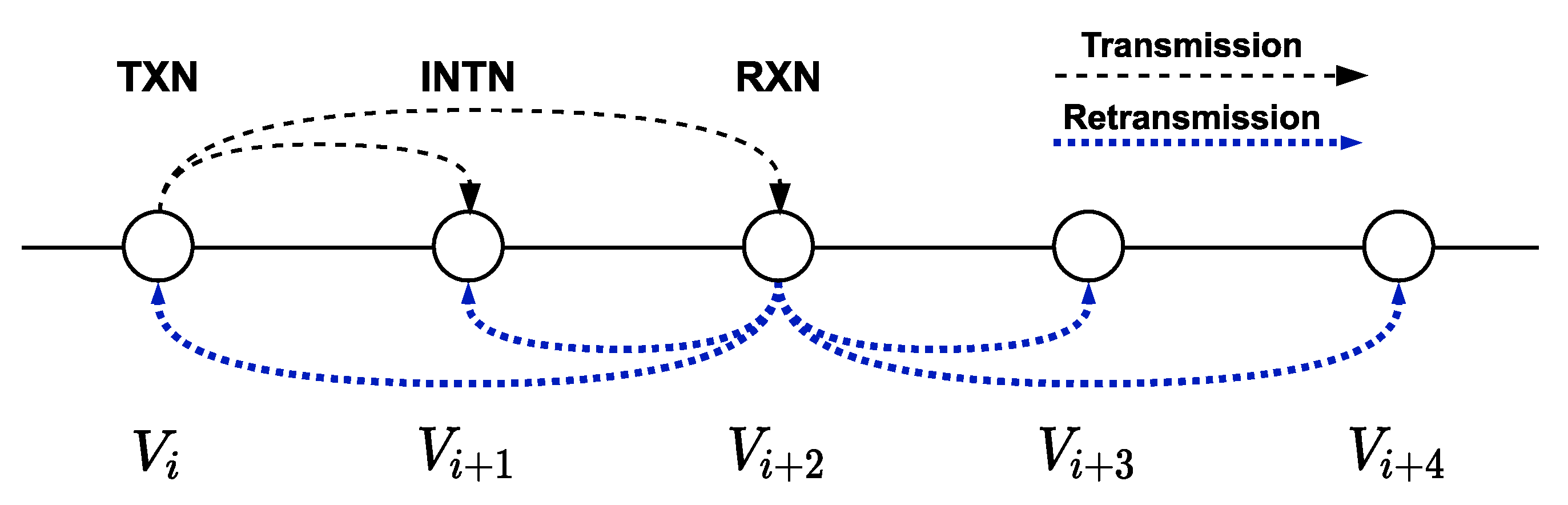
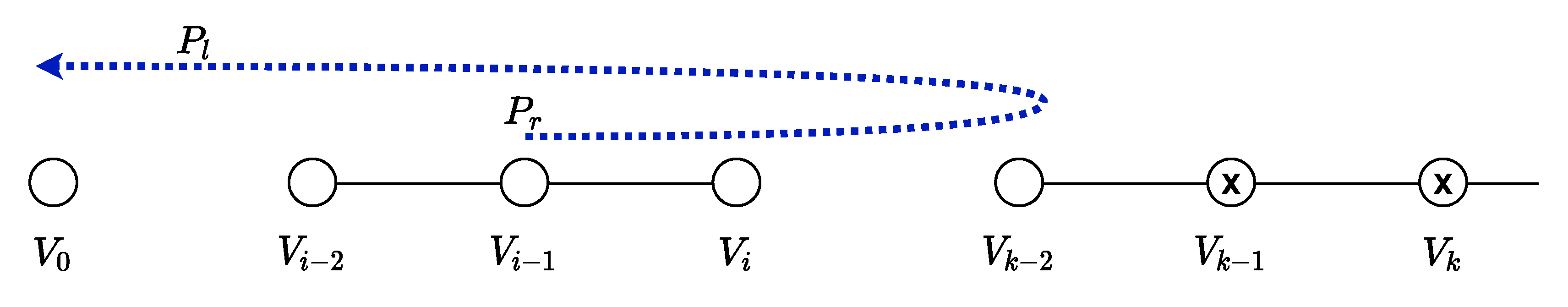
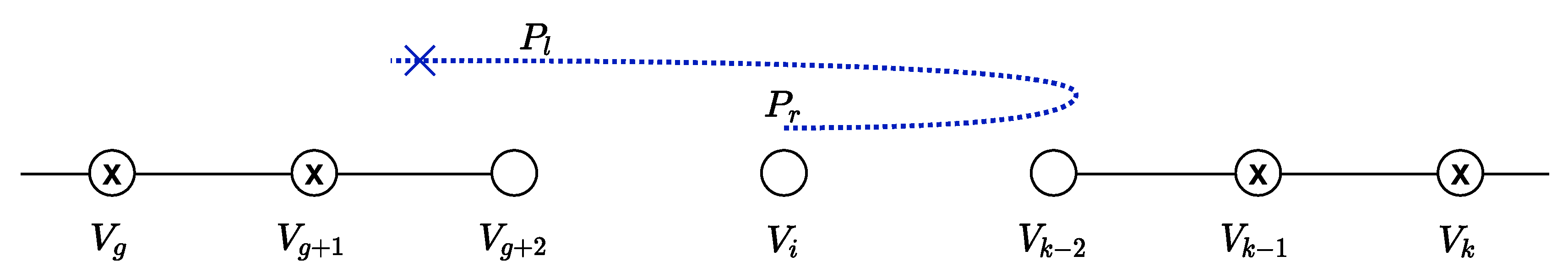
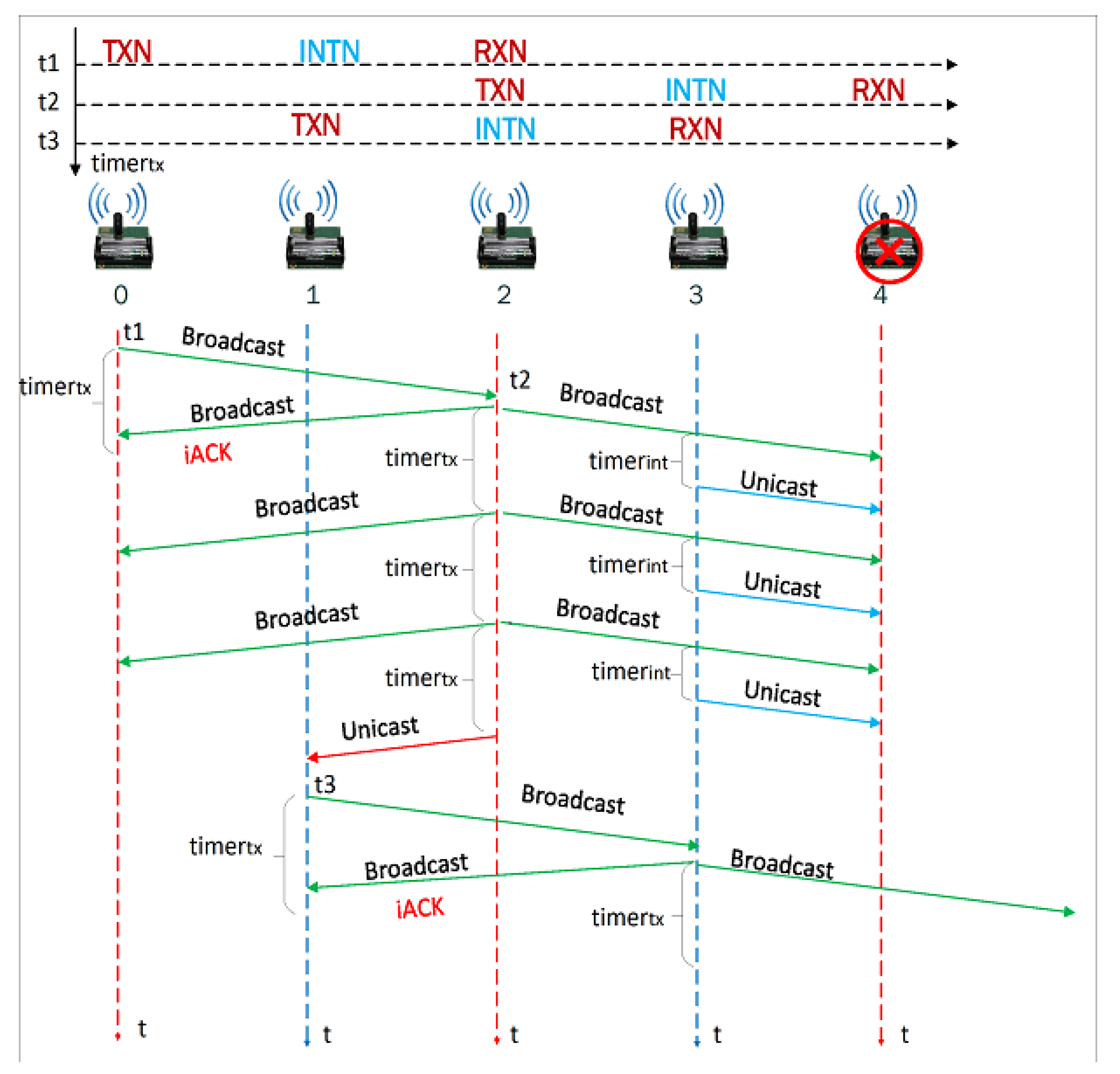
3.2. Algorithm Robustness
3.3. Traffic Minimization
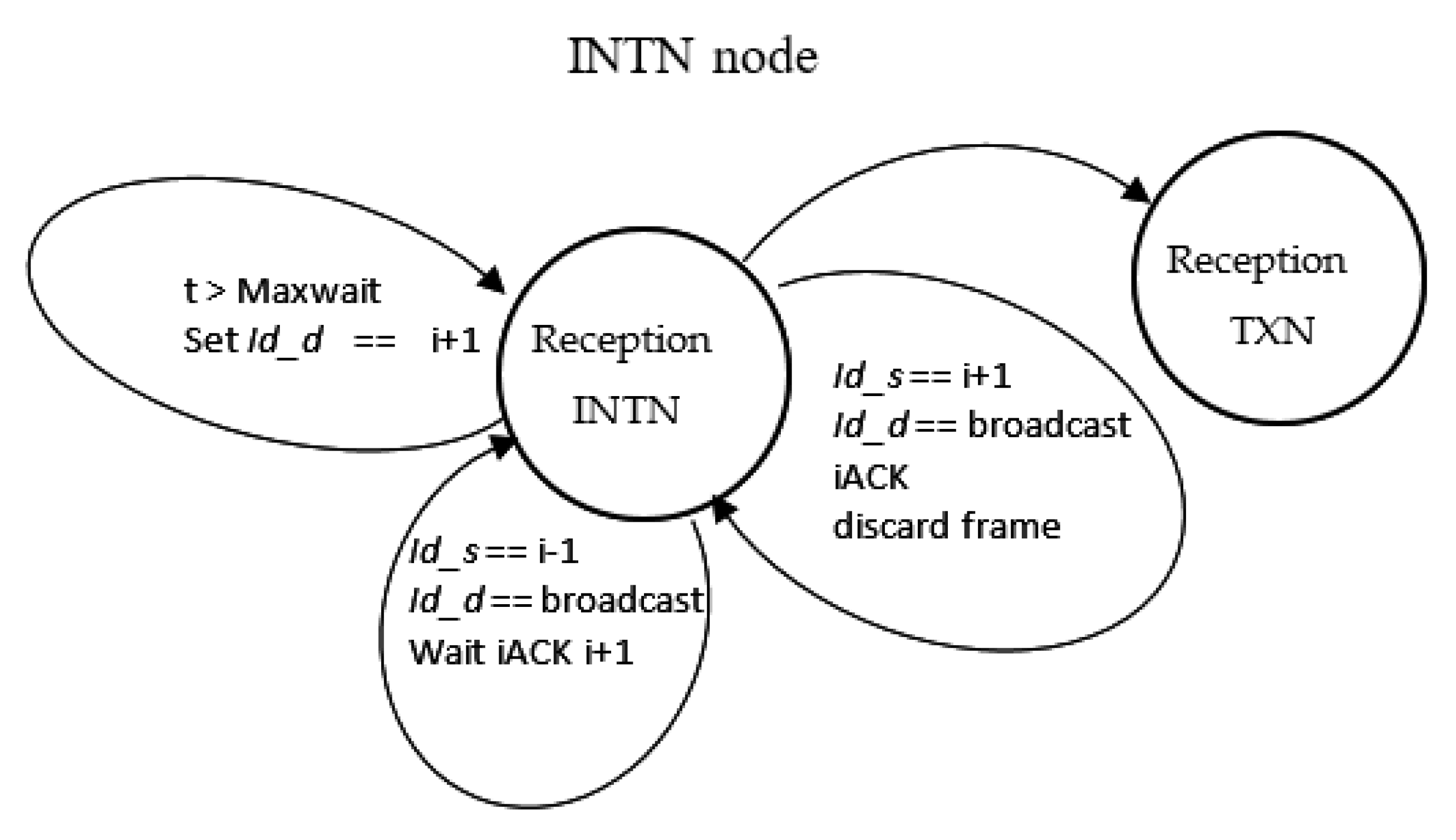
3.4. Pseudocode and State Diagram
| Algorithm 1 Pseudo-code for our proposal |
| 1 Input: id_s is source address, |
| 2 Input: id_d is destination address, |
| 3 Input: Maxwait is maximum wait time for an iACK from of node TXN or INTN, |
| 4 Input: FailN node is on |
| 5 Input: ChangeF The direction of traffic flow has not change |
| 6 if frame received then |
| 7 if frame is stored in bufferadj or bufferok then frame is discarded |
| 8 else |
| 9 case id_s == i−1, and id_d == broadcast: the node is INTN, and waits iACK from node i+1: |
| 10 case id_s == i+1: |
| 11 case id_d == broadcast: the node behaves as INTN and discards the frame clean bufferrx and stores frame in bufferok: |
| 12 case id_d == unicast: (i+3 node fail) node works as TXN and retransmits the frame with id_d = broadcast, stores the frame in buffertx: |
| 13 case id_s == i−2 and id_d == broadcast: behaves as an RXN node and retransmits the frame with id_d = broadcast, store the frame in buffertx: |
| 14 case id_s == i+2 and id_d == broadcast: |
| 15 if FailN == F then it has received an iACK, stores frame bufferok and transmits the following frame else |
| 16 case ChangeF == F, set ChangeF = T, transmit broadcast frame: |
| 17 case ChangeF == T, discard the frame: |
| 18 end if |
| 19 end if |
| 20 else |
| 21 case node INTN: retransmit unicast frame to i+1: |
| 22 case node TXN: |
| 23 if retransmission > Maxwait. then |
| 24 transmit unicast frame to node i-1 and set FailN = T |
| 25 else retransmit frame broadcast |
| 26 end if |
| 27 end if |
4. Energy and Transmission Time Analysis
4.1. System Model
- All the frames have the same length, so the transmission times are fixed.
- Distance between transmitter and receiver is 50 m.
- Probability of error when transmitting a frame in each link is the same. We include a model for comparing the latency added by a retransmission using eACK or iACK. Nevertheless, for the sake of simplicity, we did not consider retransmissions in the end-to-end analysis.
- ACK frames have a constant length.
- If the transmitted data collides at the receiver, the macAckWait duration (an IEEE 802.15.4 attribute dependent on constants and attributes of the physical layer, which defines the maximum number of symbols to wait for an ACK frame) for the transmitting node is the sum of the turnaround time of 12 Ts and the ACK duration of 22 Ts, a total of 34 Ts considering Ts = 16 μs and 1 symbol is 4 bits.
- A CCA is successful when no transmission is detected from any node, at the time of initiation of its CCA. In the IEEE 802.15.4 standard, the channel state is averaged over 8 Ts.
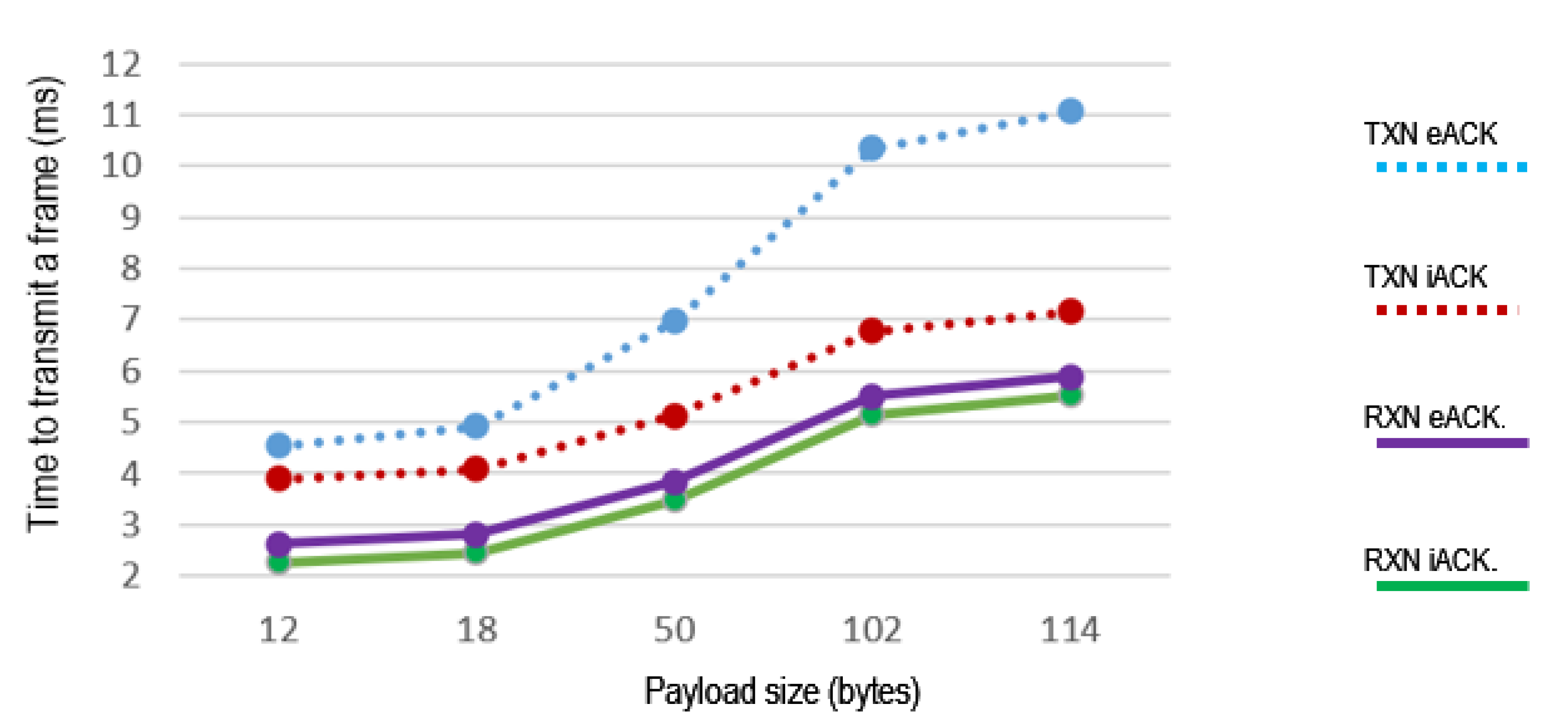
4.2. End-to-End Transmission Time
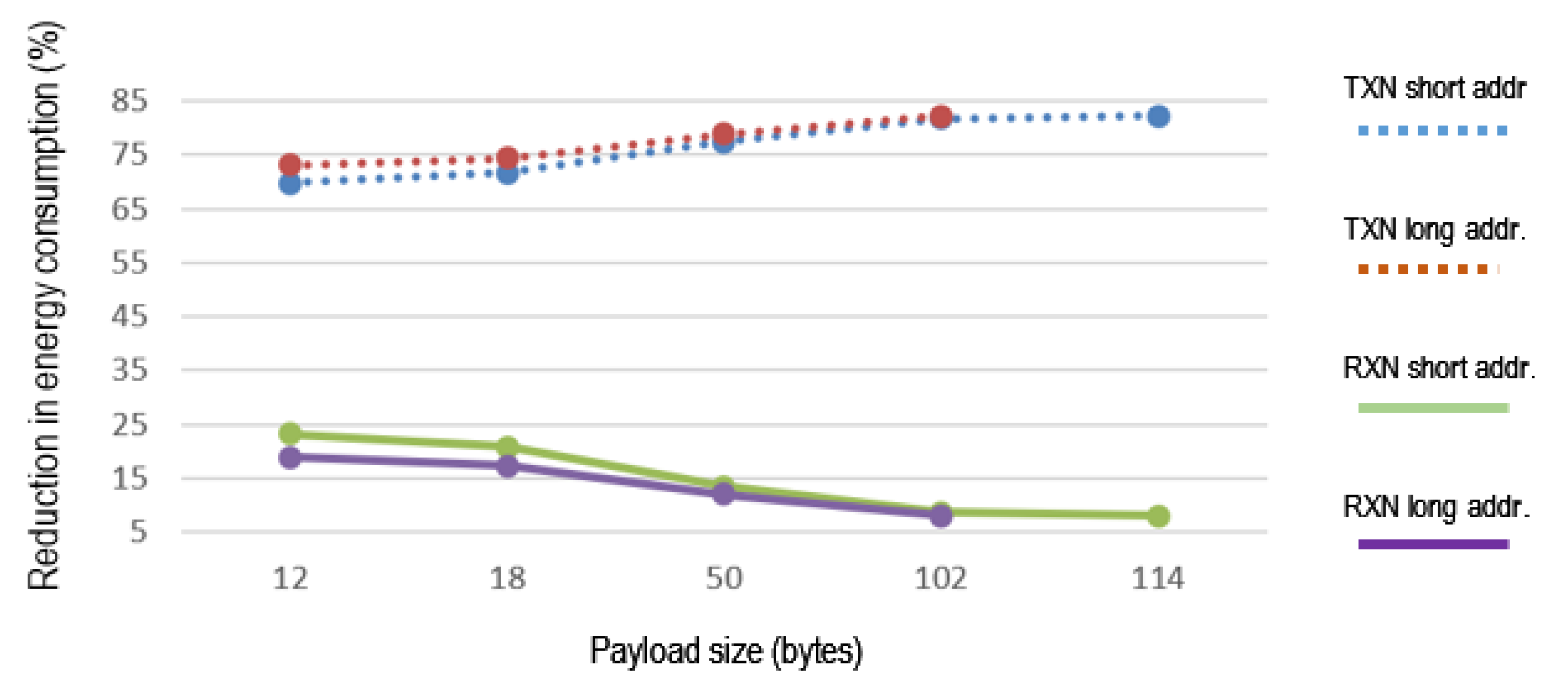
4.3. Energy Consumption
5. Implementation
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Kocakulak, M.; Butun, I. An Overview of Wireless Sensor Networks towards Internet of Things. In Proceedings of the IEEE 7th Annual Computing and Communication Workshop and Conference, Las Vegas, NV, USA, 9–11 January 2017. [Google Scholar] [CrossRef]
- Varshney, S.; Kumar, C.; Swaroop, A. Leach Based Hierarchical Routing Protocol for Monitoring of Over-ground Pipelines Using Linear Wireless Sensor Networks. Procedia Comput. Sci. 2018, 125, 208–214. [Google Scholar] [CrossRef]
- Zhang, M.; Wang, N.; Chen, L. Sensing Technologies and Automation for Precision Agriculture. In Women in Precision Agriculture. Women in Engineering and Science; Khemais, T.H., Ed.; Springer Nature Switzerland AG: Cham, Switzerland, 2021; pp. 34–54. [Google Scholar] [CrossRef]
- Singh, P.K.; Paprzycki, M. Introduction on Wireless Sensor Networks Issues and Challenges in Current Era. In Handbook of Wireless Sensor Networks: Issues and Challenges in Current Scenario’s. Advances in Intelligent Systems and Computing; Singh, P., Bhargava, B., Paprzycki, M., Kaushal, N., Hong, W.C., Eds.; Springer: Cham, Switzerland, 2020; Volume 1132. [Google Scholar] [CrossRef]
- Joshi, H.; Ravindra, E. MAC Protocols for Application-Specific Wireless Sensor Networks: A Study. Int. J. Res. Eng. Sci. Manag. 2018, 1, 2581–5782. [Google Scholar]
- Jawhar, I.; Mohamed, N.; Shuaib, K.; Kesserwan, N. An Efficient Framework and Networking Protocol for Linear Wireless Sensor Networks. Ad Hoc Sens. Wirel. Netw. 2009, 7, 3–21. [Google Scholar]
- Raja, M.K.; Chen, X.; Lei, Y.D.; Bin, Z.; Yeung, B.C.; Yuan, X. A 18 mW Tx, 22 mW Rx Transceiver for 2.45 GHz IEEE 802.15.4 WPAN in 0.18 μm CMOS. In Proceedings of the 2010 IEEE Asian Solid-State Circuits Conference, Beijing, China, 8–10 November 2010. [Google Scholar] [CrossRef]
- Farhad, A.; Zia, Y.; Hussain, F.B. Survey of Dynamic Super-Frame Adjustment Schemes in Beacon-Enabled IEEE 802.15.4 Networks: An Application’s Perspective. Wirel. Pers. Commun. 2016, 91, 119–135. [Google Scholar] [CrossRef]
- Jawhar, I.; Mohamed, N.; Agrawal, D.P. Linear wireless sensor networks: Classification and applications. J. Netw. Comput. Appl. 2011, 34, 1671–1682. [Google Scholar] [CrossRef]
- Sarr, M.D.; Delobel, F.; Misson, M.; Niang, I. Robust Discovery, Addressing and Routing Protocol for Dynamic Linear Networks. In Proceedings of the International Symposium on Wireless Communication Systems, Bologna, Italy, 28–31 August 2017. [Google Scholar] [CrossRef]
- Varshney, S.; Kumar, C.; Swaroop, A. Linear Sensor Networks: Applications, Issues and Major Research Trends. In Proceedings of the International Conference on Computing, Communication and Automation, Greater Noida, India, 5–6 May 2015. [Google Scholar] [CrossRef]
- Varshney, V.; Rajput, P.K.; Singh, A.; Varshney, G. Routing Techniques Used for Monitoring the Linear Structures Using Linear Wireless Sensor Networks: An Overview. In Proceedings of the International Conference on Computing, Communication, and Intelligent Systems, Greater Noida, India, 18–19 October 2019. [Google Scholar] [CrossRef]
- Fang, C.; Liu, H.; Qian, L. LC-MAC: An Efficient MAC Protocol for the Long-Chain Wireless Sensor Networks. In Proceedings of the 3rd International Conference on Communications and Mobile Computing, CMC, Qingdao, China, 18–20 April 2011. [Google Scholar] [CrossRef]
- Li, Z.; Chen, Q.; Zhu, G.; Choi, Y. A Delay-Aware MAC Protocol with Implicit RTS. In Proceedings of the 2014 International Conference on Information and Communication Technology Convergence (ICTC), Busan, Korea, 22–24 October 2014; pp. 541–544. [Google Scholar]
- Ndoye, E.H.; Jacquet, C.; Misson, M.; Niang, I. Using a Token Approach for the MAC Layer of Linear Sensor Networks: Impact of the Node Position on the Packet Delivery. In Proceedings of the 2014 IFIP Wireless Days (WD), Rio de Janeiro, Brazil, 12–14 November 2014. [Google Scholar] [CrossRef]
- Wang, J.; Ren, X.; Chen, F.J.; Chen, Y.; Xu, G. On MAC optimization for large-scale wireless sensor network. Wirel. Netw. 2016, 22, 1877–1889. [Google Scholar] [CrossRef]
- Sokullu, R.; Demir, E. A comparative study of MAC protocols for linear WSNs. Procedia Comput. Sci. 2015, 52, 492–499. [Google Scholar] [CrossRef]
- Vuletic, P. Application of WSN in Railway Intelligent Transportation System (RITS). In Proceedings of the 2015 23rd Telecommunications Forum, Belgrade, Serbia, 24–25 November 2015. [Google Scholar] [CrossRef]
- Shokri, R.; Yazdani, N.; Yazdani, N.; Khonsari, A. Chain-Based Anonymous Routing for Wireless Ad Hoc Networks. In Proceedings of the Consumer Communications and Networking Conference, Las Vegas, NV, USA, 11–13 January 2007; pp. 297–302. [Google Scholar]
- Sun, Z.Z.X.; He, J.; Chen, Y.; Ma, S. A New Routing Algorithm for Linear Wireless Sensor Networks. In Proceedings of the 6th International Conference on Pervasive Computing and Applications, Oulu, Finland, 11–13 May 2011; pp. 497–501. [Google Scholar]
- Chen, X.; Xu, L.; Xu, M.; Wang, L. Research on the AODV routing algorithm in linear topological wireless sensor networks. Int. J. Simul. Syst. Sci. Technol. 2016, 17, 29.1–29.5. [Google Scholar] [CrossRef]
- Malarselvi, G.; Sivajayaprakash, A. A Comprehensive Survey on Applications and Transport Layer Protocols in Wireless Sensor Networks. Int. J. Eng. Technol. 2018, 5, 146–150. [Google Scholar]
- Paek, J.; Govindan, R. RCRT: Rate-Controlled Reliable Transport for Wireless Sensor Networks. In Proceedings of the 5th International Conference on Embedded Networked Sensor Systems, Sydney, NSW, Australia, 6–9 November 2007; pp. 305–319. [Google Scholar] [CrossRef]
- Sadouni, S.; Benslama, M.; Mebarki, A.; Beylot, A. SCTP-WSN New Extension for More Reliable Sparse Wireless Sensor Networks. In Proceedings of the 13th International Wireless Communications and Mobile Computing Conference (IWCMC), Valencia, Spain, 26–30 June 2017; pp. 2109–2114. [Google Scholar] [CrossRef]
- Park, S.; Vedantham, R.; Sivakumar, R.; Akyildiz, I. GARUDA: Achieving Effective Reliability for Downstream Communication in Wireless Sensor Networks. IEEE Trans. Mob. Comput. 2008, 7, 214–230. [Google Scholar] [CrossRef]
- Sohraby, K.; Minoli, D.; Znati, T. Wireless Sensor Networks: Technology, Protocols, and Applications; Wiley-Interscience: Hoboken, NJ, USA, 2007; pp. 229–244. [Google Scholar]
- Gitman, I. Comparison of Hop-By-Hop and End-To-End Acknowledgment Schemes in Computer Communication Networks. IEEE Trans. Commun. 1976, 24, 1258–1262. [Google Scholar] [CrossRef]
- Rosberg, Z.; Liu, R.P.; Dong, Y.A.; Tuan, L.D.; Jha, S. ARQ with Implicit and Explicit ACKs in Wireless Sensor Networks. In Proceedings of the GLOBECOM—IEEE Global Telecommunications Conference, Taipei, Taiwan, 7–11 December 2008. [Google Scholar] [CrossRef]
- Rusli, M.E.; Harris, R.; Punchihewa, A. Performance Analysis of Implicit Acknowledgement Coordination Scheme for Opportunistic Routing in Wireless Sensor Networks. In Proceedings of the 2012 International Symposium on Telecommunication Technologies, Kuala Lumpur, Malaysia, 26–28 November 2012. [Google Scholar] [CrossRef]
- Ruiz, M.T.; Lytras, M.D.; Mathkour, H. Innovative services and applications of wireless sensor networks: Research challenges and opportunities. Int. J. Distrib. Sens. Netw. 2018, 14, 5. [Google Scholar] [CrossRef]
- Rahbari, D.; Nickray, M. Low-latency and energy-efficient scheduling in fog-based IoT applications. Turk. J. Electr. Eng. Comput. Sci. 2019, 27, 1406–1427. [Google Scholar] [CrossRef]
- Dwivedi, R.K.; Kumar, R. Sensor Cloud: Integrating Wireless Sensor Networks with Cloud Computing. In Proceedings of the 5th IEEE Uttar Pradesh Section International Conference on Electrical, Electronics and Computer Engineering, Gorakhpur, India, 2–4 November 2018. [Google Scholar] [CrossRef]
- Kim, B.S.; Il Kim, K.; Shah, B.; Chow, F.; Kim, K.H. Wireless sensor networks for big data systems. Sensors 2019, 19, 1565. [Google Scholar] [CrossRef] [PubMed]
- Ali, S. SimpliMote: A Wireless Sensor Network Monitoring Platform for Oil and Gas Pipelines. IEEE Syst. J. 2018, 12, 778–789. [Google Scholar] [CrossRef]
- Zimmerling, M.; Dargie, W.; Reason, J.M. Energy-Efficient Routing in Linear Wireless Sensor Networks. In Proceedings of the IEEE International Conference on Mobile Adhoc and Sensor Systems, Washington, DC, USA, 7 November 2007. [Google Scholar] [CrossRef]
- Hammoudeh, M. A wireless sensor network border monitoring system: Deployment issues and routing protocols. IEEE Sens. J. 2017, 17, 2572–2582. [Google Scholar] [CrossRef]
- Elnaggar, O.E.; Ramadan, R.A.; Fayek, M.B. WSN in monitoring oil pipelines using ACO and GA. Procedia Comput. Sci. 2015, 52, 1198–1205. [Google Scholar] [CrossRef]
- Tong, F.; Ni, M.; Shu, L.; Pan, J. A Pipelined-Forwarding, Routing Integrated and Effectively-Identifying MAC for Large-Scale WSN. In Proceedings of the GLOBCOM, Atlanta, GA, USA, 9–13 November 2013; pp. 225–230. [Google Scholar] [CrossRef]
- Villordo, I.; Torres, N.; Carvalho, M.; Menchaca, R.; Rivero, M.; Menchaca, R. A Selective-Awakening MAC Protocol for Energy-Efficient Data Forwarding in Linear Sensor Networks. Wirel. Commun. Mob. Comput. 2018, 2018, 6351623. [Google Scholar] [CrossRef]
- Khanh, H.; Ock, C.; Kim, M. RP-MAC A Cross-Layer Duty Cycle MAC Protocol with a Reduced Pipelined-Forwarding Feature for Wireless Sensor Networks. In Proceedings of the 11th International Wireless Communications and Mobile Computing Conference, IWCMC 2015, Dubrovnik, Croatia, 24–28 August 2015; pp. 1469–1474. [Google Scholar] [CrossRef]
- Khaliq, S.; Henna, S. HE-PRMAC Hop Extended Pipelined Routing Enhanced MAC Protocol for Wireless Sensor Networks. In Proceedings of the Sixth International Conference on Innovative Computing Technology (INTECH), Dublin, Ireland, 24–26 August 2016; pp. 392–397. [Google Scholar] [CrossRef]
- Malick, E.; Diallo, O.; Hakem, N.; Jacquet, F.; Misson, M. Interference-Aware clustering approach improving QoS for linear WSNs using token based MAC protocol. Int. J. Commun. Syst. 2020, 33, 2581–5782. [Google Scholar] [CrossRef]
- Lee, S.; Su, Y.W.; Shen, C.C. A Comparative Study of Wireless Protocols: Bluetooth, UWB, ZigBee, and Wi-Fi. In Proceedings of the Industrial Electronics Conference, Vigo, Spain, 4–7 June 2007. [Google Scholar] [CrossRef]
- Egas Acosta, C.; Gil-Castiñeira, F.; Costa-Montenegro, E.; Silva, J.S. Automatic Allocation of Identifiers in Linear Wireless Sensor Networks Using Link-Level Processes. In Proceedings of the 2016 8th IEEE Latin-American Conference on Communications, Medellin, Columbia, 15–17 November 2016. [Google Scholar] [CrossRef]
- Wijetunge, S. Performance Analysis of IEEE 802.15.4 Based Wireless Sensor Networks. Ph.D. Thesis, University of Western Sydney, Sydney, Australia, 2013. [Google Scholar]
- Zhu, J.; Tao, Z.; Lv, C. Performance improvement for IEEE 802.15.4 CSMA/CA scheme in large-scale wireless multi-hop sensor networks. IET Wirel. Sens. Syst. 2013, 3, 93–103. [Google Scholar] [CrossRef]
- Zhou, H.-Y.; Luo, D.-Y.; Gao, Y.; Zuo, D.C. Modeling of Node Energy Consumption for Wireless Sensor Networks. Wirel. Sens. Netw. 2011, 3, 18–23. [Google Scholar] [CrossRef]
- Rasheed, M.B.; Javaid, N.; Imran, M.; Khan, Z.A.; Qasim, U.; Vasilakos, A. Delay and energy consumption analysis of priority guaranteed MAC protocol for wireless body area networks. Wirel. Netw. 2017, 23, 1249–1266. [Google Scholar] [CrossRef]
- Bougard, B.; Catthoor, F.; Daly, D.C.; Chandrakasan, A.; Dehaene, W. Energy Efficiency of the IEEE 802.15.4 Standard in Dense Wireless Microsensor Networks: Modeling and Improvement Perspectives. In Design, Automation, and Test in Europe: The Most Influential Papers of 10 Years Date; Lauwereins, R., Madsen, J., Eds.; Springer Science Business Media B.V.: Dordrecht, The Netherlands, 2008; pp. 221–234. ISBN 978-1-4020-6487-6. [Google Scholar] [CrossRef]
- Yan, J.; Zhou, M.; Ding, Z. Recent Advances in Energy-Efficient Routing Protocols for Wireless Sensor Networks: A Review. IEEE Access 2016, 4, 5673–5686. [Google Scholar] [CrossRef]
- Fitriawan, H.; Susanto, M.; Arifin, A.S.; Mausa, D.; Trisanto, A. ZigBee Based Wireless Sensor Networks and Performance Analysis in Various Environments. In Proceedings of the 15th International Conference on Quality in Research (QiR): International Symposium on Electrical and Computer Engineering, Bali, Indonesia, 24–27 July 2017. [Google Scholar] [CrossRef]
- Atmel Corporation. 8-Bit AVR Microcontroller with Low Power 2.4GHz Transceiver for ZigBee and IEEE 802.15.4. 2014. Available online: http://ww1.microchip.com/downloads/en/DeviceDoc/Atmel-8266-MCU_Wireless-ATmega128RFA1_Datasheet.pdf (accessed on 30 January 2021).
- Atmel Corporation. Atmel AVR10004: RCB256RFR2—Hardware User ManuaL. 2013. Available online: http://ww1.microchip.com/downloads/en/AppNotes/Atmel-42081-RCB256RFR2-Hardware-User-Manual_Application-Note_AVR10004.pdf (accessed on 30 January 2021).
- Atmel Corporation. Atmel AVR4029: Atmel Software Framework User Guide. 2013. Available online: http://ww1.microchip.com/downloads/en/appnotes/atmel-8431-8-and32-bit-microcontrollers-avr4029-atmel-software-framework-user-guide_application-note.pdf (accessed on 30 January 2021).
- Hao, C. End-to-End Delay Analysis and Measurements in Wireless Sensor Networks; Mid Sweden University: Sundsvall, Sweden, 2012. [Google Scholar]
- Nefzi, B.; Song, Y.Q. Performance analysis and improvement of ZigBee routing protocol. IFAC Proc. Vol. 2007, 40, 199–206. [Google Scholar] [CrossRef]
- Tall, H.; Chalhoub, G. ABORt: Acknowledgement-based opportunistic routing protocol for high data rate multichannel WSNs. J. Sens. Actuator Netw. 2017, 6, 23. [Google Scholar] [CrossRef]
- Calveras, A.; Ludovici, A. Implementation and Evaluation of Multi-Hop Routing in 6LoWPAN. In Proceedings of the IX Jornadas de Ingeniería Telemática (JITEL 2010), Valladolid, Spain, 29 September–1 October 2010. [Google Scholar]





| Address Autoconfig. | Same Net. and Link Addr. | eACK | iACK | Linear Topology | Clustering | End-to-End Reliability | Topology Discovery | Energy Efficient | Considers End-to-End Delay | Large Scale | Access Channel | Protection against Link and Node Failure | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| This proposal | yes | yes | no | yes | yes | no | yes | yes | Yes | yes | yes | CSMA/CA | yes |
| Application and transport level | |||||||||||||
| RCRT [23] | no | no | yes | no | no | No | yes | no | No | yes | no | n.a | yes |
| GARUDA [25] | no | no | yes | no | no | Yes | yes | no | n.a. | no | yes | n.a | yes |
| ATP [26] | no | no | yes | no | no | No | yes | no | No | yes | yes | n.a | no |
| SCTPWSN [24] | no | no | yes | no | no | No | yes | yes | n.a. | no | yes | n.a. | yes |
| Network level | |||||||||||||
| SimpliMote [34] | no | yes | no | no | yes | No | no | yes | yes | no | yes | n.a. | yes |
| MERR [35] | no | no | no | no | yes | No | no | no | yes | no | yes | n.a. | no |
| LDG [36] | no | no | no | no | no | Yes | no | yes | yes | yes | yes | n.a | no |
| DiscoProto [10] | yes | yes | no | no | no | Yes | no | yes | no | yes | yes | TMAC | yes |
| ACO&GA [37] | no | no | no | no | yes | No | no | no | yes | no | yes | n.a. | no |
| LBHRP [2] | no | no | no | no | no | Yes | no | yes | no | no | yes | TDMA | yes |
| ROLS [6] | yes | no | no | yes | yes | Yes | no | no | no | no | yes | n.a. | yes |
| WTDP [29] | yes | no | no | no | no | No | no | yes | no | no | no | aloha | no |
| Link level | |||||||||||||
| PRIMAC [38] | no | no | yes | no | yes | No | no | yes | no | no | yes | n.a | no |
| SA-MAC [39] | no | no | yes | no | yes | Yes | yes | yes | no | yes | no | TDMA | no |
| RP MAC [40] | no | no | yes | no | yes | No | no | no | yes | yes | no | n.a. | no |
| HEPRMAC [41] | no | no | no | no | no | No | no | no | yes | yes | no | TDMA | no |
| Token [42] | no | no | yes | no | yes | Yes | no | no | n.a. | yes | no | Token | no |
| LCMAC [13] | no | no | yes | no | no | No | yes | no | yes | yes | yes | n.a. | no |
| MIMAC [16] | no | no | yes | no | yes | No | no | no | yes | yes | yes | CSMA/CA | no |
| Payload | Required Hops |
|---|---|
| 12 | 1 |
| 18 | 1 |
| 50 | 3 |
| 102 | 6 |
| 114 | 7 |
| Intermediate Nodes | LWSN Length (Km) | eACK Delay (s) | iACK Delay (s) |
|---|---|---|---|
| 100 | 3 | 0.33441 | 0.30721 |
| 1000 | 30 | 3.3441 | 3.0721 |
| 2000 | 60 | 6.6882 | 6.1442 |
| 3000 | 90 | 10.0323 | 9.2163 |
| 4000 | 120 | 13.3764 | 12.2884 |
| Payload | |||
|---|---|---|---|
| 18 | 22.5% | 36% | −8% |
| 114 | 8% | 14% | −2% |
| Parameter | Description |
|---|---|
| Transmission power | 0.5 dBm |
| Distance between nodes | 25 m |
| 802.15.4 broadcast frame TXN | 0.384 ms, 12 bytes |
| Processing Time at Node RXN | |||
|---|---|---|---|
| Measured [ms] | Calculated [ms] | % error | |
| eACK | 3.78 | 3.32 | 12% |
| iACK | 3.43 | 3.27 | 4.6% |
| Difference | 0.35 | 0.05 | |
| Processing Time at Node TXN | |||
|---|---|---|---|
| Measured [ms] | Calculated [ms] | % error | |
| eACK | 6.98 | 6.33 | 9.31% |
| iACK | 6.66 | 5.82 | 12% |
| Difference | 0.32 | 0.51 | |
| End to End Delay | |||
|---|---|---|---|
| Hop | Our proposal | 6LowPAN | LWSN length |
| 1 | 3.43 ms | 13.88 ms | 50 m |
| 10 | 34.3 ms | 138.8 ms | 275 m |
| 100 | 343 ms | 1.38 s | 2.525 km |
| 1000 | 3.43 s | 13.88 s | 25 km |
| 2800 | 9.06 s | 38.86 s | 70 km |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Acosta., C.E.; Gil-Castiñeira, F.; Costa-Montenegro, E.; Silva, J.S. Reliable Link Level Routing Algorithm in Pipeline Monitoring Using Implicit Acknowledgements. Sensors 2021, 21, 968. https://doi.org/10.3390/s21030968
Acosta. CE, Gil-Castiñeira F, Costa-Montenegro E, Silva JS. Reliable Link Level Routing Algorithm in Pipeline Monitoring Using Implicit Acknowledgements. Sensors. 2021; 21(3):968. https://doi.org/10.3390/s21030968
Chicago/Turabian StyleAcosta., Carlos Egas, Felipe Gil-Castiñeira, Enrique Costa-Montenegro, and Jorge Sá Silva. 2021. "Reliable Link Level Routing Algorithm in Pipeline Monitoring Using Implicit Acknowledgements" Sensors 21, no. 3: 968. https://doi.org/10.3390/s21030968
APA StyleAcosta., C. E., Gil-Castiñeira, F., Costa-Montenegro, E., & Silva, J. S. (2021). Reliable Link Level Routing Algorithm in Pipeline Monitoring Using Implicit Acknowledgements. Sensors, 21(3), 968. https://doi.org/10.3390/s21030968







